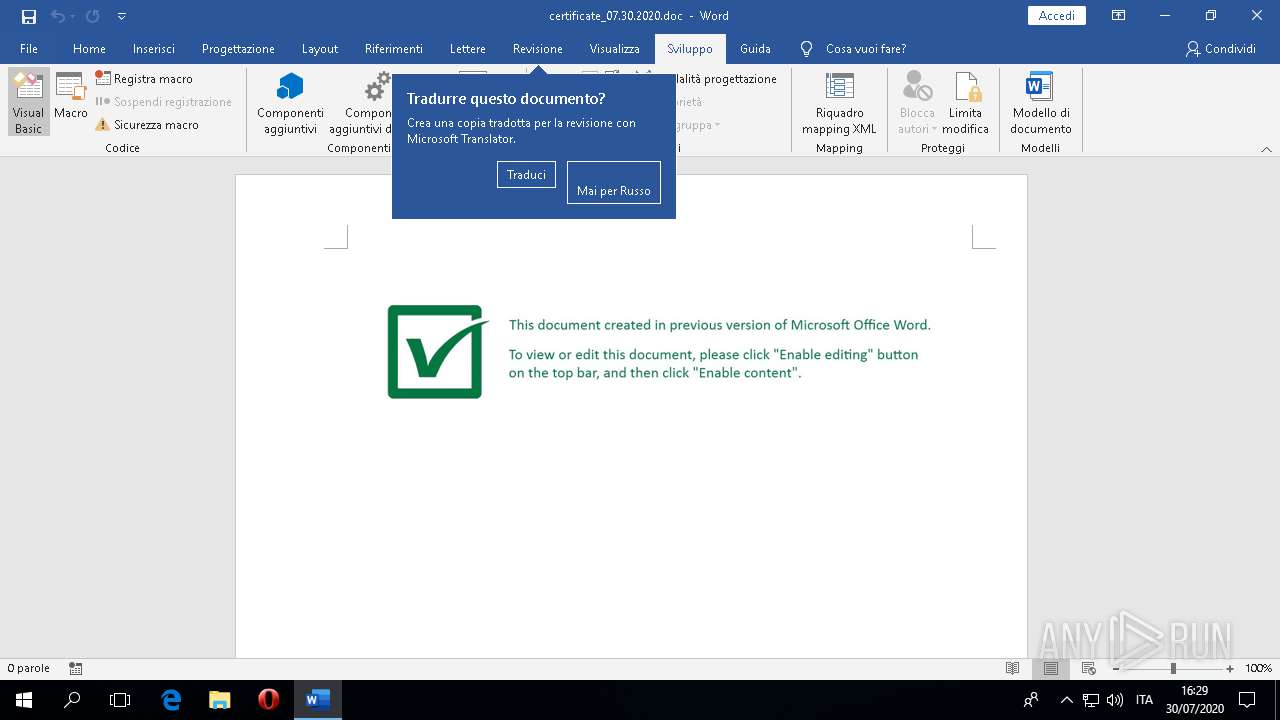
| File name: | certificate_07.30.2020.doc |
| Full analysis: | https://app.any.run/tasks/c21c6ca0-3d90-4e89-91a4-3cb373f9d785 |
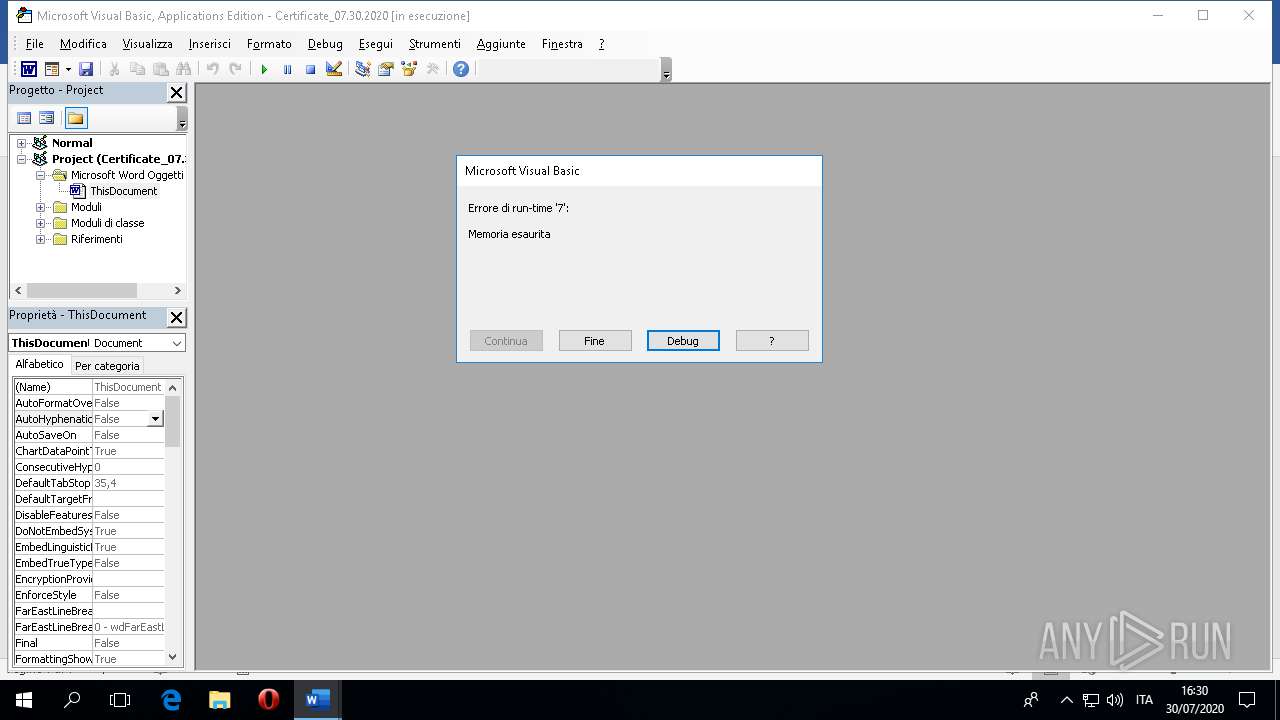
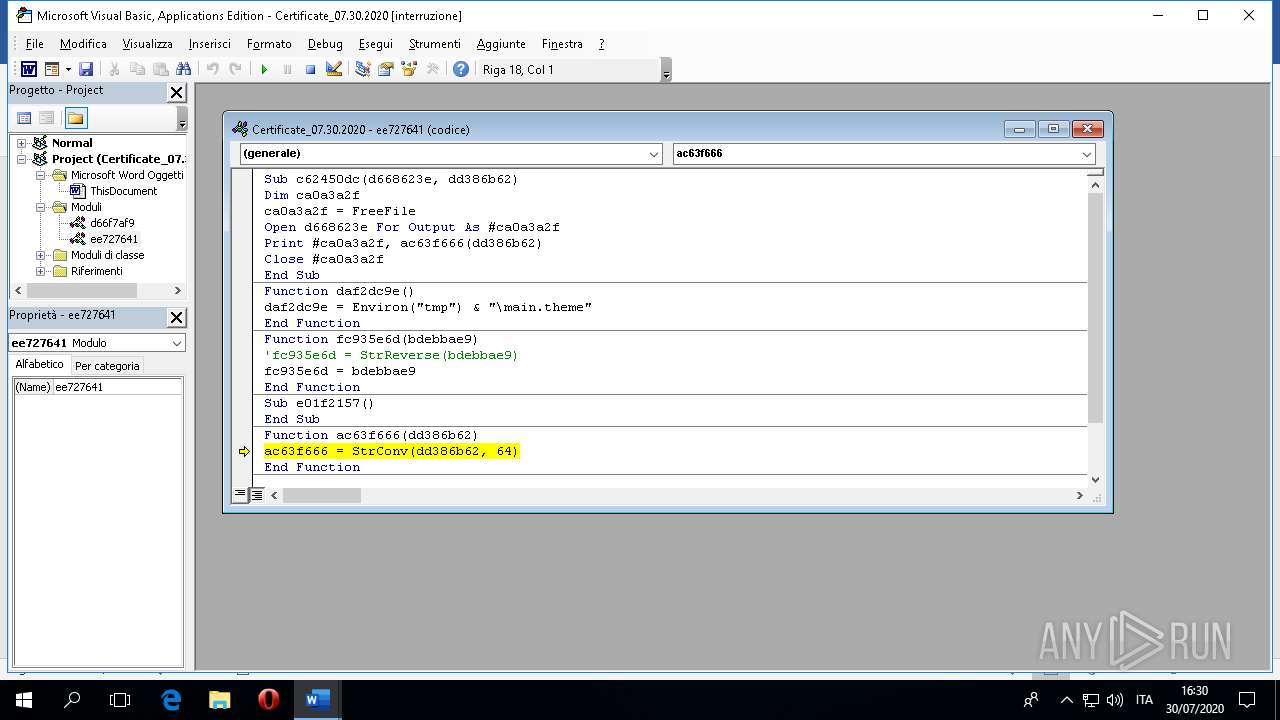
| Verdict: | Malicious activity |
| Analysis date: | July 30, 2020, 14:29:03 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 7538B27645C22E684A568C47C374D0BF |
| SHA1: | 71DA916476FBB2A77301F9B79A139276F838F2CA |
| SHA256: | 6BE3A54E9231FE0DEBA68138ECB77ED20356A54E9FFC70813EC7974C76869B36 |
| SSDEEP: | 3072:9I4q3vTvcfg99u3FUOatt+Px53NnxfffxBmNU:9IJbOUOaCZ53Nb |
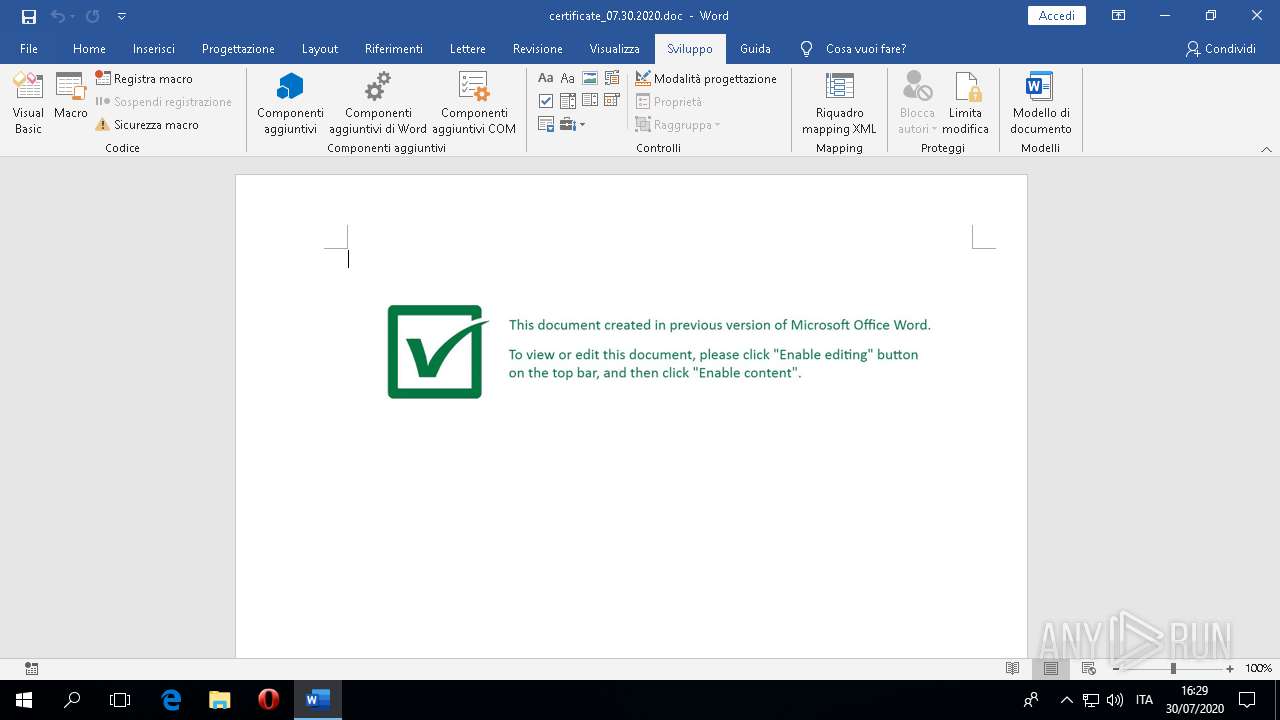
MALICIOUS
No malicious indicators.SUSPICIOUS
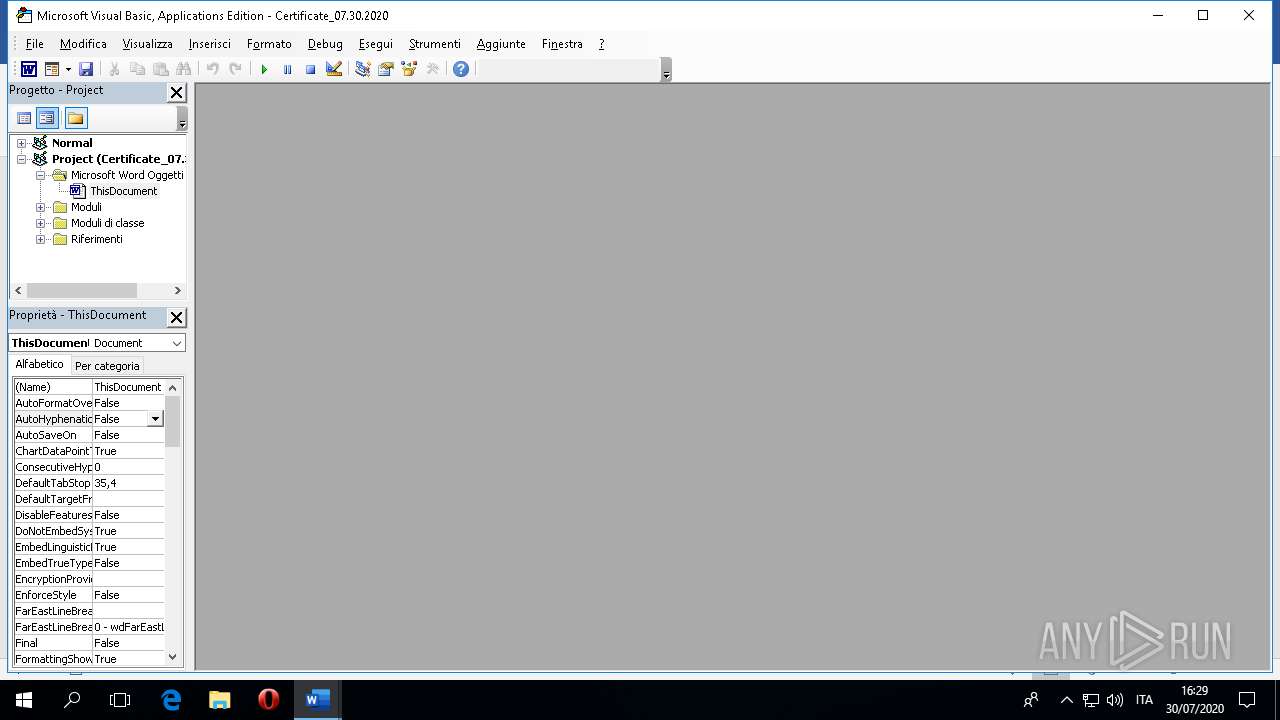
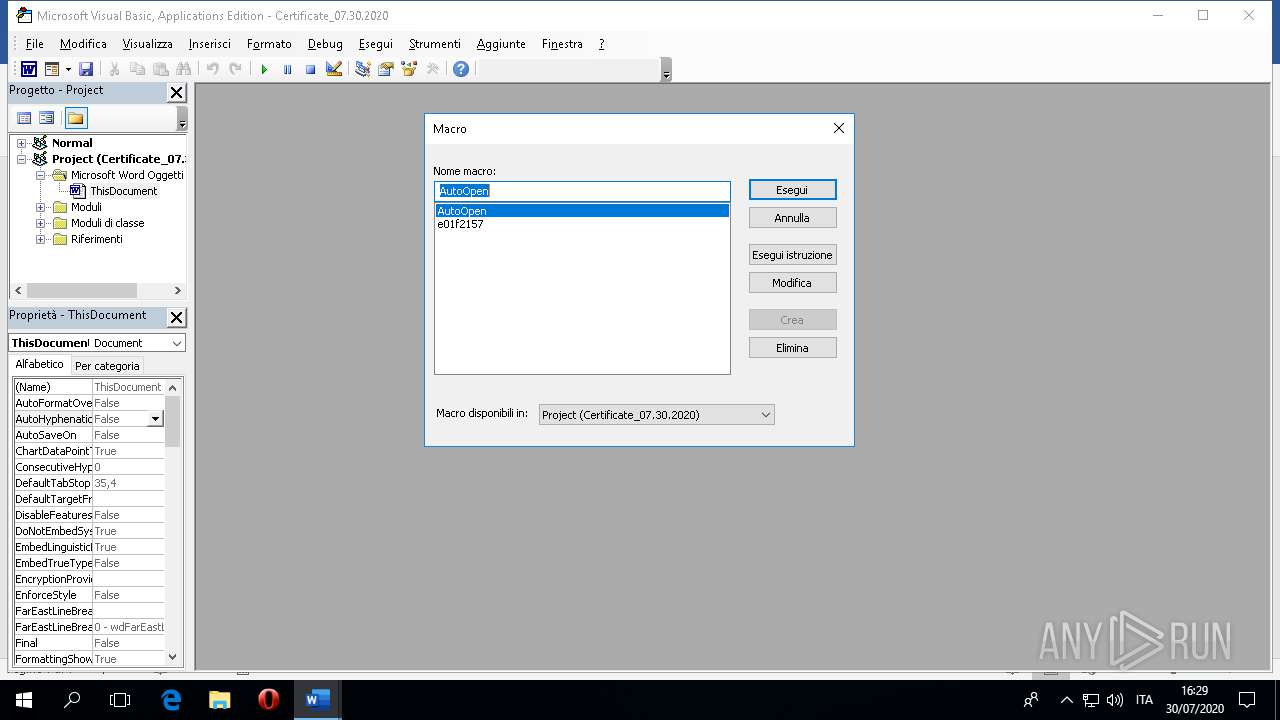
Executed via COM
- RuntimeBroker.exe (PID: 752)
- BackgroundTaskHost.exe (PID: 1060)
INFO
Scans artifacts that could help determine the target
- WINWORD.EXE (PID: 4612)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 4612)
Reads the software policy settings
- WINWORD.EXE (PID: 4612)
Reads Environment values
- WINWORD.EXE (PID: 4612)
Reads settings of System Certificates
- WINWORD.EXE (PID: 4612)
Creates files in the user directory
- WINWORD.EXE (PID: 4612)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x0c0cc35b |
| ZipCompressedSize: | 400 |
| ZipUncompressedSize: | 1505 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | Administrator |
| RevisionNumber: | 2 |
| CreateDate: | 2020:07:30 08:04:00Z |
| ModifyDate: | 2020:07:30 08:04:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | wyfioxhz |
| Description: | - |
Total processes
86
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | "C:\WINDOWS\system32\BackgroundTaskHost.exe" -ServerName:BackgroundTaskHost.WebAccountProvider | C:\WINDOWS\system32\BackgroundTaskHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Background Task Host Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
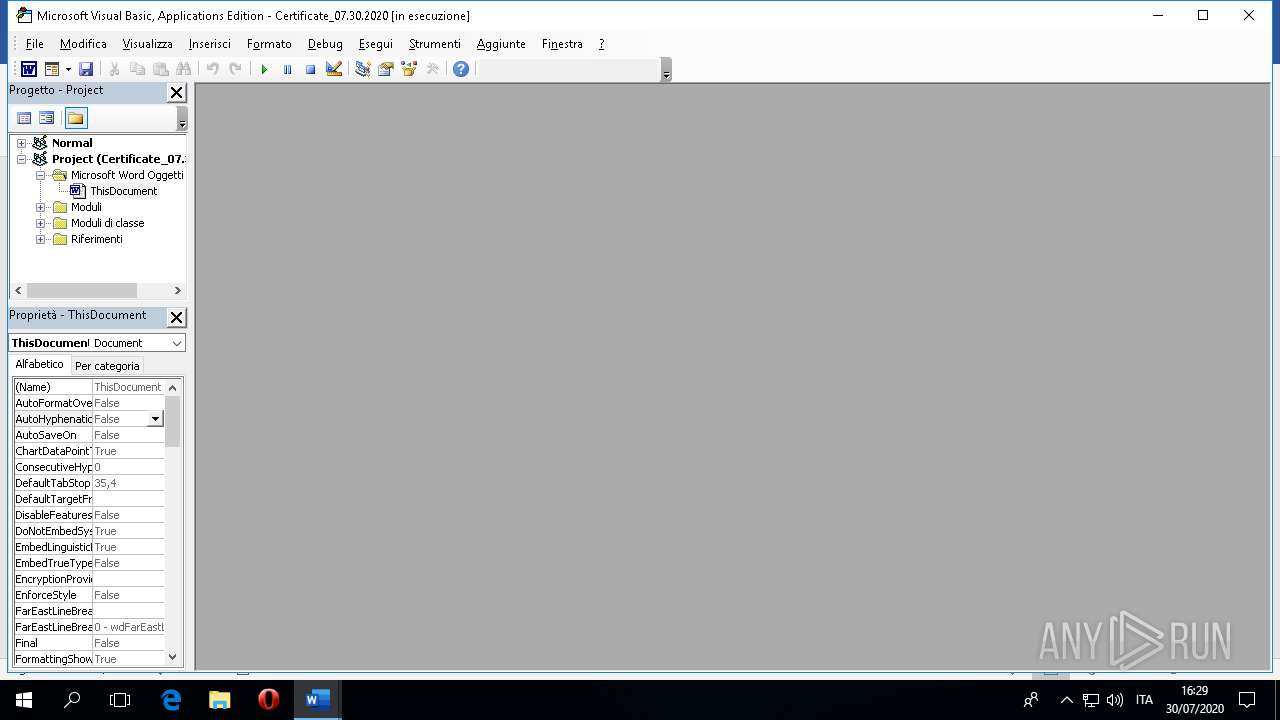
| 4612 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\certificate_07.30.2020.doc" /o "" | C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
Total events
2 385
Read events
2 093
Write events
278
Delete events
14
Modification events
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000284FFA2E02000000000000000500000000000000 | |||
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\CrashPersistence\WINWORD\4612 |
| Operation: | write | Name: | 0 |
Value: 0B0E10079DF3B0DF821248962B9738F50390BE230046E9B2DBBEDDCF99EB016A0410240044FA5D64A89E01008500A907556E6B6E6F776EC9062E2237746A7531514A7270614A676C575A3133564B5831454135496D464B2F5649644A30497A464862453674383D2200 | |||
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (4612) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
0
Suspicious files
21
Text files
9
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4612 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7COLPXCDG3XMUWAIUEPZ.temp | — | |
MD5:— | SHA256:— | |||
| 4612 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XJC7RS1NPATIIRKJRJ31.temp | — | |
MD5:— | SHA256:— | |||
| 4612 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4612 | WINWORD.EXE | C:\Users\admin\Desktop\~$rtificate_07.30.2020.doc | pgc | |
MD5:— | SHA256:— | |||
| 4612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\74a0ad00a184813f0b8867eb2f8dfef7227a18a4.tbres | binary | |
MD5:— | SHA256:— | |||
| 4612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\.ses | text | |
MD5:— | SHA256:— | |||
| 4612 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_BEB37ABADF39714871232B4792417E04 | binary | |
MD5:— | SHA256:— | |||
| 4612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\TCDD516.tmp\gosttitle.xsl | — | |
MD5:— | SHA256:— | |||
| 4612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\TCDD517.tmp\Equations.dotx | — | |
MD5:— | SHA256:— | |||
| 4612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\TCDD519.tmp\MS_MacDotsFaxCoverSheet.dotx | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
53
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4612 | WINWORD.EXE | GET | 404 | 185.144.29.2:80 | http://6kd743o1w.com/bolb/jaent.php?l=liut7.cab | RU | — | — | suspicious |
4612 | WINWORD.EXE | GET | 404 | 185.144.29.2:80 | http://6kd743o1w.com/bolb/jaent.php?l=liut7.cab | RU | — | — | suspicious |
4612 | WINWORD.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAiIzVJfGSRETRSlgpHeuVI%3D | US | der | 1.47 Kb | whitelisted |
4612 | WINWORD.EXE | GET | 200 | 2.23.95.104:80 | http://crl.microsoft.com/pki/crl/products/Microsoft%20Code%20Signing%20PCA(2).crl | unknown | der | 555 b | whitelisted |
4612 | WINWORD.EXE | GET | 200 | 2.23.95.104:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 555 b | whitelisted |
4612 | WINWORD.EXE | GET | 200 | 2.23.95.104:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
4612 | WINWORD.EXE | GET | 200 | 2.23.95.104:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4612 | WINWORD.EXE | 185.144.29.2:80 | 6kd743o1w.com | Chelyabinsk-Signal LLC | RU | suspicious |
4612 | WINWORD.EXE | 52.109.88.8:443 | officeclient.microsoft.com | Microsoft Corporation | NL | whitelisted |
— | — | 185.144.29.2:80 | 6kd743o1w.com | Chelyabinsk-Signal LLC | RU | suspicious |
4612 | WINWORD.EXE | 52.109.68.21:443 | roaming.officeapps.live.com | Microsoft Corporation | FR | whitelisted |
4612 | WINWORD.EXE | 2.23.108.120:443 | fs.microsoft.com | Akamai Technologies, Inc. | — | whitelisted |
4612 | WINWORD.EXE | 13.107.42.23:443 | config.edge.skype.com | Microsoft Corporation | US | suspicious |
4612 | WINWORD.EXE | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1076 | svchost.exe | 40.90.137.126:443 | login.live.com | Microsoft Corporation | US | unknown |
4612 | WINWORD.EXE | 52.109.76.122:443 | nleditor.osi.office.net | Microsoft Corporation | IE | suspicious |
4612 | WINWORD.EXE | 52.109.88.96:443 | messaging.office.com | Microsoft Corporation | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
6kd743o1w.com |
| suspicious |
roaming.officeapps.live.com |
| whitelisted |
config.edge.skype.com |
| malicious |
fs.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nleditor.osi.office.net |
| whitelisted |
login.live.com |
| whitelisted |
messaging.office.com |
| whitelisted |
templateservice.office.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report