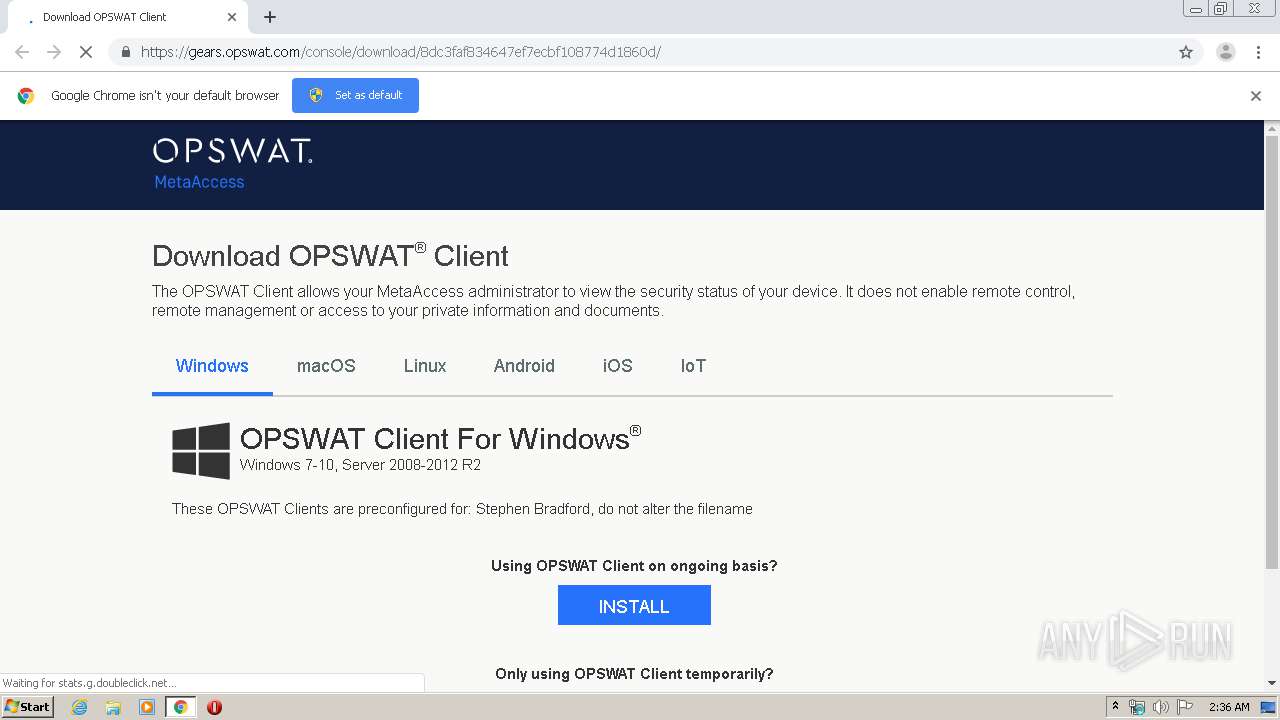
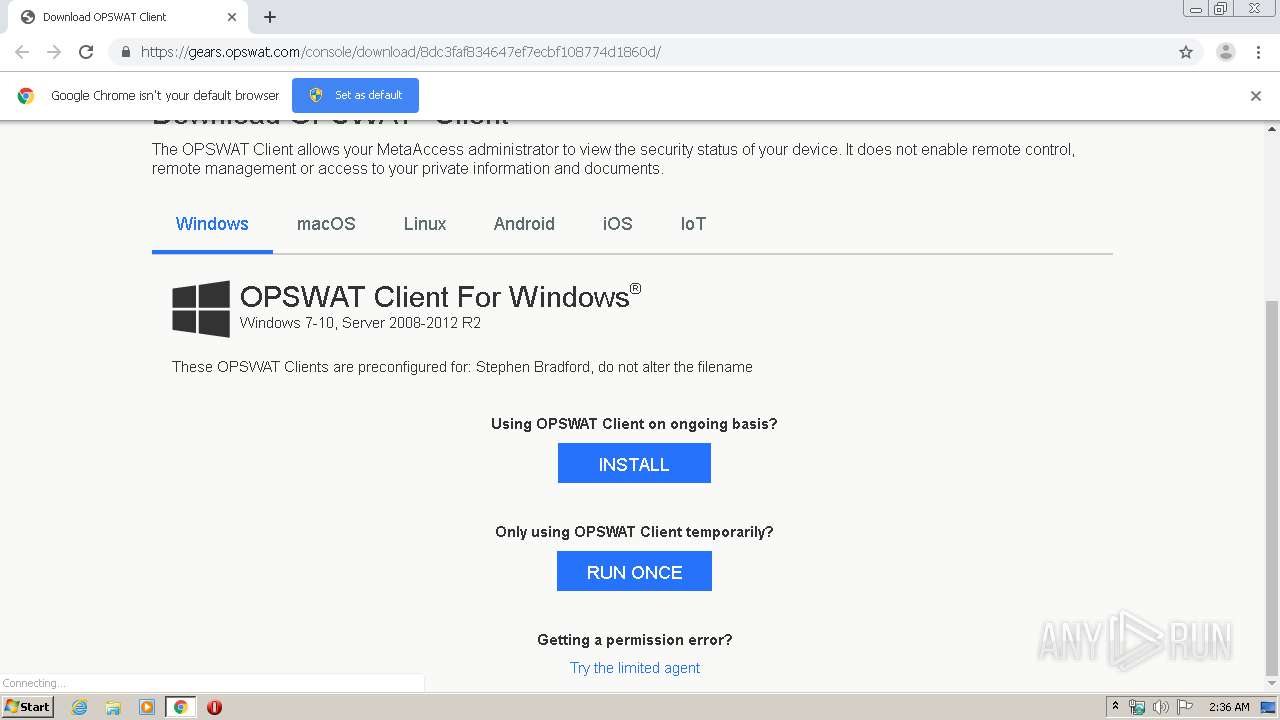
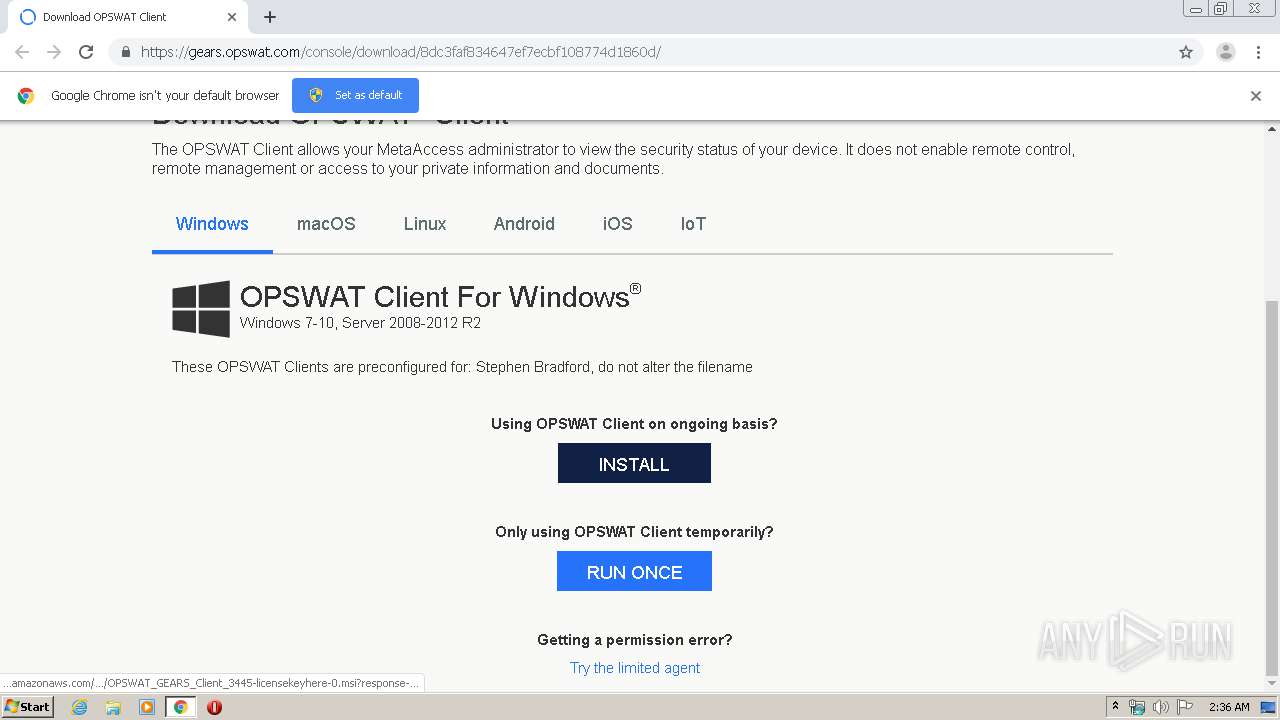
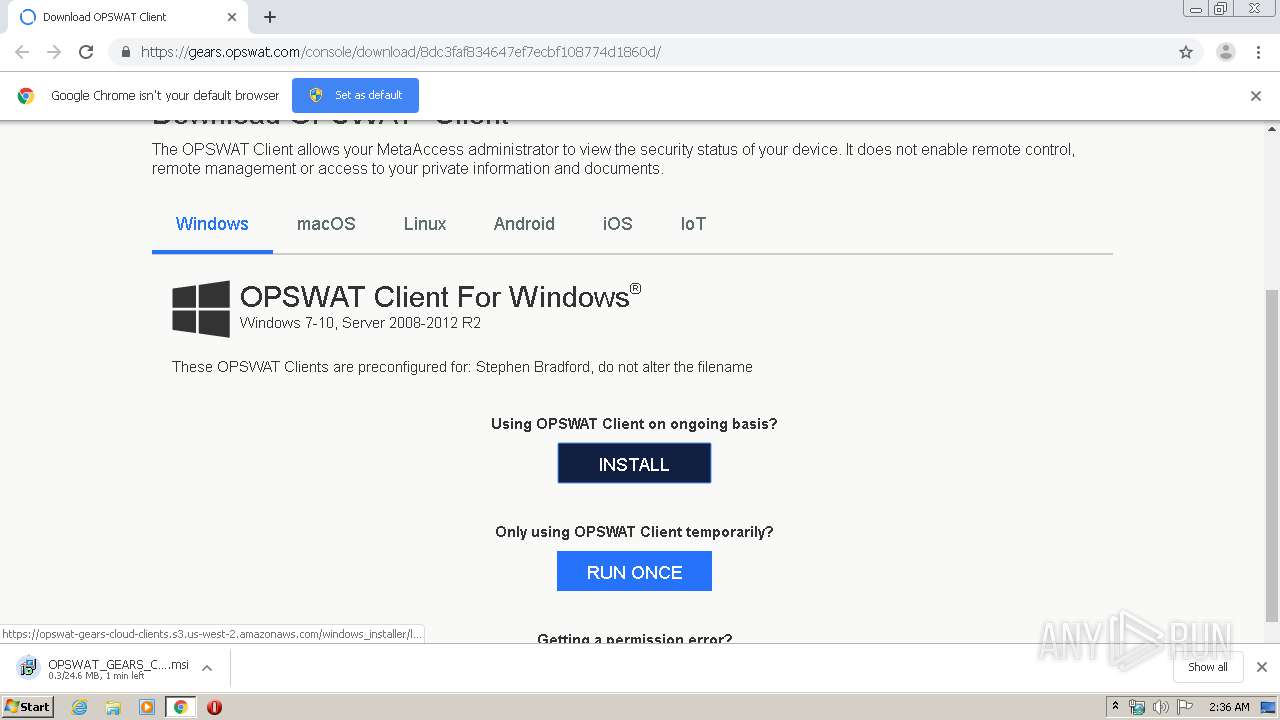
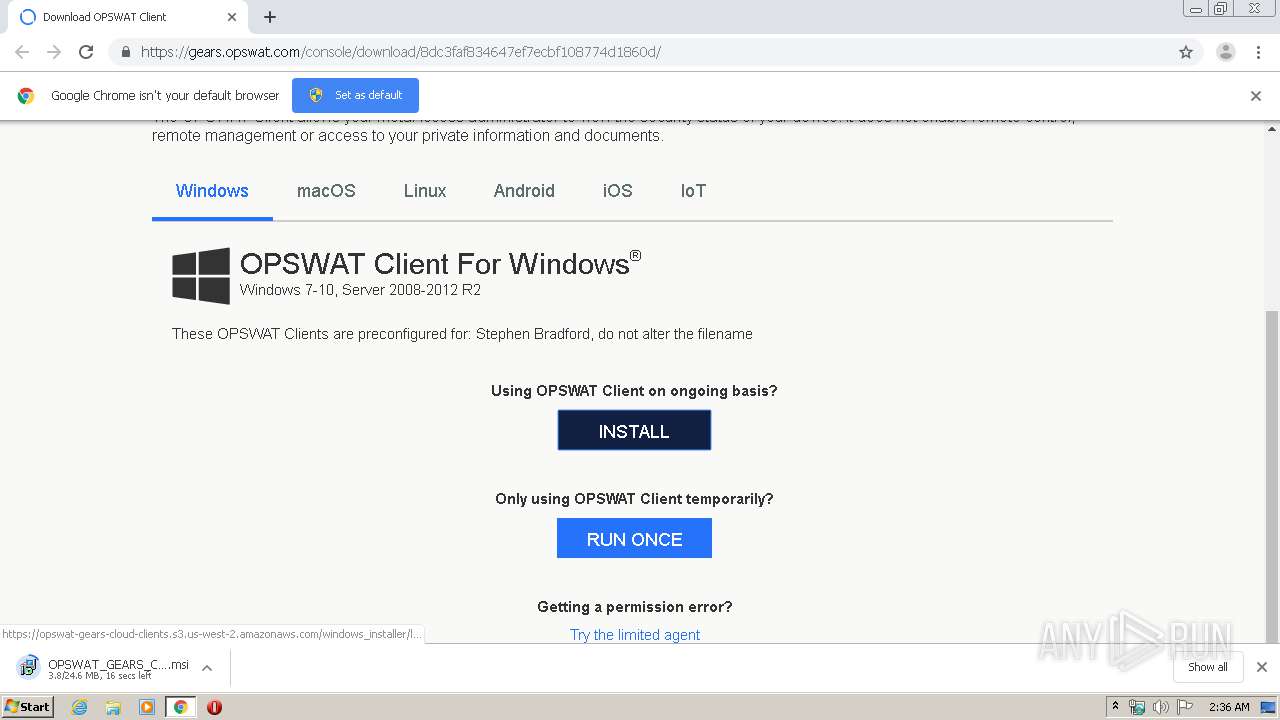
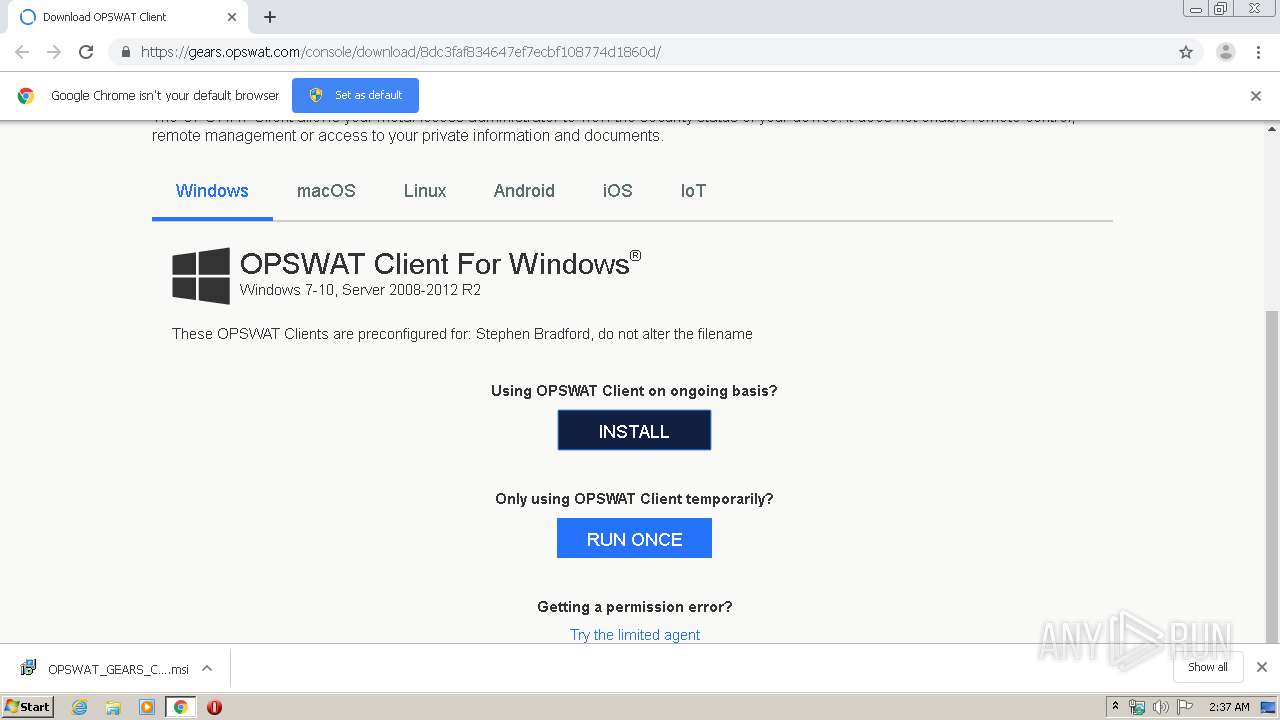
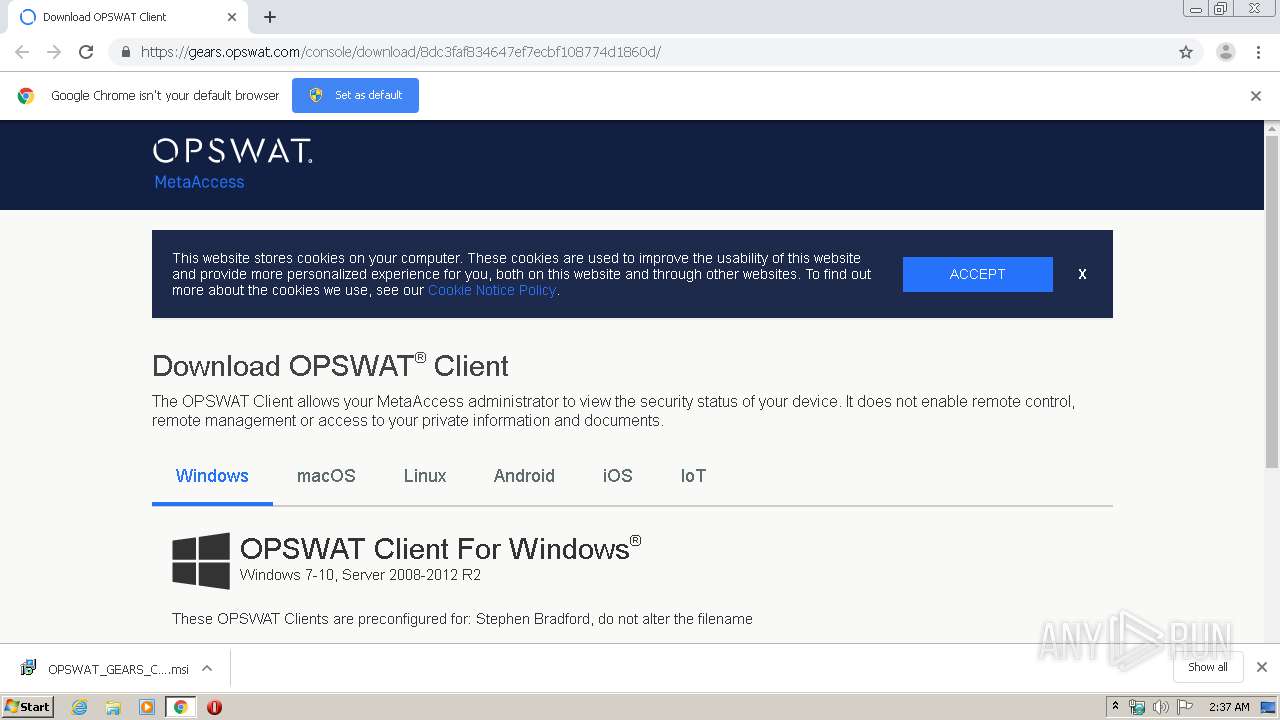
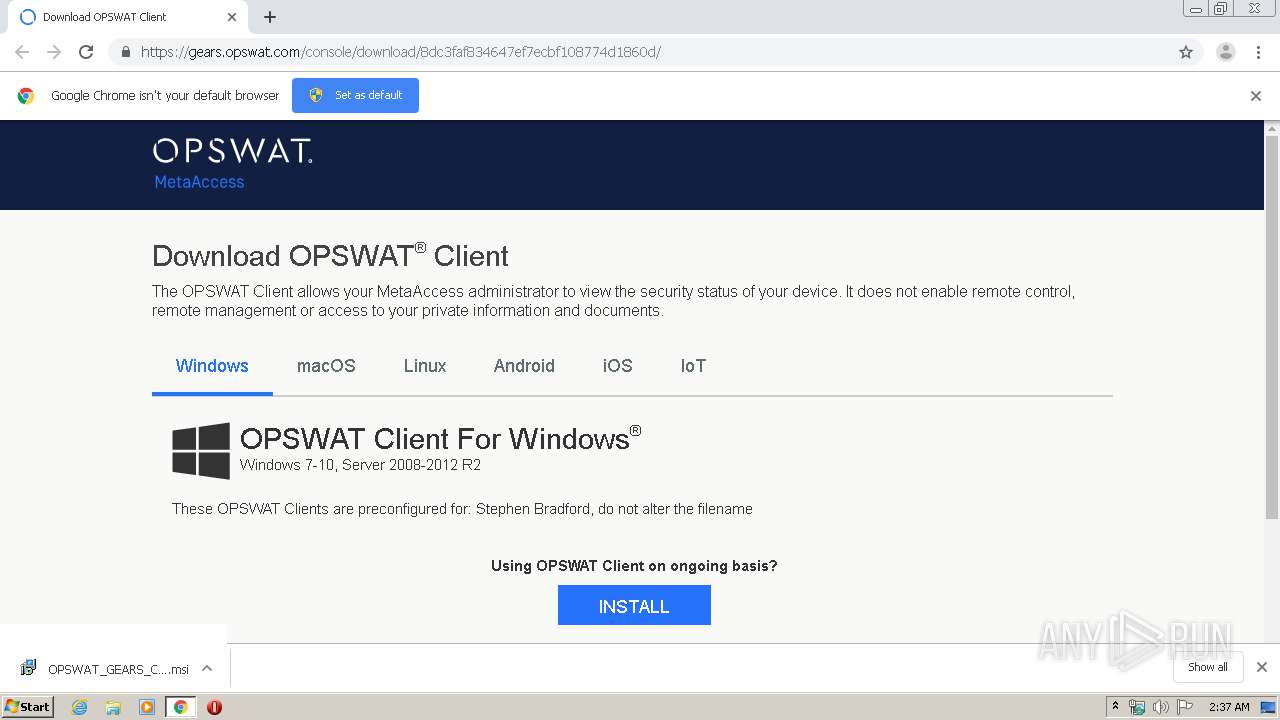
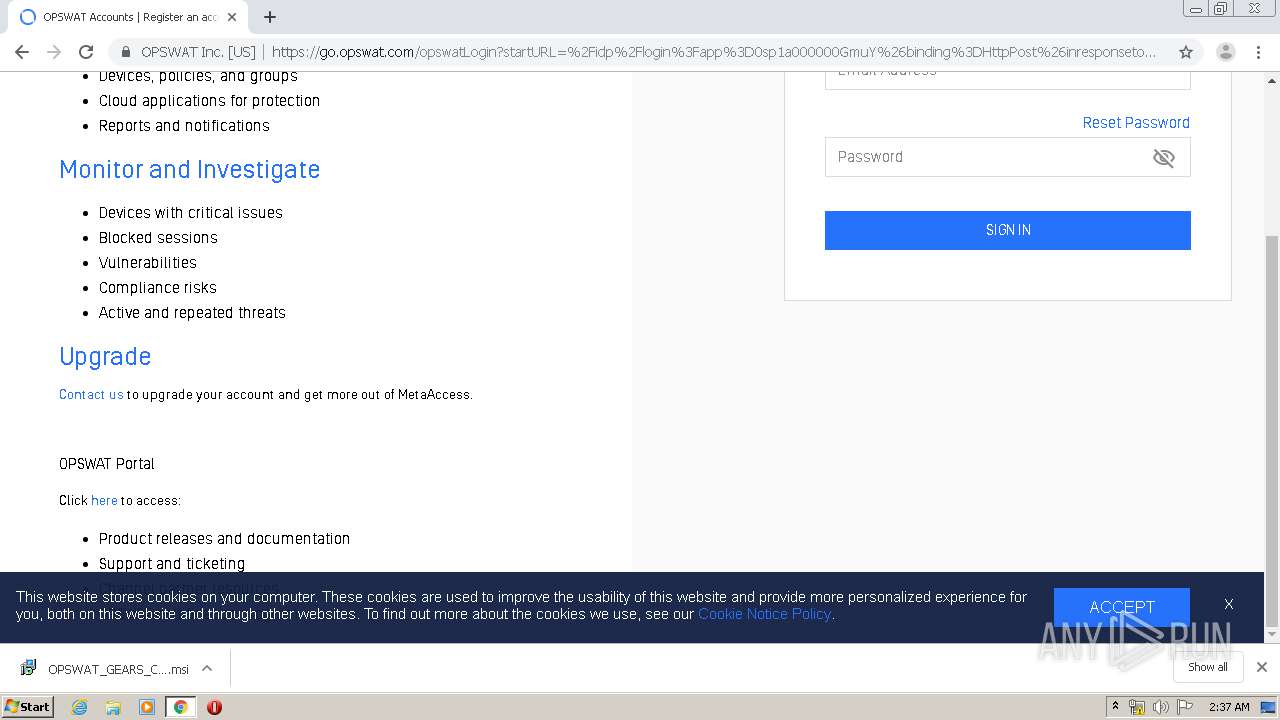
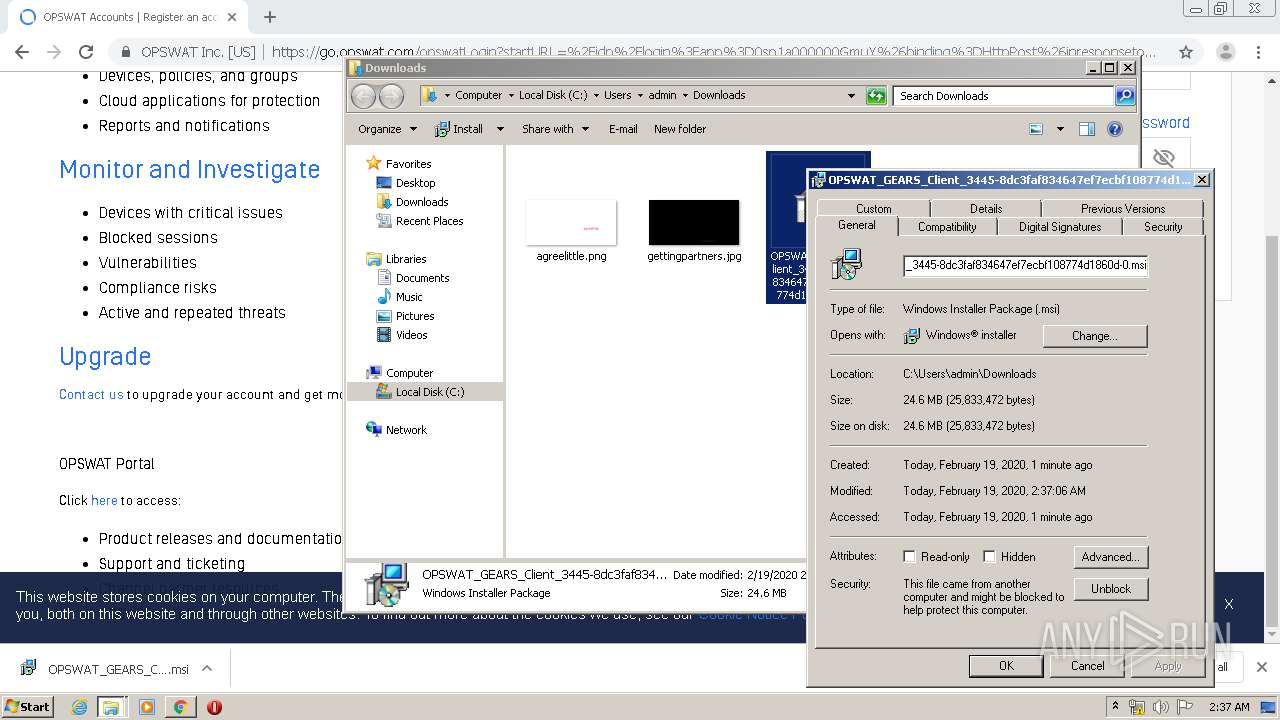
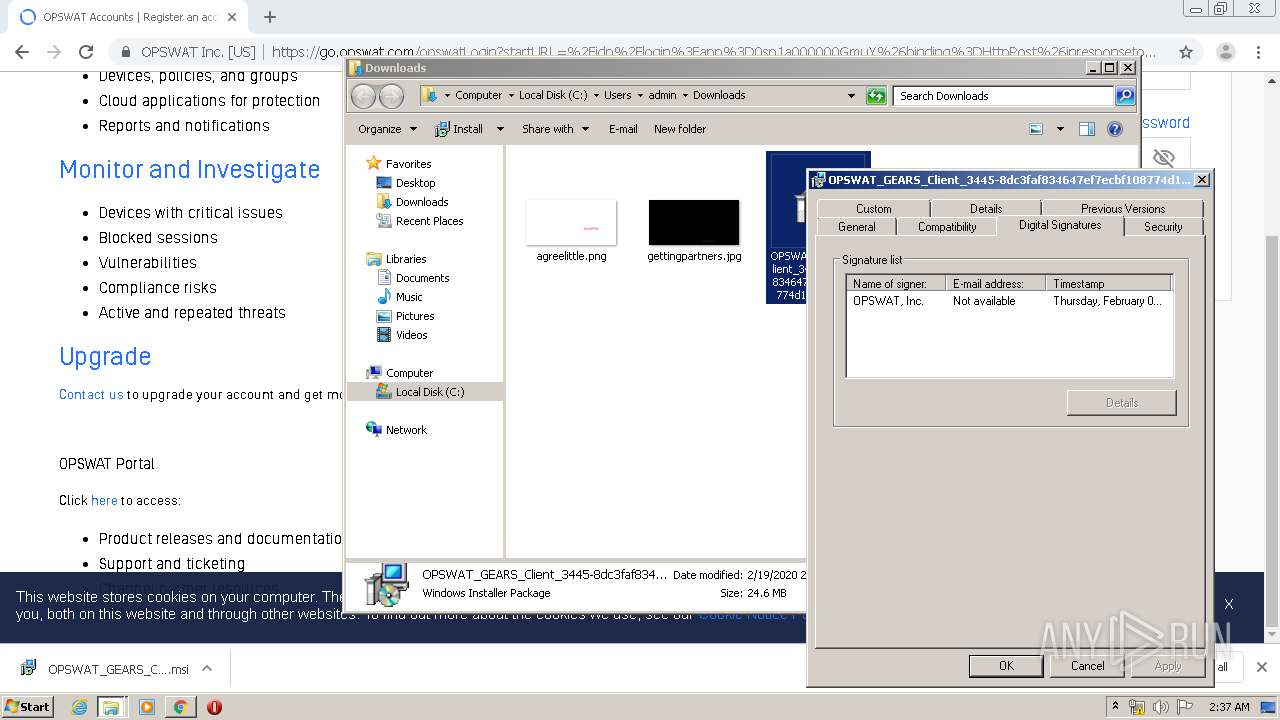
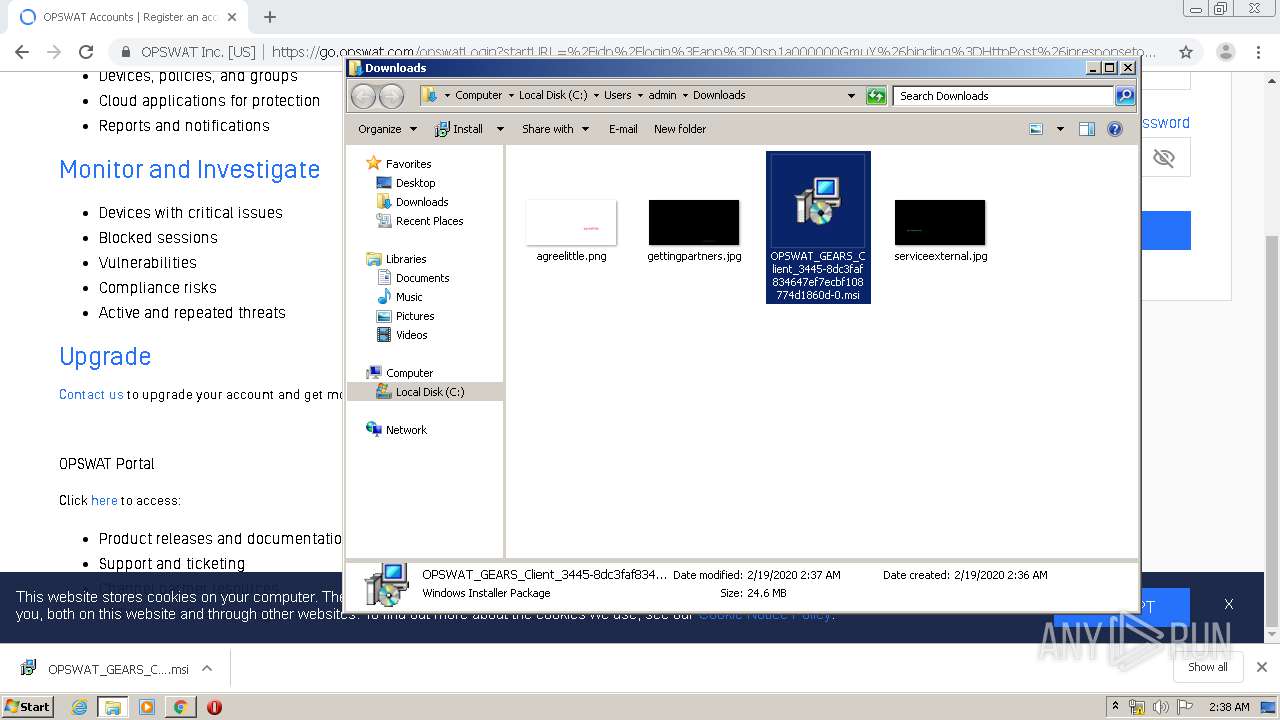
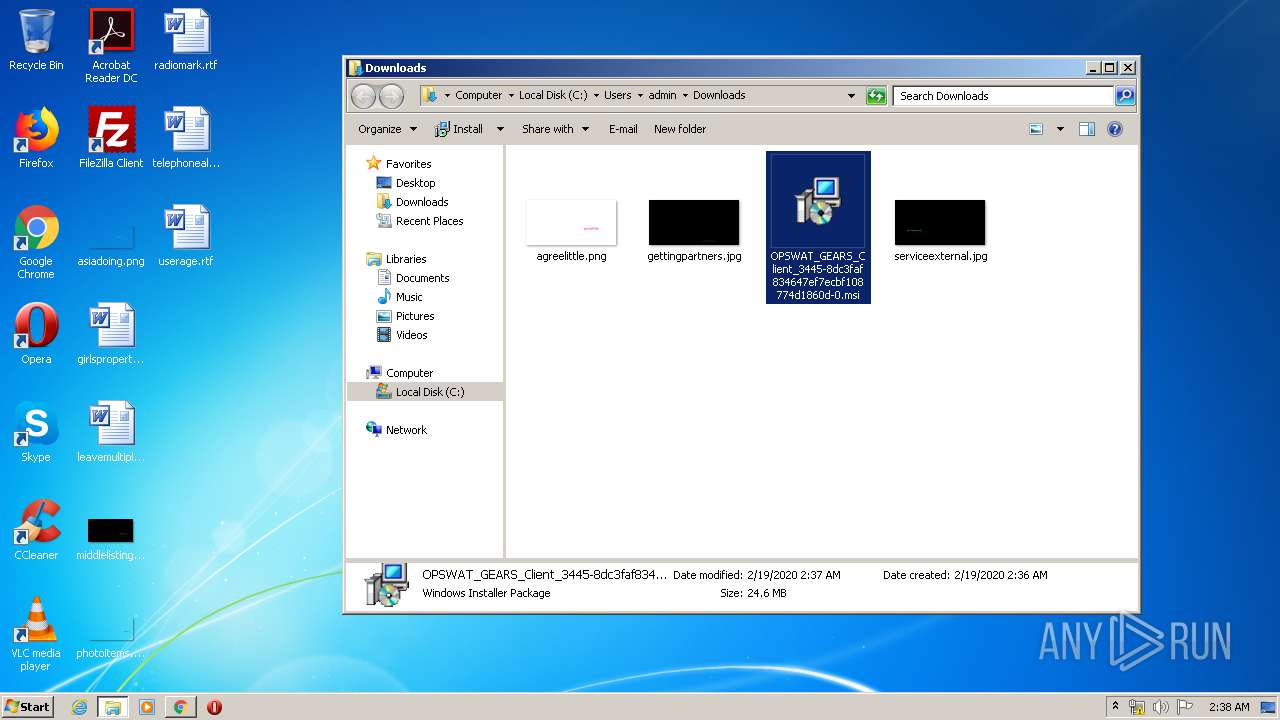
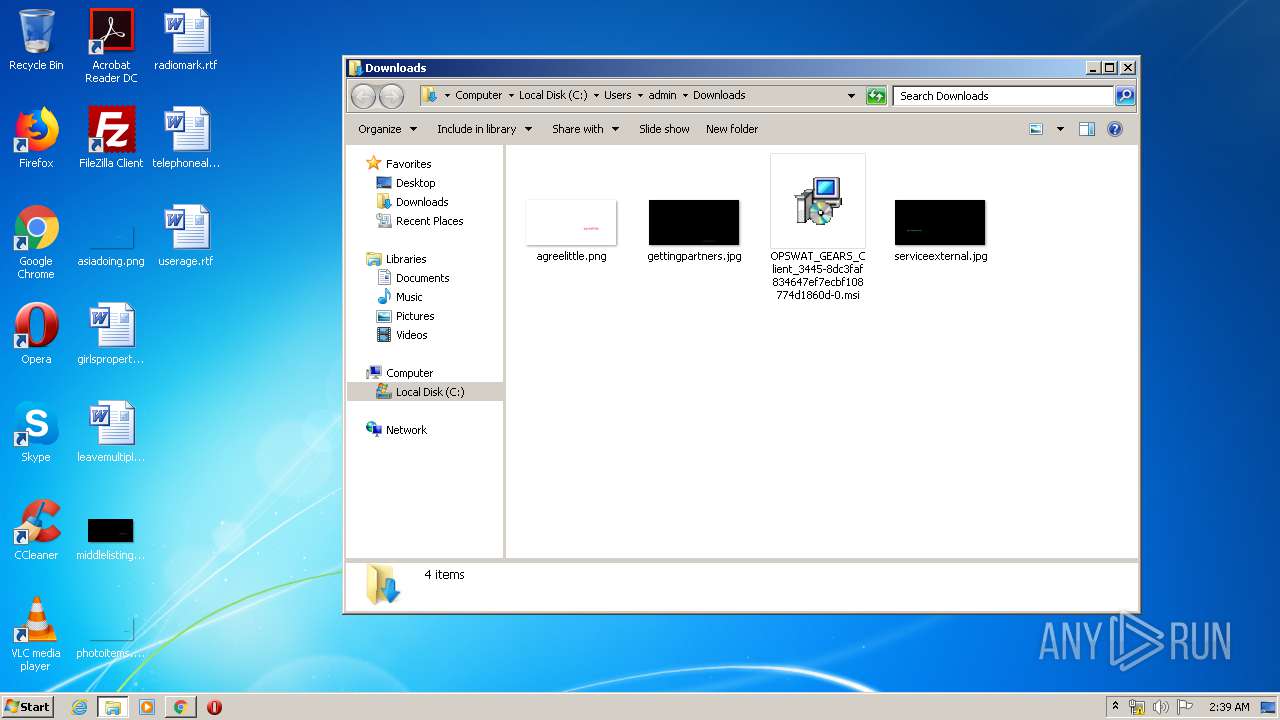
| URL: | https://gears.opswat.com/console/download/8dc3faf834647ef7ecbf108774d1860d/ |
| Full analysis: | https://app.any.run/tasks/89a32e53-06ce-4161-aac4-4055df2691ac |
| Verdict: | Malicious activity |
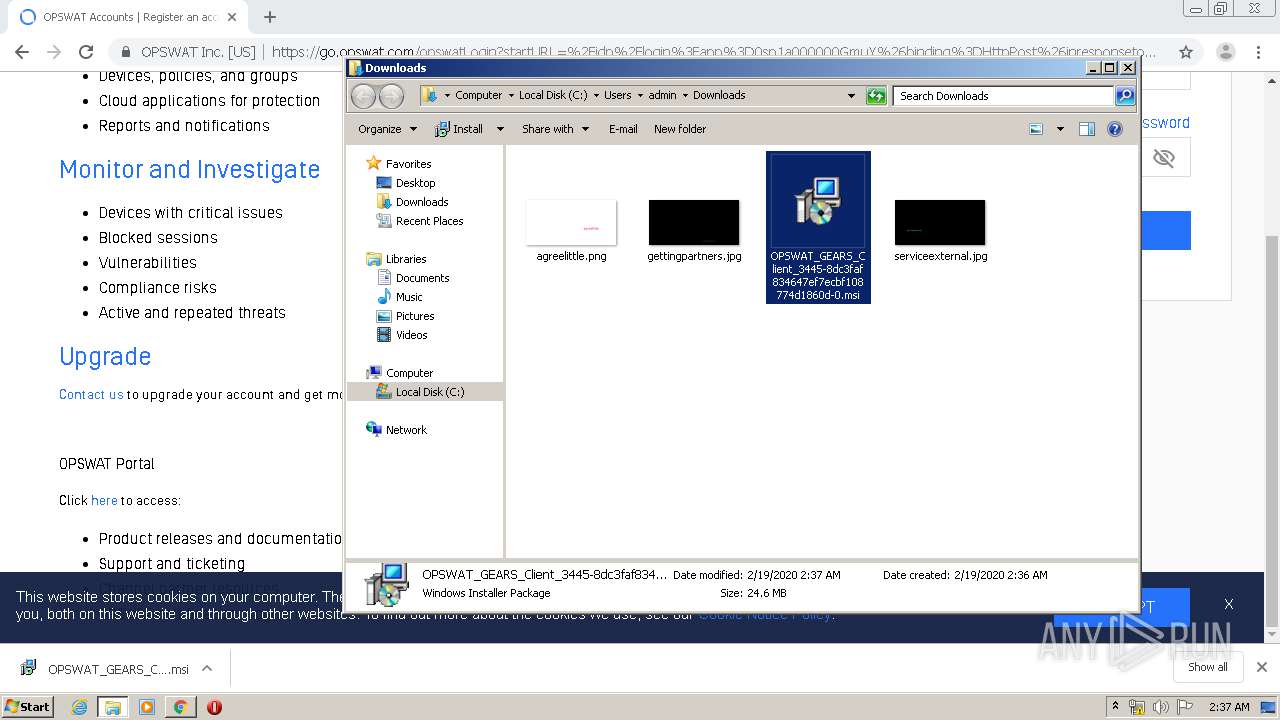
| Analysis date: | February 19, 2020, 02:36:20 |
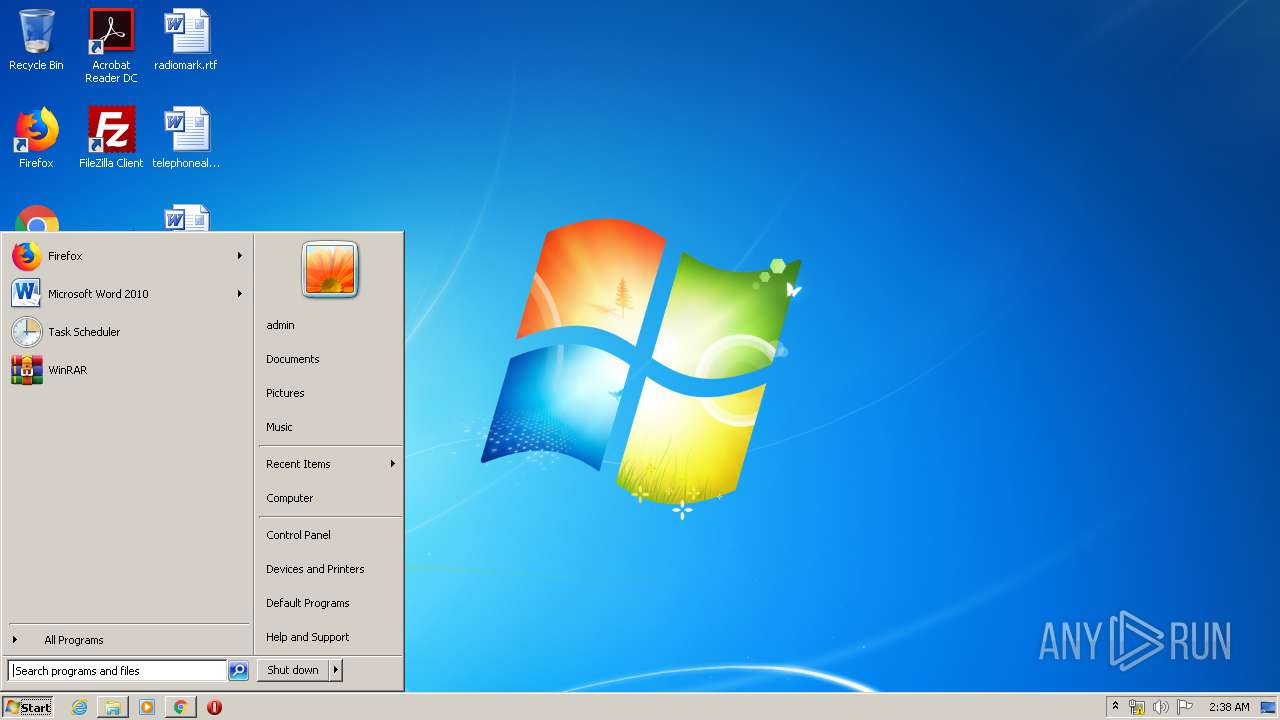
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 92C055EA7C2F56BD86B0499A465263BC |
| SHA1: | 2DBFD87D5F47C411A9335B264EFC109CB2B46351 |
| SHA256: | 6B9F27FA81DFCF12D484C445885530E1CBBA9C94E25344337768EABB76FE349D |
| SSDEEP: | 3:N8h+0tGKIKdLb0SLmd/EDITRSl8S34:2kWGKIKJISITRSin |
MALICIOUS
Application was dropped or rewritten from another process
- GearsInstaller.exe (PID: 3852)
- GearsSdkInstaller.EXE (PID: 3016)
- GearsAgentService.exe (PID: 2536)
- GearsHelper.exe (PID: 2848)
- 7z.exe (PID: 1348)
- GearsAgentService.exe (PID: 528)
- GearsAgentService.exe (PID: 3980)
- GearsHelper.exe (PID: 2340)
- Installer.exe (PID: 4072)
- Gears.exe (PID: 4040)
- waodwd.exe (PID: 3204)
- RefreshNotificationArea.exe (PID: 3236)
- wabpoes.exe (PID: 3504)
- Gears.exe (PID: 608)
- GearsAgentService.exe (PID: 3572)
- RefreshNotificationArea.exe (PID: 3712)
- RefreshNotificationArea.exe (PID: 3796)
- wa_3rd_party_host_32.exe (PID: 2428)
- RefreshNotificationArea.exe (PID: 4020)
- GearsAgentService.exe (PID: 3272)
- GearsAgentService.exe (PID: 2964)
- waodwd.exe (PID: 2736)
- wabpoes.exe (PID: 2936)
- RefreshNotificationArea.exe (PID: 1640)
- RefreshNotificationArea.exe (PID: 3604)
- Gears.exe (PID: 2692)
- wa_3rd_party_host_32.exe (PID: 2828)
- Gears.exe (PID: 3100)
- RefreshNotificationArea.exe (PID: 2888)
- RefreshNotificationArea.exe (PID: 5028)
- RefreshNotificationArea.exe (PID: 4808)
- Gears.exe (PID: 4820)
- GearsAgentService.exe (PID: 3172)
Runs injected code in another process
- GearsSdkInstaller.EXE (PID: 3016)
Starts NET.EXE for service management
- GearsInstaller.exe (PID: 3852)
Application was injected by another process
- dllhost.exe (PID: 4072)
Loads dropped or rewritten executable
- GearsAgentService.exe (PID: 2536)
- GearsHelper.exe (PID: 2848)
- GearsAgentService.exe (PID: 528)
- GearsAgentService.exe (PID: 3980)
- GearsHelper.exe (PID: 2340)
- Gears.exe (PID: 4040)
- wabpoes.exe (PID: 3504)
- RefreshNotificationArea.exe (PID: 3236)
- RefreshNotificationArea.exe (PID: 3796)
- Gears.exe (PID: 608)
- GearsAgentService.exe (PID: 3572)
- RefreshNotificationArea.exe (PID: 3712)
- RefreshNotificationArea.exe (PID: 4020)
- GearsAgentService.exe (PID: 3272)
- GearsAgentService.exe (PID: 2964)
- wabpoes.exe (PID: 2936)
- RefreshNotificationArea.exe (PID: 1640)
- Gears.exe (PID: 2692)
- RefreshNotificationArea.exe (PID: 3604)
- GearsAgentService.exe (PID: 3172)
- Gears.exe (PID: 3100)
- RefreshNotificationArea.exe (PID: 2888)
- Gears.exe (PID: 4820)
- RefreshNotificationArea.exe (PID: 4808)
- RefreshNotificationArea.exe (PID: 5028)
Changes the autorun value in the registry
- GearsInstaller.exe (PID: 3852)
- GearsAgentService.exe (PID: 528)
- GearsAgentService.exe (PID: 3272)
Changes settings of System certificates
- wabpoes.exe (PID: 3504)
- GearsAgentService.exe (PID: 528)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 2152)
- cmd.exe (PID: 2540)
- cmd.exe (PID: 2852)
Starts NET.EXE to view/change login properties
- cmd.exe (PID: 3984)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 3044)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1720)
Executed as Windows Service
- vssvc.exe (PID: 2944)
- GearsAgentService.exe (PID: 528)
- GearsHelper.exe (PID: 2340)
- GearsAgentService.exe (PID: 3272)
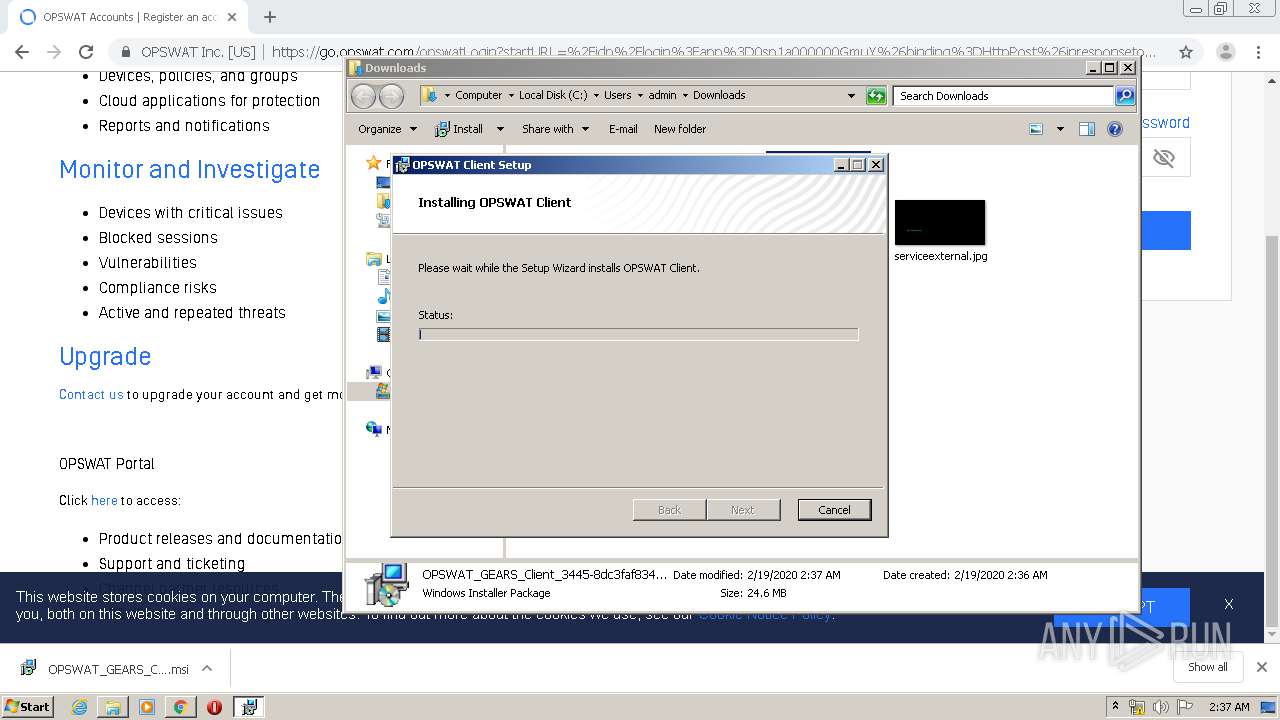
Executable content was dropped or overwritten
- msiexec.exe (PID: 3196)
- GearsSdkInstaller.EXE (PID: 3016)
- MSID73E.tmp (PID: 3920)
- Installer.exe (PID: 4072)
- GearsInstaller.exe (PID: 3852)
- 7z.exe (PID: 1348)
- GearsAgentService.exe (PID: 528)
- rundll32.exe (PID: 3816)
- wabpoes.exe (PID: 3504)
- rundll32.exe (PID: 2676)
- rundll32.exe (PID: 2368)
- rundll32.exe (PID: 3544)
- rundll32.exe (PID: 1708)
- rundll32.exe (PID: 3560)
- GearsAgentService.exe (PID: 3272)
- rundll32.exe (PID: 2924)
- rundll32.exe (PID: 3032)
- rundll32.exe (PID: 1348)
- rundll32.exe (PID: 1028)
- rundll32.exe (PID: 2164)
- rundll32.exe (PID: 4924)
- rundll32.exe (PID: 4896)
Starts CMD.EXE for commands execution
- GearsInstaller.exe (PID: 3852)
- Gears.exe (PID: 4040)
- GearsAgentService.exe (PID: 528)
- wabpoes.exe (PID: 3504)
- Gears.exe (PID: 608)
- GearsAgentService.exe (PID: 3272)
- Gears.exe (PID: 2692)
- Gears.exe (PID: 3100)
- wabpoes.exe (PID: 2936)
- Gears.exe (PID: 4820)
Creates files in the program directory
- GearsInstaller.exe (PID: 3852)
- Installer.exe (PID: 4072)
- 7z.exe (PID: 1348)
- GearsHelper.exe (PID: 2848)
- GearsAgentService.exe (PID: 528)
- waodwd.exe (PID: 3204)
- wabpoes.exe (PID: 3504)
- GearsAgentService.exe (PID: 3272)
Uses TASKKILL.EXE to kill process
- GearsInstaller.exe (PID: 3852)
Modifies the open verb of a shell class
- GearsAgentService.exe (PID: 2536)
Application launched itself
- GearsAgentService.exe (PID: 528)
- Gears.exe (PID: 4040)
- GearsAgentService.exe (PID: 3272)
- Gears.exe (PID: 608)
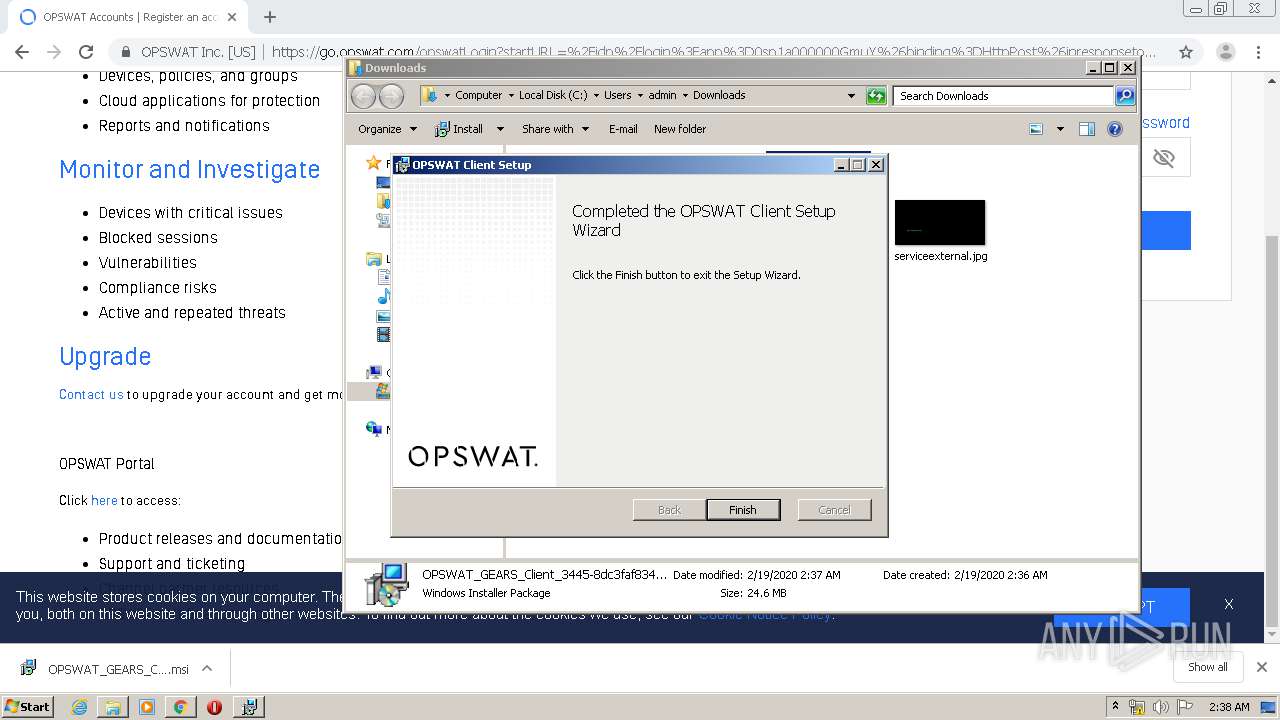
Creates a software uninstall entry
- GearsInstaller.exe (PID: 3852)
Removes files from Windows directory
- wabpoes.exe (PID: 3504)
- rundll32.exe (PID: 3816)
- GearsAgentService.exe (PID: 528)
- rundll32.exe (PID: 2676)
- rundll32.exe (PID: 2368)
- rundll32.exe (PID: 3544)
- rundll32.exe (PID: 3560)
- rundll32.exe (PID: 1708)
- rundll32.exe (PID: 2816)
- rundll32.exe (PID: 1544)
- rundll32.exe (PID: 2544)
- rundll32.exe (PID: 1352)
- rundll32.exe (PID: 2924)
- GearsAgentService.exe (PID: 3272)
- wabpoes.exe (PID: 2936)
- rundll32.exe (PID: 2904)
- rundll32.exe (PID: 3032)
- rundll32.exe (PID: 1348)
- rundll32.exe (PID: 1028)
- rundll32.exe (PID: 2164)
- rundll32.exe (PID: 3444)
- rundll32.exe (PID: 2136)
- rundll32.exe (PID: 2812)
- rundll32.exe (PID: 3948)
- rundll32.exe (PID: 4896)
- rundll32.exe (PID: 4924)
Searches for installed software
- wabpoes.exe (PID: 3504)
- GearsAgentService.exe (PID: 528)
- GearsAgentService.exe (PID: 3272)
- wabpoes.exe (PID: 2936)
Executed via COM
- unsecapp.exe (PID: 2792)
Creates files in the Windows directory
- rundll32.exe (PID: 3816)
- rundll32.exe (PID: 2676)
- rundll32.exe (PID: 2368)
- rundll32.exe (PID: 3544)
- rundll32.exe (PID: 3560)
- wabpoes.exe (PID: 3504)
- GearsAgentService.exe (PID: 528)
- rundll32.exe (PID: 1708)
- rundll32.exe (PID: 1544)
- rundll32.exe (PID: 2816)
- rundll32.exe (PID: 1352)
- rundll32.exe (PID: 2544)
- rundll32.exe (PID: 2924)
- GearsAgentService.exe (PID: 3272)
- wabpoes.exe (PID: 2936)
- rundll32.exe (PID: 2904)
- rundll32.exe (PID: 3032)
- rundll32.exe (PID: 1348)
- rundll32.exe (PID: 1028)
- rundll32.exe (PID: 2164)
- rundll32.exe (PID: 2136)
- rundll32.exe (PID: 3444)
- rundll32.exe (PID: 3948)
- rundll32.exe (PID: 4896)
- rundll32.exe (PID: 4924)
- rundll32.exe (PID: 2812)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 748)
- cmd.exe (PID: 3084)
- cmd.exe (PID: 840)
- cmd.exe (PID: 3172)
- cmd.exe (PID: 3672)
- cmd.exe (PID: 3384)
- cmd.exe (PID: 1872)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 3788)
- cmd.exe (PID: 2680)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 604)
- cmd.exe (PID: 1000)
- cmd.exe (PID: 3880)
- cmd.exe (PID: 2740)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 816)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 4428)
Creates files in the driver directory
- rundll32.exe (PID: 3816)
- rundll32.exe (PID: 2368)
- rundll32.exe (PID: 2676)
- rundll32.exe (PID: 3560)
- rundll32.exe (PID: 3544)
- rundll32.exe (PID: 1708)
- rundll32.exe (PID: 2924)
- rundll32.exe (PID: 3032)
- rundll32.exe (PID: 1348)
- rundll32.exe (PID: 1028)
- rundll32.exe (PID: 2164)
- rundll32.exe (PID: 4896)
- rundll32.exe (PID: 4924)
Creates or modifies windows services
- rundll32.exe (PID: 3544)
- rundll32.exe (PID: 2368)
- rundll32.exe (PID: 1348)
- rundll32.exe (PID: 4924)
Adds / modifies Windows certificates
- wabpoes.exe (PID: 3504)
- GearsAgentService.exe (PID: 528)
Starts application with an unusual extension
- cmd.exe (PID: 3436)
- cmd.exe (PID: 3960)
- cmd.exe (PID: 956)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 2584)
- cmd.exe (PID: 2164)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3436)
- cmd.exe (PID: 3960)
- cmd.exe (PID: 956)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 2584)
- cmd.exe (PID: 2164)
Low-level read access rights to disk partition
- wabpoes.exe (PID: 2936)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 1720)
Reads the hosts file
- chrome.exe (PID: 3864)
- chrome.exe (PID: 1720)
Reads settings of System Certificates
- chrome.exe (PID: 1720)
- chrome.exe (PID: 3864)
- wabpoes.exe (PID: 3504)
- GearsAgentService.exe (PID: 528)
- GearsAgentService.exe (PID: 3272)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2380)
- MsiExec.exe (PID: 2892)
- MsiExec.exe (PID: 836)
Creates a software uninstall entry
- msiexec.exe (PID: 3196)
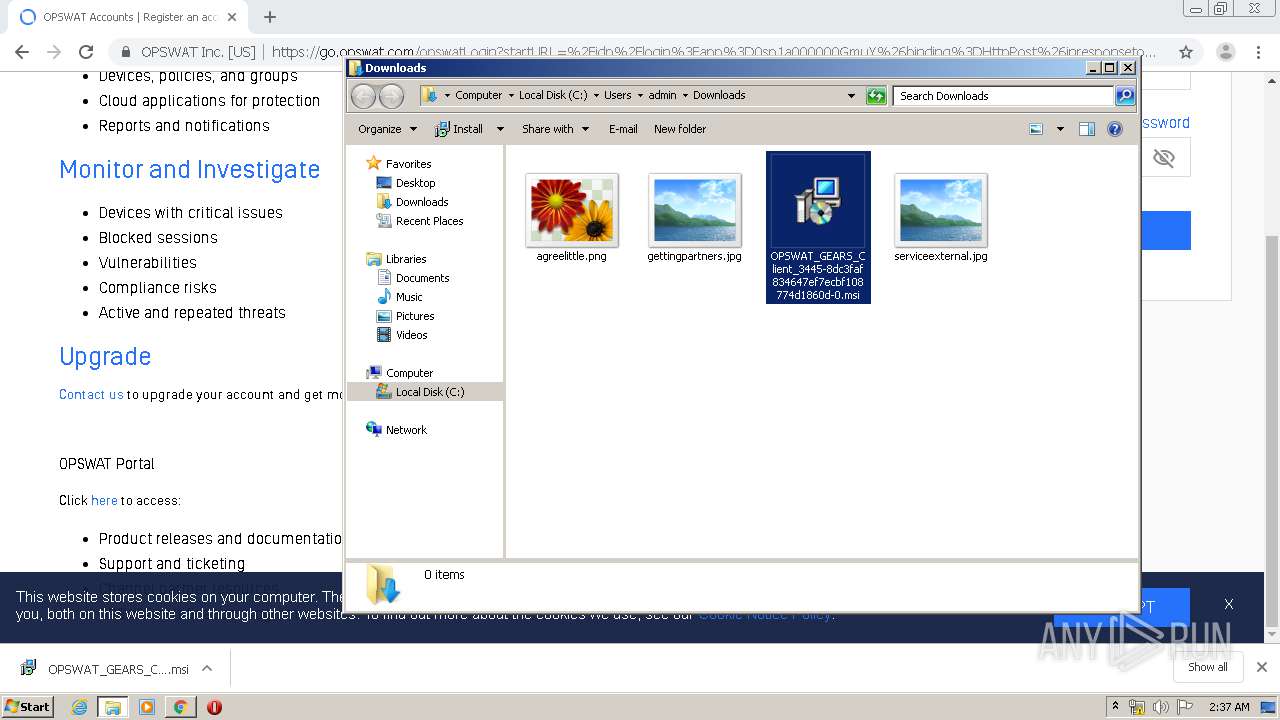
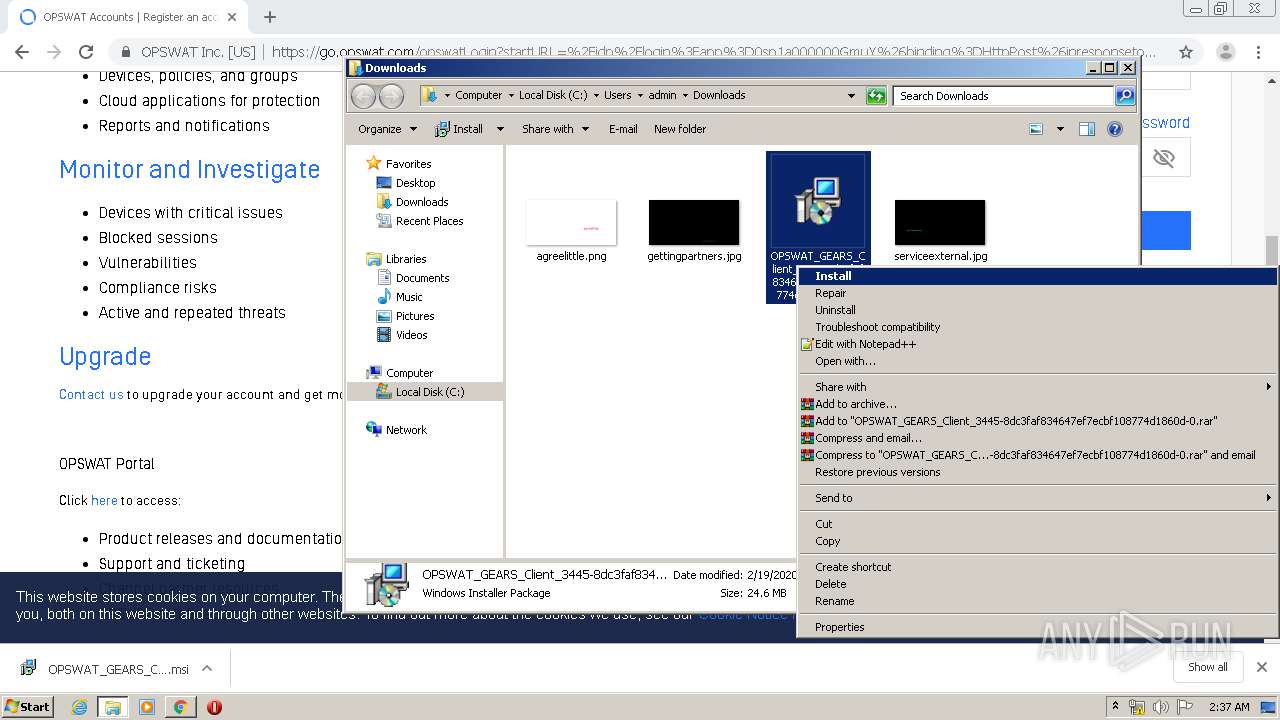
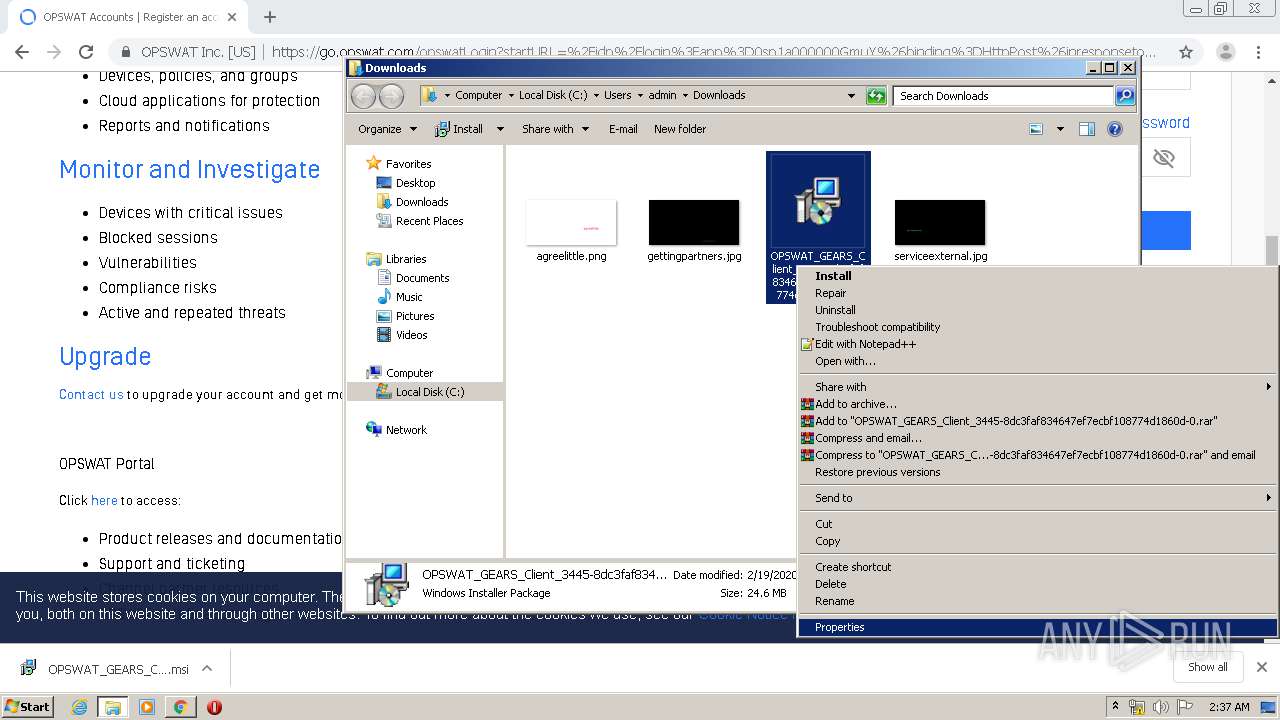
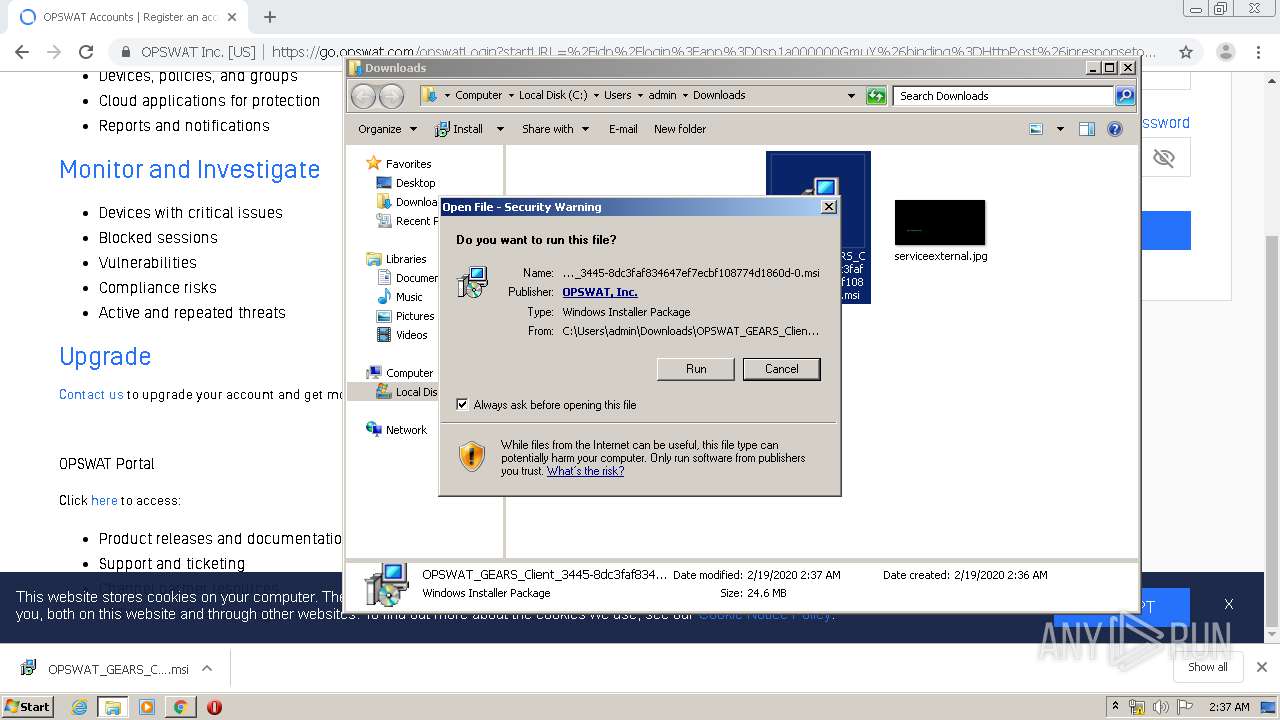
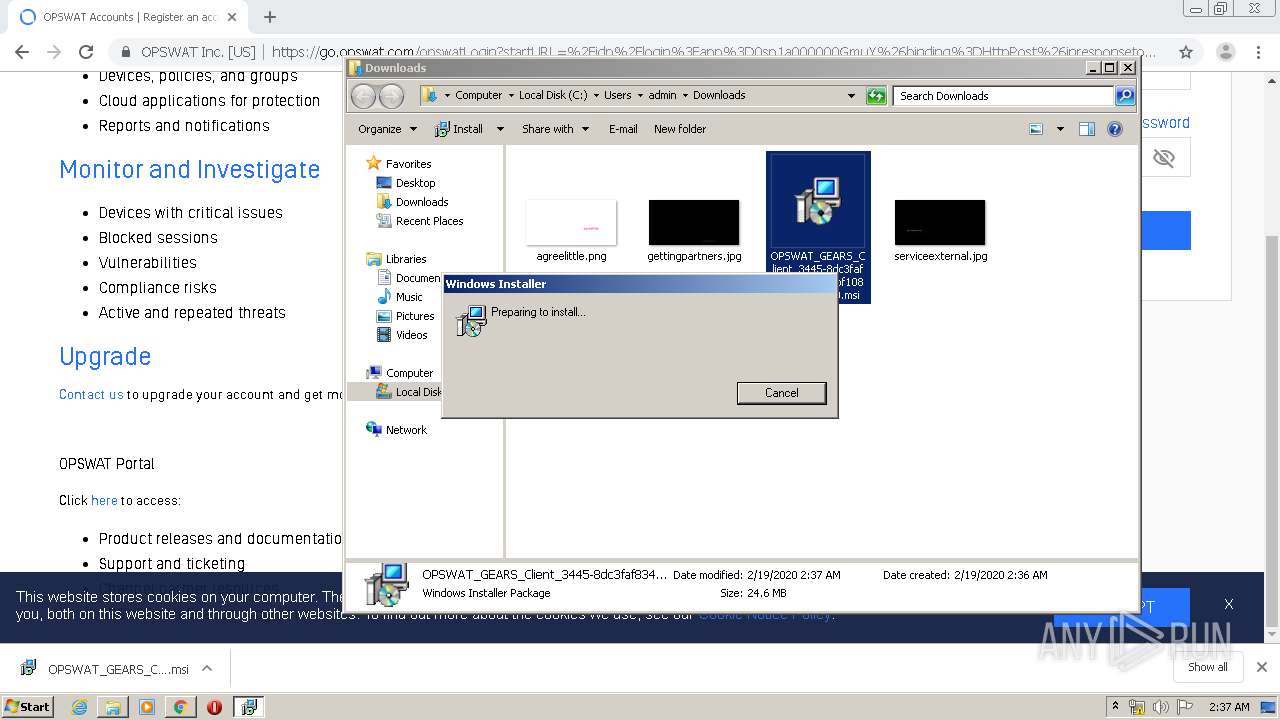
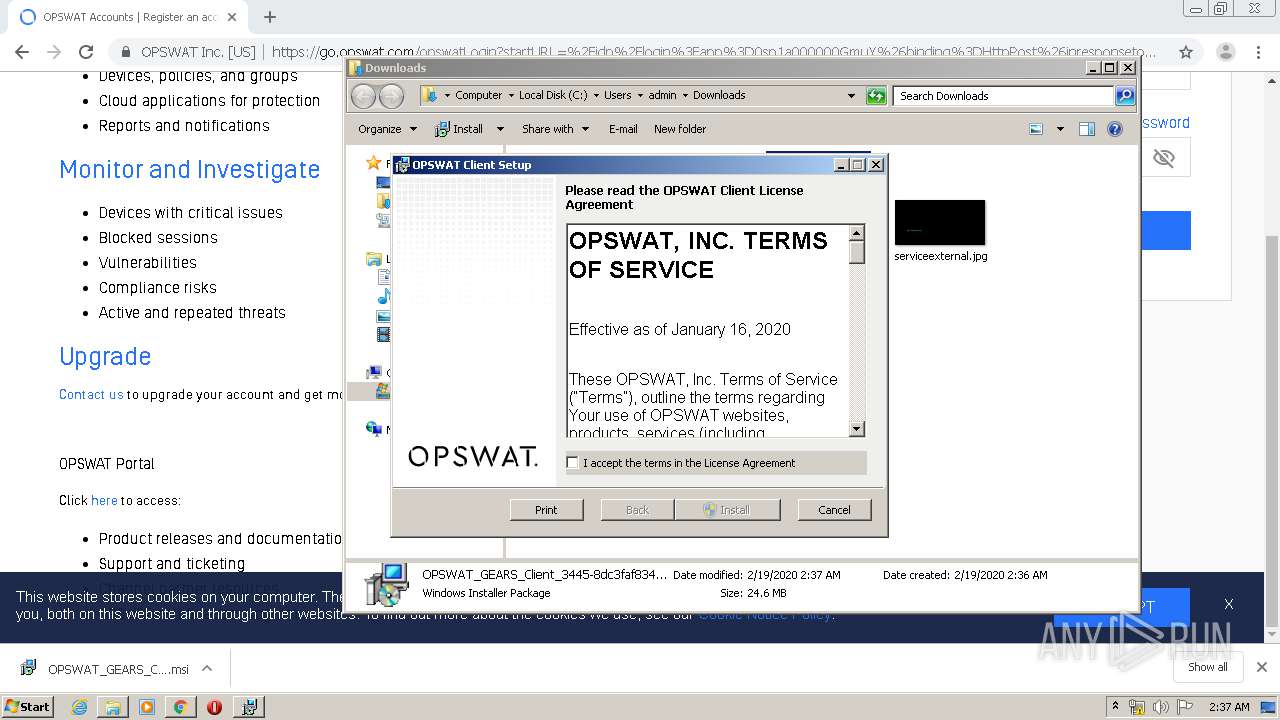
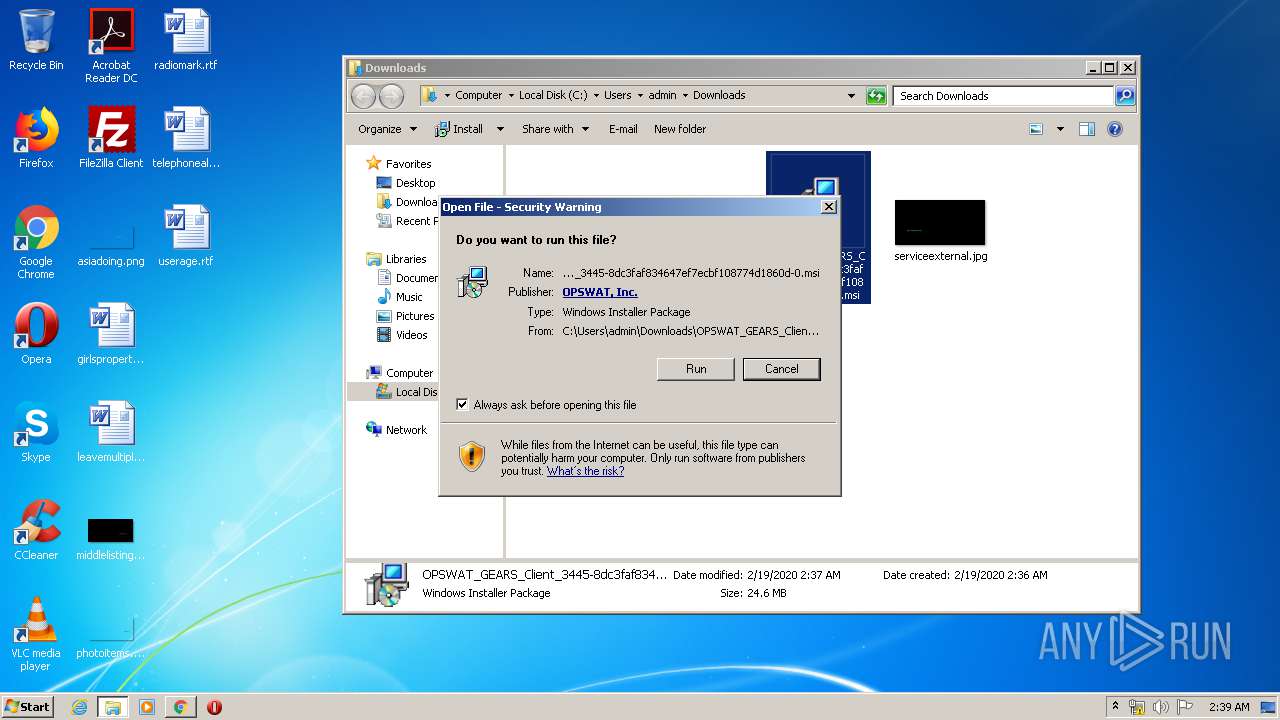
Manual execution by user
- msiexec.exe (PID: 872)
- msiexec.exe (PID: 2424)
- Gears.exe (PID: 4820)
- Gears.exe (PID: 3100)
Changes settings of System certificates
- chrome.exe (PID: 3864)
Creates files in the program directory
- MsiExec.exe (PID: 2380)
Starts application with an unusual extension
- msiexec.exe (PID: 3196)
Dropped object may contain Bitcoin addresses
- MSID73E.tmp (PID: 3920)
- GearsInstaller.exe (PID: 3852)
- Installer.exe (PID: 4072)
- GearsSdkInstaller.EXE (PID: 3016)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2944)
Searches for installed software
- msiexec.exe (PID: 3196)
Application launched itself
- msiexec.exe (PID: 3196)
- chrome.exe (PID: 1720)
Application was dropped or rewritten from another process
- MSID73E.tmp (PID: 3920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
307
Monitored processes
186
Malicious processes
41
Suspicious processes
22
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\Program Files\OPSWAT\OnDemand\GearsAgentService.exe" | C:\Program Files\OPSWAT\OnDemand\GearsAgentService.exe | services.exe | ||||||||||||
User: SYSTEM Company: OPSWAT, Inc. Integrity Level: SYSTEM Description: OPSWAT Client Exit code: 0 Version: 3.1.252.0 Modules
| |||||||||||||||
| 580 | "C:\Windows\system32\net.exe" stop WAOnDemand | C:\Windows\system32\net.exe | — | GearsInstaller.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | C:\Windows\system32\net1 user admin | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 604 | C:\Windows\system32\cmd.exe /S /C ""rundll32" setupapi,InstallHinfSection DefaultInstall 128 C:\Windows\system32\config\systemprofile\AppData\Local\Temp\libwamf.inf > "C:\Windows\system32\config\systemprofile\AppData\Local\Temp\OPS4B41.tmp" 2> "C:\Windows\system32\config\systemprofile\AppData\Local\Temp\OPS4B42.tmp"" | C:\Windows\system32\cmd.exe | — | GearsAgentService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 608 | "C:\Program Files\OPSWAT\GEARS Client\Gears.exe" -autorestarted | C:\Program Files\OPSWAT\GEARS Client\Gears.exe | Gears.exe | ||||||||||||
User: admin Company: OPSWAT, Inc. Integrity Level: HIGH Description: OPSWAT Client Exit code: 0 Version: 4, 1, 300, 0 Modules
| |||||||||||||||
| 676 | C:\Windows\system32\net1 stop WAOnDemand | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 748 | C:\Windows\system32\cmd.exe /S /C ""rundll32" setupapi,InstallHinfSection DefaultInstall 128 C:\Windows\system32\config\systemprofile\AppData\Local\Temp\libwasys.inf > "C:\Windows\system32\config\systemprofile\AppData\Local\Temp\OPS8638.tmp" 2> "C:\Windows\system32\config\systemprofile\AppData\Local\Temp\OPS8639.tmp"" | C:\Windows\system32\cmd.exe | — | GearsAgentService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 772 | "C:\Windows\system32\cmd.exe" /c mkdir "C:\ProgramData\ | C:\Windows\system32\cmd.exe | — | GearsInstaller.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,79100068742056296,2314238089483349697,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8032784018173950826 --mojo-platform-channel-handle=4300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 816 | "C:\Windows\system32\net.exe" stop OPSWATGEARSHelper | C:\Windows\system32\net.exe | — | GearsInstaller.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 090
Read events
3 599
Write events
3 460
Delete events
31
Modification events
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1720-13226553394463250 |
Value: 259 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
303
Suspicious files
121
Text files
541
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E4C9F32-6B8.pma | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7c579f6e-0c58-49f3-86db-afbce9a81d55.tmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66be1.TMP | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d97.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
474
TCP/UDP connections
285
DNS requests
52
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
528 | GearsAgentService.exe | GET | 200 | 23.37.43.27:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEFkUyCsPD%2By9CpjLIEuDric%3D | NL | der | 1.57 Kb | shared |
528 | GearsAgentService.exe | GET | 200 | 23.37.43.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | NL | der | 1.71 Kb | whitelisted |
528 | GearsAgentService.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | der | 1.74 Kb | whitelisted |
528 | GearsAgentService.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.starfieldtech.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT1ZqtwV0O1KcYi0gdzcFkHM%2BuArAQUJUWBaFAmOD07LSy%2BzWrZtj2zZmMCCDu3GKK3Cesq | US | der | 1.80 Kb | whitelisted |
3864 | chrome.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
3504 | wabpoes.exe | GET | 200 | 23.37.43.27:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEFkUyCsPD%2By9CpjLIEuDric%3D | NL | der | 1.57 Kb | shared |
3504 | wabpoes.exe | GET | 200 | 23.37.43.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | NL | der | 1.71 Kb | whitelisted |
528 | GearsAgentService.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.starfieldtech.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCAzkUhA%3D%3D | US | der | 1.70 Kb | whitelisted |
3864 | chrome.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCGviJ9xIRhzw | US | der | 1.73 Kb | whitelisted |
— | — | HEAD | 200 | 67.26.73.254:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?2002190239 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3864 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3864 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3864 | chrome.exe | 216.239.32.117:443 | www.google.com | Google Inc. | US | whitelisted |
3864 | chrome.exe | 34.211.178.80:443 | gears.opswat.com | Amazon.com, Inc. | US | unknown |
3864 | chrome.exe | 172.217.16.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3864 | chrome.exe | 172.217.18.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3864 | chrome.exe | 172.217.23.131:443 | www.google.se | Google Inc. | US | whitelisted |
3864 | chrome.exe | 173.194.76.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3864 | chrome.exe | 162.247.242.18:443 | bam.nr-data.net | New Relic | US | whitelisted |
3864 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
gears.opswat.com |
| unknown |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
www.google.com |
| malicious |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.google.se |
| whitelisted |
js-agent.newrelic.com |
| whitelisted |
bam.nr-data.net |
| whitelisted |
Threats
Process | Message |
|---|---|
GearsInstaller.exe | |
GearsInstaller.exe | C:\ProgramData |
GearsInstaller.exe | |
GearsInstaller.exe | C:\ProgramData\OPSWAT\Gears\logs\install.log |
GearsInstaller.exe | C:\ProgramData |
GearsInstaller.exe | |
GearsInstaller.exe | |
GearsInstaller.exe | C:\ProgramData |
GearsInstaller.exe | |
GearsInstaller.exe | C:\ProgramData |