| File name: | RMLLauncher.exe |
| Full analysis: | https://app.any.run/tasks/145f1172-bfcb-4556-920f-99f717cfcfa0 |
| Verdict: | Suspicious activity |
| Analysis date: | June 26, 2020, 21:49:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A61659B291A0ABA3D39CAEB7BBE4C59A |
| SHA1: | D7AF375A687EBD0827D3334651755AB635D20D04 |
| SHA256: | 6BFA762B72ED8D94B70B0457327B96B04E15837EBDBF71A445014801EF0A5B55 |
| SSDEEP: | 6144:BWRs0tpuW4gvbRuaBqwzGIWEj9O3whKqWeuW4gvbeuaBXVBE56w93wXb3wXw:BW20GW4SRuUqwtRwAhWW4SeuUjP |
MALICIOUS
Application was dropped or rewritten from another process
- HMLCore.exe (PID: 864)
SUSPICIOUS
Creates files in the user directory
- RMLLauncher.exe (PID: 2328)
- HMLCore.exe (PID: 864)
Reads Environment values
- HMLCore.exe (PID: 864)
Executable content was dropped or overwritten
- RMLLauncher.exe (PID: 2328)
Reads internet explorer settings
- HMLCore.exe (PID: 864)
Modifies the open verb of a shell class
- HMLCore.exe (PID: 864)
Reads Internet Cache Settings
- HMLCore.exe (PID: 864)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (62) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2070:04:10 08:13:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 351232 |
| InitializedDataSize: | 137728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x57b26 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
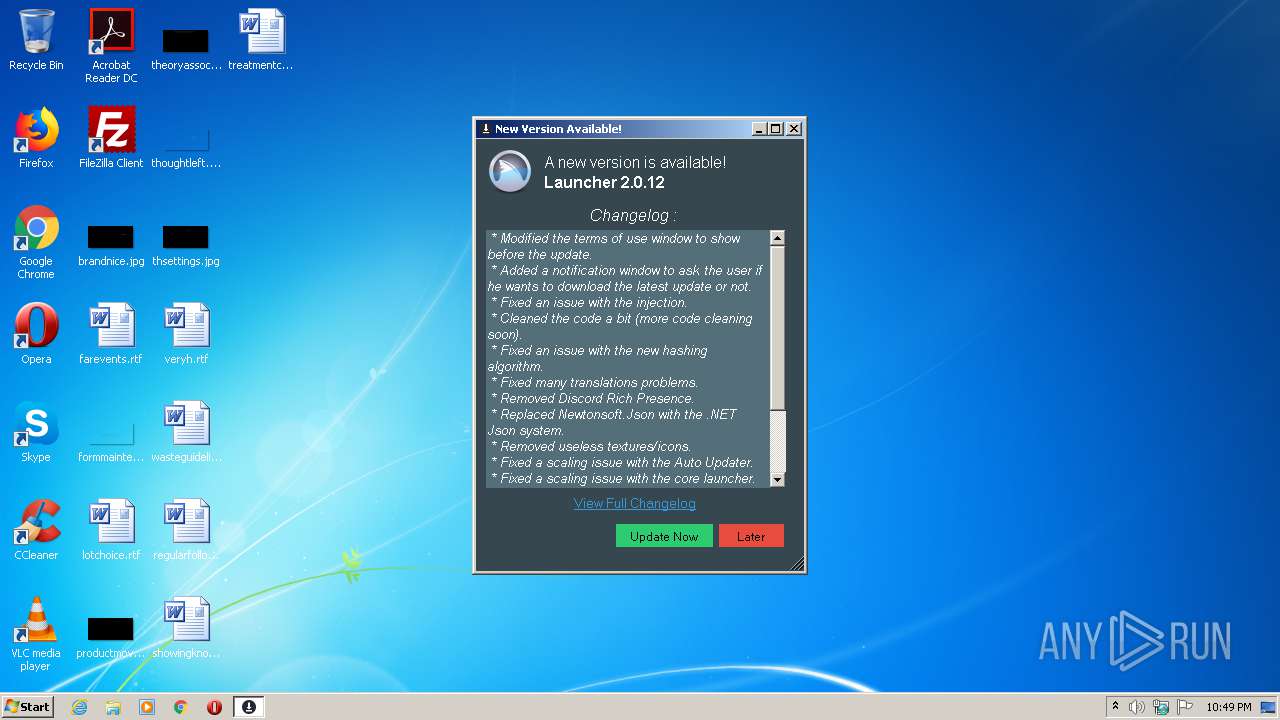
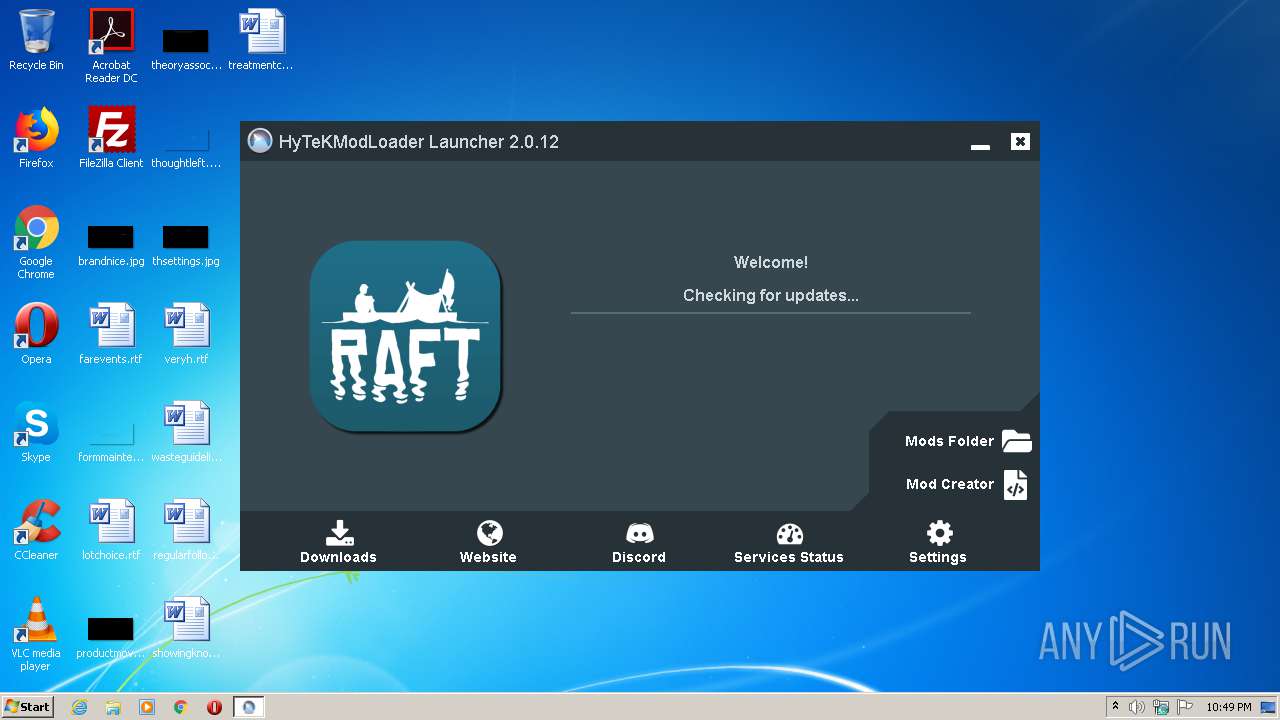
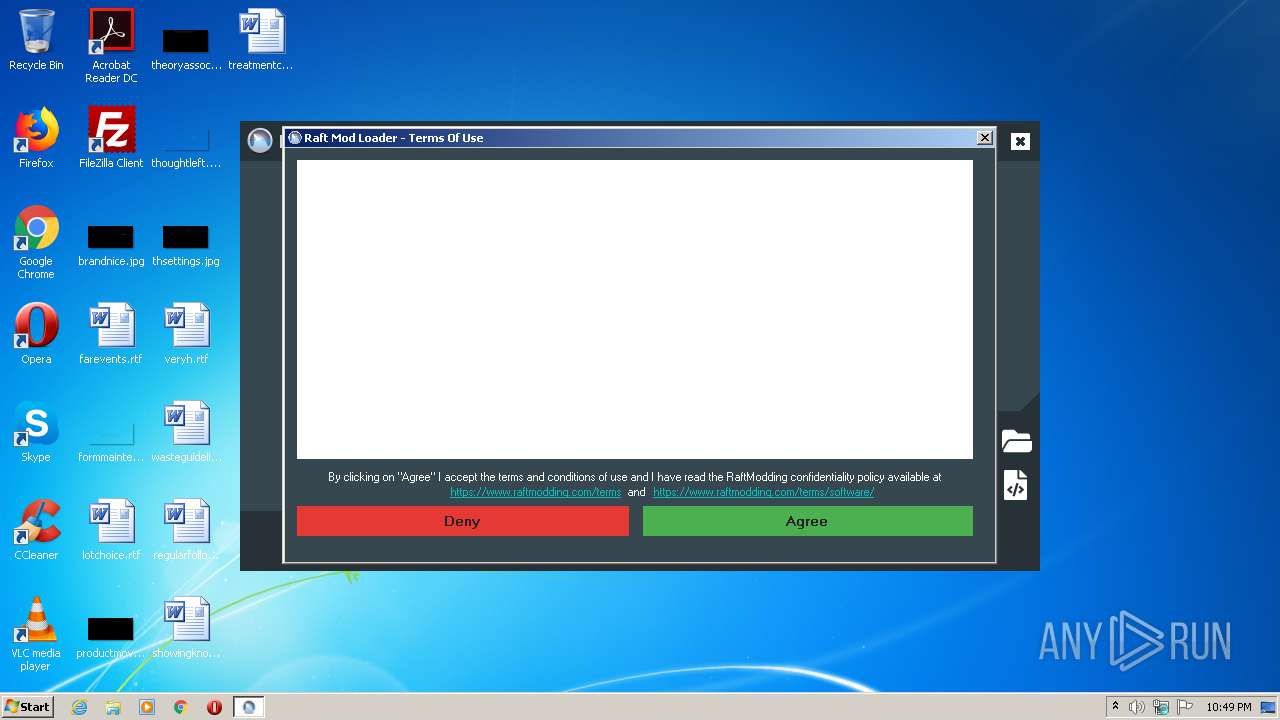
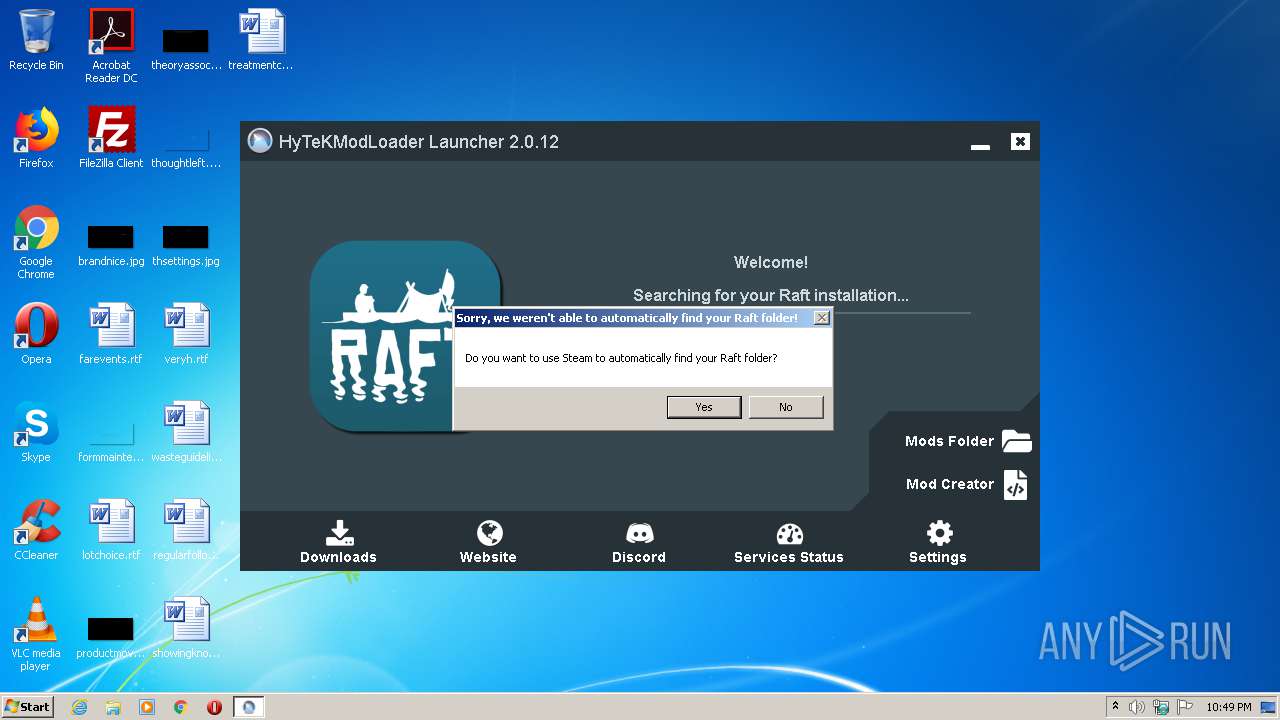
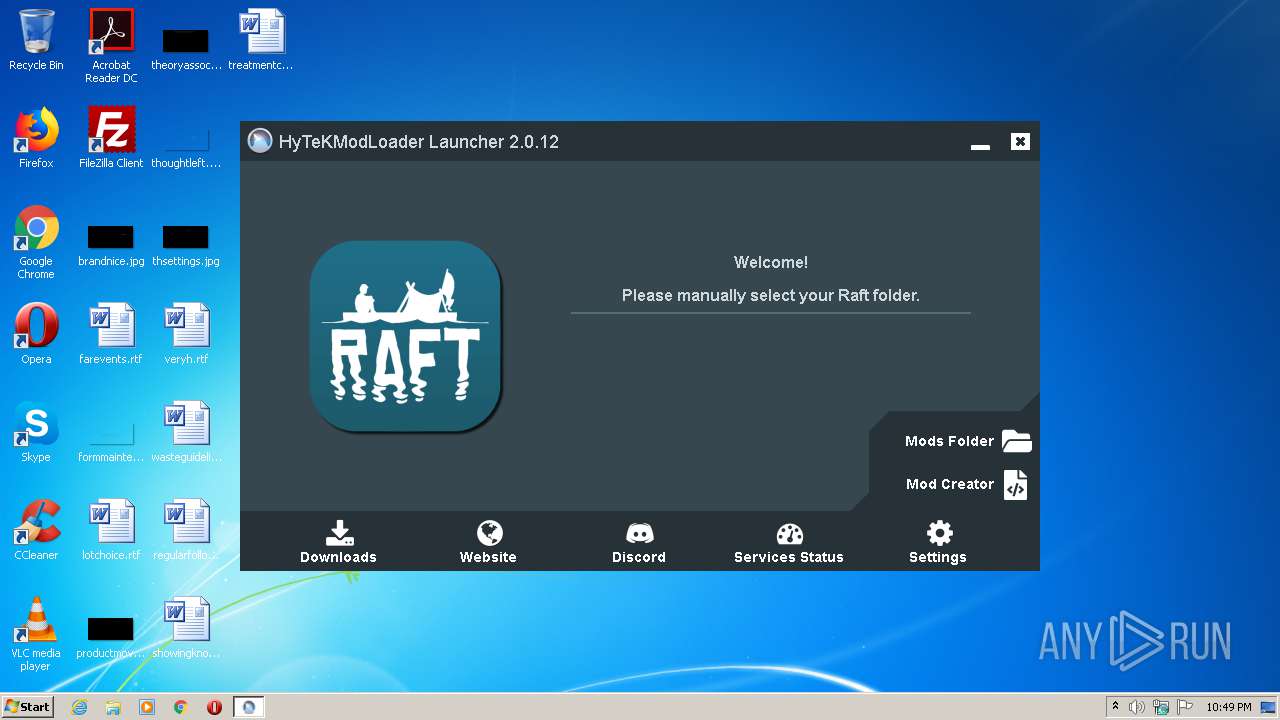
| Comments: | This software installs HyTeKModLoader for you and keep it up to date! |
| CompanyName: | https://www.hytekgames.net |
| FileDescription: | HyTeKModLoader Launcher Updater |
| FileVersion: | 2.0.0.0 |
| InternalName: | HyTeKLauncherUpdater.exe |
| LegalCopyright: | Copyright HyTeKGames © 2020 |
| LegalTrademarks: | HyTeKGames |
| OriginalFileName: | HyTeKLauncherUpdater.exe |
| ProductName: | HyTeK Mod Loader Launcher Updater |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Mar-1934 23:45:11 |
| Debug artifacts: |
|
| Comments: | This software installs HyTeKModLoader for you and keep it up to date! |
| CompanyName: | https://www.hytekgames.net |
| FileDescription: | HyTeKModLoader Launcher Updater |
| FileVersion: | 2.0.0.0 |
| InternalName: | HyTeKLauncherUpdater.exe |
| LegalCopyright: | Copyright HyTeKGames © 2020 |
| LegalTrademarks: | HyTeKGames |
| OriginalFilename: | HyTeKLauncherUpdater.exe |
| ProductName: | HyTeK Mod Loader Launcher Updater |
| ProductVersion: | 2.0.0.0 |
| Assembly Version: | 2.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Mar-1934 23:45:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00055B2C | 0x00055C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.87809 |
.rsrc | 0x00058000 | 0x0002178A | 0x00021800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.55703 |
.reloc | 0x0007A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.05939 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.05942 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.63445 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.05772 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.69583 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 7.95102 | 33566 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.77685 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
MAINICON | 1.6789 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Users\admin\AppData\Roaming\RaftModLoader\HMLCore.exe" | C:\Users\admin\AppData\Roaming\RaftModLoader\HMLCore.exe | RMLLauncher.exe | ||||||||||||
User: admin Company: https://www.hytekgames.net Integrity Level: MEDIUM Description: HyTeK Mod Loader Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2328 | "C:\Users\admin\Downloads\RMLLauncher.exe" | C:\Users\admin\Downloads\RMLLauncher.exe | explorer.exe | ||||||||||||
User: admin Company: https://www.hytekgames.net Integrity Level: MEDIUM Description: HyTeKModLoader Launcher Updater Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
Total events
625
Read events
559
Write events
66
Delete events
0
Modification events
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2328) RMLLauncher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RMLLauncher_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
4
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 864 | HMLCore.exe | C:\Users\admin\AppData\Local\Temp\CabB4A1.tmp | — | |
MD5:— | SHA256:— | |||
| 864 | HMLCore.exe | C:\Users\admin\AppData\Local\Temp\TarB4A2.tmp | — | |
MD5:— | SHA256:— | |||
| 864 | HMLCore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C1B3CC7FF1466C71640A202F8258105B_A1176F6D250B1A534FB2DE8EBFF44E24 | der | |
MD5:— | SHA256:— | |||
| 2328 | RMLLauncher.exe | C:\Users\admin\AppData\Roaming\RaftModLoader\HMLCore.exe | executable | |
MD5:— | SHA256:— | |||
| 864 | HMLCore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C1B3CC7FF1466C71640A202F8258105B_A1176F6D250B1A534FB2DE8EBFF44E24 | binary | |
MD5:— | SHA256:— | |||
| 864 | HMLCore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\software[1].htm | html | |
MD5:— | SHA256:— | |||
| 864 | HMLCore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\24ESPUQH.txt | text | |
MD5:— | SHA256:— | |||
| 864 | HMLCore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:— | SHA256:— | |||
| 864 | HMLCore.exe | C:\Users\admin\AppData\Roaming\RaftModLoader\launcher_config.json | text | |
MD5:— | SHA256:— | |||
| 864 | HMLCore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
864 | HMLCore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
864 | HMLCore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAtVJ%2B9ZdM0z695kcqzDrJg%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2328 | RMLLauncher.exe | 104.27.139.72:443 | fastdl.raftmodding.com | Cloudflare Inc | US | unknown |
864 | HMLCore.exe | 104.27.139.72:80 | fastdl.raftmodding.com | Cloudflare Inc | US | unknown |
864 | HMLCore.exe | 104.27.139.72:443 | fastdl.raftmodding.com | Cloudflare Inc | US | unknown |
864 | HMLCore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 104.27.139.72:443 | fastdl.raftmodding.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fastdl.raftmodding.com |
| malicious |
www.raftmodding.com |
| malicious |
ocsp.digicert.com |
| whitelisted |