| File name: | PingPlotter.v3.30.4_KEYGEN-FFF.exe |
| Full analysis: | https://app.any.run/tasks/308899f3-5a63-48a0-b4c5-0dbcfd746c35 |
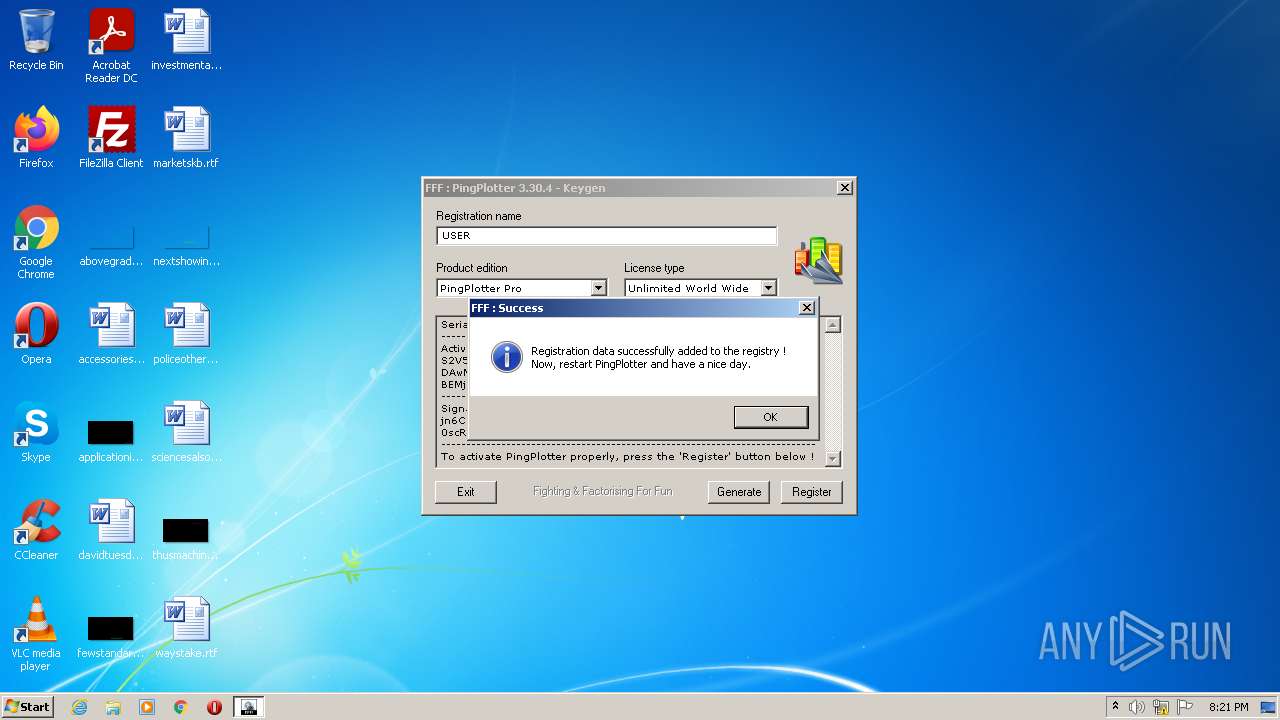
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2022, 20:20:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CB3267E801381492384E401D53880716 |
| SHA1: | D313ACC4478A87015DA03935A4BD0CEE76AFA42E |
| SHA256: | 6B8E8068C0C816861B00FFC82C54ECB32446C60D50D1B33FD3BCE336747435D7 |
| SSDEEP: | 12288:n1gnI0R3PDUFfhbXzAZqGZlxt1vGzjHIzJVmMEJ:nqR3PDUFJbjAkGDTwHcMJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- PingPlotter.v3.30.4_KEYGEN-FFF.exe (PID: 3820)
Reads Windows owner or organization settings
- PingPlotter.v3.30.4_KEYGEN-FFF.exe (PID: 3820)
Reads the Windows organization settings
- PingPlotter.v3.30.4_KEYGEN-FFF.exe (PID: 3820)
Reads the computer name
- PingPlotter.v3.30.4_KEYGEN-FFF.exe (PID: 3820)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.7) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.4) |
| .exe | | | DOS Executable Generic (23.4) |
| .vxd | | | VXD Driver (0.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xa83cf |
| UninitializedDataSize: | - |
| InitializedDataSize: | 247808 |
| CodeSize: | 392704 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.textbss\x84b\x0a | 0x00001000 | 0x000A6284 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.text | 0x000A8000 | 0x00001000 | 0x00000D53 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40104 |
.data | 0x000A9000 | 0x00071000 | 0x00070515 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.67768 |
.idata | 0x0011A000 | 0x00001000 | 0x000002E4 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.08231 |
.tls | 0x0011B000 | 0x00001000 | 0x00000018 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.55351 |
.rsrc | 0x0011C000 | 0x00004000 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13956 |
.reloc | 0x00120000 | 0x00001000 | 0x00000018 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.70915 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 0 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
2 | 0 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 0 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 0 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 0 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 0 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 0 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
50 | 5.64611 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 5.26588 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4075 | 0 | 480 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Total processes
34
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3820 | "C:\Users\admin\AppData\Local\Temp\PingPlotter.v3.30.4_KEYGEN-FFF.exe" | C:\Users\admin\AppData\Local\Temp\PingPlotter.v3.30.4_KEYGEN-FFF.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
54
Read events
50
Write events
4
Delete events
0
Modification events
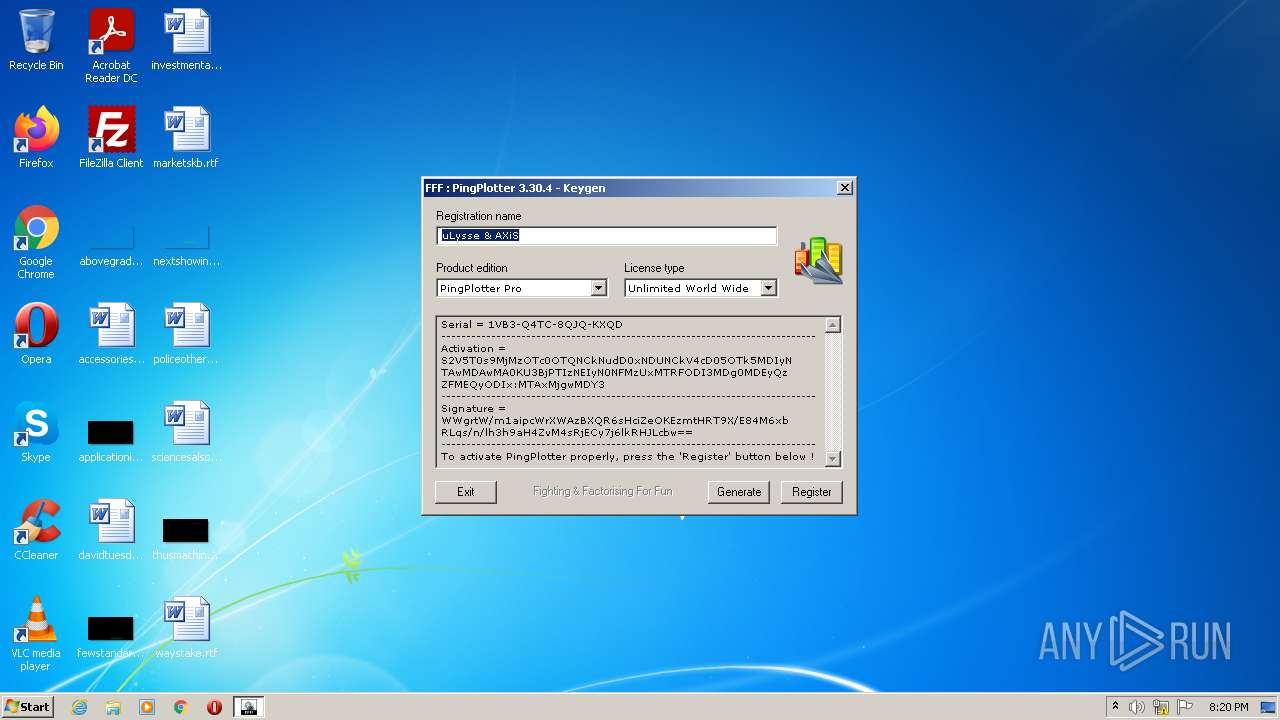
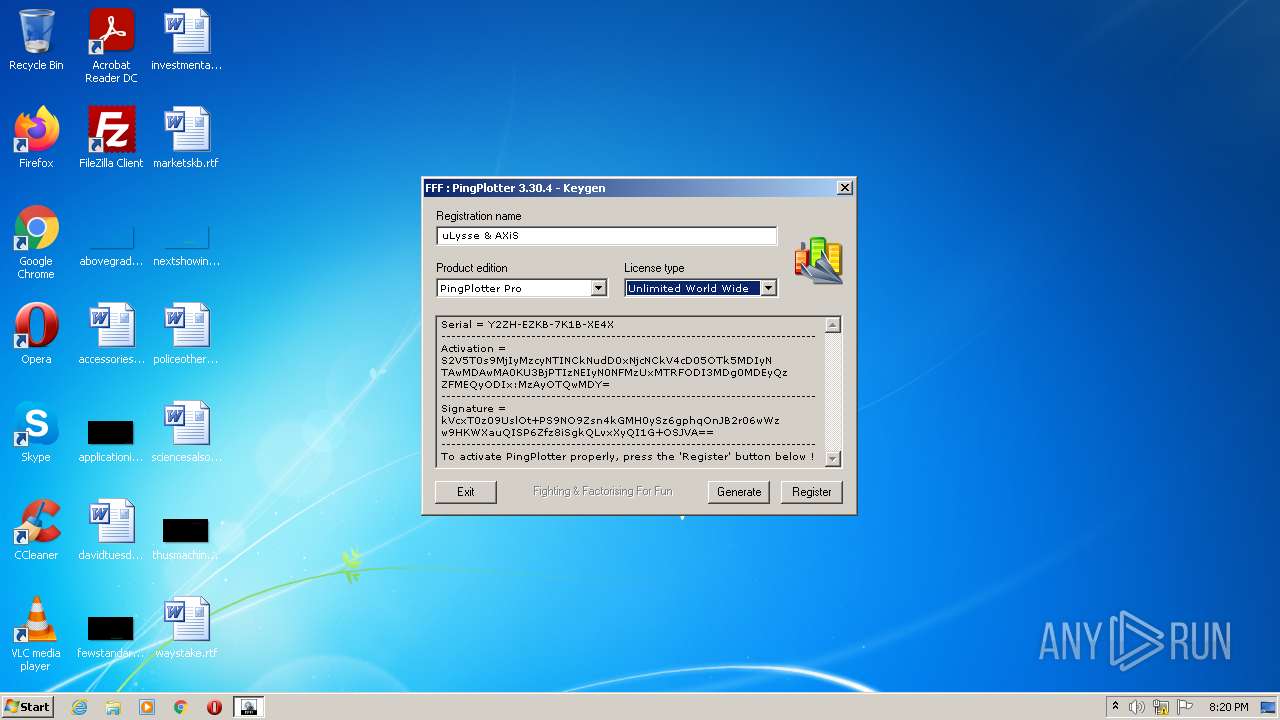
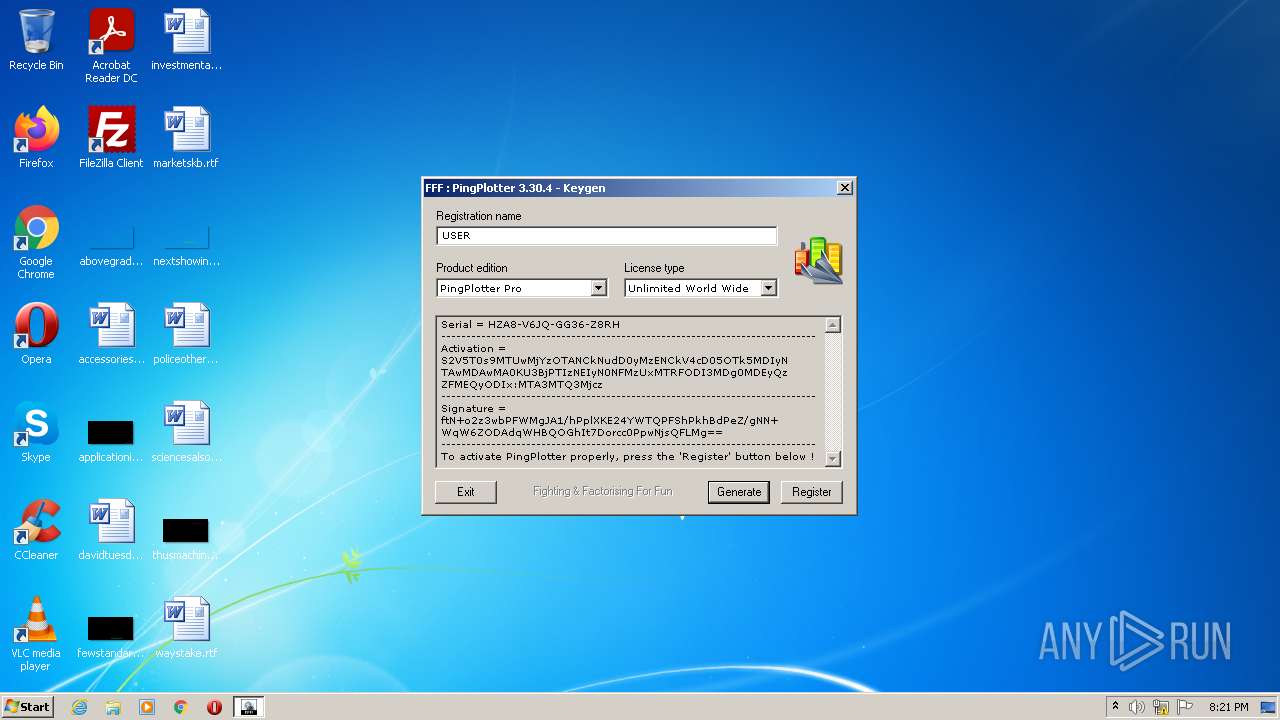
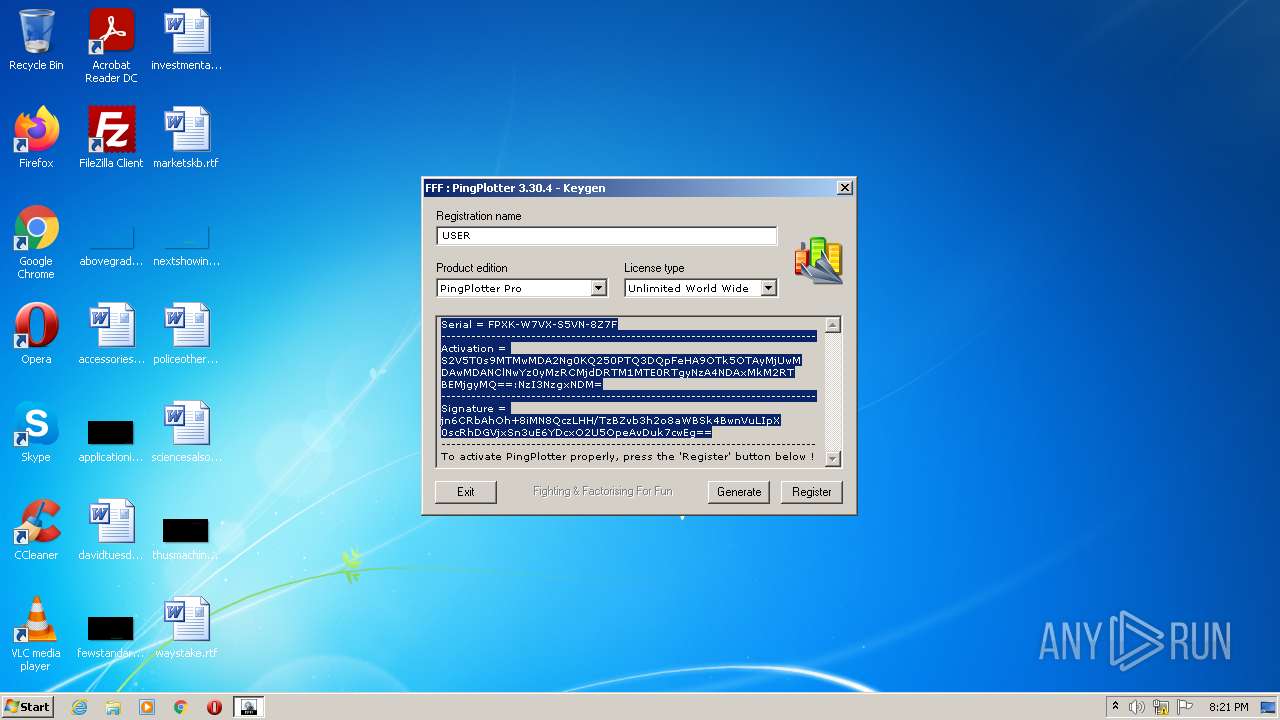
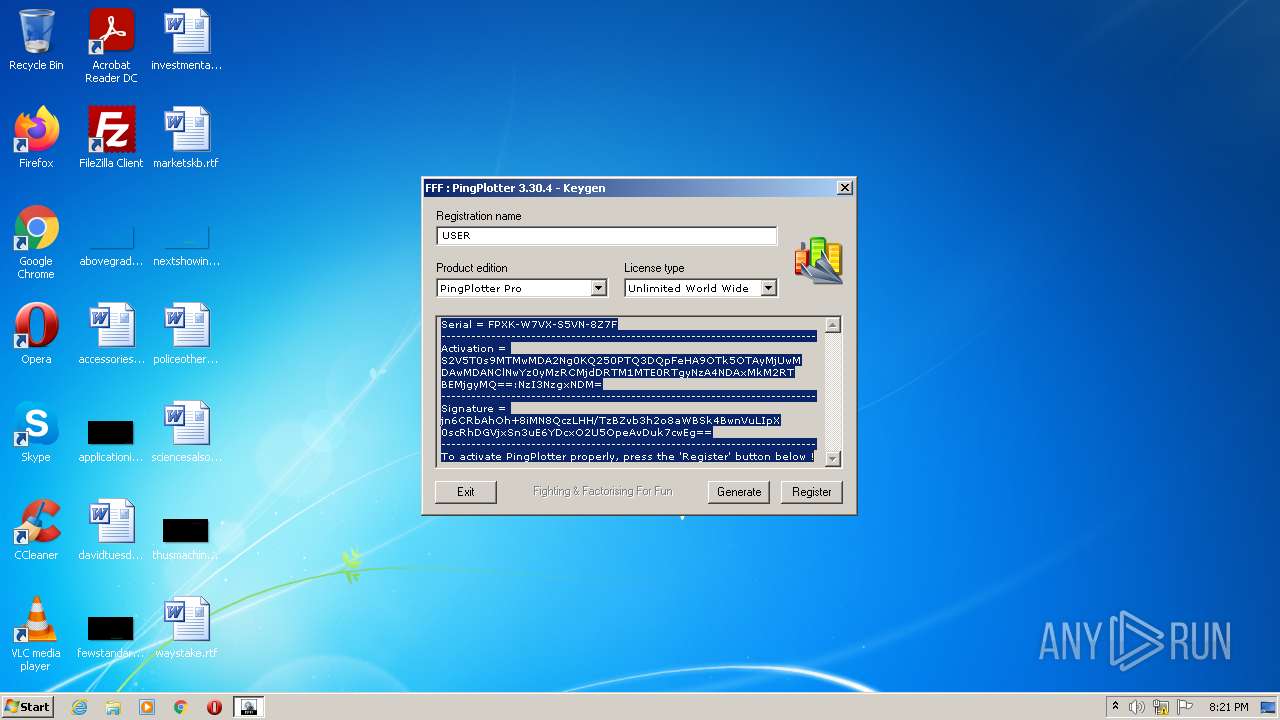
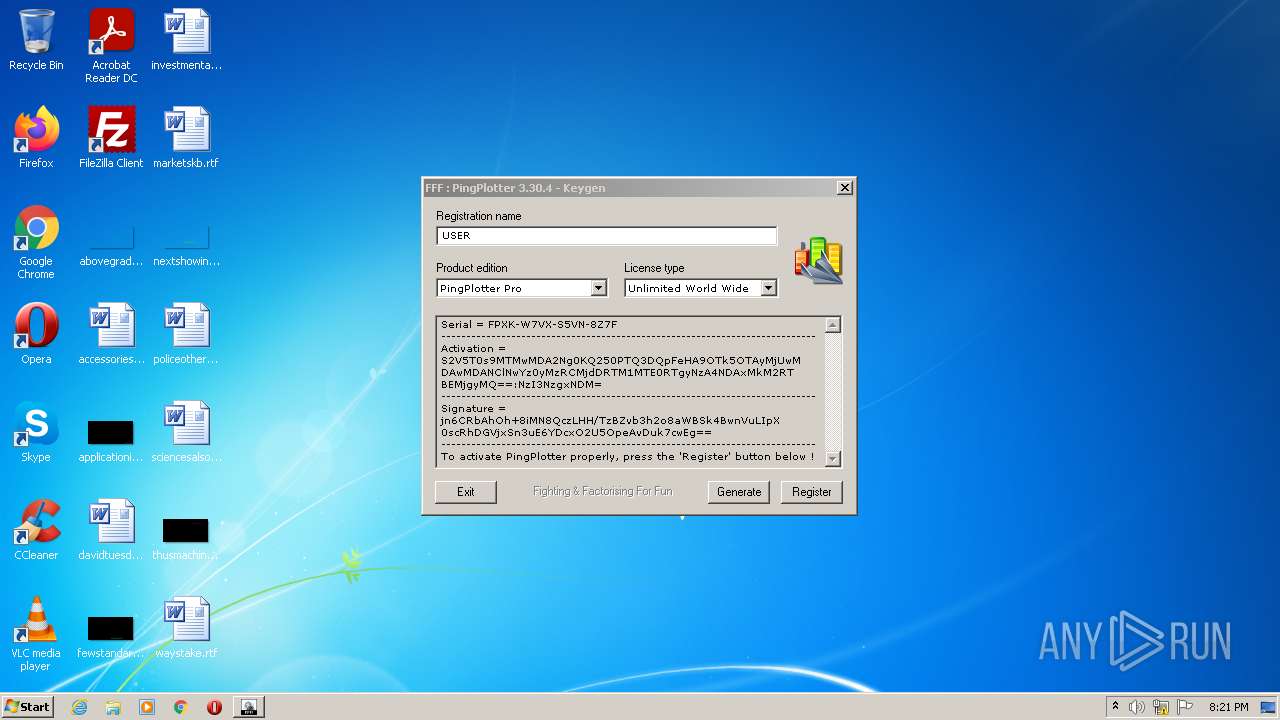
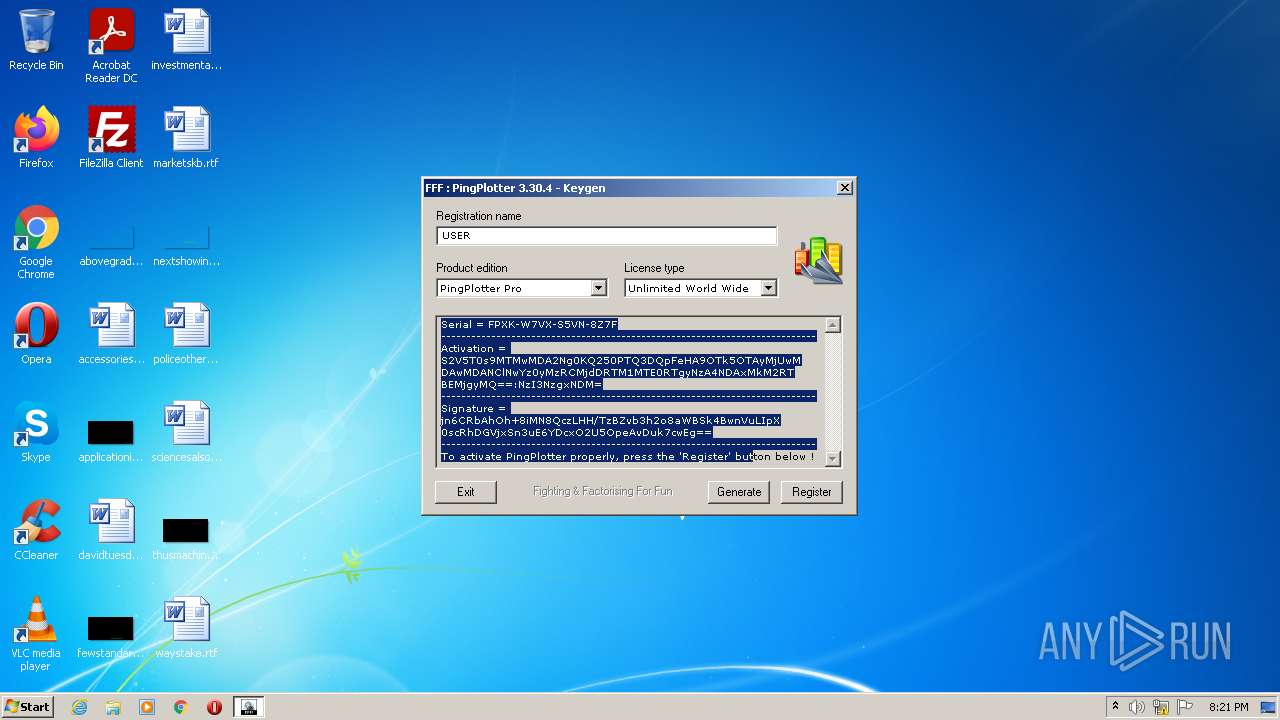
| (PID) Process: | (3820) PingPlotter.v3.30.4_KEYGEN-FFF.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Nessoft\PingPlotter Pro\User |
| Operation: | write | Name: | UserName |
Value: USER | |||
| (PID) Process: | (3820) PingPlotter.v3.30.4_KEYGEN-FFF.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Nessoft\PingPlotter Pro\User |
| Operation: | write | Name: | RegistrationCode |
Value: FPXK-W7VX-S5VN-8Z7F | |||
| (PID) Process: | (3820) PingPlotter.v3.30.4_KEYGEN-FFF.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Nessoft\PingPlotter Pro\User |
| Operation: | write | Name: | Key1 |
Value: S2V5T0s9MTMwMDA2Ng0KQ250PTQ3DQpFeHA9OTk5OTAyMjUwMDAwMDANClNwYz0yMzRCMjdDRTM1MTE0RTgyNzA4NDAxMkM2RTBEMjgyMQ==:NzI3NzgxNDM= | |||
| (PID) Process: | (3820) PingPlotter.v3.30.4_KEYGEN-FFF.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Nessoft\PingPlotter Pro\User |
| Operation: | write | Name: | Key2 |
Value: jn6CRbAhOh+8iMN8QczLHH/TzBZvb3h2o8aWBSk4BwnVuLIpX0scRhDGVjxSn3uE6YDcxO2U5OpeAvDuk7cwEg== | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report