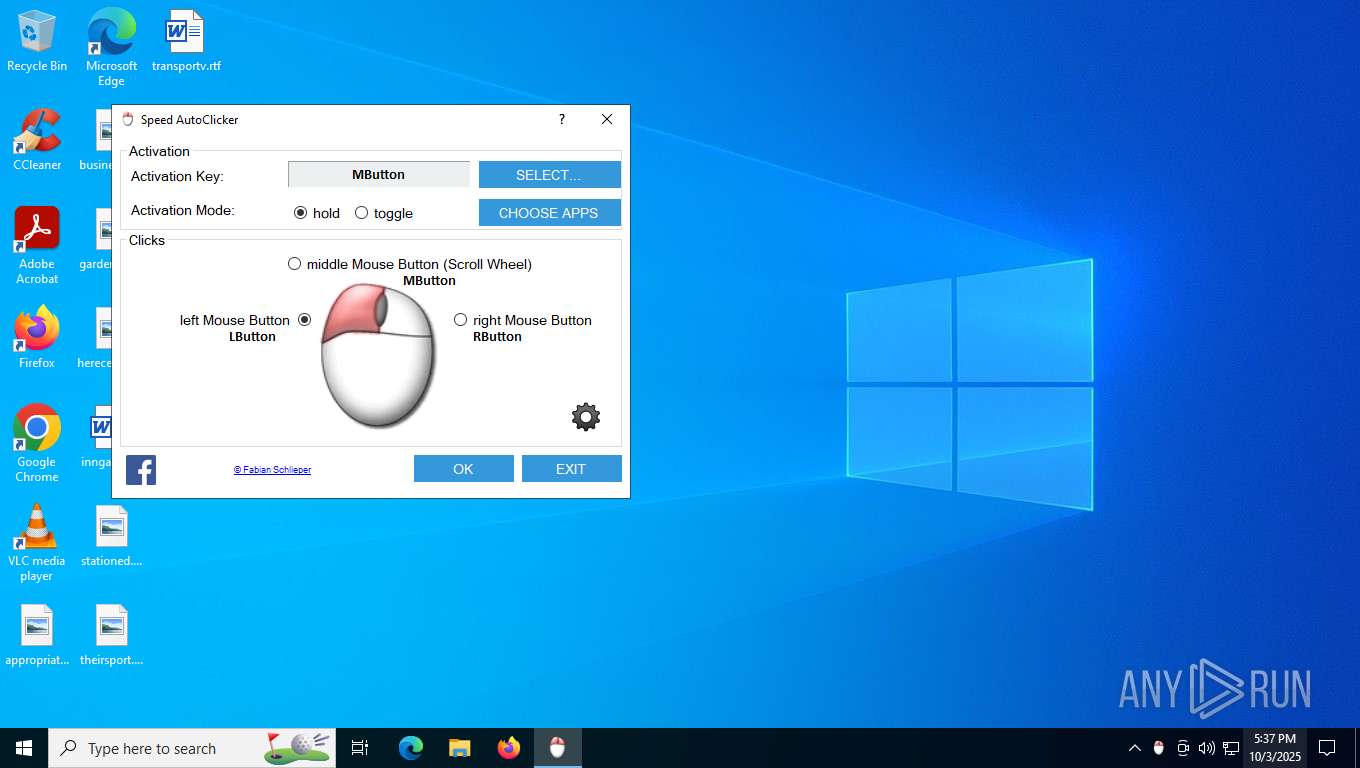
| File name: | SpeedAutoClicker.exe |
| Full analysis: | https://app.any.run/tasks/5af6b4ee-e5ef-4adc-b244-510f7762b595 |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2025, 17:37:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | B3A2E60B9CF66A908FBC22FEC9A5F398 |
| SHA1: | 7E8BC7E0E0C7DE380E1B5D6565BD9258317E80F5 |
| SHA256: | 6BC32E935A514DA31E6ED5559252C36D82FD64B1E6403748B0BA86598EF20071 |
| SSDEEP: | 49152:ypJWi2J3Y2ptHEAz+axysYC6syUkoPaPS2AJNyxUP+MkZBFj:22Jo2rytClVkoOSfJNAUWJ3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- SpeedAutoClicker.exe (PID: 7560)
Reads Internet Explorer settings
- SpeedAutoClicker.exe (PID: 7560)
INFO
Reads the machine GUID from the registry
- SpeedAutoClicker.exe (PID: 7560)
Checks supported languages
- SpeedAutoClicker.exe (PID: 7560)
Creates files in the program directory
- SpeedAutoClicker.exe (PID: 7560)
Reads the computer name
- SpeedAutoClicker.exe (PID: 7560)
Reads Environment values
- SpeedAutoClicker.exe (PID: 7560)
Creates files or folders in the user directory
- SpeedAutoClicker.exe (PID: 7560)
Disables trace logs
- SpeedAutoClicker.exe (PID: 7560)
Checks proxy server information
- SpeedAutoClicker.exe (PID: 7560)
- slui.exe (PID: 7440)
Reads the software policy settings
- SpeedAutoClicker.exe (PID: 7560)
- slui.exe (PID: 7440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:05 07:17:50+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 2174976 |
| InitializedDataSize: | 56832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x214e0e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.2.0 |
| ProductVersionNumber: | 1.6.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | fabi.me |
| FileDescription: | Speed AutoClicker |
| FileVersion: | 1.6.2.0 |
| InternalName: | SpeedAutoClicker.exe |
| LegalCopyright: | © 2019 Fabian Schlieper |
| LegalTrademarks: | - |
| OriginalFileName: | SpeedAutoClicker.exe |
| ProductName: | Speed AutoClicker |
| ProductVersion: | 1.6.2.0 |
| AssemblyVersion: | 1.6.2.0 |
Total processes
158
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7440 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7560 | "C:\Users\admin\Desktop\SpeedAutoClicker.exe" | C:\Users\admin\Desktop\SpeedAutoClicker.exe | explorer.exe | ||||||||||||
User: admin Company: fabi.me Integrity Level: MEDIUM Description: Speed AutoClicker Version: 1.6.2.0 Modules
| |||||||||||||||
Total events
7 772
Read events
7 748
Write events
23
Delete events
1
Modification events
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\SpeedAutoClicker_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\SpeedAutoClicker_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\SpeedAutoClicker_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\SpeedAutoClicker_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7560) SpeedAutoClicker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\SpeedAutoClicker_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7560 | SpeedAutoClicker.exe | C:\Users\admin\AppData\Local\fabi.me\ac.config | xml | |
MD5:D4A9C55E2EB5FA765D1BE883B19F5DF0 | SHA256:69CCC597449CE2E3A24A0619E7F1E3C4D765B2AB84AC20B9FA54141446972E90 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
14
DNS requests
6
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 4.154.209.85:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | unknown |
— | — | POST | 500 | 4.154.209.85:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | unknown |
— | — | GET | 401 | 85.13.164.70:443 | https://fabi.me/wp-json/wp/v2/wpfb-files/876 | DE | binary | 125 b | unknown |
— | — | GET | 200 | 85.13.164.70:443 | https://fabi.me/wp-json/wp/v2/wpfb-files/713 | DE | binary | 1.54 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6016 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
8108 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7560 | SpeedAutoClicker.exe | 85.13.164.70:443 | fabi.me | Neue Medien Muennich GmbH | DE | suspicious |
6016 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5948 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4256 | slui.exe | 4.154.209.85:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7440 | slui.exe | 4.154.209.85:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
fabi.me |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | A Network Trojan was detected | ET HUNTING Terse Request for WordPress Site ending in all digits |
— | — | A Network Trojan was detected | ET HUNTING Terse Request for WordPress Site ending in all digits |
— | — | A Network Trojan was detected | ET HUNTING Terse Request for WordPress Site ending in all digits |
— | — | A Network Trojan was detected | ET HUNTING Terse Request for WordPress Site ending in all digits |