| File name: | Gem Hack In Growtopia No Survey No Download WORKING .exe |
| Full analysis: | https://app.any.run/tasks/94cecc46-ad03-4062-bd48-9684e96df0e1 |
| Verdict: | Suspicious activity |
| Analysis date: | June 08, 2018, 09:26:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1739AB23CB3662E7FE24EBBEC859E24A |
| SHA1: | 6D6368D8365C0FE40ECE24FE318E0F7CE5BD8B0A |
| SHA256: | 6B940ED25BC105D33E8BA7D0968D648DB119477A08AEAC808A46B4212DE657F4 |
| SSDEEP: | 12288:0z5cWN3aPbD3x6imu00ufz6HSkdxvN+RrA55N2uSgcbUe6Q8SAEe3nTJlu:0NrNKPbDVmH0uf+HSkHl+RsnNFSgcD6+ |
MALICIOUS
Application was dropped or rewritten from another process
- DownloadManager.exe (PID: 2324)
- DownloadManager.exe (PID: 1352)
- DownloadManager.exe (PID: 3952)
SUSPICIOUS
Executable content was dropped or overwritten
- Gem Hack In Growtopia No Survey No Download WORKING .exe (PID: 2780)
INFO
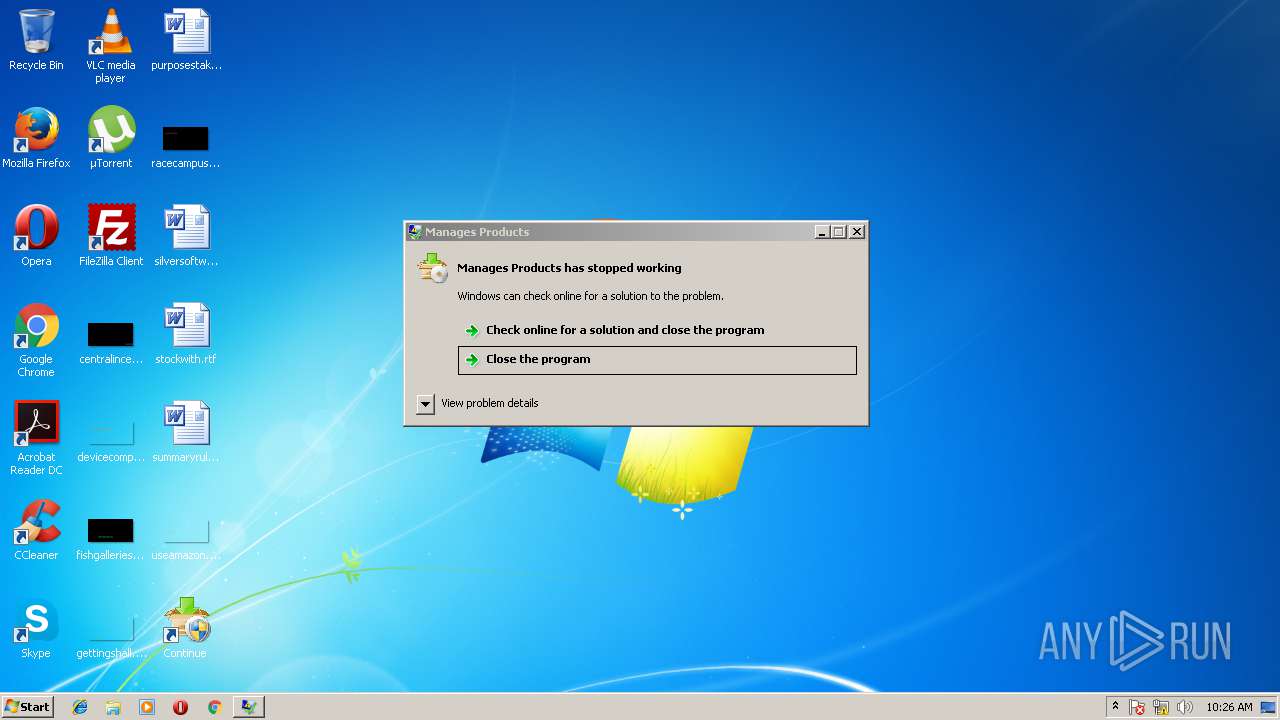
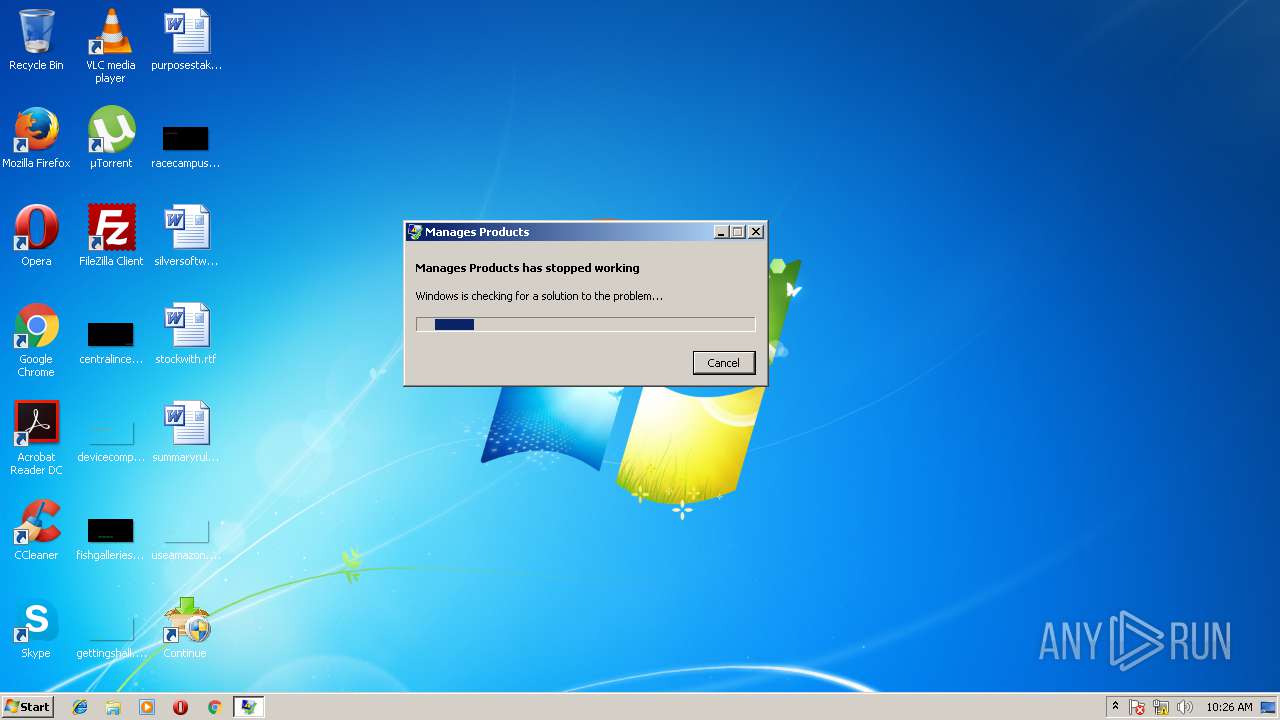
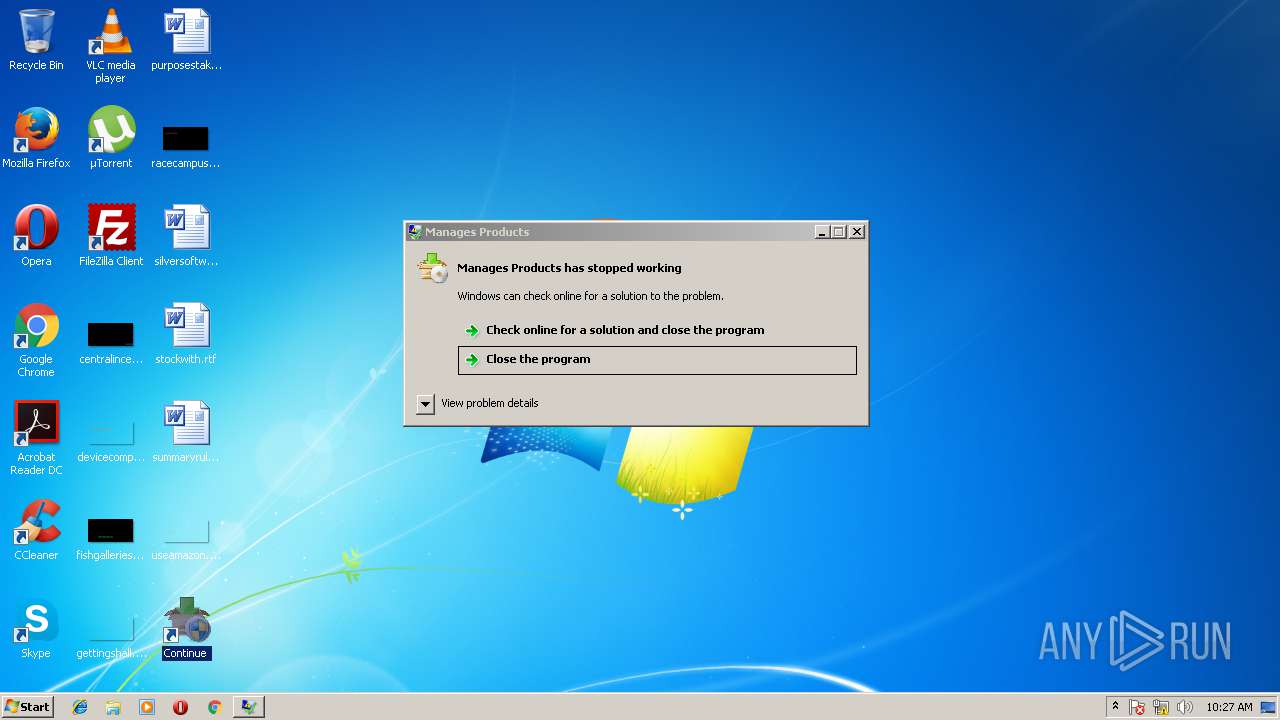
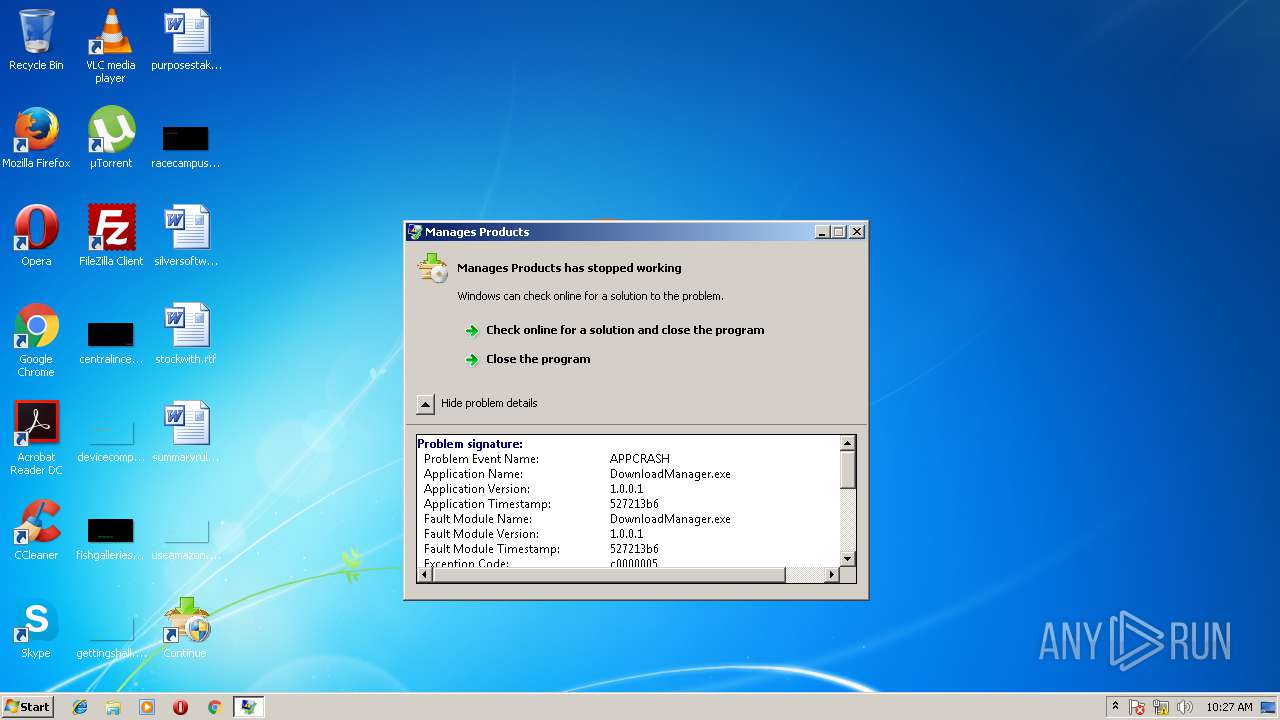
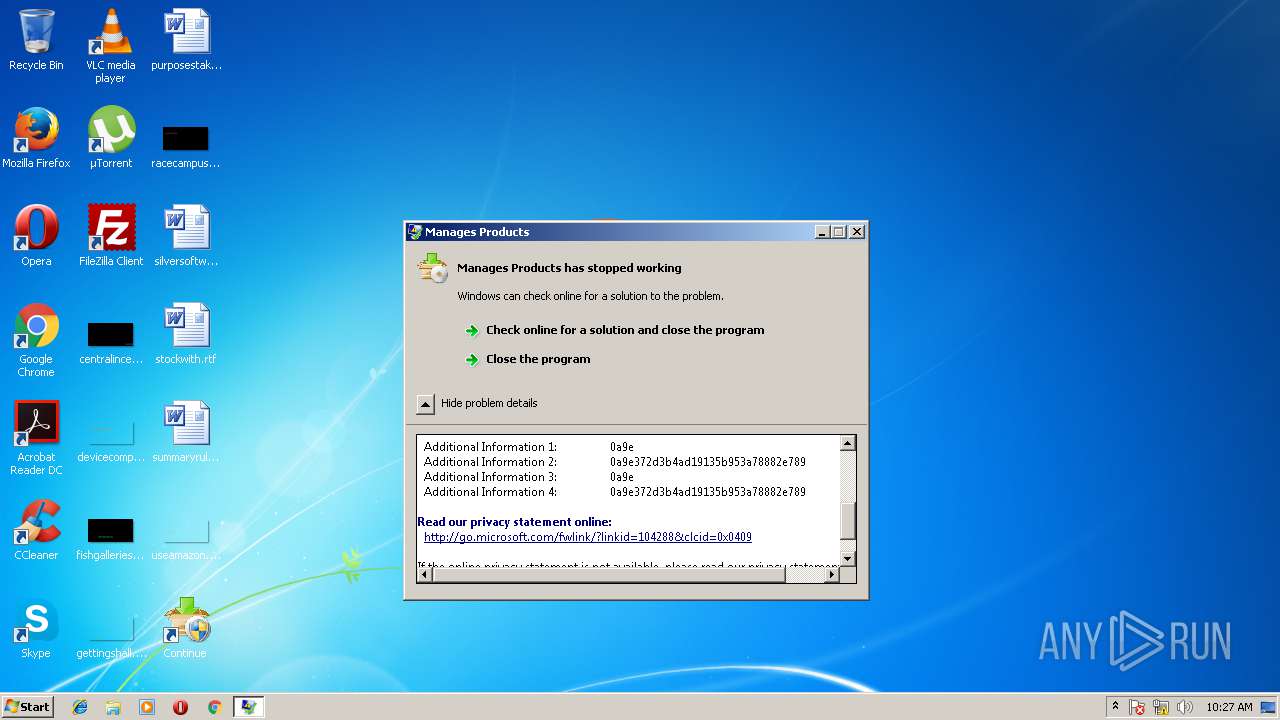
Application was crashed
- DownloadManager.exe (PID: 2324)
- DownloadManager.exe (PID: 1352)
Dropped object may contain URL's
- DownloadManager.exe (PID: 2324)
- DownloadManager.exe (PID: 1352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| Comments: | Game Cheat Tool |
| CompanyName: | Game Cheat Tool |
| FileDescription: | Download the cheat for this game |
| LegalCopyright: | JS Marketing ltd Jenna Stevens |
| LegalTrademarks: | Game Cheat Tool |
| ProductName: | Game Cheat Tool |
| ProductVersion: | 3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
| Comments: | Game Cheat Tool |
| CompanyName: | Game Cheat Tool |
| FileDescription: | Download the cheat for this game |
| LegalCopyright: | JS Marketing ltd Jenna Stevens |
| LegalTrademarks: | Game Cheat Tool |
| ProductName: | Game Cheat Tool |
| ProductVersion: | 3.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x00000D08 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.12913 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19512 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
49
Monitored processes
5
Malicious processes
0
Suspicious processes
0
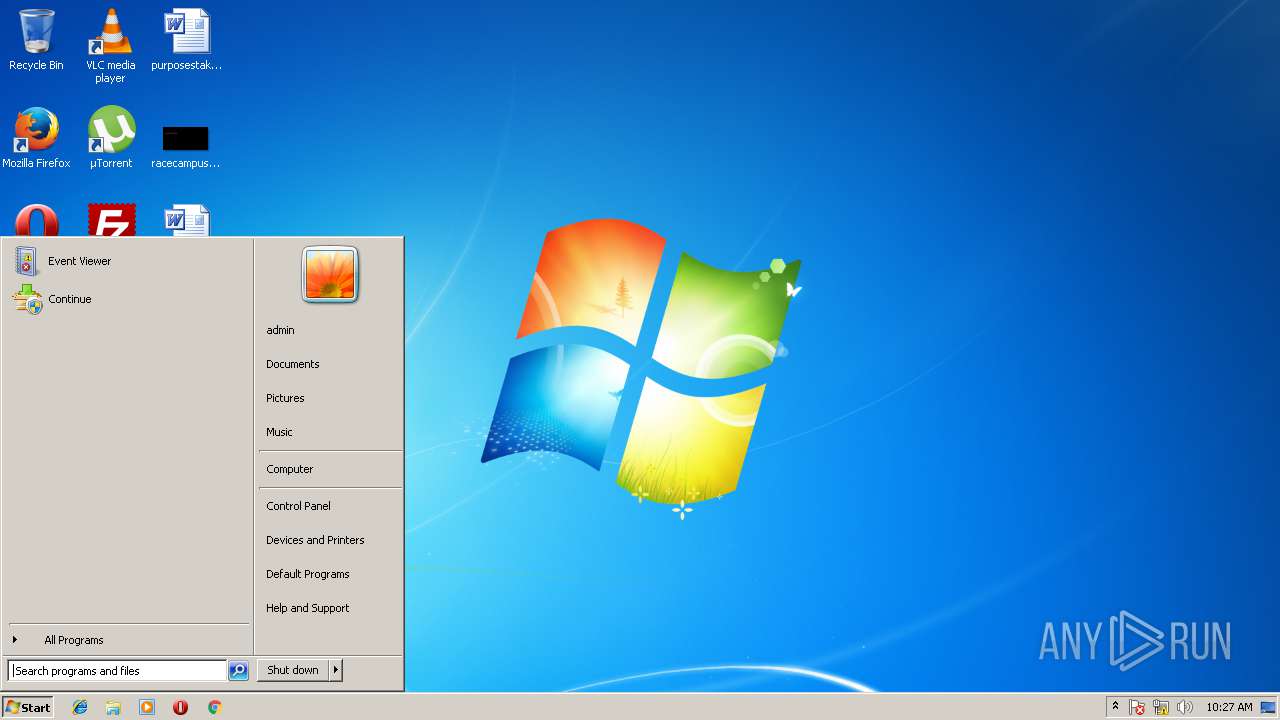
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1352 | C:\Users\admin\AppData\Local\Temp\DownloadManager.exe " /PID=1625 /SUBPID=0 /DISTID=1397 /NETWORDK=1 /CID=0 /PRODUCT_ID=1316 /SERVER_URL=http://installer.ppdownload.com " | C:\Users\admin\AppData\Local\Temp\DownloadManager.exe | Gem Hack In Growtopia No Survey No Download WORKING .exe | ||||||||||||
User: admin Company: @ Integrity Level: HIGH Description: Manages Products Exit code: 3221225477 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1732 | "C:\Users\admin\AppData\Local\Temp\Gem Hack In Growtopia No Survey No Download WORKING .exe" | C:\Users\admin\AppData\Local\Temp\Gem Hack In Growtopia No Survey No Download WORKING .exe | — | explorer.exe | |||||||||||
User: admin Company: Game Cheat Tool Integrity Level: MEDIUM Description: Download the cheat for this game Exit code: 3221226540 Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\AppData\Local\Temp\DownloadManager.exe" C:\Users\admin\AppData\Local\Temp\DownloadManager.exe " /PID=1625 /SUBPID=0 /DISTID=1397 /NETWORDK=1 /CID=0 /PRODUCT_ID=1316 /SERVER_URL=http://installer.ppdownload.com " | C:\Users\admin\AppData\Local\Temp\DownloadManager.exe | explorer.exe | ||||||||||||
User: admin Company: @ Integrity Level: HIGH Description: Manages Products Exit code: 3221225477 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\AppData\Local\Temp\Gem Hack In Growtopia No Survey No Download WORKING .exe" | C:\Users\admin\AppData\Local\Temp\Gem Hack In Growtopia No Survey No Download WORKING .exe | explorer.exe | ||||||||||||
User: admin Company: Game Cheat Tool Integrity Level: HIGH Description: Download the cheat for this game Exit code: 0 Modules
| |||||||||||||||
| 3952 | "C:\Users\admin\AppData\Local\Temp\DownloadManager.exe" C:\Users\admin\AppData\Local\Temp\DownloadManager.exe " /PID=1625 /SUBPID=0 /DISTID=1397 /NETWORDK=1 /CID=0 /PRODUCT_ID=1316 /SERVER_URL=http://installer.ppdownload.com " | C:\Users\admin\AppData\Local\Temp\DownloadManager.exe | — | explorer.exe | |||||||||||
User: admin Company: @ Integrity Level: MEDIUM Description: Manages Products Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
1 093
Read events
1 069
Write events
19
Delete events
5
Modification events
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D3388703-5092-487C-8217-11ADA1CA68B5} |
| Operation: | write | Name: | |
Value: CBrowserExternal Class | |||
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D3388703-5092-487C-8217-11ADA1CA68B5}\LocalServer32 |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\Temp\DownloadManager.exe" | |||
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D3388703-5092-487C-8217-11ADA1CA68B5}\LocalServer32 |
| Operation: | write | Name: | ServerExecutable |
Value: C:\Users\admin\AppData\Local\Temp\DownloadManager.exe | |||
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D3388703-5092-487C-8217-11ADA1CA68B5}\TypeLib |
| Operation: | write | Name: | |
Value: {DCABB943-792E-44C4-9029-ECBEE6265AF9} | |||
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D3388703-5092-487C-8217-11ADA1CA68B5}\Version |
| Operation: | write | Name: | |
Value: 1.0 | |||
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{DCABB943-792E-44C4-9029-ECBEE6265AF9}\1.0 |
| Operation: | write | Name: | |
Value: SmartInstallerLib | |||
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{DCABB943-792E-44C4-9029-ECBEE6265AF9}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 0 | |||
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{DCABB943-792E-44C4-9029-ECBEE6265AF9}\1.0\0\win32 |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\DownloadManager.exe | |||
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{DCABB943-792E-44C4-9029-ECBEE6265AF9}\1.0\HELPDIR |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp | |||
| (PID) Process: | (1352) DownloadManager.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{3408AC0D-510E-4808-8F7B-6B70B1F88534} |
| Operation: | write | Name: | |
Value: IBrowserExternals | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
2
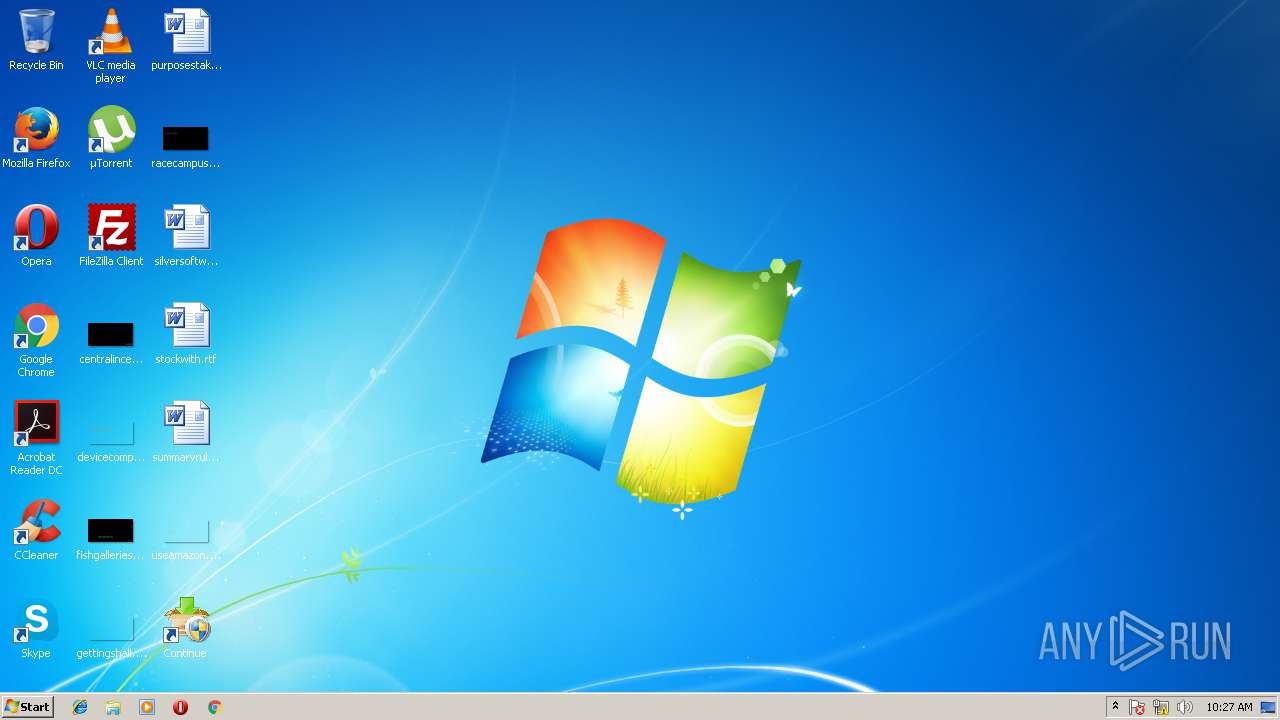
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2780 | Gem Hack In Growtopia No Survey No Download WORKING .exe | C:\Users\admin\AppData\Local\Temp\DownloadManager.exe | executable | |
MD5:— | SHA256:— | |||
| 1352 | DownloadManager.exe | C:\Users\admin\Desktop\Continue .lnk | lnk | |
MD5:— | SHA256:— | |||
| 2324 | DownloadManager.exe | C:\Users\admin\Desktop\Continue .lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2524 | WerFault.exe | GET | — | 13.66.59.253:80 | http://watson.microsoft.com/StageOne/DownloadManager_exe/1_0_0_1/527213b6/DownloadManager_exe/1_0_0_1/527213b6/c0000005/00008e62.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2524 | WerFault.exe | 13.66.59.253:80 | watson.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
installer.ppdownload.com |
| malicious |
watson.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2524 | WerFault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |