| File name: | Windows7-USB-DVD-Download-Tool-Installer-en-US.exe |
| Full analysis: | https://app.any.run/tasks/2f0e46e3-9104-4737-84ef-42334e046fd8 |
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2019, 03:44:11 |
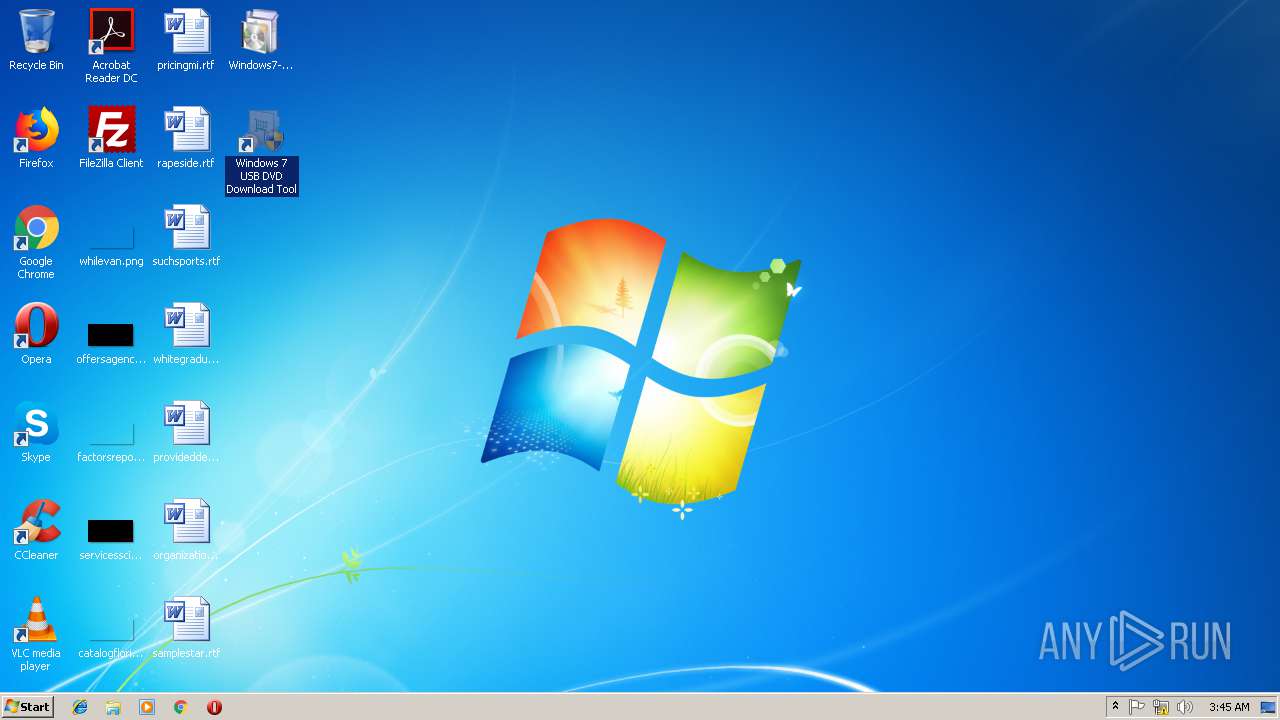
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | AF911BE206423BF440EA9D4DF075A632 |
| SHA1: | ED1108A525066D1F850023CB5BFA05FC4ED21983 |
| SHA256: | 6B7CEA4838D892A0A0F625BAB2DF3D378A035C365209DB3C573253F037882229 |
| SSDEEP: | 49152:JDHlPyp6jE1/8Sfov72CmSj/pL2gyIPgaStBPEBiwChHHVPlcnSebHc8:DaUjw/8Xv69fgyIPgaXiPbPlzer9 |
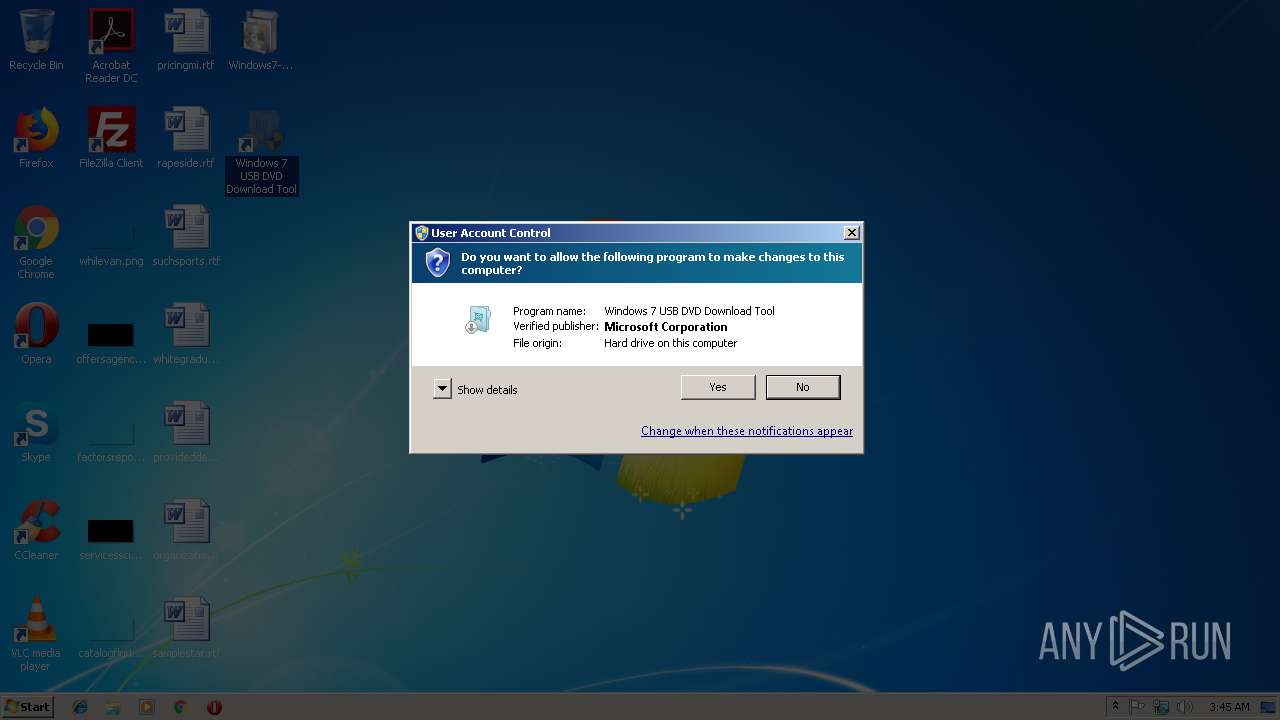
MALICIOUS
Application was dropped or rewritten from another process
- Windows7-USB-DVD-Download-Tool.exe (PID: 2132)
- Windows7-USB-DVD-Download-Tool.exe (PID: 3780)
Loads dropped or rewritten executable
- explorer.exe (PID: 116)
SUSPICIOUS
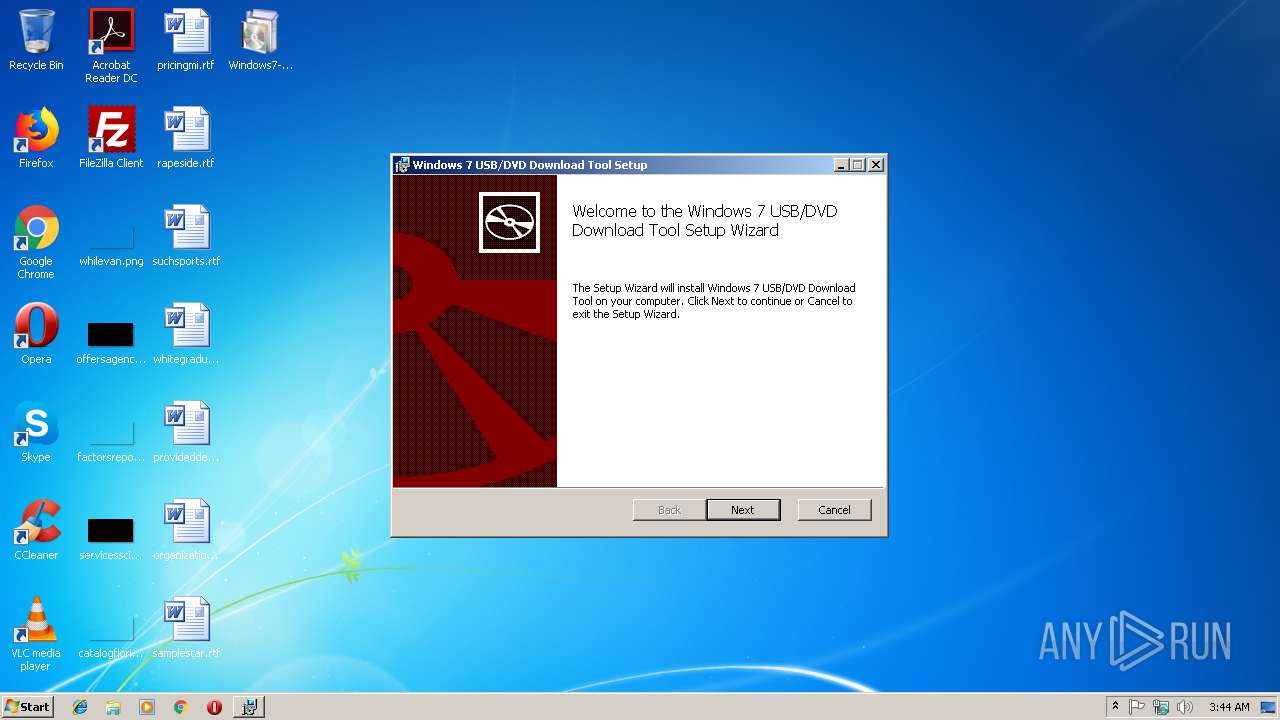
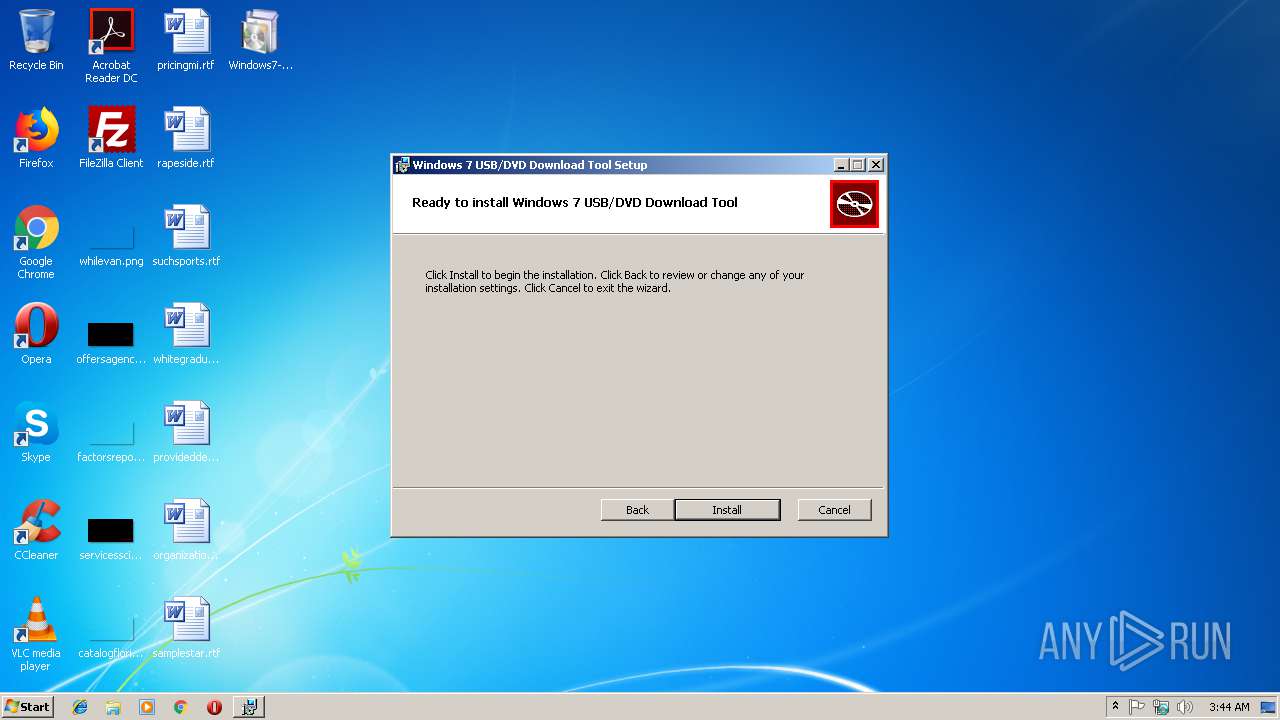
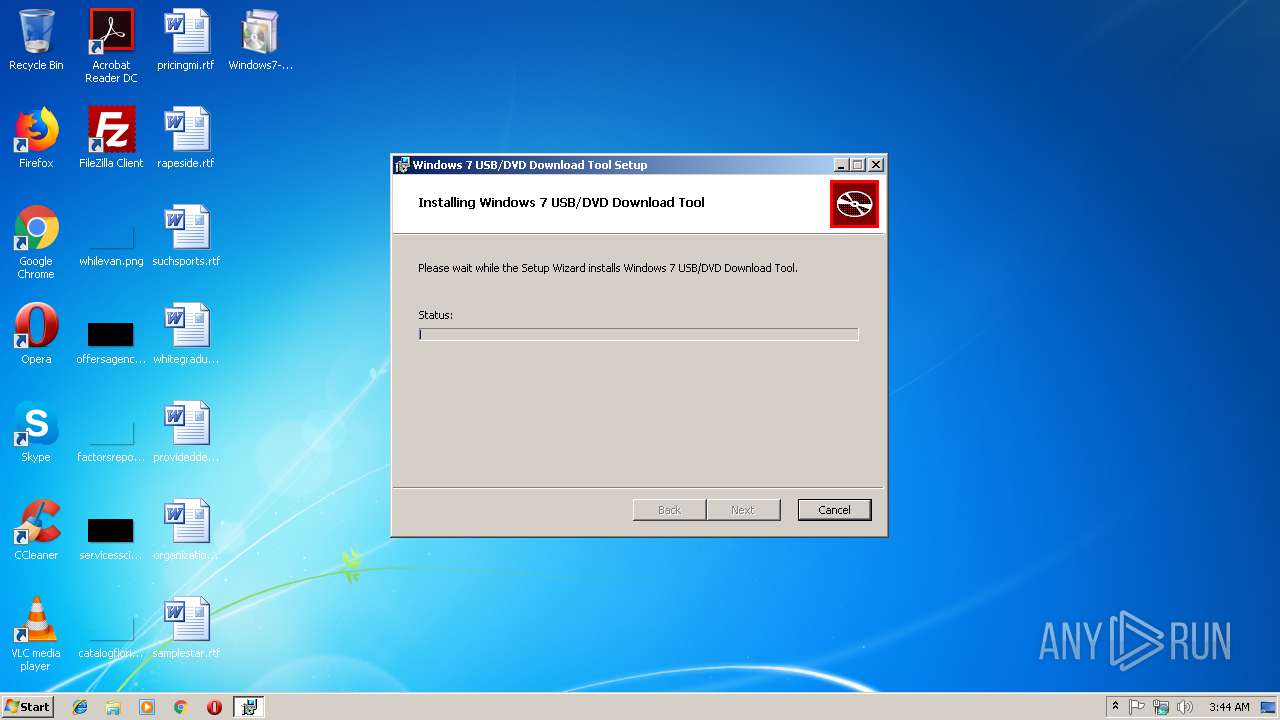
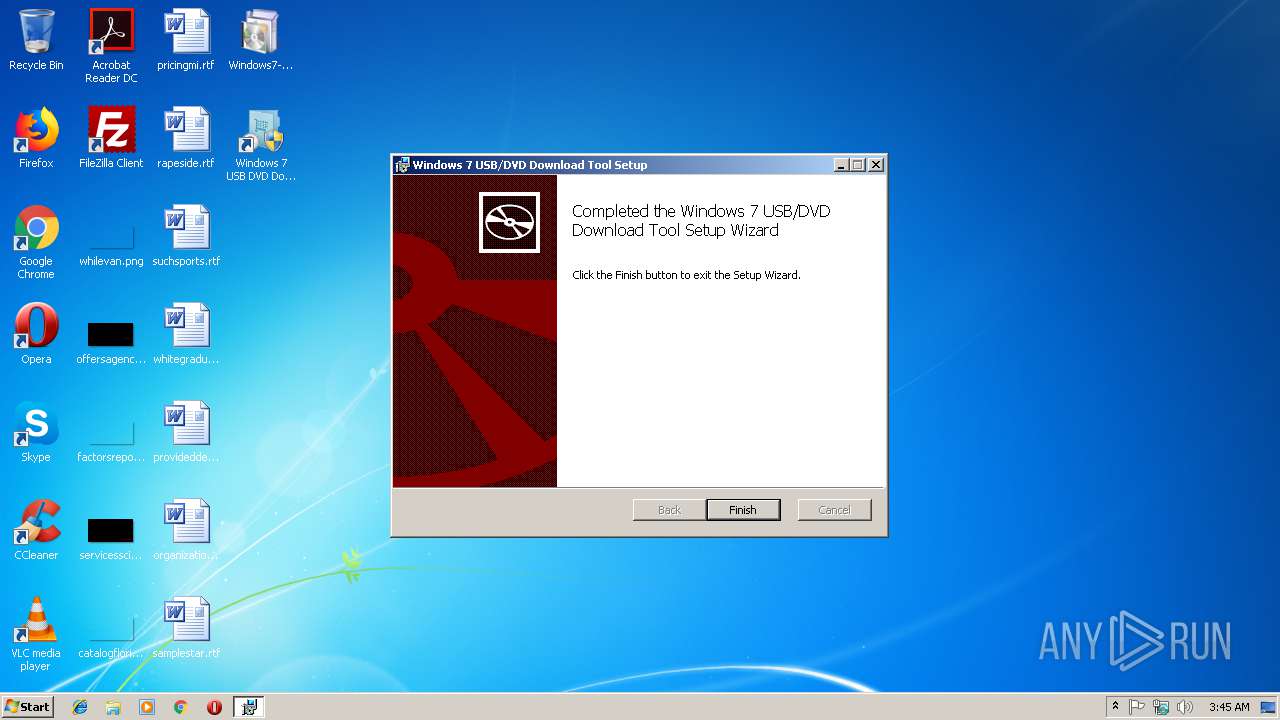
Starts Microsoft Installer
- cmd.exe (PID: 3024)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3924)
- Windows7-USB-DVD-Download-Tool-Installer-en-US.exe (PID: 3476)
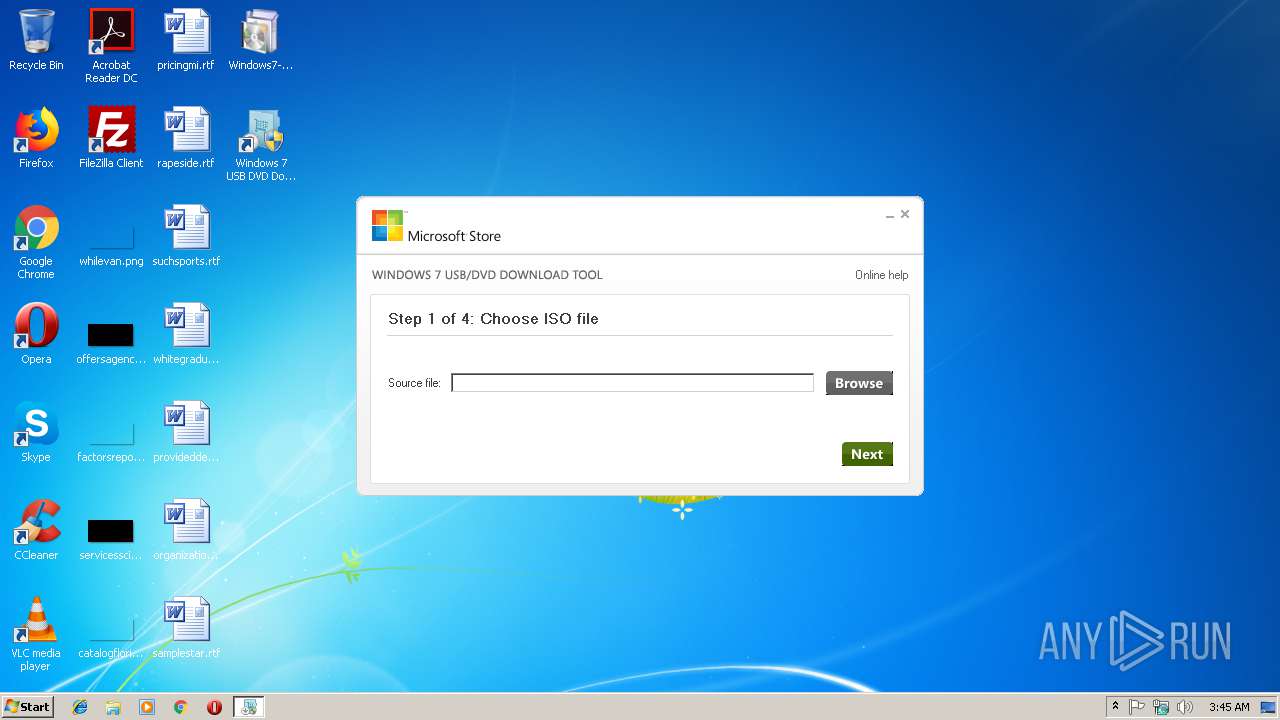
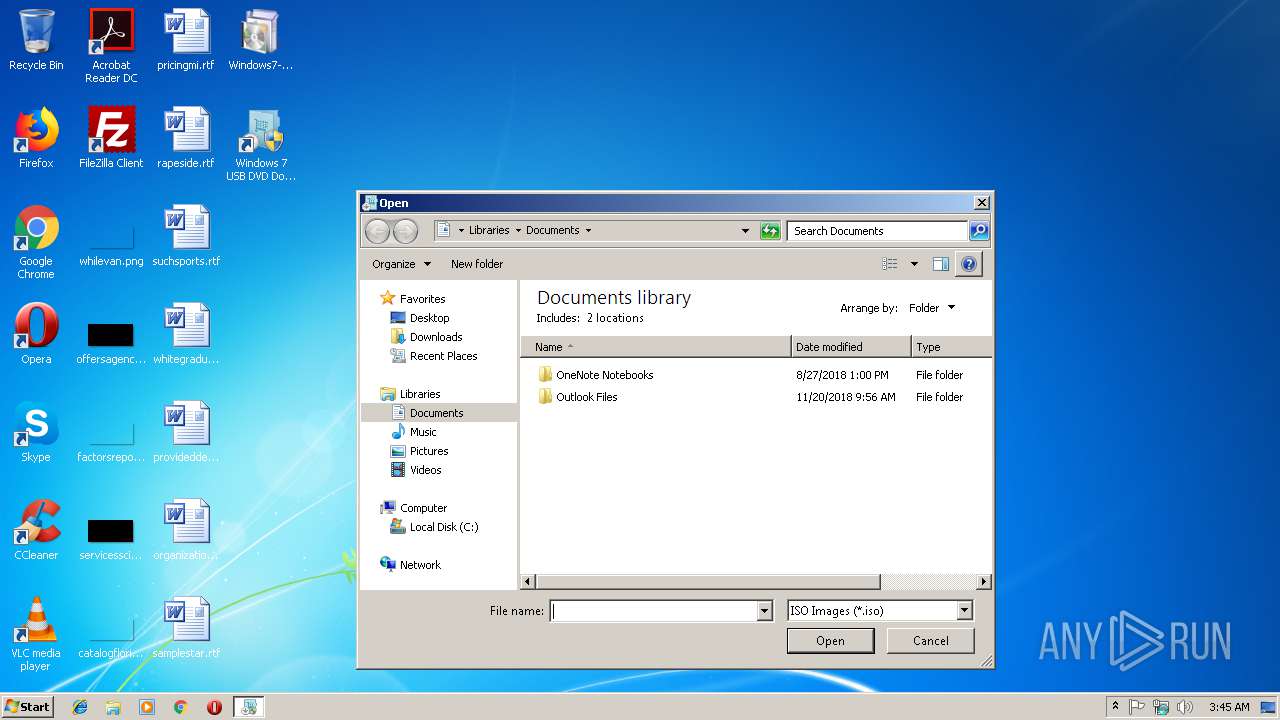
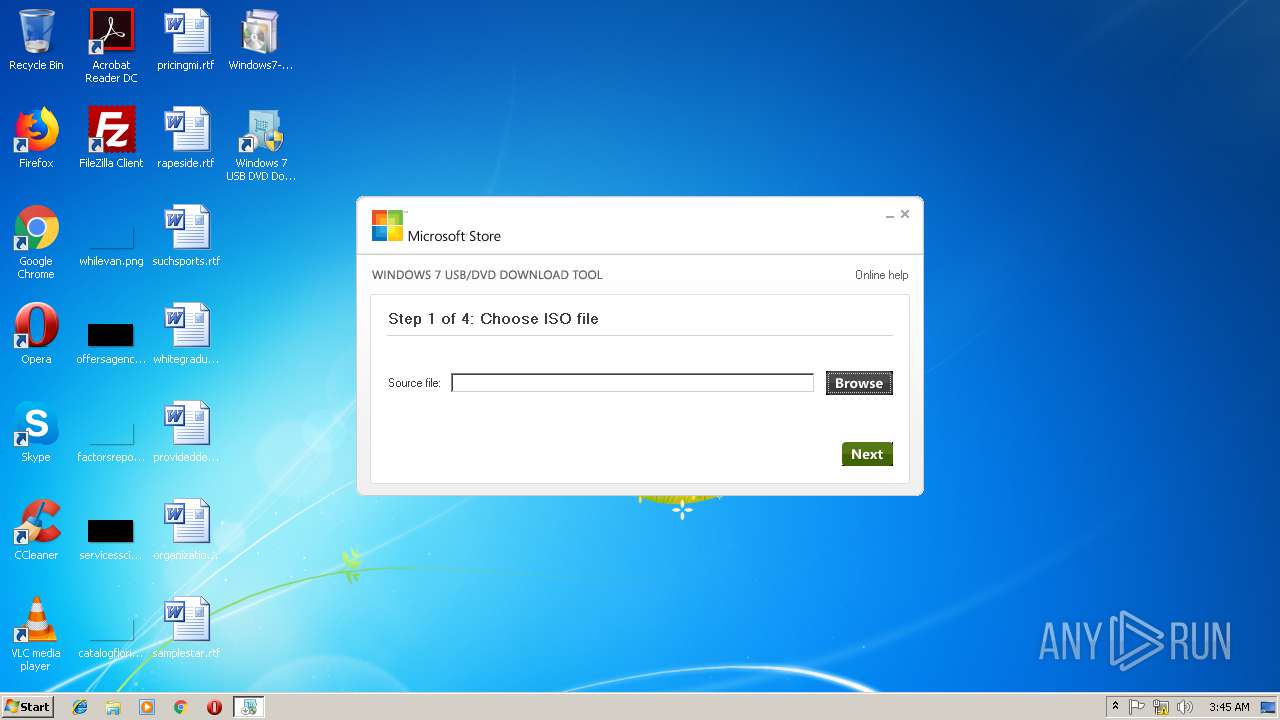
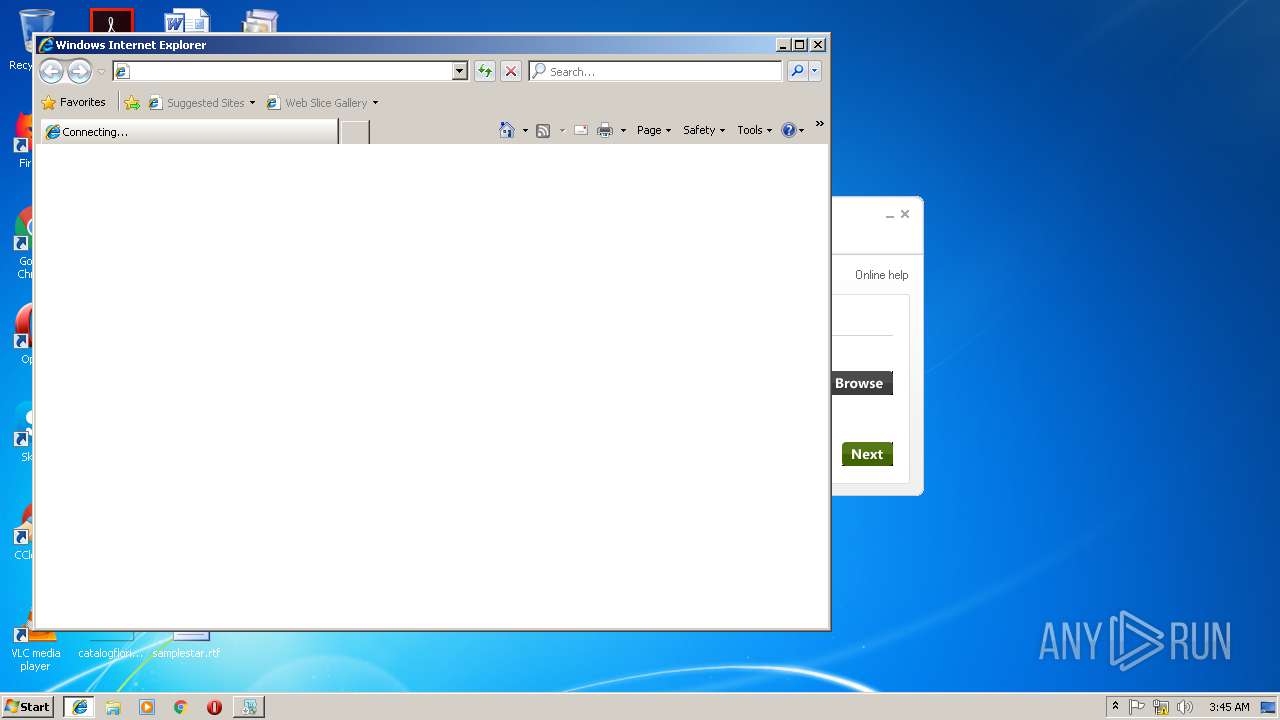
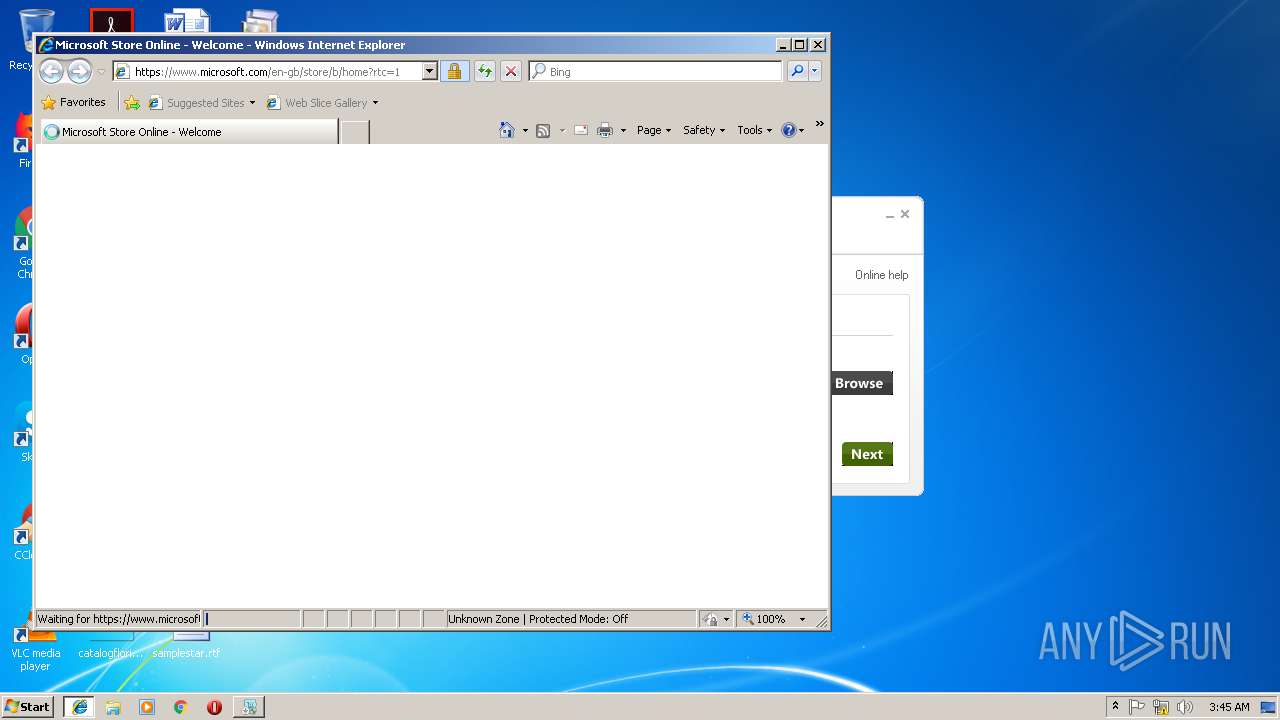
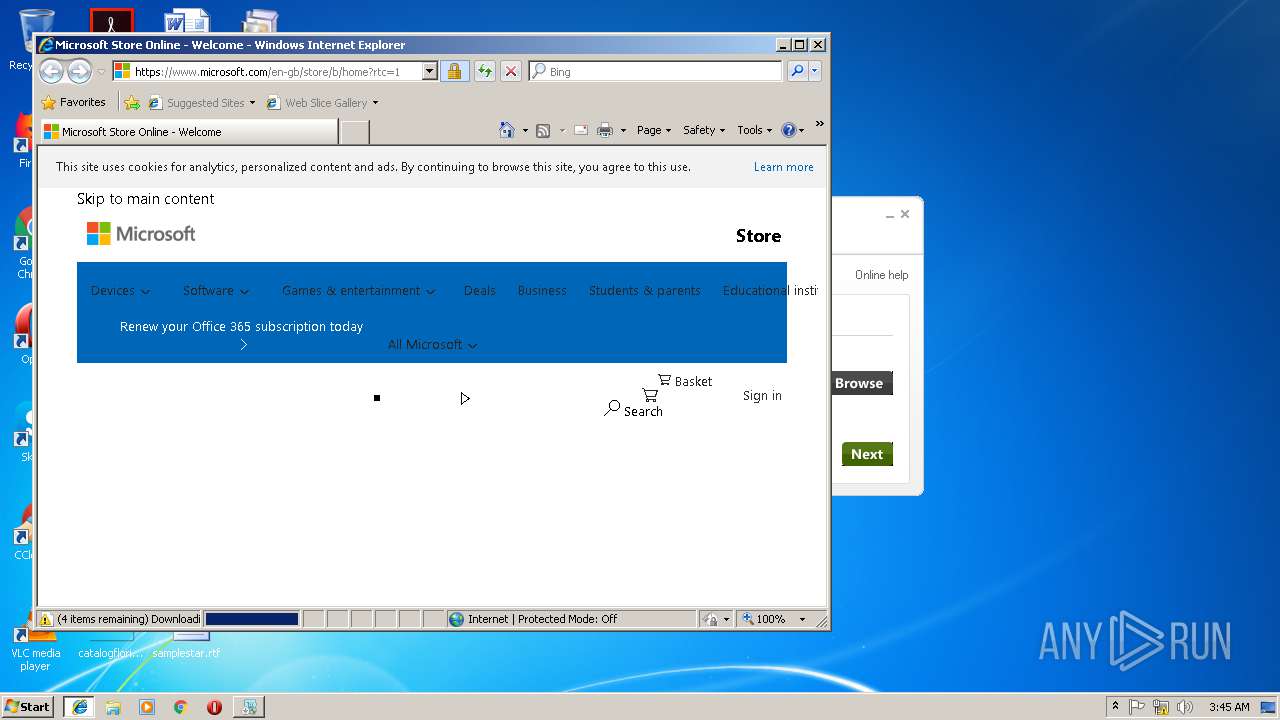
Starts Internet Explorer
- Windows7-USB-DVD-Download-Tool.exe (PID: 2132)
Starts CMD.EXE for commands execution
- Windows7-USB-DVD-Download-Tool-Installer-en-US.exe (PID: 3476)
Creates files in the user directory
- msiexec.exe (PID: 3924)
INFO
Searches for installed software
- msiexec.exe (PID: 3924)
Creates a software uninstall entry
- msiexec.exe (PID: 3924)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2784)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3816)
Reads internet explorer settings
- iexplore.exe (PID: 3816)
Changes settings of System certificates
- iexplore.exe (PID: 3816)
Creates files in the user directory
- iexplore.exe (PID: 3816)
Reads Internet Cache Settings
- iexplore.exe (PID: 3816)
Changes internet zones settings
- iexplore.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | MS generic-sfx Cabinet File Unpacker (32/64bit MSCFU) (45.4) |
|---|---|---|
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (39.3) |
| .exe | | | InstallShield setup (5.5) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (4) |
| .exe | | | Win64 Executable (generic) (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:07:14 01:42:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 44032 |
| InitializedDataSize: | 2670080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6af8 |
| OSVersion: | 6.1 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.7600.16385 |
| ProductVersionNumber: | 8.0.7600.16385 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 8.00.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Windows® Internet Explorer |
| ProductVersion: | 8.00.7600.16385 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jul-2009 23:42:43 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 8.00.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WEXTRACT.EXE .MUI |
| ProductName: | Windows® Internet Explorer |
| ProductVersion: | 8.00.7600.16385 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Jul-2009 23:42:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000AAE4 | 0x0000AC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54415 |
.data | 0x0000C000 | 0x0000225C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.59775 |
.rsrc | 0x0000F000 | 0x0028B000 | 0x0028AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99018 |
.reloc | 0x0029A000 | 0x00000D98 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.8066 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.84816 | 1260 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.15864 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.07737 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.50949 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56662 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.94251 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.99361 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.37828 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98515 | 55762 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.33023 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
msvcrt.dll |
Total processes
46
Monitored processes
11
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
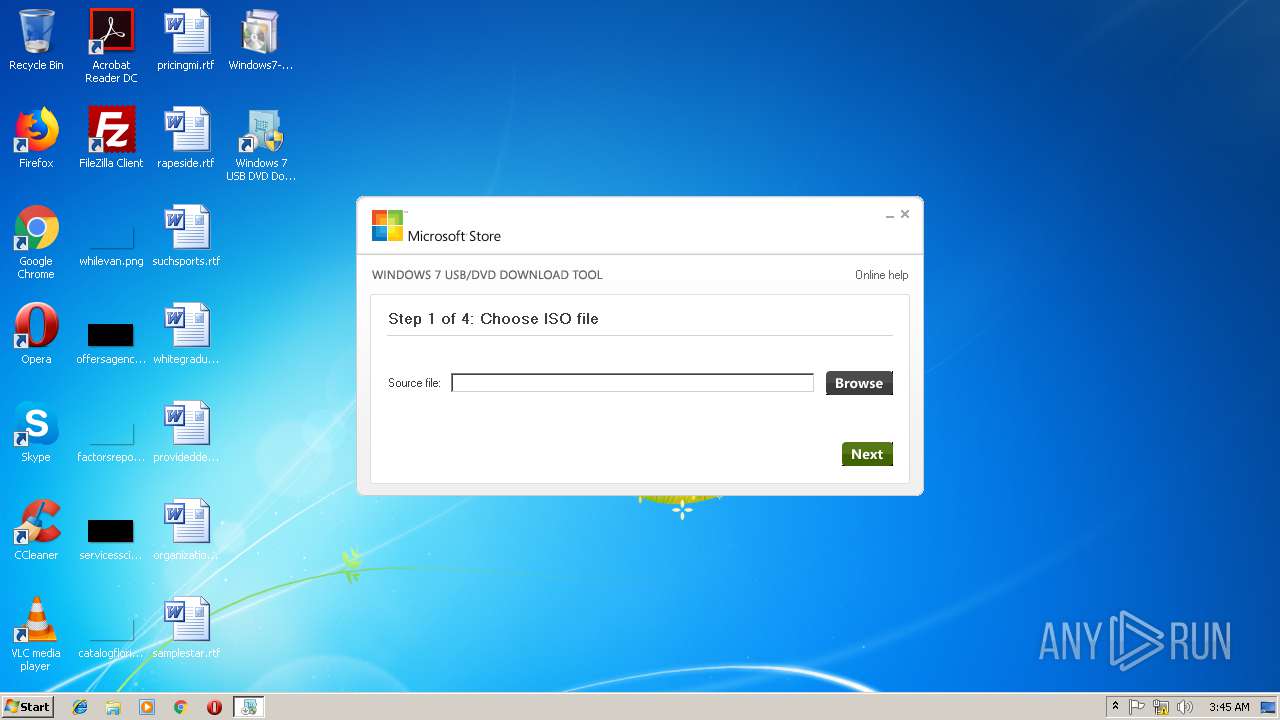
| 2132 | "C:\Users\admin\AppData\Local\Apps\Windows 7 USB DVD Download Tool\Windows7-USB-DVD-Download-Tool.exe" | C:\Users\admin\AppData\Local\Apps\Windows 7 USB DVD Download Tool\Windows7-USB-DVD-Download-Tool.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Store ISO Backup Tool Exit code: 0 Version: 1.0.30 Modules
| |||||||||||||||
| 2516 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Wudt.msi" | C:\Windows\System32\msiexec.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2784 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | cmd /c C:\Users\admin\AppData\Local\Temp\IXP000.TMP\setup.cmd | C:\Windows\system32\cmd.exe | — | Windows7-USB-DVD-Download-Tool-Installer-en-US.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3120 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Windows7-USB-DVD-Download-Tool.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3476 | "C:\Users\admin\Desktop\Windows7-USB-DVD-Download-Tool-Installer-en-US.exe" | C:\Users\admin\Desktop\Windows7-USB-DVD-Download-Tool-Installer-en-US.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3780 | "C:\Users\admin\AppData\Local\Apps\Windows 7 USB DVD Download Tool\Windows7-USB-DVD-Download-Tool.exe" | C:\Users\admin\AppData\Local\Apps\Windows 7 USB DVD Download Tool\Windows7-USB-DVD-Download-Tool.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Store ISO Backup Tool Exit code: 3221226540 Version: 1.0.30 Modules
| |||||||||||||||
| 3816 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3120 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3924 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 137
Read events
4 749
Write events
371
Delete events
17
Modification events
| (PID) Process: | (3024) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3024) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Zvpebfbsg.Jvaqbjf.JvaqbjfVafgnyyre |
Value: 000000000000000000000000E4010000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002E0000003D000000DE3C1500090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000E0000005DEC04007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000003702000008023CE23702350100C082BAD075B048D4750200000001000000A048D4750100000068E23702C5B8D075A848D47501000000C81008000000000090E237026BB9D07500000000350100C001000000B0E23702973CB8779C3CB877F58CF77501000000350100C00000000088E23702FFFFFFFFF8E23702EDE0B47745727800FEFFFFFFC0E237020D6BD075A0E737028CE8370200000000F8E23702973CB8779C3CB877BD8CF775000000008CE83702A0E73702D0E237020100000070E73702EDE0B47745727800FEFFFFFF08E337020D6BD0757E0000008CE8370280E73702F36BD075E186D0752794C6128CE8370210000000570104003E0040008CE83702A0E73702000000000000000000000000000008025CE537020000080254E33702350100C000000000D8E637023200000018000000000000000000000088E3370211000000B8450B00B0450B0032000000D8E63702F0E300009B1EC112A0E3370282919576F0E33702A4E3370227959576000000006C155002CCE33702CD9495766C15500278E43702E0105002E194957600000000E010500278E43702D4E33702090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (3924) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000500BAF274EB8D401540F0000100A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3924) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000500BAF274EB8D401540F0000100A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3924) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (3924) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000007CB71C284EB8D401540F0000100A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3924) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007CB71C284EB8D401540F0000B0080000E803000001000000000000000000000049C6AFE590E7A348A41659DA7090B7E10000000000000000 | |||
| (PID) Process: | (2784) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000098052B284EB8D401E00A0000480D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
6
Suspicious files
9
Text files
112
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3924 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF712A76BDB2C46A2A.TMP | — | |
MD5:— | SHA256:— | |||
| 2784 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 4072 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:— | SHA256:— | |||
| 3924 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{e5afc649-e790-48a3-a416-59da7090b7e1}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 3924 | msiexec.exe | C:\Config.Msi\1a0301.rbs | — | |
MD5:— | SHA256:— | |||
| 3924 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF75A7EDB39818A427.TMP | — | |
MD5:— | SHA256:— | |||
| 3120 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4072 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
25
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3816 | iexplore.exe | GET | 301 | 40.112.72.205:80 | http://store.microsoft.com/Help/ISO-Tool | IE | — | — | whitelisted |
3816 | iexplore.exe | GET | 302 | 23.51.118.23:80 | http://go.microsoft.com/fwlink/?LinkId=163455&clcid=0x409 | NL | — | — | whitelisted |
3120 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3816 | iexplore.exe | 23.51.118.23:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | whitelisted |
3816 | iexplore.exe | 2.18.233.62:443 | c.s-microsoft.com | Akamai International B.V. | — | whitelisted |
3816 | iexplore.exe | 23.45.104.124:443 | mem.gfx.ms | Akamai International B.V. | NL | whitelisted |
3816 | iexplore.exe | 2.18.232.244:443 | uhf.microsoft.com | Akamai International B.V. | — | whitelisted |
3816 | iexplore.exe | 40.77.226.250:443 | web.vortex.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
3816 | iexplore.exe | 2.16.186.40:443 | img-prod-cms-rt-microsoft-com.akamaized.net | Akamai International B.V. | — | whitelisted |
3816 | iexplore.exe | 2.16.186.27:443 | statics-storeexp-neu-ms-com.akamaized.net | Akamai International B.V. | — | whitelisted |
3120 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3816 | iexplore.exe | 40.112.72.205:80 | store.microsoft.com | Microsoft Corporation | IE | malicious |
3816 | iexplore.exe | 23.45.104.156:443 | www.microsoftstore.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
store.microsoft.com |
| whitelisted |
www.microsoftstore.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
statics-storeexp-neu-ms-com.akamaized.net |
| whitelisted |
c.s-microsoft.com |
| whitelisted |
mem.gfx.ms |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |
web.vortex.data.microsoft.com |
| whitelisted |