| File name: | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b |
| Full analysis: | https://app.any.run/tasks/009b8243-dad1-4769-b935-1783b9326cd4 |
| Verdict: | Malicious activity |
| Analysis date: | December 22, 2023, 21:20:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A47F0158462A8B9A0E53582D7FA7D9B3 |
| SHA1: | 482F2866604FC86FA8F5542FA251DFBAD9BEFA84 |
| SHA256: | 6C050D46A6CF851F2CD826EF5F4B8A117A61E3B81638AEDB77323DEAFAE60E7B |
| SSDEEP: | 98304:hNlX42GIuLxjLblu37trhxOxJpCBaSzrIRQRMXhqXnpaD0V+0E1S9WEhk1AUmHY6:l1gE890xr/FFZq8fF |
MALICIOUS
Actions looks like stealing of personal data
- ns213.tmp (PID: 572)
- taskkill.exe (PID: 1380)
- ns127.tmp (PID: 2420)
- taskkill.exe (PID: 1216)
- WebActiveX5.1.412649.0.exe (PID: 1936)
- 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe (PID: 2080)
- WebSocketServer23450.exe (PID: 1576)
SUSPICIOUS
Uses TASKKILL.EXE to kill process
- ns127.tmp (PID: 2420)
- ns213.tmp (PID: 572)
Starts application with an unusual extension
- 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe (PID: 2080)
INFO
Checks supported languages
- 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe (PID: 2080)
- ns127.tmp (PID: 2420)
- ns213.tmp (PID: 572)
- WebSocketServer23450.exe (PID: 1576)
- WebActiveX5.1.412649.0.exe (PID: 1936)
Create files in a temporary directory
- 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe (PID: 2080)
Creates files in the program directory
- 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe (PID: 2080)
- WebSocketServer23450.exe (PID: 1576)
Reads the computer name
- 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe (PID: 2080)
- WebSocketServer23450.exe (PID: 1576)
- WebActiveX5.1.412649.0.exe (PID: 1936)
Drops the executable file immediately after the start
- 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe (PID: 2080)
Creates files or folders in the user directory
- 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe (PID: 2080)
Reads the machine GUID from the registry
- WebSocketServer23450.exe (PID: 1576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.19433.0 |
| ProductVersionNumber: | 5.1.19433.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | ASCII |
| FileVersion: | 5.1.412649.0 |
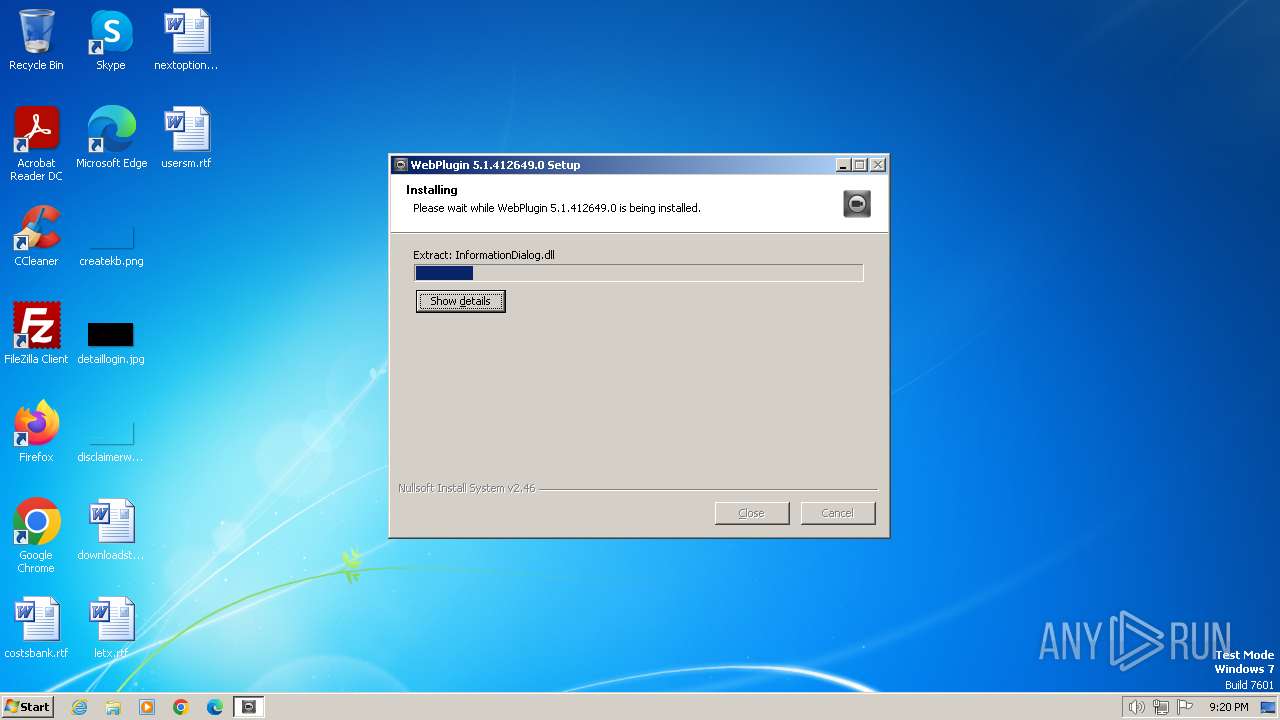
| ProductName: | WebPlugin 5.1.412649.0 |
| ProductVersion: | 5.1.412649.0 |
Total processes
46
Monitored processes
8
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Users\admin\AppData\Local\Temp\nsh117.tmp\ns213.tmp" TASKKILL /F /IM WebSocketServer23450.exe | C:\Users\admin\AppData\Local\Temp\nsh117.tmp\ns213.tmp | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
| 1216 | TASKKILL /F /IM WebSocketServer23450.exe | C:\Windows\System32\taskkill.exe | ns213.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | TASKKILL /F /IM WebActiveX5.1.412649.0.exe | C:\Windows\System32\taskkill.exe | ns127.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1576 | "C:\Program Files\webrec\Torch\5.1.412649.0\WebSocketServer23450.exe" 23450 | C:\Program Files\webrec\Torch\5.1.412649.0\WebSocketServer23450.exe | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1692 | "C:\Users\admin\AppData\Local\Temp\6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe" | C:\Users\admin\AppData\Local\Temp\6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 5.1.412649.0 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\webrec\Torch\5.1.412649.0\WebActiveX5.1.412649.0.exe" /regserver | C:\Program Files\webrec\Torch\5.1.412649.0\WebActiveX5.1.412649.0.exe | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: WebActiveX Module Exit code: 0 Version: 4, 0, 0, 0 Modules
| |||||||||||||||
| 2080 | "C:\Users\admin\AppData\Local\Temp\6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe" | C:\Users\admin\AppData\Local\Temp\6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 5.1.412649.0 Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\AppData\Local\Temp\nsh117.tmp\ns127.tmp" TASKKILL /F /IM WebActiveX5.1.412649.0.exe | C:\Users\admin\AppData\Local\Temp\nsh117.tmp\ns127.tmp | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
Total events
986
Read events
970
Write events
1
Delete events
15
Modification events
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\Control |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\Implemented Categories\{7DD95801-9882-11CF-9FA9-00AA006C42C4} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\Implemented Categories\{7DD95802-9882-11CF-9FA9-00AA006C42C4} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\Implemented Categories |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\Insertable |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\LocalServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\MiscStatus\1 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\MiscStatus |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\ProgID |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1936) WebActiveX5.1.412649.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BC74A141-0E0B-44AF-90DE-0F929A0CE141}\Programmable |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
47
Suspicious files
2
Text files
55
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Users\admin\AppData\Local\Temp\nsh117.tmp\nsExec.dll | executable | |
MD5:ACC2B699EDFEA5BF5AAE45ABA3A41E96 | SHA256:168A974EAA3F588D759DB3F47C1A9FDC3494BA1FA1A73A84E5E3B2A4D58ABD7E | |||
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Program Files\webrec\Torch\5.1.412649.0\dllmavg729dec.dll | executable | |
MD5:9C93D95EFCED481C86C1954A77C75CC1 | SHA256:53C2E3344D4A3E0D305FD859BA28176990523716CE4074F47E449DA7189404E4 | |||
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Program Files\webrec\Torch\5.1.412649.0\cximagecrt.dll | executable | |
MD5:99538665E2DAFD03859161574359CDA8 | SHA256:1D5E2A1679D5D04700B62D1B8EDFFA5E67EA90052E683287BD209B444FCAA109 | |||
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Program Files\webrec\Torch\5.1.412649.0\h264dec.dll | executable | |
MD5:BC0E22F621DDC38778174D4F2597E58E | SHA256:2D60919B1ECE4F01FCEA67E12C6FE70CFE012CF5451C514B40EABA4036E1D9D7 | |||
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Program Files\webrec\Torch\5.1.412649.0\SedProtocolClient.dll | executable | |
MD5:0810E683A5D2E1096700A1D473F59CAC | SHA256:66240BD0551CC6FB5F2DDE8BA017DEEEF274696CBCA1901D11F0F10B9479E936 | |||
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Users\admin\AppData\Local\Temp\nsh117.tmp\ns127.tmp | executable | |
MD5:ACC2B699EDFEA5BF5AAE45ABA3A41E96 | SHA256:168A974EAA3F588D759DB3F47C1A9FDC3494BA1FA1A73A84E5E3B2A4D58ABD7E | |||
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Program Files\webrec\Torch\5.1.412649.0\InformationDialog.dll | executable | |
MD5:218A0F4CC89E22B89BD9A066D5B28ABB | SHA256:4DA1F5B750E92F5999D9C0A7C22C1FC1DA26290DC158DFFE29C9EF13E57B2283 | |||
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Program Files\webrec\Torch\5.1.412649.0\plugin.data | binary | |
MD5:4BD4034157ECF58239DDAC04FBC5CA9A | SHA256:1734A645C64AB6CBE7622ACB6EA59C4CFFF53128D029D917362543E271170898 | |||
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Program Files\webrec\Torch\5.1.412649.0\MasterSlaveAPI.dll | executable | |
MD5:67D843FA5798FC250B68D72FB5FFD621 | SHA256:E5B4F981B4DC146FE742B853BB24511BB13235D10E49F6A77082F9A4CBA3E084 | |||
| 2080 | 6c050d46a6cf851f2cd826ef5f4b8a117a61e3b81638aedb77323deafae60e7b.exe | C:\Program Files\webrec\Torch\5.1.412649.0\dllmavg711.dll | executable | |
MD5:0A9F8AD73BFA3F55E00315A6D2CD3BCC | SHA256:2A595DAF290F40242FFD56CD2DCFA631DA448341FA91EAEC69C52D7143FDEDD4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
WebSocketServer23450.exe | 23450 |
WebSocketServer23450.exe |
_tWinMain: |
WebSocketServer23450.exe | |
WebSocketServer23450.exe | [21:20:37 warn Unknown 1808 ThreadPool.cpp:325]InitConsoleDebug Failed! try again.
|
WebSocketServer23450.exe | [21:20:37 trace Unknown 1808 Thread.cpp:126]ThreadBody Enter name:NetFramework0 daemon, id:1808, prior:N64, stack:0251F8B8
|
WebSocketServer23450.exe | [DHTS][.\Src\queue.cpp:2136]: CSchedManager init success
|
WebSocketServer23450.exe | [21:20:37 trace Unknown 1792 Thread.cpp:126]ThreadBody Enter name:NetFramework0, id:1792, prior:N64, stack:02B4FC70
|
WebSocketServer23450.exe | [21:20:37 info Unknown 1848 DhtsDispatcher.cpp:254]CDhtsIoCollecter::ThreadProc thread start...
|
WebSocketServer23450.exe | [DHTS][.\Src\api.cpp:271]: dhts lib startup, Status 1
|
WebSocketServer23450.exe | [21:20:37 trace Unknown 712 Thread.cpp:126]ThreadBody Enter name:Timer_Thread, id:712, prior:N64, stack:0239FA10
|