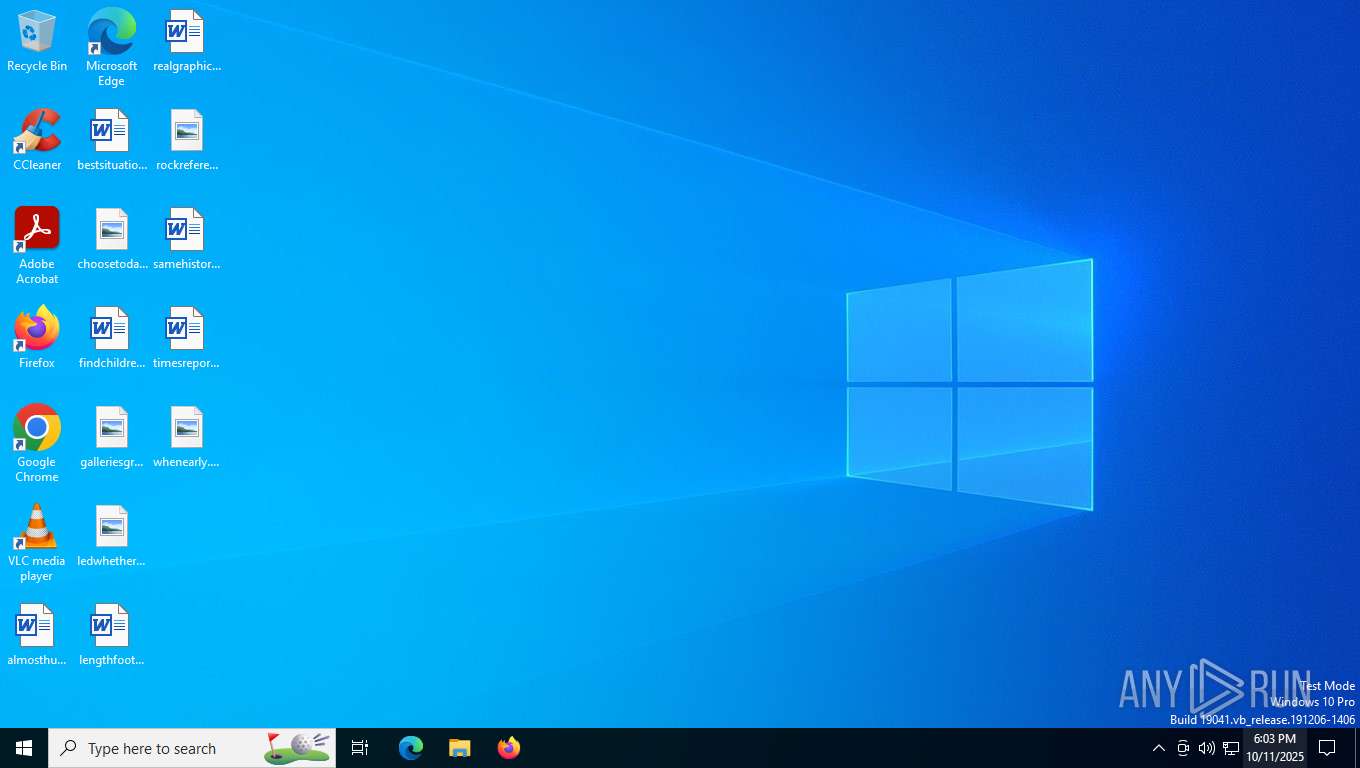
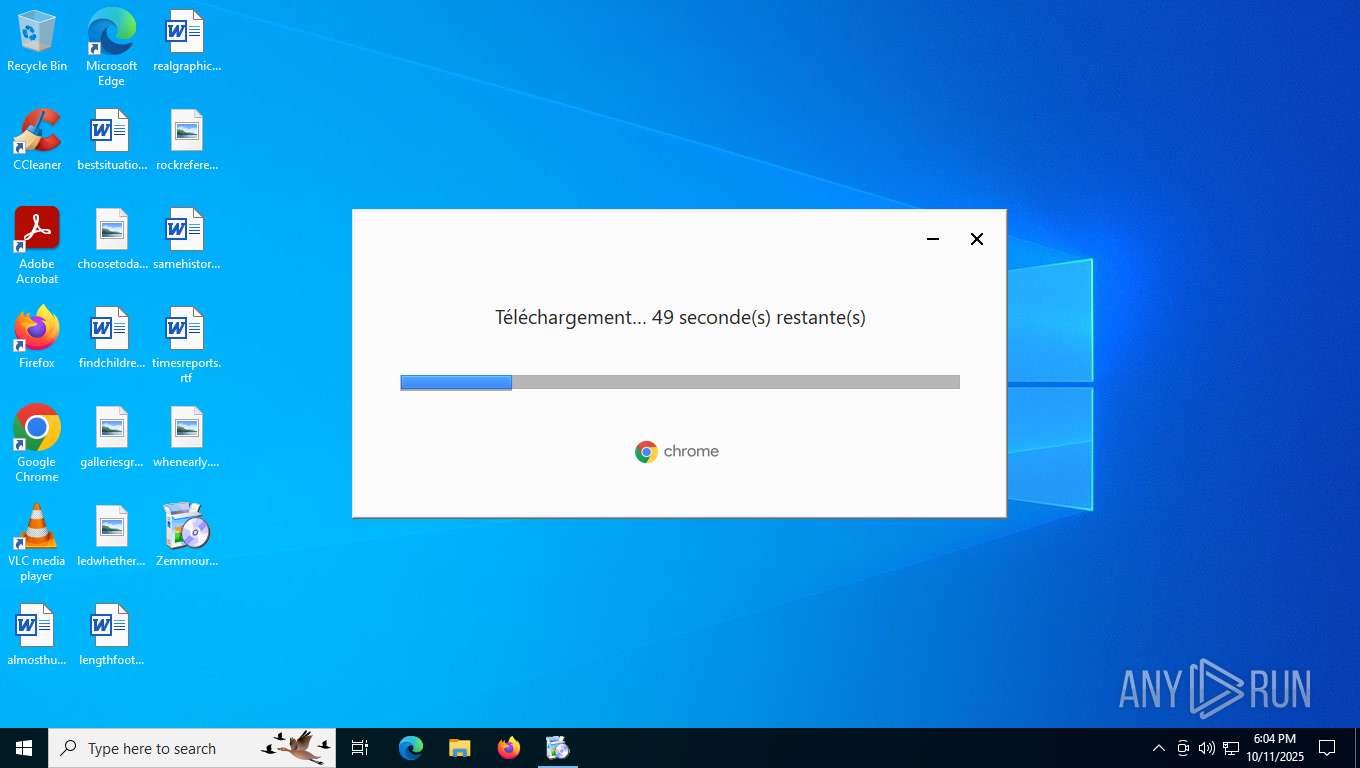
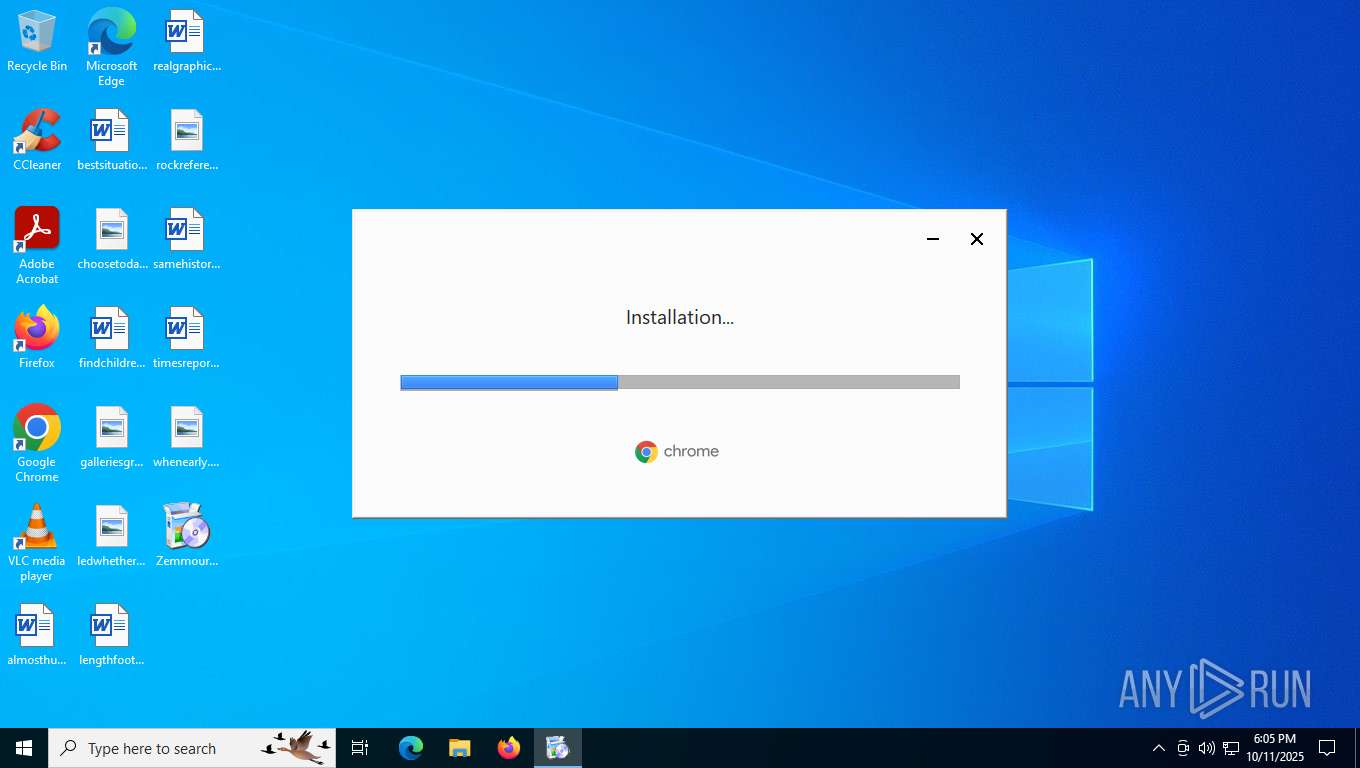
| File name: | Zemmourpanel.exe |
| Full analysis: | https://app.any.run/tasks/66ab0f17-ed45-4402-abd1-0bcb810d26c6 |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2025, 18:03:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 9 sections |
| MD5: | DBC08AE18FC6ED4B91EF220D9A290BD8 |
| SHA1: | 8B2B7486EEE2E416C1D37B4D0B6E18A1AF7E29E8 |
| SHA256: | 6B914DAAEE7CC562D0E5063FDFBDAA046CFB0AFDD23B2523B2A9E196A76A65A7 |
| SSDEEP: | 98304:hTqNObjWFGfXZPphr6W787ri8caGRifRkYRf1kQik/Al5onCnXOhJbR7M4P4TM1O:TUGSk |
MALICIOUS
Changes the autorun value in the registry
- setup.exe (PID: 3504)
SUSPICIOUS
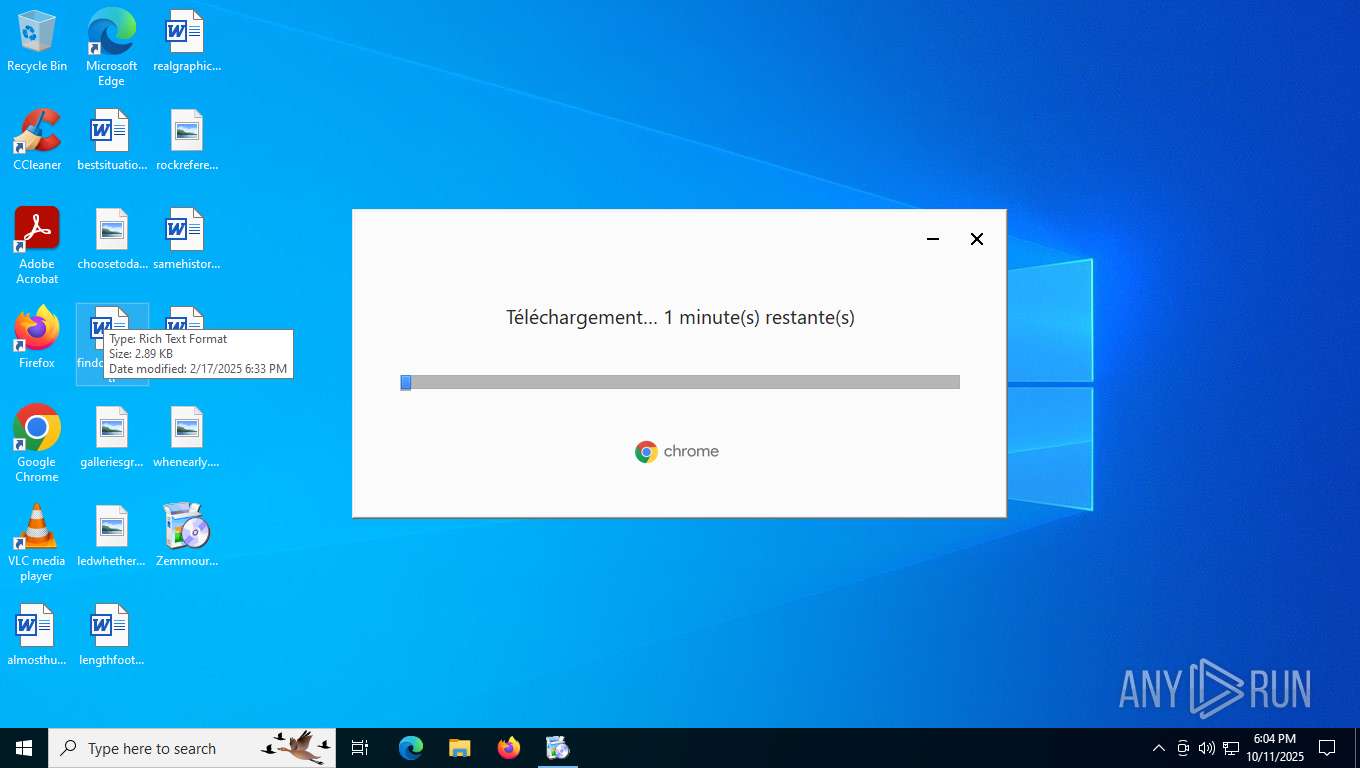
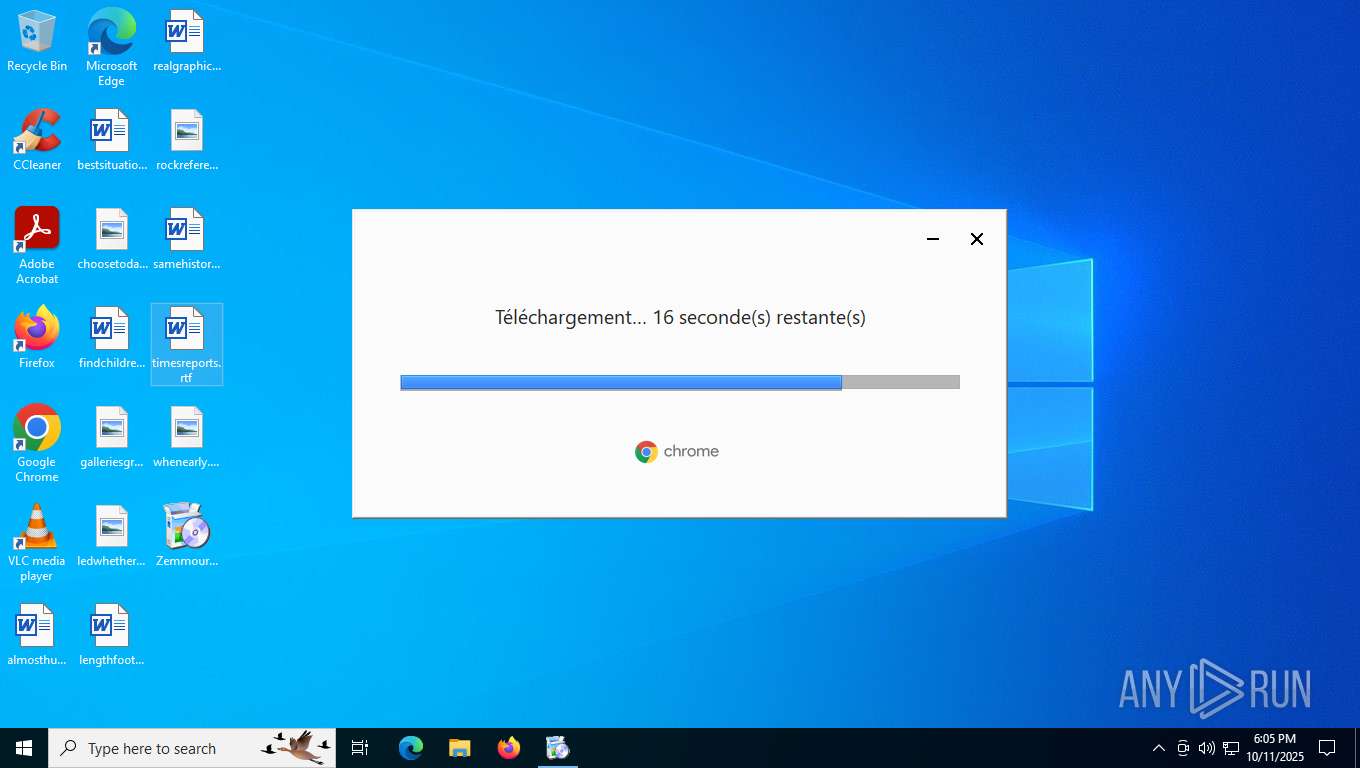
Executable content was dropped or overwritten
- updater.exe (PID: 8348)
- updater.exe (PID: 8672)
- 141.0.7390.77_chrome_installer_uncompressed.exe (PID: 4352)
- setup.exe (PID: 3504)
- updater.exe (PID: 7568)
- updater.exe (PID: 5040)
Executes as Windows Service
- updater.exe (PID: 8672)
- updater.exe (PID: 8812)
- updater.exe (PID: 8296)
- updater.exe (PID: 1600)
- updater.exe (PID: 7568)
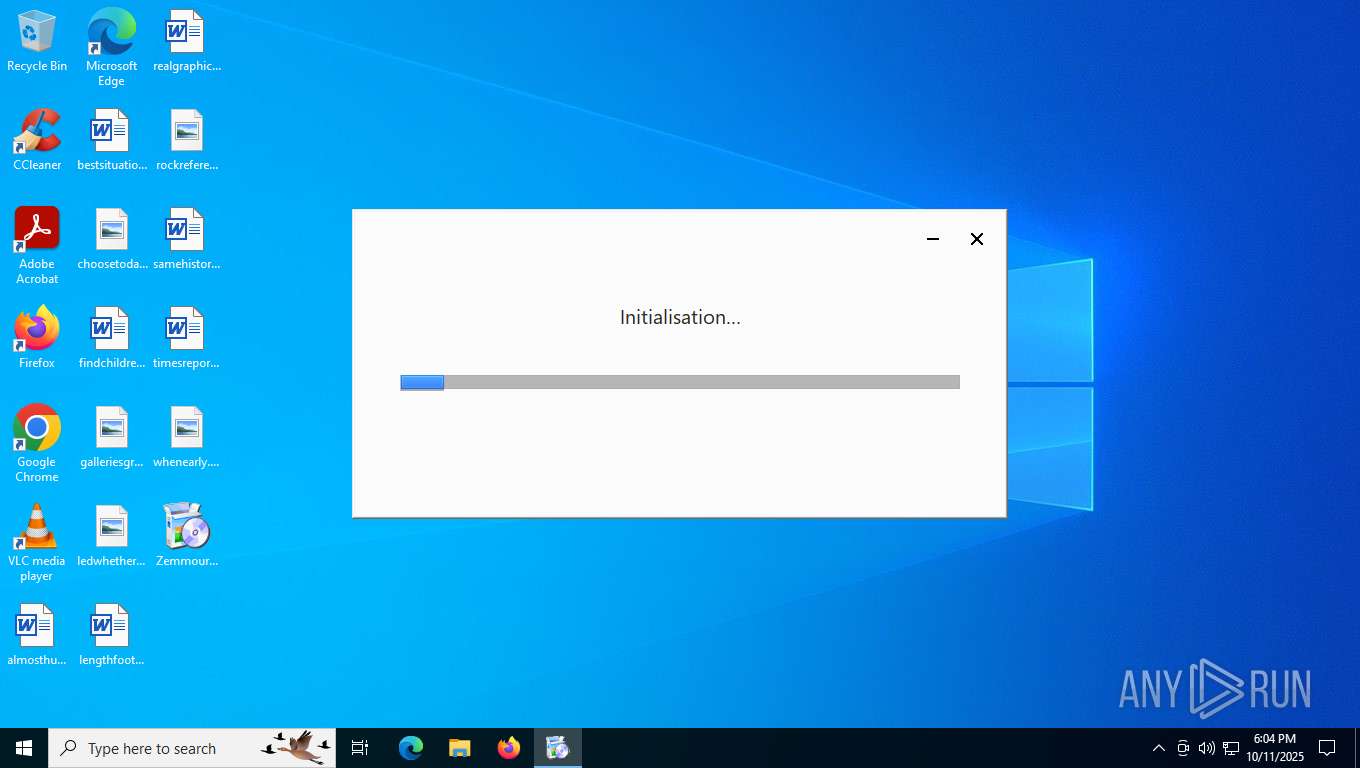
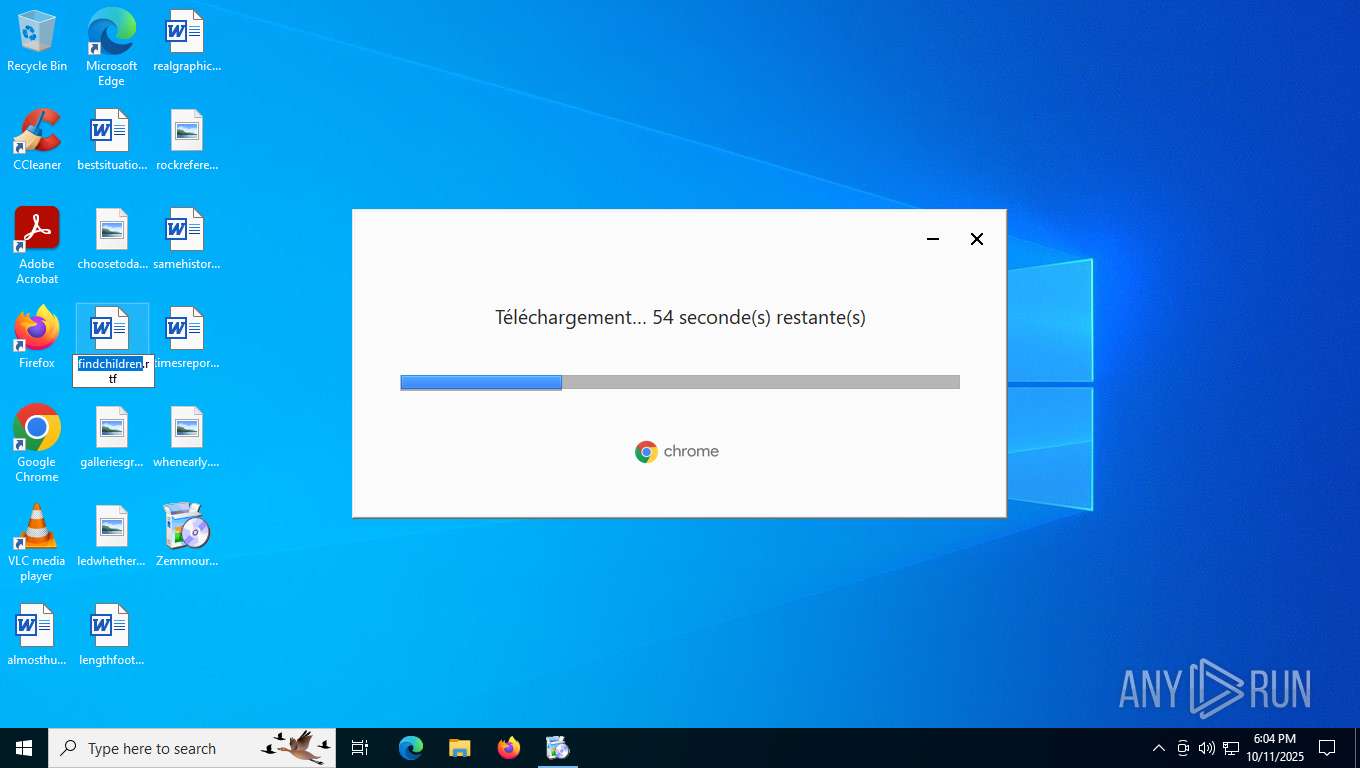
Application launched itself
- Zemmourpanel.exe (PID: 7032)
- setup.exe (PID: 3504)
- setup.exe (PID: 8660)
- updater.exe (PID: 5040)
- updater.exe (PID: 8348)
Reads security settings of Internet Explorer
- Zemmourpanel.exe (PID: 7032)
- updater.exe (PID: 8348)
Searches for installed software
- setup.exe (PID: 3504)
INFO
The sample compiled with english language support
- Zemmourpanel.exe (PID: 7032)
- updater.exe (PID: 8348)
- updater.exe (PID: 8672)
- 141.0.7390.77_chrome_installer_uncompressed.exe (PID: 4352)
- setup.exe (PID: 3504)
- updater.exe (PID: 7568)
- updater.exe (PID: 5040)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8576)
- BackgroundTransferHost.exe (PID: 9040)
- BackgroundTransferHost.exe (PID: 7776)
- BackgroundTransferHost.exe (PID: 9208)
- BackgroundTransferHost.exe (PID: 8644)
Checks supported languages
- updater.exe (PID: 8420)
- Zemmourpanel.exe (PID: 7032)
- Zemmourpanel.exe (PID: 8268)
- 141.0.7390.77_chrome_installer_uncompressed.exe (PID: 4352)
- setup.exe (PID: 3504)
- setup.exe (PID: 8608)
- setup.exe (PID: 8660)
- setup.exe (PID: 8688)
- elevation_service.exe (PID: 8732)
- UpdaterSetup.exe (PID: 2188)
- updater.exe (PID: 5040)
- updater.exe (PID: 8348)
- updater.exe (PID: 8424)
Reads the computer name
- Zemmourpanel.exe (PID: 8268)
- Zemmourpanel.exe (PID: 7032)
- 141.0.7390.77_chrome_installer_uncompressed.exe (PID: 4352)
- setup.exe (PID: 3504)
- setup.exe (PID: 8660)
- elevation_service.exe (PID: 8732)
- updater.exe (PID: 5040)
- updater.exe (PID: 8348)
Process checks computer location settings
- Zemmourpanel.exe (PID: 7032)
Create files in a temporary directory
- Zemmourpanel.exe (PID: 8268)
- updater.exe (PID: 8348)
Creates files in the program directory
- updater.exe (PID: 8672)
- updater.exe (PID: 8812)
- setup.exe (PID: 3504)
- setup.exe (PID: 8660)
- updater.exe (PID: 8296)
- updater.exe (PID: 5040)
- updater.exe (PID: 8424)
- updater.exe (PID: 8420)
- updater.exe (PID: 8348)
- updater.exe (PID: 7568)
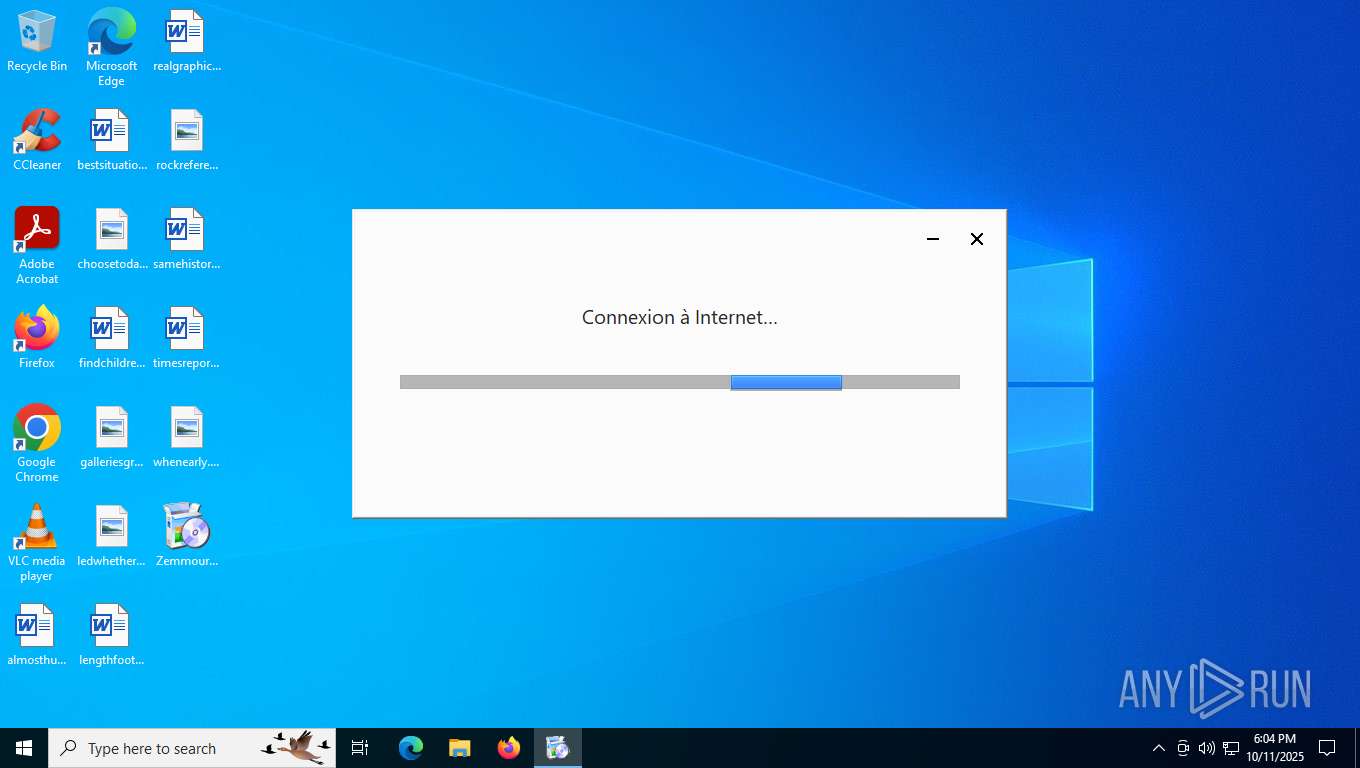
Checks proxy server information
- updater.exe (PID: 8348)
- BackgroundTransferHost.exe (PID: 9040)
- slui.exe (PID: 2368)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 9040)
- updater.exe (PID: 8812)
- updater.exe (PID: 8348)
- slui.exe (PID: 2368)
- updater.exe (PID: 7568)
Reads the machine GUID from the registry
- updater.exe (PID: 8812)
- updater.exe (PID: 8348)
- updater.exe (PID: 7568)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 9040)
- updater.exe (PID: 8348)
Manual execution by a user
- chrome.exe (PID: 8528)
- msedge.exe (PID: 5340)
- msedge.exe (PID: 6456)
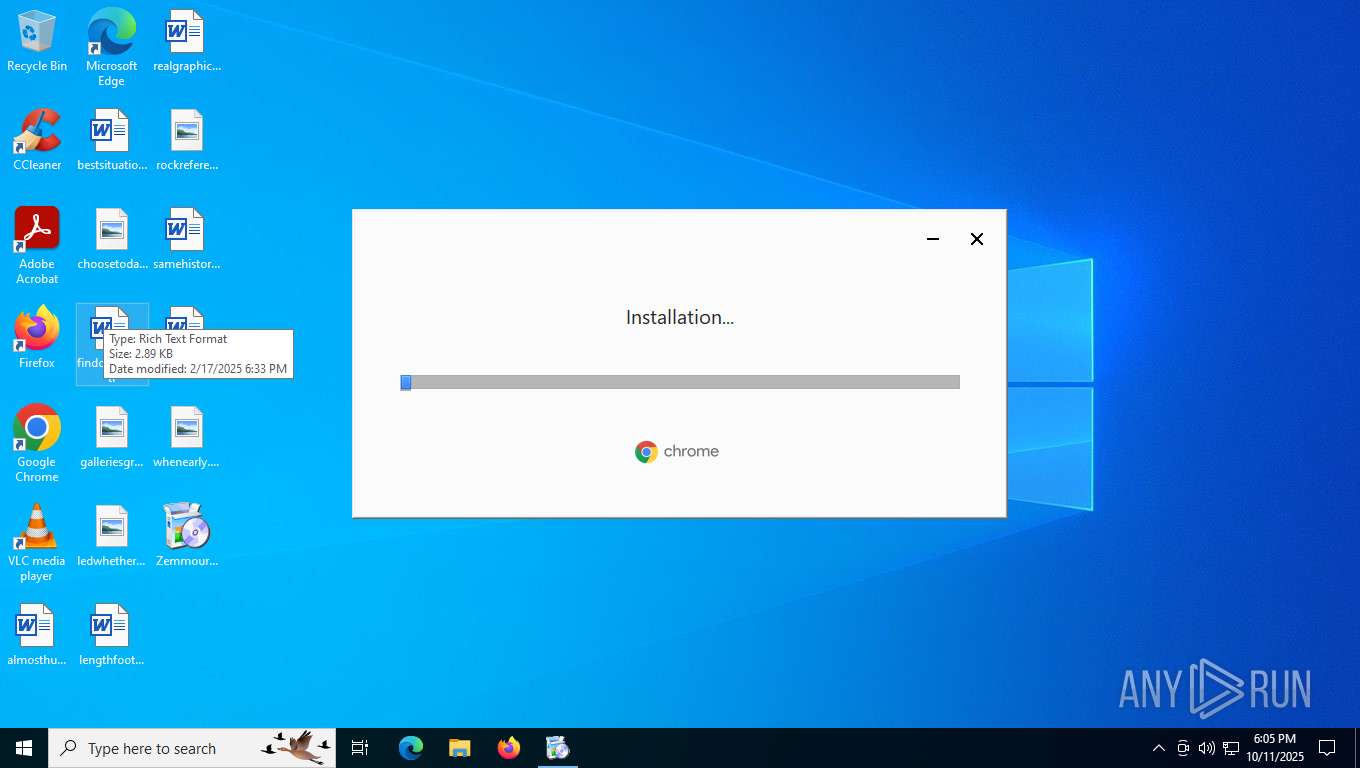
Creates a software uninstall entry
- setup.exe (PID: 3504)
Application launched itself
- chrome.exe (PID: 8528)
- msedge.exe (PID: 5340)
Executes as Windows Service
- elevation_service.exe (PID: 8732)
Connects to unusual port
- chrome.exe (PID: 8712)
Process checks whether UAC notifications are on
- updater.exe (PID: 8348)
- updater.exe (PID: 5040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:07:02 03:02:05+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 3554816 |
| InitializedDataSize: | 7469568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1dd910 |
| OSVersion: | 10 |
| ImageVersion: | - |
| SubsystemVersion: | 10 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 140.0.7273.0 |
| ProductVersionNumber: | 140.0.7273.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Google LLC |
| FileDescription: | Google Installer (x86) |
| FileVersion: | 140.0.7273.0 |
| InternalName: | Google Installer (x86) |
| LegalCopyright: | Copyright 2025 Google LLC. All rights reserved. |
| OriginalFileName: | UpdaterSetup.exe |
| ProductName: | Google Installer (x86) |
| ProductVersion: | 140.0.7273.0 |
| CompanyShortName: | |
| ProductShortName: | GoogleUpdater |
| LastChange: | cdbcba33653a1d72092fb0be472085f03b5f149d-refs/branch-heads/7273@{#1} |
| OfficialBuild: | 1 |
Total processes
254
Monitored processes
82
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --force-high-res-timeticks=disabled --metrics-shmem-handle=6708,i,10522639205300483317,5362503116335421358,524288 --field-trial-handle=2024,i,5019173991694912443,1056251917318486414,262144 --variations-seed-version --mojo-platform-channel-handle=7144 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 141.0.7390.77 Modules
| |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --force-high-res-timeticks=disabled --metrics-shmem-handle=4088,i,14034135491400119578,15330593231029663386,524288 --field-trial-handle=2024,i,5019173991694912443,1056251917318486414,262144 --variations-seed-version --mojo-platform-channel-handle=4416 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 141.0.7390.77 Modules
| |||||||||||||||
| 1372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --subproc-heap-profiling --always-read-main-dll --field-trial-handle=2736,i,3651247411926373358,4180496116546047948,262144 --variations-seed-version --mojo-platform-channel-handle=2672 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --subproc-heap-profiling --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=5592,i,3651247411926373358,4180496116546047948,262144 --variations-seed-version --mojo-platform-channel-handle=5612 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1600 | "C:\Program Files (x86)\Google\GoogleUpdater\140.0.7273.0\updater.exe" --system --windows-service --service=update-internal | C:\Program Files (x86)\Google\GoogleUpdater\140.0.7273.0\updater.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater (x86) Exit code: 0 Version: 140.0.7273.0 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --force-high-res-timeticks=disabled --metrics-shmem-handle=7092,i,13961748099630630614,15290522027680275735,524288 --field-trial-handle=2024,i,5019173991694912443,1056251917318486414,262144 --variations-seed-version --mojo-platform-channel-handle=7132 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 141.0.7390.77 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --force-high-res-timeticks=disabled --metrics-shmem-handle=3804,i,17040598457475517609,14655402030943690763,524288 --field-trial-handle=2024,i,5019173991694912443,1056251917318486414,262144 --variations-seed-version --mojo-platform-channel-handle=4284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 141.0.7390.77 Modules
| |||||||||||||||
| 2188 | "C:\WINDOWS\SystemTemp\chrome_Unpacker_BeginUnzipping7568_1066167230\UpdaterSetup.exe" --enable-ceca-experiment --update --system --enable-logging --vmodule=*/chrome/updater/*=2 | C:\Windows\SystemTemp\chrome_Unpacker_BeginUnzipping7568_1066167230\UpdaterSetup.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Installer (x64) Exit code: 0 Version: 142.0.7416.0 Modules
| |||||||||||||||
| 2368 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | "C:\Program Files (x86)\Google\GoogleUpdater\140.0.7273.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\140.0.7273.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=140.0.7273.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x2b0,0x2b4,0x2b8,0x28c,0x2bc,0xea31a8,0xea31b4,0xea31c0 | C:\Program Files (x86)\Google\GoogleUpdater\140.0.7273.0\updater.exe | — | updater.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Updater (x86) Exit code: 0 Version: 140.0.7273.0 Modules
| |||||||||||||||
Total events
35 603
Read events
35 376
Write events
214
Delete events
13
Modification events
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{8018F647-BF07-55BB-82BE-A2D7049F7CE4} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{8A1D4361-2C08-4700-A351-3EAA9CBFF5E4} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{534F5323-3569-4F42-919D-1E1CF93E5BF6} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{521FDB42-7130-4806-822A-FC5163FAD983} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{ABC01078-F197-4B0B-ADBC-CFE684B39C82} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{8018F647-BF07-55BB-82BE-A2D7049F7CE4} |
| Operation: | write | Name: | AppID |
Value: {8018F647-BF07-55BB-82BE-A2D7049F7CE4} | |||
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{8018F647-BF07-55BB-82BE-A2D7049F7CE4} |
| Operation: | write | Name: | LocalService |
Value: GoogleUpdaterService140.0.7273.0 | |||
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{8018F647-BF07-55BB-82BE-A2D7049F7CE4} |
| Operation: | write | Name: | ServiceParameters |
Value: --com-service | |||
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{8A1D4361-2C08-4700-A351-3EAA9CBFF5E4} |
| Operation: | write | Name: | AppID |
Value: {8A1D4361-2C08-4700-A351-3EAA9CBFF5E4} | |||
| (PID) Process: | (8672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{8A1D4361-2C08-4700-A351-3EAA9CBFF5E4} |
| Operation: | write | Name: | LocalService |
Value: GoogleUpdaterService140.0.7273.0 | |||
Executable files
18
Suspicious files
202
Text files
104
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8268 | Zemmourpanel.exe | C:\Users\admin\AppData\Local\Temp\Google8268_417617678\UPDATER.PACKED.7Z | — | |
MD5:— | SHA256:— | |||
| 9040 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\95474901-2a1d-4b8c-8895-6d976be0d80d.down_data | — | |
MD5:— | SHA256:— | |||
| 8348 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\140.0.7273.0\uninstall.cmd | text | |
MD5:FBC297EE9060D4256192E4EDB98CAD1B | SHA256:099592FFA867124D16C0C6D868AF1214FD2B7180FA76E4EEE01ABF2A5CF8F044 | |||
| 8348 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\updater.log | text | |
MD5:783FC0CA5FF79322D84E64E44652E921 | SHA256:AB3868D9DDB34E4DFFC1E489F8E2131AD74DE8DC8CD314A2C09CAE9DF16D125A | |||
| 8348 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\prefs.json~RF171fbd.TMP | binary | |
MD5:6A7C22B00ADBF302C1F53F51AF1AB2F6 | SHA256:BFD4268EDA9AB3F0E8D8D2ED0884BD28C0B34546332B36E54EBD30ACF45053FF | |||
| 8348 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\140.0.7273.0\Crashpad\settings.dat | binary | |
MD5:48965EF7C6E78D3297FBA574CEBE027E | SHA256:202762BCC782CEB4D3A304922E73DB406FD1D927C7A93EEF01BB04E2F39B0CE9 | |||
| 8348 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\cc9ac9c1-59ed-41d3-aab5-ca6909f936ac.tmp | binary | |
MD5:B0220CEA5E8C34F4D274D19B38E043DB | SHA256:939FA5BCA89134D865E556516D85ECC53F0C8669E46FA299B77E3035981445D6 | |||
| 8812 | updater.exe | C:\Windows\SystemTemp\chrome_url_fetcher_8812_770252623\2969df8b7e12dfe7f92837cb92aa0181414854e733df1f783cc109aacd68bd6c | — | |
MD5:— | SHA256:— | |||
| 8812 | updater.exe | C:\Windows\SystemTemp\chrome_url_fetcher_8812_770252623\decoded_xz | — | |
MD5:— | SHA256:— | |||
| 8812 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\crx_cache\3114fcf164f17debed64fbe04edec2dc6a55c83a6264b8f96910d7a33937522f | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
207
TCP/UDP connections
155
DNS requests
96
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.86.251.30:443 | https://www.bing.com/DSB/search?dsbmr=1&format=dsbjson&client=windowsminiserp&dsbschemaversion=1.1&dsbminiserp=1&q=q&cc=US&setlang=en-us&clientDateTime=10%2F11%2F2025%2C%206%3A03%3A56%20PM | unknown | binary | 57.7 Kb | unknown |
— | — | POST | 200 | 40.126.32.140:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | unknown |
— | — | POST | 200 | 40.126.32.140:443 | https://login.live.com/RST2.srf | unknown | xml | 11.2 Kb | unknown |
— | — | GET | 200 | 184.86.251.30:443 | https://www.bing.com/th?id=ODSWG.24eaf1a6-2ff8-4317-ae4d-06726b48b9ce&pid=dsb | unknown | image | 11.2 Kb | unknown |
— | — | GET | 200 | 2.16.204.138:443 | https://www.bing.com/th?id=ODSWG.53df395b-c52e-4625-8b67-acbc33939a04&pid=dsb | unknown | — | — | unknown |
— | — | POST | 200 | 20.190.160.67:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | unknown |
— | — | POST | 204 | 2.16.204.139:443 | https://www.bing.com/threshold/xls.aspx?t=5&dl=1&wsbc=1 | unknown | — | — | unknown |
— | — | POST | 200 | 40.126.32.68:443 | https://login.live.com/RST2.srf | unknown | xml | 11.2 Kb | unknown |
— | — | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | xml | 11.2 Kb | unknown |
— | — | POST | 200 | 20.190.160.2:443 | https://login.live.com/RST2.srf | unknown | xml | 11.3 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7552 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6016 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.204.141:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5224 | SearchApp.exe | 2.16.204.141:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6176 | backgroundTaskHost.exe | 2.16.204.141:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6016 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
dl.google.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |