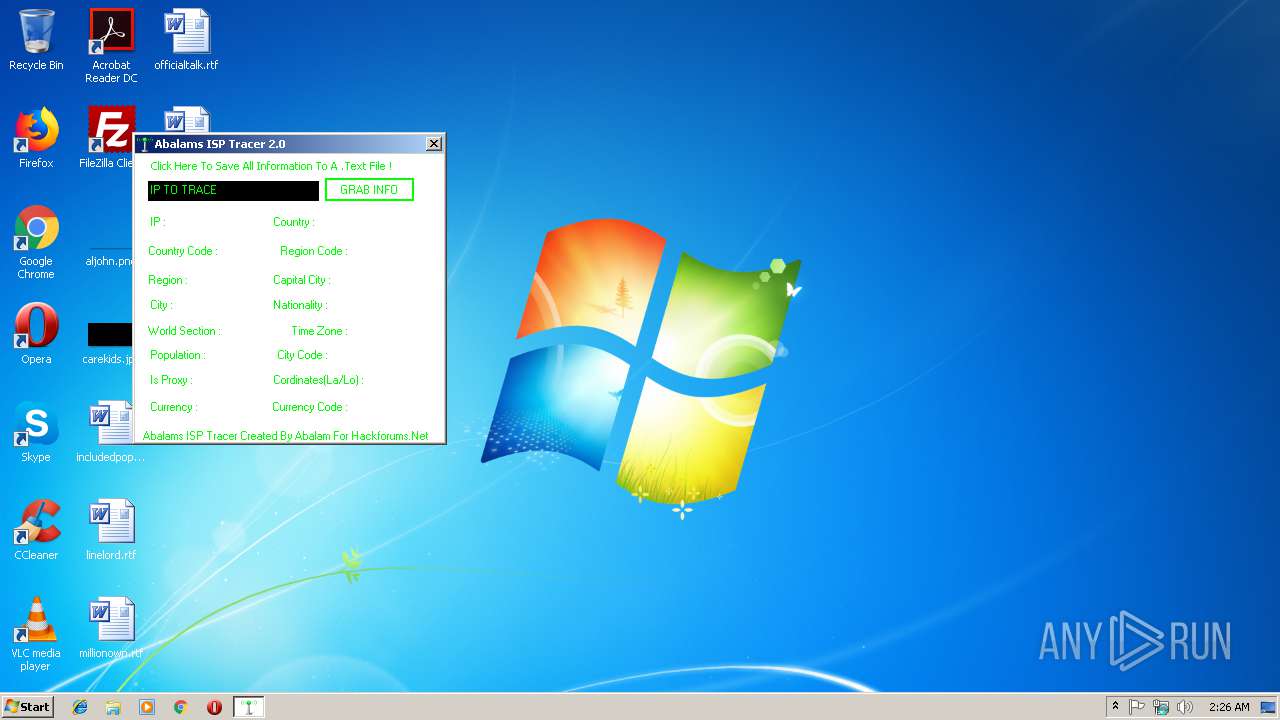
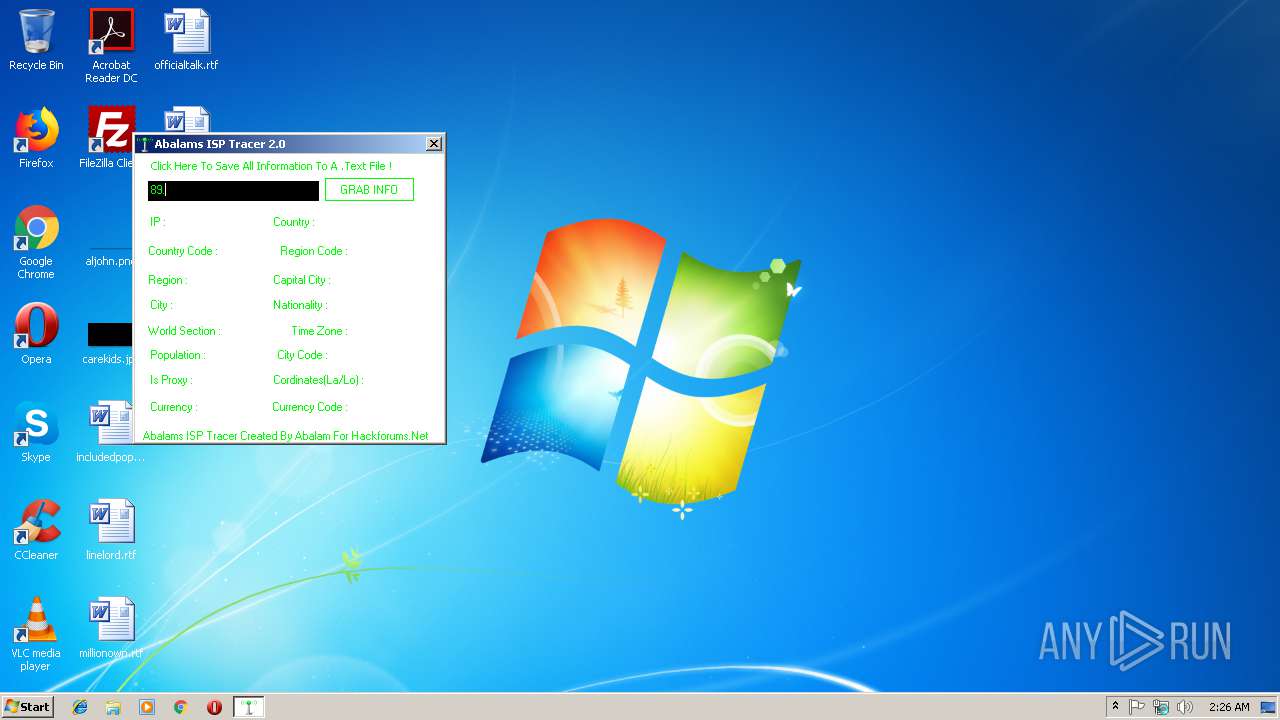
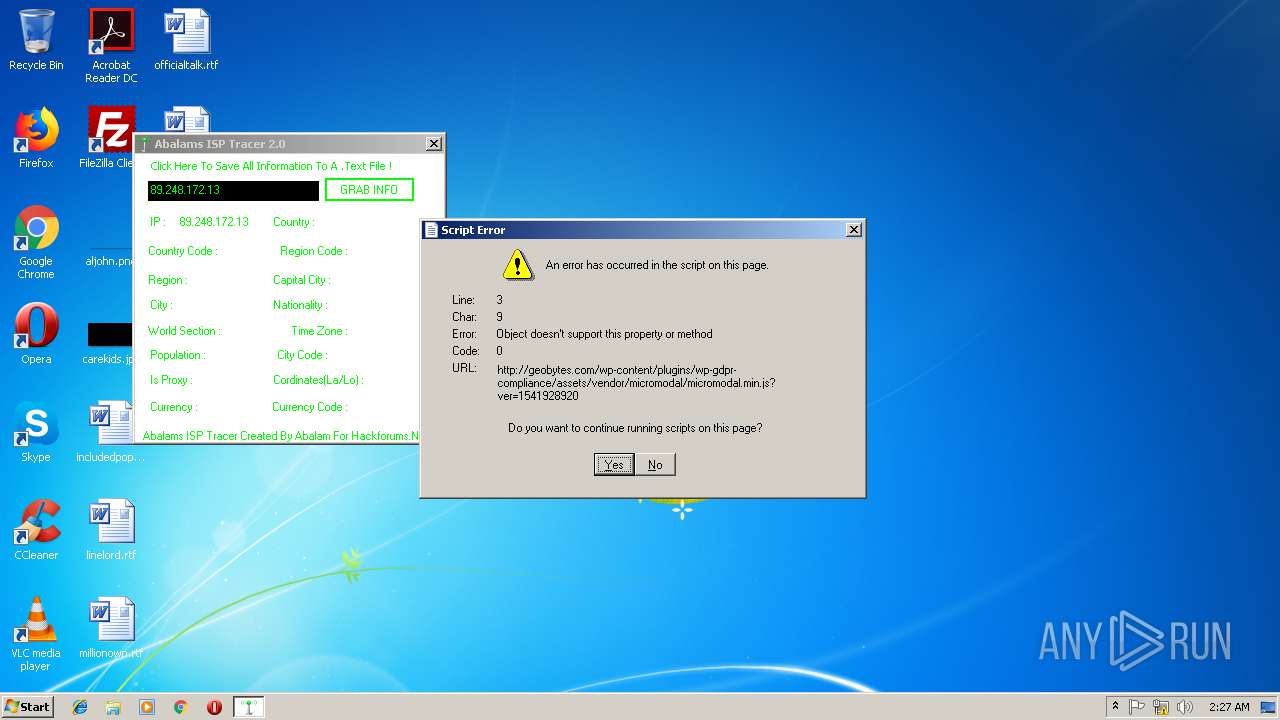
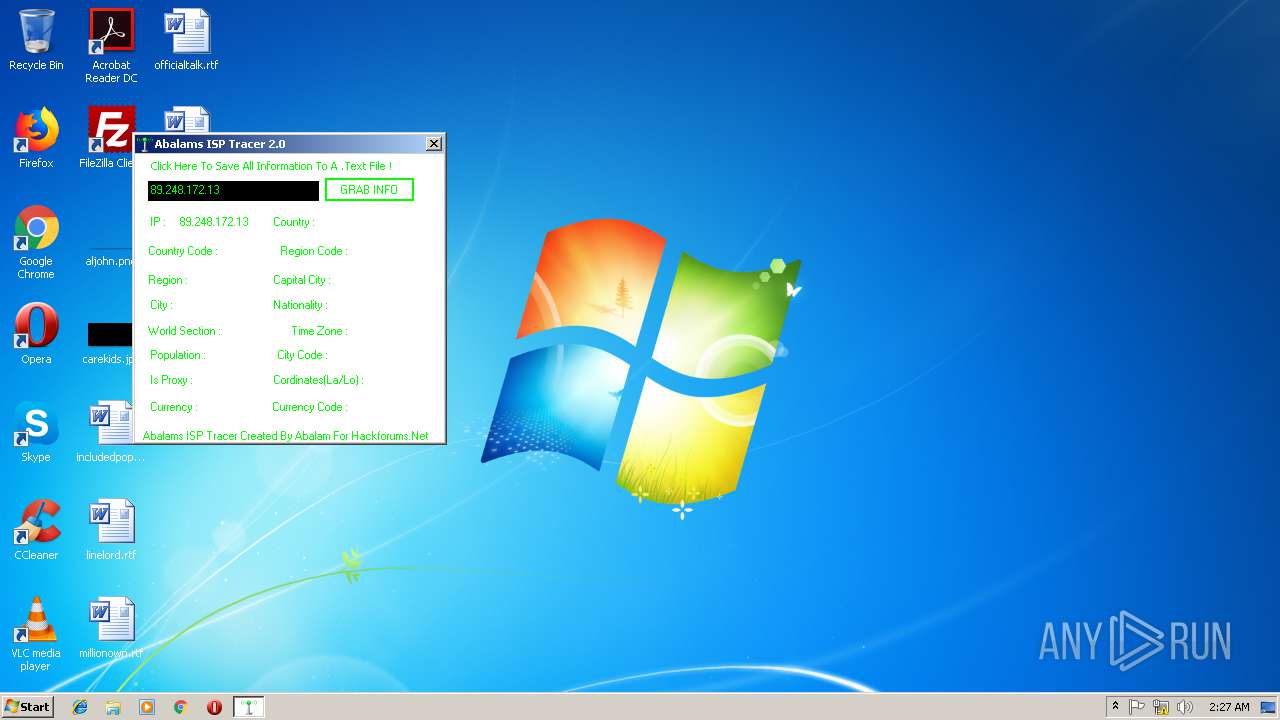
| File name: | Abalams ISP Tracer.exe |
| Full analysis: | https://app.any.run/tasks/94e764b3-ba49-4224-846d-aa18f0414256 |
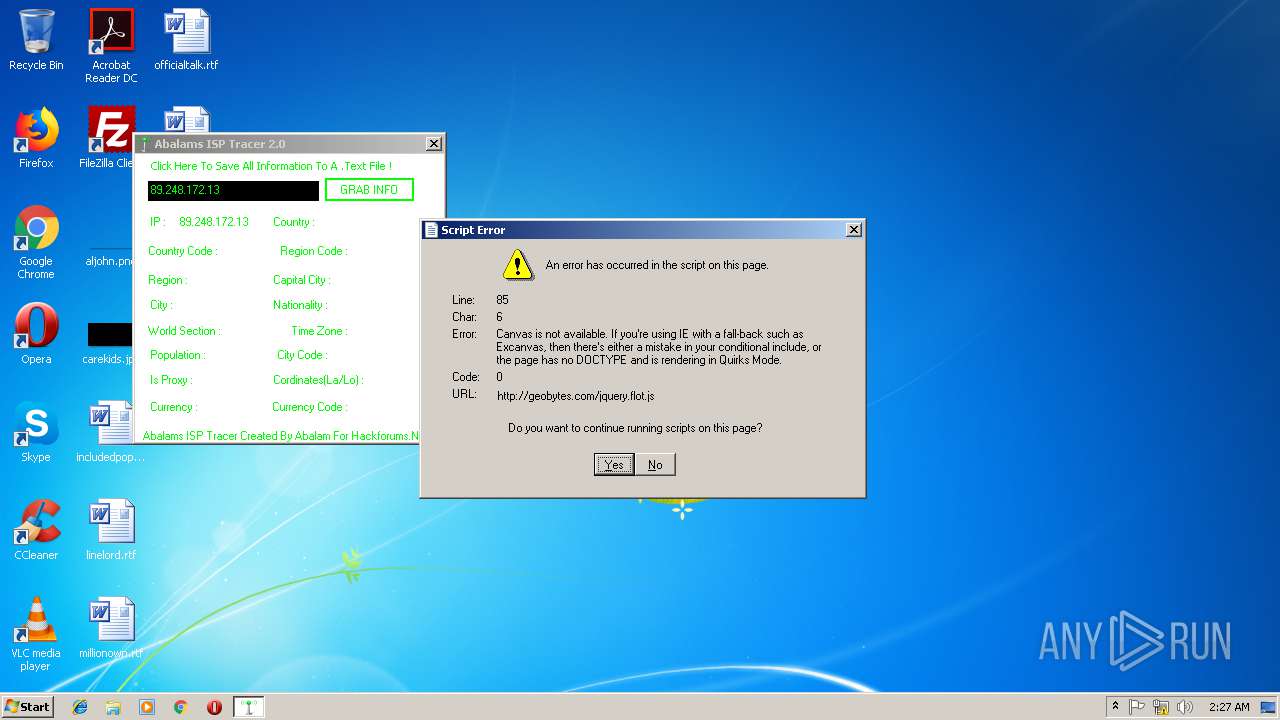
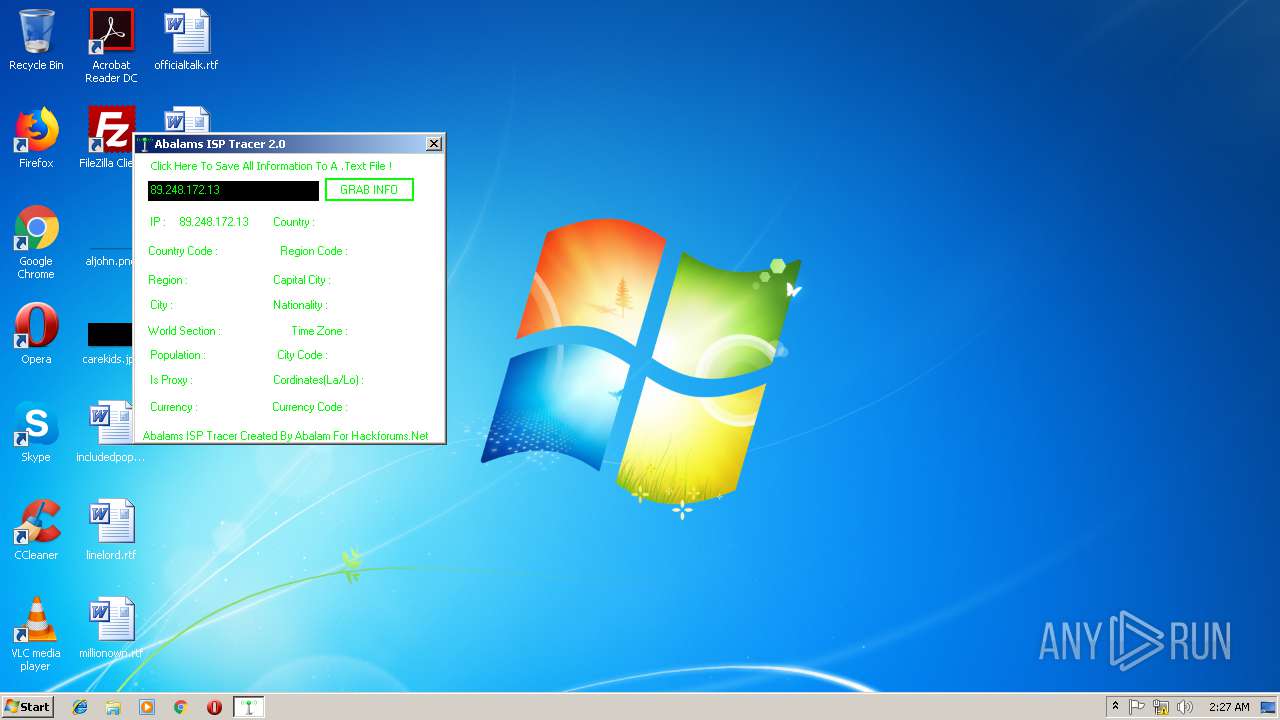
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2019, 02:25:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | F4831615DF9BEA3F57B3431884498E0C |
| SHA1: | A7CDC211B5E2A26F0F4DA8F056C05C3EDAD9915B |
| SHA256: | 6BA947E702E73C71DA242B4B56926FC318701DFAD75BBA840EAC1056F86847E3 |
| SSDEEP: | 3072:x1ppM48X3+3PW2Spj9Ty9FFtFxq/AoidKeRW+i3j9Ty:j/bD3PW2cjMU/zRj |
MALICIOUS
Changes settings of System certificates
- Abalams ISP Tracer.exe (PID: 3088)
SUSPICIOUS
Creates files in the user directory
- Abalams ISP Tracer.exe (PID: 3088)
Adds / modifies Windows certificates
- Abalams ISP Tracer.exe (PID: 3088)
Reads internet explorer settings
- Abalams ISP Tracer.exe (PID: 3088)
Reads Internet Cache Settings
- Abalams ISP Tracer.exe (PID: 3088)
INFO
Reads settings of System Certificates
- Abalams ISP Tracer.exe (PID: 3088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:05:14 11:48:32+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 171520 |
| InitializedDataSize: | 70144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2bdae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Track IP Addresses |
| CompanyName: | Qtex Corporation |
| FileDescription: | Track IP |
| FileVersion: | 1.0.0.0 |
| InternalName: | Abalams ISP Tracer.exe |
| LegalCopyright: | Copyright © 2011 |
| OriginalFileName: | Abalams ISP Tracer.exe |
| ProductName: | Track IP |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-May-2012 09:48:32 |
| Debug artifacts: |
|
| Comments: | Track IP Addresses |
| CompanyName: | Qtex Corporation |
| FileDescription: | Track IP |
| FileVersion: | 1.0.0.0 |
| InternalName: | Abalams ISP Tracer.exe |
| LegalCopyright: | Copyright © 2011 |
| OriginalFilename: | Abalams ISP Tracer.exe |
| ProductName: | Track IP |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 14-May-2012 09:48:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00029DB4 | 0x00029E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.26506 |
.sdata | 0x0002C000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.2376 |
.rsrc | 0x0002E000 | 0x00010C88 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.64426 |
.reloc | 0x00040000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.32476 | 860 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 4.66186 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.16096 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
30
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3088 | "C:\Users\admin\AppData\Local\Temp\Abalams ISP Tracer.exe" | C:\Users\admin\AppData\Local\Temp\Abalams ISP Tracer.exe | explorer.exe | ||||||||||||
User: admin Company: Qtex Corporation Integrity Level: MEDIUM Description: Track IP Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
239
Read events
194
Write events
44
Delete events
1
Modification events
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Abalams ISP Tracer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Abalams ISP Tracer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Abalams ISP Tracer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Abalams ISP Tracer_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Abalams ISP Tracer_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Abalams ISP Tracer_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Abalams ISP Tracer_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3088) Abalams ISP Tracer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Abalams ISP Tracer_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
93
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\sfsi-style[1].css | text | |
MD5:— | SHA256:— | |||
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\wordpress_file_upload_style_safe_relaxed[1].css | text | |
MD5:— | SHA256:— | |||
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\monaco[1].css | text | |
MD5:5A45E2995168322E4B29B4C3F0D2B274 | SHA256:8B33EEBC11529672AFC8F1AC6D5D4EF24BED8DFEC1505A2510C805E0DD21565F | |||
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\wordpress_file_upload_style_relaxed[1].css | text | |
MD5:— | SHA256:— | |||
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\html5[1].js | html | |
MD5:5A98A86B5CB48C1506F338463259CE41 | SHA256:86FBFE313672EEA1721475598CA81E520C6D1F788EC4EF7726C7AF3CD987E560 | |||
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\light_style[1].css | text | |
MD5:C20E636EFB7DB3374183C0EB207581B7 | SHA256:8FEEAB8C1BF06B50257479AF3E684756EE3E96F09C2F053DDD593C22A71E2DE4 | |||
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\iplocator[1].txt | html | |
MD5:— | SHA256:— | |||
| 3088 | Abalams ISP Tracer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\f[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
83
TCP/UDP connections
29
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
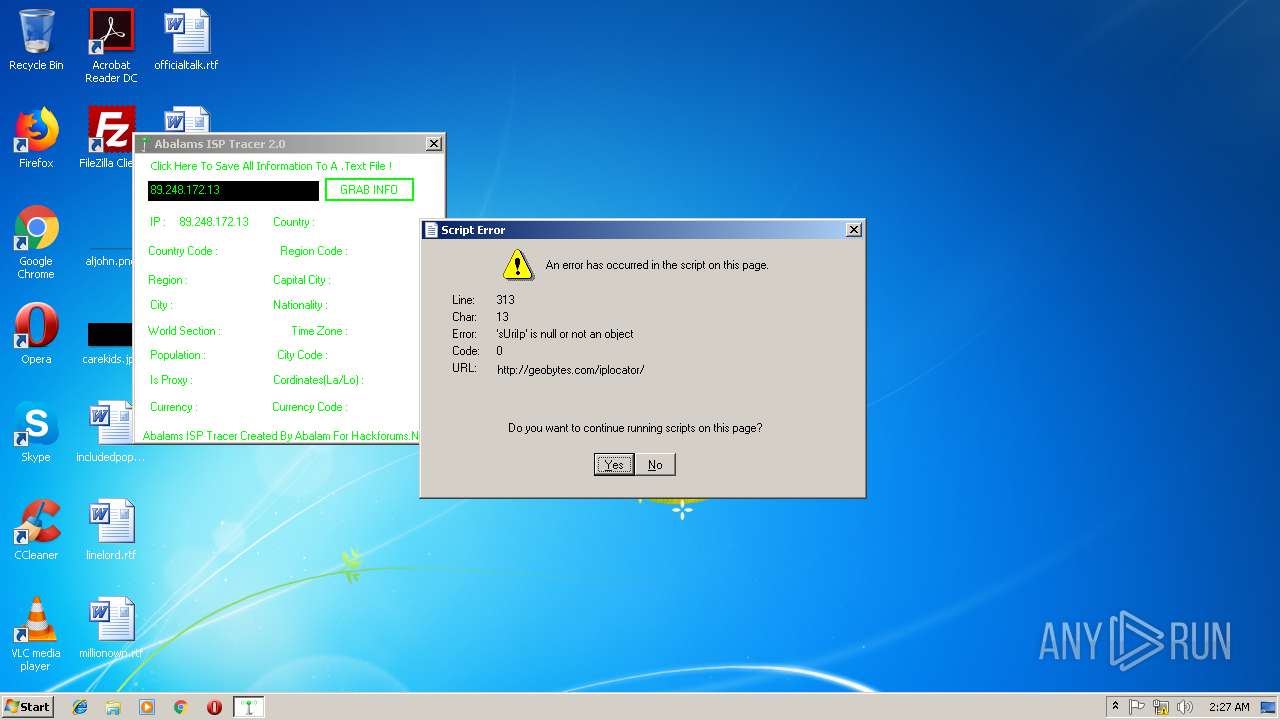
3088 | Abalams ISP Tracer.exe | GET | 200 | 69.16.219.23:80 | http://gd.geobytes.com/gd?after=-1&variables=GeobytesCountry,GeobytesCity,GeobytesCode,GeobytesLatitude,GeobytesLongitude,GeobytesIpAddress | US | text | 273 b | suspicious |
3088 | Abalams ISP Tracer.exe | GET | 200 | 172.217.22.98:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 29.4 Kb | whitelisted |
3088 | Abalams ISP Tracer.exe | GET | 200 | 69.16.219.22:80 | http://geobytes.com/wp-content/themes/twentyfourteen/style.css?ver=4.9.9 | US | text | 13.5 Kb | suspicious |
3088 | Abalams ISP Tracer.exe | GET | 200 | 69.16.219.22:80 | http://geobytes.com/wp-content/plugins/wp-file-upload/css/wordpress_file_upload_style_safe_relaxed.css?ver=1.0 | US | text | 213 b | suspicious |
3088 | Abalams ISP Tracer.exe | GET | 200 | 172.217.16.170:80 | http://fonts.googleapis.com/css?family=Lato%3A300%2C400%2C700%2C900%2C300italic%2C400italic%2C700italic&subset=latin%2Clatin-ext | US | text | 155 b | whitelisted |
3088 | Abalams ISP Tracer.exe | GET | 200 | 69.16.219.22:80 | http://geobytes.com/wp-content/plugins/wp-file-upload/css/wordpress_file_upload_style_relaxed.css?ver=1.0 | US | text | 2.88 Kb | suspicious |
3088 | Abalams ISP Tracer.exe | GET | 200 | 69.16.219.22:80 | http://geobytes.com/wp-content/plugins/ultimate-social-media-icons/css/sfsi-style.css?ver=4.9.9 | US | text | 8.47 Kb | suspicious |
3088 | Abalams ISP Tracer.exe | GET | 200 | 69.16.219.22:80 | http://geobytes.com/wp-content/themes/twentyfourteen/js/html5.js | US | html | 1.22 Kb | suspicious |
3088 | Abalams ISP Tracer.exe | GET | 200 | 69.16.219.22:80 | http://geobytes.com/wp-content/plugins/crayon-syntax-highlighter/css/min/crayon.min.css?ver=_2.7.2_beta | US | text | 3.87 Kb | suspicious |
3088 | Abalams ISP Tracer.exe | GET | 200 | 69.16.219.22:80 | http://geobytes.com/wp-content/plugins/jquery-collapse-o-matic/light_style.css?ver=1.6 | US | text | 433 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3088 | Abalams ISP Tracer.exe | 205.185.208.52:80 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
3088 | Abalams ISP Tracer.exe | 69.16.219.22:80 | geobytes.com | Liquid Web, L.L.C | US | unknown |
3088 | Abalams ISP Tracer.exe | 172.217.16.170:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3088 | Abalams ISP Tracer.exe | 172.217.22.98:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3088 | Abalams ISP Tracer.exe | 216.58.207.67:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3088 | Abalams ISP Tracer.exe | 104.19.196.151:80 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
3088 | Abalams ISP Tracer.exe | 152.199.19.160:80 | ajax.aspnetcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
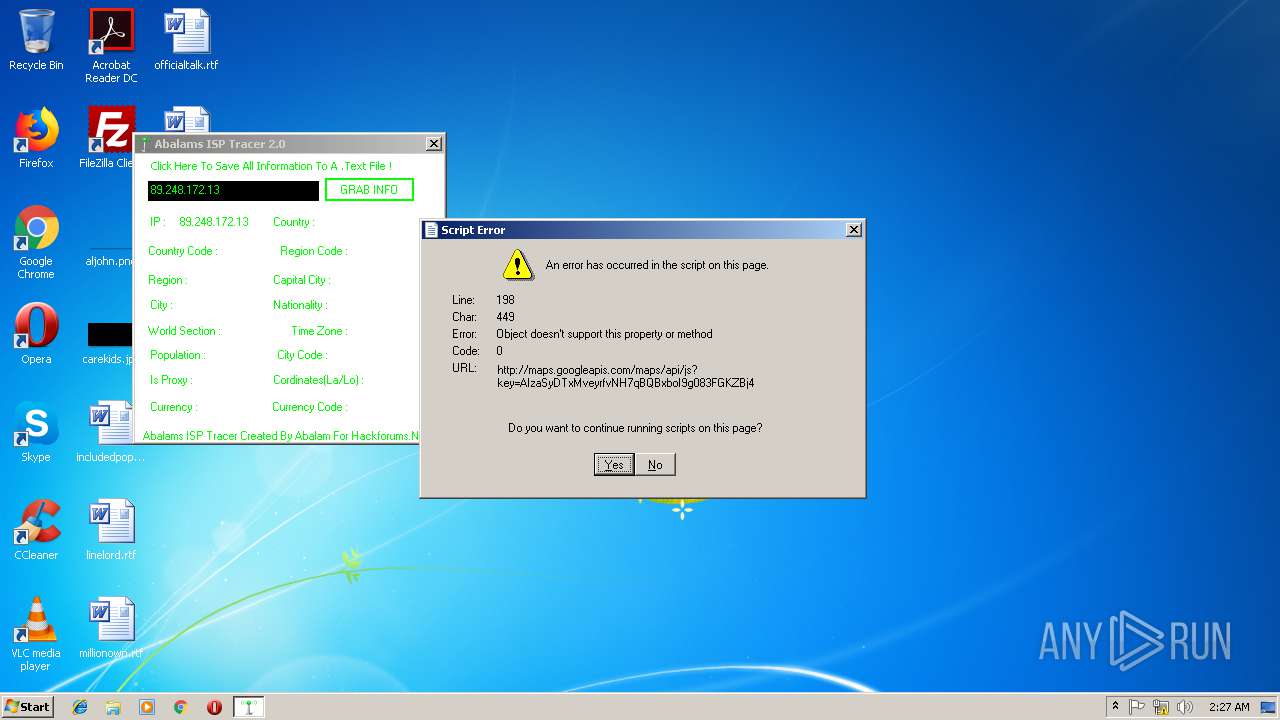
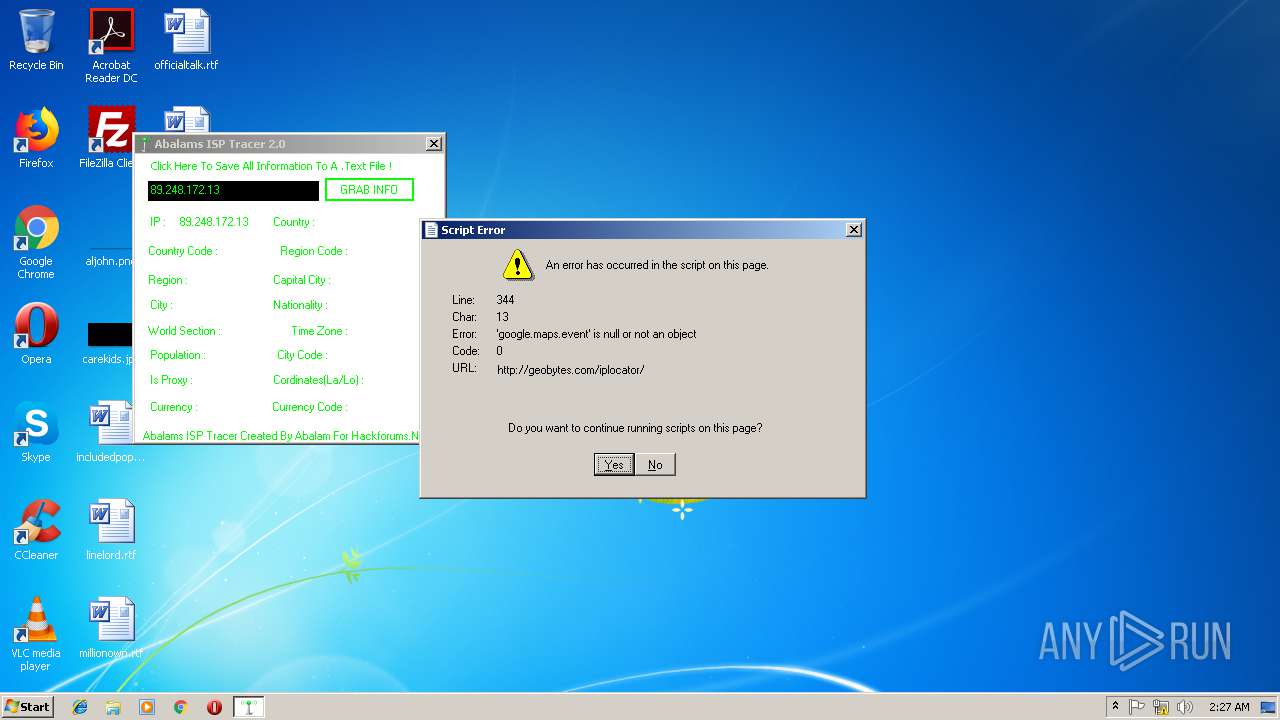
3088 | Abalams ISP Tracer.exe | 216.58.207.74:80 | maps.googleapis.com | Google Inc. | US | whitelisted |
3088 | Abalams ISP Tracer.exe | 216.58.207.42:80 | maps.googleapis.com | Google Inc. | US | whitelisted |
3088 | Abalams ISP Tracer.exe | 157.240.1.23:80 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.geobytes.com |
| suspicious |
geobytes.com |
| suspicious |
code.jquery.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
maps.googleapis.com |
| whitelisted |
ajax.aspnetcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3088 | Abalams ISP Tracer.exe | A Network Trojan was detected | MALWARE [PTsecurity] PowerShell.Downloader httpHeader |