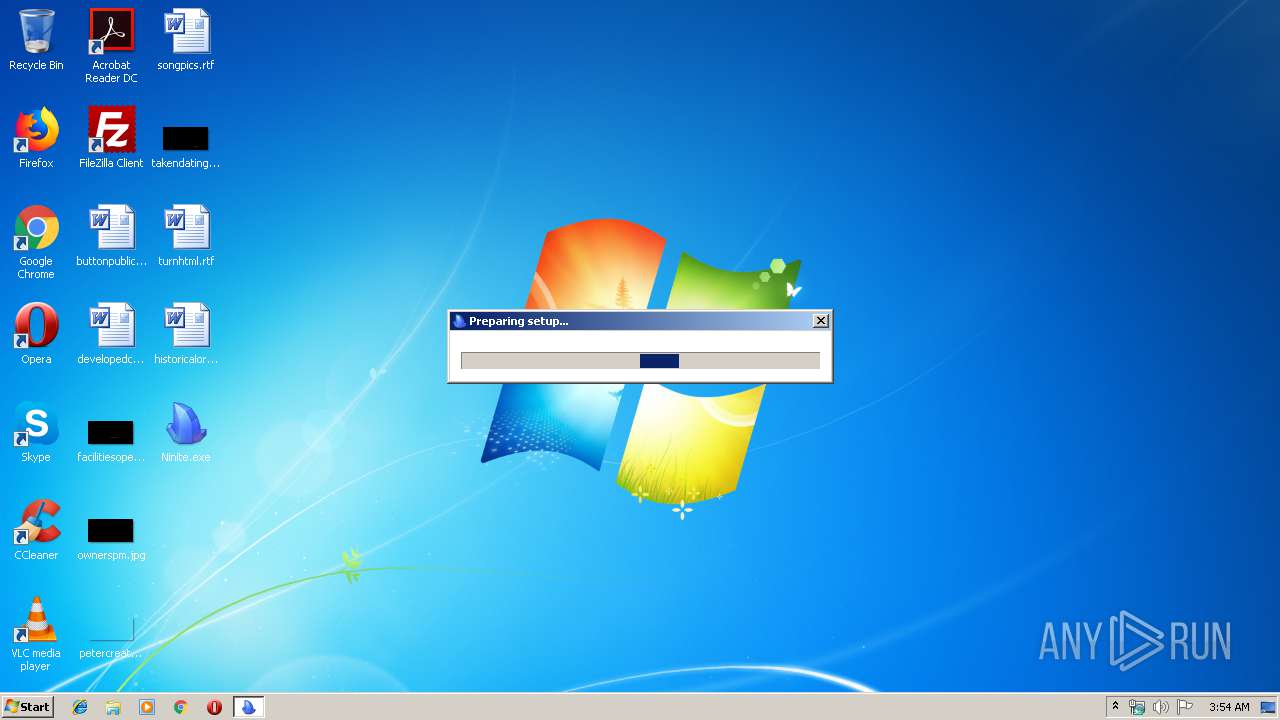
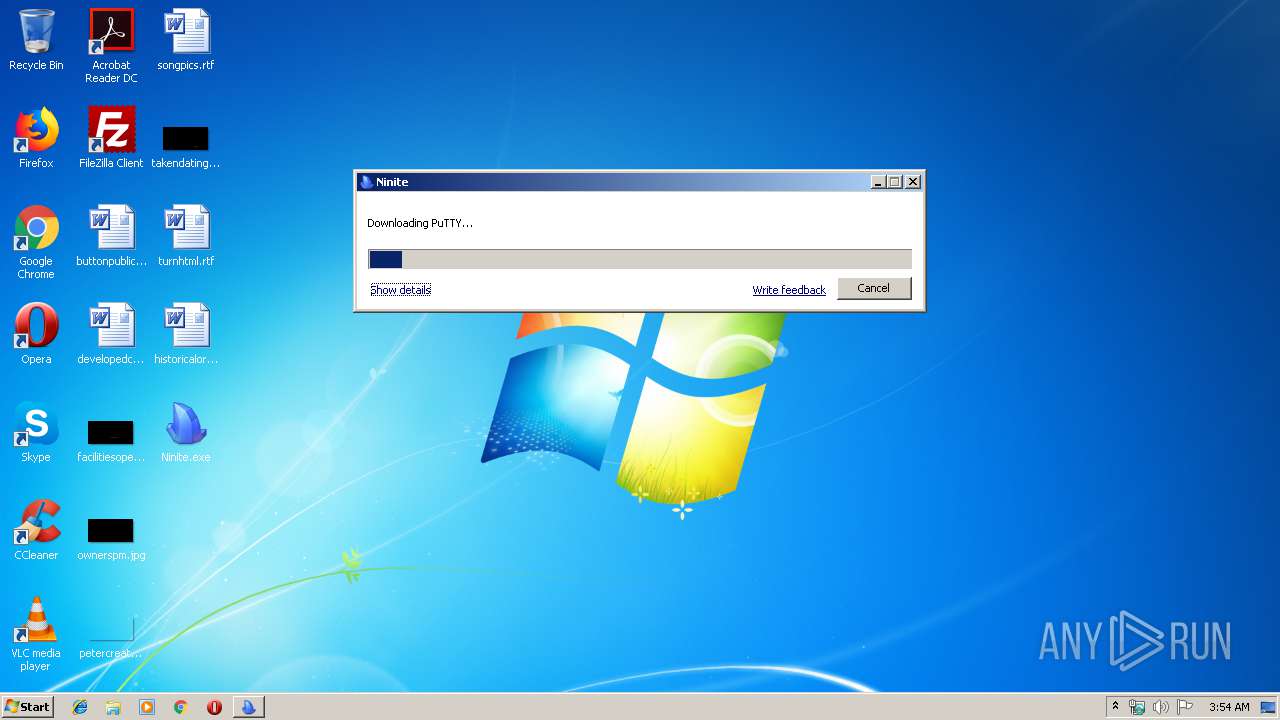
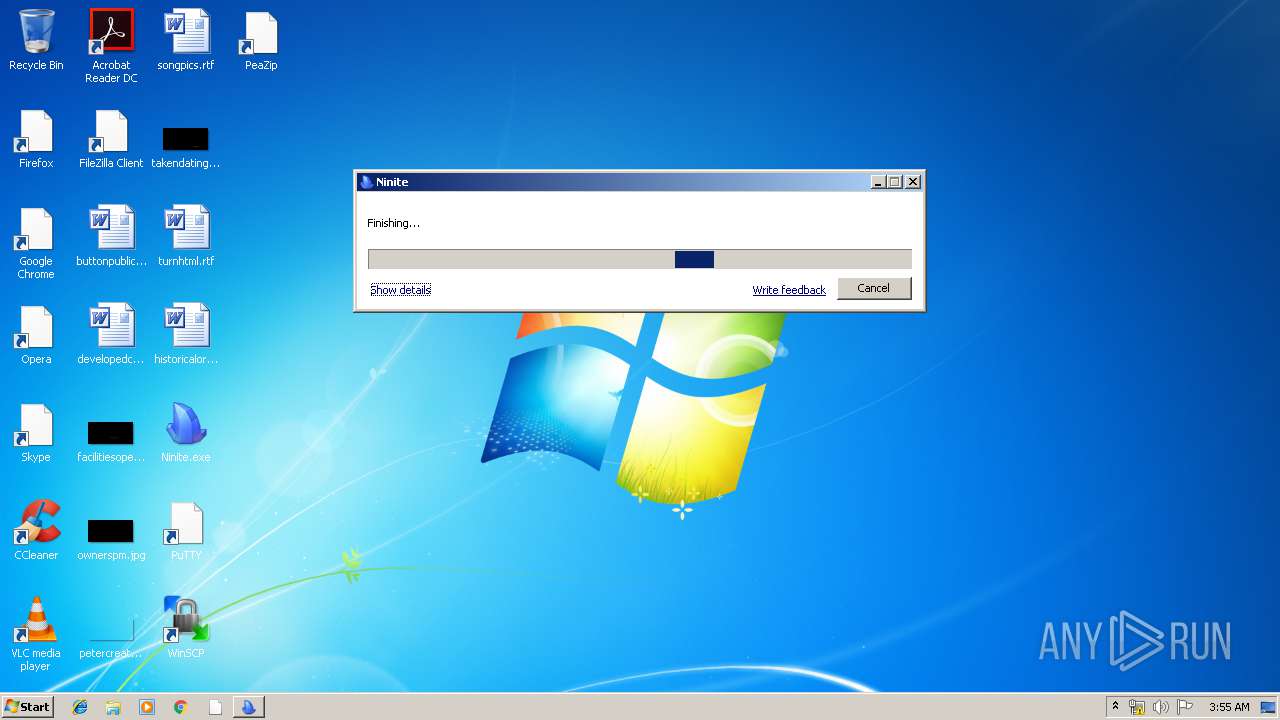
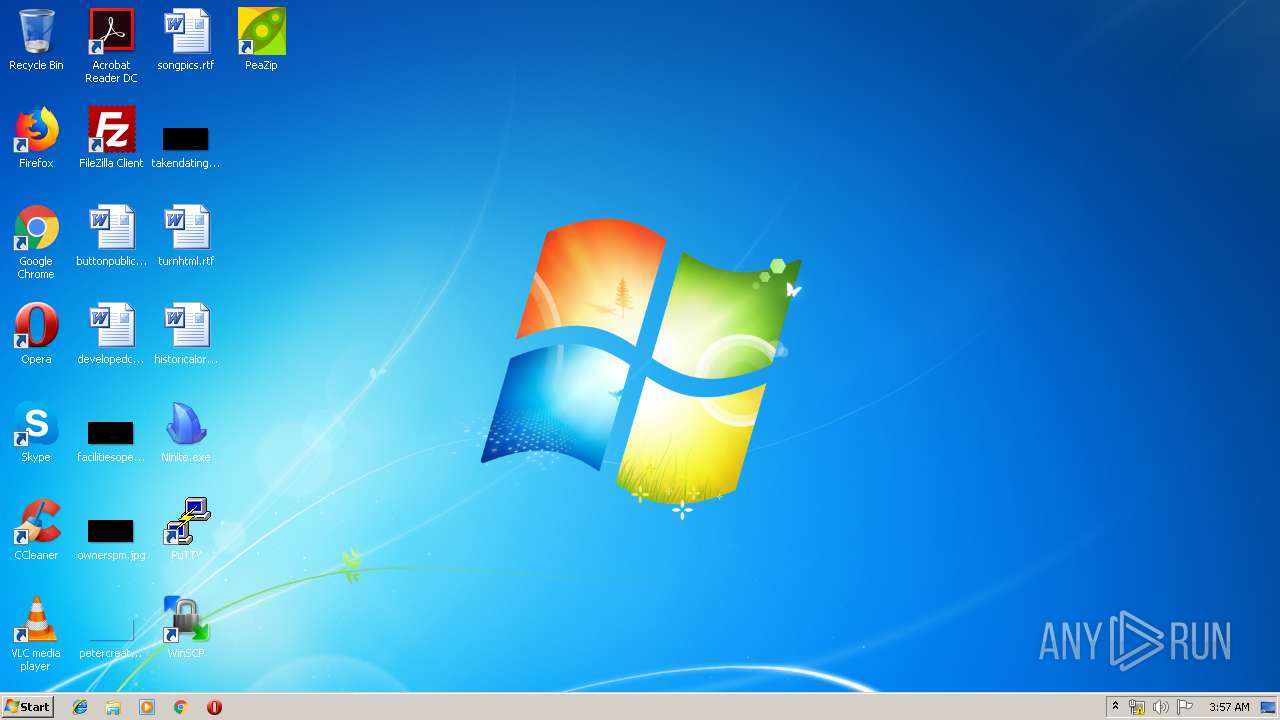
| File name: | Ninite.exe |
| Full analysis: | https://app.any.run/tasks/e00b1a10-d0e9-4180-8dda-d9c2ace7c4a4 |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2019, 02:54:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7871A02C59CBB3A5FE92CD63BB53D356 |
| SHA1: | 2395D0C2A9722195169D1CBBF0690DDC029B8CBC |
| SHA256: | 6BFE12282464B2497E8F6568583388810DC24B26C21BBA4BCE8091B0043DACD7 |
| SSDEEP: | 6144:AhuGbXZA2zNMPMPwVtiN44zAi5NAOig3TBrCZMszqLi7ksvmacmWnZ+e:suypA2hESwGRwg3TBPi7BvmZmwZL |
MALICIOUS
Application was dropped or rewritten from another process
- Ninite.exe (PID: 2200)
- Ninite.exe (PID: 3916)
- target.exe (PID: 2384)
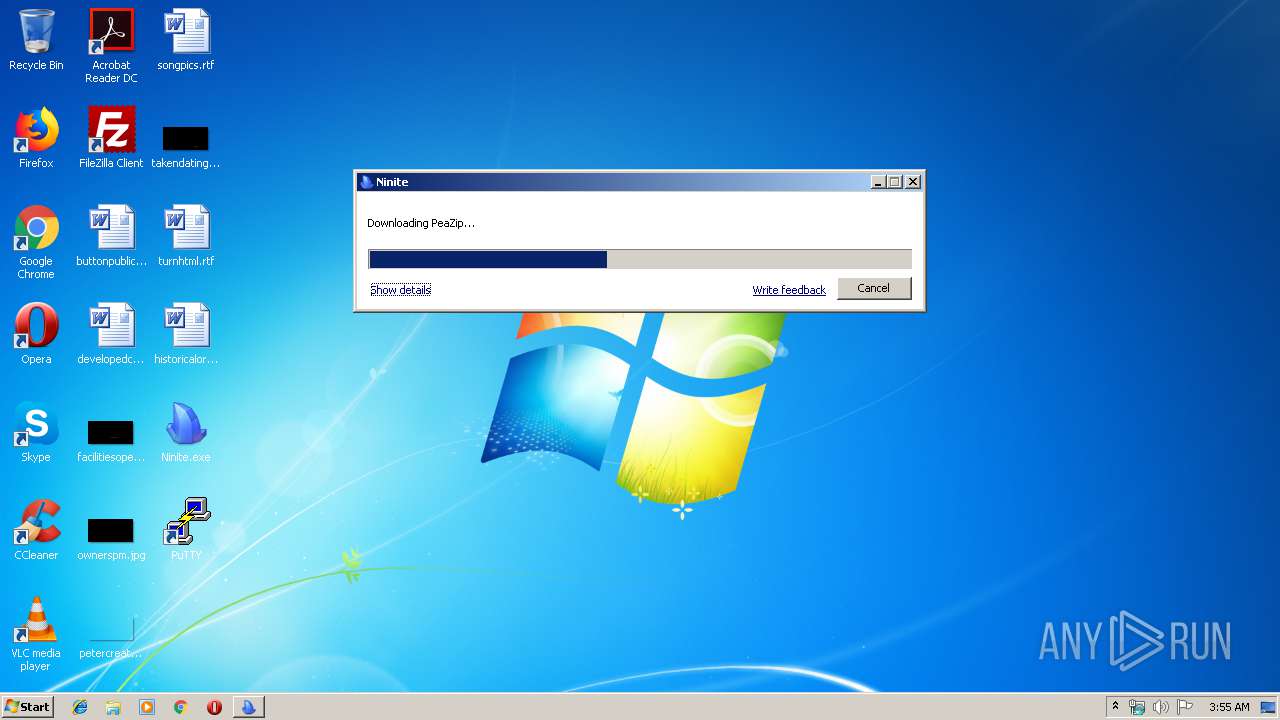
- peazip.exe (PID: 2688)
- target.exe (PID: 3744)
- WinSCP.exe (PID: 2132)
- WinSCP.exe (PID: 3156)
Changes settings of System certificates
- Ninite.exe (PID: 2200)
- msiexec.exe (PID: 2508)
Loads dropped or rewritten executable
- peazip.exe (PID: 2688)
- regsvr32.exe (PID: 2876)
Registers / Runs the DLL via REGSVR32.EXE
- target.tmp (PID: 2620)
SUSPICIOUS
Executable content was dropped or overwritten
- Ninite.exe (PID: 3620)
- Ninite.exe (PID: 2200)
- msiexec.exe (PID: 2508)
- target.exe (PID: 2384)
- target.tmp (PID: 3116)
- target.exe (PID: 3744)
- target.tmp (PID: 2620)
Adds / modifies Windows certificates
- msiexec.exe (PID: 2508)
- Ninite.exe (PID: 2200)
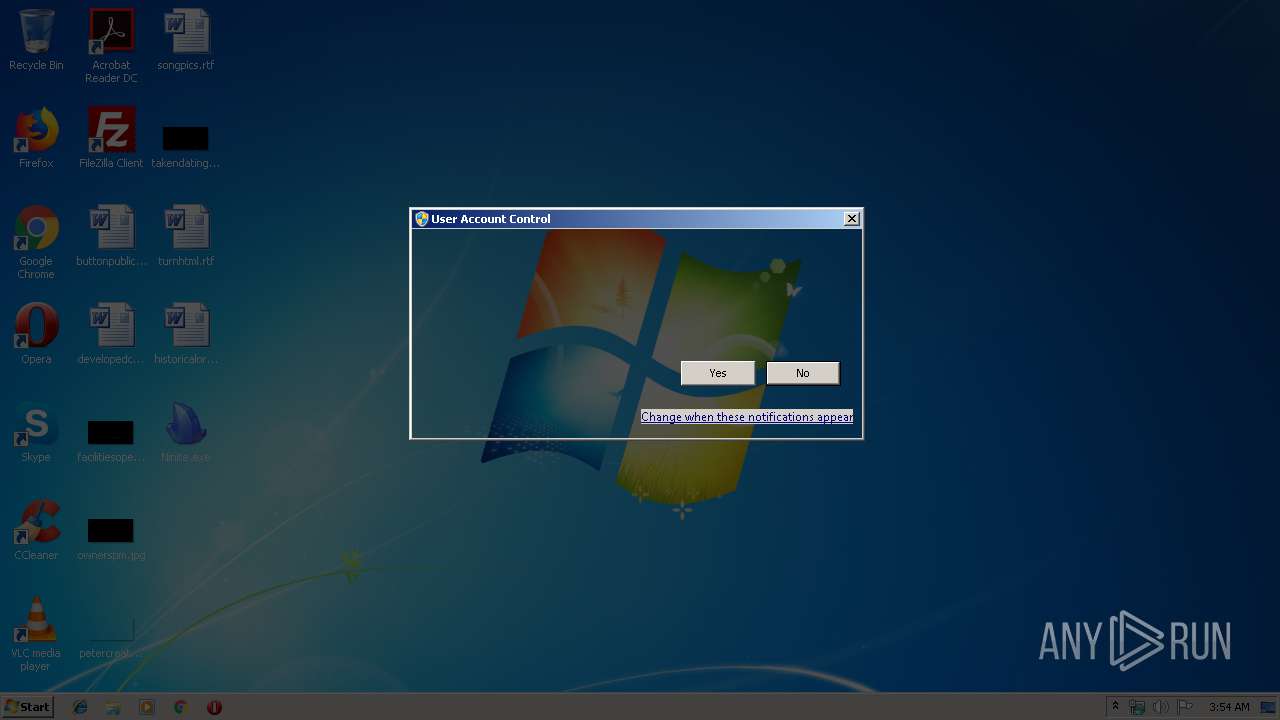
Application launched itself
- Ninite.exe (PID: 3916)
Reads the machine GUID from the registry
- Ninite.exe (PID: 2200)
Creates files in the user directory
- Ninite.exe (PID: 2200)
- target.tmp (PID: 3116)
- peazip.exe (PID: 2688)
- target.tmp (PID: 2620)
- WinSCP.exe (PID: 3156)
Reads the Windows organization settings
- target.tmp (PID: 3116)
- target.tmp (PID: 2620)
Modifies the open verb of a shell class
- msiexec.exe (PID: 2508)
- target.tmp (PID: 3116)
- WinSCP.exe (PID: 2132)
Reads Windows owner or organization settings
- target.tmp (PID: 3116)
- target.tmp (PID: 2620)
Starts CMD.EXE for commands execution
- peazip.exe (PID: 2688)
Searches for installed software
- WinSCP.exe (PID: 2132)
- Ninite.exe (PID: 2200)
- WinSCP.exe (PID: 3156)
Creates COM task schedule object
- regsvr32.exe (PID: 2876)
Reads Environment values
- WinSCP.exe (PID: 2132)
- WinSCP.exe (PID: 3156)
INFO
Creates a software uninstall entry
- msiexec.exe (PID: 2508)
- target.tmp (PID: 3116)
- target.tmp (PID: 2620)
Creates files in the program directory
- msiexec.exe (PID: 2508)
- target.tmp (PID: 2620)
- target.tmp (PID: 3116)
Application was dropped or rewritten from another process
- target.tmp (PID: 3116)
- target.tmp (PID: 2620)
Dropped object may contain Bitcoin addresses
- target.tmp (PID: 3116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:04:12 02:19:47+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 233472 |
| InitializedDataSize: | 182272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a53a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.1.1.1183 |
| ProductVersionNumber: | 0.1.1.1183 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
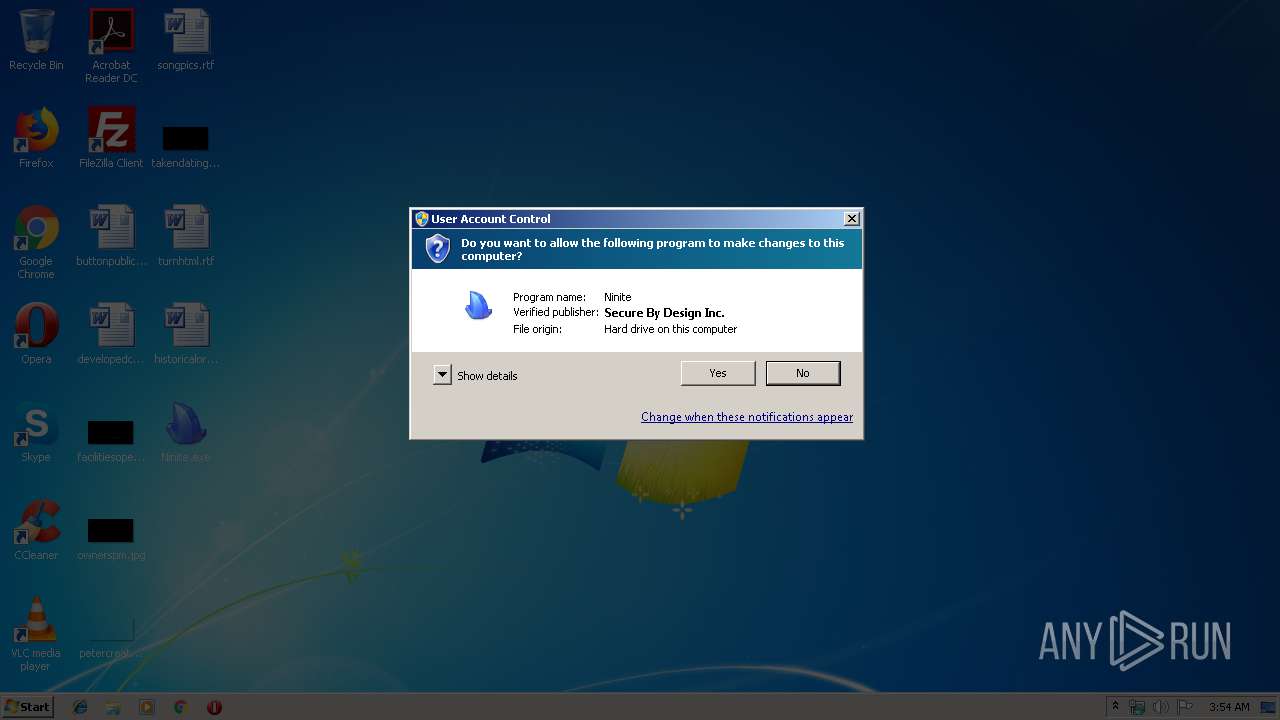
| CompanyName: | Secure By Design Inc. |
| FileDescription: | Ninite |
| FileVersion: | 0,1,1,1183 |
| InternalName: | Ninite |
| LegalCopyright: | Copyright (C) 2009 Secure By Design Inc |
| OriginalFileName: | - |
| ProductName: | Ninite |
| ProductVersion: | 0,1,1,1183 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Apr-2017 00:19:47 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Secure By Design Inc. |
| FileDescription: | Ninite |
| FileVersion: | 0,1,1,1183 |
| InternalName: | Ninite |
| LegalCopyright: | Copyright (C) 2009 Secure By Design Inc |
| OriginalFilename: | - |
| ProductName: | Ninite |
| ProductVersion: | 0,1,1,1183 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 12-Apr-2017 00:19:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00038FCB | 0x00039000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65103 |
.rdata | 0x0003A000 | 0x00016510 | 0x00016600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.7058 |
.data | 0x00051000 | 0x00002320 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70057 |
.gfids | 0x00054000 | 0x000001D0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.69528 |
.rsrc | 0x00055000 | 0x000108C0 | 0x00010A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.96686 |
.reloc | 0x00066000 | 0x0000315C | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.57778 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21106 | 1344 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.34612 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 3.20853 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 7.919 | 41725 | UNKNOWN | English - United States | RT_ICON |
5 | 4.29057 | 9640 | UNKNOWN | English - United States | RT_ICON |
6 | 4.22273 | 4264 | UNKNOWN | English - United States | RT_ICON |
7 | 4.77095 | 1128 | UNKNOWN | English - United States | RT_ICON |
129 | 3.04788 | 164 | UNKNOWN | English - United States | RT_DIALOG |
131 | 3.1497 | 374 | UNKNOWN | English - United States | RT_DIALOG |
132 | 2.33827 | 30 | UNKNOWN | English - United States | RT_MENU |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINTRUST.dll |
urlmon.dll |
Total processes
54
Monitored processes
14
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | msiexec.exe /i target.msi /qn /norestart REBOOT=ReallySuppress ALLUSERS=1 | C:\Windows\system32\msiexec.exe | — | Ninite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | cmd /c rmdir "C:\Users\admin\AppData\Local\Temp\peazip-tmp\" /s /q | C:\Windows\system32\cmd.exe | — | peazip.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2132 | "C:\Program Files\WinSCP\WinSCP.exe" /RegisterForDefaultProtocols | C:\Program Files\WinSCP\WinSCP.exe | — | target.tmp | |||||||||||
User: admin Company: Martin Prikryl Integrity Level: HIGH Description: WinSCP: SFTP, FTP, WebDAV, S3 and SCP client Exit code: 0 Version: 5.15.3.9730 Modules
| |||||||||||||||
| 2200 | "C:\Users\admin\AppData\Local\Temp\d4fce87c-c7ac-11e9-b86f-5254004a04af\Ninite.exe" "A9BD463632D2F174C9C64896FAAA8D3E81372DEA" /fullpath "C:\Users\admin\Desktop\Ninite.exe" /relaunch | C:\Users\admin\AppData\Local\Temp\d4fce87c-c7ac-11e9-b86f-5254004a04af\Ninite.exe | Ninite.exe | ||||||||||||
User: admin Company: Secure By Design Inc. Integrity Level: HIGH Description: Ninite Exit code: 0 Version: 0,1,1,1336 Modules
| |||||||||||||||
| 2384 | target.exe /sp- /verysilent /norestart | C:\Users\admin\AppData\Local\Temp\E4FF9F~1\target.exe | Ninite.exe | ||||||||||||
User: admin Company: Giorgio Tani Integrity Level: HIGH Description: PeaZip Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2508 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2620 | "C:\Users\admin\AppData\Local\Temp\is-U8L64.tmp\target.tmp" /SL5="$202AA,9213679,204800,C:\Users\admin\AppData\Local\Temp\EC8D32~1\target.exe" /VERYSILENT /NORESTART /NOCLOSEAPPLICATIONS /NOCANDY | C:\Users\admin\AppData\Local\Temp\is-U8L64.tmp\target.tmp | target.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\PeaZip\peazip.exe" -peaziplanguage en.txt | C:\Program Files\PeaZip\peazip.exe | — | target.tmp | |||||||||||
User: admin Company: Giorgio Tani Integrity Level: HIGH Description: PeaZip, file and archive manager Exit code: 0 Version: 6.8.1 Modules
| |||||||||||||||
| 2876 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\WinSCP\DragExt.dll" | C:\Windows\system32\regsvr32.exe | — | target.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3116 | "C:\Users\admin\AppData\Local\Temp\is-U8L64.tmp\target.tmp" /SL5="$50148,6750010,151552,C:\Users\admin\AppData\Local\Temp\E4FF9F~1\target.exe" /sp- /verysilent /norestart | C:\Users\admin\AppData\Local\Temp\is-U8L64.tmp\target.tmp | target.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
4 442
Read events
3 166
Write events
1 258
Delete events
18
Modification events
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3620) Ninite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Ninite_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
85
Suspicious files
18
Text files
109
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3620 | Ninite.exe | C:\Users\admin\AppData\Local\Temp\CabA5BA.tmp | — | |
MD5:— | SHA256:— | |||
| 3620 | Ninite.exe | C:\Users\admin\AppData\Local\Temp\TarA5BB.tmp | — | |
MD5:— | SHA256:— | |||
| 3620 | Ninite.exe | C:\Users\admin\AppData\Local\Temp\CabA5CC.tmp | — | |
MD5:— | SHA256:— | |||
| 3620 | Ninite.exe | C:\Users\admin\AppData\Local\Temp\TarA5CD.tmp | — | |
MD5:— | SHA256:— | |||
| 3620 | Ninite.exe | C:\Users\admin\AppData\Local\Temp\CabAA71.tmp | — | |
MD5:— | SHA256:— | |||
| 3620 | Ninite.exe | C:\Users\admin\AppData\Local\Temp\TarAA82.tmp | — | |
MD5:— | SHA256:— | |||
| 2200 | Ninite.exe | C:\Users\admin\AppData\Local\Temp\de3a5189-c7ac-11e9-b86f-5254004a04af\target.msi_de3a518a-c7ac-11e9-b86f-5254004a04af | — | |
MD5:— | SHA256:— | |||
| 2508 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab791.tmp | — | |
MD5:— | SHA256:— | |||
| 2508 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar792.tmp | — | |
MD5:— | SHA256:— | |||
| 2508 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF159DF7743596FCA2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
19
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3620 | Ninite.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.6 Kb | whitelisted |
3620 | Ninite.exe | GET | 200 | 99.86.255.92:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2200 | Ninite.exe | GET | 301 | 82.187.89.53:80 | http://www.peazip.org/downloads/peazip-6.9.0.WINDOWS.exe | IT | html | 180 b | suspicious |
2200 | Ninite.exe | GET | 301 | 82.187.89.53:80 | http://www.peazip.org/downloads/peazip-6.9.0.WINDOWS.exe | IT | html | 180 b | suspicious |
2200 | Ninite.exe | GET | 301 | 82.187.89.53:80 | http://www.peazip.org/downloads/peazip-6.9.0.WINDOWS.exe | IT | html | 180 b | suspicious |
2200 | Ninite.exe | GET | 301 | 82.187.89.53:80 | http://www.peazip.org/downloads/peazip-6.9.0.WINDOWS.exe | IT | html | 180 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3620 | Ninite.exe | 100.25.56.93:443 | ninite.com | — | US | unknown |
3620 | Ninite.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2200 | Ninite.exe | 100.25.56.93:443 | ninite.com | — | US | unknown |
2200 | Ninite.exe | 46.43.34.31:443 | the.earth.li | Bytemark Limited | GB | suspicious |
2200 | Ninite.exe | 82.187.89.53:80 | www.peazip.org | Telecom Italia | IT | unknown |
2200 | Ninite.exe | 82.187.89.53:443 | www.peazip.org | Telecom Italia | IT | unknown |
2200 | Ninite.exe | 192.175.120.182:443 | iweb.dl.sourceforge.net | iWeb Technologies Inc. | CA | suspicious |
2620 | target.tmp | 87.106.181.237:443 | winscp.net | 1&1 Internet SE | DE | unknown |
3620 | Ninite.exe | 52.217.32.4:443 | ninite-stages.s3.amazonaws.com | Amazon.com, Inc. | US | suspicious |
3620 | Ninite.exe | 99.86.255.92:80 | x.ss2.us | AT&T Services, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ninite.com |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ninite-stages.s3.amazonaws.com |
| shared |
the.earth.li |
| whitelisted |
www.peazip.org |
| suspicious |
iweb.dl.sourceforge.net |
| suspicious |
winscp.net |
| whitelisted |