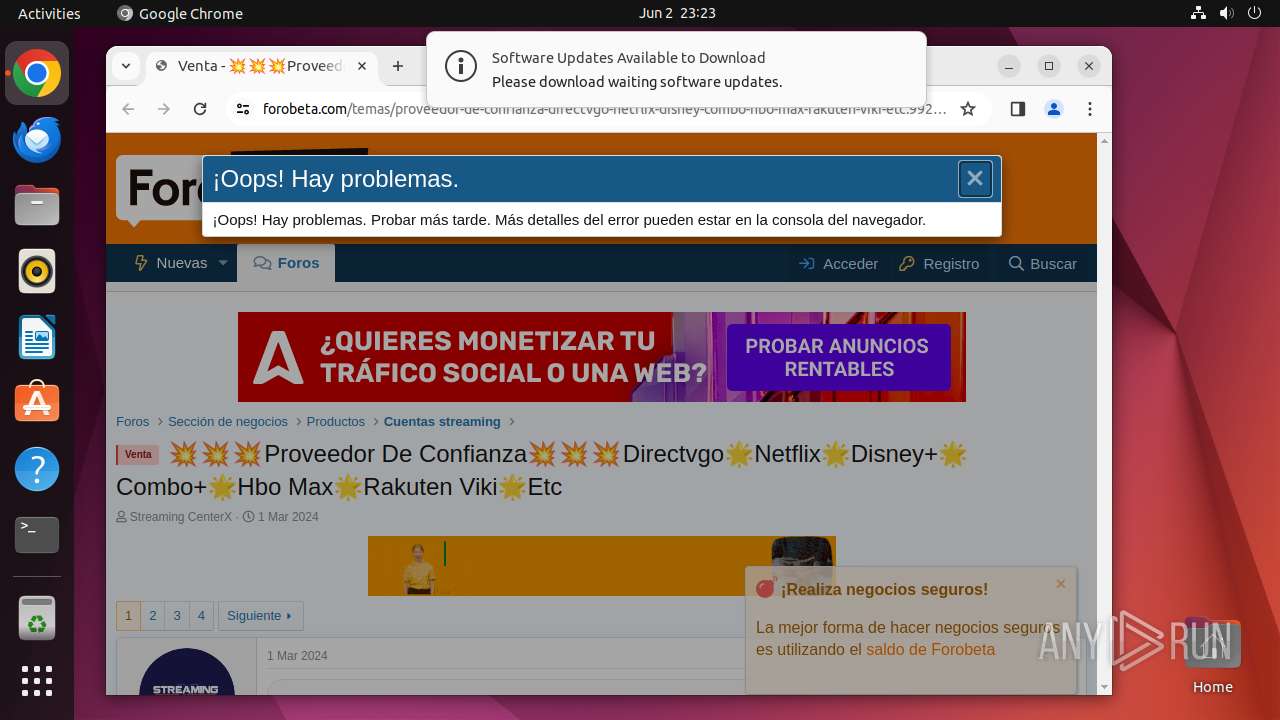
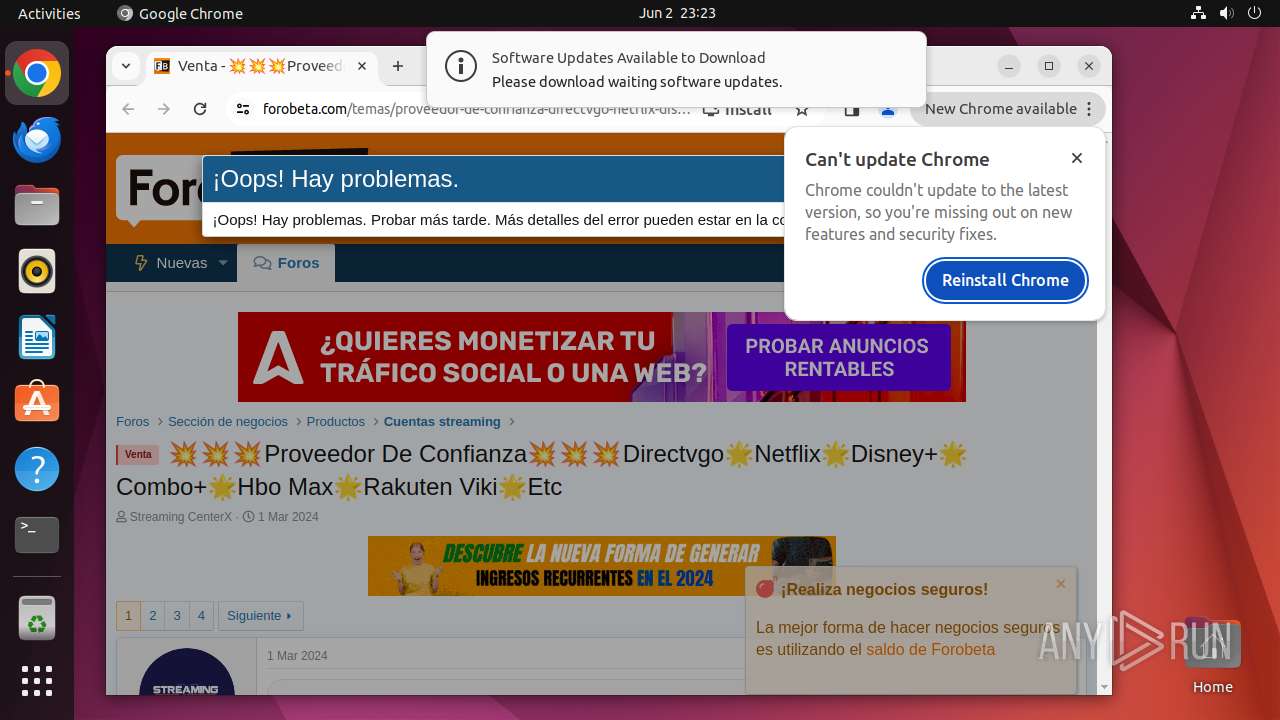
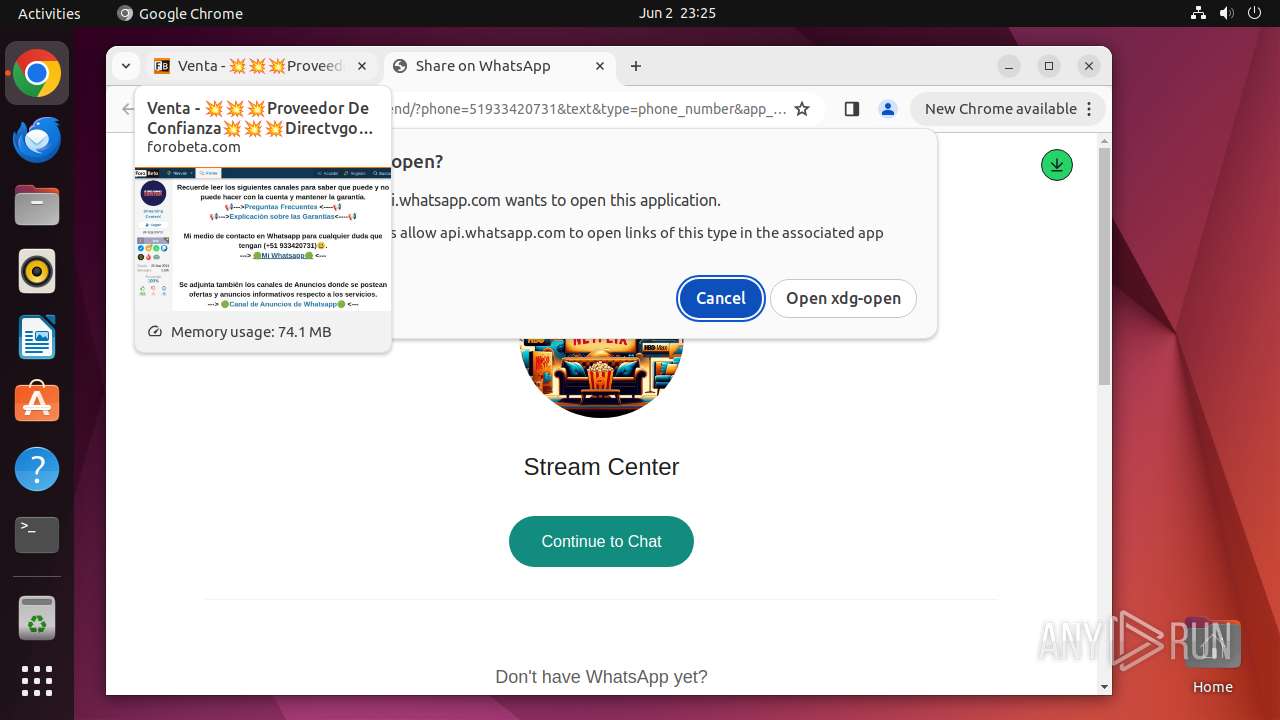
| URL: | https://forobeta.com/temas/proveedor-de-confianza-directvgo-netflix-disney-combo-hbo-max-rakuten-viki-etc.992136 |
| Full analysis: | https://app.any.run/tasks/99acbef9-61bb-4b81-b977-9836fe28e7b7 |
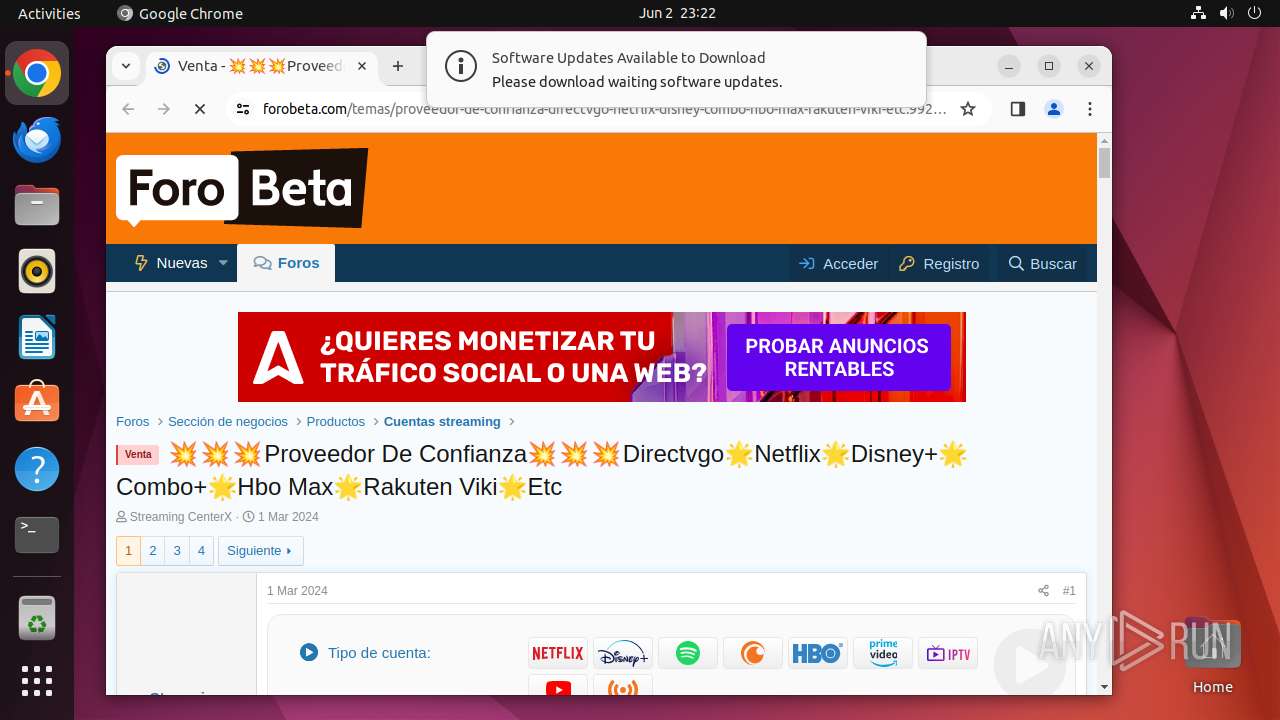
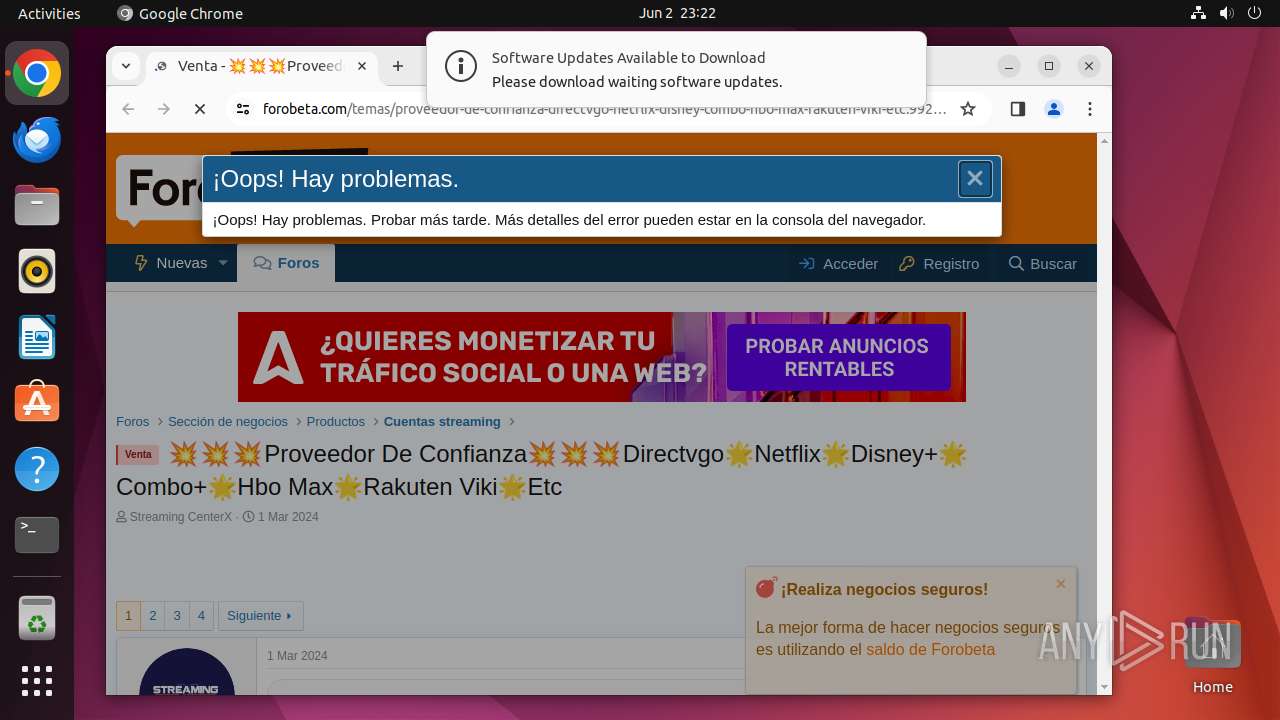
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2024, 22:22:49 |
| OS: | Ubuntu 22.04.2 |
| MD5: | 73720D593025C9A4901E6FBCBD6F6CE2 |
| SHA1: | DA1E399C1E25E6562101B356BCE03E6423388A0F |
| SHA256: | 6BA2AA0946EC1AFB07781F3D44ABFB4375A8A291AD3AF7C808BEBDED468EED6C |
| SSDEEP: | 3:N8a4mIKvQLoIUD5A5MPMEOQRHY9RuEU:2Q3DD5A5IME6R5U |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
464
Monitored processes
253
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 11946 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://forobeta\.com/temas/proveedor-de-confianza-directvgo-netflix-disney-combo-hbo-max-rakuten-viki-etc\.992136 " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 11947 | sudo -iu user google-chrome https://forobeta.com/temas/proveedor-de-confianza-directvgo-netflix-disney-combo-hbo-max-rakuten-viki-etc.992136 | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 11948 | /usr/bin/google-chrome https://forobeta.com/temas/proveedor-de-confianza-directvgo-netflix-disney-combo-hbo-max-rakuten-viki-etc.992136 | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 11949 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 11950 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 11951 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 11952 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 11953 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 11954 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 11955 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 11948 | chrome | /proc/11948/fd/63 | — | |
MD5:— | SHA256:— | |||
| 11948 | chrome | /dev/shm/.com.google.Chrome.vzzPQR | — | |
MD5:— | SHA256:— | |||
| 11948 | chrome | /dev/shm/.com.google.Chrome.vyNOUs | — | |
MD5:— | SHA256:— | |||
| 11948 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/metadata/LOG | — | |
MD5:— | SHA256:— | |||
| 11948 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/LOG | — | |
MD5:— | SHA256:— | |||
| 11948 | chrome | /home/user/.config/google-chrome/PrivacySandboxAttestationsPreloaded/2024.5.29.0/attestations_sentinel | — | |
MD5:— | SHA256:— | |||
| 11948 | chrome | /home/user/.config/google-chrome/WidevineCdm/.com.google.Chrome.e9Oj0o | — | |
MD5:— | SHA256:— | |||
| 11948 | chrome | /dev/shm/.com.google.Chrome.FxG9vP | — | |
MD5:— | SHA256:— | |||
| 11948 | chrome | /dev/shm/.com.google.Chrome.kBNxxF | — | |
MD5:— | SHA256:— | |||
| 11948 | chrome | /dev/shm/.com.google.Chrome.2xH8TD | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
56
DNS requests
58
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/lmelglejhemejginpboagddgdfbepgmp/1.3e6a99367b6b37be5ad828dac3f4612241ac241264ca3955b108ff8b9333b5d3/1.7c7270ef0b71ec063a98f512831a53690989605dcb0fbf503b95ca5bb4f98b63/52ad120a5d427563fdc59b68c6d3e362041126c0fd5c5ee848d9c837706267fd.puff | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflhchccmppkfebkiaminageehmchikm/1.0e328777fe67413cad512fdd0e3cba0a9035e9f4399d4b93258133481fafb26f/1.a7160bdc1e283a03d9b90954917f1792a6523479be9e1750aab8a72ed52a55d2/580e69b5728b7848df63e65e370ecc0458986987ec599475e928a5edd129a773.puff | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gonpemdgkjcecdgbnaabipppbmgfggbe/1.e73a7fe8092191e16e2807ea7f48e54261b783aa2525152082ca6a0d59274dbd/1.046a7153ace40b4c1fcb2423ffdd0bda38820d2bade6aa5ab6929fe80e4acea3/5f6d5d03503db866ffdb28b772991231a1e832d579f71dd48c56f70200a76d3e.puff | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/hfnkpimlhhgieaddgfemjhofmfblmnib/1.3392b2d6627586e5d4d7df79e9be3a7c6f31273b672a67324edc962ef585e482/1.bbe9bb5ed30cbff90cc9e294b968884dc0a6a7e54137af95892e8655b60ab17f/8a31f9160ca085db5231e392ed62c1f20ff53be4c448406c0bc48e6f5a680b6d.puff | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/niikhdgajlphfehepabhhblakbdgeefj/1.284a35ea58c93c47906d767700307ea381780803f9257878c2bb271d5779eab3/1.1dbb3990e16ba546e7367ef84c38441173fbb5a7b570bb9b183d3b6faaeb622d/6133200764ee137d190022c62831090d474aae6c66b6bd2671efdfb948f829aa.puff | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.97:80 | — | Canonical Group Limited | GB | unknown |
— | — | 156.146.33.138:443 | odrs.gnome.org | Datacamp Limited | DE | unknown |
485 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | malicious |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 142.250.186.67:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 64.233.166.84:443 | accounts.google.com | — | — | unknown |
11948 | chrome | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 216.246.113.54:443 | forobeta.com | SERVERCENTRAL | US | unknown |
— | — | 151.101.193.91:443 | google-ohttp-relay-safebrowsing.fastly-edge.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| unknown |
api.snapcraft.io |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
forobeta.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
169.100.168.192.in-addr.arpa |
| unknown |
content-autofill.googleapis.com |
| whitelisted |