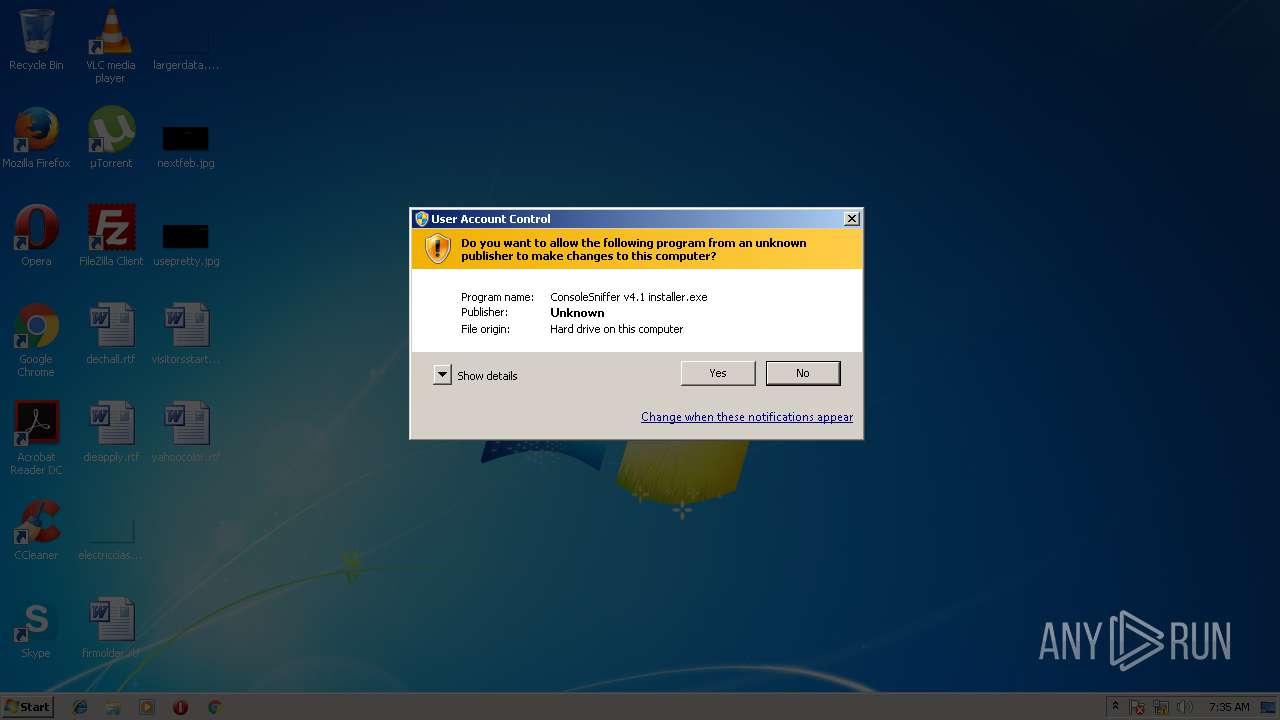
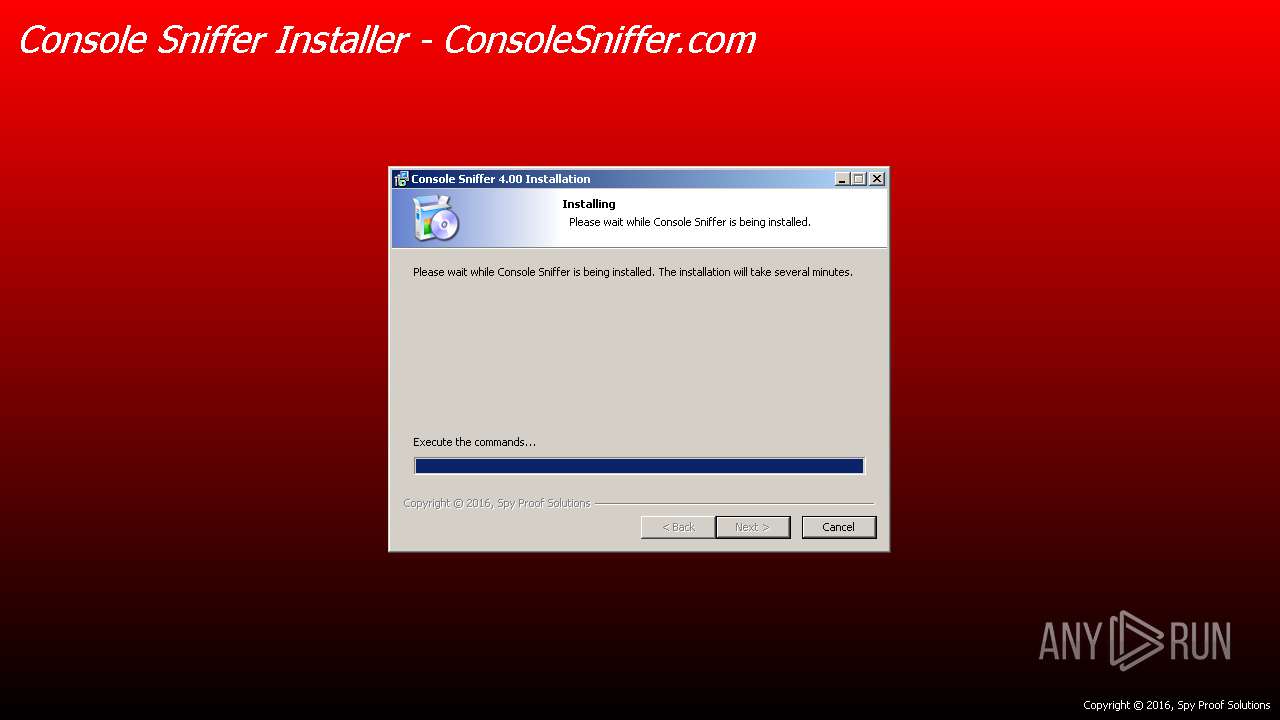
| File name: | ConsoleSniffer v4.1 installer.exe |
| Full analysis: | https://app.any.run/tasks/07c6d3c5-e09f-4baa-a90d-1af8c27d2793 |
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2018, 06:35:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9E24D7787ACBB9AB91536FC82EC84C6C |
| SHA1: | 603D7FD0AD43EDCDF369DD35FE4641CDF523F31D |
| SHA256: | 6B84979505ECF68D5FEEFBC4C47B4770E5ABC1FB18E1CE54503E05FC637812B3 |
| SSDEEP: | 196608:itMTz5OWL1WFFFBonjTfLfoZ8o3GXc9RokqF:n/EWstcvUWs9RokqF |
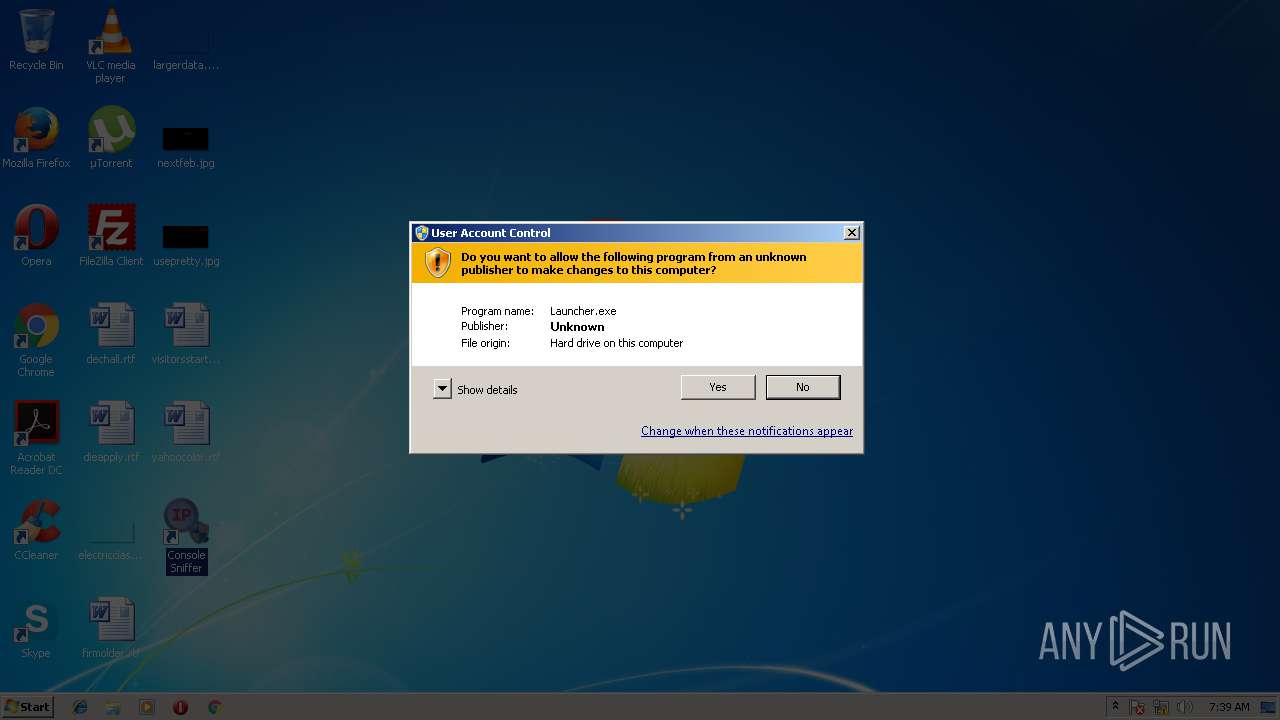
MALICIOUS
Application was dropped or rewritten from another process
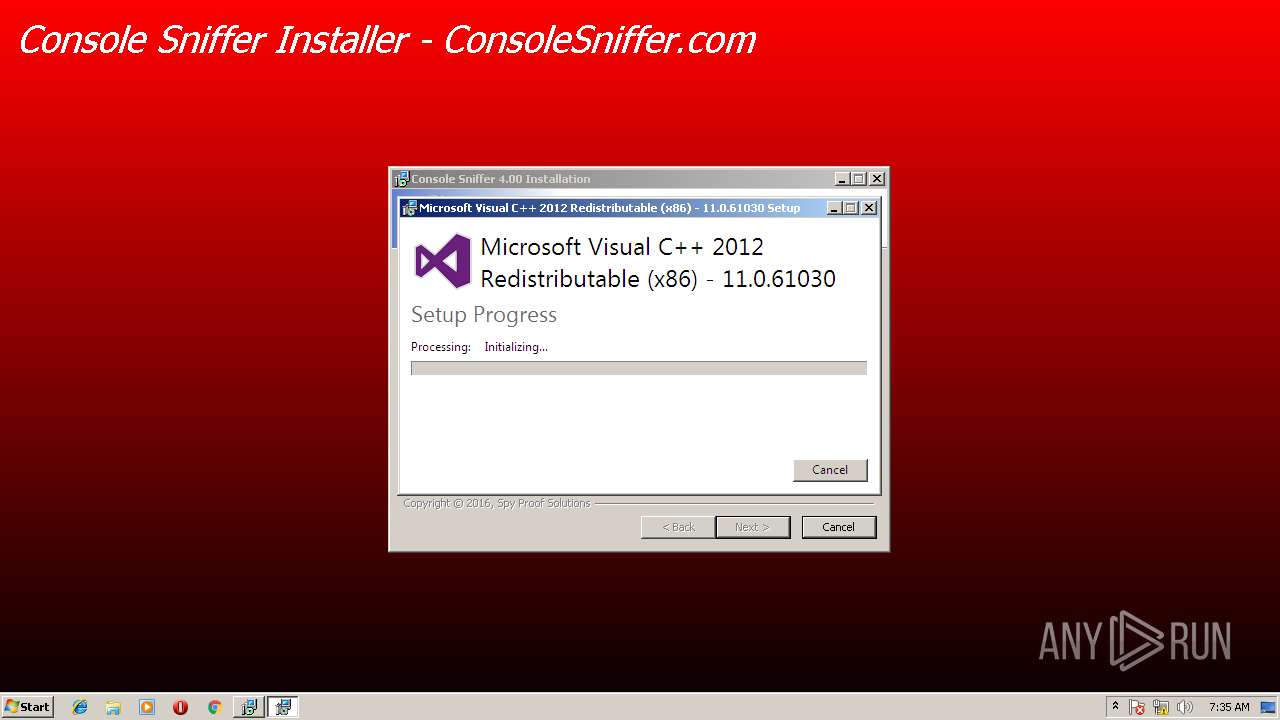
- vcredist_x86 - 2012 update 4.exe (PID: 2792)
- vcredist_x86 - 2012 update 4.exe (PID: 1396)
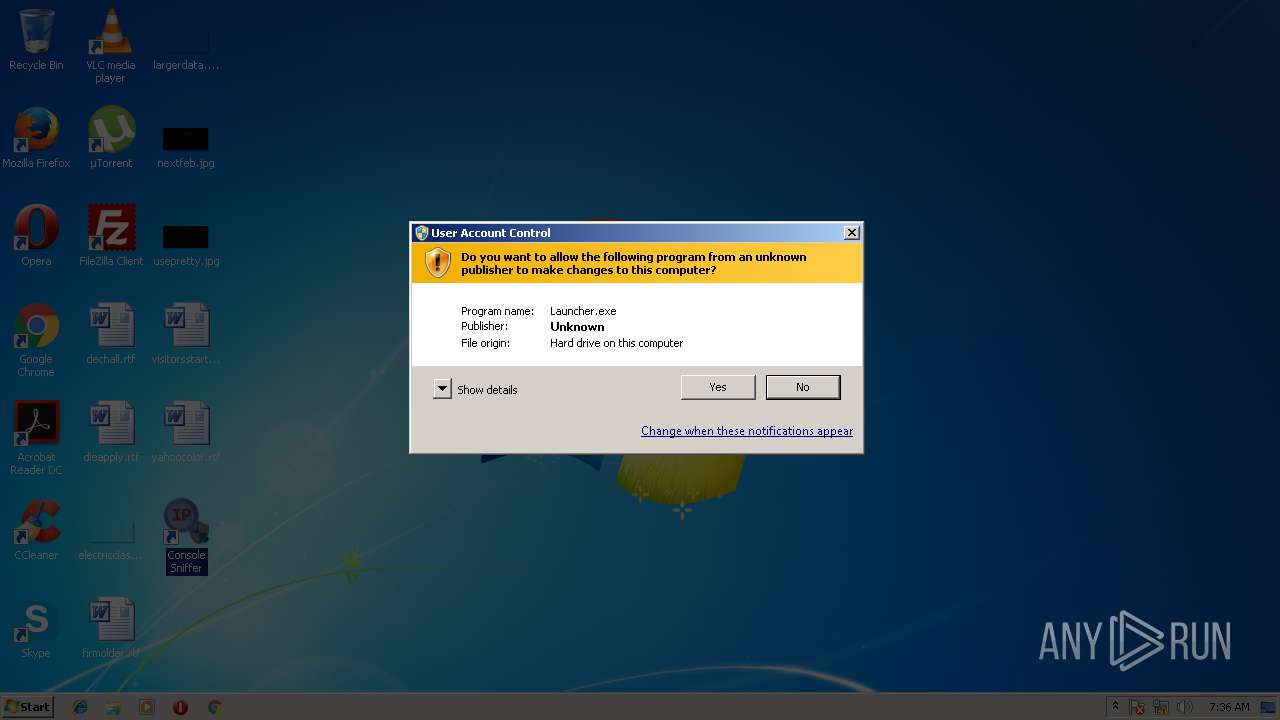
- Launcher.exe (PID: 3980)
- Installer.exe (PID: 3476)
- Launcher.exe (PID: 3752)
- ConsoleSniffer.exe (PID: 3112)
- Launcher.exe (PID: 1500)
- update.exe (PID: 2388)
- Launcher.exe (PID: 2608)
- Launcher.exe (PID: 3152)
- update.exe (PID: 3116)
- ConsoleSniffer.exe (PID: 4044)
Loads dropped or rewritten executable
- vcredist_x86 - 2012 update 4.exe (PID: 1396)
- Launcher.exe (PID: 3980)
- Launcher.exe (PID: 2608)
- Launcher.exe (PID: 1500)
- ConsoleSniffer.exe (PID: 3112)
- update.exe (PID: 2388)
- ConsoleSniffer.exe (PID: 4044)
- update.exe (PID: 3116)
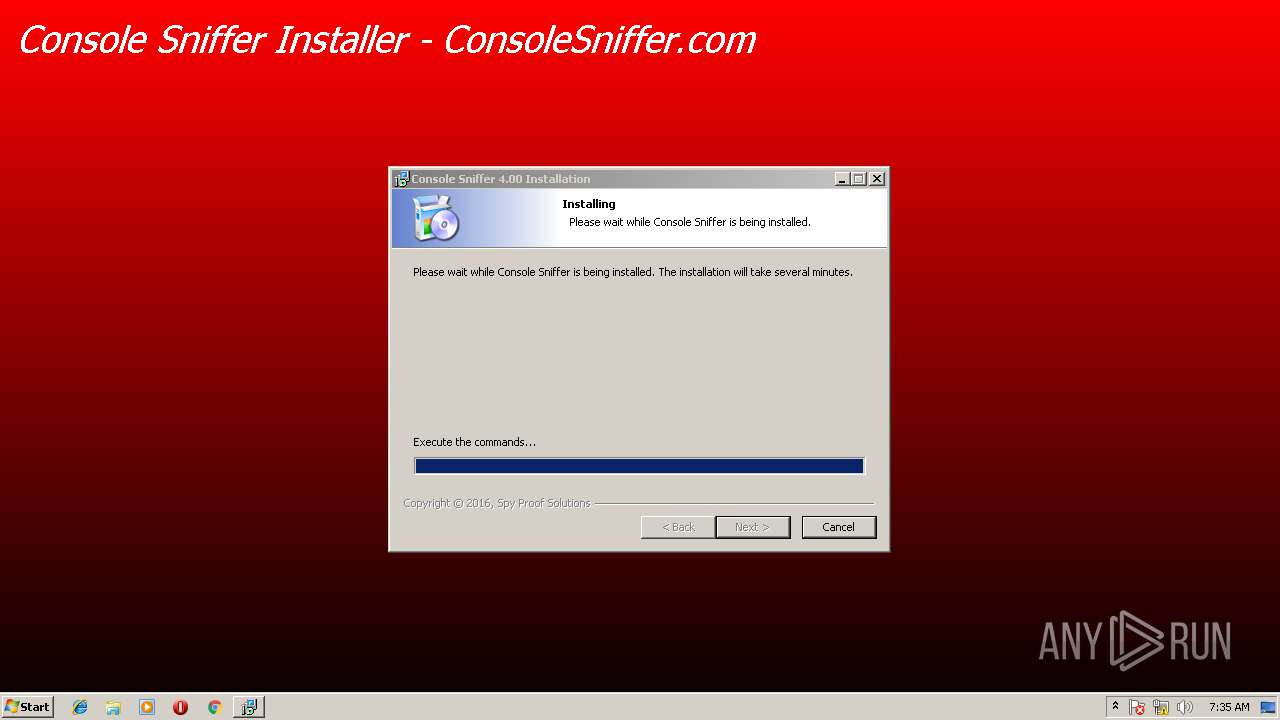
Changes the autorun value in the registry
- vcredist_x86 - 2012 update 4.exe (PID: 2792)
SUSPICIOUS
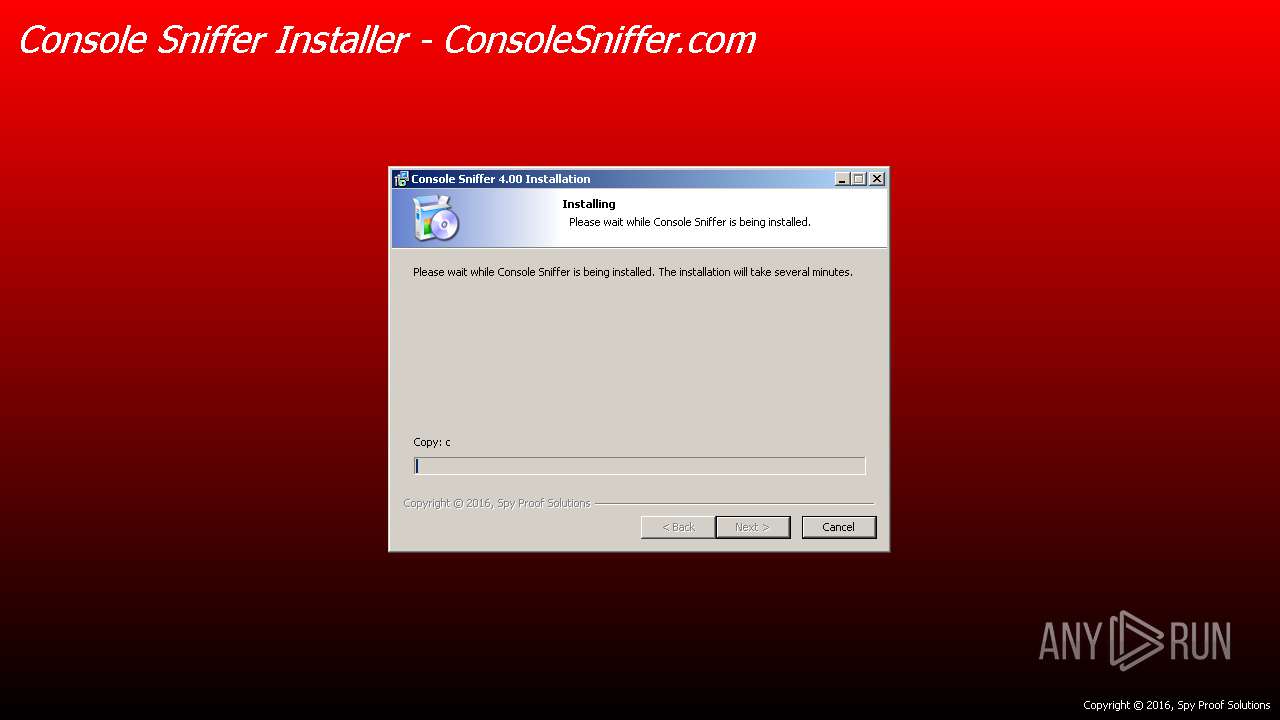
Executable content was dropped or overwritten
- vcredist_x86 - 2012 update 4.exe (PID: 1396)
- ConsoleSniffer v4.1 installer.exe (PID: 1768)
- msiexec.exe (PID: 3796)
- msiexec.exe (PID: 2892)
- Installer.exe (PID: 3476)
- DrvInst.exe (PID: 2500)
Creates a software uninstall entry
- ConsoleSniffer v4.1 installer.exe (PID: 1768)
- vcredist_x86 - 2012 update 4.exe (PID: 2792)
Creates files in the program directory
- ConsoleSniffer v4.1 installer.exe (PID: 1768)
Searches for installed software
- vcredist_x86 - 2012 update 4.exe (PID: 1396)
- vcredist_x86 - 2012 update 4.exe (PID: 2792)
Creates files in the Windows directory
- vcredist_x86 - 2012 update 4.exe (PID: 2792)
- DrvInst.exe (PID: 2500)
- Installer.exe (PID: 3476)
Creates files in the user directory
- ConsoleSniffer v4.1 installer.exe (PID: 1768)
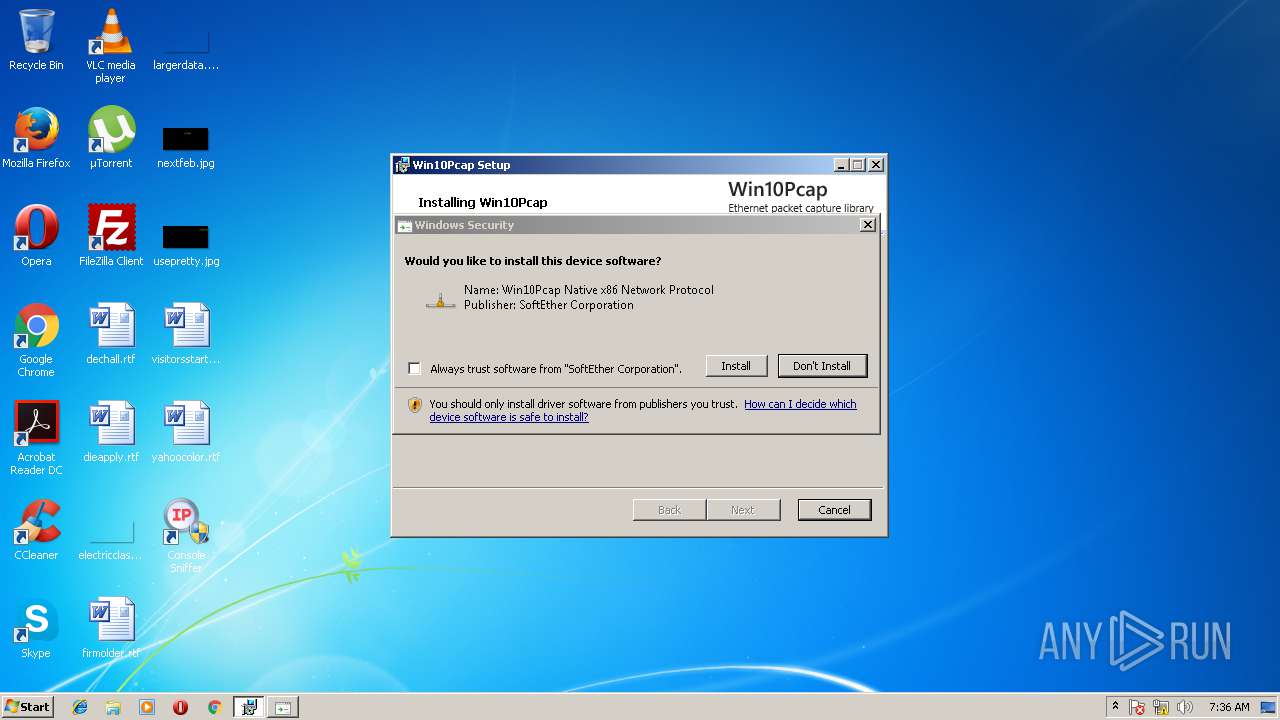
Creates or modifies windows services
- vcredist_x86 - 2012 update 4.exe (PID: 2792)
- Installer.exe (PID: 3476)
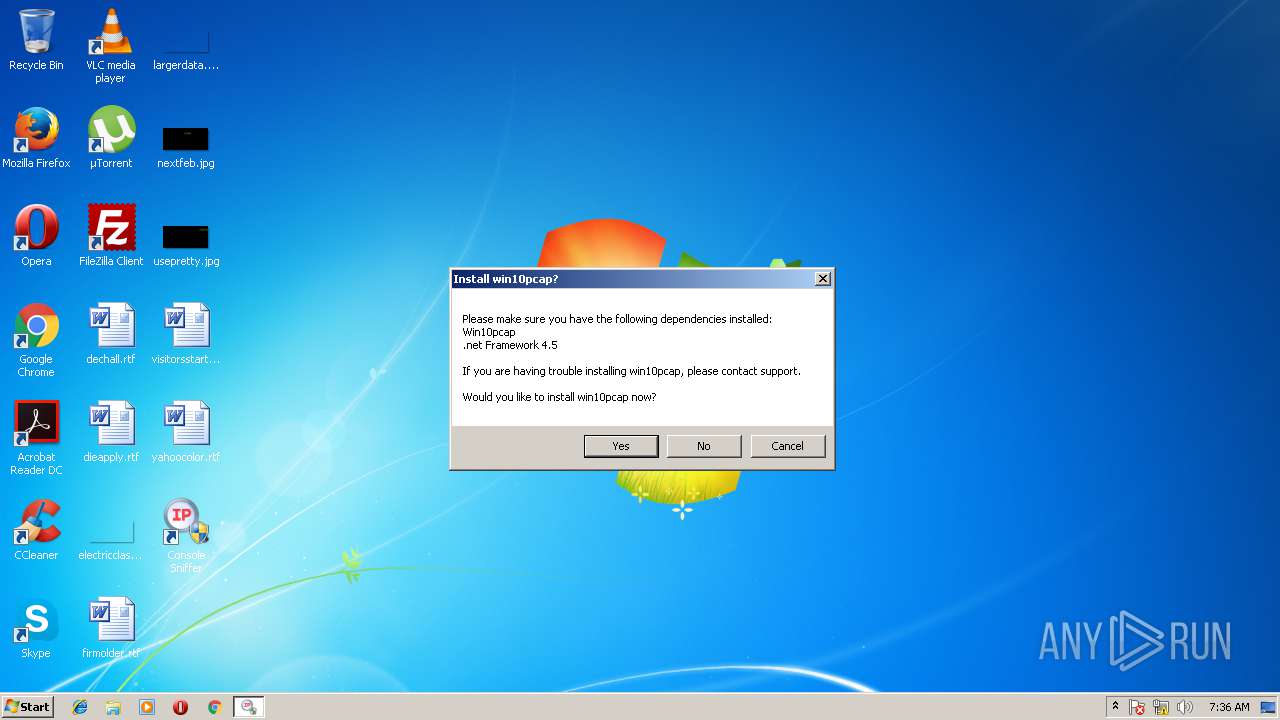
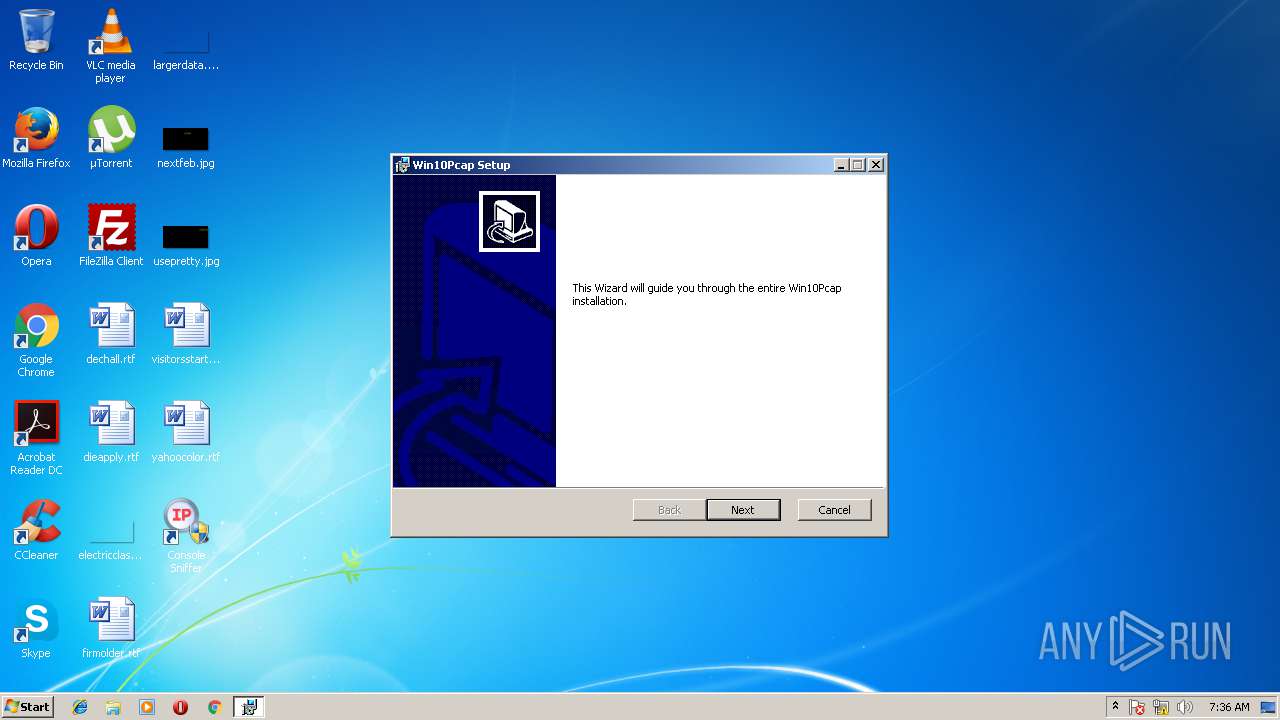
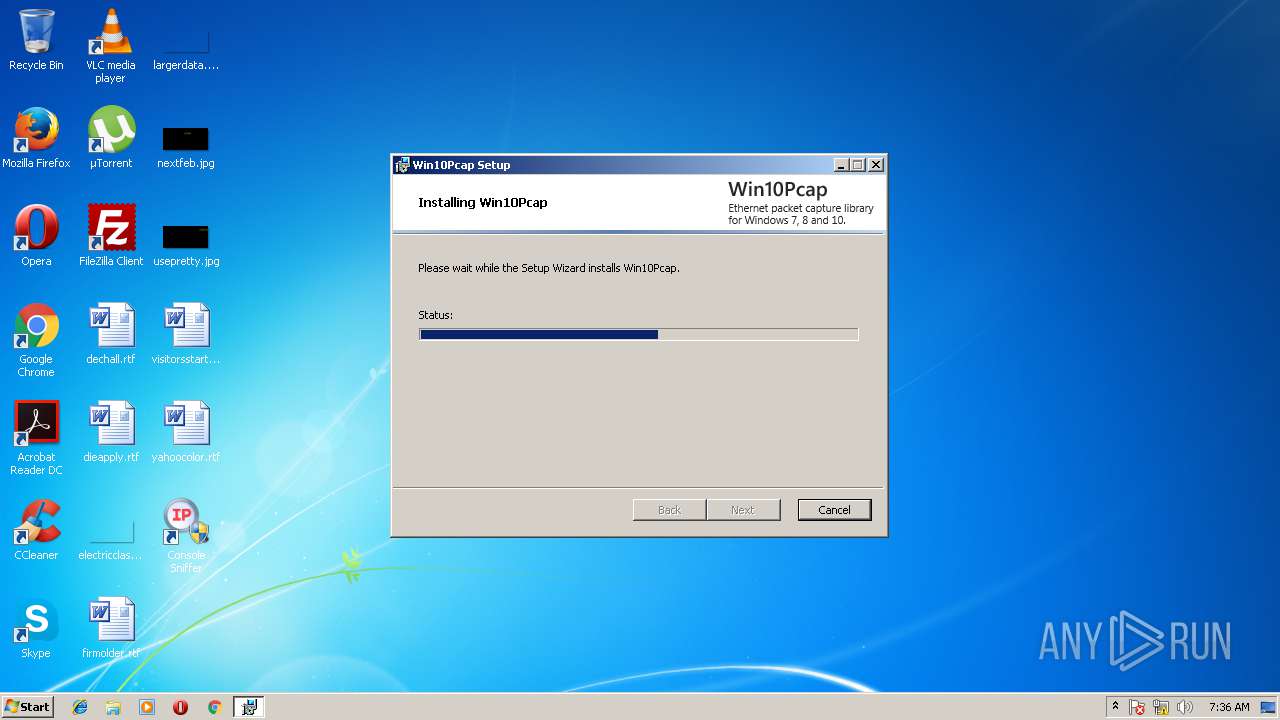
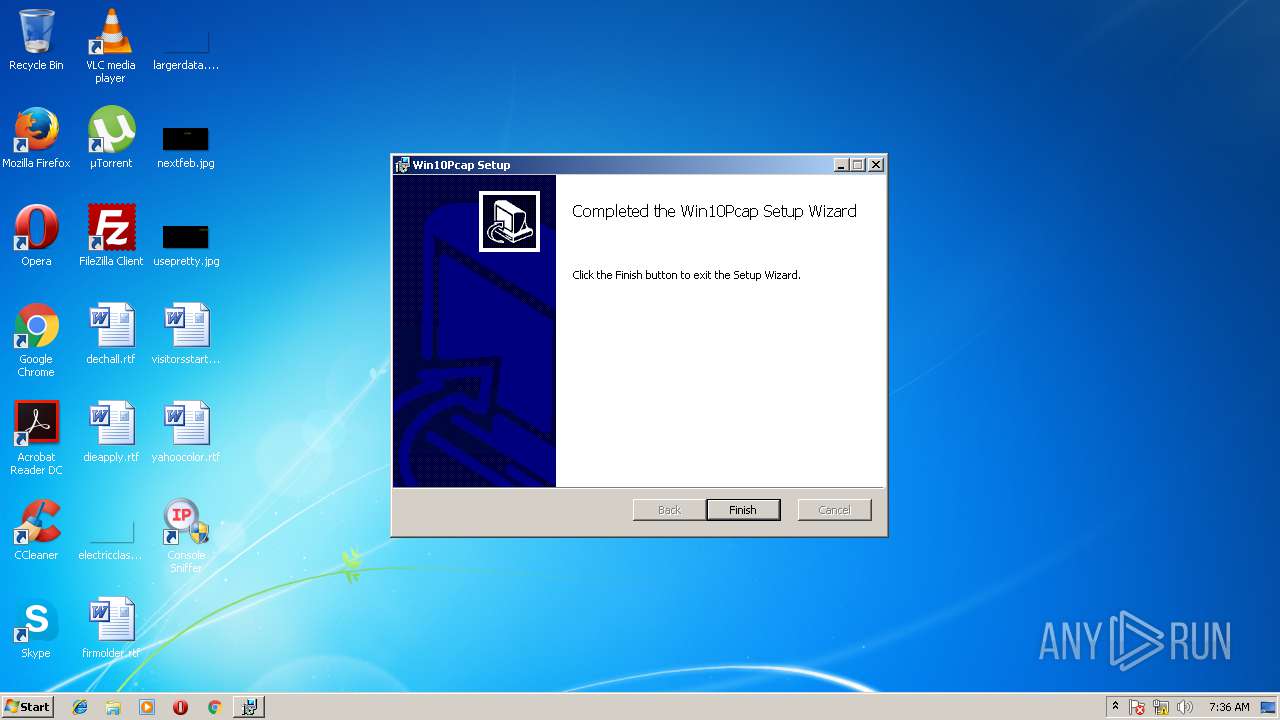
Starts Microsoft Installer
- Launcher.exe (PID: 3980)
Creates files in the driver directory
- DrvInst.exe (PID: 2500)
- Installer.exe (PID: 3476)
Removes files from Windows directory
- DrvInst.exe (PID: 2500)
- Installer.exe (PID: 3476)
INFO
Dropped object may contain URL's
- ConsoleSniffer v4.1 installer.exe (PID: 1768)
- vcredist_x86 - 2012 update 4.exe (PID: 1396)
- DrvInst.exe (PID: 2500)
- Installer.exe (PID: 3476)
- msiexec.exe (PID: 2892)
Low-level read access rights to disk partition
- vssvc.exe (PID: 4056)
Creates or modifies windows services
- msiexec.exe (PID: 2892)
- vssvc.exe (PID: 4056)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1264)
Reads settings of System Certificates
- DrvInst.exe (PID: 2564)
Creates files in the program directory
- msiexec.exe (PID: 2892)
Changes settings of System certificates
- DrvInst.exe (PID: 2500)
Application launched itself
- msiexec.exe (PID: 2892)
Creates a software uninstall entry
- msiexec.exe (PID: 2892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (49.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (16.2) |
| .scr | | | Windows screen saver (14.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 148992 |
| InitializedDataSize: | 31744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25468 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
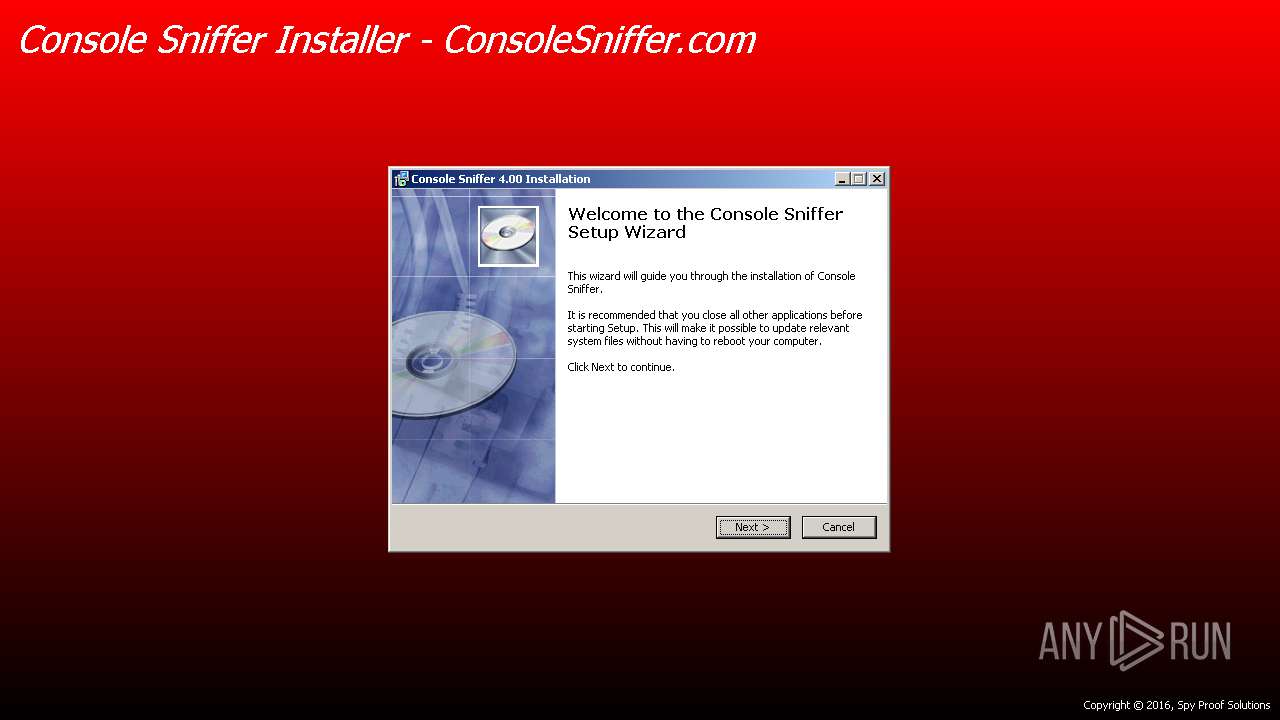
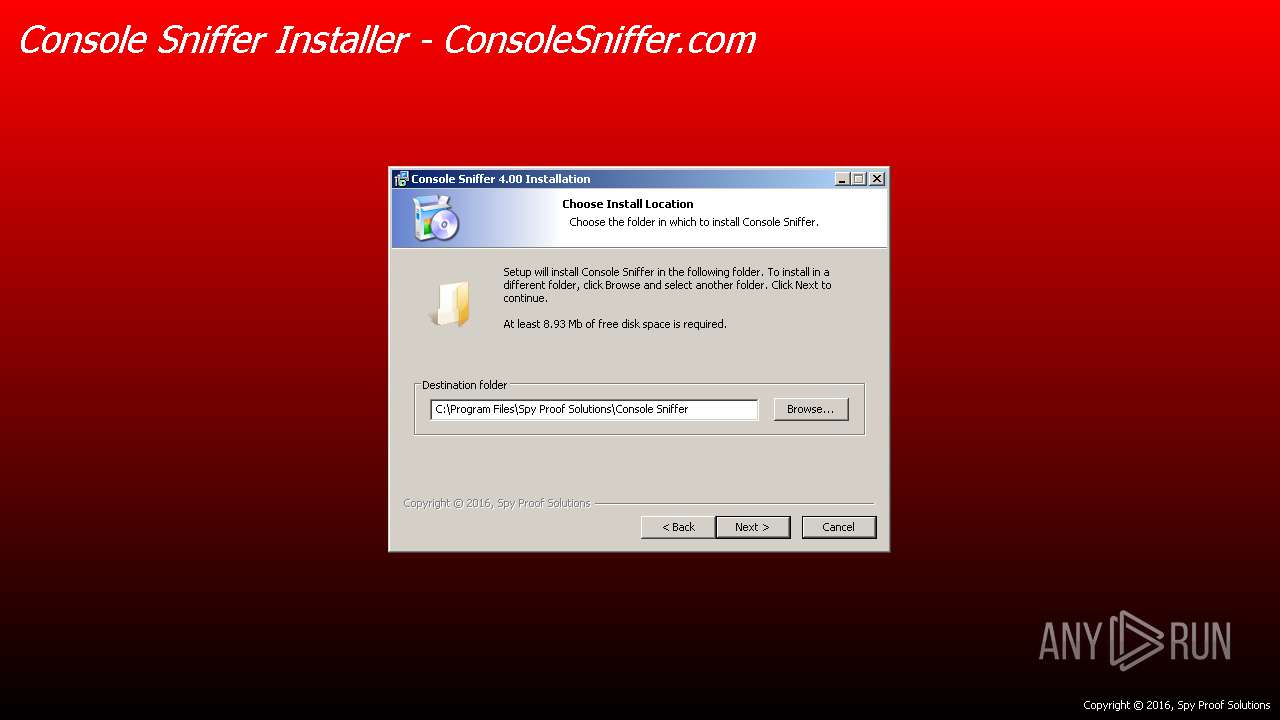
| CompanyName: | Spy Proof Solutions |
| FileDescription: | Console Sniffer 4.00 Installation |
| FileVersion: | 4.00 |
| LegalCopyright: | Spy Proof Solutions |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Spy Proof Solutions |
| FileDescription: | Console Sniffer 4.00 Installation |
| FileVersion: | 4.00 |
| LegalCopyright: | Spy Proof Solutions |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x00001CDC | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.76069 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 3.25755 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.01345 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 3.92897 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 4.27475 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.57938 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
68
Monitored processes
21
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1264 | C:\Windows\system32\MsiExec.exe -Embedding D91849C224512E3486B659272D22A533 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Spy Proof Solutions\Console Sniffer\vcredist_x86 - 2012 update 4.exe" /passive /norestart -burn.unelevated BurnPipe.{F447287A-7A72-4ED0-A653-73FA71E984F4} {3A513642-9232-4D1E-857D-DAFEA1E92A1E} 2792 | C:\Program Files\Spy Proof Solutions\Console Sniffer\vcredist_x86 - 2012 update 4.exe | vcredist_x86 - 2012 update 4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Spy Proof Solutions\Console Sniffer\Launcher.exe" | C:\Program Files\Spy Proof Solutions\Console Sniffer\Launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1768 | "C:\Users\admin\Downloads\ConsoleSniffer v4.1 installer.exe" | C:\Users\admin\Downloads\ConsoleSniffer v4.1 installer.exe | explorer.exe | ||||||||||||
User: admin Company: Spy Proof Solutions Integrity Level: HIGH Description: Console Sniffer 4.00 Installation Exit code: 0 Version: 4.00 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Spy Proof Solutions\Console Sniffer\update.exe" | C:\Program Files\Spy Proof Solutions\Console Sniffer\update.exe | — | Launcher.exe | |||||||||||
User: admin Company: Plan A Software Integrity Level: HIGH Description: An unmanaged command line application for injecting the .net runtime and .net assemblies into x86 or x64 unmanaged or managed remote processes. Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2500 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{77c3b44b-4ffa-0118-318d-0c5d9208dd79}\Win10Pcap.inf" "0" "631592c13" "000005A4" "WinSta0\Default" "0000057C" "208" "C:\Program Files\Win10Pcap\Win32\drivers\win78" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot44" "" "" "65733adb3" "00000000" "0000057C" "000005D4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Spy Proof Solutions\Console Sniffer\Launcher.exe" | C:\Program Files\Spy Proof Solutions\Console Sniffer\Launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2792 | "C:\Program Files\Spy Proof Solutions\Console Sniffer\vcredist_x86 - 2012 update 4.exe" /passive /norestart | C:\Program Files\Spy Proof Solutions\Console Sniffer\vcredist_x86 - 2012 update 4.exe | ConsoleSniffer v4.1 installer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 2832 | "C:\Users\admin\Downloads\ConsoleSniffer v4.1 installer.exe" | C:\Users\admin\Downloads\ConsoleSniffer v4.1 installer.exe | — | explorer.exe | |||||||||||
User: admin Company: Spy Proof Solutions Integrity Level: MEDIUM Description: Console Sniffer 4.00 Installation Exit code: 3221226540 Version: 4.00 Modules
| |||||||||||||||
Total events
1 496
Read events
893
Write events
580
Delete events
23
Modification events
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | DisplayName |
Value: Console Sniffer 4.00 | |||
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | DisplayVersion |
Value: 4.00 | |||
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | VersionMajor |
Value: 4 | |||
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | VersionMinor |
Value: 0 | |||
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | Publisher |
Value: Spy Proof Solutions | |||
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Spy Proof Solutions\Console Sniffer\Uninstall.exe | |||
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Spy Proof Solutions\Console Sniffer\Uninstall.exe | |||
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Spy Proof Solutions\Console Sniffer\ | |||
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | InstallSource |
Value: C:\Users\admin\Downloads\ | |||
| (PID) Process: | (1768) ConsoleSniffer v4.1 installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Console Sniffer 4.00 |
| Operation: | write | Name: | InstallDate |
Value: 20180611 | |||
Executable files
37
Suspicious files
16
Text files
183
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:AF5DE111142A20EA6F01AB6E1606FDC2 | SHA256:4DE4CAC91A55053A0C29AD262588B411C19C3FA625C421EF7B95B9EE4F9E3310 | |||
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Users\admin\AppData\Local\Temp\$inst\7.tmp | image | |
MD5:696641D2325E8B142B6C16D1183ACA43 | SHA256:4A56FFCE0E414F3495F70E9C2960837DF25423B0DBAFD21A073DBDBAA461BC90 | |||
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Program Files\Spy Proof Solutions\Console Sniffer\atheme.dll | executable | |
MD5:C0CF544B1B6308236A4E8A8998A56DCC | SHA256:BDC643CE9F9496CCE85A3F9E8F483E1E1766F4891CEC6A7245C0CB41B4135776 | |||
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Program Files\Spy Proof Solutions\Console Sniffer\Bootstrap.dll | executable | |
MD5:C7824FEAC987C3983553525E58D937F1 | SHA256:2A2759A2FC05841E417F2AF6C80F381F06093254AE36C9E4AB758F7C5A08EB1F | |||
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Program Files\Spy Proof Solutions\Console Sniffer\Launcher.exe | executable | |
MD5:345E0B839A2F5DDC69BCC46F6C27FEE3 | SHA256:2E9EF7080AE71971B90D6B91122A91F13AF0D74E898BCE3E3A6E41ED1F958C6A | |||
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Program Files\Spy Proof Solutions\Console Sniffer\ConsoleSniffer.exe | executable | |
MD5:24BFA107CD277DCED68B9DB818F8D773 | SHA256:A59FCC0B7AD4D48DEEDEC39DFF096CF4FAA0E93526A3A44A96C4F451C33A74A0 | |||
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Users\admin\AppData\Local\Temp\$inst\5.tmp | image | |
MD5:AB2021E67E0E08657288D880ABFBAA72 | SHA256:331D997E586CBA40D4DA0587887FC4CAA4CC44E53421737DAFA67E67445E6753 | |||
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Program Files\Spy Proof Solutions\Console Sniffer\d | executable | |
MD5:C614A015978930363C12E0F722884C78 | SHA256:84A1E5BECE6CC615A1EB55D0514CB2C3633D03E35BE441DFA4855809F8C0DB49 | |||
| 1768 | ConsoleSniffer v4.1 installer.exe | C:\Program Files\Spy Proof Solutions\Console Sniffer\c | executable | |
MD5:382CD65512DE4F47E3F6809A90DCDB7C | SHA256:1D9E26121EFD940B15BDFC96EB42EB56C364F37F26E4A437DA817C0DF897F695 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
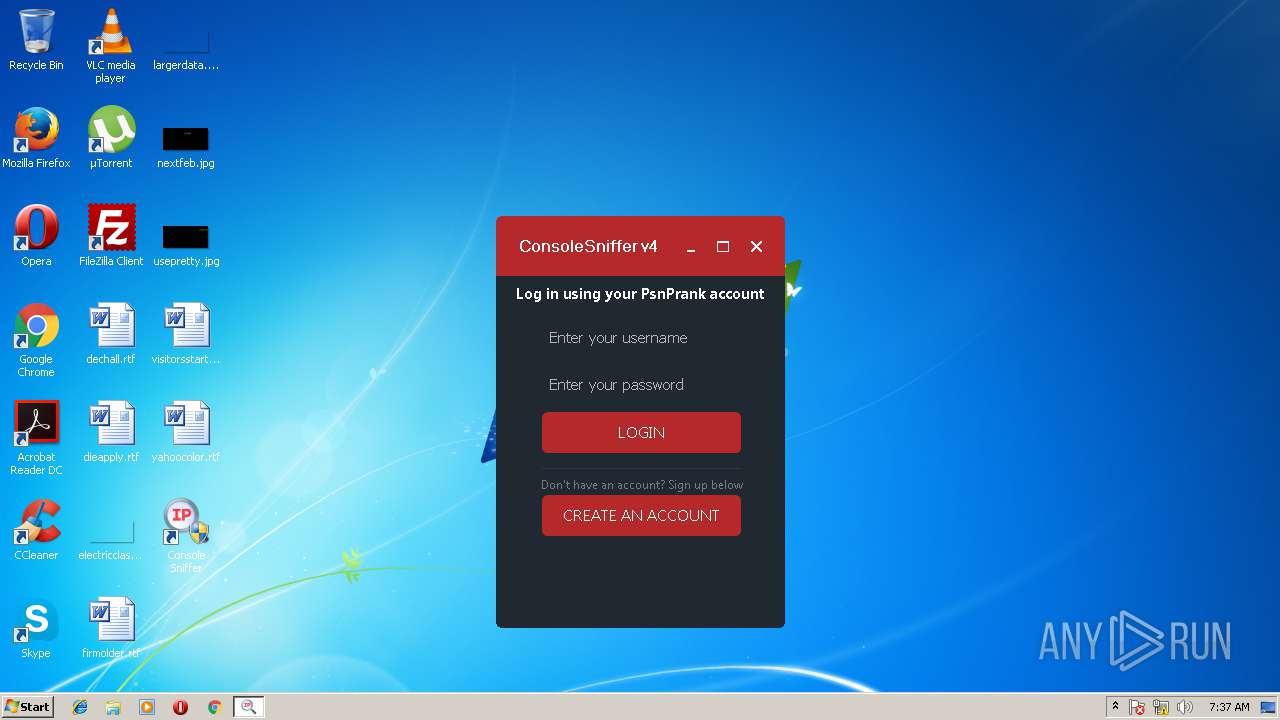
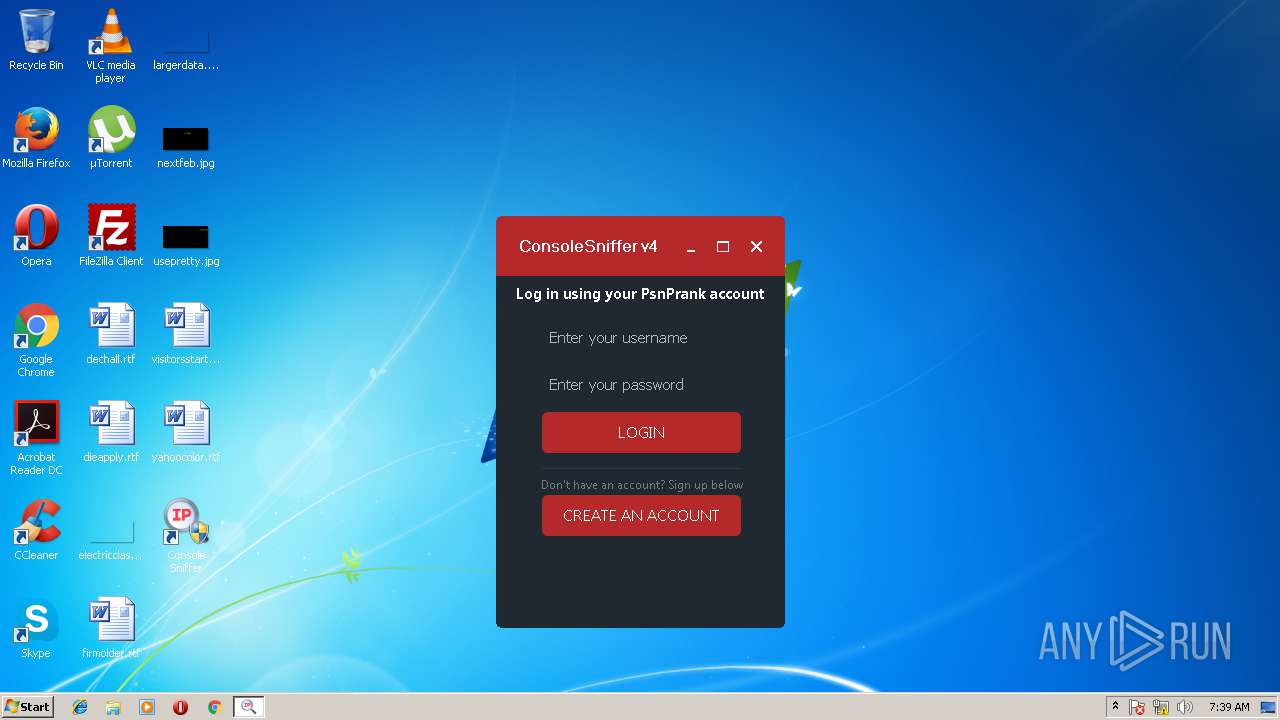
3112 | ConsoleSniffer.exe | GET | 200 | 149.56.133.157:80 | http://hub.psnprank.com/api/?a=sendmessage&user_triggered=true&user=Enter%20your%20username&pass=Enter%20your%20password&sniff&id=w6C%2FczPD73DKSrGIOoDwi3vvGAPNc0v%2F&k=FC4ED6AIl2NAox%2BAKLpddoLNKeHwutRPYP3beqSr2r4yPQBX%2FsiP4MvENkw76BCQKQCHJJ4iBBg%3D&version=4&ran=42644&license_email= | CA | text | 41 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3112 | ConsoleSniffer.exe | 149.56.133.157:80 | hub.psnprank.com | OVH SAS | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hub.psnprank.com |
| unknown |