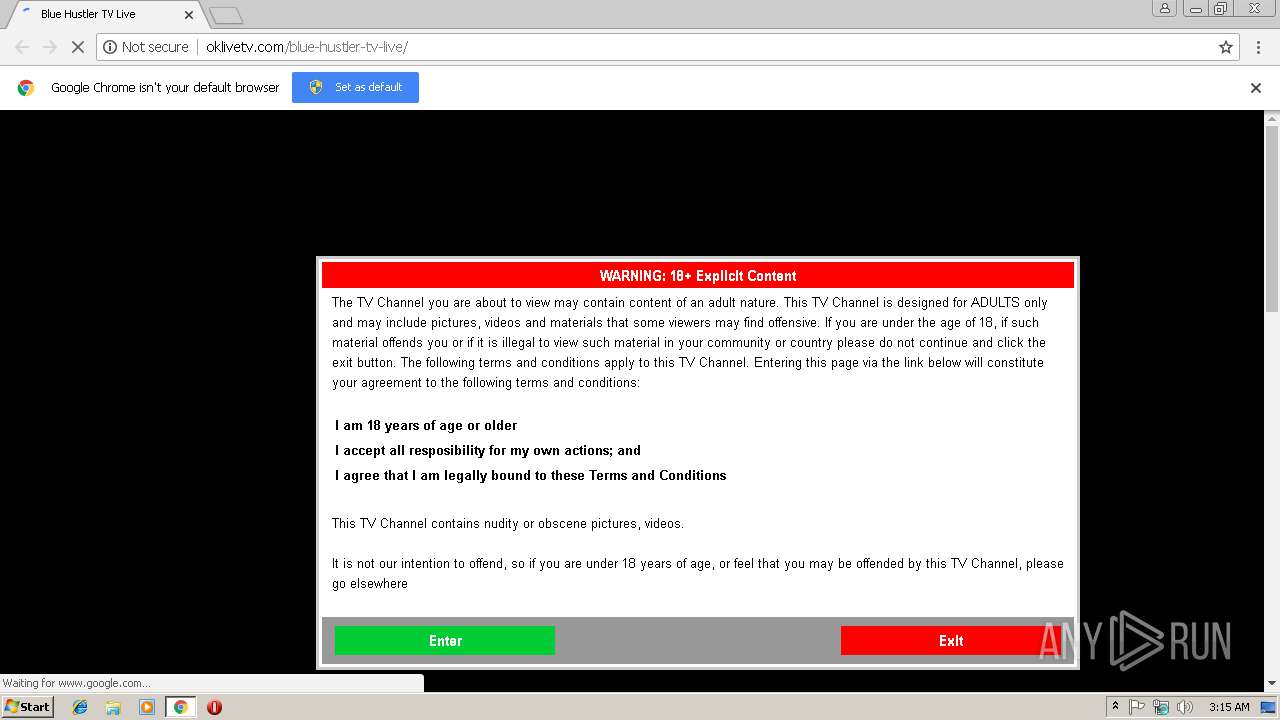
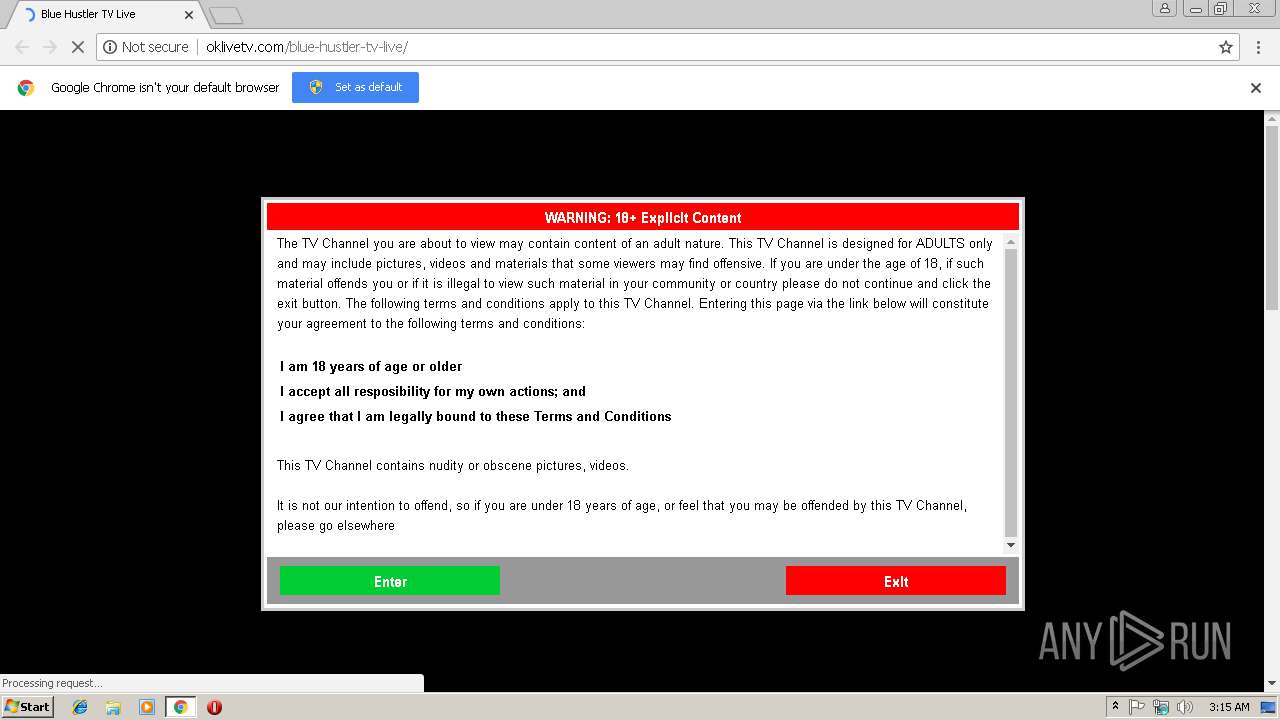
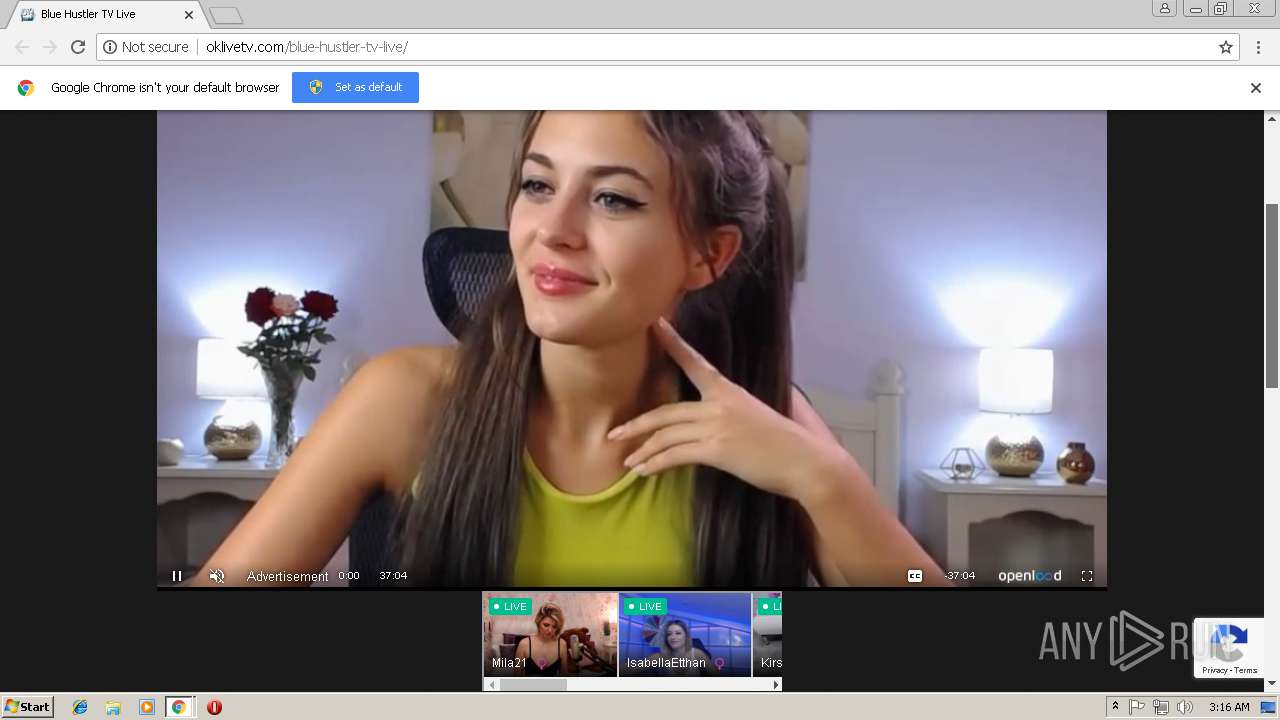
| URL: | http://oklivetv.com/blue-hustler-tv-live/ |
| Full analysis: | https://app.any.run/tasks/802f4fcd-4753-494e-8f87-e175c5416ab9 |
| Verdict: | Malicious activity |
| Analysis date: | March 06, 2019, 03:15:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 38AEBE65DE9F601BF80BB24763E5AFB9 |
| SHA1: | 8C84795A7125714F5C1A9620DC0D16CC061C1D34 |
| SHA256: | 6BB70F97C5F05DB743F27BD7CA9CFEE0E412676D7486B7784D2CD26757EAD2A9 |
| SSDEEP: | 3:N1KROJ9mKILCw7:Co7mKQJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 3260)
Dropped object may contain TOR URL's
- chrome.exe (PID: 3260)
Application launched itself
- chrome.exe (PID: 3260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D24AAD625AB16B6FA0E38663173B429A --mojo-platform-channel-handle=992 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5BD9FCC7C34DE03D11F9FBB31D92CCFE --mojo-platform-channel-handle=4052 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --service-pipe-token=BA9BD930A5890A3E39150447521DBC3E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=BA9BD930A5890A3E39150447521DBC3E --renderer-client-id=4 --mojo-platform-channel-handle=1868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3264 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://oklivetv.com/blue-hustler-tv-live/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=E4100A5D38CD2E322E75685034DF928F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E4100A5D38CD2E322E75685034DF928F --renderer-client-id=7 --mojo-platform-channel-handle=3280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --service-pipe-token=4FF06B6EAE765D4E6A9019CAB33F4FBE --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4FF06B6EAE765D4E6A9019CAB33F4FBE --renderer-client-id=3 --mojo-platform-channel-handle=2044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=2EBA479942E7243F3DAAA92DADD4F74E --mojo-platform-channel-handle=4484 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=82B127C779A0C4B324CDBFB69D938A89 --mojo-platform-channel-handle=4716 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
618
Read events
569
Write events
46
Delete events
3
Modification events
| (PID) Process: | (3260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3260-13196315729644750 |
Value: 259 | |||
| (PID) Process: | (3260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3260) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3260-13196315729644750 |
Value: 259 | |||
| (PID) Process: | (3260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
46
Text files
611
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\990d5da7-0433-4b62-8a46-e8180ccbbc62.tmp | — | |
MD5:— | SHA256:— | |||
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cee1cf02-ffe5-4ce3-a24a-e8677c31aa2c.tmp | — | |
MD5:— | SHA256:— | |||
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF19862e.TMP | text | |
MD5:— | SHA256:— | |||
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19865c.TMP | text | |
MD5:— | SHA256:— | |||
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF19865c.TMP | text | |
MD5:— | SHA256:— | |||
| 3260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
120
TCP/UDP connections
142
DNS requests
81
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/wp-content/plugins/facebook-page-promoter-lightbox/includes/featherlight/featherlight.min.css?ver=5.0.3 | US | text | 701 b | suspicious |
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/blue-hustler-tv-live/ | US | html | 19.8 Kb | suspicious |
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/wp-content/themes/oklivetv/responsive.css?ver=1.4.3 | US | text | 1.42 Kb | suspicious |
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/wp-content/themes/oklivetv/style.css?ver=1.4.3 | US | text | 10.6 Kb | suspicious |
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/wp-content/uploads/YrjuJXUfUrZC/yixZMCbXxzDo.css?ver=2.2.3 | US | text | 1018 b | suspicious |
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/wp-content/plugins/facebook-page-promoter-lightbox/includes/featherlight/featherlight.min.js?ver=5.0.3 | US | text | 3.47 Kb | suspicious |
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/wp-content/plugins/facebook-page-promoter-lightbox/includes/launch/launch.min.js?ver=5.0.3 | US | text | 897 b | suspicious |
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/wp-content/plugins/advanced-ads-slider/public/assets/js/jquery.event.move.js?ver=1.1.2 | US | text | 2.13 Kb | suspicious |
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/wp-content/plugins/advanced-ads-slider/public/assets/js/jquery.event.swipe.js?ver=1.1.2 | US | text | 617 b | suspicious |
3260 | chrome.exe | GET | 200 | 104.18.55.132:80 | http://oklivetv.com/wp-content/themes/oklivetv/js/modernizr.min.js?ver=2.6.2 | US | html | 5.45 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3260 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3260 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3260 | chrome.exe | 104.18.55.132:80 | oklivetv.com | Cloudflare Inc | US | shared |
3260 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3260 | chrome.exe | 31.13.90.6:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3260 | chrome.exe | 205.185.208.52:80 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
3260 | chrome.exe | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3260 | chrome.exe | 104.16.89.20:80 | cdn.jsdelivr.net | Cloudflare Inc | US | shared |
3260 | chrome.exe | 104.16.89.20:443 | cdn.jsdelivr.net | Cloudflare Inc | US | shared |
3260 | chrome.exe | 216.58.206.10:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
oklivetv.com |
| suspicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.google.com |
| malicious |
ads.exosrv.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s.w.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3260 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3260 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3260 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3260 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |