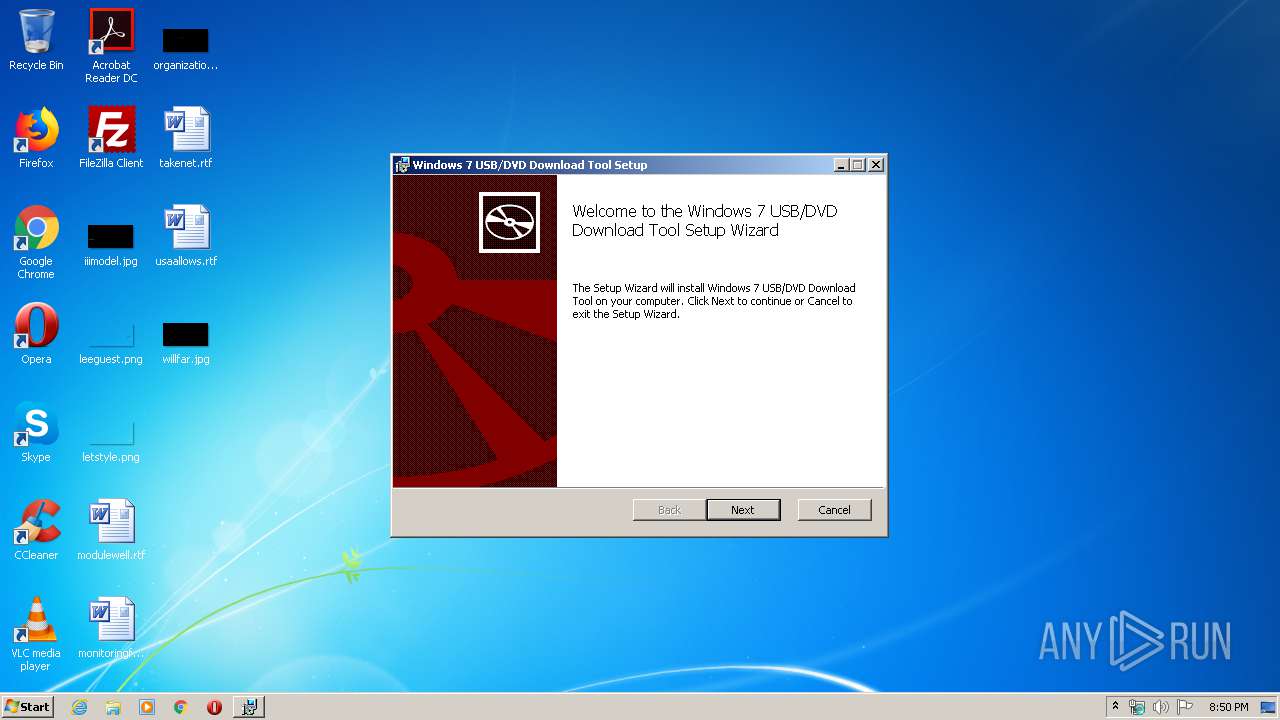
| File name: | Windows7-USB-DVD-Download-Tool-Installer-en-US.exe |
| Full analysis: | https://app.any.run/tasks/01abc334-8cf4-4b42-bbf8-7fe70395feaa |
| Verdict: | No threats detected |
| Analysis date: | April 12, 2020, 19:50:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | AF911BE206423BF440EA9D4DF075A632 |
| SHA1: | ED1108A525066D1F850023CB5BFA05FC4ED21983 |
| SHA256: | 6B7CEA4838D892A0A0F625BAB2DF3D378A035C365209DB3C573253F037882229 |
| SSDEEP: | 49152:JDHlPyp6jE1/8Sfov72CmSj/pL2gyIPgaStBPEBiwChHHVPlcnSebHc8:DaUjw/8Xv69fgyIPgaXiPbPlzer9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Microsoft Installer
- cmd.exe (PID: 3028)
Starts CMD.EXE for commands execution
- Windows7-USB-DVD-Download-Tool-Installer-en-US.exe (PID: 2228)
Executable content was dropped or overwritten
- Windows7-USB-DVD-Download-Tool-Installer-en-US.exe (PID: 2228)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | MS generic-sfx Cabinet File Unpacker (32/64bit MSCFU) (45.4) |
|---|---|---|
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (39.3) |
| .exe | | | InstallShield setup (5.5) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (4) |
| .exe | | | Win64 Executable (generic) (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:07:14 01:42:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 44032 |
| InitializedDataSize: | 2670080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6af8 |
| OSVersion: | 6.1 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.7600.16385 |
| ProductVersionNumber: | 8.0.7600.16385 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 8.00.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Windows® Internet Explorer |
| ProductVersion: | 8.00.7600.16385 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jul-2009 23:42:43 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 8.00.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WEXTRACT.EXE .MUI |
| ProductName: | Windows® Internet Explorer |
| ProductVersion: | 8.00.7600.16385 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Jul-2009 23:42:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000AAE4 | 0x0000AC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54415 |
.data | 0x0000C000 | 0x0000225C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.59775 |
.rsrc | 0x0000F000 | 0x0028B000 | 0x0028AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99018 |
.reloc | 0x0029A000 | 0x00000D98 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.8066 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.84816 | 1260 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.15864 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.07737 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.50949 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56662 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.94251 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.99361 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.37828 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98515 | 55762 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.33023 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
msvcrt.dll |
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2228 | "C:\Users\admin\AppData\Local\Temp\Windows7-USB-DVD-Download-Tool-Installer-en-US.exe" | C:\Users\admin\AppData\Local\Temp\Windows7-USB-DVD-Download-Tool-Installer-en-US.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2640 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3028 | cmd /c C:\Users\admin\AppData\Local\Temp\IXP000.TMP\setup.cmd | C:\Windows\system32\cmd.exe | — | Windows7-USB-DVD-Download-Tool-Installer-en-US.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3980 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Wudt.msi" | C:\Windows\System32\msiexec.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
442
Read events
438
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3028) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3028) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2228 | Windows7-USB-DVD-Download-Tool-Installer-en-US.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\setup.cmd | text | |
MD5:2425E77694E8BAF8ACB69984689549E9 | SHA256:16F32FEBCB38DADD19AD439468CB2EC4A3052142F0155B7A45268C6112BBF07A | |||
| 2228 | Windows7-USB-DVD-Download-Tool-Installer-en-US.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Wudt.msi | executable | |
MD5:2AAEE498598F20497111A4199B20FBE3 | SHA256:D988C4E674B0B901B8CB5A71589C60421D700CC66E546317E7DEC1D582338A65 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report