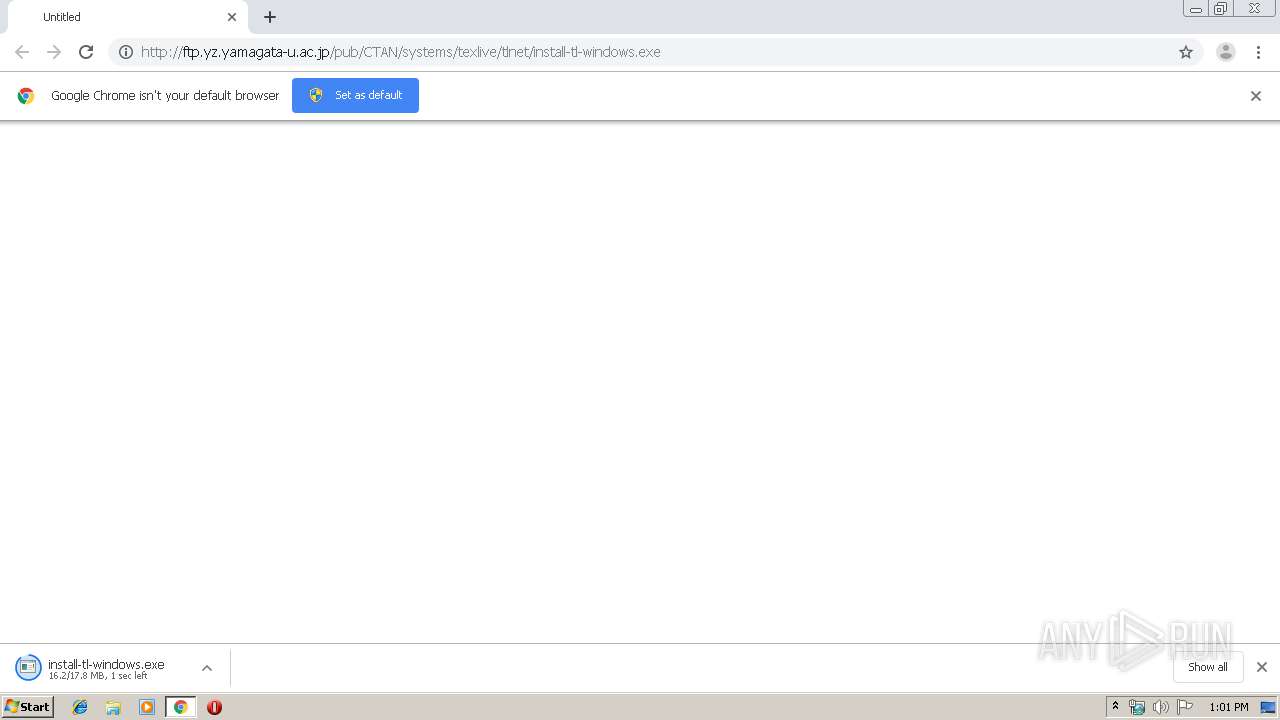
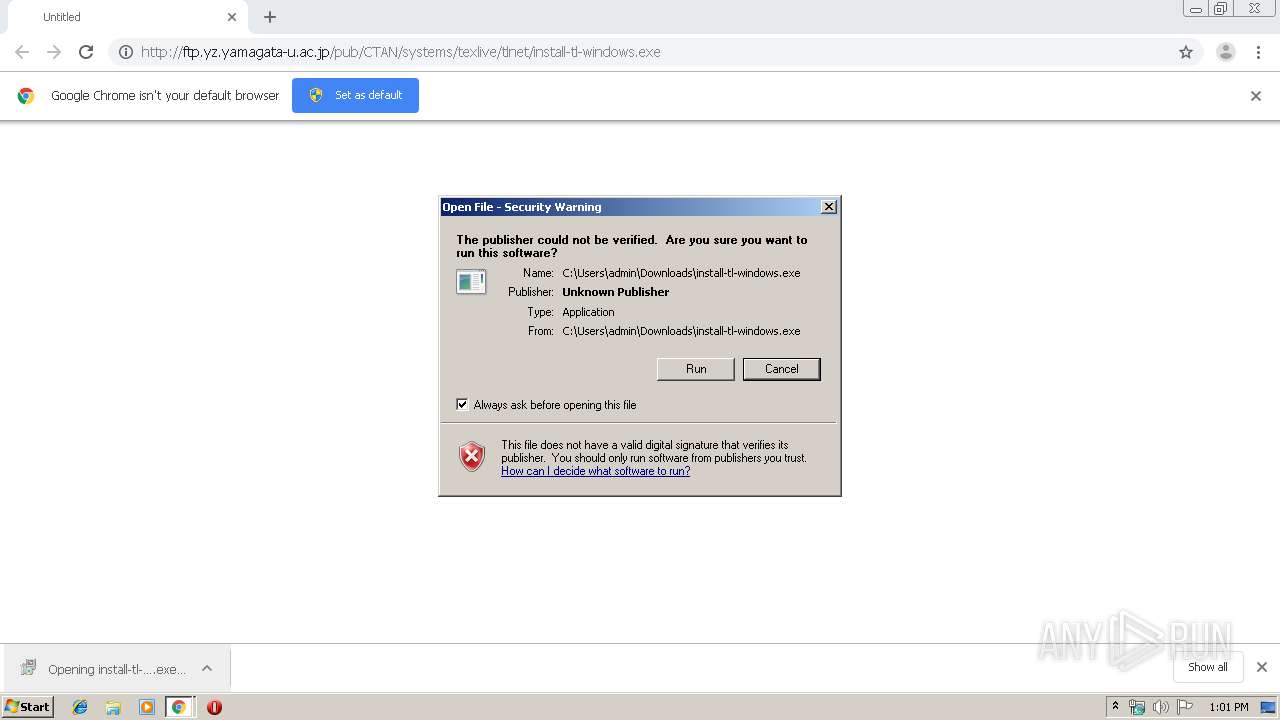
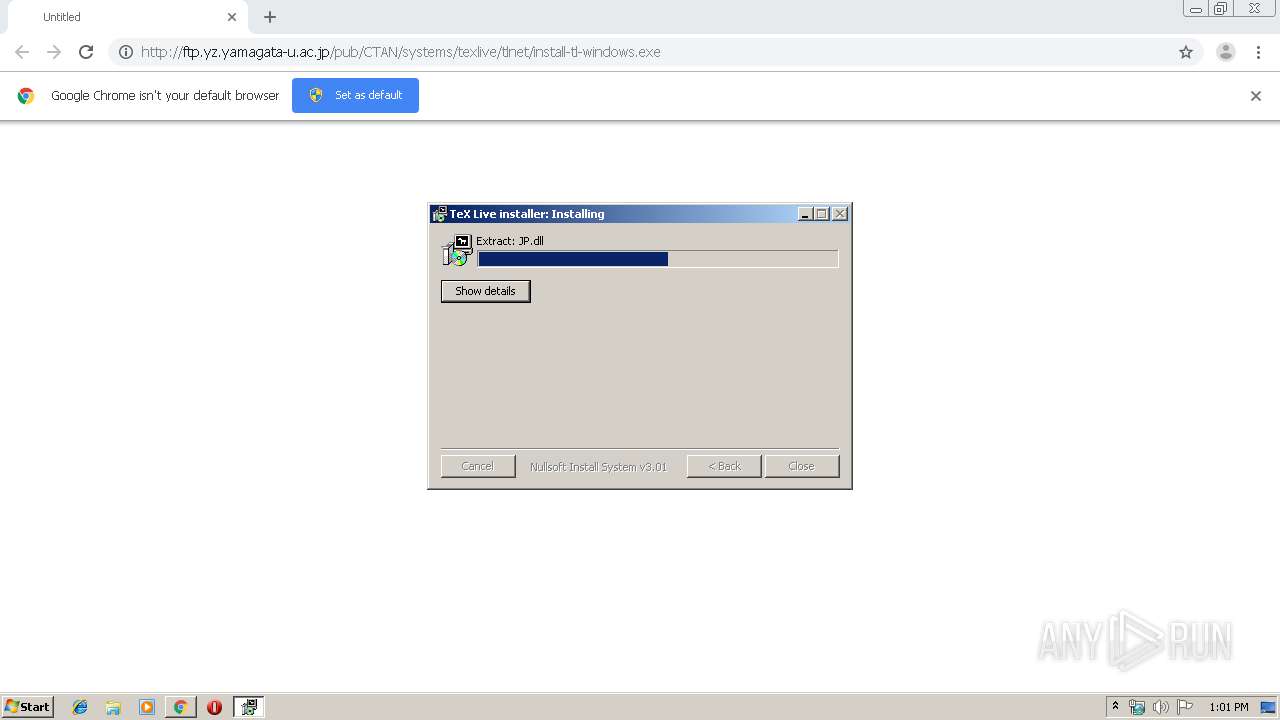
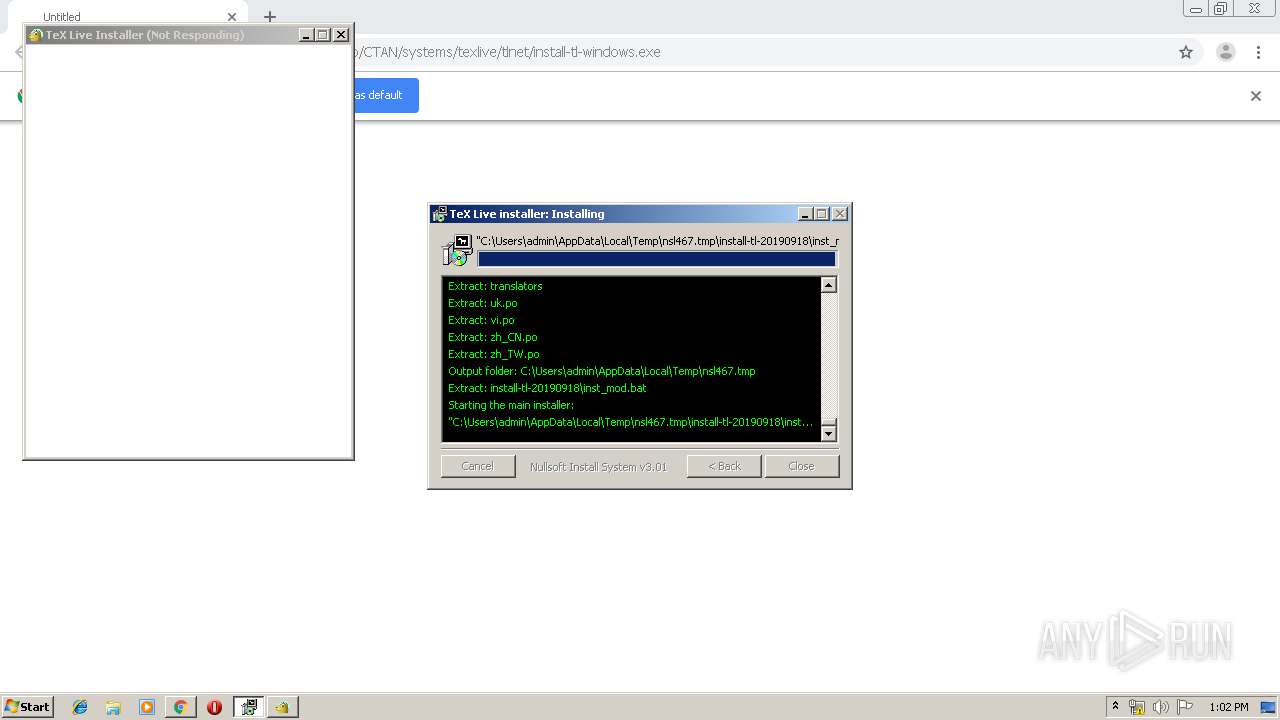
| URL: | http://ftp.yz.yamagata-u.ac.jp/pub/CTAN/systems/texlive/tlnet/install-tl-windows.exe |
| Full analysis: | https://app.any.run/tasks/06255610-02bf-4dbc-b516-862dd342a9ff |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 12:00:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F8B1C6A6E9CBE76A156219C7E0F83EB0 |
| SHA1: | 671216CE0D944DC514BFEB057122C647219F4424 |
| SHA256: | 6C32F1B74911E6CA257C06260554EB7447E42D9FFFF93133871B4E9542AC8B79 |
| SSDEEP: | 3:N1KYnECEEIm/qGkrKW/o00KDgGRGSkrA:CYnnEET/qGkK0zkGRqrA |
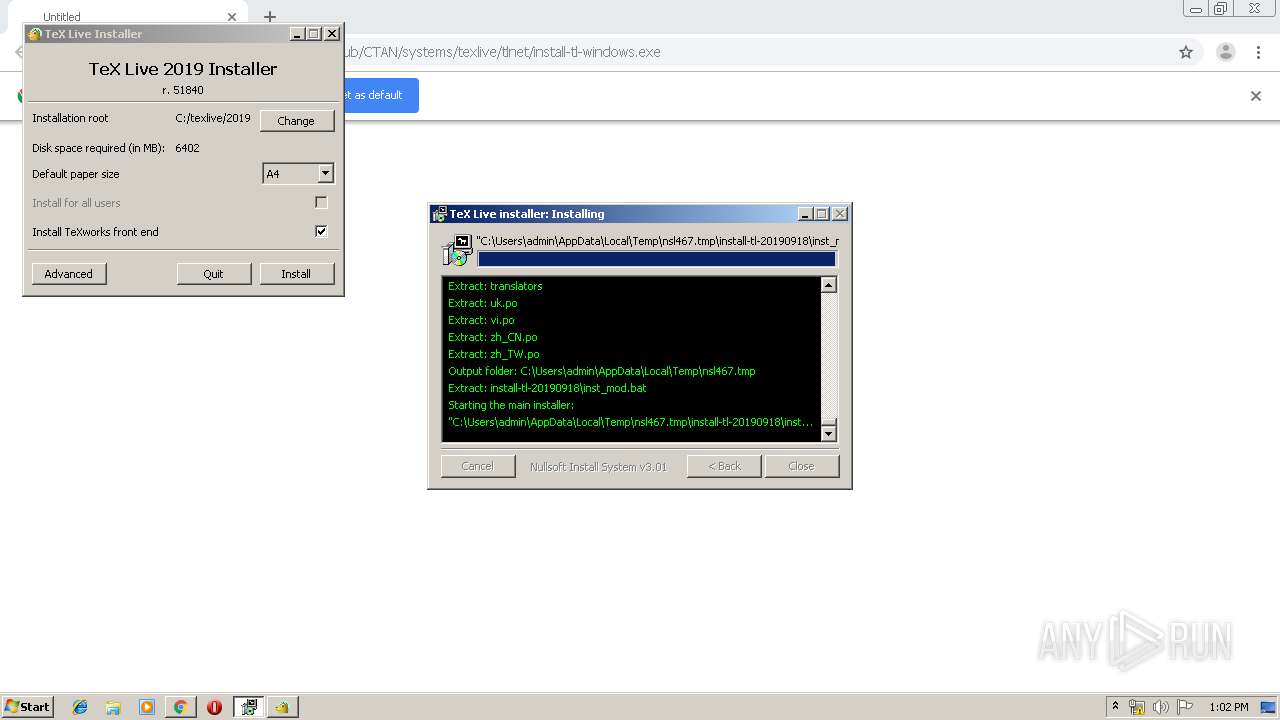
MALICIOUS
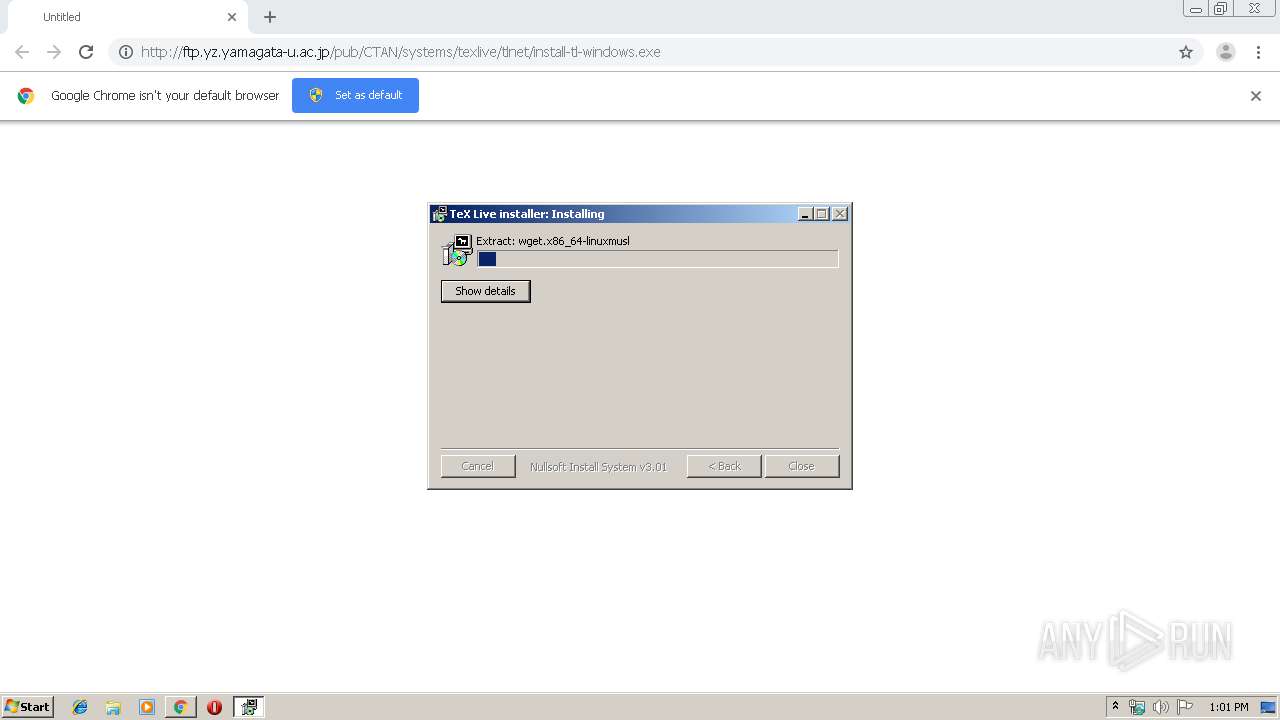
Application was dropped or rewritten from another process
- install-tl-windows.exe (PID: 1856)
- perl.exe (PID: 2528)
- tar.exe (PID: 1512)
- wget.exe (PID: 3652)
- xz.exe (PID: 3192)
- ns5D75.tmp (PID: 2112)
- tclkit.exe (PID: 3712)
- wget.exe (PID: 2544)
- xz.exe (PID: 2068)
- wget.exe (PID: 3956)
Loads dropped or rewritten executable
- install-tl-windows.exe (PID: 1856)
- perl.exe (PID: 2528)
SUSPICIOUS
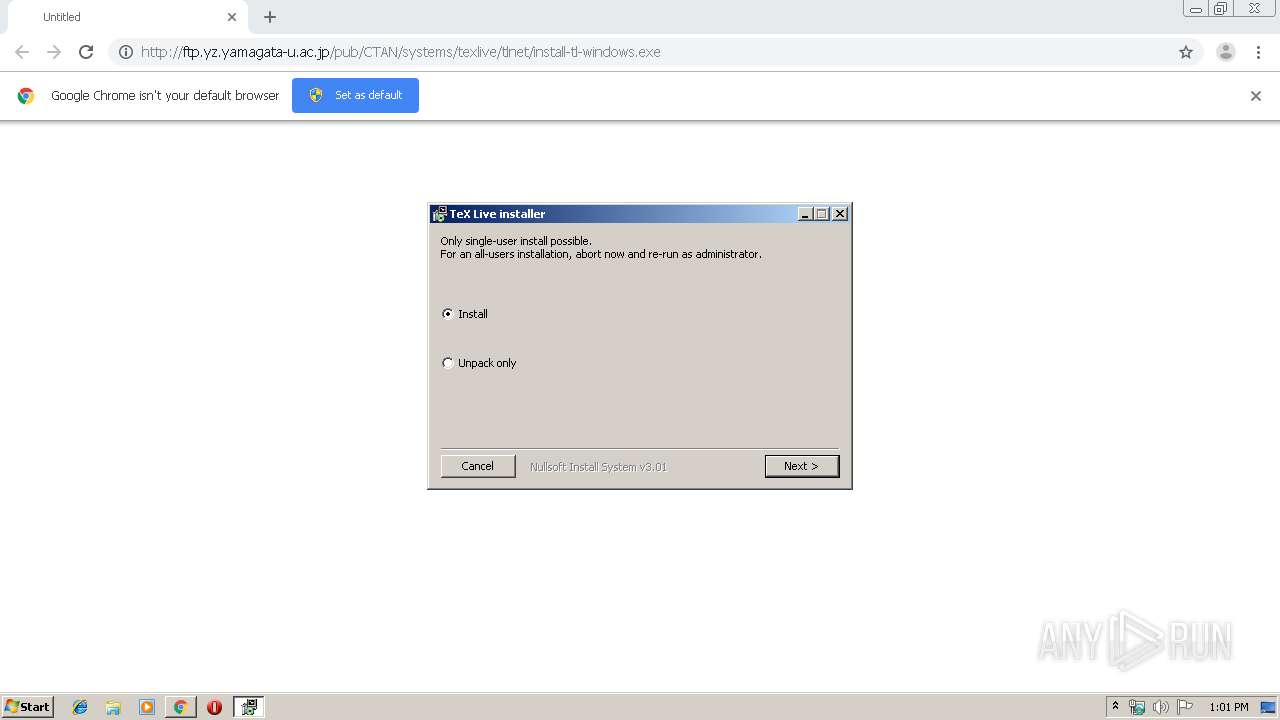
Starts application with an unusual extension
- install-tl-windows.exe (PID: 1856)
Executable content was dropped or overwritten
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2792)
- install-tl-windows.exe (PID: 1856)
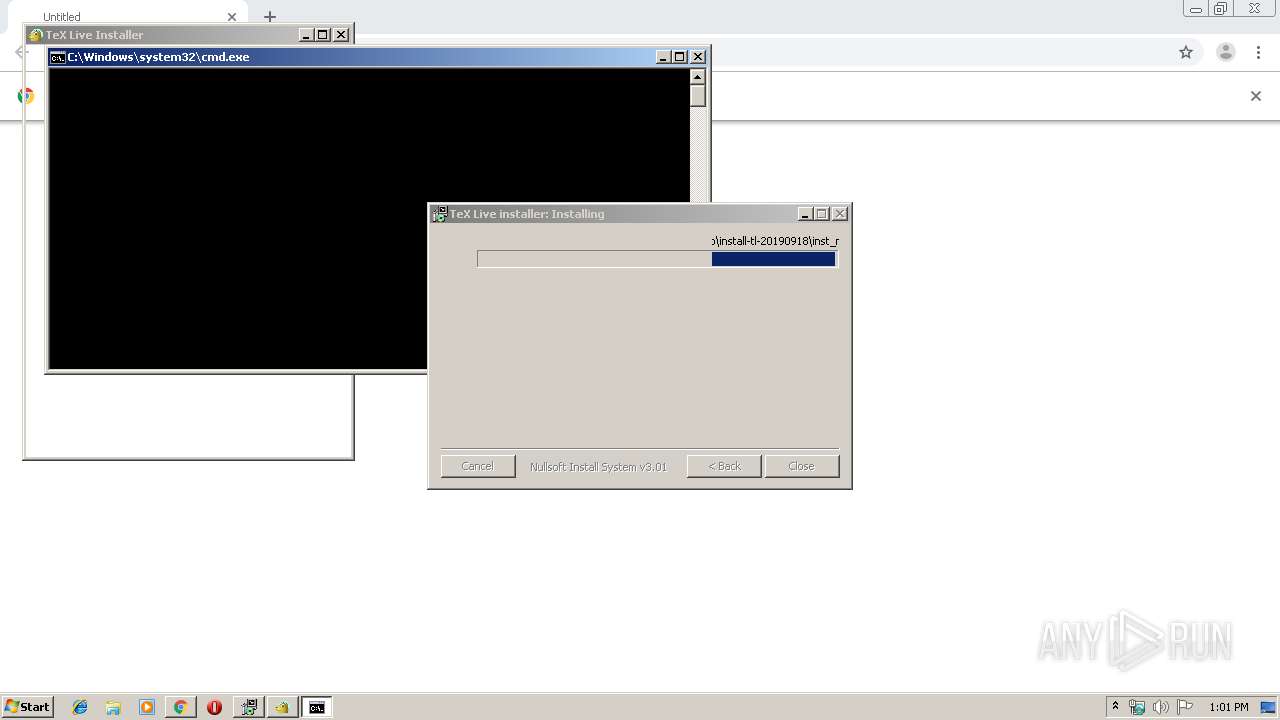
Starts CMD.EXE for commands execution
- ns5D75.tmp (PID: 2112)
- cmd.exe (PID: 2900)
- perl.exe (PID: 2528)
INFO
Reads the hosts file
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2792)
Creates files in the user directory
- chrome.exe (PID: 2792)
Reads Internet Cache Settings
- chrome.exe (PID: 2792)
Dropped object may contain Bitcoin addresses
- install-tl-windows.exe (PID: 1856)
Application launched itself
- chrome.exe (PID: 2792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
35
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,5678156902663964700,1986047999899398892,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18364631940238918941 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1512 | C:\Users\admin\AppData\Local\Temp\nsl467.tmp\install-tl-20190918\tlpkg\installer\tar.exe --version | C:\Users\admin\AppData\Local\Temp\nsl467.tmp\install-tl-20190918\tlpkg\installer\tar.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1856 | "C:\Users\admin\Downloads\install-tl-windows.exe" | C:\Users\admin\Downloads\install-tl-windows.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2068 | C:\Users\admin\AppData\Local\Temp\nsl467.tmp\install-tl-20190918\tlpkg\installer\xz\xz.exe -dcf | C:\Users\admin\AppData\Local\Temp\nsl467.tmp\install-tl-20190918\tlpkg\installer\xz\xz.exe | — | cmd.exe | |||||||||||
User: admin Company: The Tukaani Project <https://tukaani.org/> Integrity Level: MEDIUM Description: xz data compression tool for .xz and .lzma files Exit code: 0 Version: 5.2.4 Modules
| |||||||||||||||
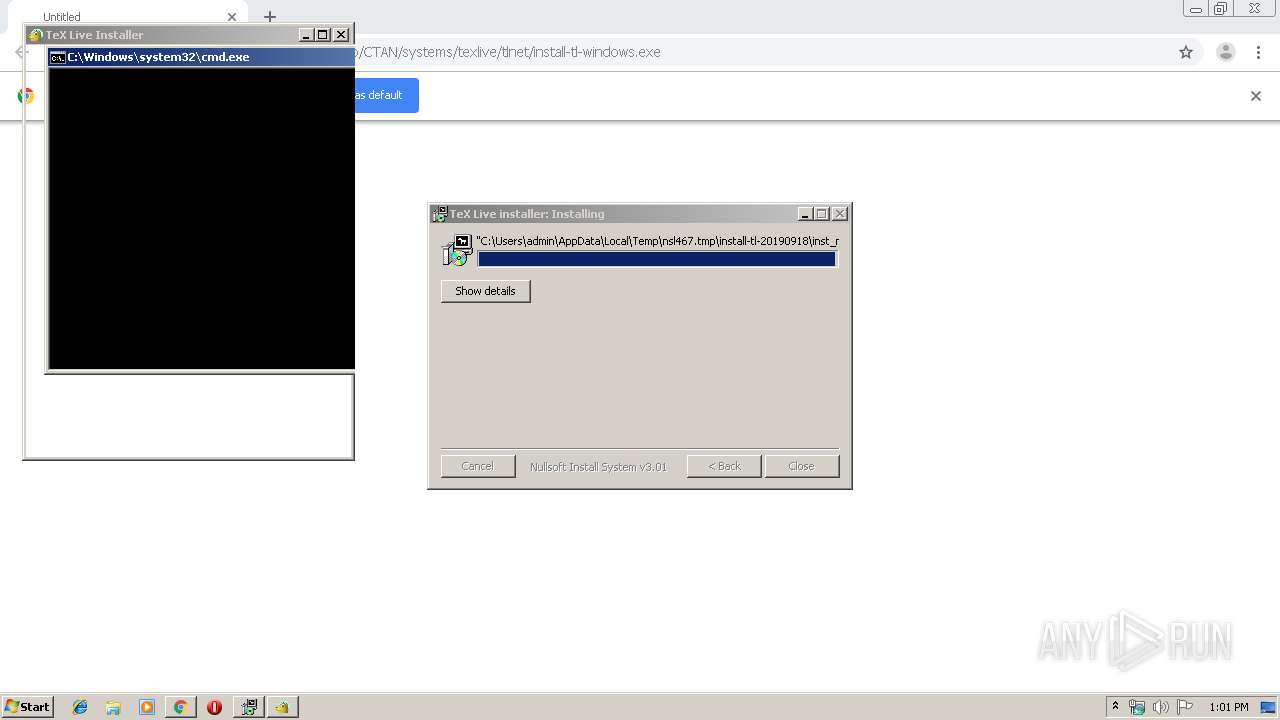
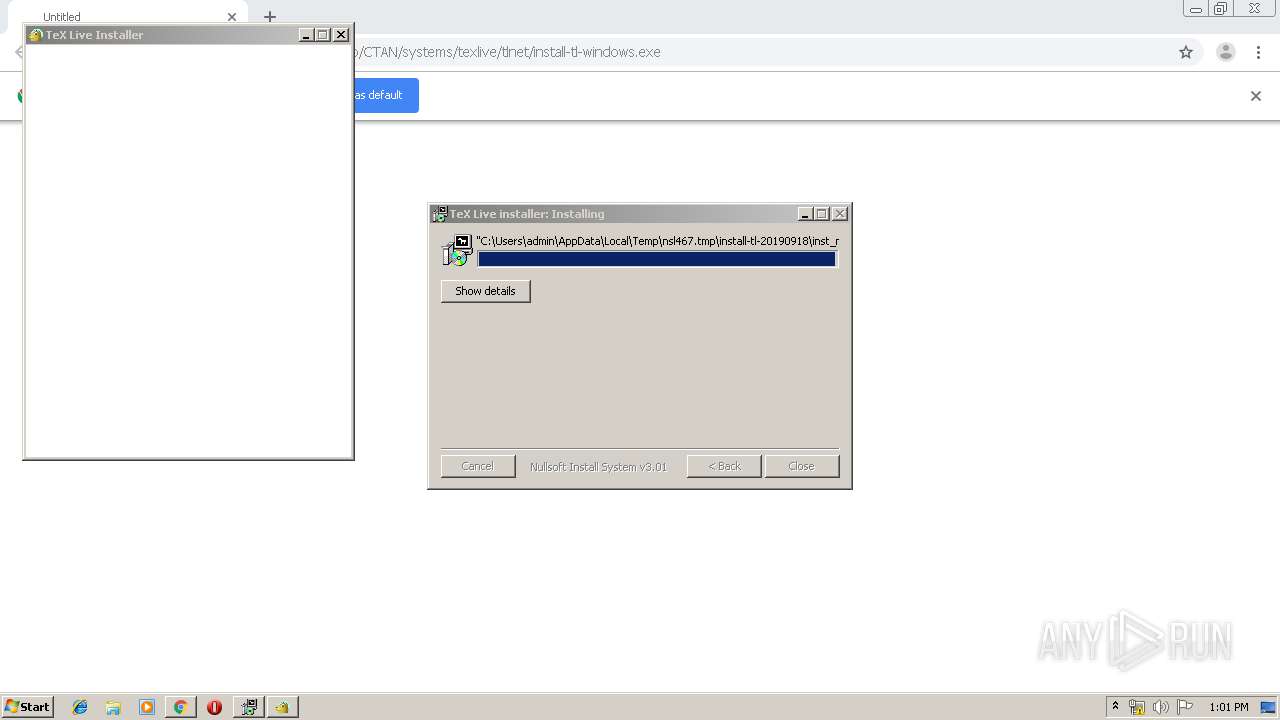
| 2112 | "C:\Users\admin\AppData\Local\Temp\nsl467.tmp\ns5D75.tmp" "C:\Users\admin\AppData\Local\Temp\nsl467.tmp\install-tl-20190918\inst_mod.bat" | C:\Users\admin\AppData\Local\Temp\nsl467.tmp\ns5D75.tmp | — | install-tl-windows.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2200 | cmd.exe /x/d/c ver | C:\Windows\system32\cmd.exe | — | perl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,5678156902663964700,1986047999899398892,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14266949305079669338 --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2512 | cmd.exe /x/d/c "C:\Users\admin\AppData\Local\Temp\nsl467.tmp\install-tl-20190918\tlpkg\installer\xz\xz.exe --version >nul 2>&1" | C:\Windows\system32\cmd.exe | — | perl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,5678156902663964700,1986047999899398892,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12336067688843740366 --mojo-platform-channel-handle=2508 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2528 | C:\Users\admin\AppData\Local\Temp\nsl467.tmp\install-tl-20190918\tlpkg\tlperl\bin\perl.exe C:/Users/admin/AppData/Local/Temp/nsl467.tmp/install-tl-20190918/install-tl -from_ext_gui | C:\Users\admin\AppData\Local\Temp\nsl467.tmp\install-tl-20190918\tlpkg\tlperl\bin\perl.exe | — | tclkit.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 347
Read events
1 296
Write events
48
Delete events
3
Modification events
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2792-13213368054800125 |
Value: 259 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
85
Suspicious files
28
Text files
1 736
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fd2962d3-5e19-4a0d-b15e-d4afb559dafe.tmp | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF168bf9.TMP | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
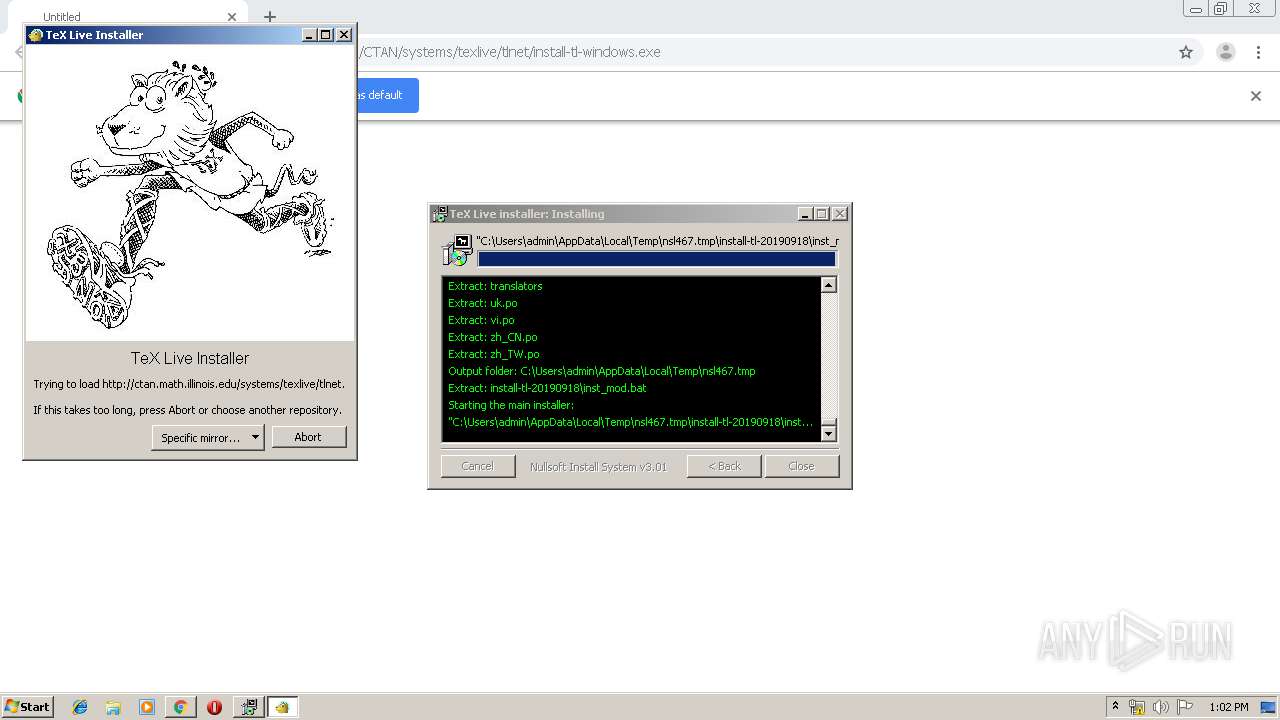
2544 | wget.exe | GET | 302 | 5.35.249.60:80 | http://mirror.ctan.org/ | DE | html | 295 b | whitelisted |
2544 | wget.exe | GET | — | 192.17.3.223:80 | http://ctan.math.illinois.edu/ | US | — | — | unknown |
2544 | wget.exe | GET | 200 | 192.17.3.223:80 | http://ctan.math.illinois.edu/ | US | html | 8.97 Kb | unknown |
3956 | wget.exe | GET | 200 | 192.17.3.223:80 | http://ctan.math.illinois.edu/systems/texlive/tlnet/tlpkg/texlive.tlpdb.xz | US | xz | 2.02 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2332 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2332 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2332 | chrome.exe | 133.24.248.17:80 | ftp.yz.yamagata-u.ac.jp | Yamagata University | JP | suspicious |
2332 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2332 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2332 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2332 | chrome.exe | 133.24.248.19:80 | ftp.yz.yamagata-u.ac.jp | Yamagata University | JP | unknown |
2544 | wget.exe | 5.35.249.60:80 | mirror.ctan.org | Host Europe GmbH | DE | unknown |
2544 | wget.exe | 192.17.3.223:80 | ctan.math.illinois.edu | University of Illinois | US | unknown |
2332 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ftp.yz.yamagata-u.ac.jp |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
mirror.ctan.org |
| unknown |
ctan.math.illinois.edu |
| unknown |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2332 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |