| File name: | download.exe |
| Full analysis: | https://app.any.run/tasks/65f1c451-b5b1-466c-bc90-de0ead30d281 |
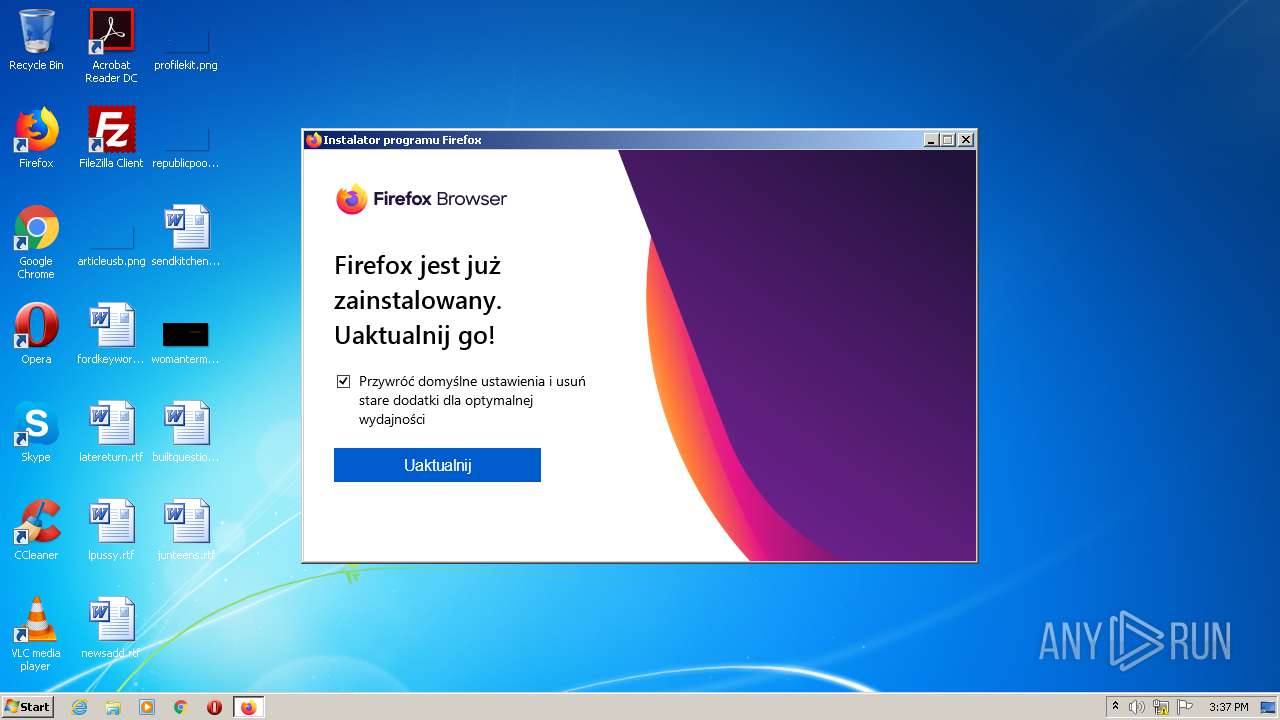
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 14:35:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | BF46229C3085549297091E76B3654D45 |
| SHA1: | 8390A82DA612525E8061FBF76B76DF7218E5CF21 |
| SHA256: | 6C26BBA25CE4F0B40D938653B04AB4C24583BF1B5135878132D9F708730A22B8 |
| SSDEEP: | 6144:XaVWdyzOxeA1DfdwX3MmIOxFsO2XrFapn3mQzIldCnnPwNAdZShEyA:XMROxdDfOnMmXx2O2bFa0tdCnPwQZShI |
MALICIOUS
Loads dropped or rewritten executable
- setup-stub.exe (PID: 2016)
- setup-stub.exe (PID: 3332)
Application was dropped or rewritten from another process
- setup-stub.exe (PID: 2016)
- setup-stub.exe (PID: 3332)
Actions looks like stealing of personal data
- setup-stub.exe (PID: 2016)
Changes settings of System certificates
- setup-stub.exe (PID: 2016)
SUSPICIOUS
Executable content was dropped or overwritten
- download.exe (PID: 1556)
- setup-stub.exe (PID: 3332)
- setup-stub.exe (PID: 2016)
Application launched itself
- setup-stub.exe (PID: 3332)
Reads Internet Cache Settings
- setup-stub.exe (PID: 2016)
Adds / modifies Windows certificates
- setup-stub.exe (PID: 2016)
Creates files in the program directory
- setup-stub.exe (PID: 2016)
Reads internet explorer settings
- setup-stub.exe (PID: 2016)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:31 00:18:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 69632 |
| InitializedDataSize: | 65536 |
| UninitializedDataSize: | 147456 |
| EntryPoint: | 0x34fa0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 18.5.0.0 |
| ProductVersionNumber: | 18.5.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Mozilla |
| FileDescription: | Firefox |
| FileVersion: | 18.05 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Mozilla |
| OriginalFileName: | 7zS.sfx.exe |
| ProductName: | Firefox |
| ProductVersion: | 18.05 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Aug-2018 22:18:33 |
| Detected languages: |
|
| CompanyName: | Mozilla |
| FileDescription: | Firefox |
| FileVersion: | 18.05 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Mozilla |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | Firefox |
| ProductVersion: | 18.05 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 30-Aug-2018 22:18:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00024000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00025000 | 0x00011000 | 0x00010200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.87799 |
.rsrc | 0x00036000 | 0x00010000 | 0x0000FC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.52725 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.38843 | 1365 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.52861 | 5160 | UNKNOWN | English - United States | RT_ICON |
3 | 5.45625 | 11560 | UNKNOWN | English - United States | RT_ICON |
4 | 7.98617 | 43467 | UNKNOWN | English - United States | RT_ICON |
5 | 6.34937 | 136 | UNKNOWN | English - United States | RT_STRING |
97 | 6.74142 | 184 | UNKNOWN | English - United States | RT_DIALOG |
188 | 6.07381 | 84 | UNKNOWN | English - United States | RT_STRING |
207 | 5.37823 | 52 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.DLL |
MSVCRT.dll |
Total processes
39
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1556 | "C:\Users\admin\AppData\Local\Temp\download.exe" | C:\Users\admin\AppData\Local\Temp\download.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 18.05 Modules
| |||||||||||||||
| 2016 | "C:\Users\admin\AppData\Local\Temp\7zS416D3052\setup-stub.exe" /UAC:30128 /NCRC | C:\Users\admin\AppData\Local\Temp\7zS416D3052\setup-stub.exe | setup-stub.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: HIGH Description: Firefox Installer Exit code: 0 Version: 81.0 Modules
| |||||||||||||||
| 3332 | .\setup-stub.exe | C:\Users\admin\AppData\Local\Temp\7zS416D3052\setup-stub.exe | download.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Installer Exit code: 0 Version: 81.0 Modules
| |||||||||||||||
Total events
771
Read events
748
Write events
22
Delete events
1
Modification events
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Mozilla |
| Operation: | write | Name: | FirefoxInstallerTest |
Value: Write Test | |||
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Mozilla |
| Operation: | delete value | Name: | FirefoxInstallerTest |
Value: Write Test | |||
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Mozilla\Firefox\TaskBarIDs |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox |
Value: 308046B0AF4A39CB | |||
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\A8985D3A65E5E5C4B2D7D66D40C6DD2FB19C5436 |
| Operation: | write | Name: | Blob |
Value: 04000000010000001000000079E4A9840D7D3A96D7C04FE2434C892E0F0000000100000014000000B34DDD372ED92E8F2ABFBB9E20A9D31F204F194B030000000100000014000000A8985D3A65E5E5C4B2D7D66D40C6DD2FB19C54361D000000010000001000000059779E39E21A2E3DFCED6857ED5C5FD90B000000010000001200000044006900670069004300650072007400000014000000010000001400000003DE503556D14CBB66F0A3E21B1BC397B23DD1556200000001000000200000004348A0E9444C78CB265E058D5E8944B4D84F9662BD26DB257F8934A443C701615300000001000000230000003021301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B060105050703081900000001000000100000000F3A0527D242DE2DC98E5CFCB1E991EE2000000001000000B3030000308203AF30820297A0030201020210083BE056904246B1A1756AC95991C74A300D06092A864886F70D01010505003061310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D3120301E06035504031317446967694365727420476C6F62616C20526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A3061310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D3120301E06035504031317446967694365727420476C6F62616C20526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100E23BE11172DEA8A4D3A357AA50A28F0B7790C9A2A5EE12CE965B010920CC0193A74E30B753F743C46900579DE28D22DD870640008109CECE1B83BFDFCD3B7146E2D666C705B37627168F7B9E1E957DEEB748A308DAD6AF7A0C3906657F4A5D1FBC17F8ABBEEE28D7747F7A78995985686E5C23324BBF4EC0E85A6DE370BF7710BFFC01F685D9A844105832A97518D5D1A2BE47E2276AF49A33F84908608BD45FB43A84BFA1AA4A4C7D3ECF4F5F6C765EA04B37919EDC22E66DCE141A8E6ACBFECDB3146417C75B299E32BFF2EEFAD30B42D4ABB74132DA0CD4EFF881D5BB8D583FB51BE84928A270DA3104DDF7B216F24C0A4E07A8ED4A3D5EB57FA390C3AF270203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E0416041403DE503556D14CBB66F0A3E21B1BC397B23DD155301F0603551D2304183016801403DE503556D14CBB66F0A3E21B1BC397B23DD155300D06092A864886F70D01010505000382010100CB9C37AA4813120AFADD449C4F52B0F4DFAE04F5797908A32418FC4B2B84C02DB9D5C7FEF4C11F58CBB86D9C7A74E79829AB11B5E370A0A1CD4C8899938C9170E2AB0F1CBE93A9FF63D5E40760D3A3BF9D5B09F1D58EE353F48E63FA3FA7DBB466DF6266D6D16E418DF22DB5EA774A9F9D58E22B59C04023ED2D2882453E7954922698E08048A837EFF0D6796016DEACE80ECD6EAC4417382F49DAE1453E2AB93653CF3A5006F72EE8C457496C612118D504AD783C2C3A806BA7EBAF1514E9D889C1B9386CE2916C8AFF64B977255730C01B24A3E1DCE9DF477CB5B424080530EC2DBD0BBF45BF50B9A9F3EB980112ADC888C698345F8D0A3CC6E9D595956DDE | |||
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2016) setup-stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
9
Suspicious files
4
Text files
7
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2016 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\Cab83E6.tmp | — | |
MD5:— | SHA256:— | |||
| 2016 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\Tar83E7.tmp | — | |
MD5:— | SHA256:— | |||
| 1556 | download.exe | C:\Users\admin\AppData\Local\Temp\7zS416D3052\setup-stub.exe | executable | |
MD5:— | SHA256:— | |||
| 2016 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\nse8151.tmp\System.dll | executable | |
MD5:17ED1C86BD67E78ADE4712BE48A7D2BD | SHA256:BD046E6497B304E4EA4AB102CAB2B1F94CE09BDE0EEBBA4C59942A732679E4EB | |||
| 2016 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\nse8151.tmp\UAC.dll | executable | |
MD5:113C5F02686D865BC9E8332350274FD1 | SHA256:0D21041A1B5CD9F9968FC1D457C78A802C9C5A23F375327E833501B65BCD095D | |||
| 2016 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\nse8151.tmp\UserInfo.dll | executable | |
MD5:1B446B36F5B4022D50FFDC0CF567B24A | SHA256:2862C7BC7F11715CEBDEA003564A0D70BF42B73451E2B672110E1392EC392922 | |||
| 3332 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\nsm7C11.tmp\UAC.dll | executable | |
MD5:113C5F02686D865BC9E8332350274FD1 | SHA256:0D21041A1B5CD9F9968FC1D457C78A802C9C5A23F375327E833501B65BCD095D | |||
| 2016 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\nse8151.tmp\stub_common.js | text | |
MD5:58B8AC894C64370CFA137F5848AEB88D | SHA256:0E28AA770B0AFADE30BE85C6DC1E50344DB8F8CDD3FA01989D81A9E20A4990BD | |||
| 1556 | download.exe | C:\Users\admin\AppData\Local\Temp\7zS416D3052\postSigningData | text | |
MD5:— | SHA256:— | |||
| 2016 | setup-stub.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1E11E75149C17A93653DA7DC0B8CF53F_0CE58C7814E604EF410B4A46E10F97A5 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2016 | setup-stub.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2016 | setup-stub.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAqFR8NrFFUItcKTf94Y2FE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2016 | setup-stub.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2016 | setup-stub.exe | 143.204.201.94:443 | product-details.mozilla.org | — | US | suspicious |
1052 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
product-details.mozilla.org |
| shared |
ocsp.digicert.com |
| whitelisted |