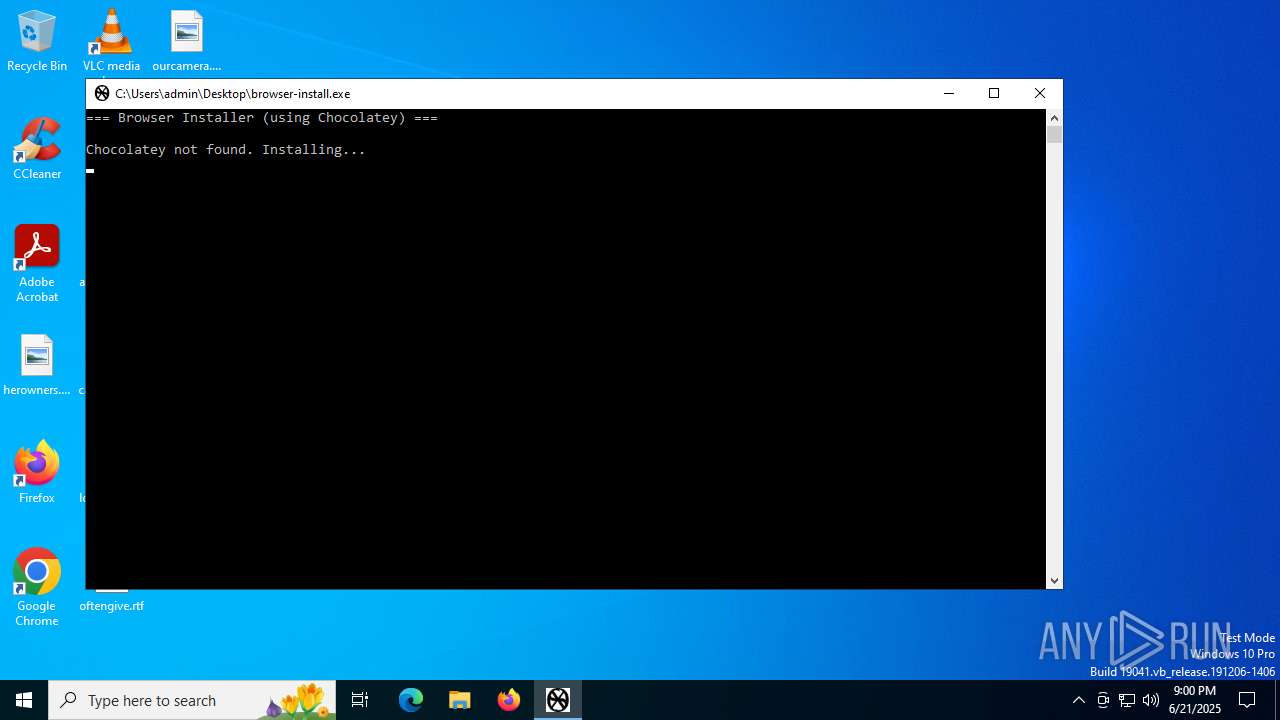
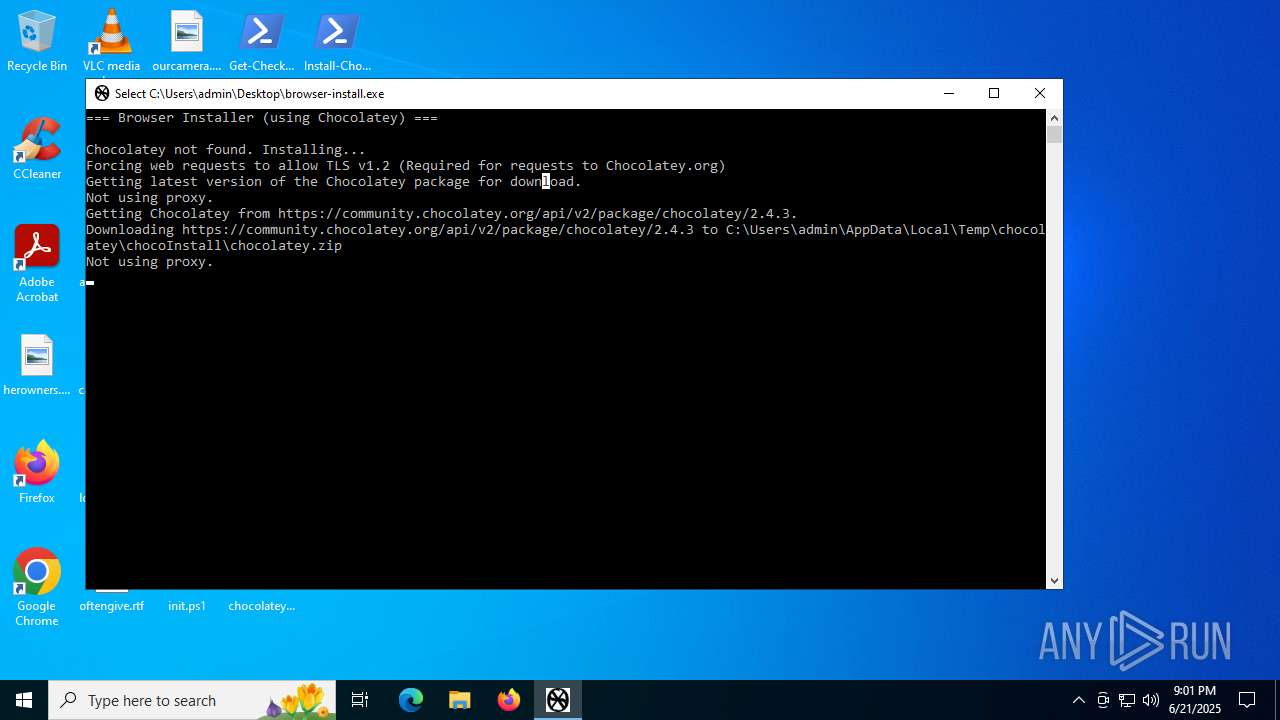
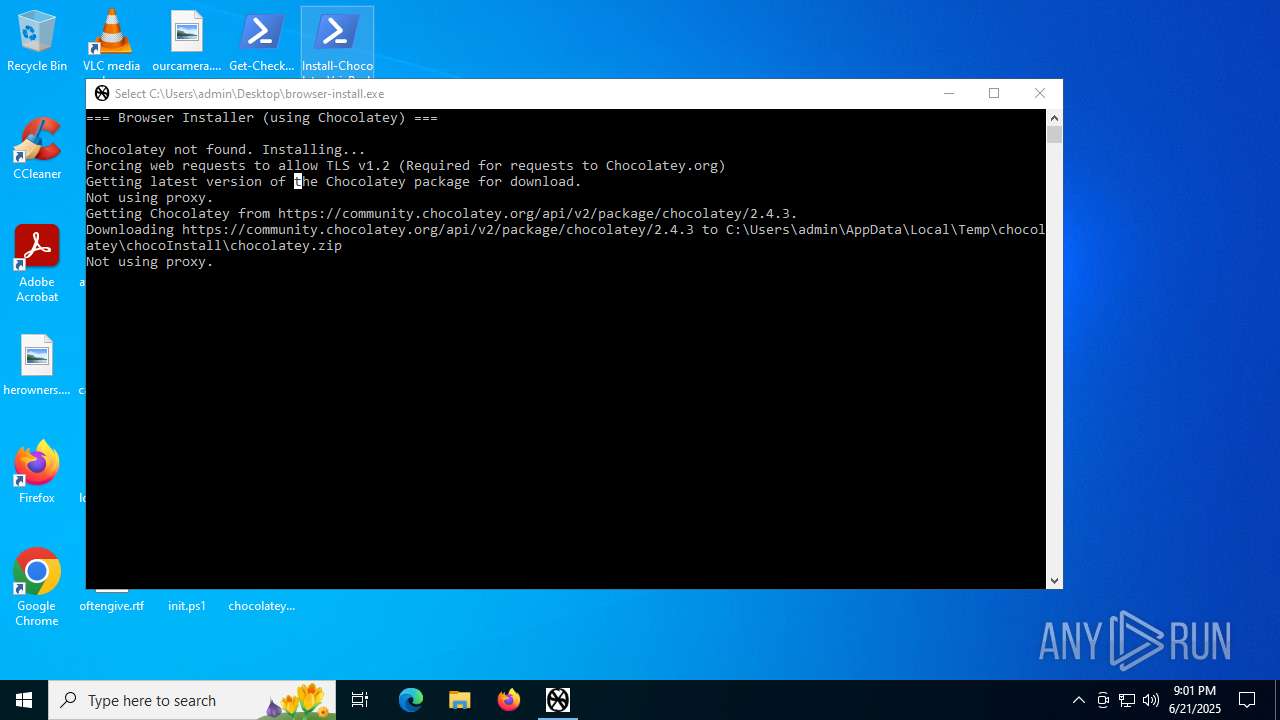
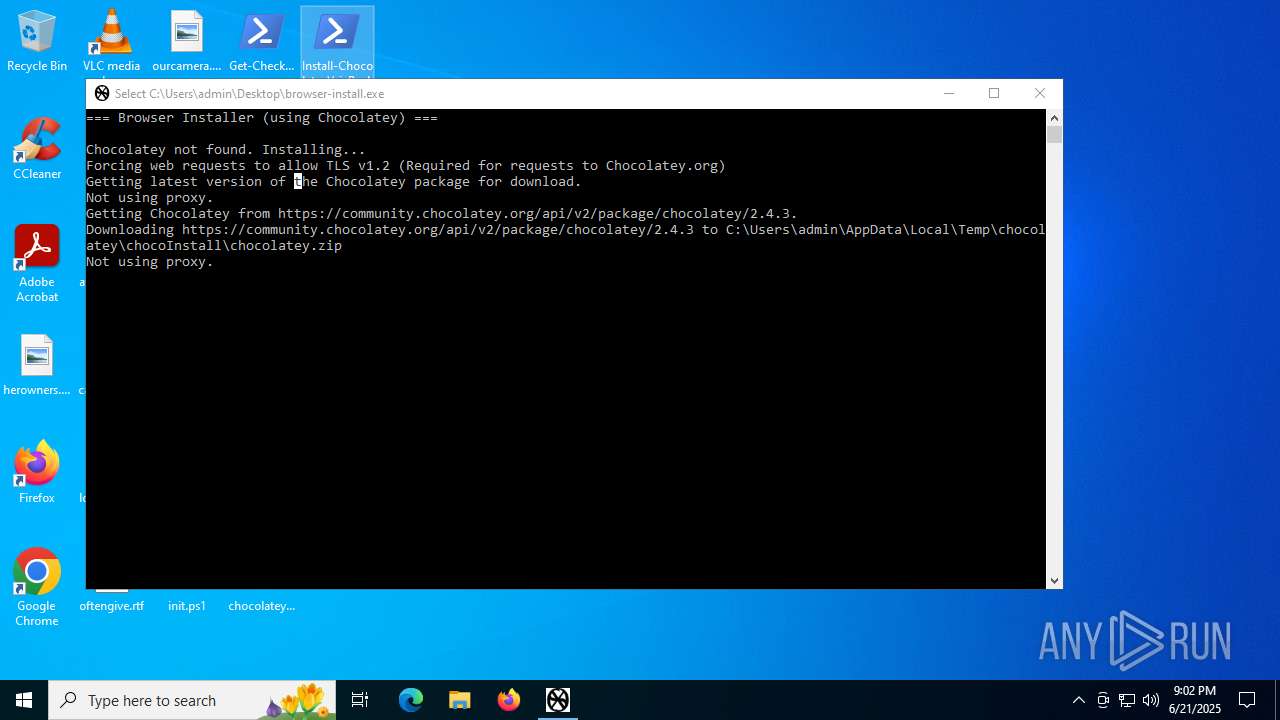
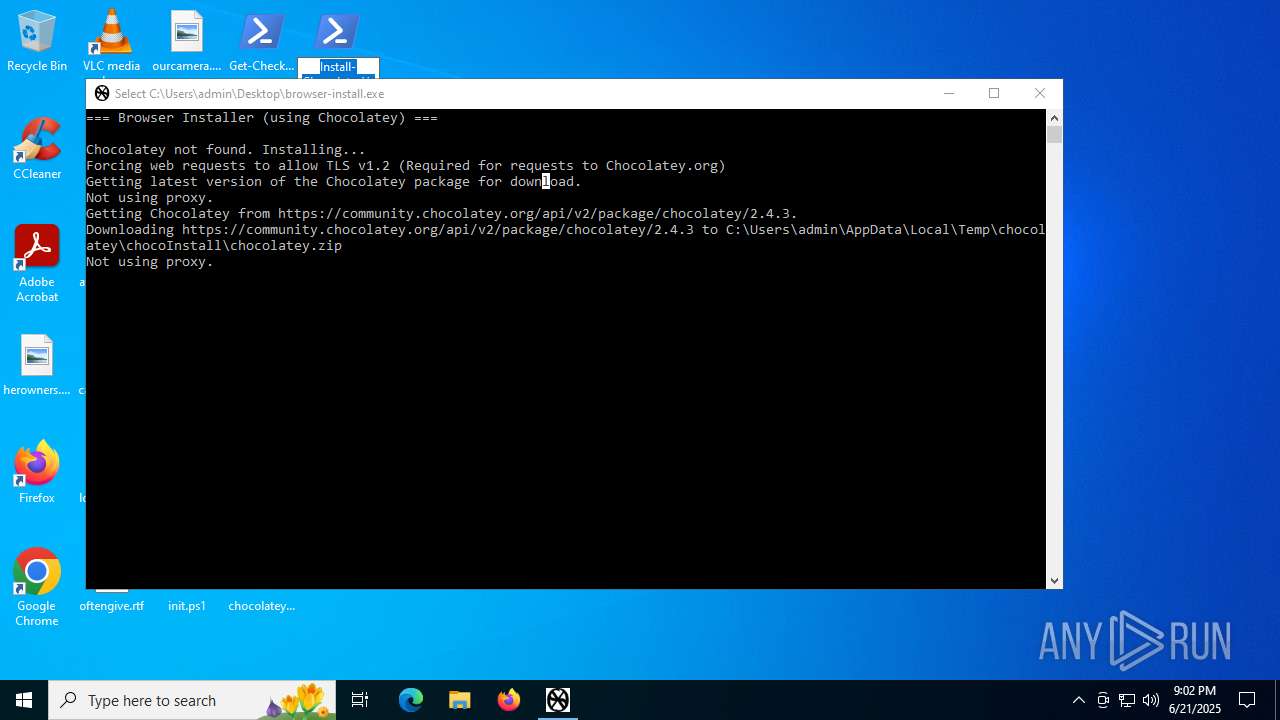
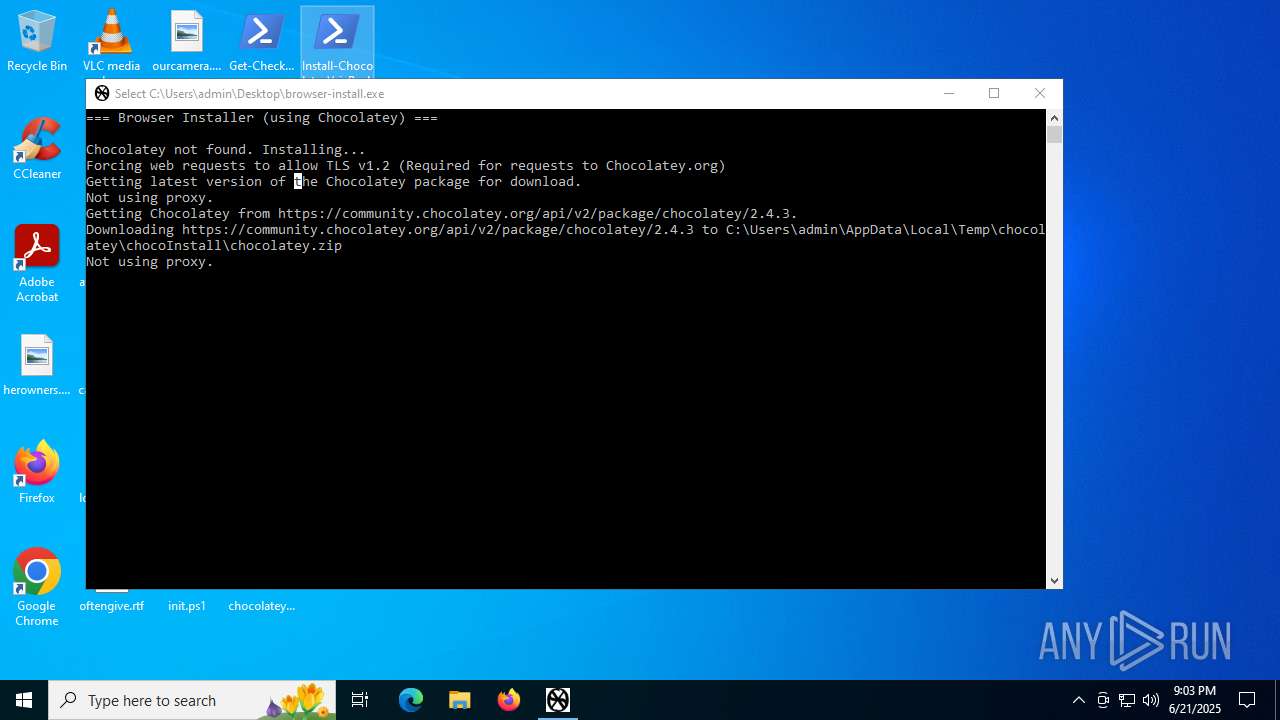
| File name: | browser-install.exe |
| Full analysis: | https://app.any.run/tasks/10f28d1b-3215-4661-8c90-0160643ee0c7 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 21:00:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2425BA44CD77B9CB1B23B41C912BE2F9 |
| SHA1: | F04CDD543FB0EB624ABCADD410049C80D8D123A4 |
| SHA256: | 6C446ACEF4165F8EC20A4B4E3B92689E18CD9BF8D83EA678BFA1304970718E25 |
| SSDEEP: | 384:dpKFO3gqQbw78zcb4GckOHE6D394hxjNiQDrTRDca4/ArouquJ/lW1:dug85tPHE6D394h1rq3qoe/q |
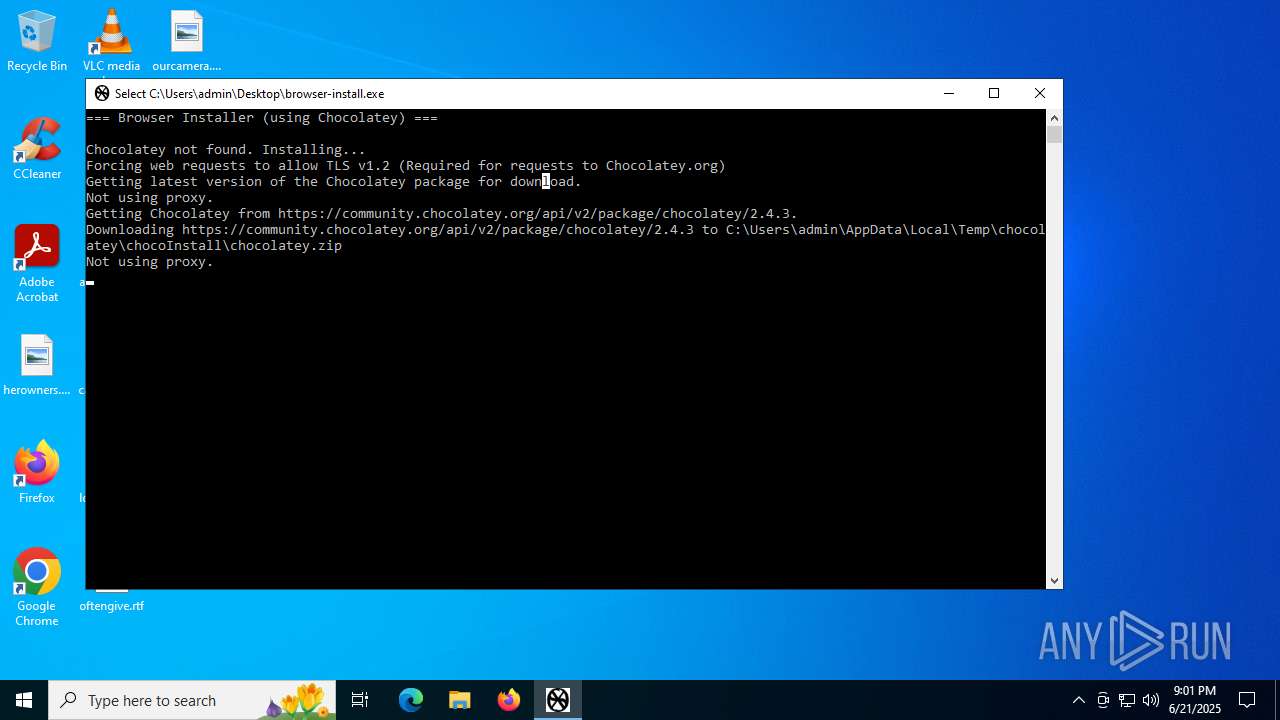
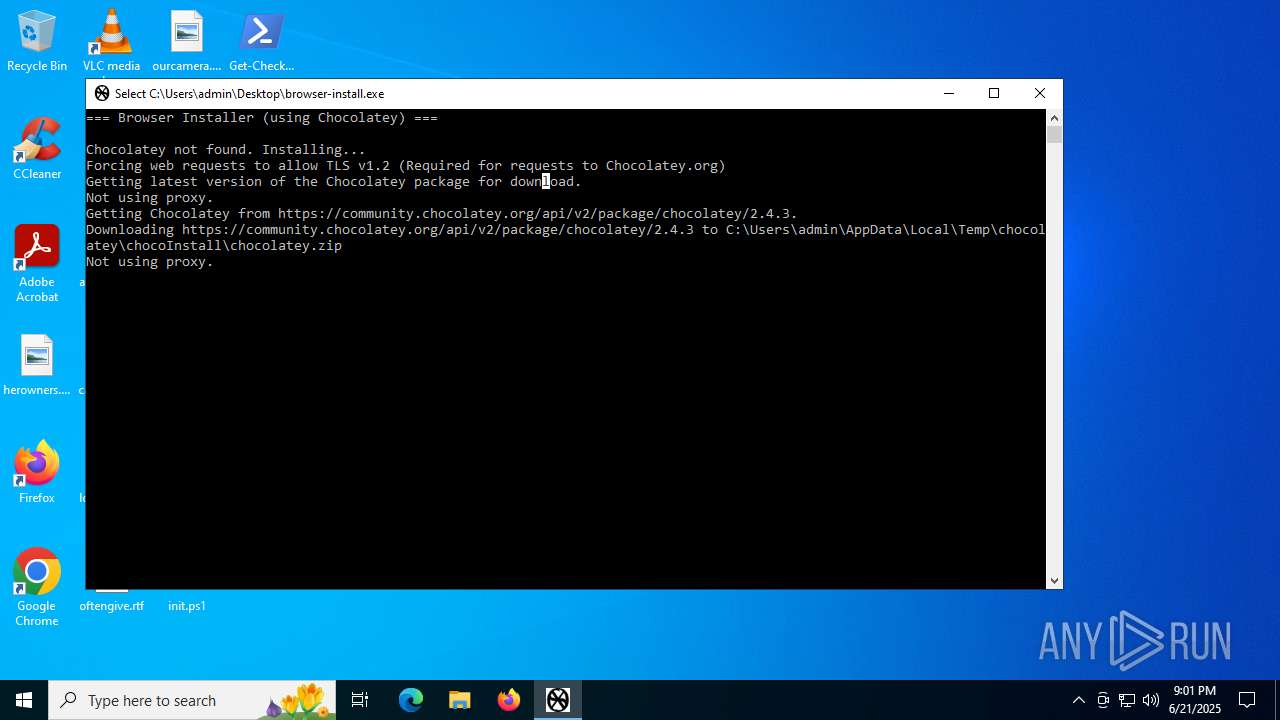
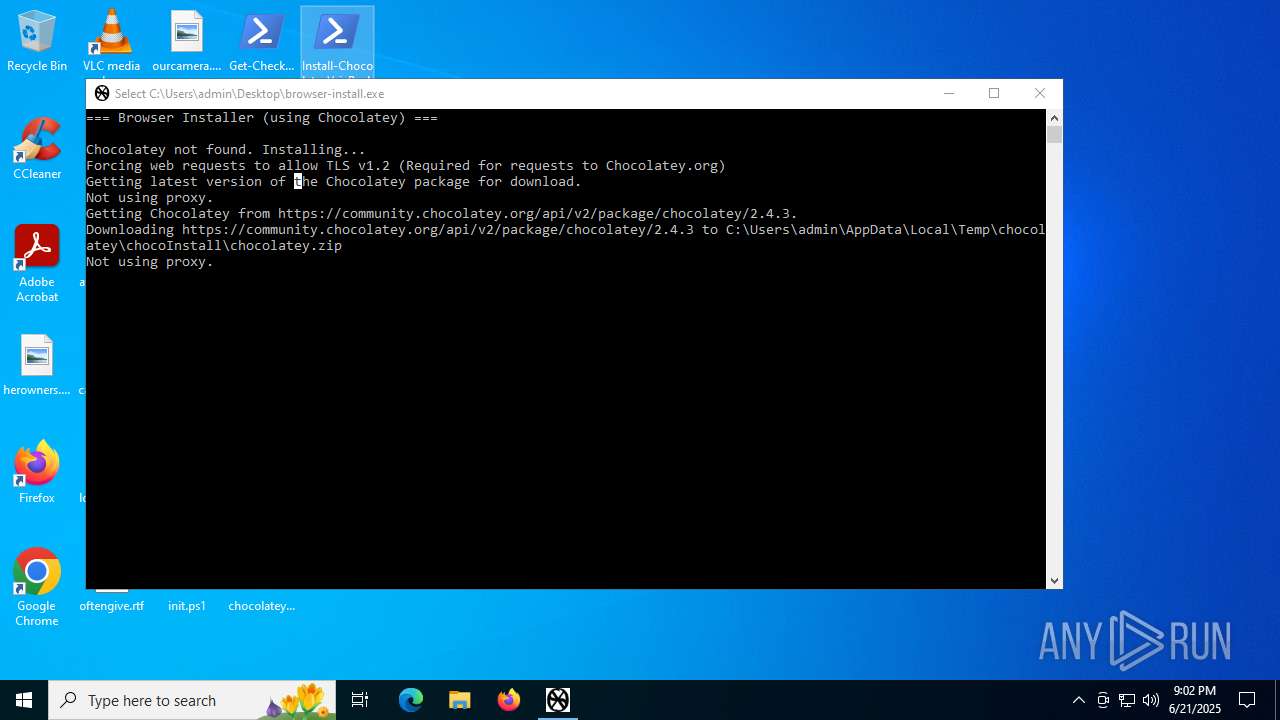
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 2804)
- powershell.exe (PID: 2228)
- powershell.exe (PID: 1936)
- powershell.exe (PID: 5252)
- powershell.exe (PID: 6936)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 5768)
- powershell.exe (PID: 6896)
Changes powershell execution policy (Bypass)
- browser-install.exe (PID: 1520)
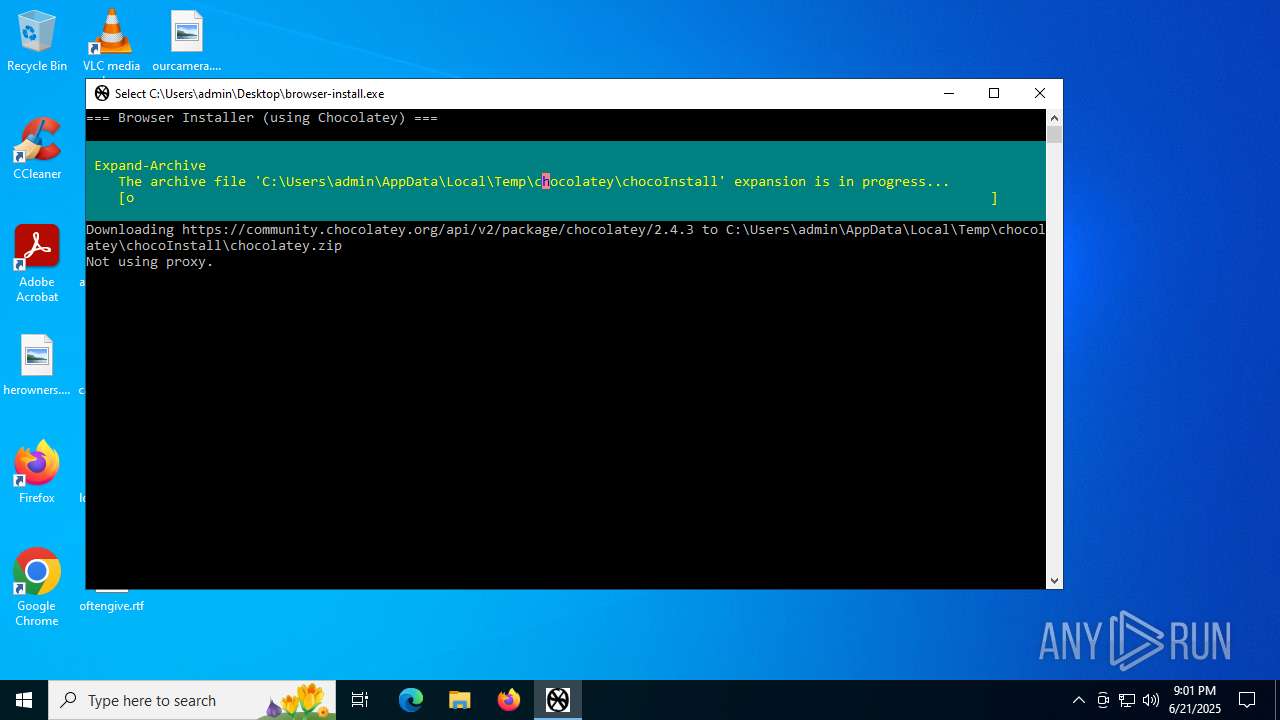
Script downloads file (POWERSHELL)
- powershell.exe (PID: 2804)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 2804)
SUSPICIOUS
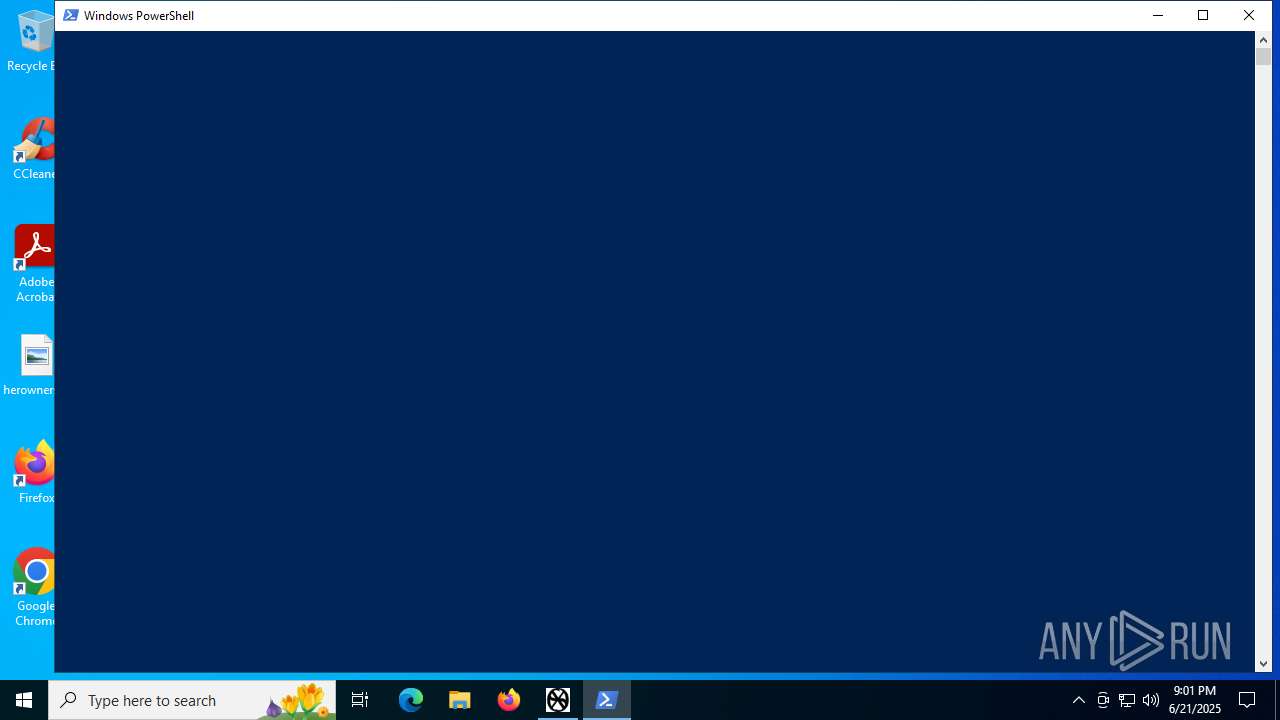
The process executes Powershell scripts
- browser-install.exe (PID: 1520)
The process bypasses the loading of PowerShell profile settings
- browser-install.exe (PID: 1520)
Starts POWERSHELL.EXE for commands execution
- browser-install.exe (PID: 1520)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 2804)
Possibly malicious use of IEX has been detected
- browser-install.exe (PID: 1520)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 2804)
Executable content was dropped or overwritten
- powershell.exe (PID: 2804)
The process creates files with name similar to system file names
- powershell.exe (PID: 2804)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 2804)
Application launched itself
- cmd.exe (PID: 7072)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 6948)
- cmd.exe (PID: 3756)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7072)
Probably download files using WebClient
- browser-install.exe (PID: 1520)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 2804)
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 2804)
INFO
Checks supported languages
- browser-install.exe (PID: 1520)
Reads the computer name
- browser-install.exe (PID: 1520)
Disables trace logs
- powershell.exe (PID: 2804)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2804)
Checks proxy server information
- powershell.exe (PID: 2804)
- slui.exe (PID: 2032)
The sample compiled with english language support
- powershell.exe (PID: 2804)
Manual execution by a user
- powershell.exe (PID: 1936)
- powershell.exe (PID: 5252)
- powershell.exe (PID: 2228)
- powershell.exe (PID: 6936)
- cmd.exe (PID: 7072)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 5768)
- powershell.exe (PID: 6896)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2804)
- powershell.exe (PID: 6896)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2848)
- WMIC.exe (PID: 5628)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2804)
Reads the software policy settings
- slui.exe (PID: 2032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2044:05:01 18:07:02+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 7168 |
| InitializedDataSize: | 108544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3aca |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | browser-install |
| FileVersion: | 1.0.0.0 |
| InternalName: | browser-install.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | browser-install.exe |
| ProductName: | browser-install |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
183
Monitored processes
50
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1200 | "C:\WINDOWS\System32\Reg" QUERY "HKLM\System\CurrentControlSet\Control\Session Manager\Environment" /v "POWERSHELL_DISTRIBUTION_CHANNEL" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | C:\WINDOWS\system32\cmd.exe /S /D /c" set /p dummy="Refreshing environment variables from registry for cmd.exe. Please wait..."" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | "C:\WINDOWS\System32\Reg" QUERY "HKLM\System\CurrentControlSet\Control\Session Manager\Environment" /v "PROCESSOR_LEVEL" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\Desktop\browser-install.exe" | C:\Users\admin\Desktop\browser-install.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: browser-install Version: 1.0.0.0 Modules
| |||||||||||||||
| 1560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1740 | "C:\WINDOWS\System32\Reg" QUERY "HKCU\Environment" /v "TEMP" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1936 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\init.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
47 220
Read events
47 206
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2804) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
7
Suspicious files
24
Text files
84
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bqw4dase.11z.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocoInstall\chocolatey.nuspec | xml | |
MD5:A4E0034972F8F29B70847FE6F04593DD | SHA256:B243F33B776F1E24492629350FBA09E0105A862B53CB5253852CF22A0023C4DC | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocoInstall\tools\chocolateyInstall.ps1 | text | |
MD5:DB89FC7120818885D1A1E112AC7BE6C1 | SHA256:C46903CFED1D74620630D0653CE057B3079AF5789AFEB1A5F884298A8693B4EC | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bcgnjg2z.dsi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocoInstall\tools\chocolateyInstall\helpers\Chocolatey.PowerShell.dll-help.xml | xml | |
MD5:4AEA8AE4FCE73819E9ED3F0D1DDCCE15 | SHA256:DAE3916C3CBAB1E4FC6EC9AFB052D878DFB6DF4430B1CD7DB2FEE836F9FC0DAE | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocoInstall\tools\chocolateyInstall\CREDITS.txt | text | |
MD5:2FDBAE8C0D612245A358336D15C76E70 | SHA256:CCA29EBA9D06E746B5ABECA46DD5864FE410A2D461F72820D093BEA792AF962A | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocoInstall\_rels\.rels | xml | |
MD5:FD1D900C4D3CED664DD6397316A4F594 | SHA256:CC55A8AD652B47CAC23FF0C02217AC43001B52F613348FCC151DF8D2F800EC9C | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocoInstall\tools\chocolateysetup.psm1 | text | |
MD5:D082F6FA1357886CA99CFD9EB03FAA04 | SHA256:FB8E51208A641C5BEF628629BADAE9E3530A7D71495687BBA75EF88473C64026 | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocoInstall\tools\chocolateyInstall\choco.exe | executable | |
MD5:C55851E6BB0578E19C16F48A531F99C0 | SHA256:39B3C01845B3FE22B2577B62672437D3EE9C372C085A657BCB82C189BD7FD11F | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\chocolatey\chocoInstall\tools\init.ps1 | text | |
MD5:534EDDF59B2A518F5475B44362D9FFF6 | SHA256:71C2606BF144C5D697B85BB170D063892D484A87F9F7FB146356BDE827D4264E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
49
DNS requests
20
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5612 | RUXIMICS.exe | GET | 200 | 2.18.121.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.18.121.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.18.21.76:443 | https://community.chocolatey.org/install.ps1 | unknown | text | 35.3 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.138:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
— | — | GET | 302 | 104.18.20.76:443 | https://community.chocolatey.org/api/v2/package/chocolatey/2.4.3 | unknown | html | 171 b | whitelisted |
— | — | POST | 200 | 40.126.32.74:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.140:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.138:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5612 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.18.121.139:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.18.121.139:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
5612 | RUXIMICS.exe | 2.18.121.139:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
1268 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
community.chocolatey.org |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
packages.chocolatey.org |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2804 | powershell.exe | Potentially Bad Traffic | ET INFO Observed Chocolatey Windows Package Management Domain (chocolatey .org in TLS SNI) |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Potentially Bad Traffic | ET INFO Chocolatey Windows Package Management Installation File Retrieval |
— | — | Potentially Bad Traffic | ET HUNTING Generic Powershell DownloadString Command |
— | — | Potentially Bad Traffic | ET HUNTING Generic Powershell DownloadFile Command |
— | — | Potentially Bad Traffic | ET HUNTING PowerShell DownloadString Command Common In Powershell Stagers |
— | — | Potentially Bad Traffic | ET HUNTING PowerShell DownloadFile Command Common In Powershell Stagers |