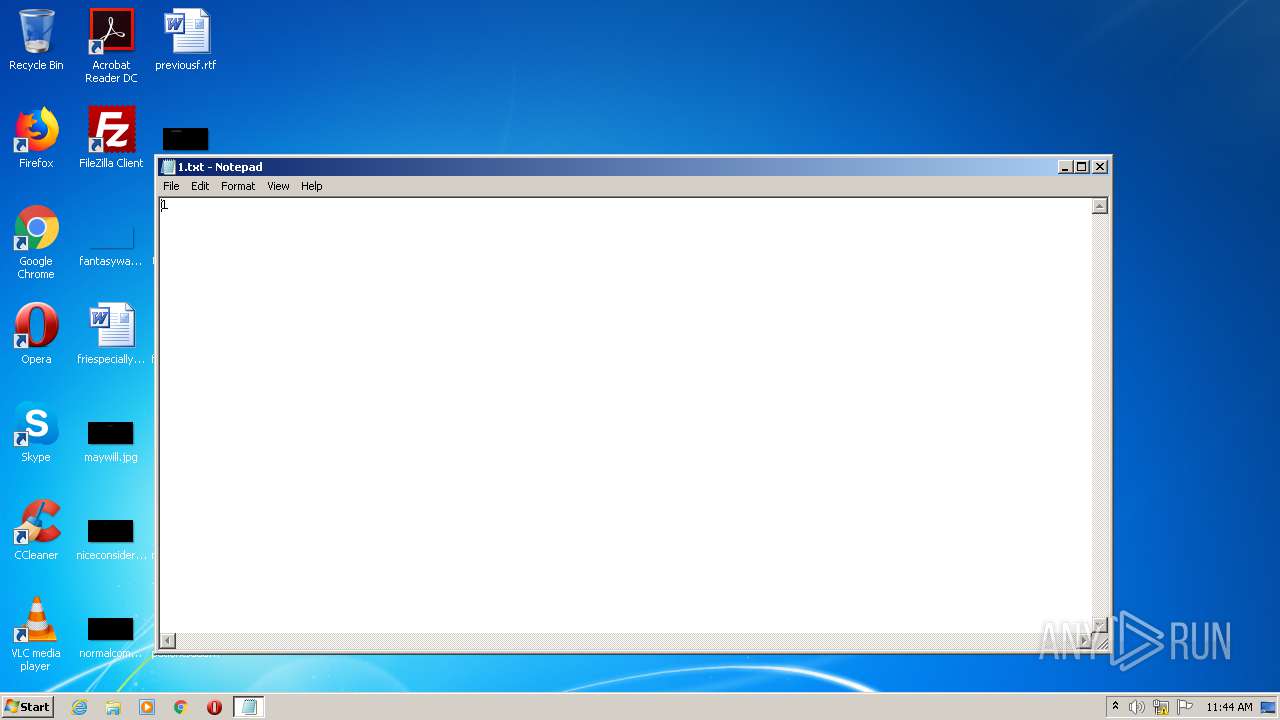
| File name: | 1.txt |
| Full analysis: | https://app.any.run/tasks/edf14bc7-9ee5-45cc-a7ef-feefad3dcd04 |
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2020, 10:43:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | very short file (no magic) |
| MD5: | C4CA4238A0B923820DCC509A6F75849B |
| SHA1: | 356A192B7913B04C54574D18C28D46E6395428AB |
| SHA256: | 6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B |
| SSDEEP: | 3:U:U |
MALICIOUS
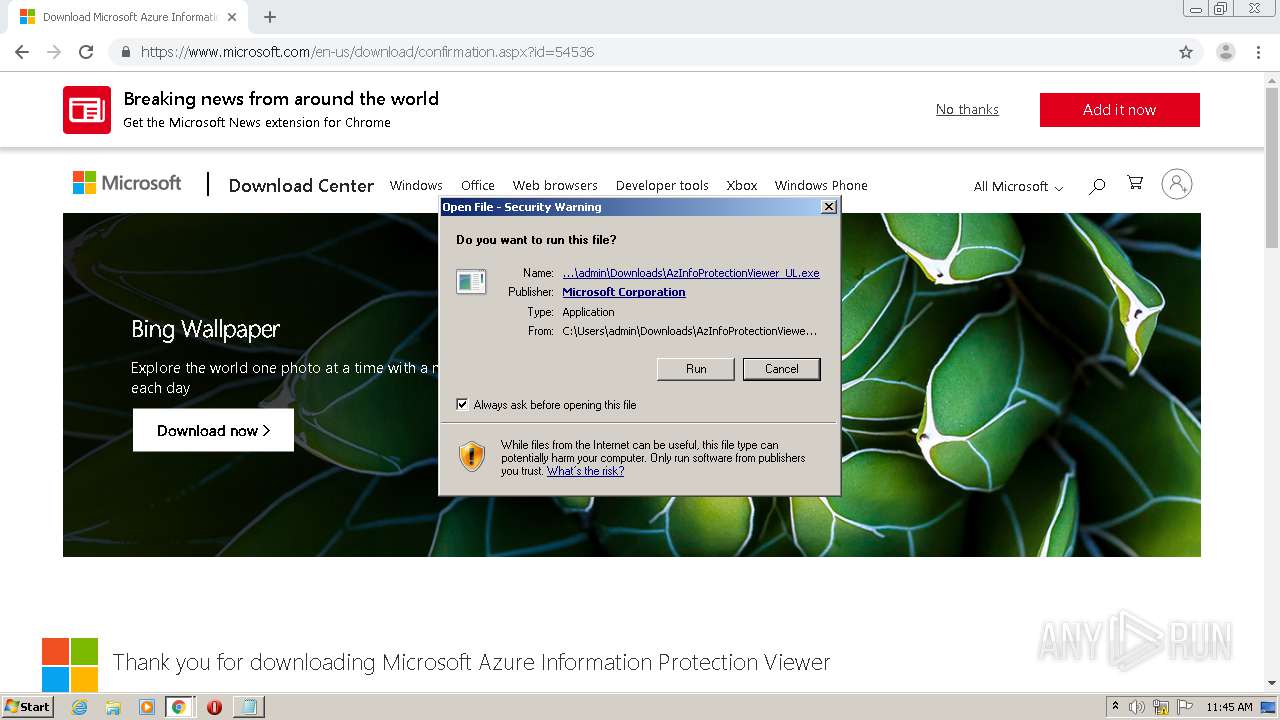
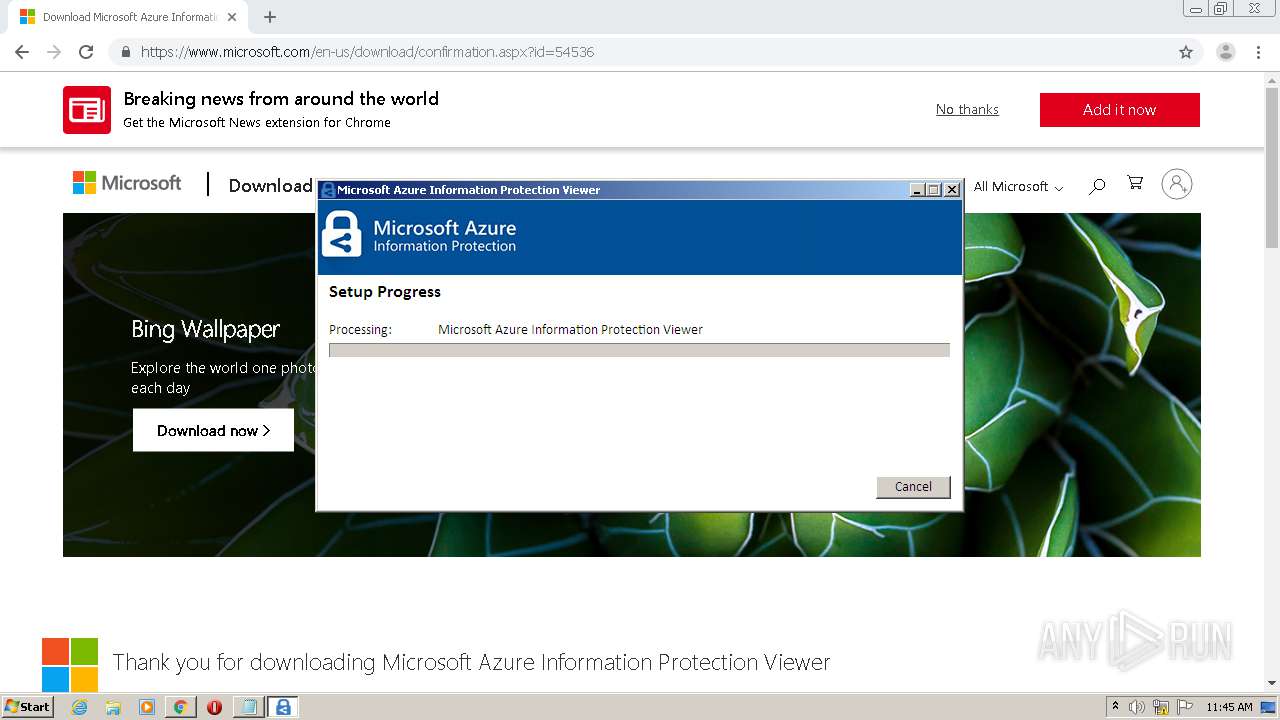
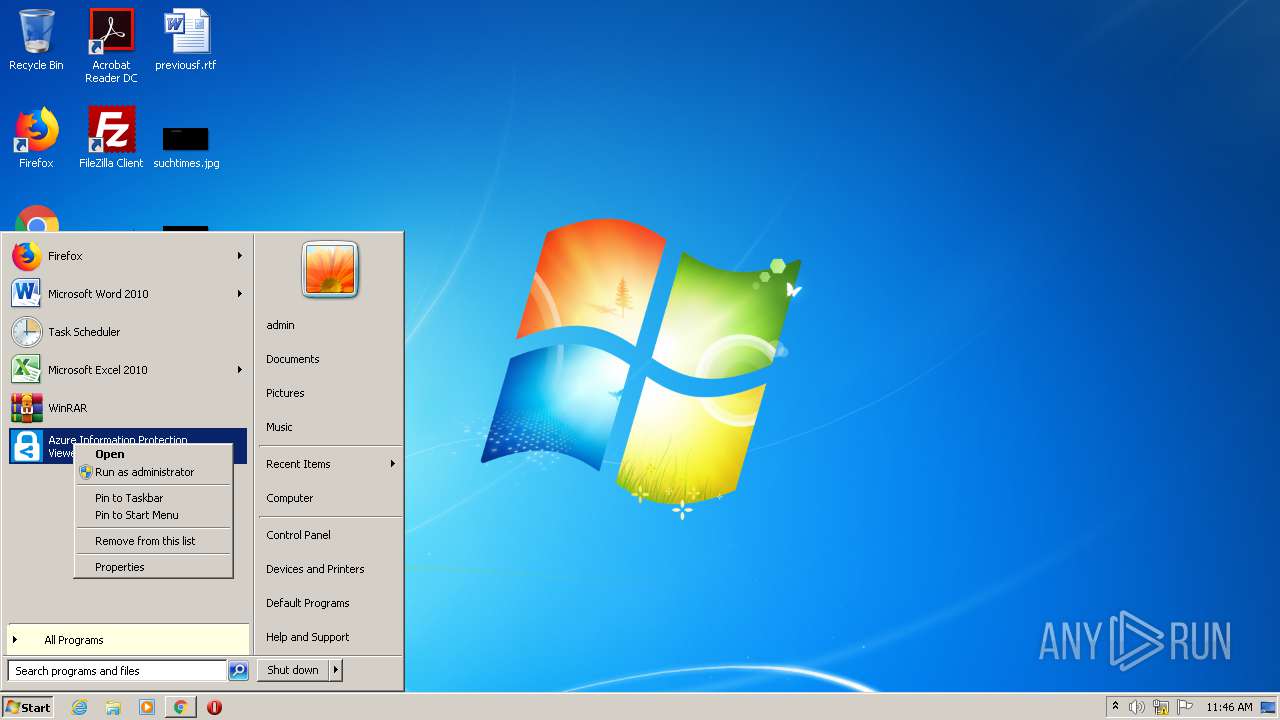
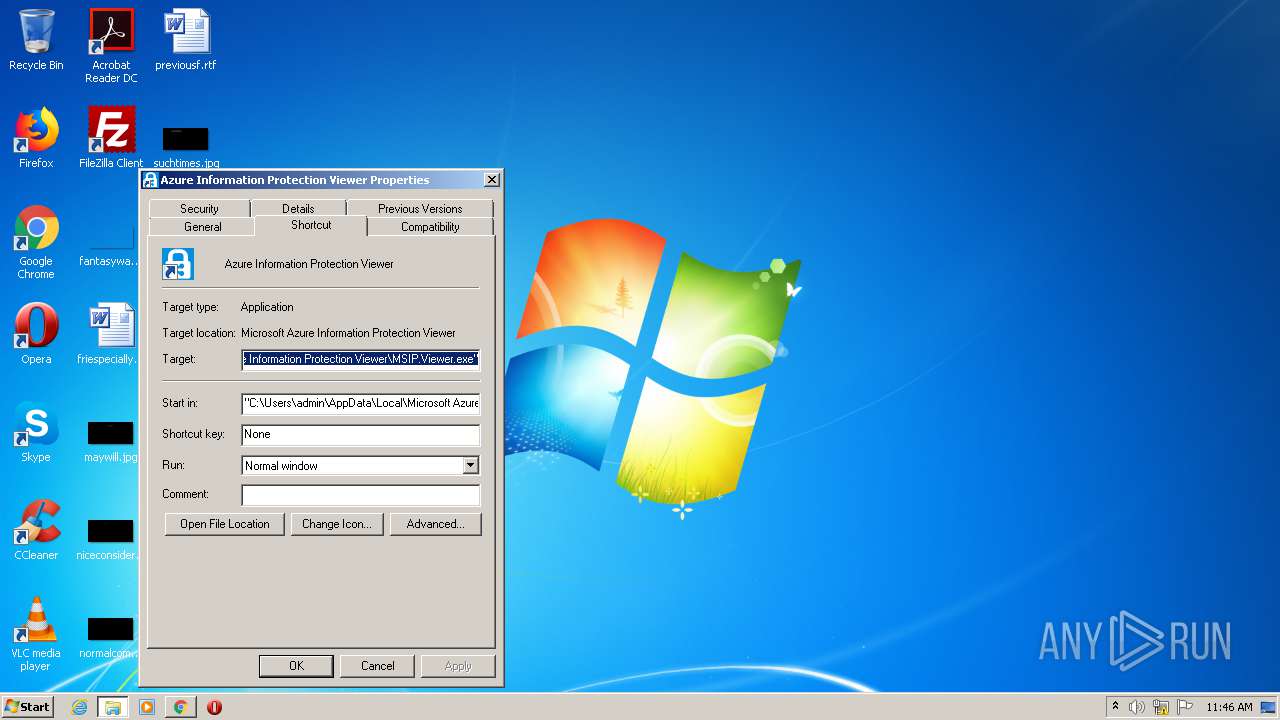
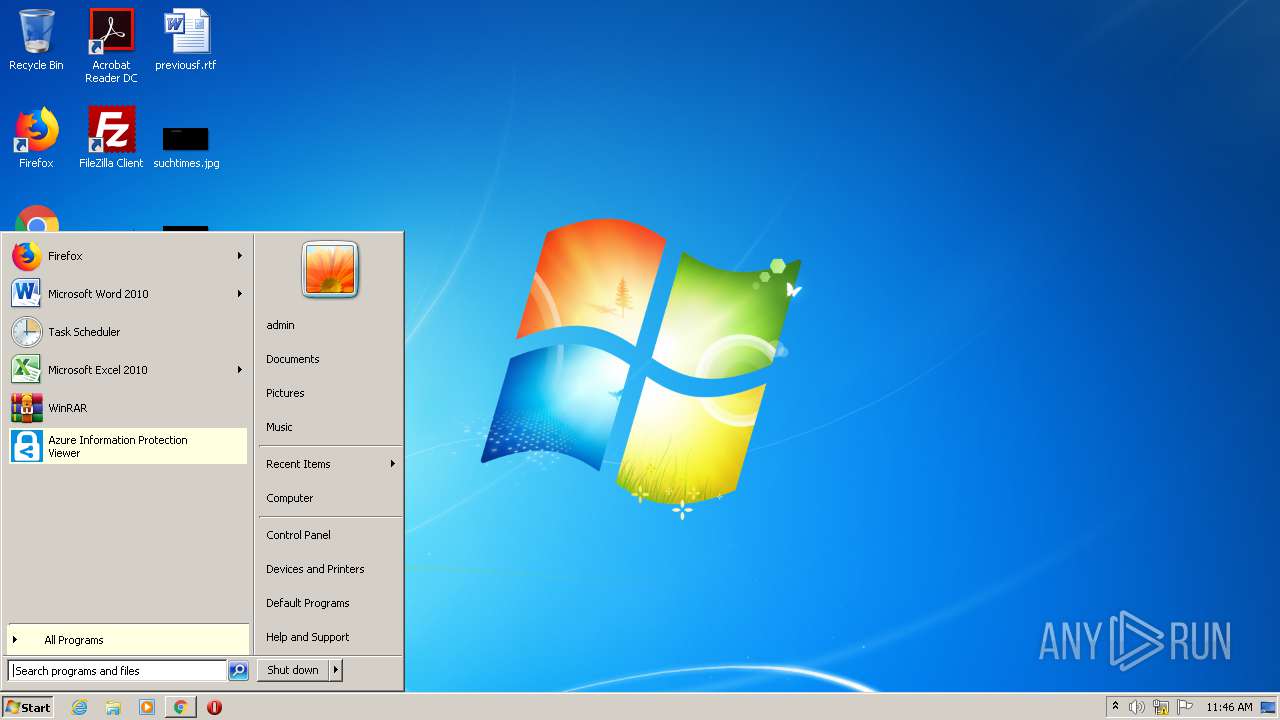
Application was dropped or rewritten from another process
- AzInfoProtectionViewer_UL.exe (PID: 956)
- AzInfoProtectionViewer_UL.exe (PID: 2400)
- MSIP.Viewer.exe (PID: 2396)
Loads dropped or rewritten executable
- AzInfoProtectionViewer_UL.exe (PID: 2400)
- explorer.exe (PID: 352)
- MSIP.Viewer.exe (PID: 2396)
Changes the autorun value in the registry
- AzInfoProtectionViewer_UL.exe (PID: 2400)
SUSPICIOUS
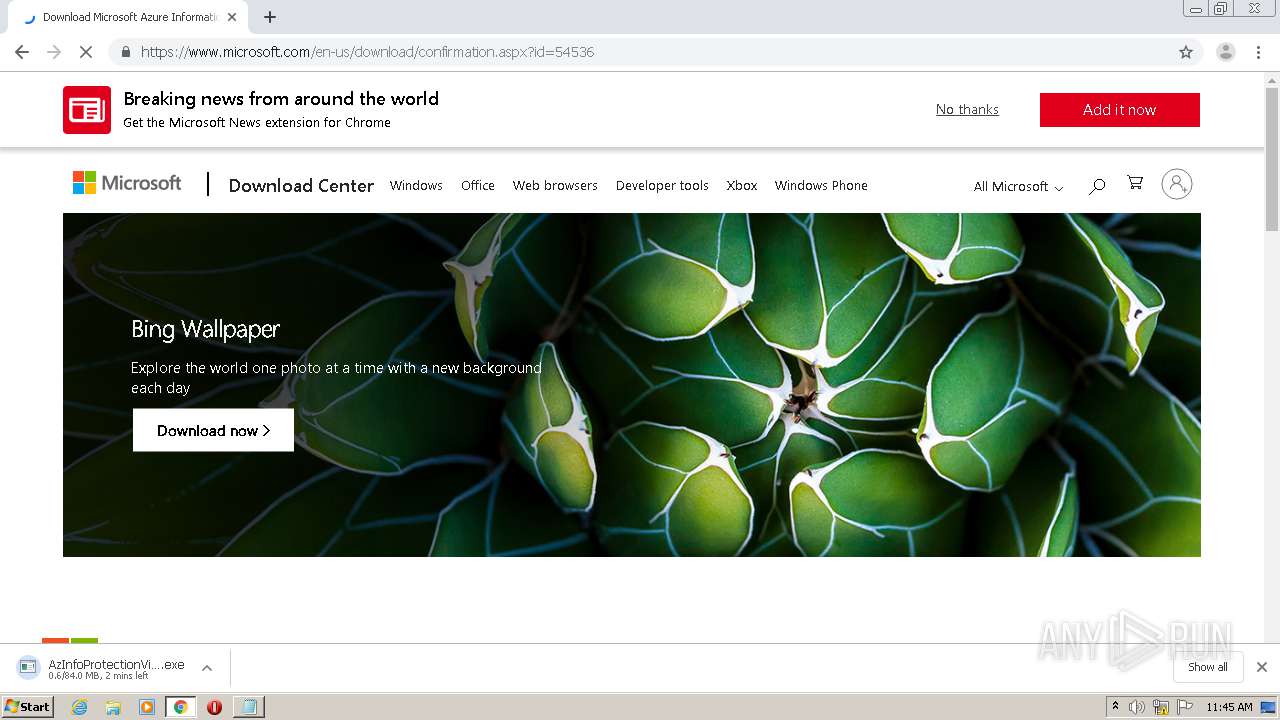
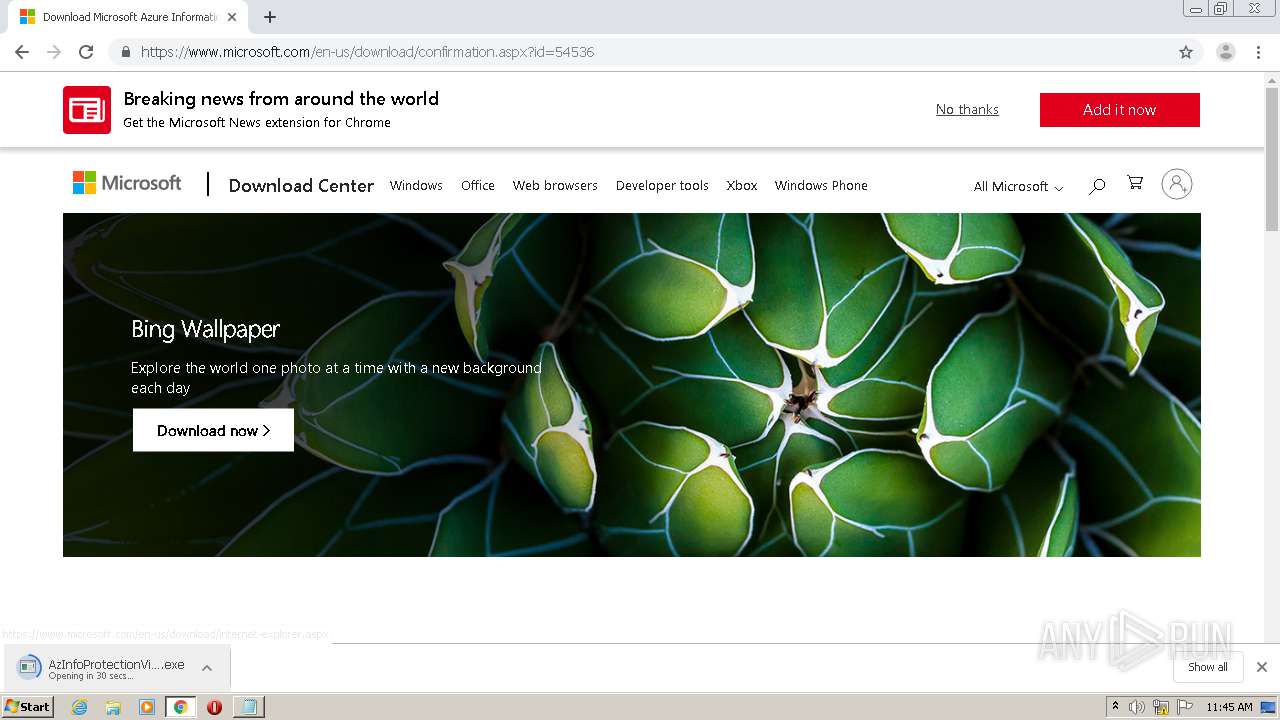
Executable content was dropped or overwritten
- chrome.exe (PID: 1512)
- AzInfoProtectionViewer_UL.exe (PID: 956)
- AzInfoProtectionViewer_UL.exe (PID: 2400)
Creates a software uninstall entry
- AzInfoProtectionViewer_UL.exe (PID: 2400)
Writes to a desktop.ini file (may be used to cloak folders)
- explorer.exe (PID: 352)
Creates files in the program directory
- MSIP.Viewer.exe (PID: 2396)
Creates files in the user directory
- explorer.exe (PID: 352)
Reads Environment values
- MSIP.Viewer.exe (PID: 2396)
Reads the machine GUID from the registry
- MSIP.Viewer.exe (PID: 2396)
Reads Internet Cache Settings
- MSIP.Viewer.exe (PID: 2396)
INFO
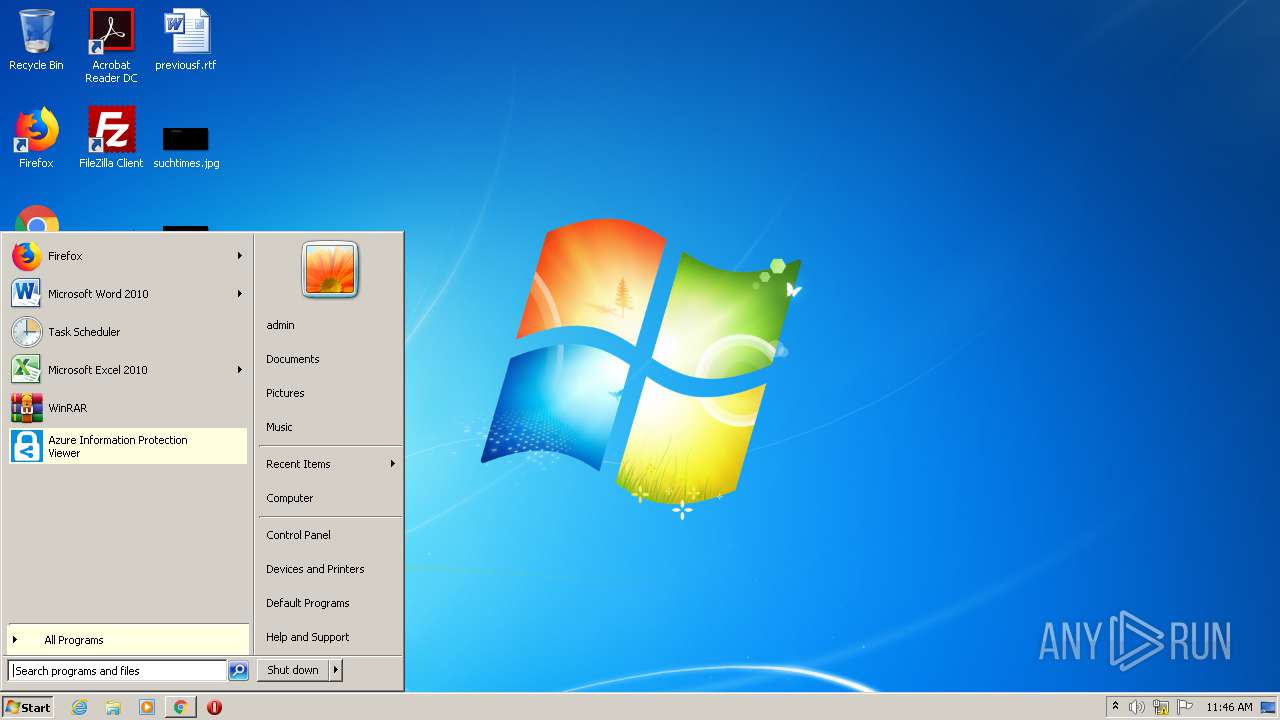
Application launched itself
- chrome.exe (PID: 1512)
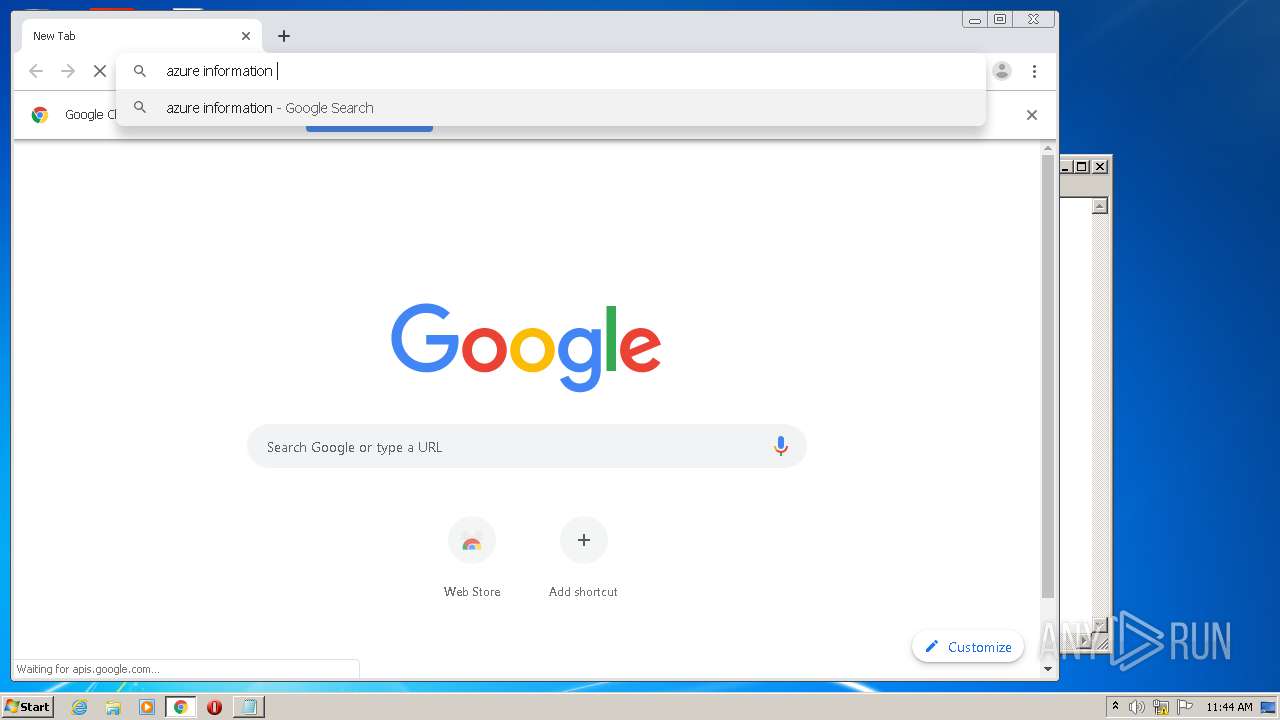
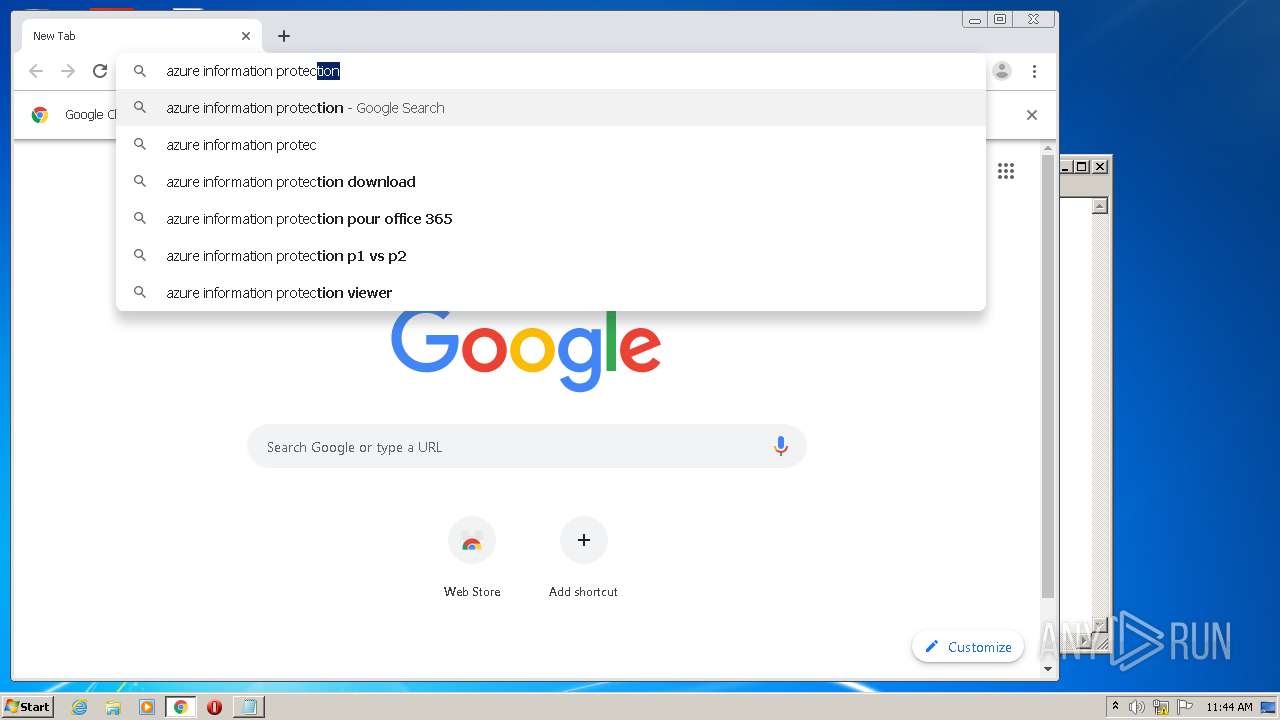
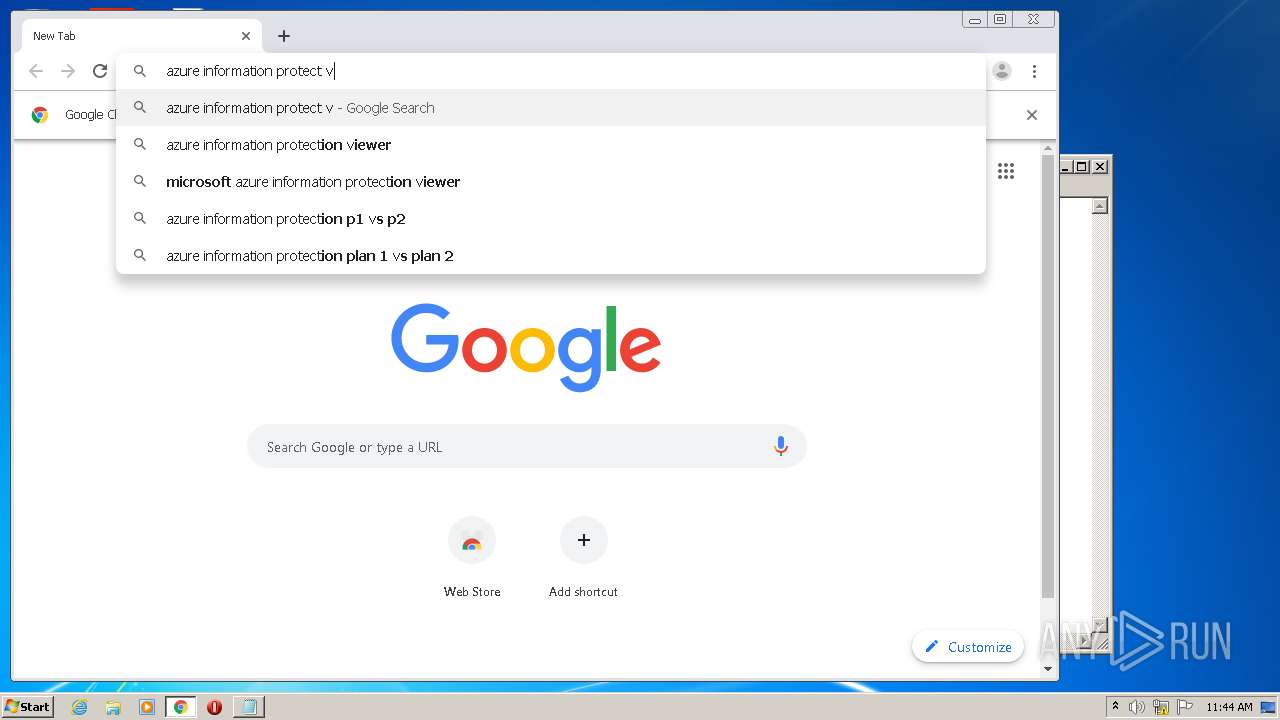
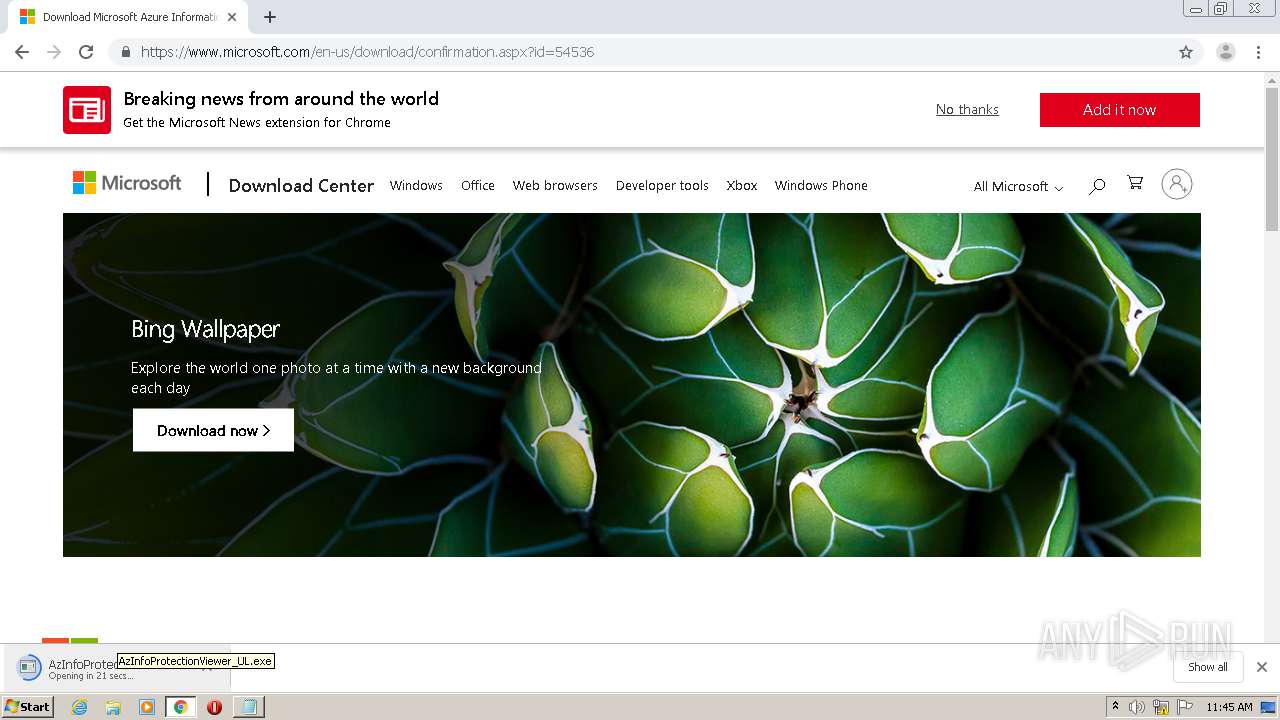
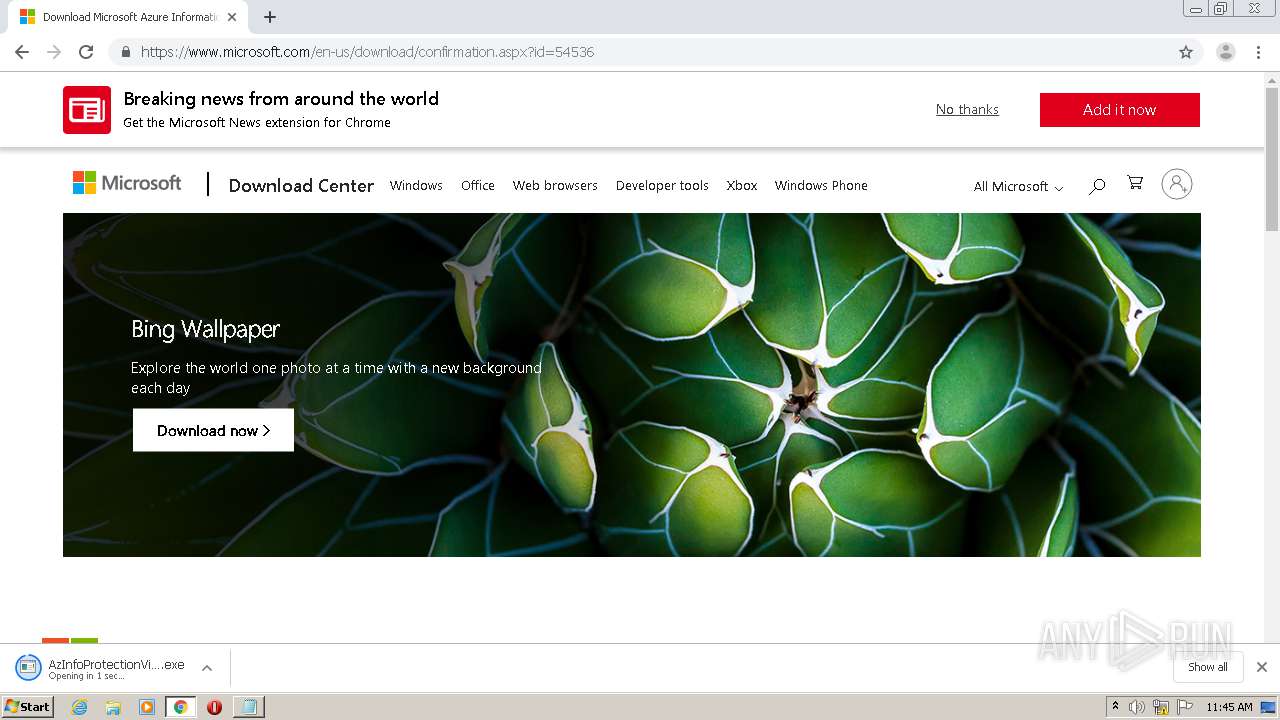
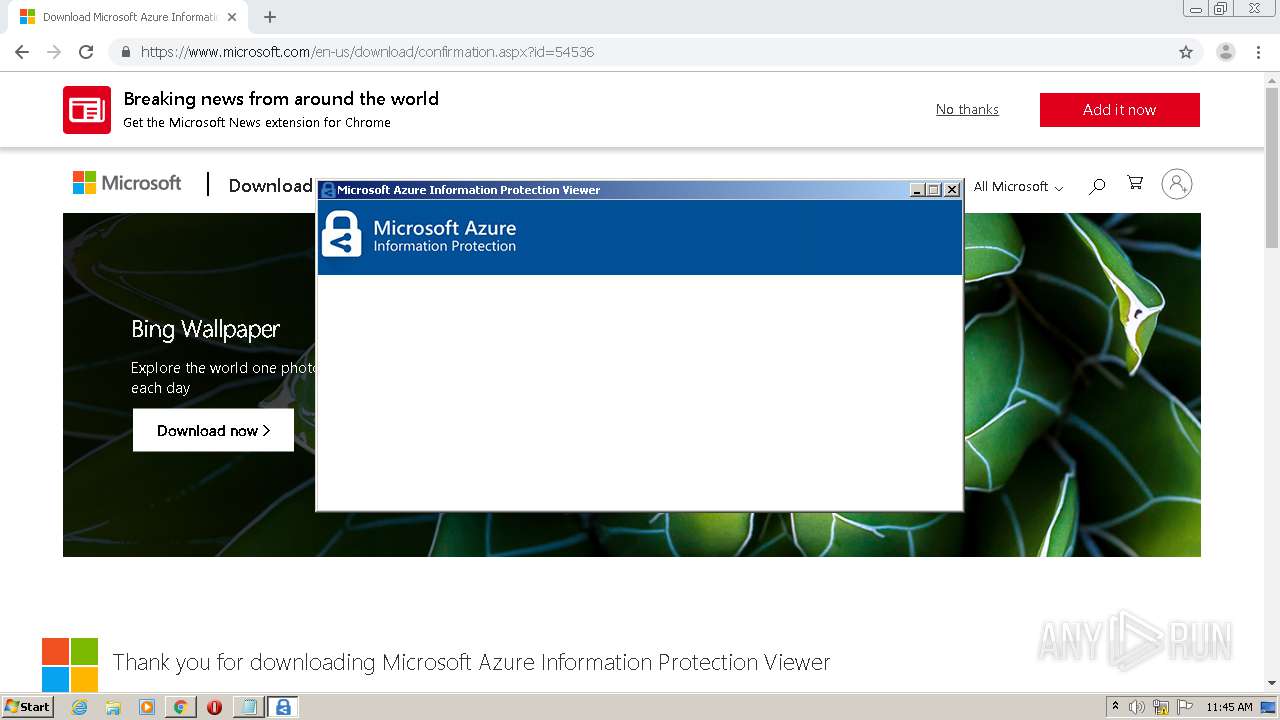
Manual execution by user
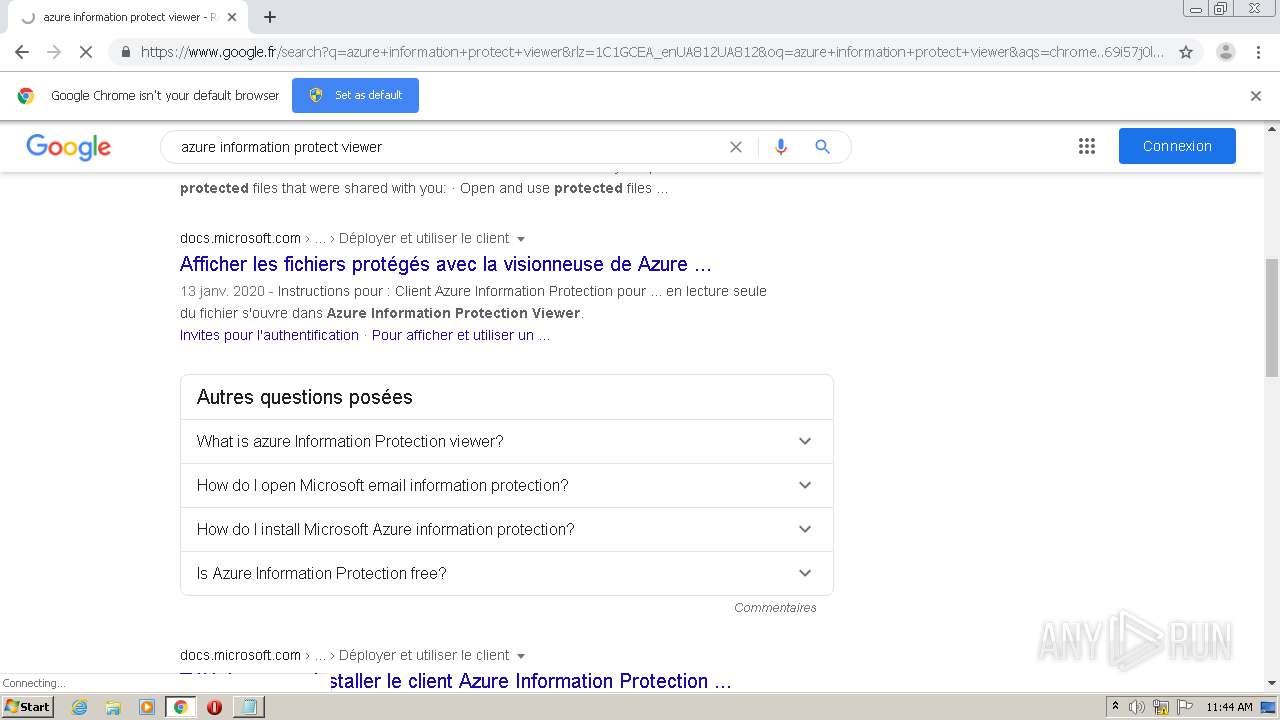
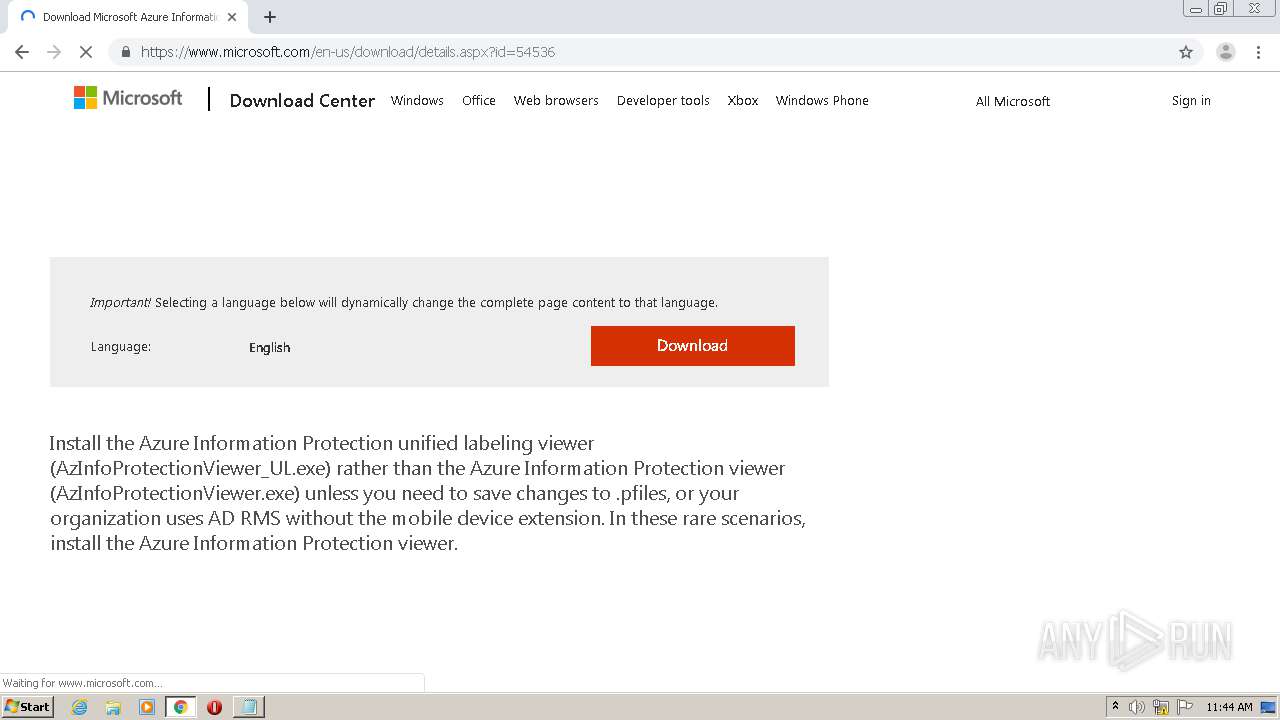
- chrome.exe (PID: 1512)
Reads the hosts file
- chrome.exe (PID: 1512)
- chrome.exe (PID: 2308)
Reads Internet Cache Settings
- chrome.exe (PID: 1512)
Reads settings of System Certificates
- chrome.exe (PID: 1512)
Dropped object may contain Bitcoin addresses
- MSIP.Viewer.exe (PID: 2396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
27
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
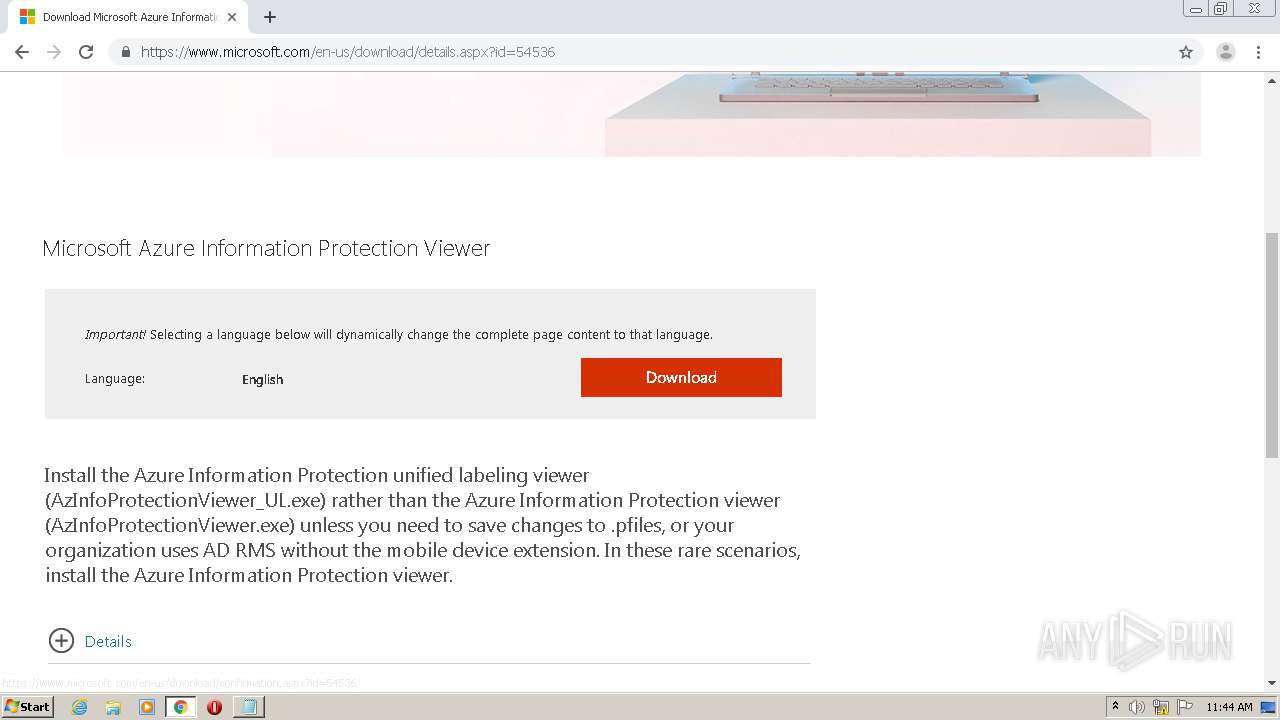
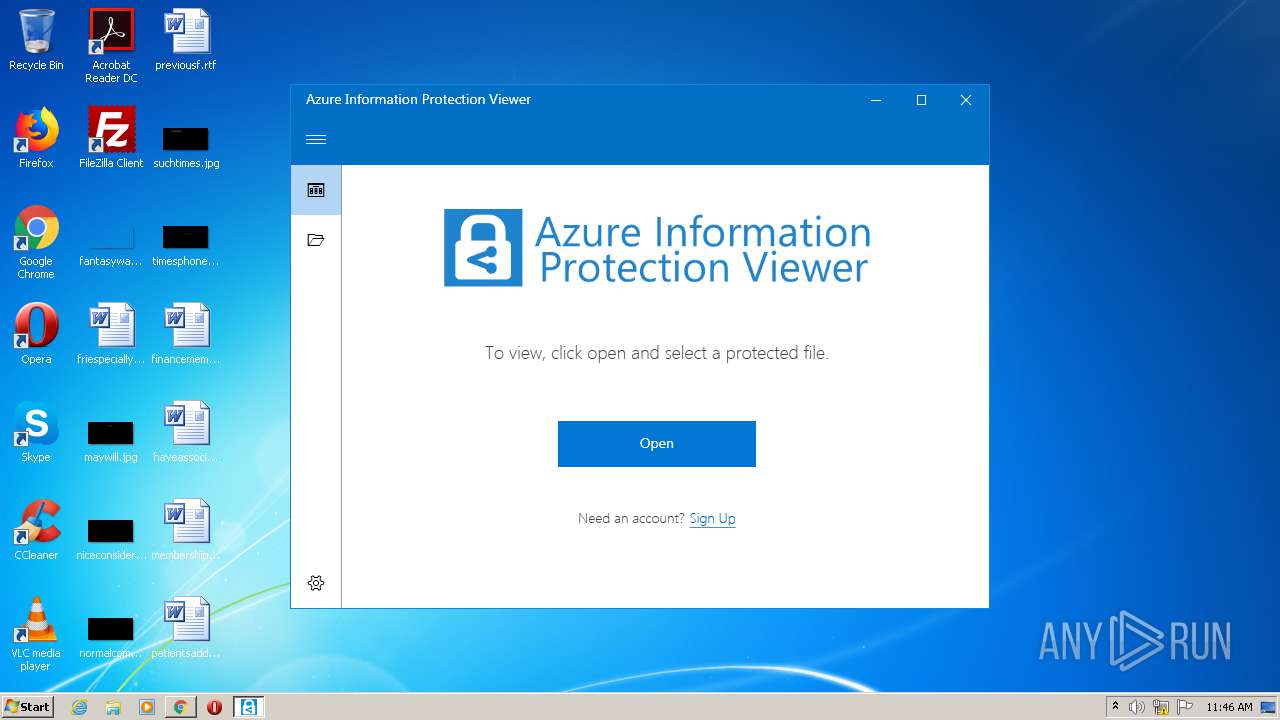
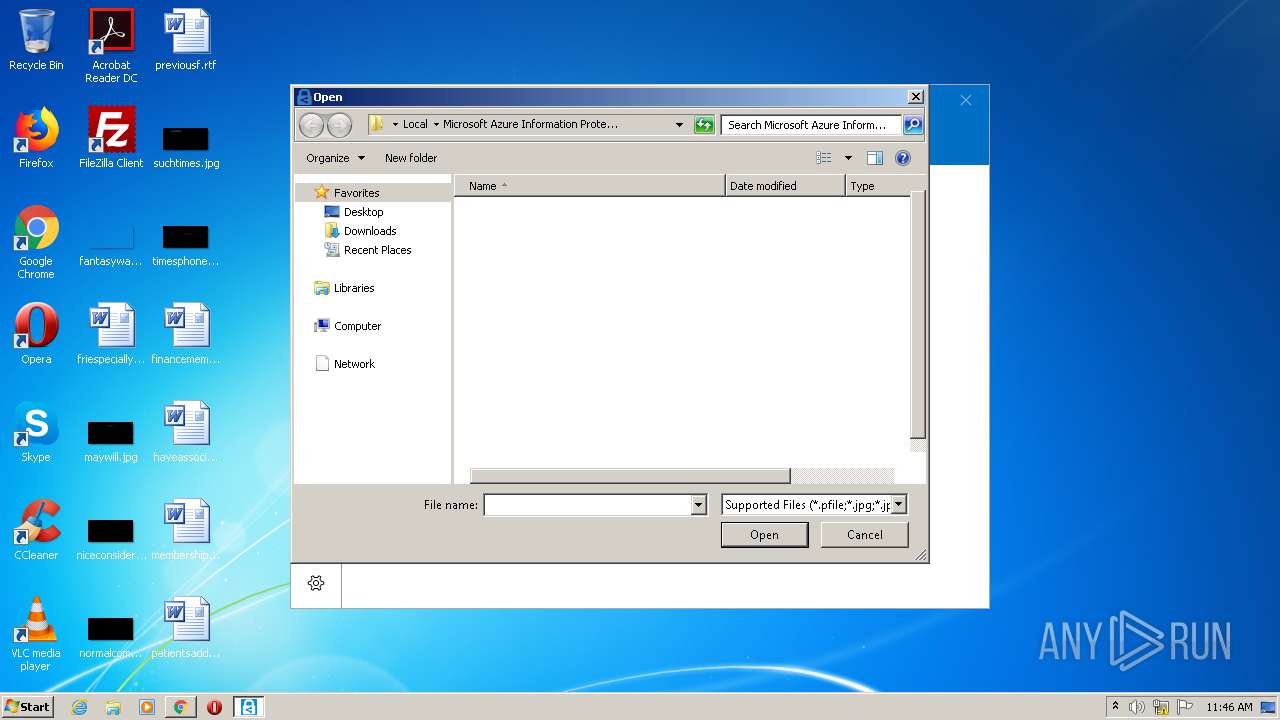
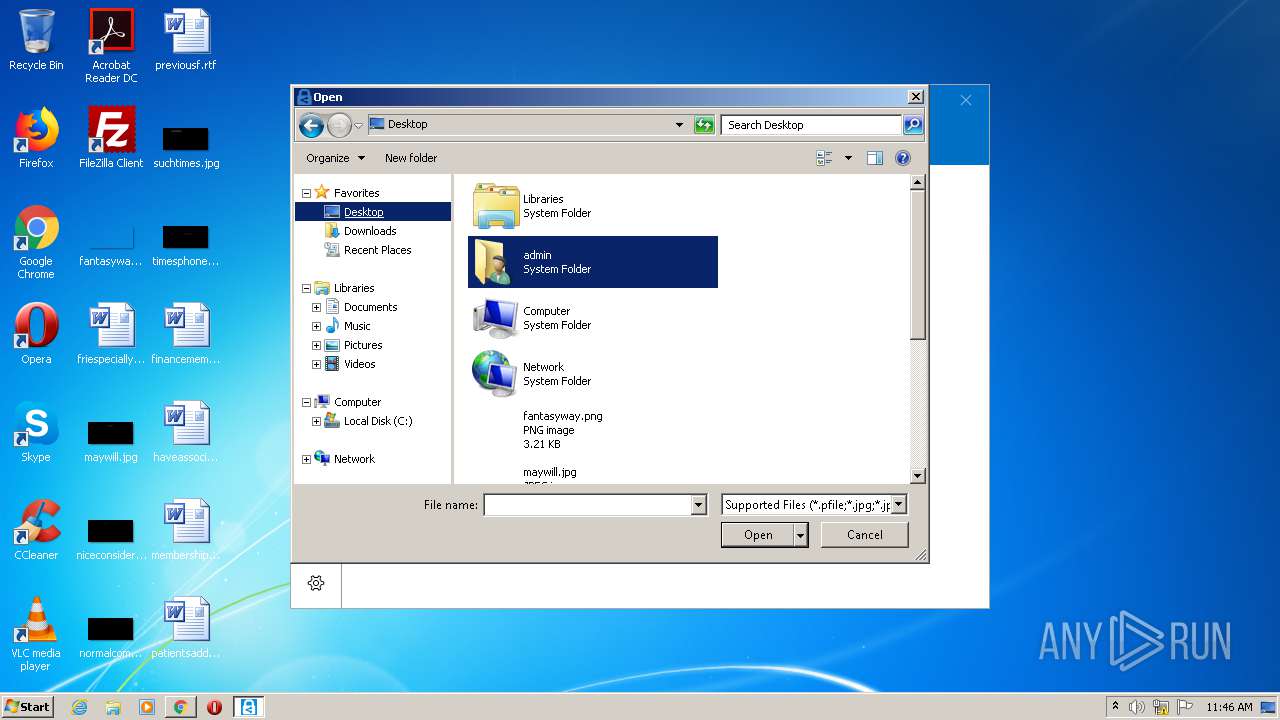
| 956 | "C:\Users\admin\Downloads\AzInfoProtectionViewer_UL.exe" | C:\Users\admin\Downloads\AzInfoProtectionViewer_UL.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Azure Information Protection Viewer Exit code: 0 Version: 2.7.99.0 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,14715581120365963434,12294522650982324709,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6152609663818179959 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,14715581120365963434,12294522650982324709,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13588879243640583852 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1716 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,14715581120365963434,12294522650982324709,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2247270929699532519 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,14715581120365963434,12294522650982324709,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12100131063608022434 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,14715581120365963434,12294522650982324709,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=192462169579350713 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,14715581120365963434,12294522650982324709,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11651737624816855868 --mojo-platform-channel-handle=3332 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 671
Read events
3 330
Write events
332
Delete events
9
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\abgrcnq.rkr |
Value: 00000000000000000100000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004A000000720000007C7532000C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D02 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Puebzr |
Value: 0000000006000000070000007BBF0600000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFF0E471AA1576D60100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004B000000720000007C7532000C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D02 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 00000000010000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFF0E471AA1576D60100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002600000000000000250000000C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A030C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A030C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A03 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 00000000010000000000000001000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFF0E471AA1576D60100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002600000000000000260000000C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A030C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A030C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A03 | |||
| (PID) Process: | (1512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
6
Suspicious files
107
Text files
163
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e3ecf12a-5fa0-4d51-82e0-9a42d19280fa.tmp | — | |
MD5:— | SHA256:— | |||
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF191e3c.TMP | text | |
MD5:— | SHA256:— | |||
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF191e0d.TMP | text | |
MD5:— | SHA256:— | |||
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF191ff2.TMP | — | |
MD5:— | SHA256:— | |||
| 1512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
55
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2396 | MSIP.Viewer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
2396 | MSIP.Viewer.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPC1vZt9qvn7bzY3Iidtbhla4mKQQUWIif1tycSCK3FD7%2FhIjo5oX%2F%2Bn0CE2EAGQzwfKaEj9NsuAgAAAAZDPA%3D | US | der | 1.79 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
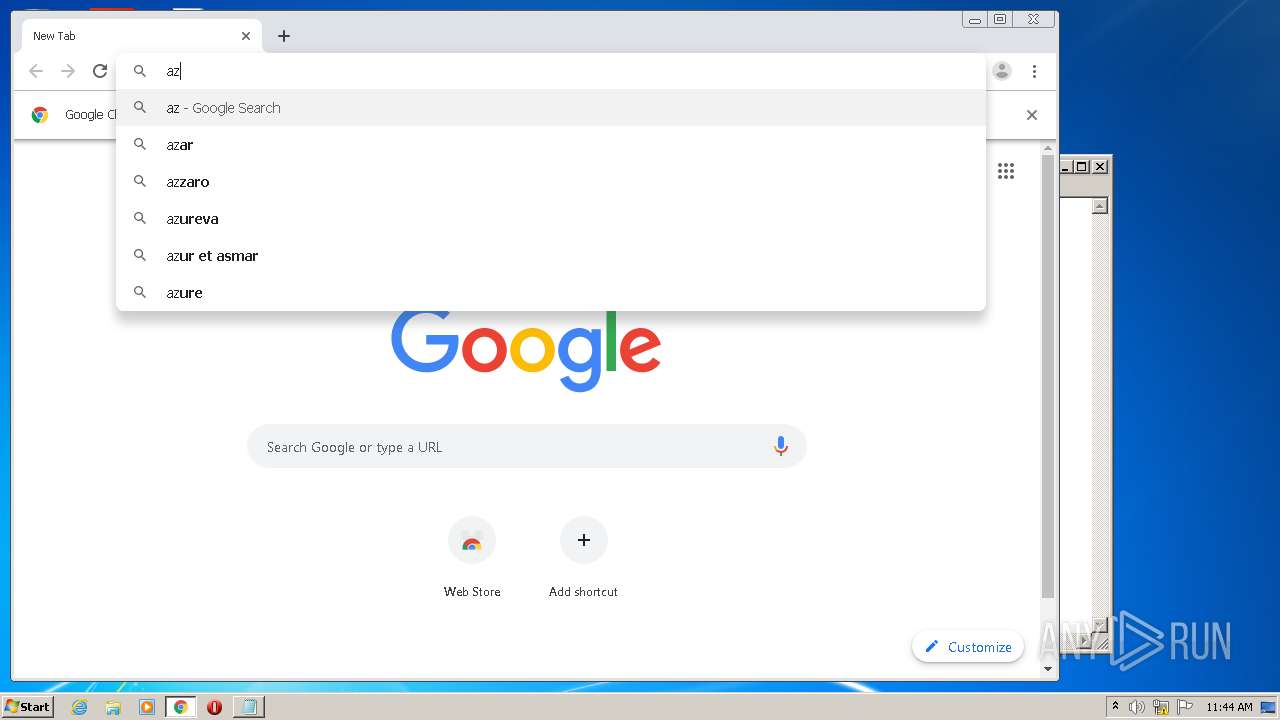
2308 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2308 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 172.217.16.131:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2308 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 216.58.210.14:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2308 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
— | — | 216.58.210.14:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |