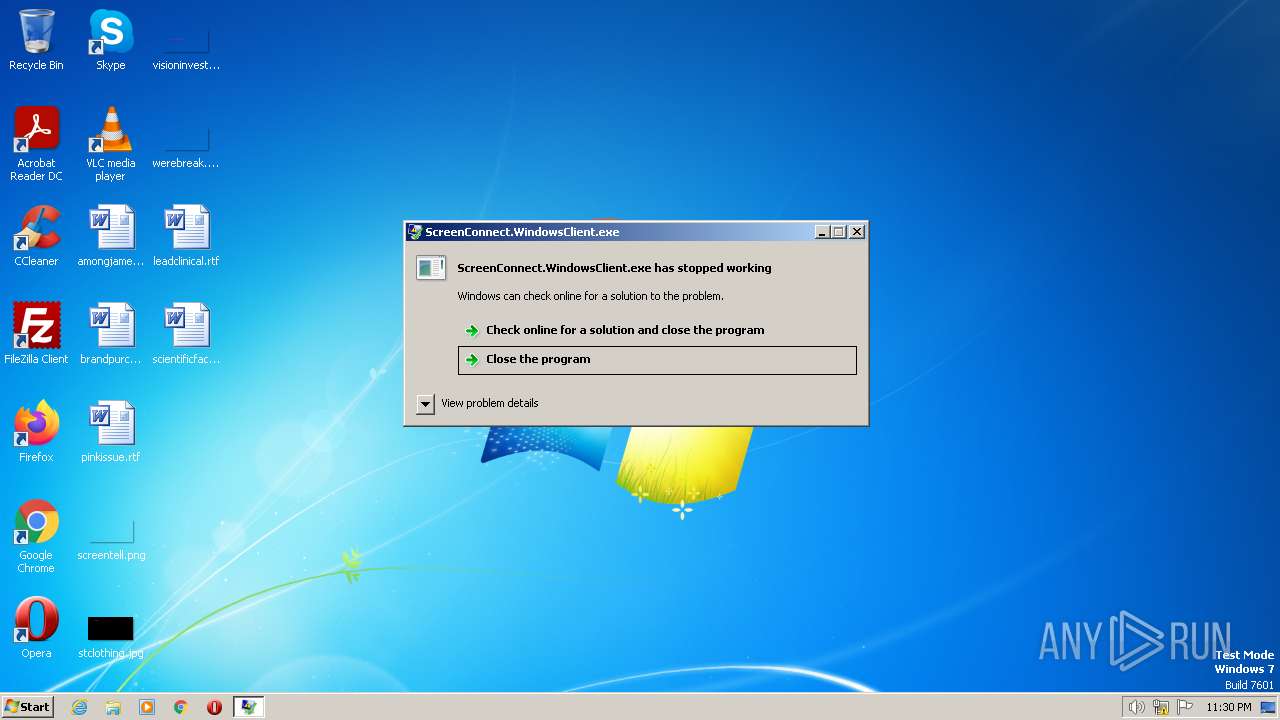
| File name: | ScreenConnect.WindowsClient.exe |
| Full analysis: | https://app.any.run/tasks/e9d4e40f-089d-4b3d-b8c1-6b83f938535a |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2023, 22:30:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 254A33EC9D5391577B95D2CEA3CF06D8 |
| SHA1: | A23587D95E94D7D5222B675867B3D525C2B4DB5F |
| SHA256: | 6BD3AB0299B3826E476461CAF1244E672D9F12858243921BEB3939134618B790 |
| SSDEEP: | 12288:8gLFQAXrjKm+PNopYY5A1NmOuccpIZU23dTQ4IY3es:8GrjKvFopYY5r9MUwdT9IYx |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- ScreenConnect.WindowsClient.exe (PID: 944)
Reads settings of System Certificates
- ScreenConnect.WindowsClient.exe (PID: 944)
Checks Windows Trust Settings
- ScreenConnect.WindowsClient.exe (PID: 944)
INFO
The process checks LSA protection
- ScreenConnect.WindowsClient.exe (PID: 944)
Reads the computer name
- ScreenConnect.WindowsClient.exe (PID: 944)
- dw20.exe (PID: 2996)
Checks supported languages
- ScreenConnect.WindowsClient.exe (PID: 944)
- dw20.exe (PID: 2996)
Reads the machine GUID from the registry
- ScreenConnect.WindowsClient.exe (PID: 944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| AssemblyVersion: | 23.2.9.8466 |
|---|---|
| ProductVersion: | 23.2.9.8466 |
| ProductName: | ScreenConnect |
| OriginalFileName: | ScreenConnect.WindowsClient.exe |
| LegalCopyright: | |
| InternalName: | ScreenConnect.WindowsClient.exe |
| FileVersion: | 23.2.9.8466 |
| FileDescription: | |
| CompanyName: | ScreenConnect Software |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 23.2.9.8466 |
| FileVersionNumber: | 23.2.9.8466 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x8af36 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1536 |
| CodeSize: | 562688 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, Large address aware |
| TimeStamp: | 2054:02:17 06:41:41+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Feb-2054 06:41:41 |
| CompanyName: | ScreenConnect Software |
| FileDescription: | - |
| FileVersion: | 23.2.9.8466 |
| InternalName: | ScreenConnect.WindowsClient.exe |
| LegalCopyright: | - |
| OriginalFilename: | ScreenConnect.WindowsClient.exe |
| ProductName: | ScreenConnect |
| ProductVersion: | 23.2.9.8466 |
| Assembly Version: | 23.2.9.8466 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 17-Feb-2054 06:41:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00089504 | 0x00089600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.12132 |
.rsrc | 0x0008C000 | 0x00000394 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.01158 |
.reloc | 0x0008E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40638 | 824 | UNKNOWN | UNKNOWN | RT_VERSION |
Imports
mscoree.dll |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Users\admin\AppData\Local\Temp\ScreenConnect.WindowsClient.exe" | C:\Users\admin\AppData\Local\Temp\ScreenConnect.WindowsClient.exe | explorer.exe | ||||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: Exit code: 0 Version: 23.2.9.8466 Modules
| |||||||||||||||
| 2996 | dw20.exe -x -s 880 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | ScreenConnect.WindowsClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
Total events
6 420
Read events
6 380
Write events
36
Delete events
4
Modification events
| (PID) Process: | (944) ScreenConnect.WindowsClient.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (944) ScreenConnect.WindowsClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\DDFB16CD4931C973A2037D3FC83A4D7D775D05E4 |
| Operation: | write | Name: | Blob |
Value: 090000000100000034000000303206082B0601050507030206082B0601050507030306082B0601050507030406082B0601050507030106082B06010505070308190000000100000010000000FFAC207997BB2CFE865570179EE037B90B00000001000000320000004400690067006900430065007200740020005400720075007300740065006400200052006F006F0074002000470034000000620000000100000020000000552F7BDCF1A7AF9E6CE672017F4F12ABF77240C78E761AC203D1D9D20AC89988140000000100000014000000ECD7E382D2715D644CDF2E673FE7BA98AE1C0F4F1D0000000100000010000000A86DC6A233EB339610F3ED414927C559030000000100000014000000DDFB16CD4931C973A2037D3FC83A4D7D775D05E40F00000001000000300000004EA1B34B10B982A96A38915843507820AD632C6AAD8343E337B34D660CD8366FA154544AE80668AE1FDF3931D57E1996530000000100000040000000303E301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C02000000001000000940500003082059030820378A0030201020210059B1B579E8E2132E23907BDA777755C300D06092A864886F70D01010C05003062310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D3121301F060355040313184469676943657274205472757374656420526F6F74204734301E170D3133303830313132303030305A170D3338303131353132303030305A3062310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D3121301F060355040313184469676943657274205472757374656420526F6F7420473430820222300D06092A864886F70D01010105000382020F003082020A0282020100BFE6907368DEBBE45D4A3C3022306933ECC2A7252EC9213DF28AD859C2E129A73D58AB769ACDAE7B1B840DC4301FF31BA43816EB56C6976D1DABB279F2CA11D2E45FD6053C520F521FC69E15A57EBE9FA95716595572AF689370C2B2BA75996A733294D11044102EDF82F30784E6743B6D71E22D0C1BEE20D5C9201D63292DCEEC5E4EC893F821619B34EB05C65EEC5B1ABCEBC9CFCDAC34405FB17A66EE77C848A86657579F54588E0C2BB74FA730D956EECA7B5DE3ADC94F5EE535E731CBDA935EDC8E8F80DAB69198409079C378C7B6B1C4B56A183803108DD8D437A42E057D88F5823E109170AB55824132D7DB04732A6E91017C214CD4BCAE1B03755D7866D93A31449A3340BF08D75A49A4C2E6A9A067DDA427BCA14F39B5115817F7245C468F64F7C169887698763D595D4276878997697A48F0E0A2121B669A74CADE4B1EE70E63AEE6D4EF92923A9E3DDC00E4452589B69A44192B7EC094B4D2616DEB33D9C5DF4B0400CC7D1C95C38FF721B2B211B7BB7FF2D58C702C4160AAB1631844951A76627EF680B0FBE864A633D18907E1BDB7E643A418B8A67701E10F940C211DB2542925896CE50E52514774BE26ACB64175DE7AAC5F8D3FC9BCD34111125BE51050EB31C5CA72162209DF7C4C753F63EC215FC420516B6FB1AB868B4FC2D6455F9D20FCA11EC5C08FA2B17E0A2699F5E4692F981D2DF5D9A9B21DE51B0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020186301D0603551D0E04160414ECD7E382D2715D644CDF2E673FE7BA98AE1C0F4F300D06092A864886F70D01010C05000382020100BB61D97DA96CBE17C4911BC3A1A2008DE364680F56CF77AE70F9FD9A4A99B9C9785C0C0C5FE4E61429560B36495D4463E0AD9C9618661B230D3D79E96D6BD654F8D23CC14340AE1D50F552FC903BBB9899696BC7C1A7A868A427DC9DF927AE3085B9F6674D3A3E8F5939225344EBC85D03CAED507A7D62210A80C87366D1A005605FE8A5B4A7AFA8F76D359C7C5A8AD6A23899F3788BF44DD2200BDE04EE8C9B4781720DC01432EF30592EAEE071F256E46A976F92506D968D687A9AB236147A06F224B9091150D708B1B8897A8423614229E5A3CDA22041D7D19C64D9EA26A18B14D74C19B25041713D3F4D7023860C4ADC81D2CC3294840D0809971C4FC0EE6B207430D2E03934108521150108E85532DE7149D92817504DE6BE4DD175ACD0CAFB41B843A5AAD3C305444F2C369BE2FAE245B823536C066F67557F46B54C3F6E285A7926D2A4A86297D21EE2ED4A8BBC1BFD474A0DDF67667EB25B41D03BE4F43BF40463E9EFC2540051A08A2AC9CE78CCD5EA870418B3CEAF4988AFF39299B6B3E6610FD28500E7501AE41B959D19A1B99CB19BB1001EEFD00F4F426CC90ABCEE43FA3A71A5C84D26A535FD895DBC85621D32D2A02B54ED9A57C1DBFA10CF19B78B4A1B8F01B6279553E8B6896D5BBC68D423E88B51A256F9F0A680A0D61EB3BC0F0F537529AAEA1377E4DE8C8121AD07104711AD873D07D175BCCFF3667E | |||
| (PID) Process: | (944) ScreenConnect.WindowsClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\DDFB16CD4931C973A2037D3FC83A4D7D775D05E4 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report