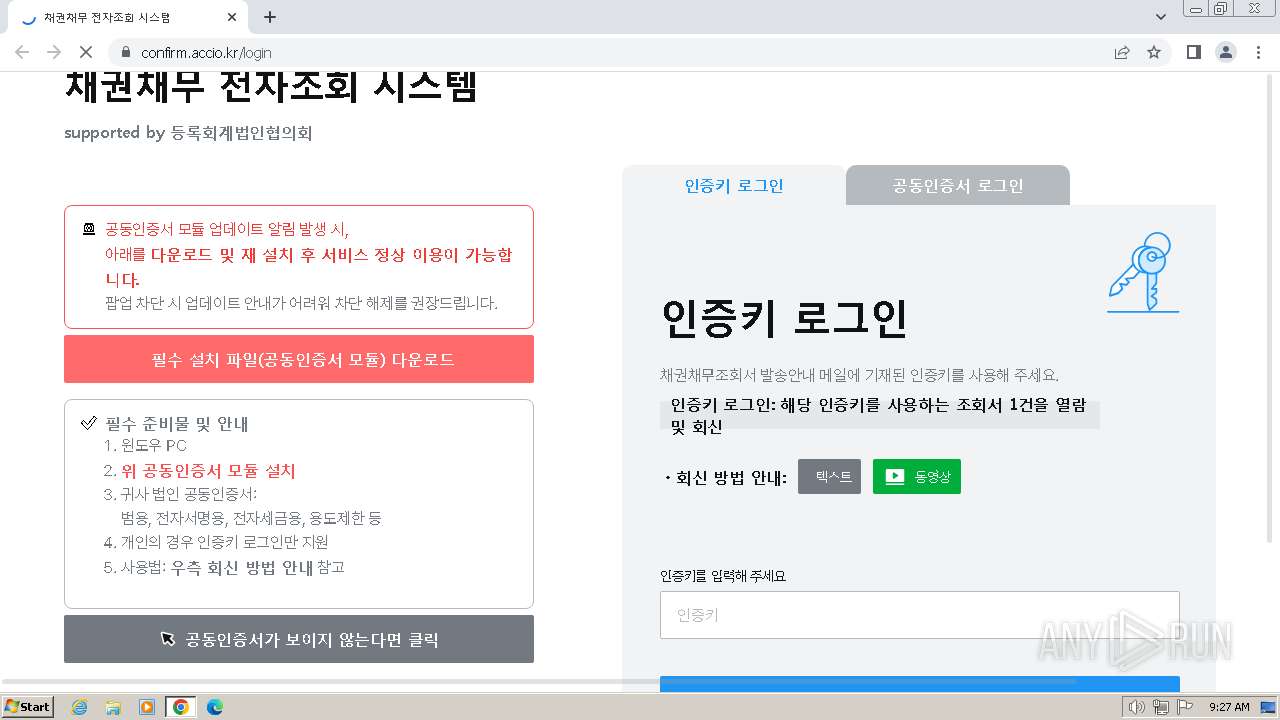
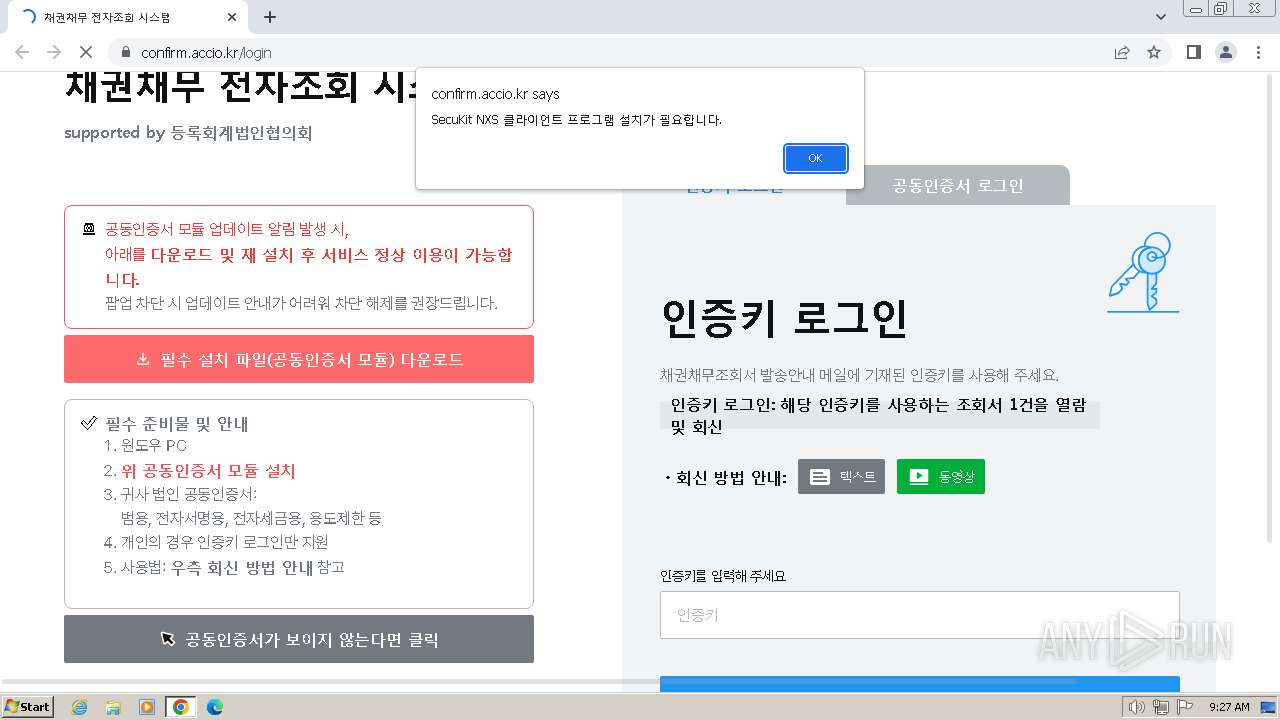
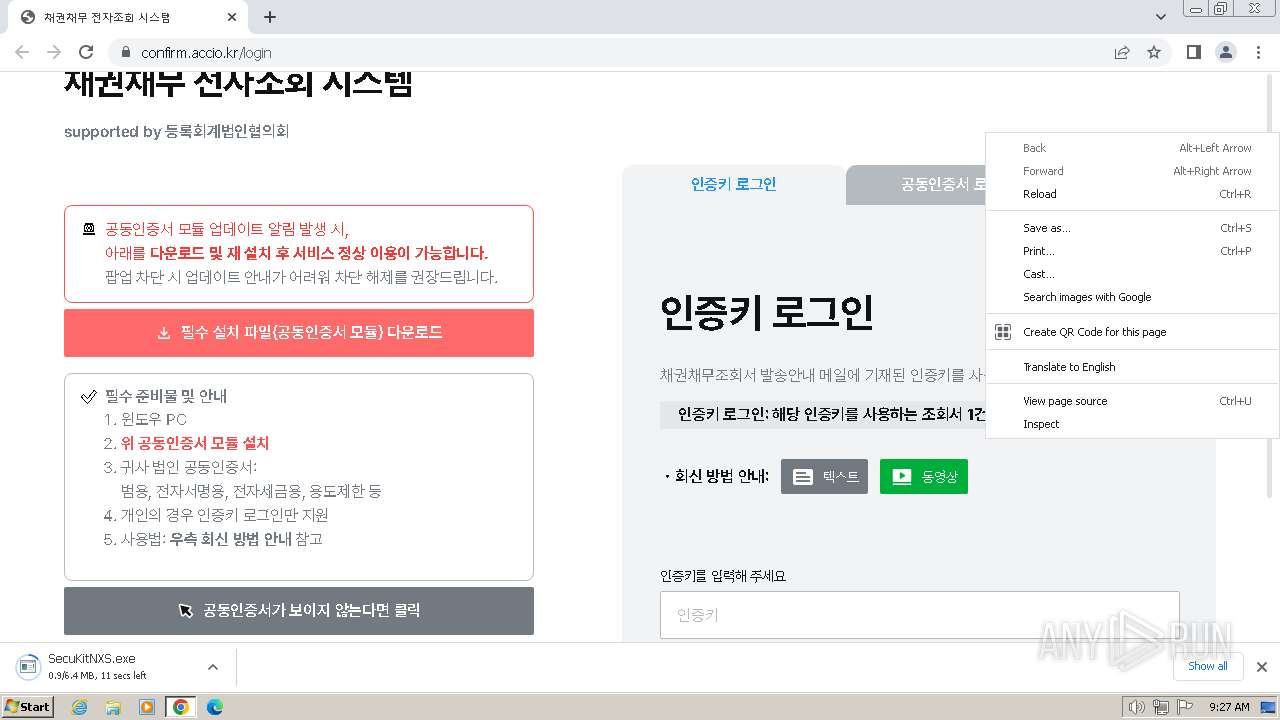
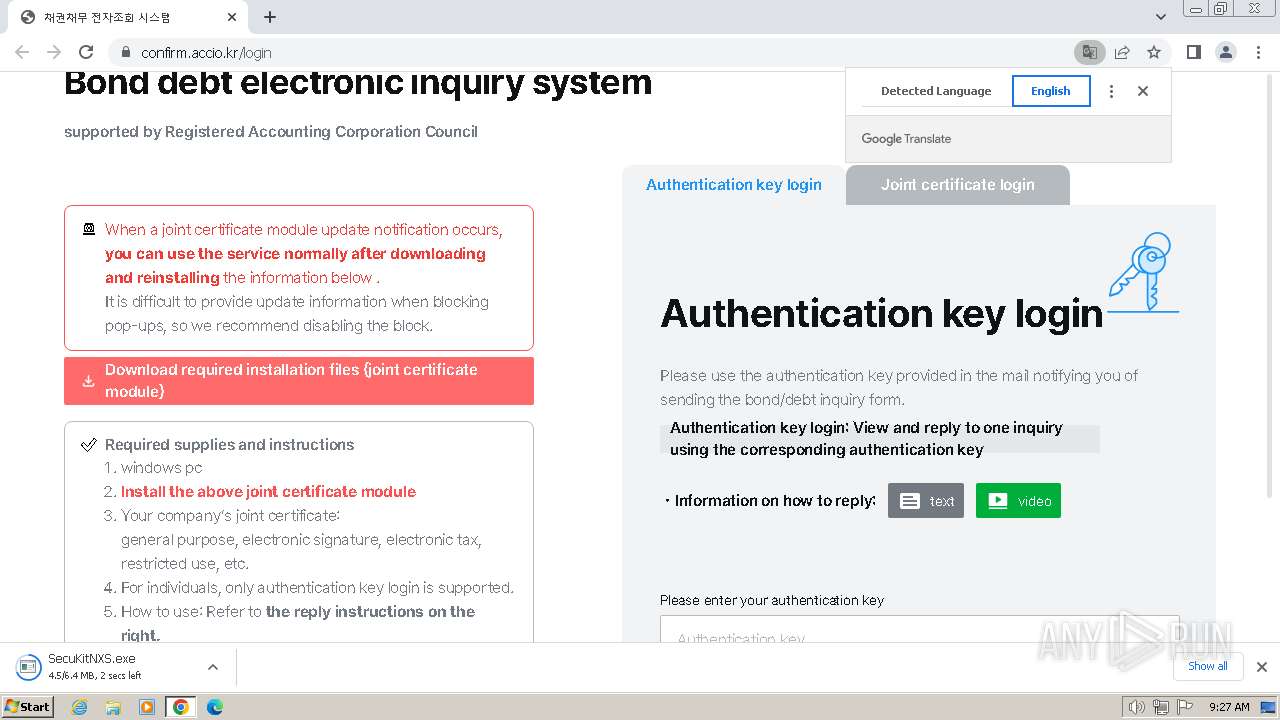
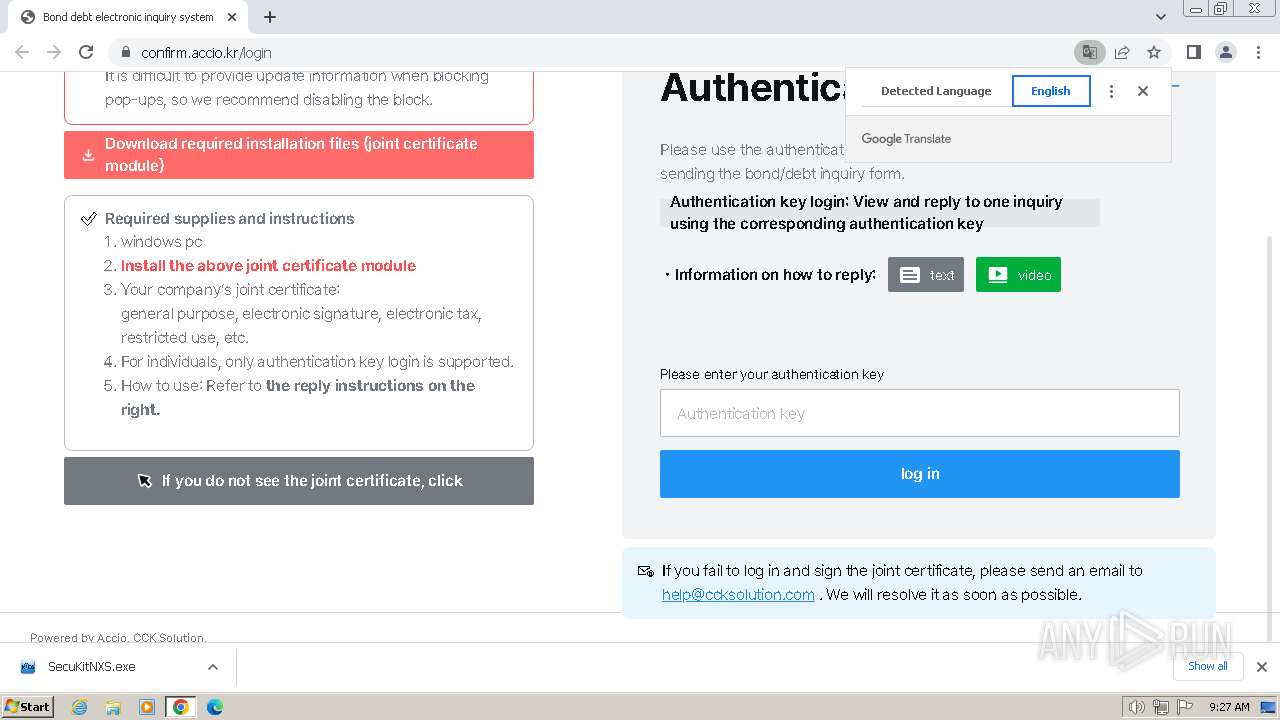
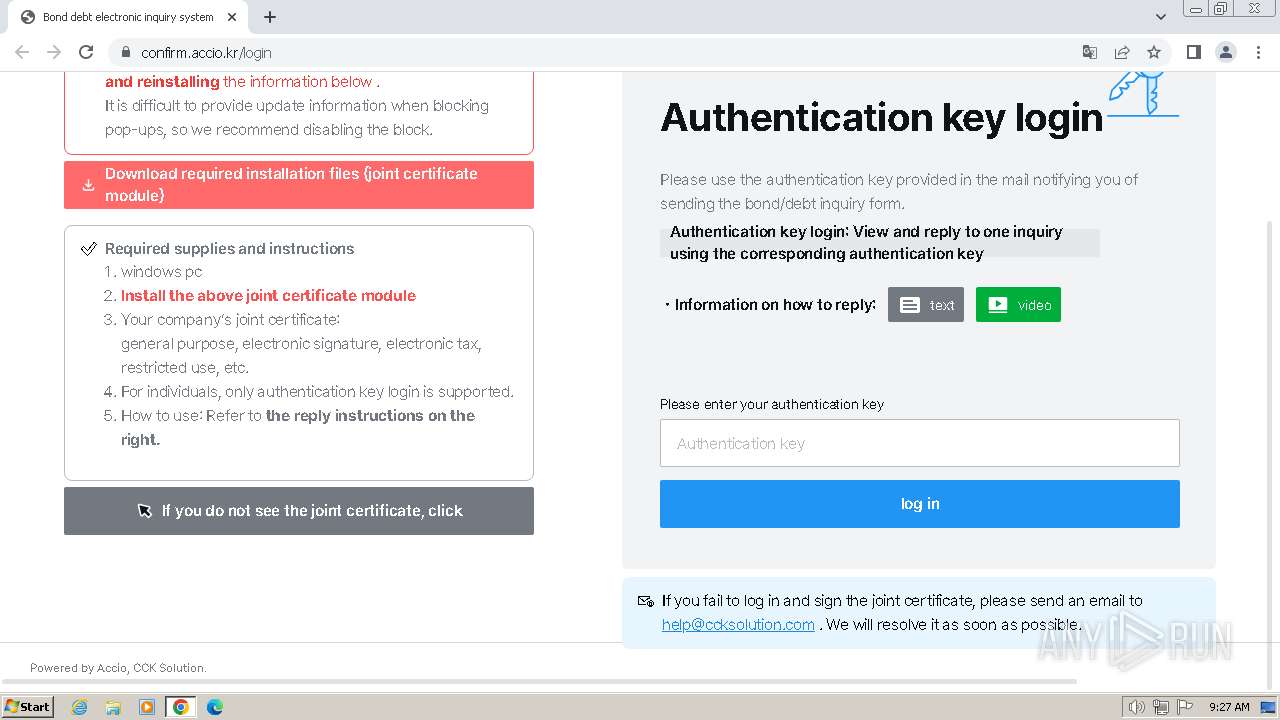
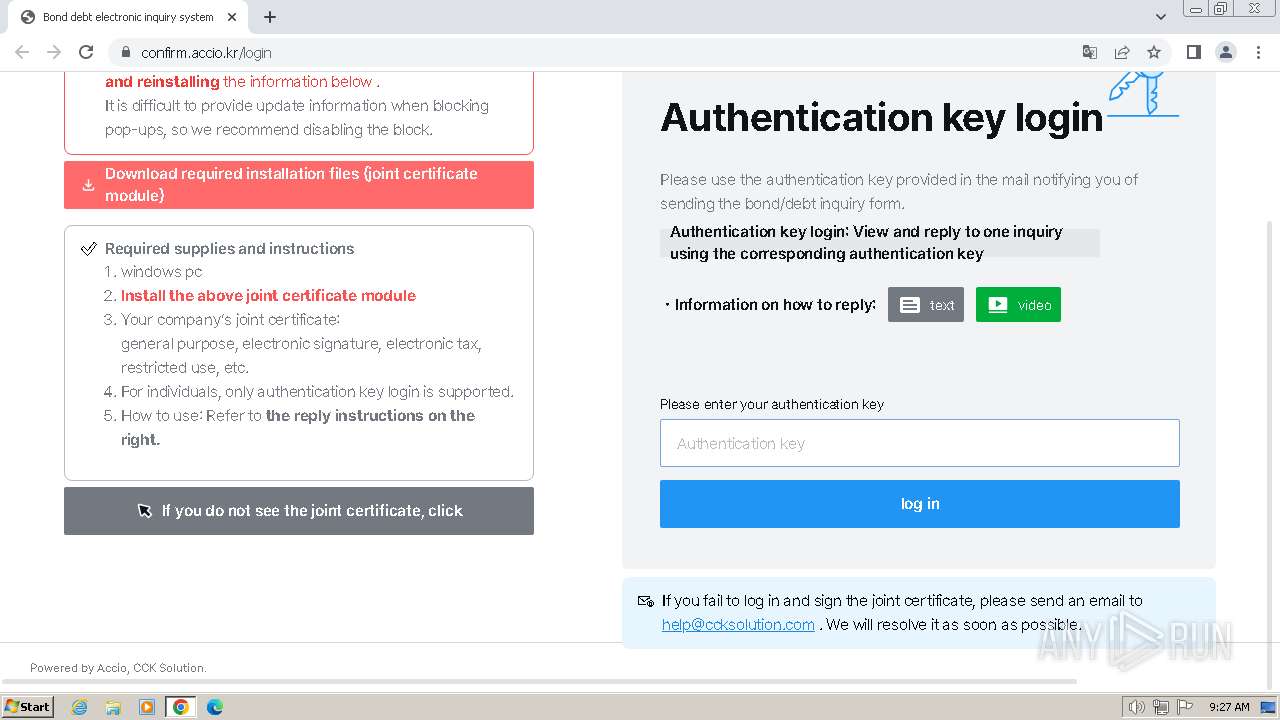
| URL: | https://confirm.accio.kr |
| Full analysis: | https://app.any.run/tasks/0a03395b-4bd3-491c-87e3-f310cb6c7517 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2024, 08:26:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 45779F8B794F81BC43399BA128E7FEEF |
| SHA1: | D189ABA8278AE878D0415E63E043BF60616A954F |
| SHA256: | 6C3B5136887A6071FFB7A600EEB0AF8151A73DB3F77AC54327C98D1D49989FA2 |
| SSDEEP: | 3:N8X8XjcX:2MzcX |
MALICIOUS
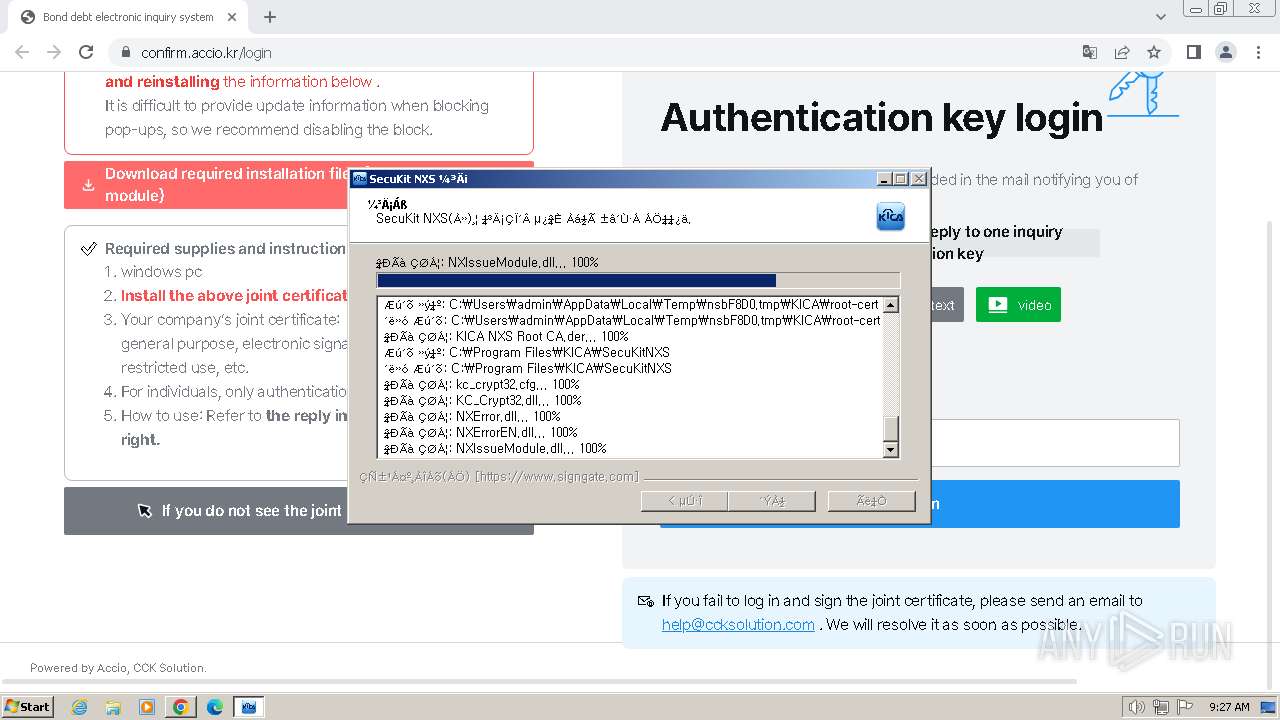
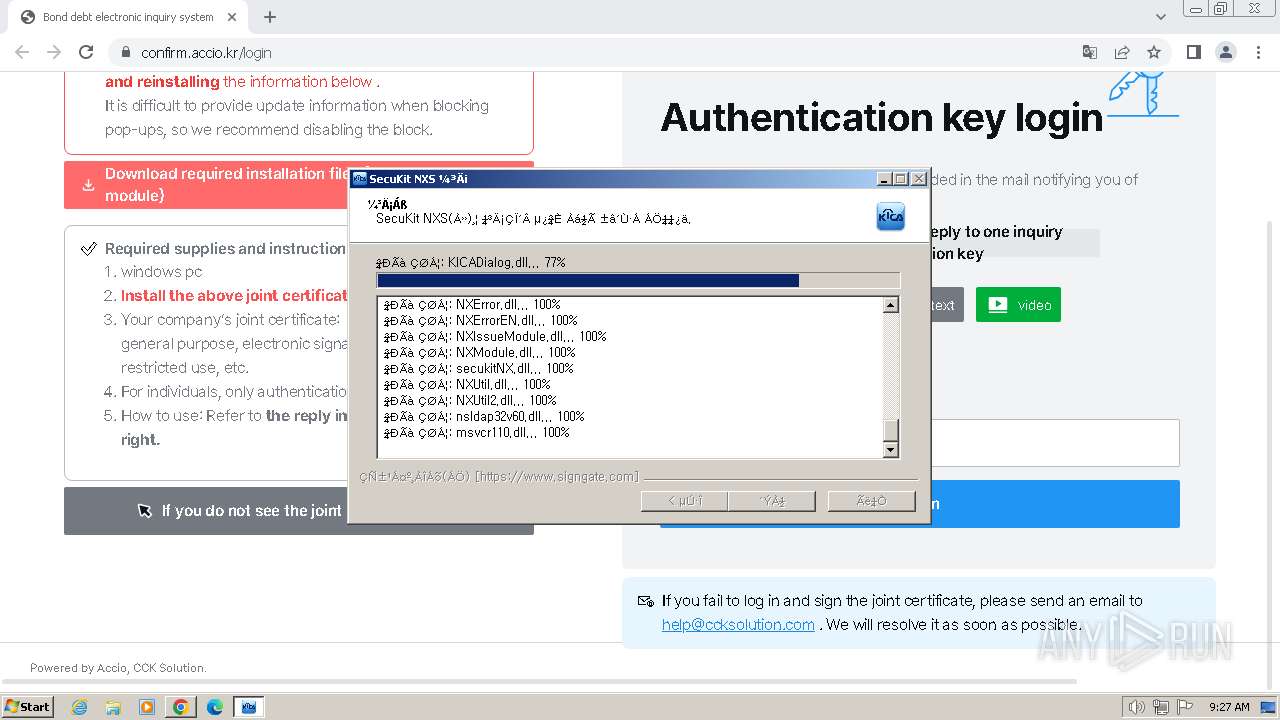
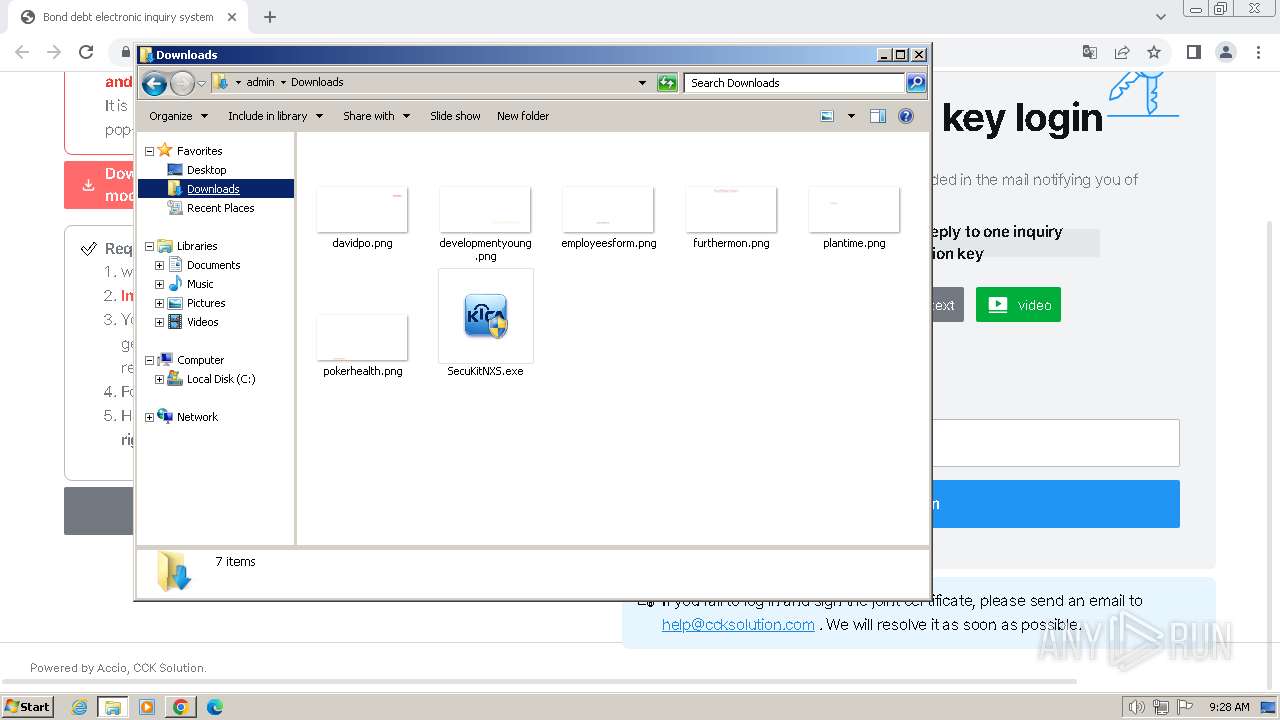
Drops the executable file immediately after the start
- SecuKitNXS.exe (PID: 1348)
Actions looks like stealing of personal data
- cmd.exe (PID: 3964)
- certutil.exe (PID: 3164)
- certutil.exe (PID: 3724)
- certutil.exe (PID: 2792)
- certutil.exe (PID: 4004)
Changes the autorun value in the registry
- SecuKitNXS.exe (PID: 1348)
SUSPICIOUS
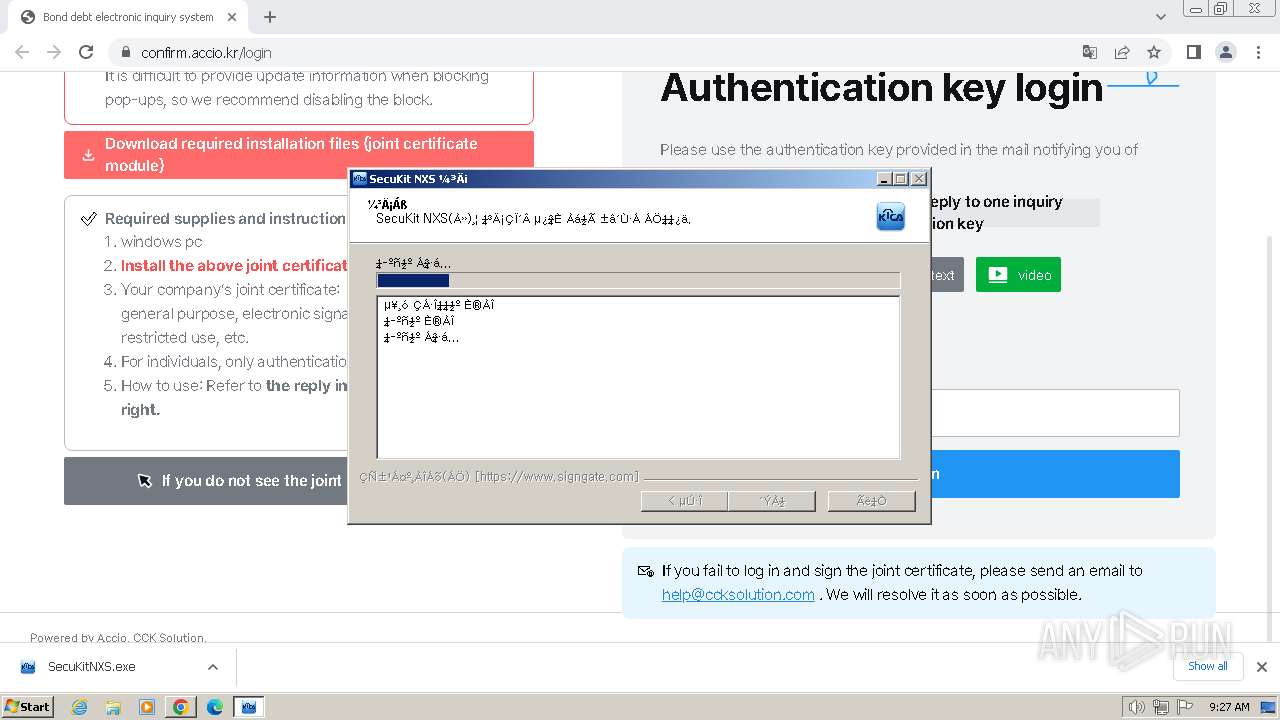
Malware-specific behavior (creating "System.dll" in Temp)
- SecuKitNXS.exe (PID: 1348)
Process drops legitimate windows executable
- SecuKitNXS.exe (PID: 1348)
The process creates files with name similar to system file names
- SecuKitNXS.exe (PID: 1348)
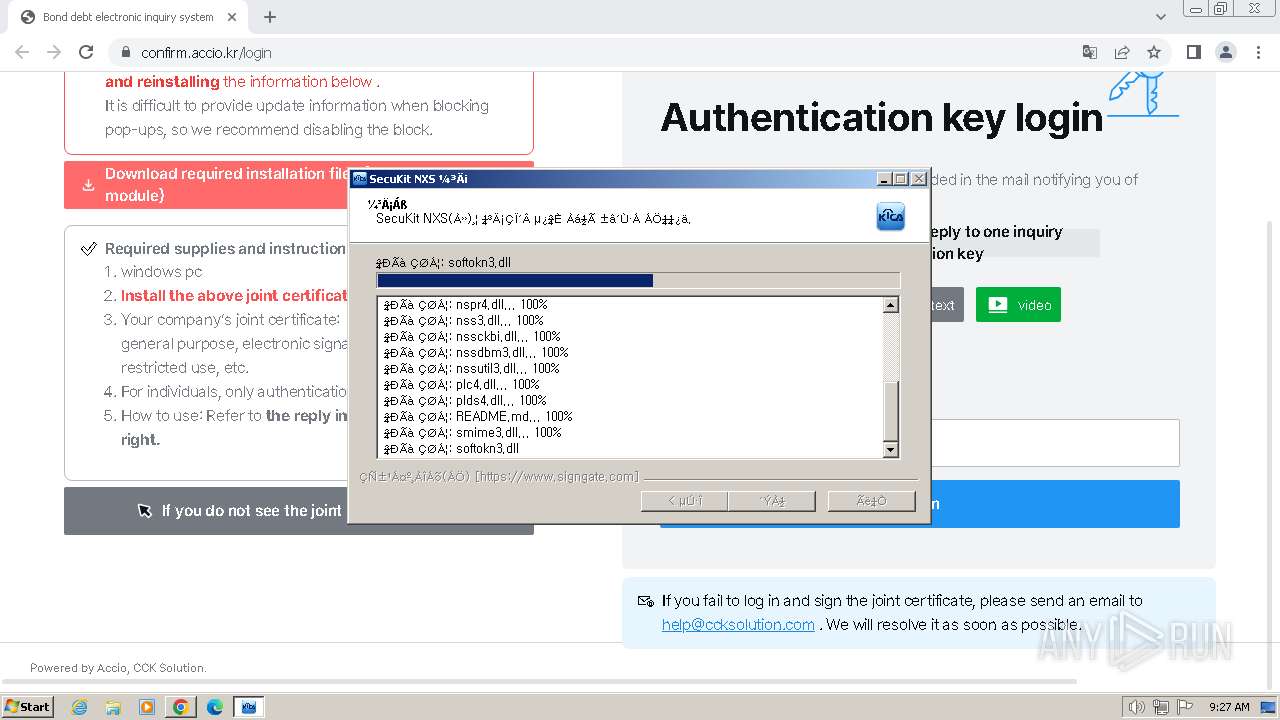
Executing commands from ".cmd" file
- nsEF9.tmp (PID: 2364)
The process drops C-runtime libraries
- SecuKitNXS.exe (PID: 1348)
Executable content was dropped or overwritten
- SecuKitNXS.exe (PID: 1348)
Starts CMD.EXE for commands execution
- nsEF9.tmp (PID: 2364)
The executable file from the user directory is run by the CMD process
- certutil.exe (PID: 2124)
- certutil.exe (PID: 3724)
- certutil.exe (PID: 2792)
- certutil.exe (PID: 4004)
- certutil.exe (PID: 3164)
- certutil.exe (PID: 2324)
Starts application with an unusual extension
- SecuKitNXS.exe (PID: 1348)
Creates a software uninstall entry
- SecuKitNXS.exe (PID: 1348)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3964)
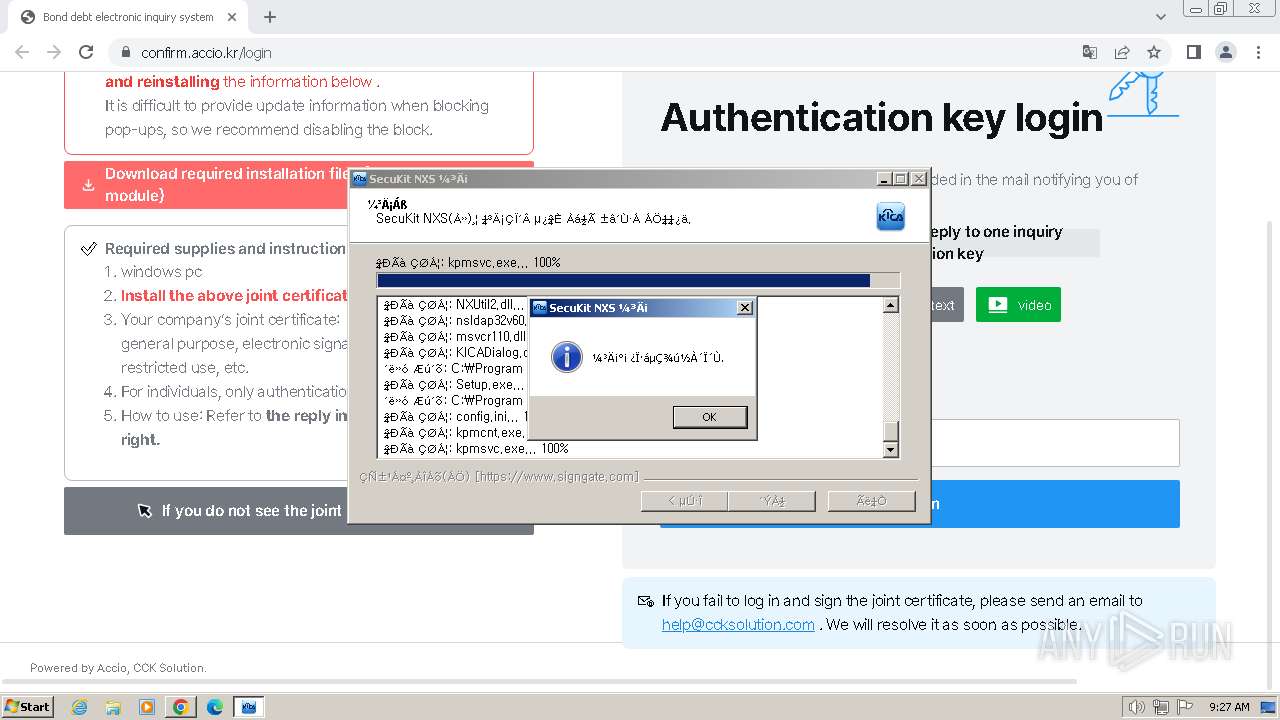
Executes as Windows Service
- kpmsvc.exe (PID: 2060)
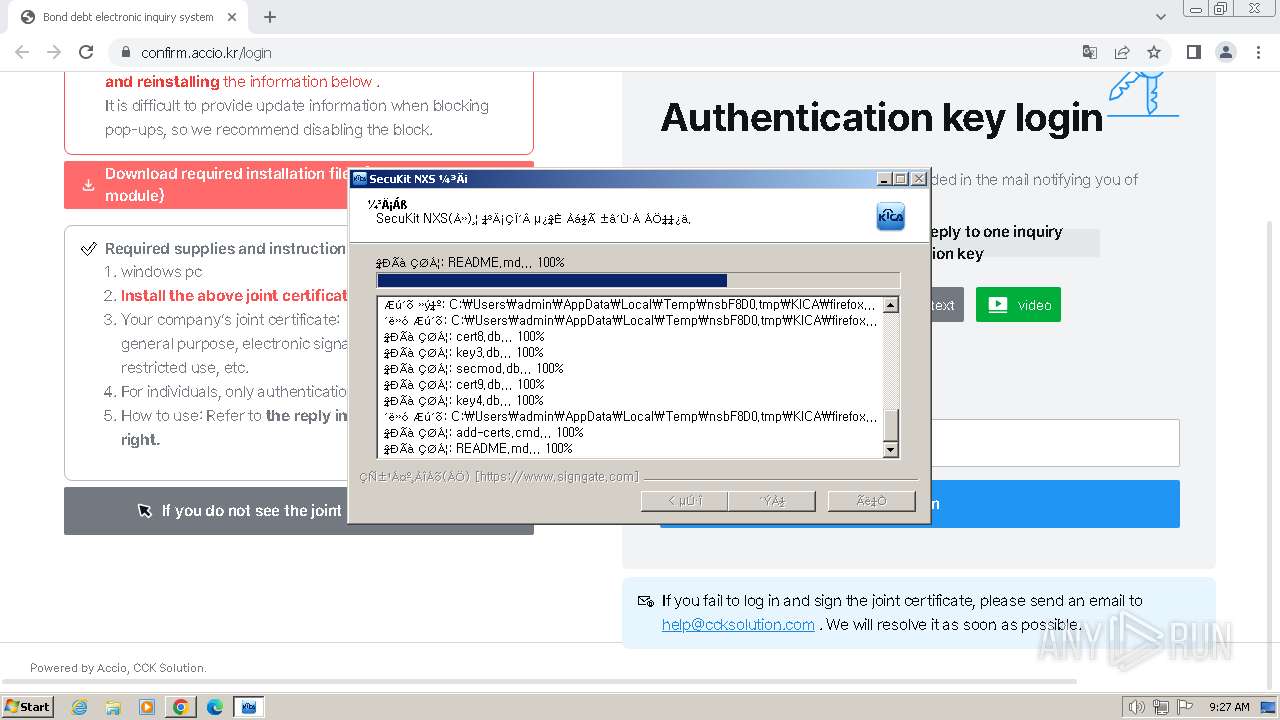
Adds/modifies Windows certificates
- SecuKitNXS.exe (PID: 1348)
INFO
Application launched itself
- chrome.exe (PID: 3768)
Reads the computer name
- SecuKitNXS.exe (PID: 1348)
- certutil.exe (PID: 2124)
- certutil.exe (PID: 3724)
- certutil.exe (PID: 2792)
- certutil.exe (PID: 3164)
- certutil.exe (PID: 2324)
- kpmsvc.exe (PID: 2060)
- kpmcnt.exe (PID: 1928)
- certutil.exe (PID: 4004)
Checks supported languages
- SecuKitNXS.exe (PID: 1348)
- nsEF9.tmp (PID: 2364)
- certutil.exe (PID: 2124)
- certutil.exe (PID: 3724)
- certutil.exe (PID: 2792)
- certutil.exe (PID: 3164)
- certutil.exe (PID: 4004)
- kpmsvc.exe (PID: 2060)
- certutil.exe (PID: 2324)
- kpmcnt.exe (PID: 1928)
- kpmcnt.exe (PID: 3620)
Create files in a temporary directory
- SecuKitNXS.exe (PID: 1348)
Drops the executable file immediately after the start
- chrome.exe (PID: 3768)
The process uses the downloaded file
- chrome.exe (PID: 2164)
- chrome.exe (PID: 3768)
Executable content was dropped or overwritten
- chrome.exe (PID: 3768)
Creates files in the program directory
- cmd.exe (PID: 3964)
- SecuKitNXS.exe (PID: 1348)
Creates files or folders in the user directory
- certutil.exe (PID: 2792)
- certutil.exe (PID: 4004)
Reads the machine GUID from the registry
- kpmcnt.exe (PID: 1928)
Manual execution by a user
- explorer.exe (PID: 2088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
30
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ba18b38,0x6ba18b48,0x6ba18b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
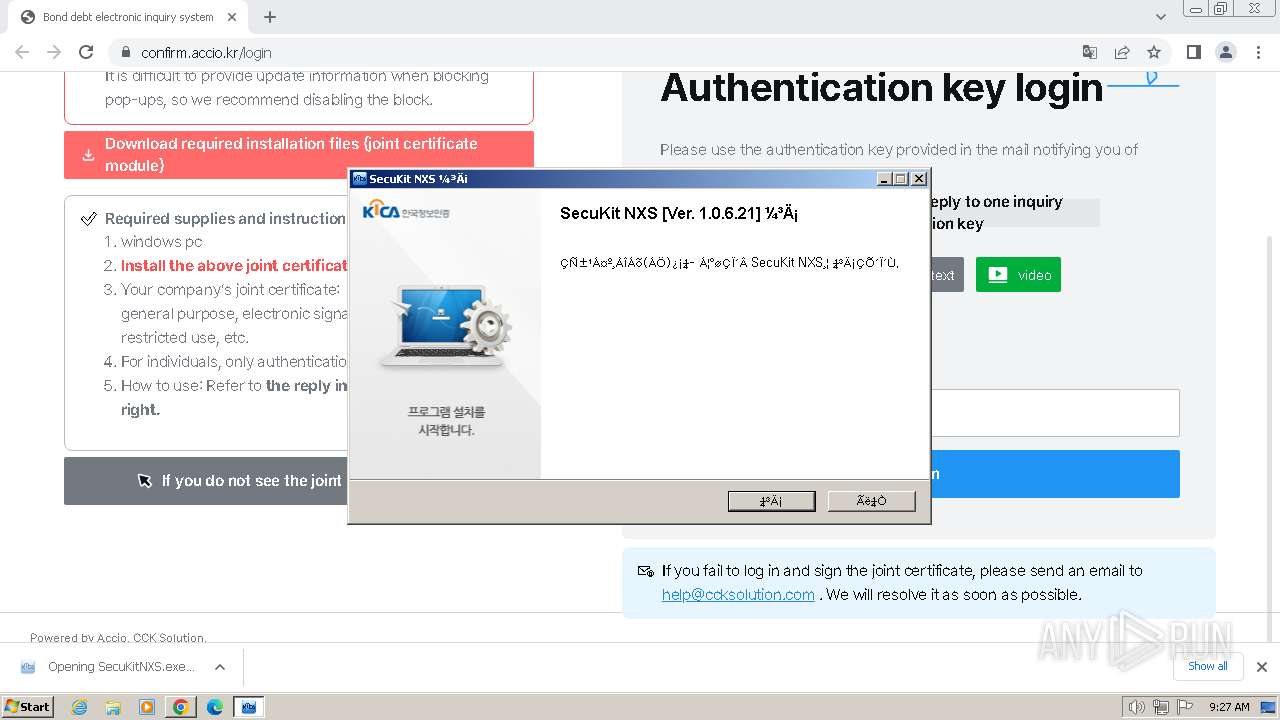
| 1348 | "C:\Users\admin\Downloads\SecuKitNXS.exe" | C:\Users\admin\Downloads\SecuKitNXS.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SecukitNX Setup Exit code: 0 Version: 1.0.6.21 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\KICA\Common\kpmsvc\kpmcnt.exe" | C:\Program Files\KICA\Common\kpmsvc\kpmcnt.exe | kpmsvc.exe | ||||||||||||
User: admin Company: KICA Inc. Integrity Level: HIGH Description: KICA Process Manager Service Version: 1.1.5.5 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3388 --field-trial-handle=1180,i,8075613277166158309,17835892975285682383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\KICA\Common\kpmsvc\kpmsvc.exe" | C:\Program Files\KICA\Common\kpmsvc\kpmsvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: KICA Inc. Integrity Level: SYSTEM Description: KICA Prosess Manager Service 1.1.5.0 Version: 1.1.5.2 Modules
| |||||||||||||||
| 2088 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3168 --field-trial-handle=1180,i,8075613277166158309,17835892975285682383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\Temp\nsbF8D0.tmp\KICA\firefox-add-certs\bin\certutil.exe" -A -n "AddedByUser RootCA" -i "C:\Users\admin\AppData\Local\Temp\nsbF8D0.tmp\KICA\firefox-add-certs\cacert\RootCA.pem" -t "cTC,cTC,cTC", -d "C:\Program Files\Mozilla Firefox\browser\defaults\Profile" | C:\Users\admin\AppData\Local\Temp\nsbF8D0.tmp\KICA\firefox-add-certs\bin\certutil.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3876 --field-trial-handle=1180,i,8075613277166158309,17835892975285682383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1092 --field-trial-handle=1180,i,8075613277166158309,17835892975285682383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
14 891
Read events
14 798
Write events
85
Delete events
8
Modification events
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
37
Suspicious files
38
Text files
53
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1be849.TMP | — | |
MD5:— | SHA256:— | |||
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1bea7c.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1be7dc.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1bf28a.TMP | — | |
MD5:— | SHA256:— | |||
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3768 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF1be8e5.TMP | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
26
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | binary | 5.88 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | binary | 9.99 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | binary | 21.3 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | binary | 33.8 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | binary | 180 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | binary | 678 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | binary | 1.09 Mb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | binary | 140 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | binary | 1.36 Mb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
3472 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3768 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3472 | chrome.exe | 15.165.26.173:443 | confirm.accio.kr | AMAZON-02 | KR | unknown |
3472 | chrome.exe | 142.250.181.228:443 | www.google.com | GOOGLE | US | whitelisted |
3472 | chrome.exe | 172.217.23.106:443 | www.googleapis.com | GOOGLE | US | whitelisted |
3472 | chrome.exe | 172.217.18.106:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
3472 | chrome.exe | 104.26.13.204:443 | api.iconify.design | CLOUDFLARENET | US | unknown |
3472 | chrome.exe | 142.250.184.202:443 | translate.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
confirm.accio.kr |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
api.iconify.design |
| unknown |
content-autofill.googleapis.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
translate.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
kpmcnt.exe | [kpmcnt] [1584] (TRAC) EventProc() --> Function Name : checkLicense
|
kpmcnt.exe | [kpmcnt] [ 764] (TRAC) EventProc() --> Function Name : setEnvironment
|