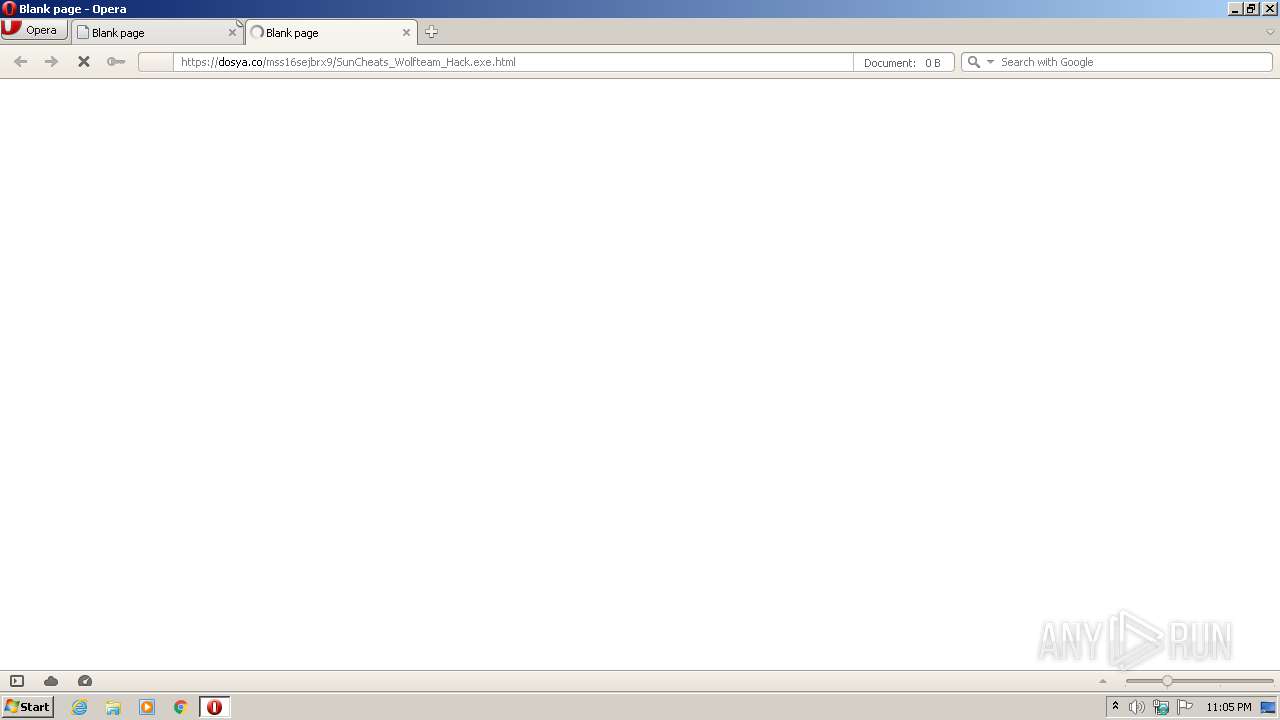
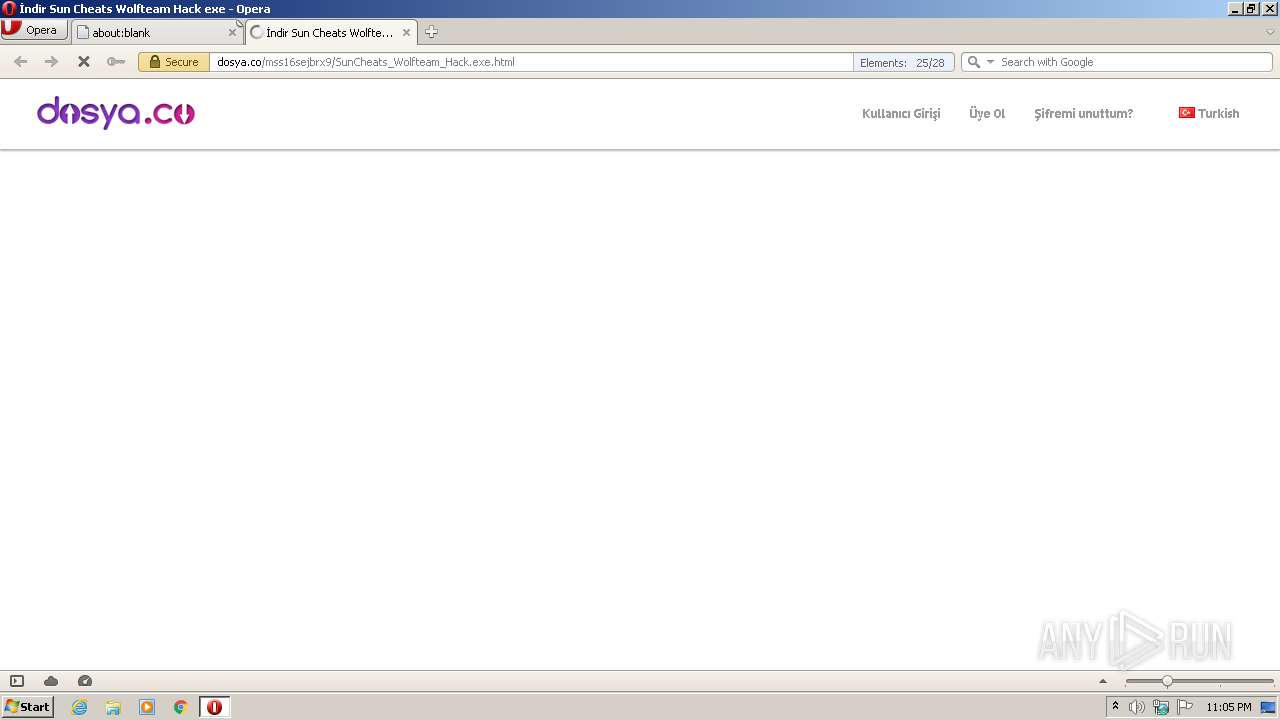
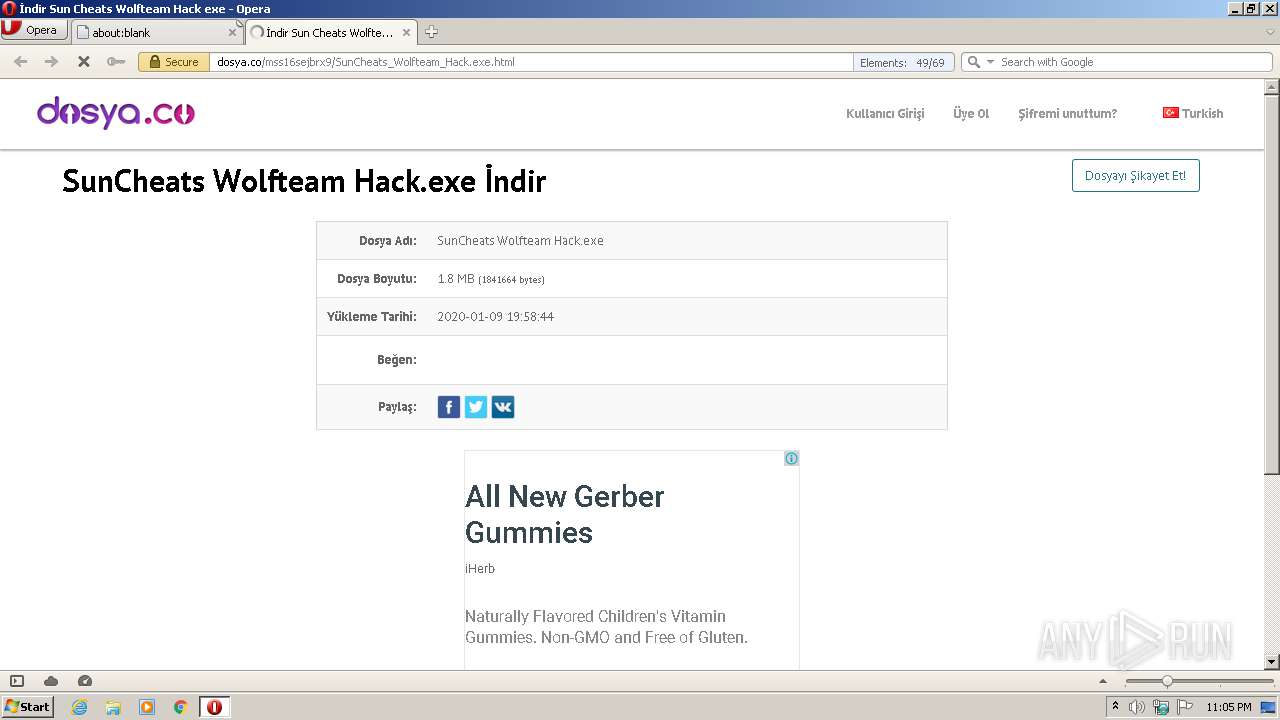
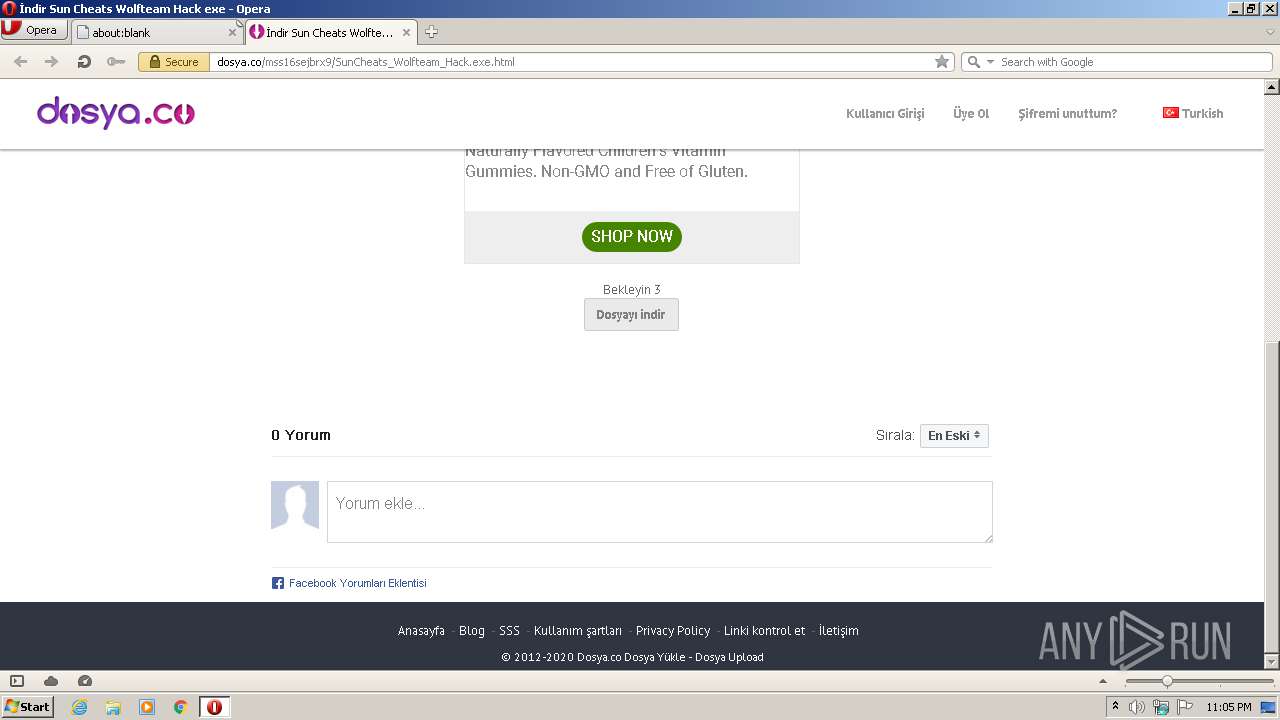
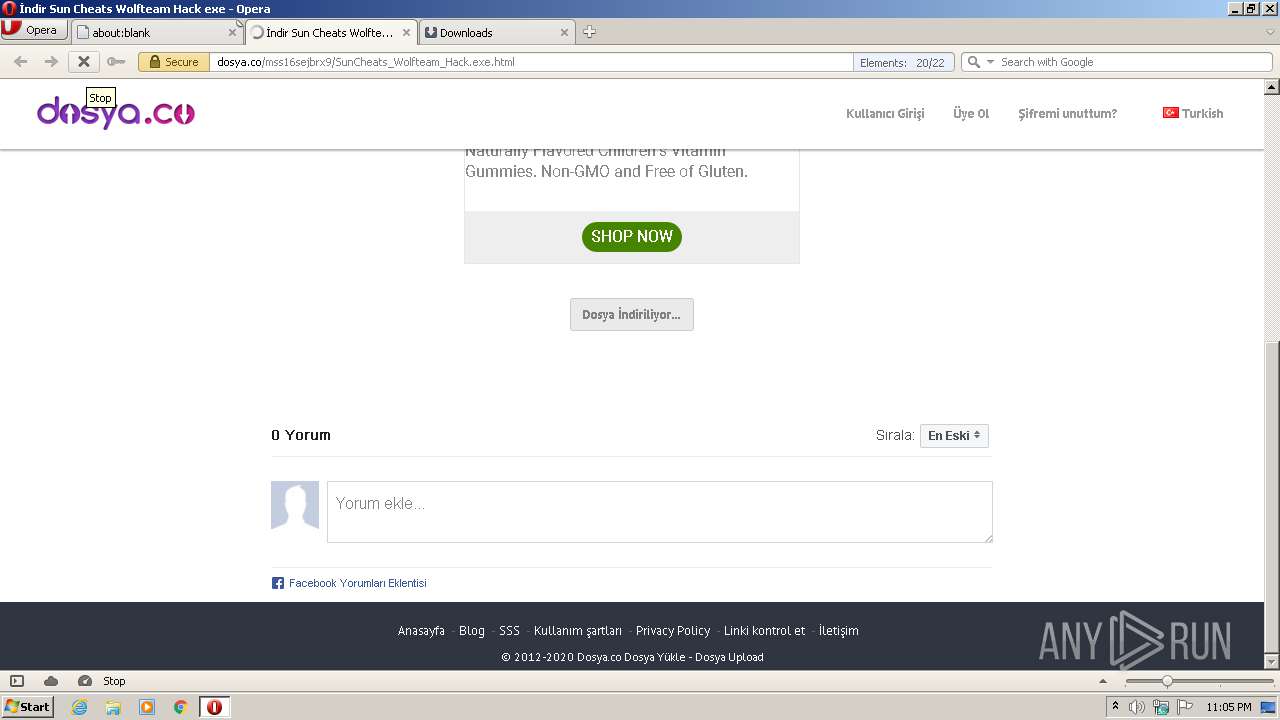
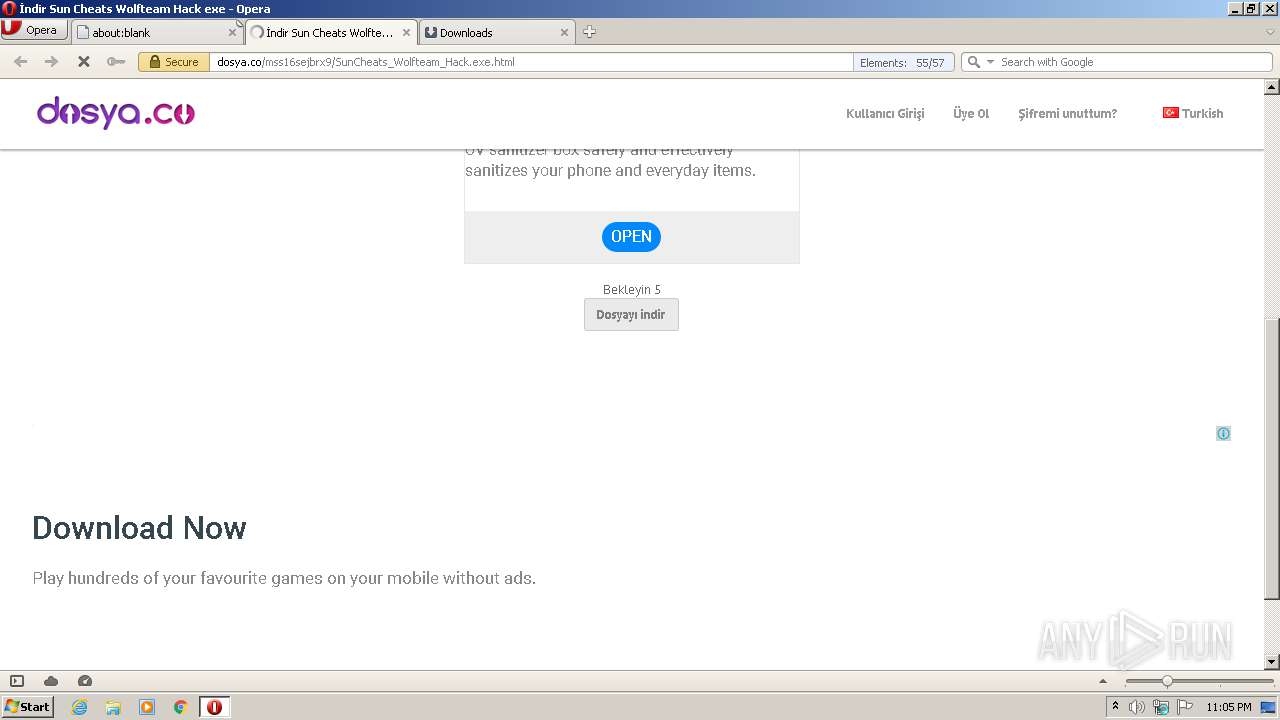
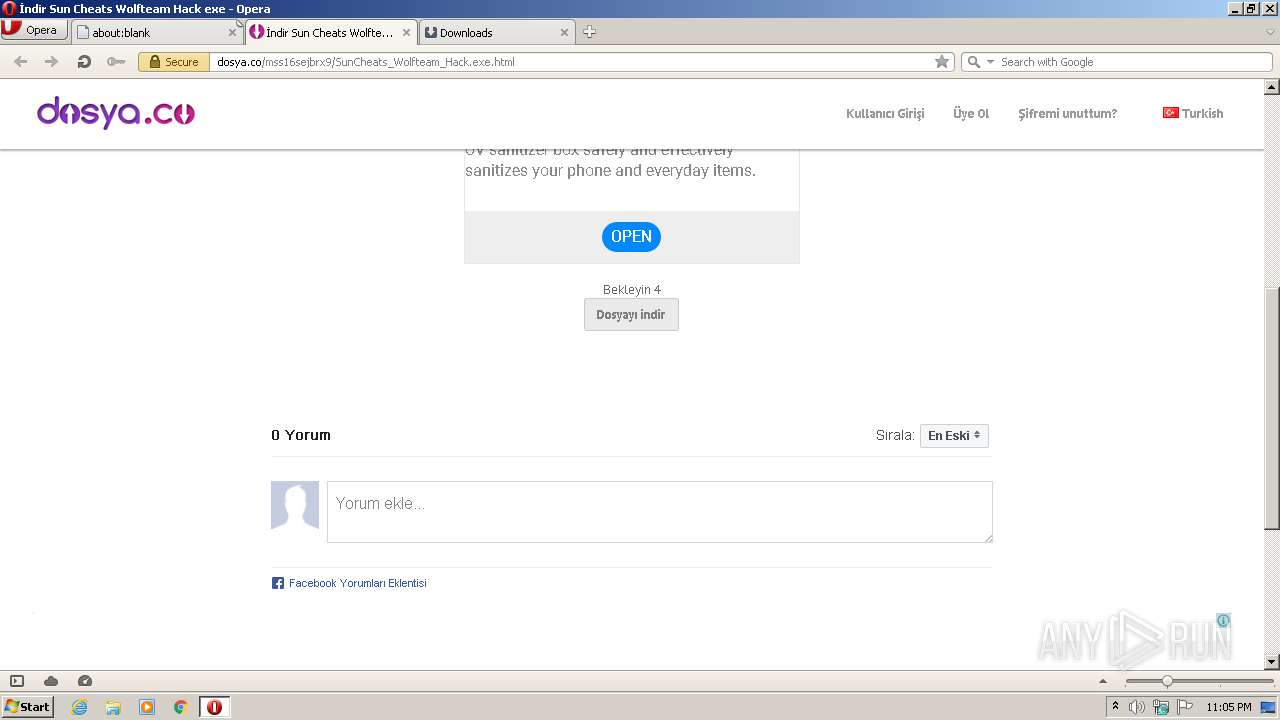
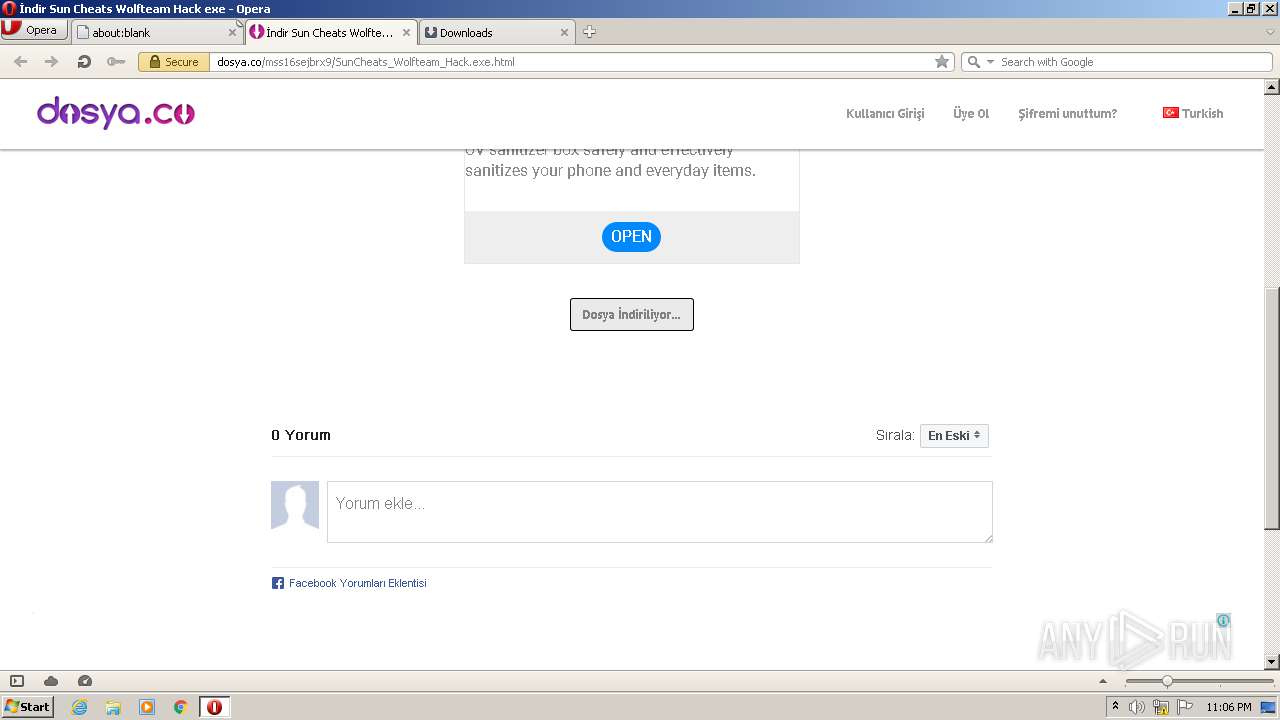
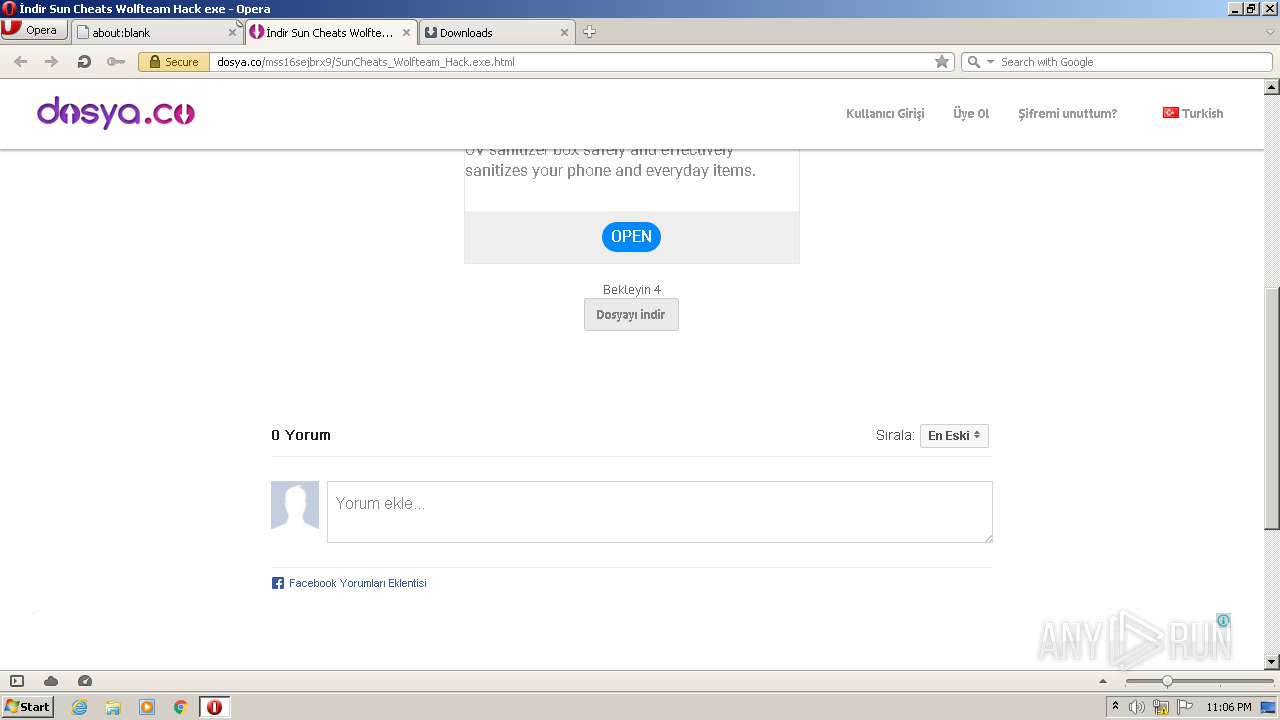
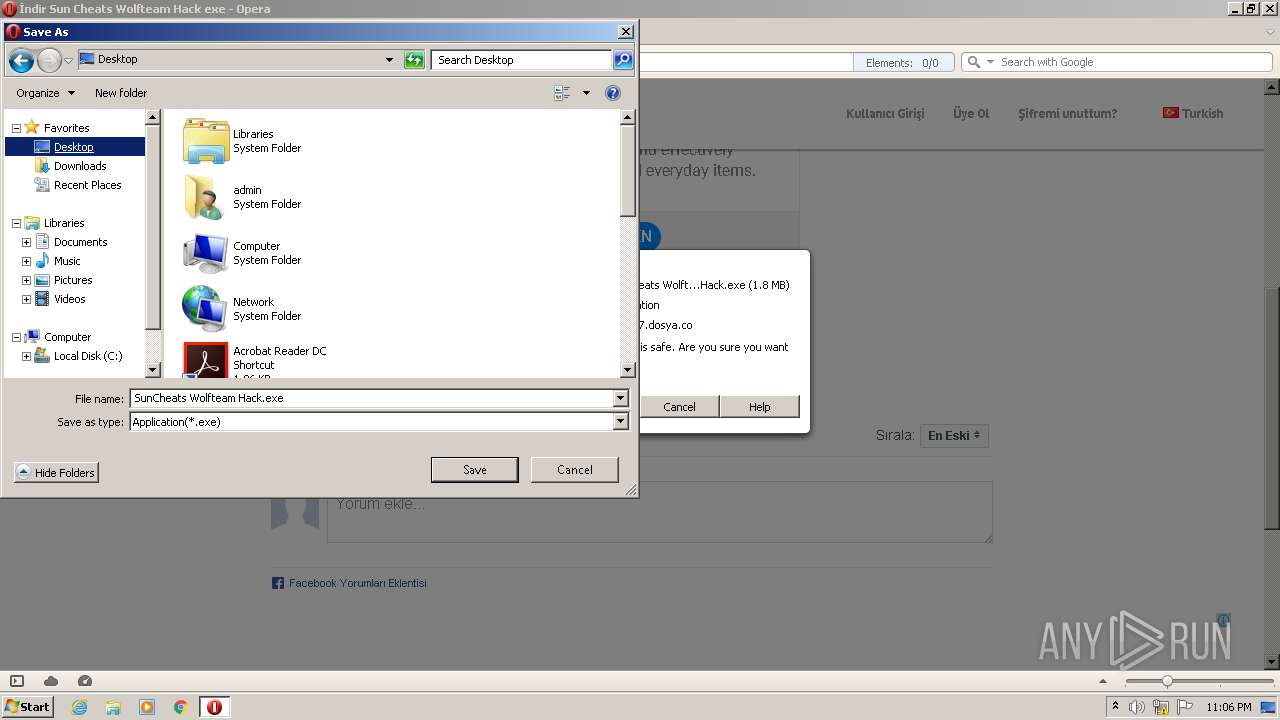
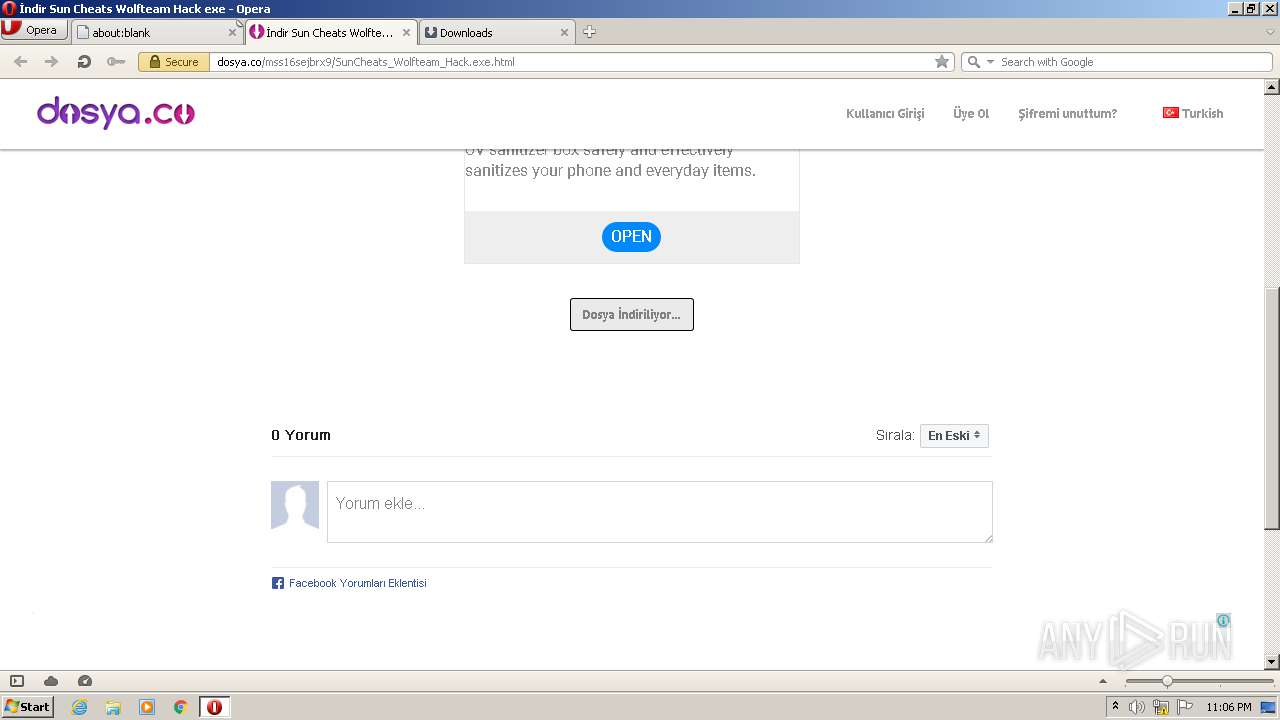
| URL: | https://dosya.co/mss16sejbrx9/SunCheats_Wolfteam_Hack.exe.html |
| Full analysis: | https://app.any.run/tasks/aab3fb7d-a5df-4ed8-ad30-b68e6d4e8251 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 22:04:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | ECAC8F8B0C8057C18B48B9596042EAAC |
| SHA1: | 239DDE47B67AB929150A6074F9CD3274223882A4 |
| SHA256: | 6BAD9B84B849B66B383D864B32B24A28E0792956107A31B727E34567EE368746 |
| SSDEEP: | 3:N8SgLddS/OJhw6ZcEHhOJ5G:2S826nHYW |
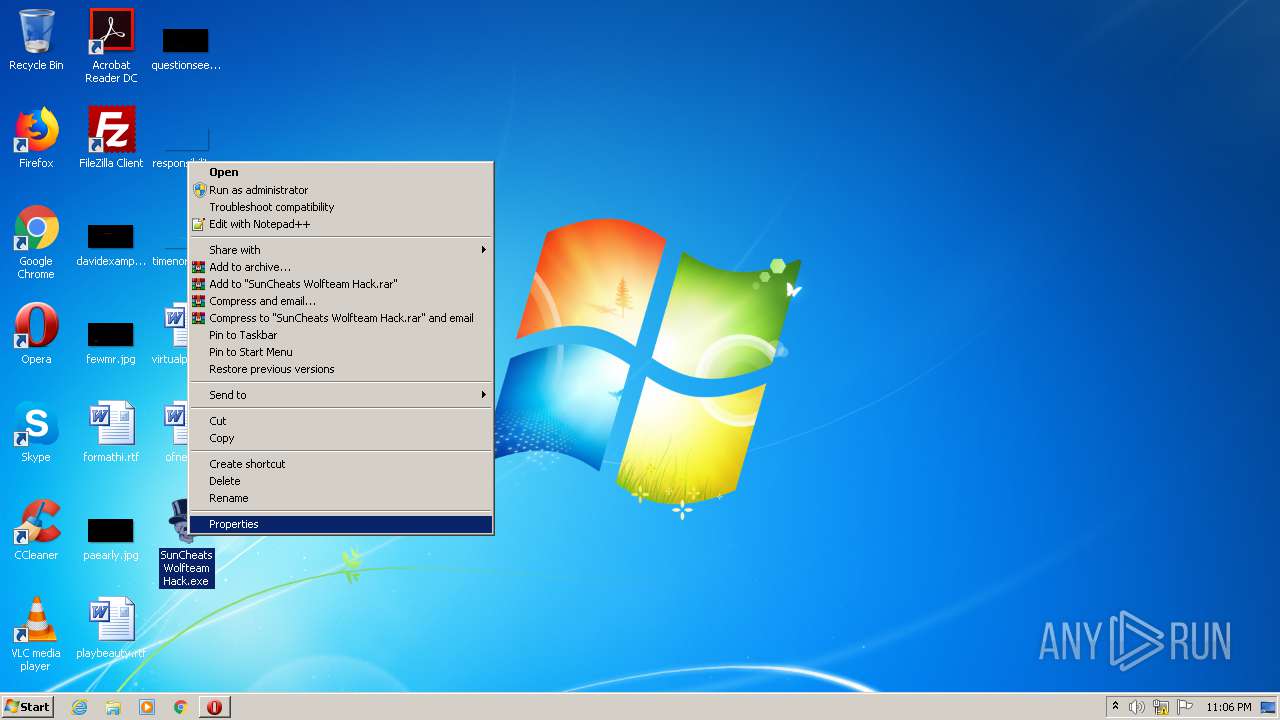
MALICIOUS
Application was dropped or rewritten from another process
- SunCheats Wolfteam Hack.exe (PID: 2480)
- SunCheats Wolfteam Hack.exe (PID: 348)
SUSPICIOUS
Executable content was dropped or overwritten
- opera.exe (PID: 1980)
INFO
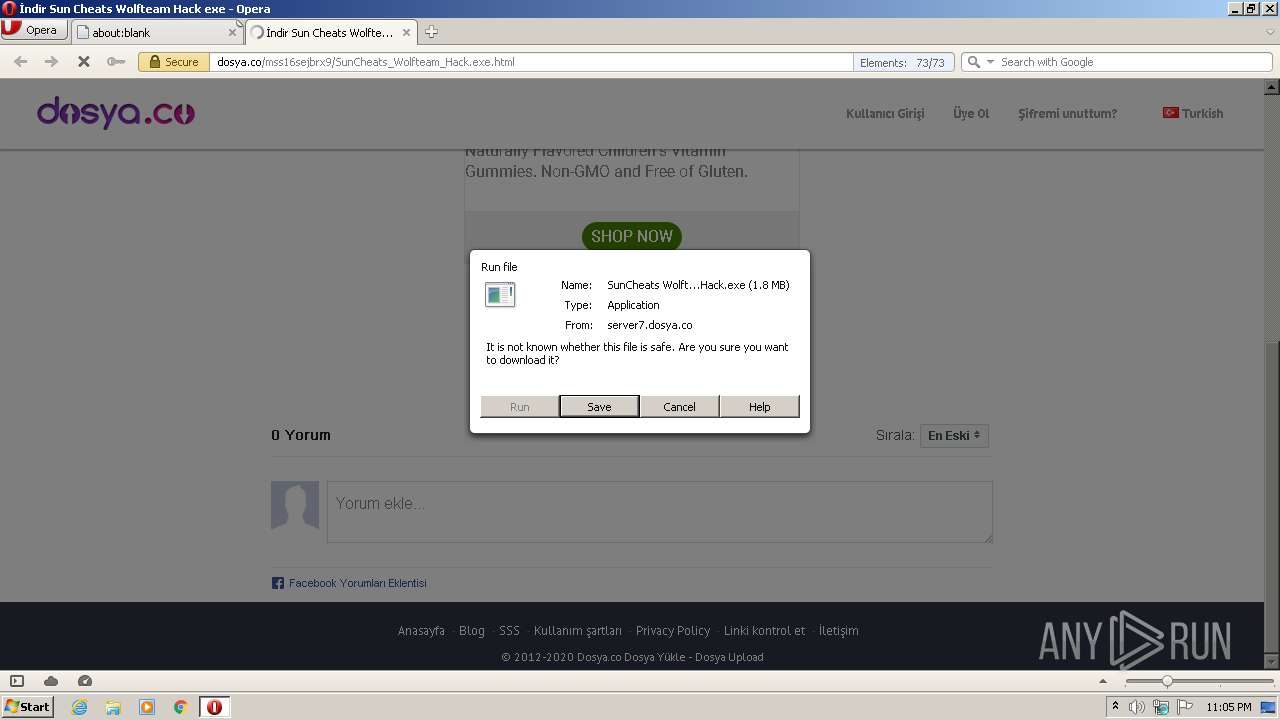
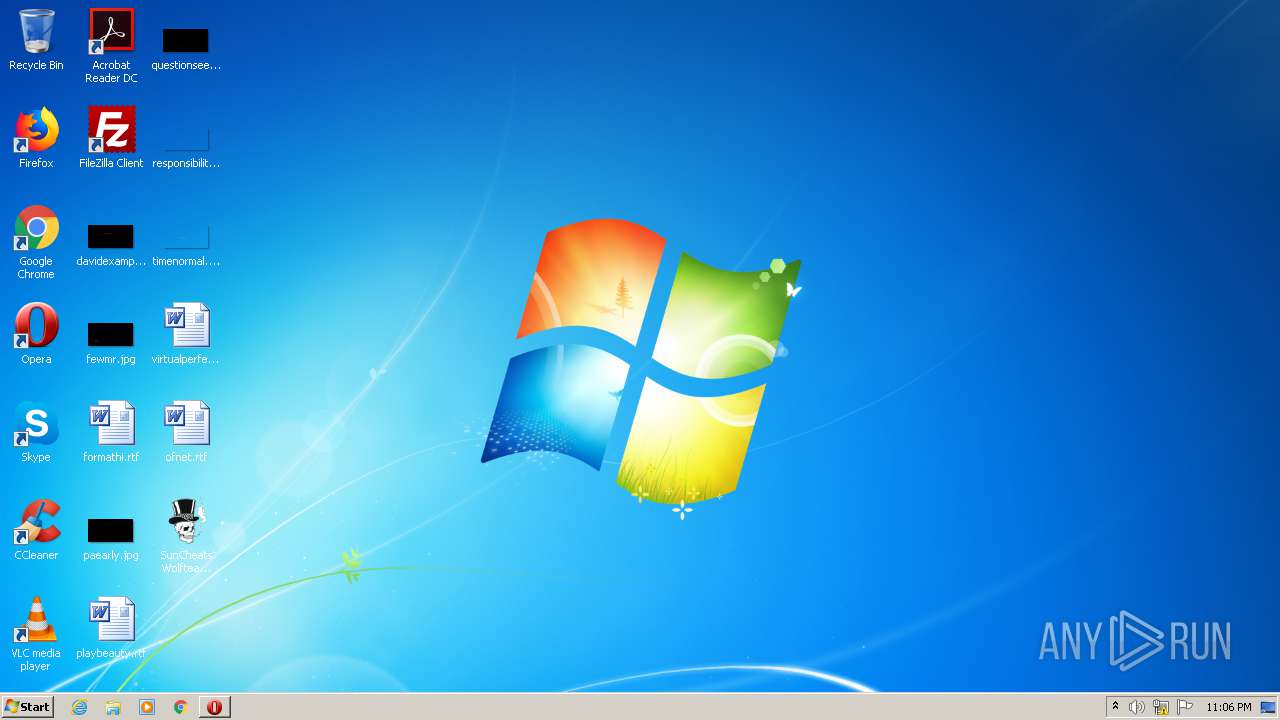
Manual execution by user
- SunCheats Wolfteam Hack.exe (PID: 2480)
Creates files in the user directory
- opera.exe (PID: 1980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
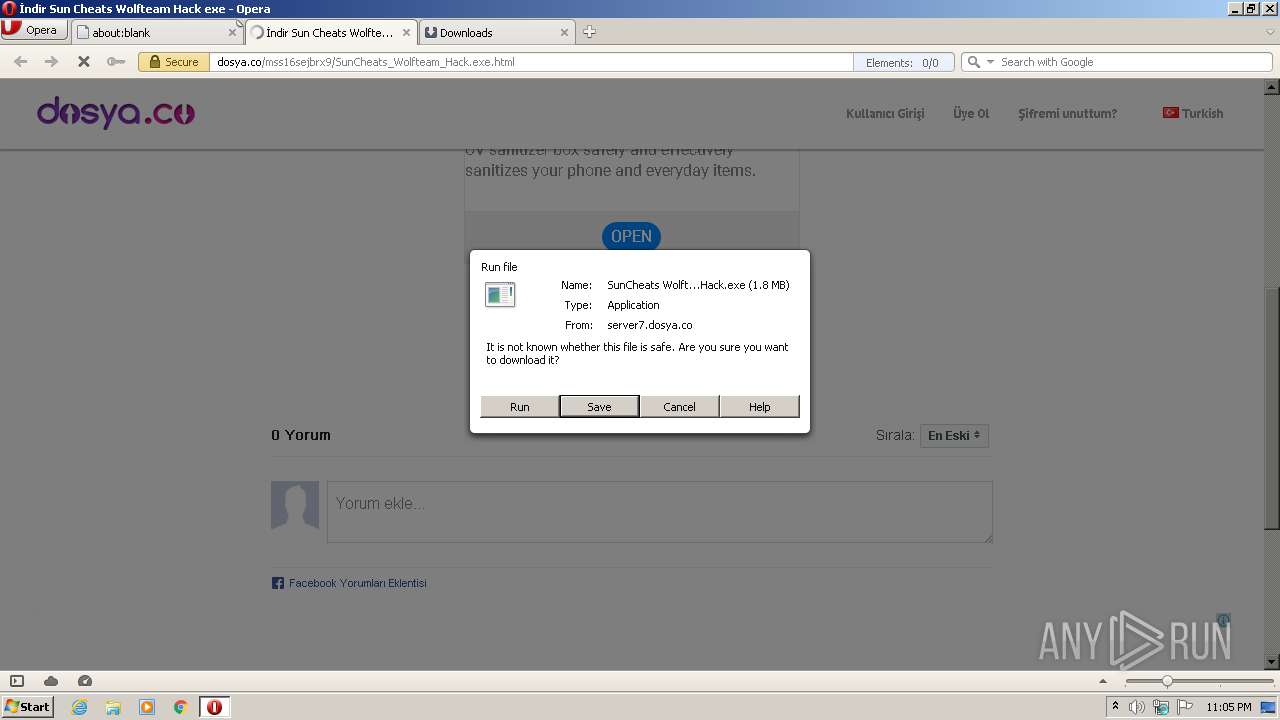
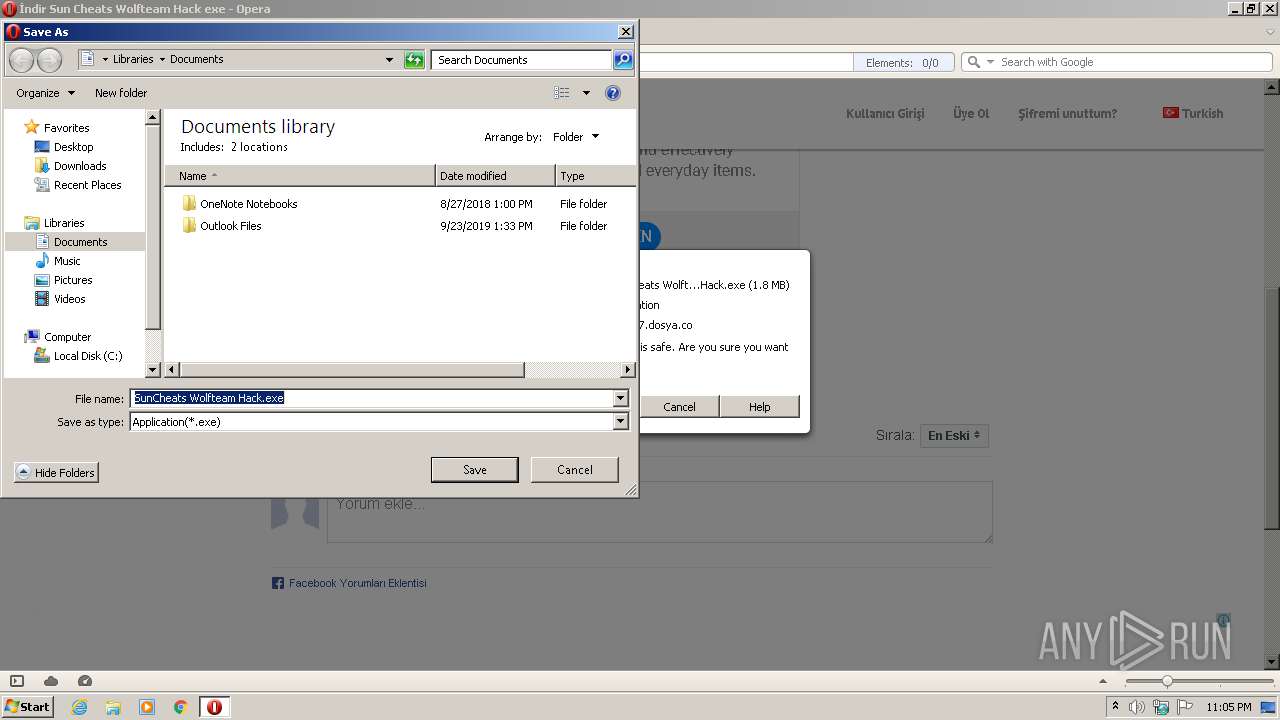
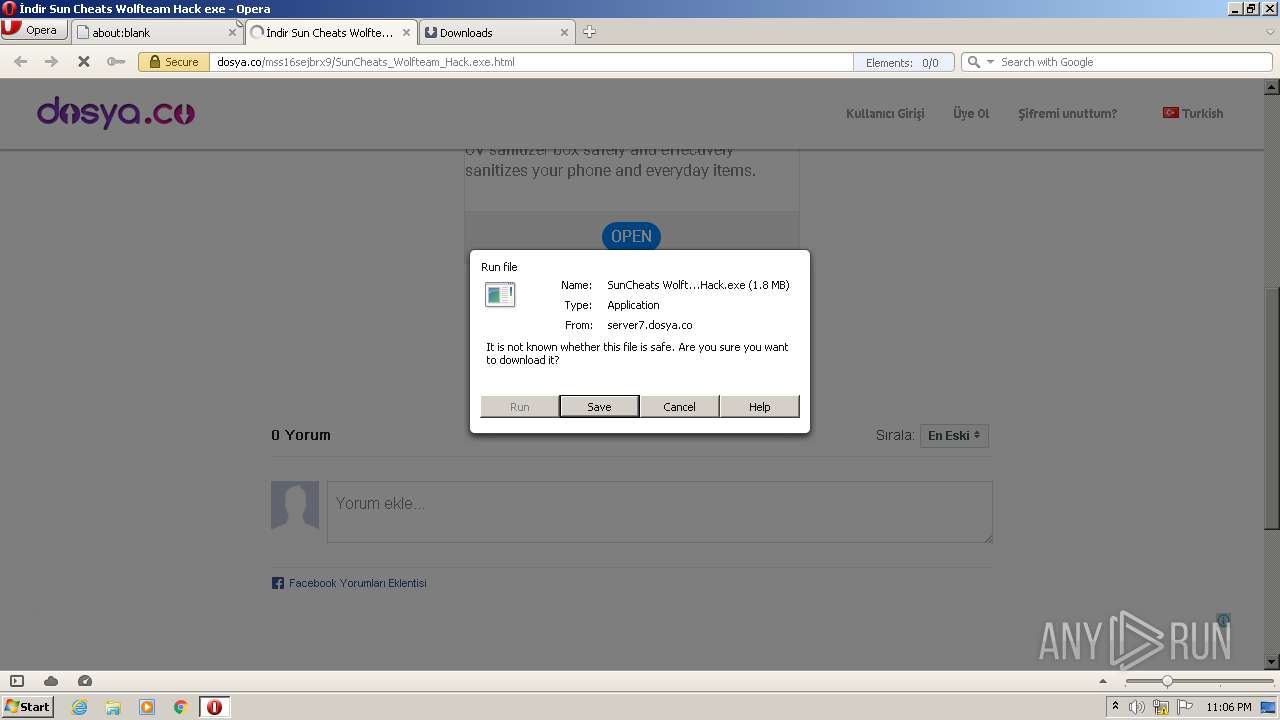
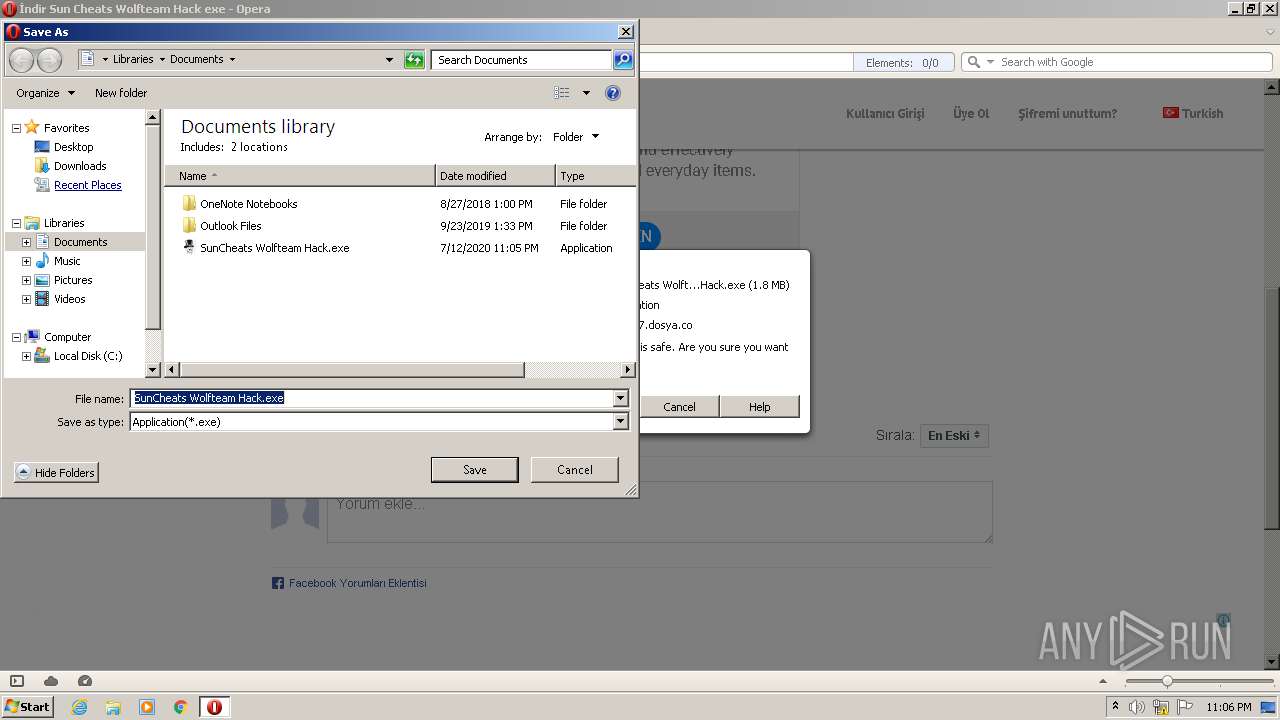
| 348 | "C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\SunCheats Wolfteam Hack.exe" | C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\SunCheats Wolfteam Hack.exe | — | opera.exe | |||||||||||
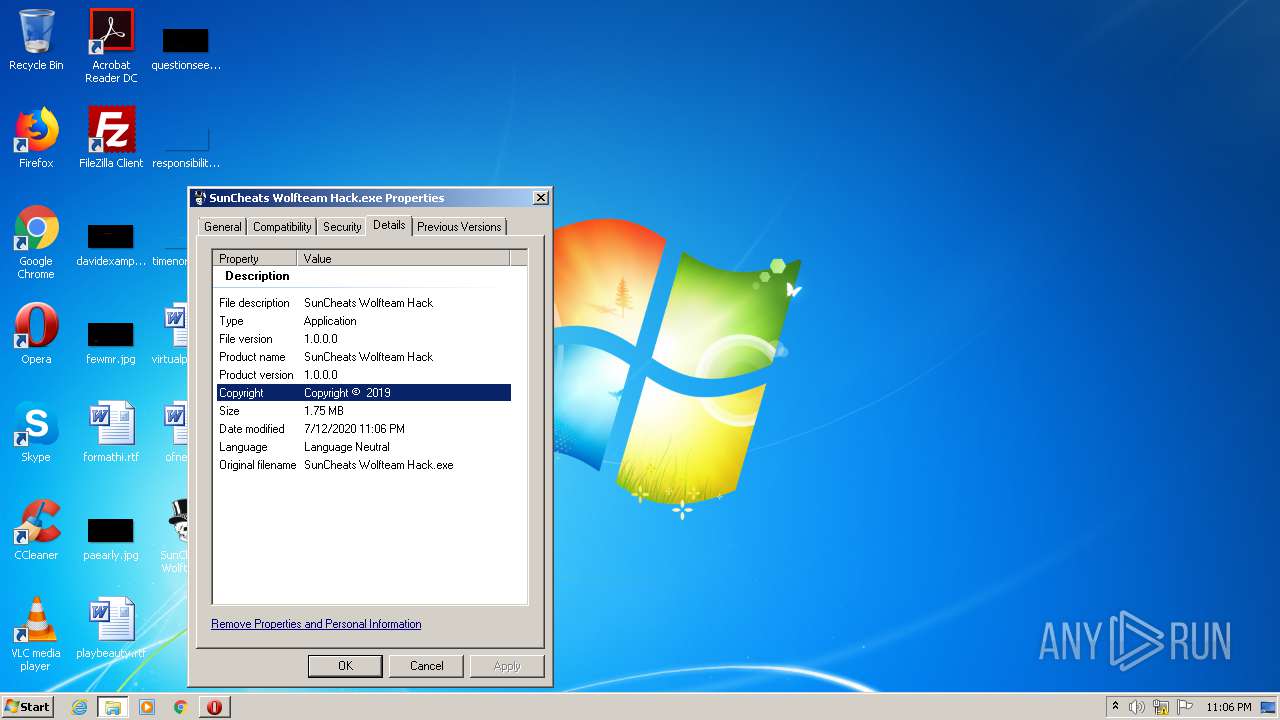
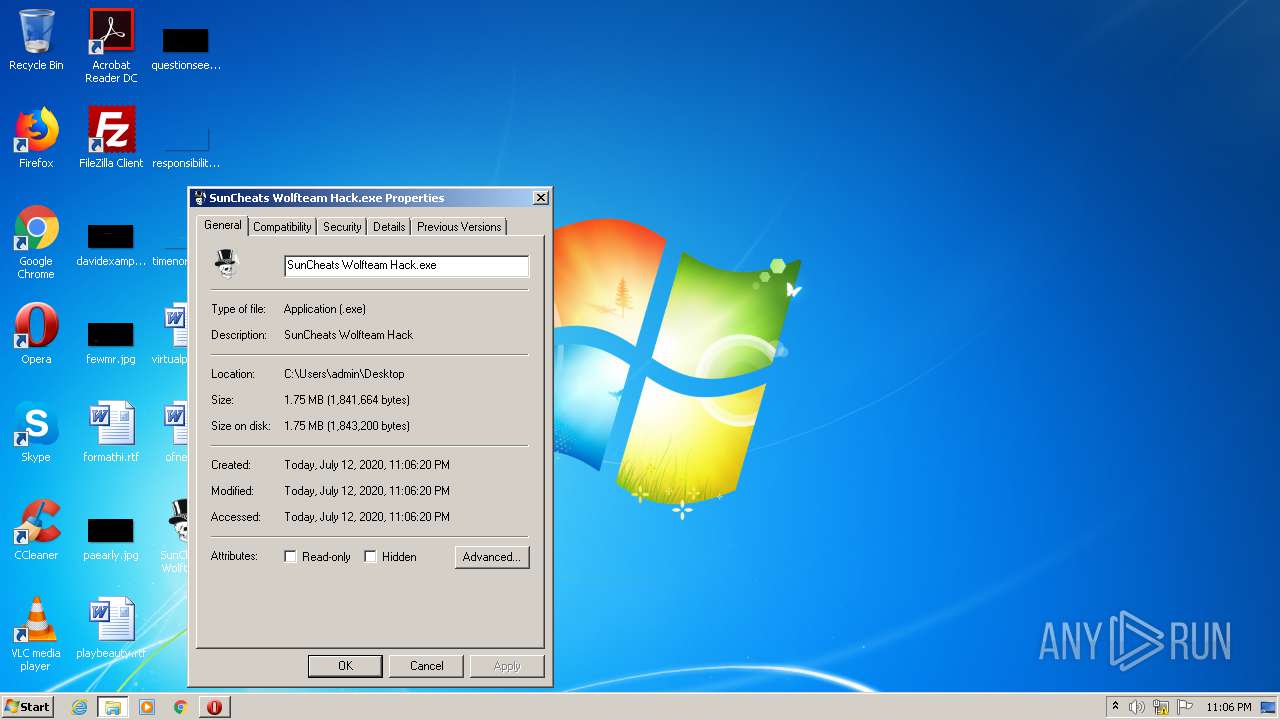
User: admin Integrity Level: MEDIUM Description: SunCheats Wolfteam Hack Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
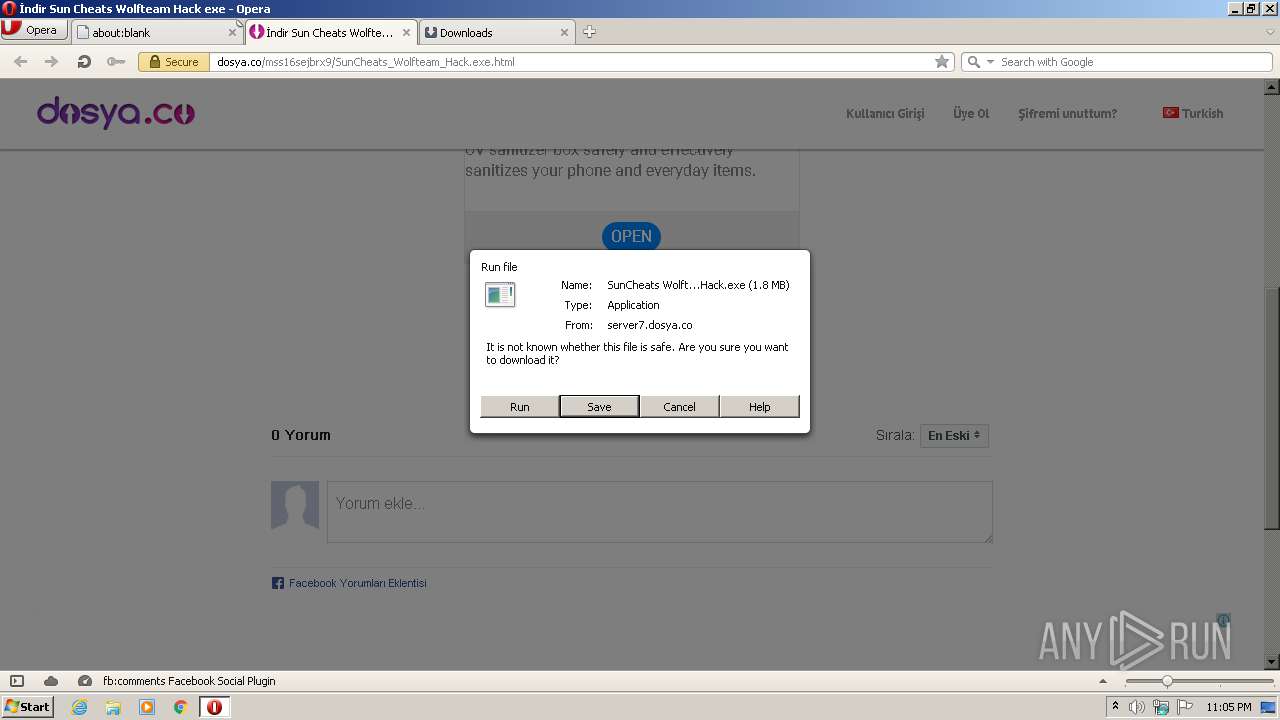
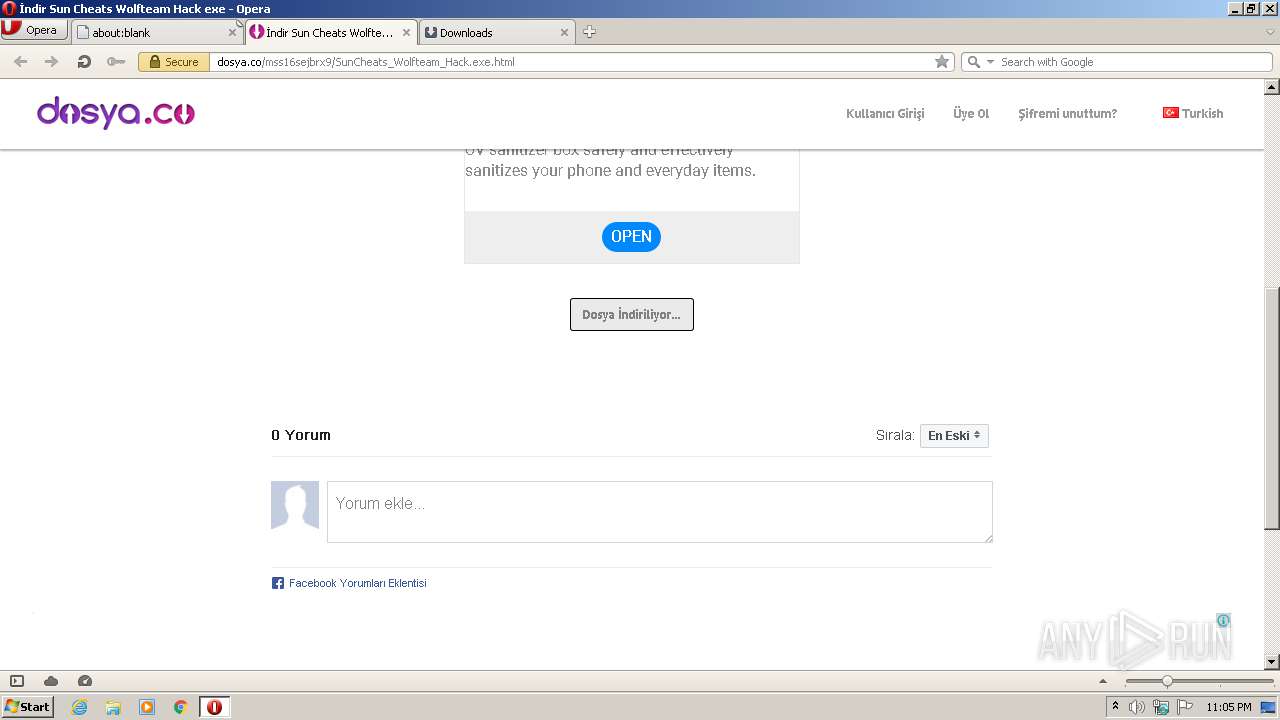
| 1980 | "C:\Program Files\Opera\opera.exe" "https://dosya.co/mss16sejbrx9/SunCheats_Wolfteam_Hack.exe.html" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\Desktop\SunCheats Wolfteam Hack.exe" | C:\Users\admin\Desktop\SunCheats Wolfteam Hack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SunCheats Wolfteam Hack Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
817
Read events
630
Write events
181
Delete events
6
Modification events
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "https://dosya.co/mss16sejbrx9/SunCheats_Wolfteam_Hack.exe.html" | |||
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000001000000000000000A00000007000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\2 |
| Operation: | write | Name: | MRUListEx |
Value: 0000000001000000FFFFFFFF | |||
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (1980) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
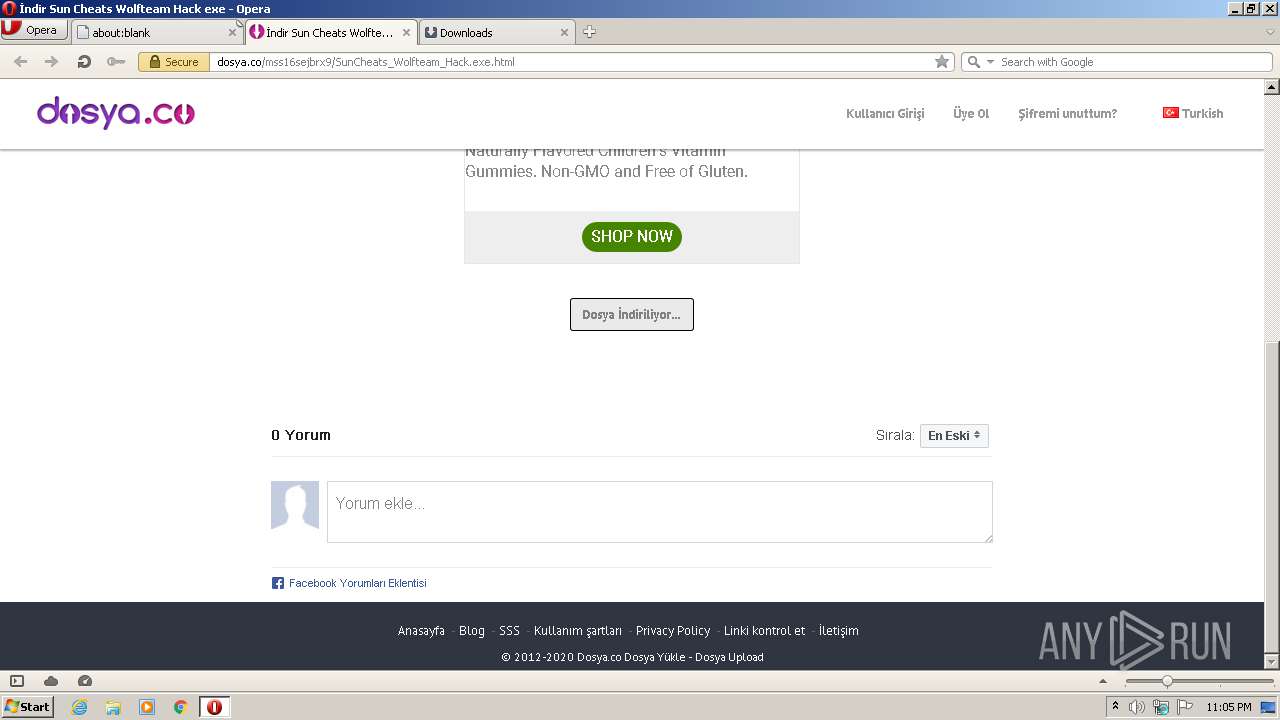
Executable files
9
Suspicious files
125
Text files
54
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1980 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprA76D.tmp | — | |
MD5:— | SHA256:— | |||
| 1980 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprA77E.tmp | — | |
MD5:— | SHA256:— | |||
| 1980 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprA7BD.tmp | — | |
MD5:— | SHA256:— | |||
| 1980 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 1980 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00002.tmp | — | |
MD5:— | SHA256:— | |||
| 1980 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GK8OCF1KVCQWT33I47FY.temp | — | |
MD5:— | SHA256:— | |||
| 1980 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprBABA.tmp | — | |
MD5:— | SHA256:— | |||
| 1980 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 1980 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 1980 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RF10b335.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
130
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1980 | opera.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFXyxIGm3b8PCAAAAABH7mQ%3D | US | der | 471 b | whitelisted |
1980 | opera.exe | GET | 200 | 192.35.177.64:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 994 b | whitelisted |
1980 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
1980 | opera.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCwIsPibuyeAAgAAAAAR%2B6d | US | der | 472 b | whitelisted |
1980 | opera.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD8FF6Y5j92SgIAAAAAbwUe | US | der | 472 b | whitelisted |
1980 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 922 b | whitelisted |
1980 | opera.exe | GET | 200 | 2.16.107.43:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgTIIj3sAf%2B3FG3fRnVeBN6nCw%3D%3D | unknown | der | 527 b | whitelisted |
1980 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTlMusCQK2hbCidwnVINVIaWKpcFQQUGKka%2FLJFScFvMDQIK9mHnLAlV3oCEA680sv68bC%2BkfVI6XB5G7o%3D | US | der | 471 b | whitelisted |
1980 | opera.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCn0AdbX9w0VwIAAAAAbwYe | US | der | 472 b | whitelisted |
1980 | opera.exe | GET | 200 | 216.58.207.67:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 950 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1980 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
1980 | opera.exe | 195.201.111.49:443 | dosya.co | Awanti Ltd. | RU | suspicious |
1980 | opera.exe | 192.35.177.64:80 | crl.identrust.com | IdenTrust | US | malicious |
1980 | opera.exe | 2.16.107.43:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | suspicious |
1980 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1980 | opera.exe | 82.145.216.16:443 | sitecheck2.opera.com | Opera Software AS | — | suspicious |
1980 | opera.exe | 82.145.216.15:443 | sitecheck2.opera.com | Opera Software AS | — | suspicious |
1980 | opera.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
1980 | opera.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1980 | opera.exe | 104.16.132.229:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dosya.co |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
crl4.digicert.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
apis.google.com |
| whitelisted |