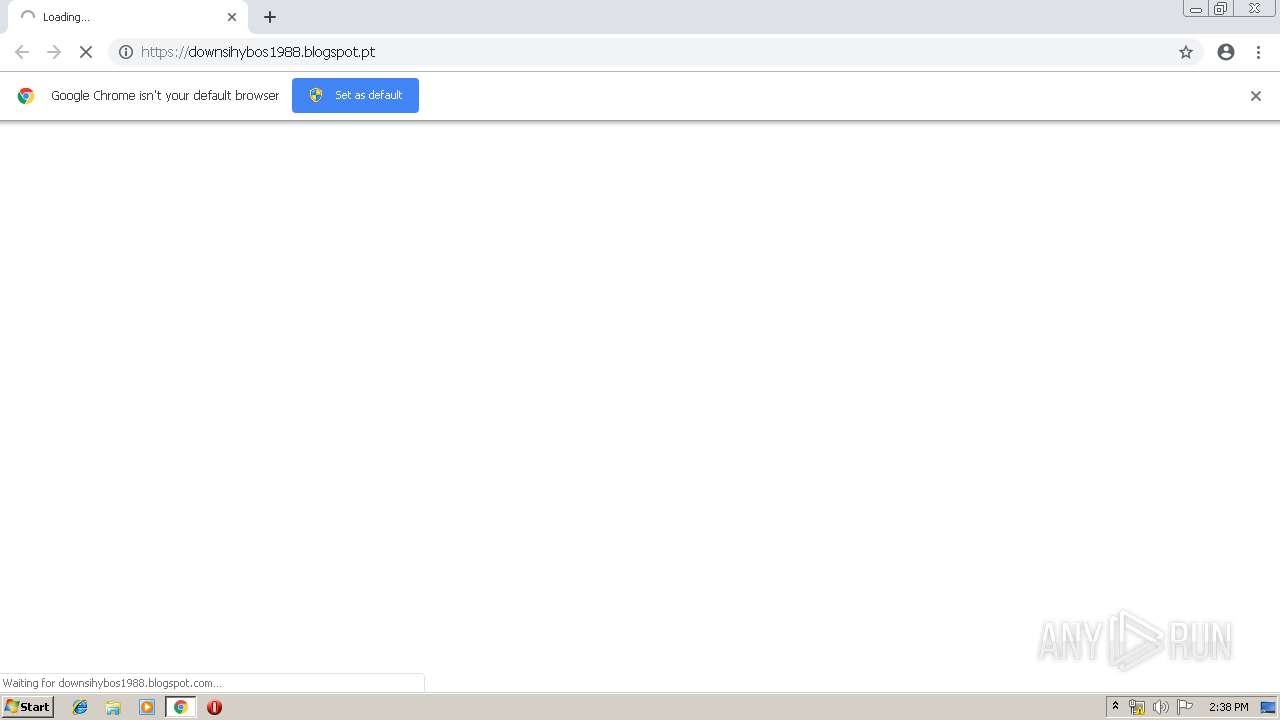
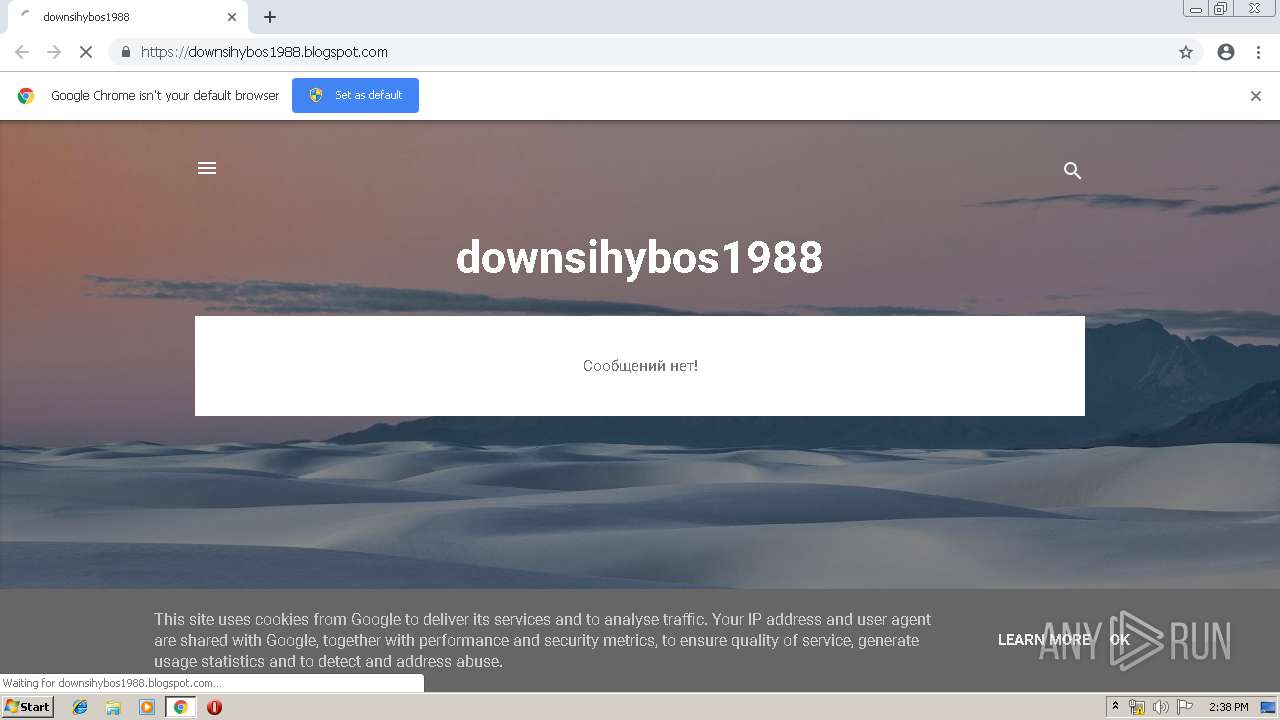
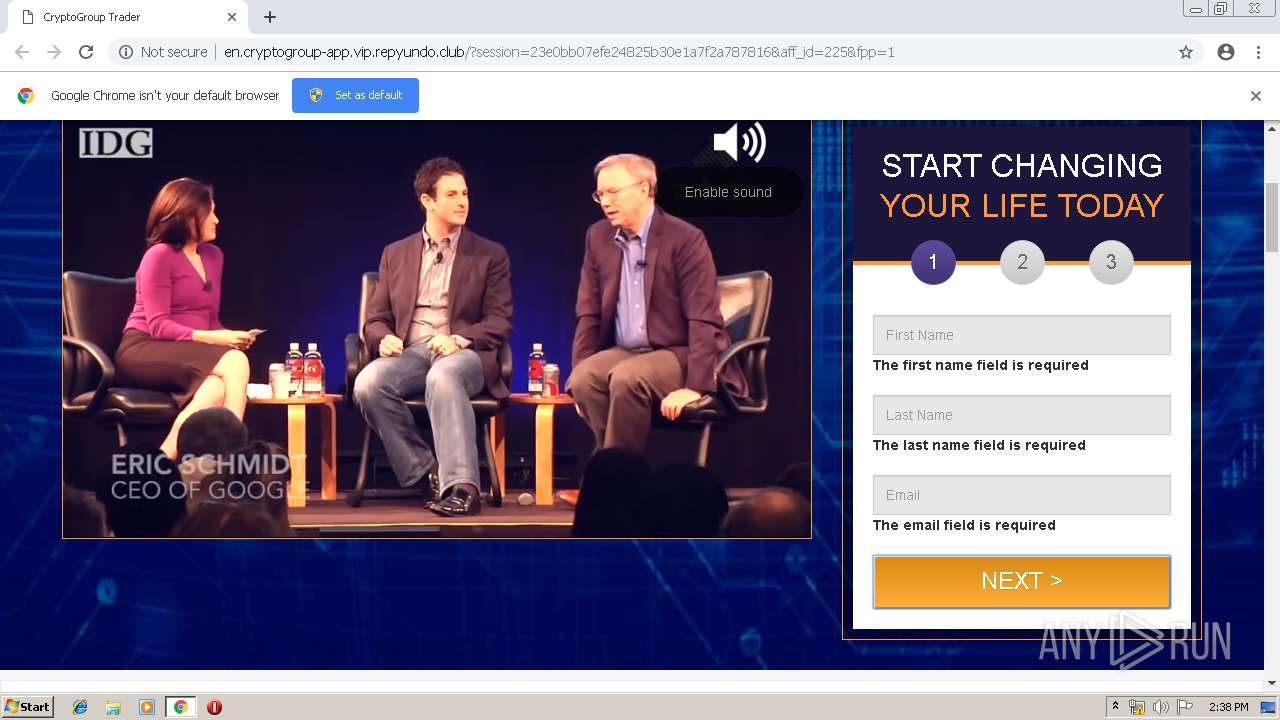
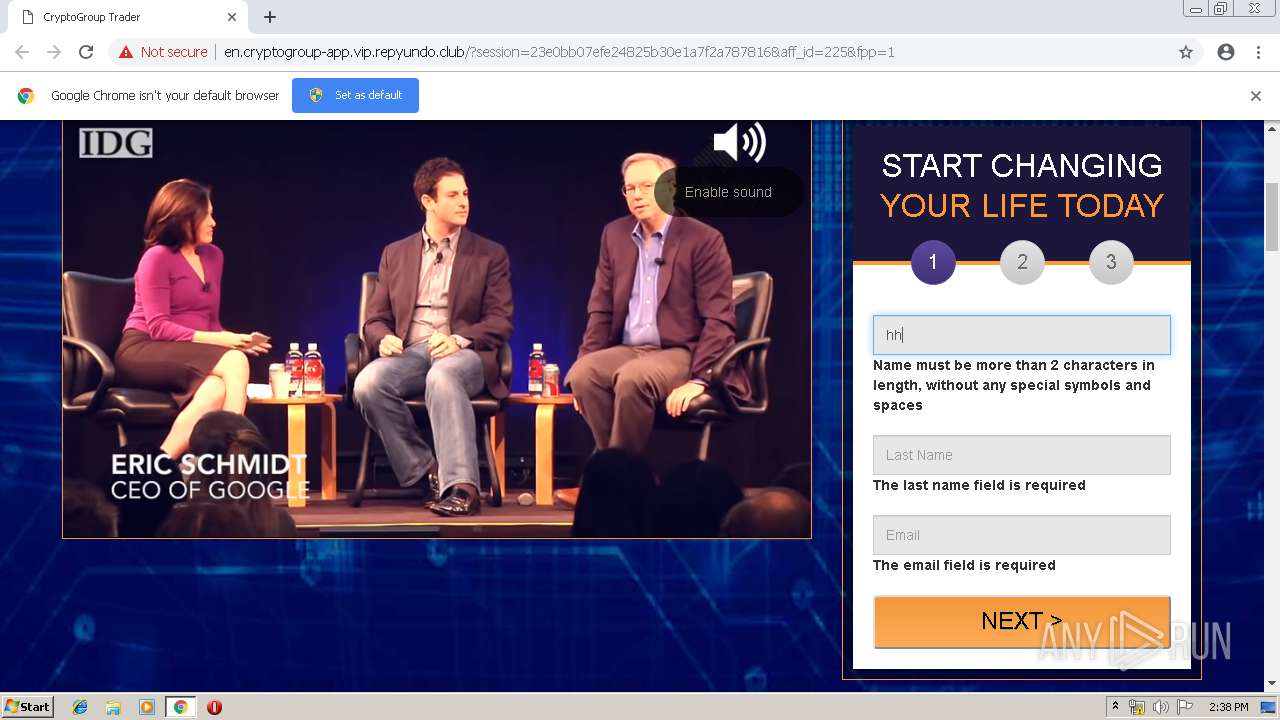
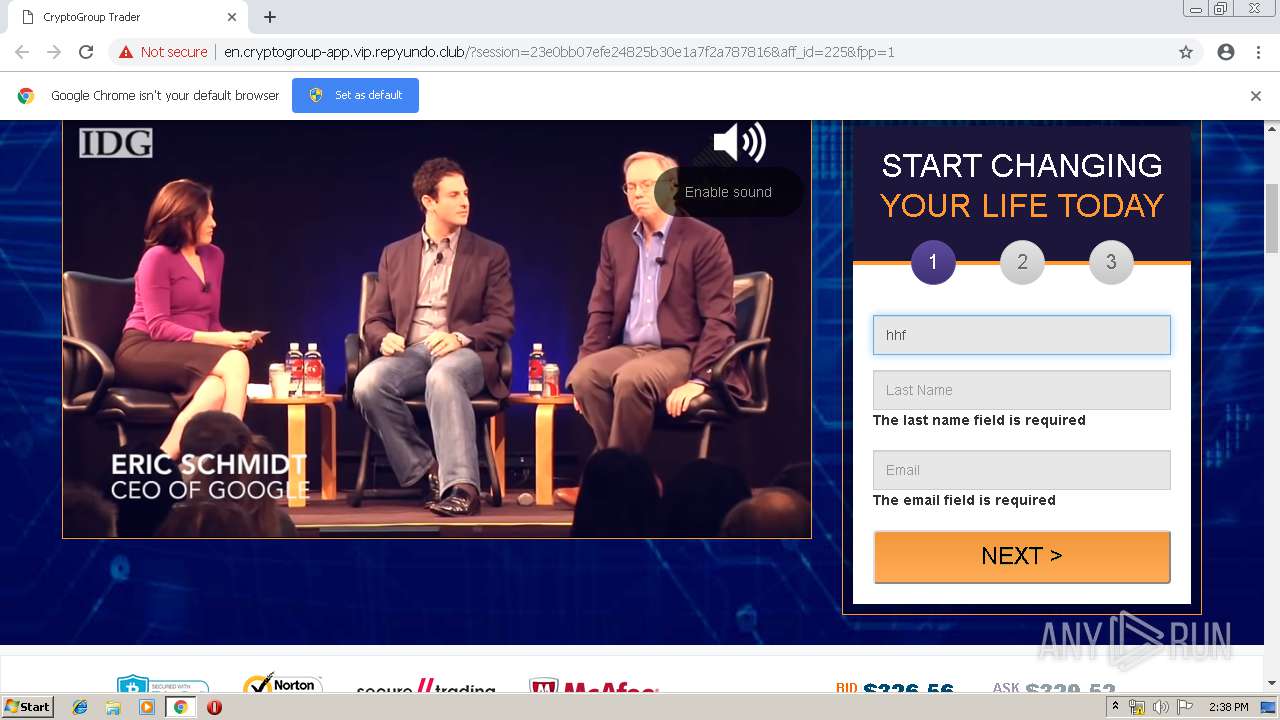
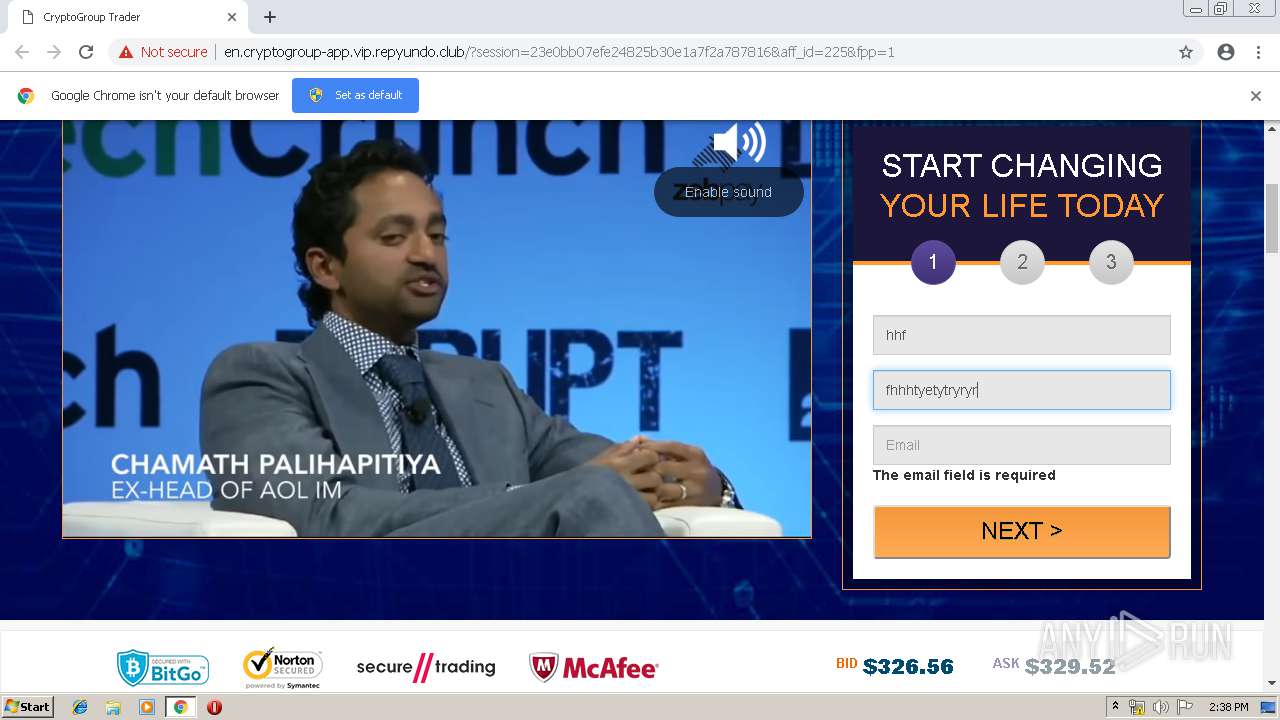
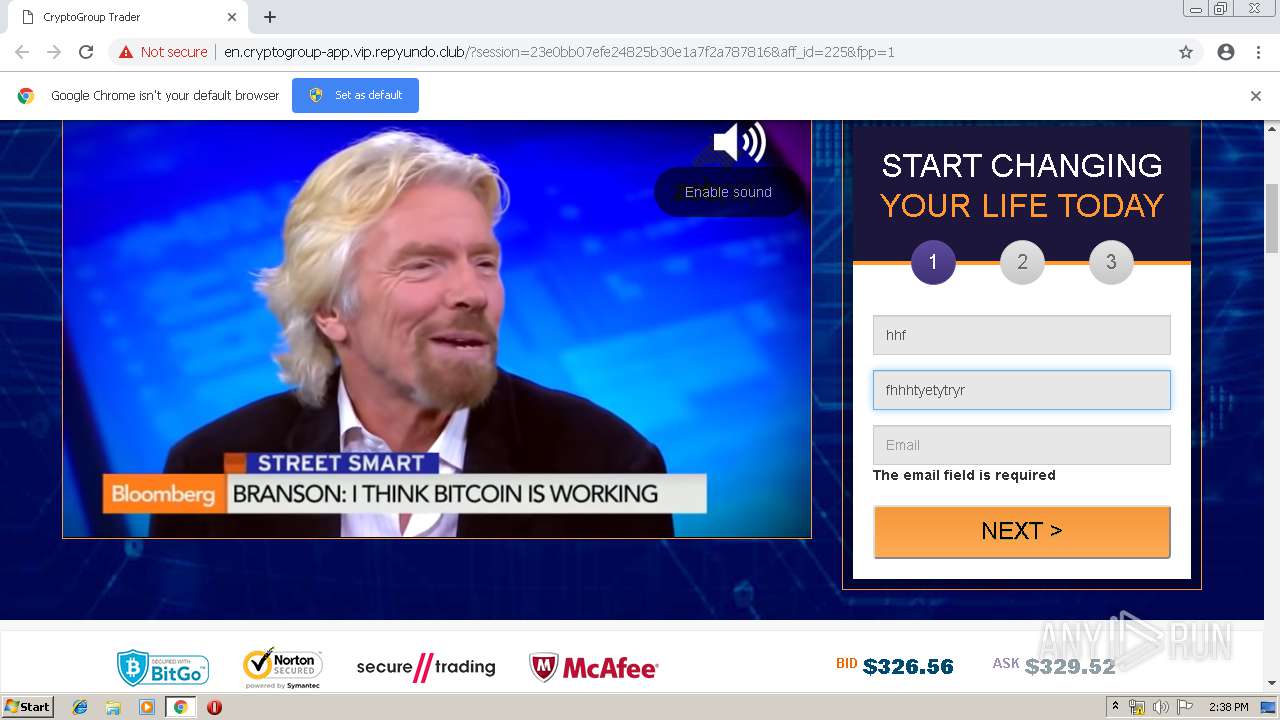
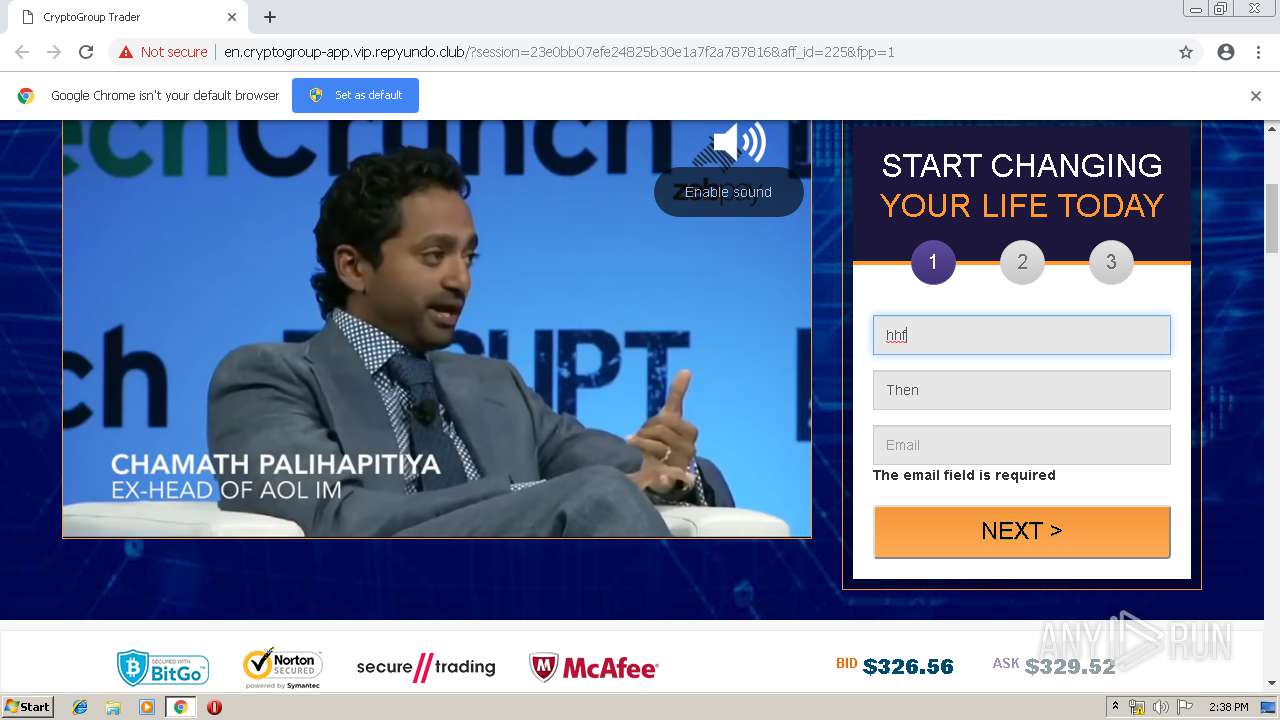
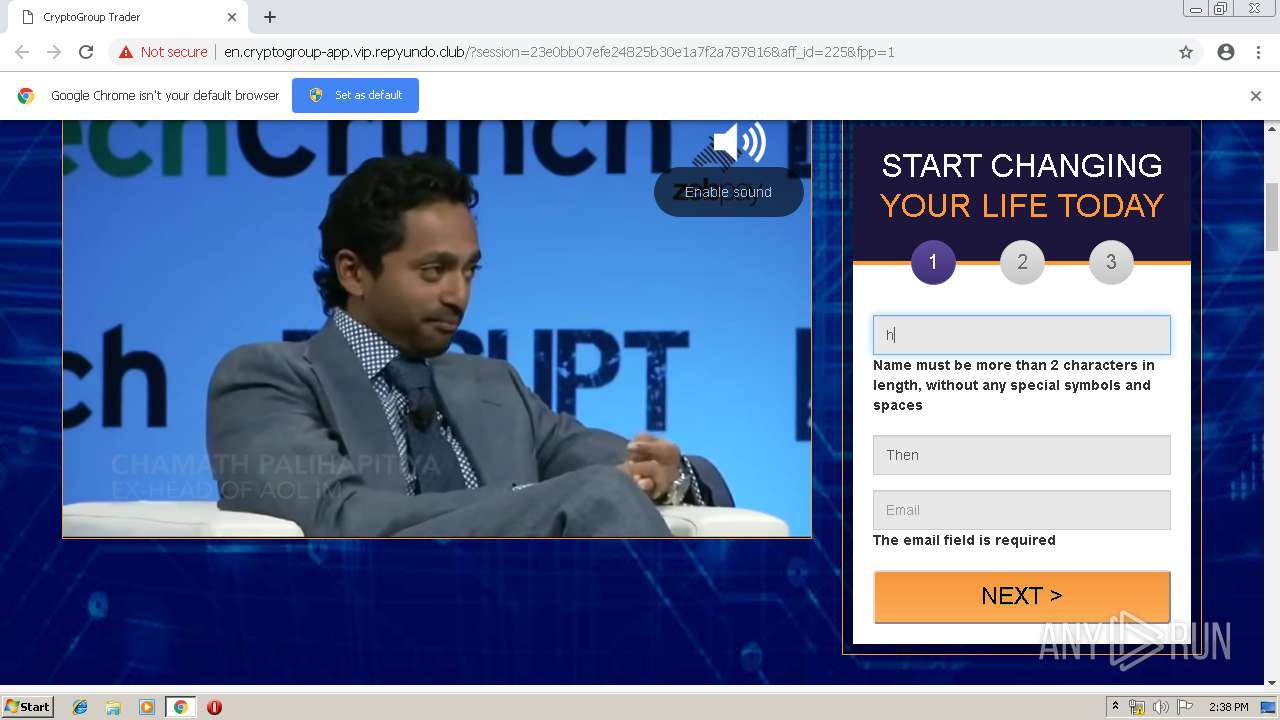
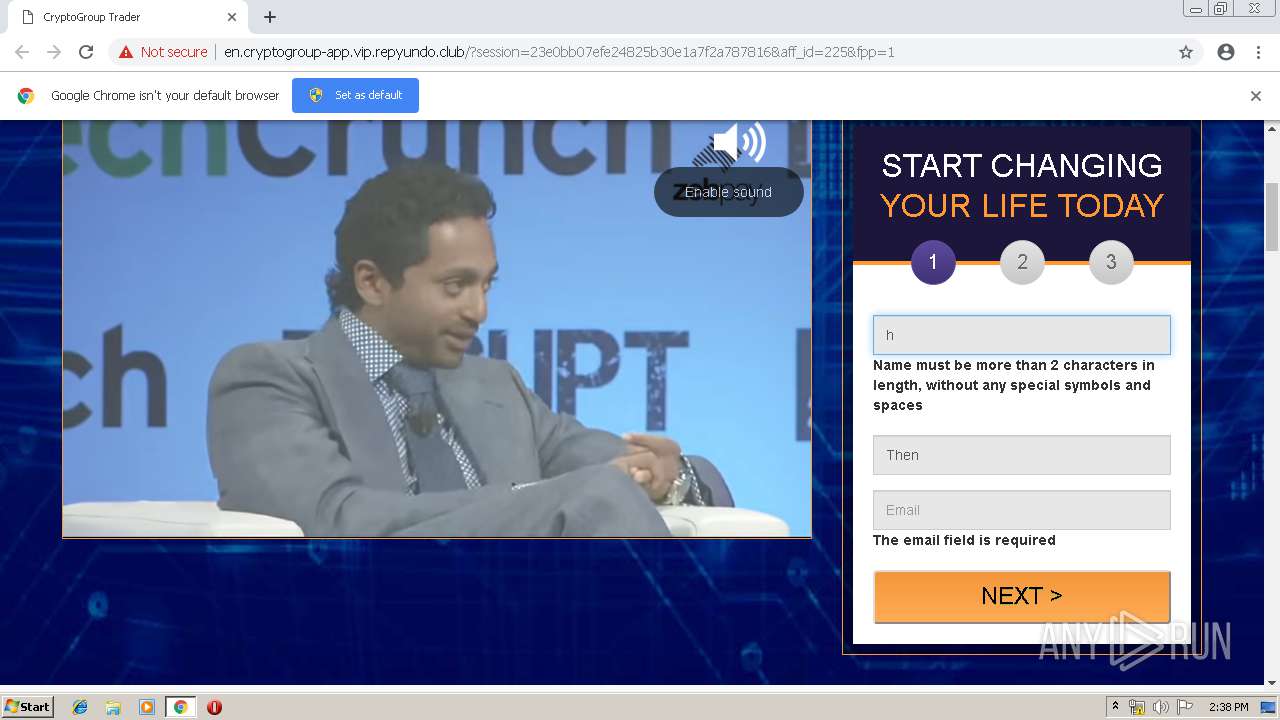
| URL: | https://downsihybos1988.blogspot.pt/ |
| Full analysis: | https://app.any.run/tasks/1cddd903-1cae-4ff7-ba1c-573a30579a9e |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 13:37:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DC95874B58E2D8A907D38BFEECF9FE77 |
| SHA1: | 61B5C76285733CE08E06F1065B2CFD00AB964FF2 |
| SHA256: | 6B5AFA833F66998C73FAE117ADA870EF80E437AB02038710CA1314F2235714D4 |
| SSDEEP: | 3:N8SbFGa3O:2SbRO |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3332)
INFO
Application launched itself
- chrome.exe (PID: 3332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15920027177994419801 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6172381328791772715 --mojo-platform-channel-handle=4740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1263606747134842341 --mojo-platform-channel-handle=4280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --service-pipe-token=10543181930582881302 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10543181930582881302 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2187703686595470880 --mojo-platform-channel-handle=4728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=277778596323212525 --mojo-platform-channel-handle=4508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3272 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=18145480575523629233 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18145480575523629233 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --service-pipe-token=18162348817561641235 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18162348817561641235 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f5e0f18,0x6f5e0f28,0x6f5e0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
577
Read events
487
Write events
85
Delete events
5
Modification events
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3332-13203178678468125 |
Value: 259 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
56
Text files
170
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5b4bb8eb-1635-4071-9ba4-10f83aa5375b.tmp | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
44
DNS requests
31
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
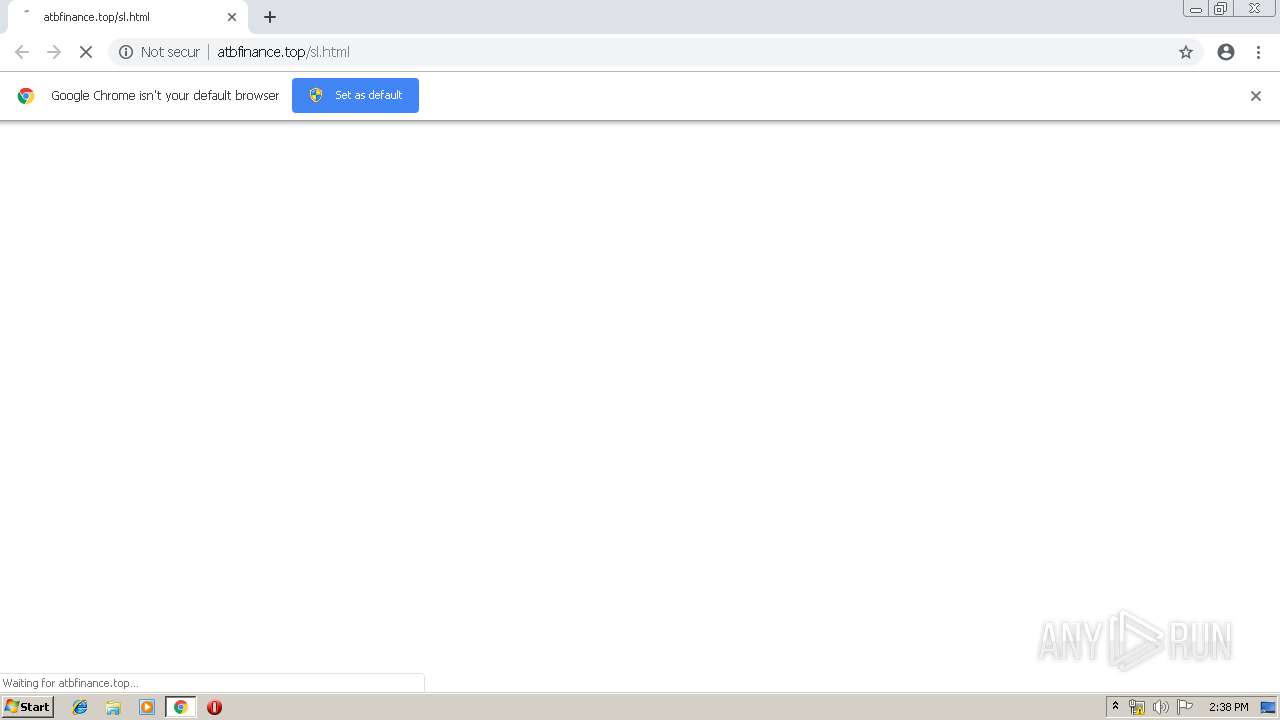
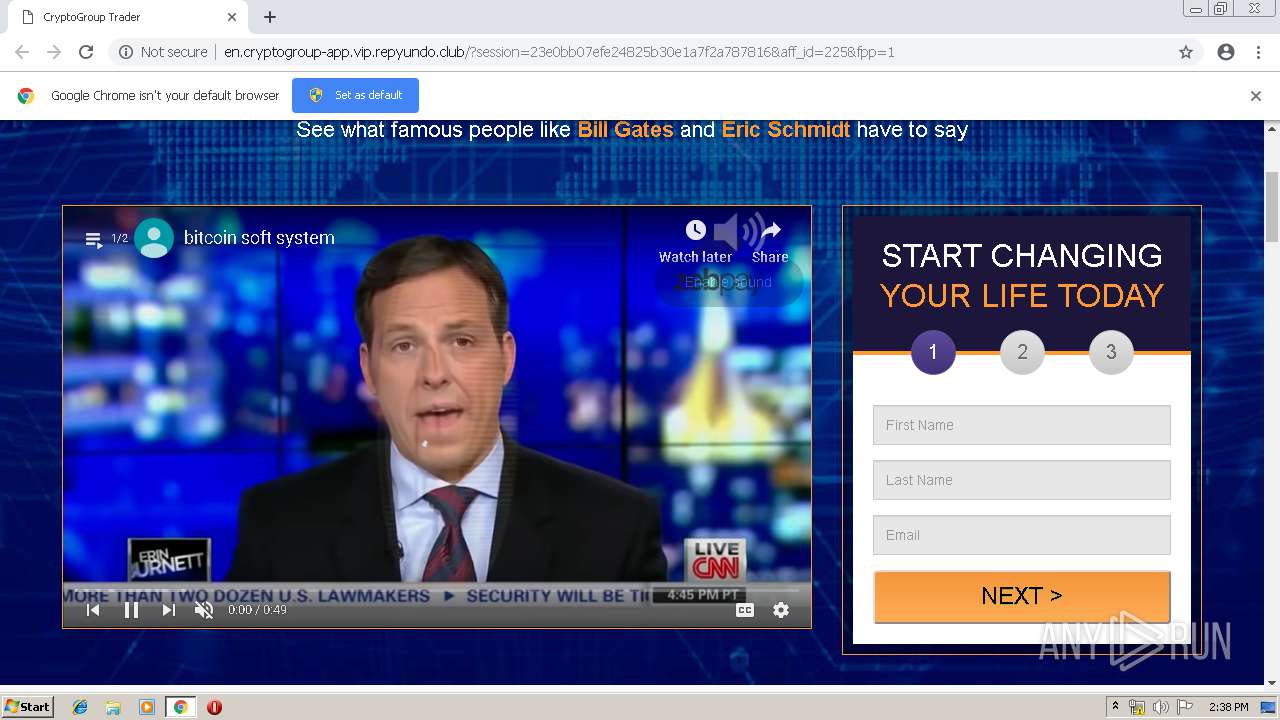
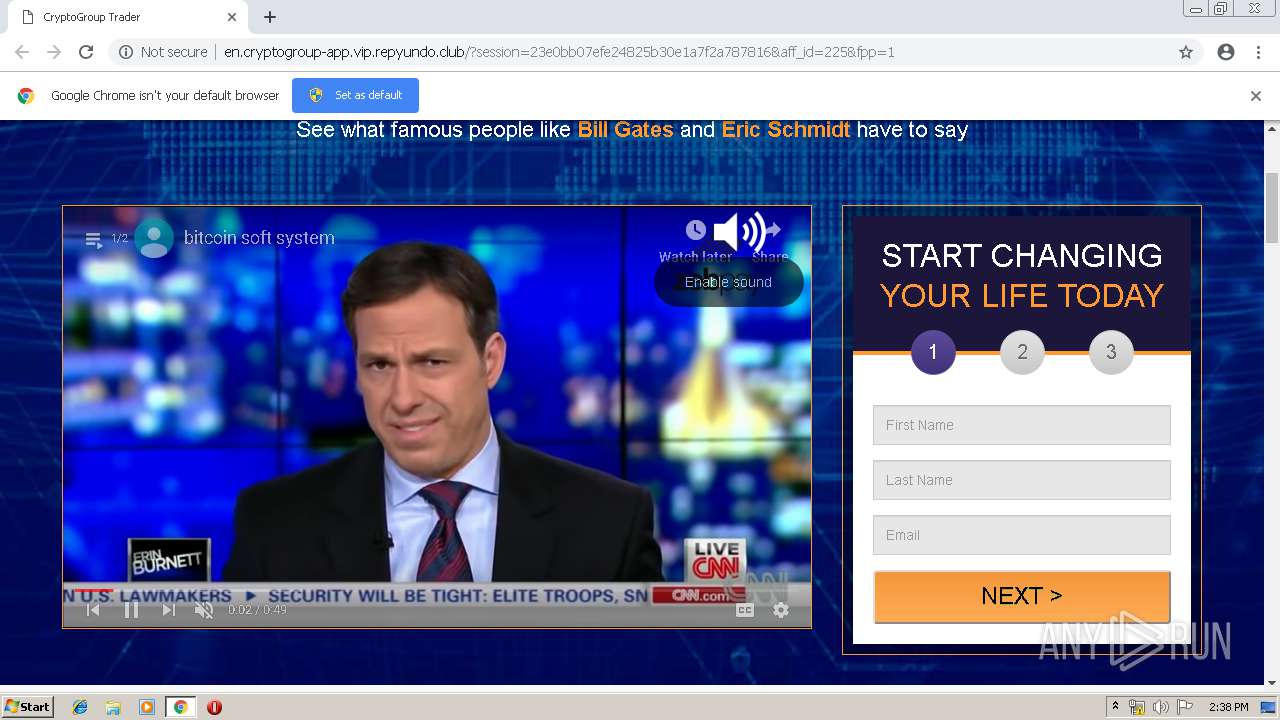
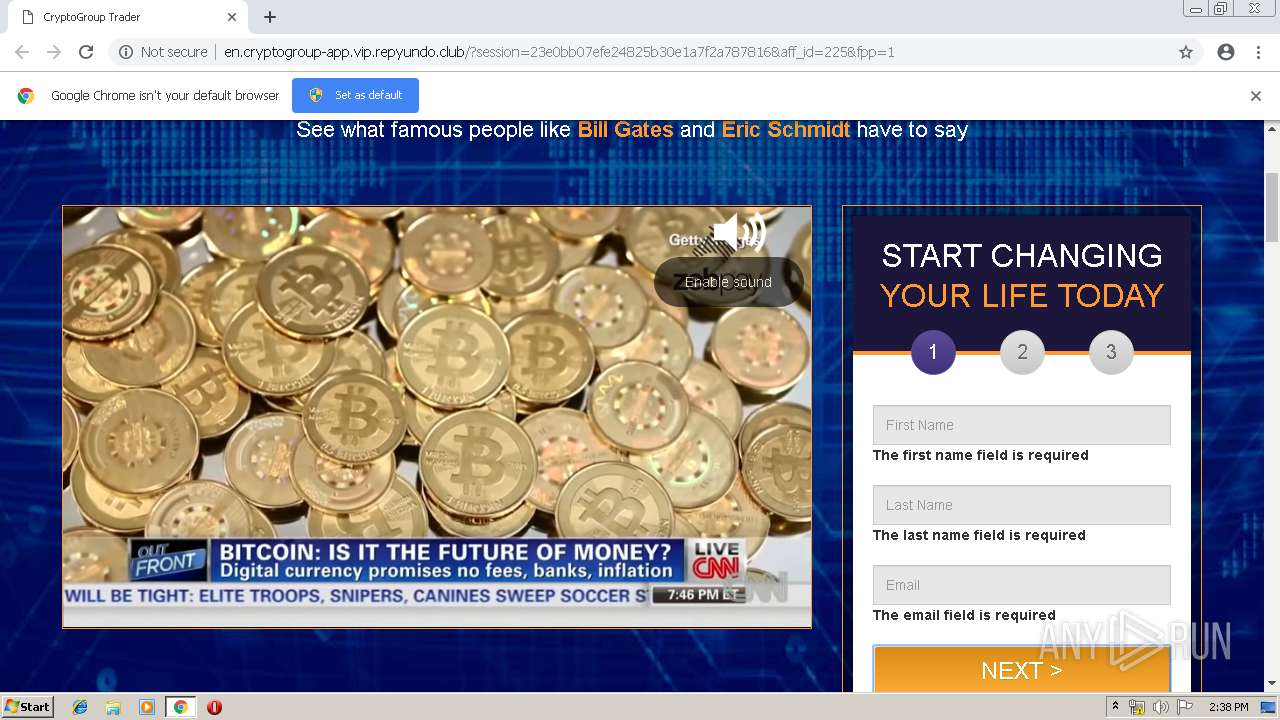
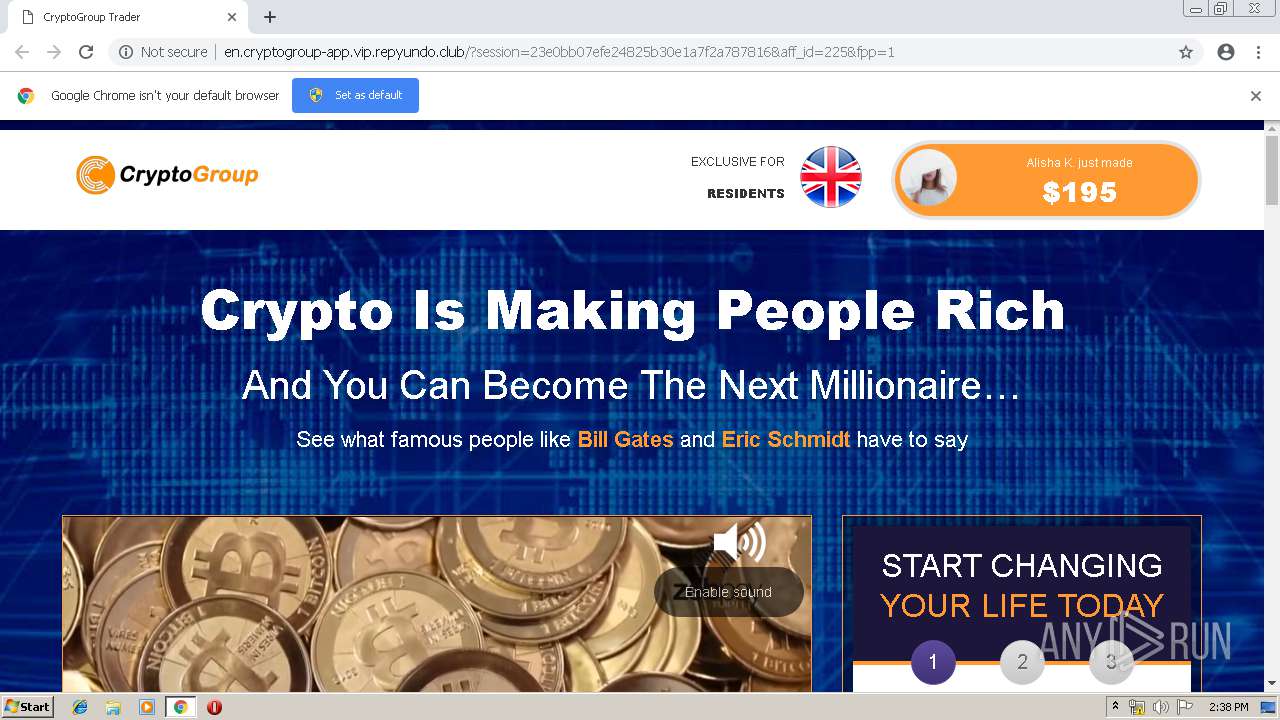
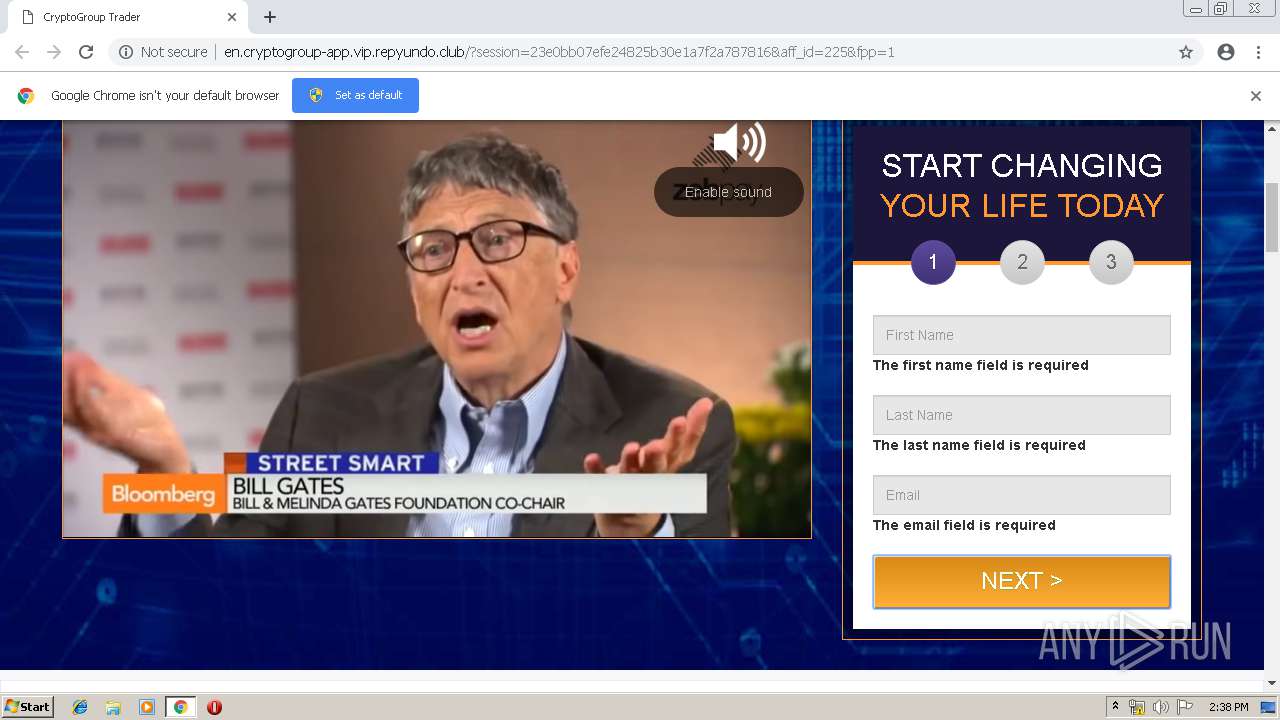
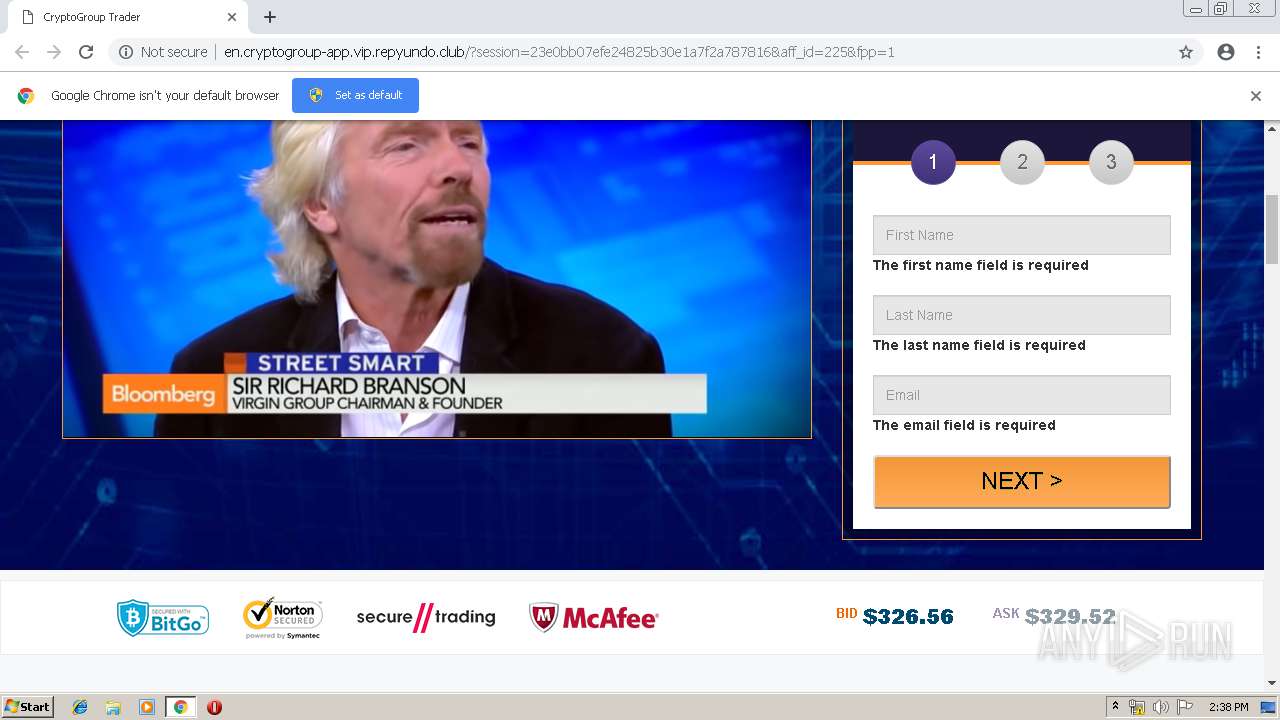
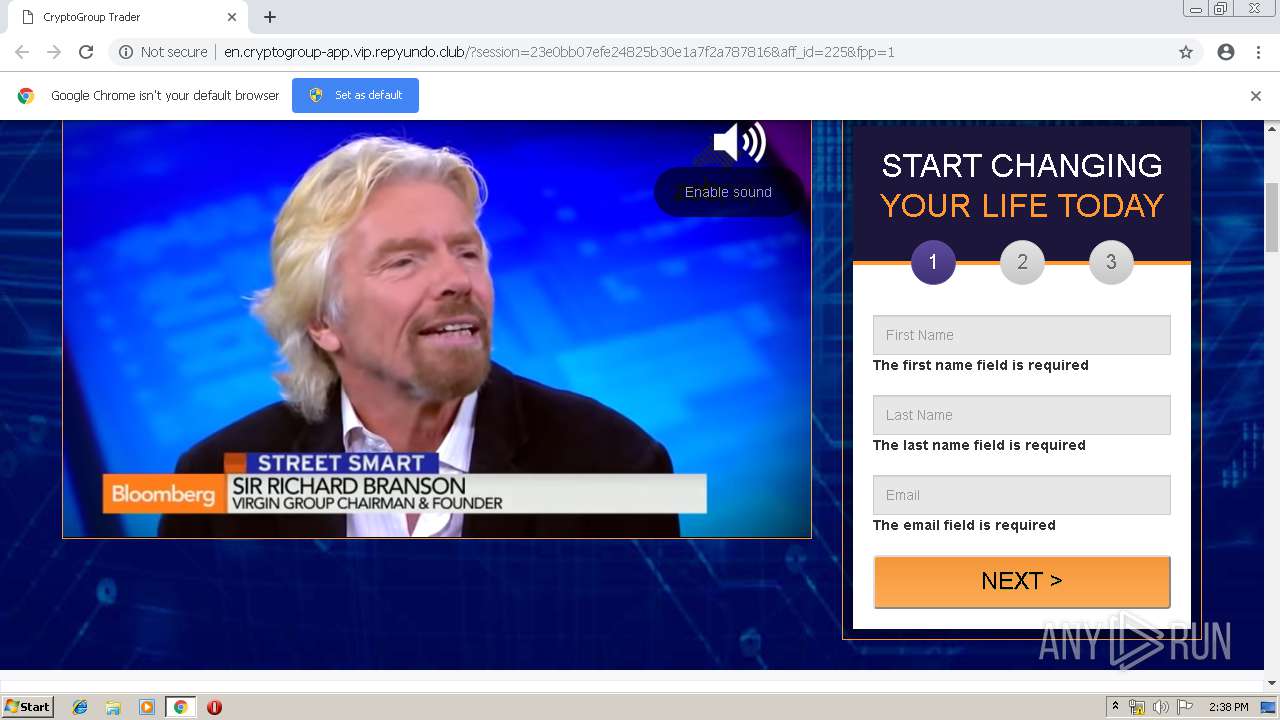
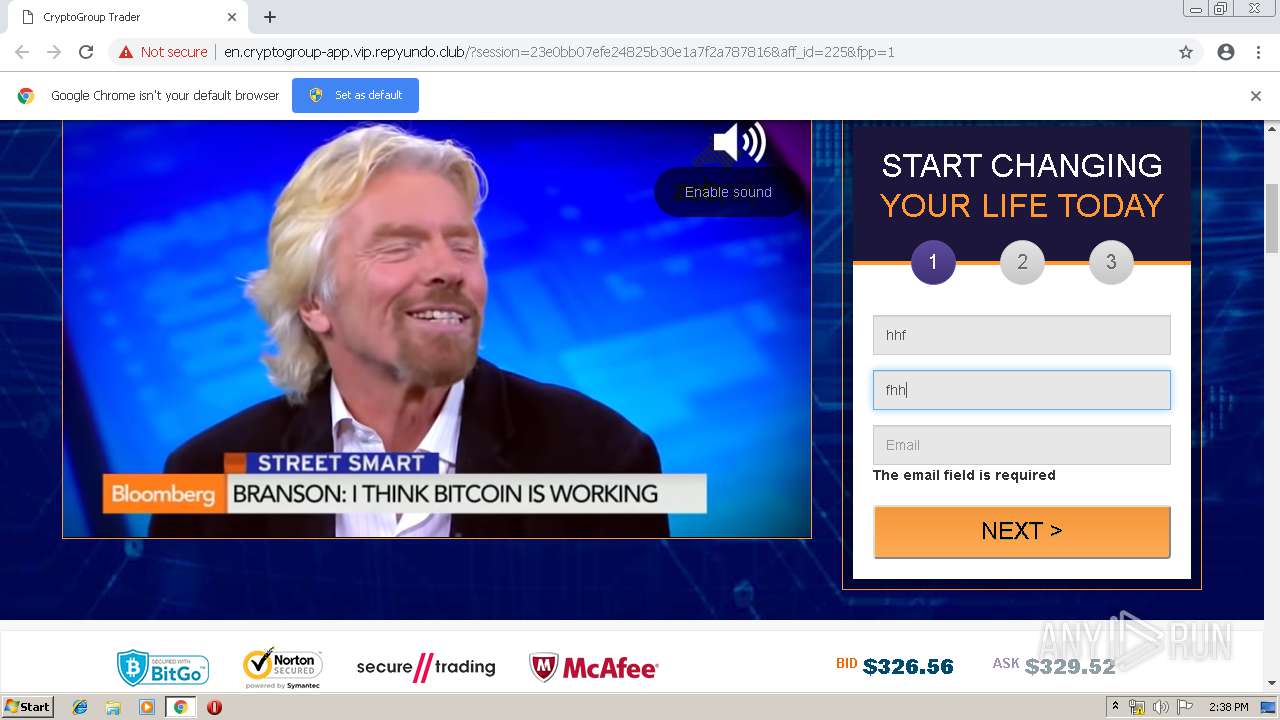
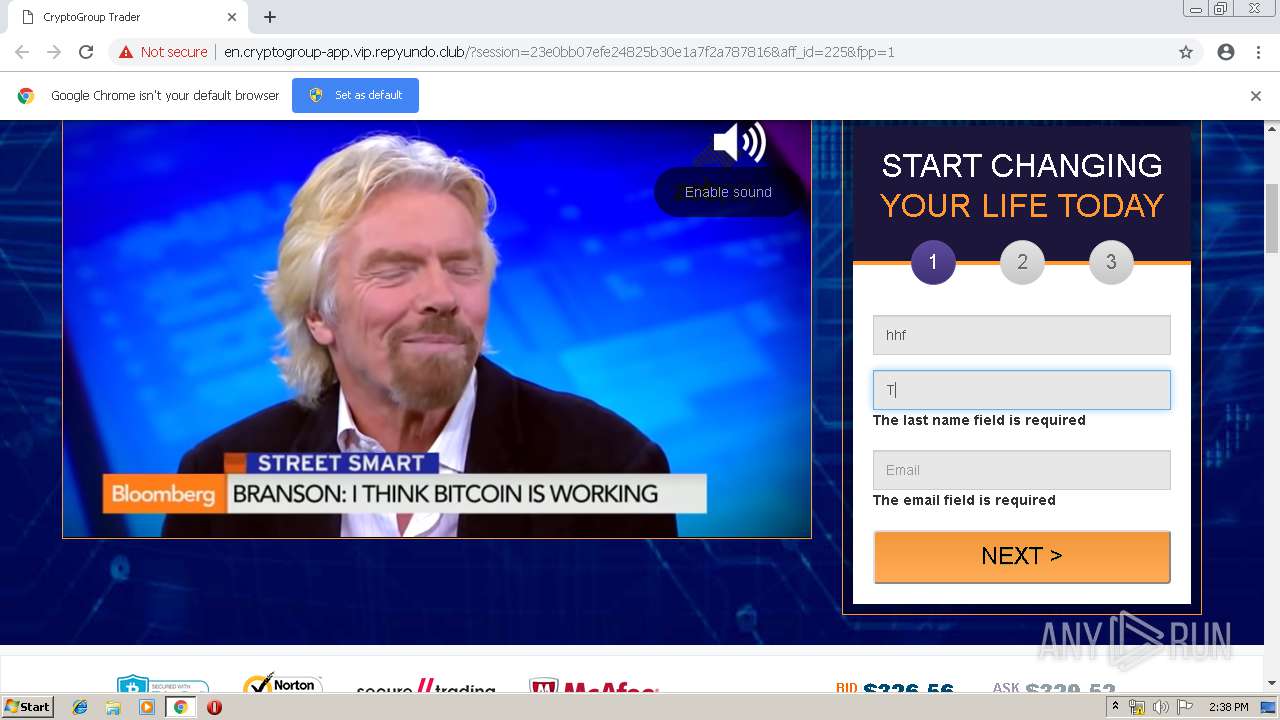
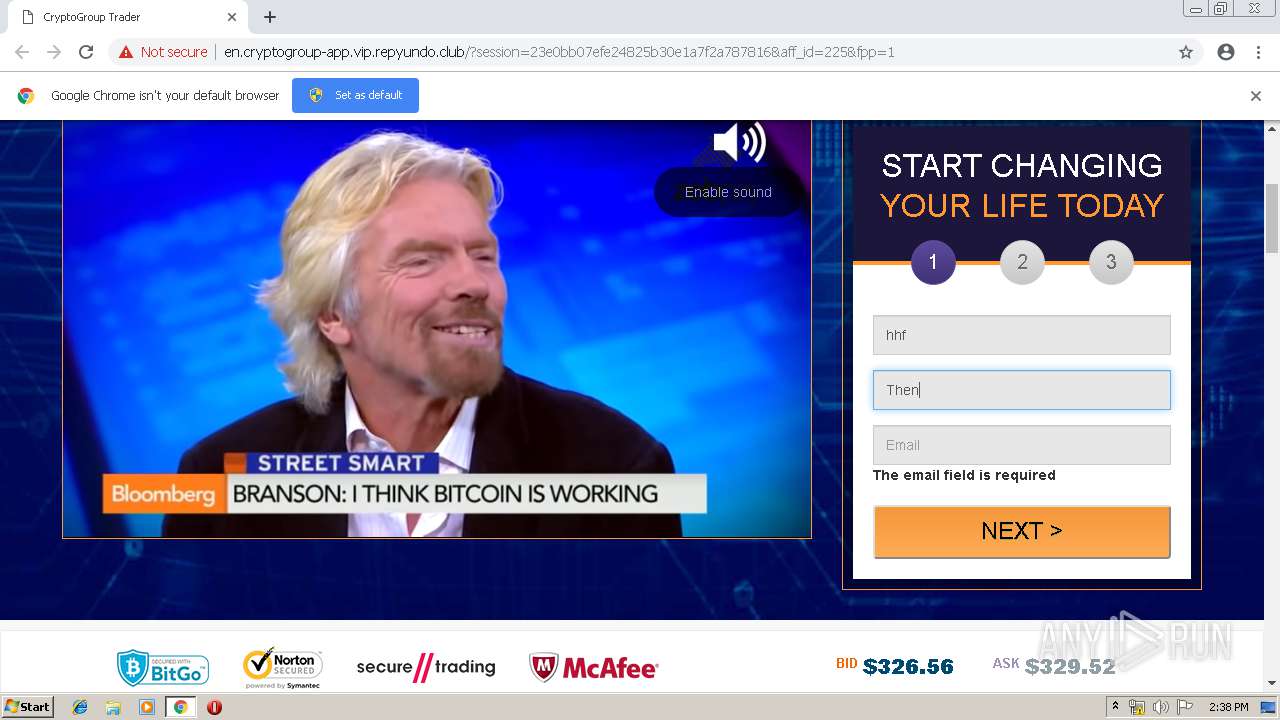
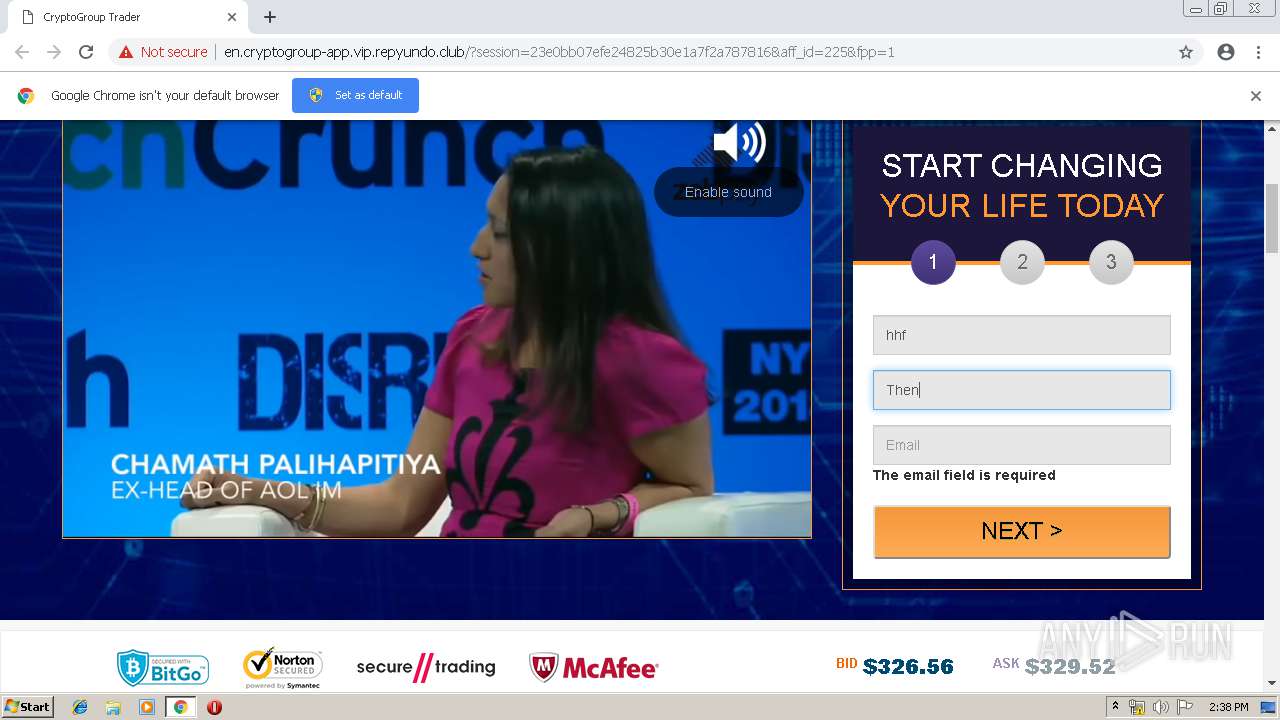
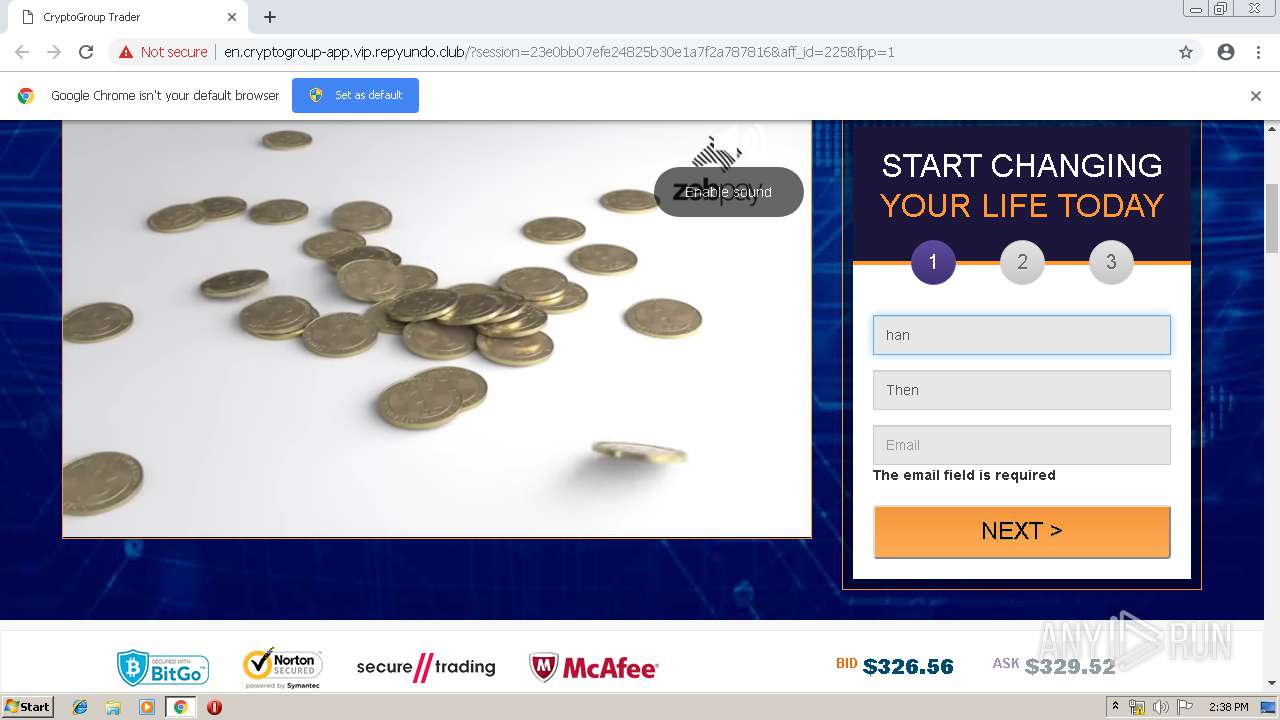
3332 | chrome.exe | GET | — | 47.254.71.233:80 | http://atbfinance.top/favicon.ico | US | — | — | suspicious |
3332 | chrome.exe | GET | 302 | 104.18.33.237:80 | http://vip.repyundo.club/tracker?s_id=7&aff_id=225 | US | — | — | suspicious |
3332 | chrome.exe | GET | 200 | 104.18.32.237:80 | http://en.cryptogroup-app.vip.repyundo.club/images/volume_1.png | US | image | 920 b | suspicious |
3332 | chrome.exe | GET | 200 | 104.18.32.237:80 | http://en.cryptogroup-app.vip.repyundo.club/js/countries.js | US | text | 3.56 Kb | suspicious |
3332 | chrome.exe | GET | 200 | 104.18.32.237:80 | http://en.cryptogroup-app.vip.repyundo.club/js/multistep-form.js | US | text | 1.63 Kb | suspicious |
3332 | chrome.exe | GET | 200 | 104.18.32.237:80 | http://en.cryptogroup-app.vip.repyundo.club/js/commonJs.js | US | text | 2.13 Kb | suspicious |
3332 | chrome.exe | GET | 200 | 47.254.71.233:80 | http://atbfinance.top/sl.html | US | html | 133 b | suspicious |
3332 | chrome.exe | GET | 200 | 104.18.32.237:80 | http://en.cryptogroup-app.vip.repyundo.club/js/intlTelInput.js | US | text | 18.7 Kb | suspicious |
3332 | chrome.exe | GET | 200 | 104.18.32.237:80 | http://en.cryptogroup-app.vip.repyundo.club/js/custom.js | US | html | 532 b | suspicious |
3332 | chrome.exe | GET | 200 | 104.18.32.237:80 | http://en.cryptogroup-app.vip.repyundo.club/css/intlTelInput.css | US | text | 2.82 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3332 | chrome.exe | 216.58.207.46:80 | www.youtube.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.193:443 | downsihybos1988.blogspot.pt | Google Inc. | US | whitelisted |
3332 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 172.217.21.193:443 | downsihybos1988.blogspot.pt | Google Inc. | US | whitelisted |
3332 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 172.217.22.9:443 | resources.blogblog.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 216.58.207.33:443 | themes.googleusercontent.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 172.217.16.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 47.254.71.233:80 | atbfinance.top | Alibaba (China) Technology Co., Ltd. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
downsihybos1988.blogspot.pt |
| whitelisted |
accounts.google.com |
| shared |
downsihybos1988.blogspot.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
resources.blogblog.com |
| whitelisted |
www.blogger.com |
| shared |
themes.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3332 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |