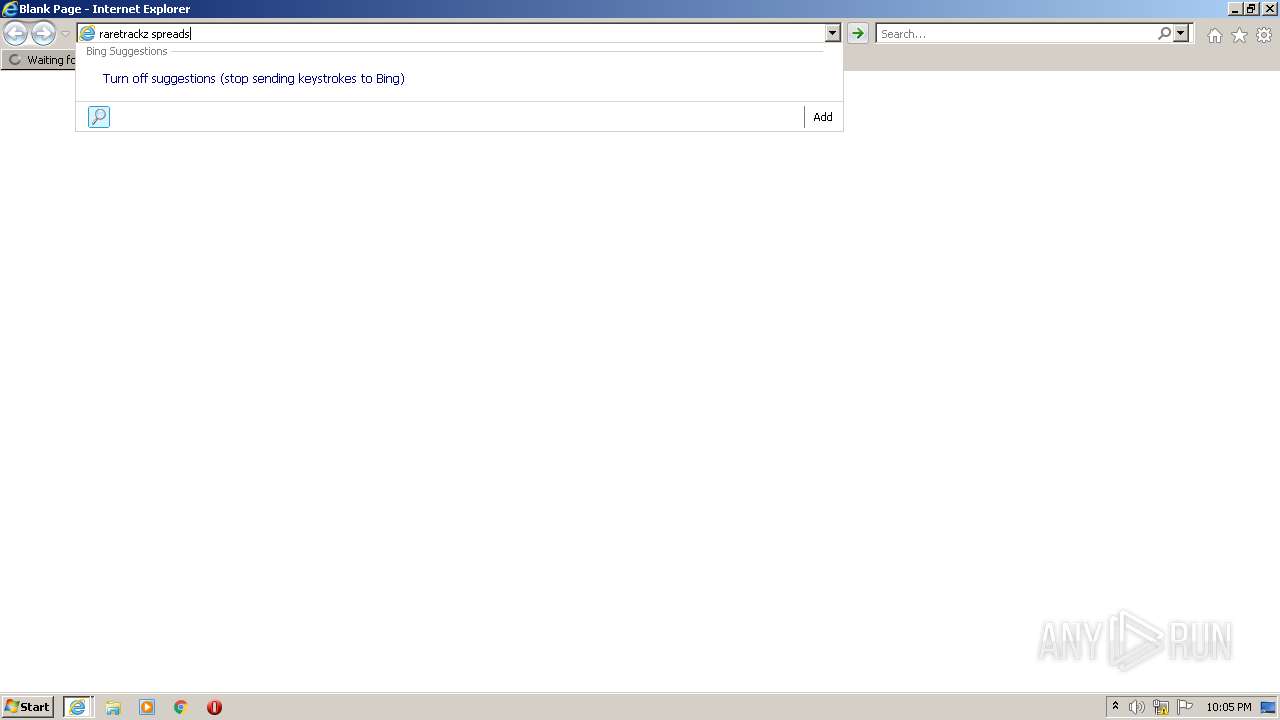
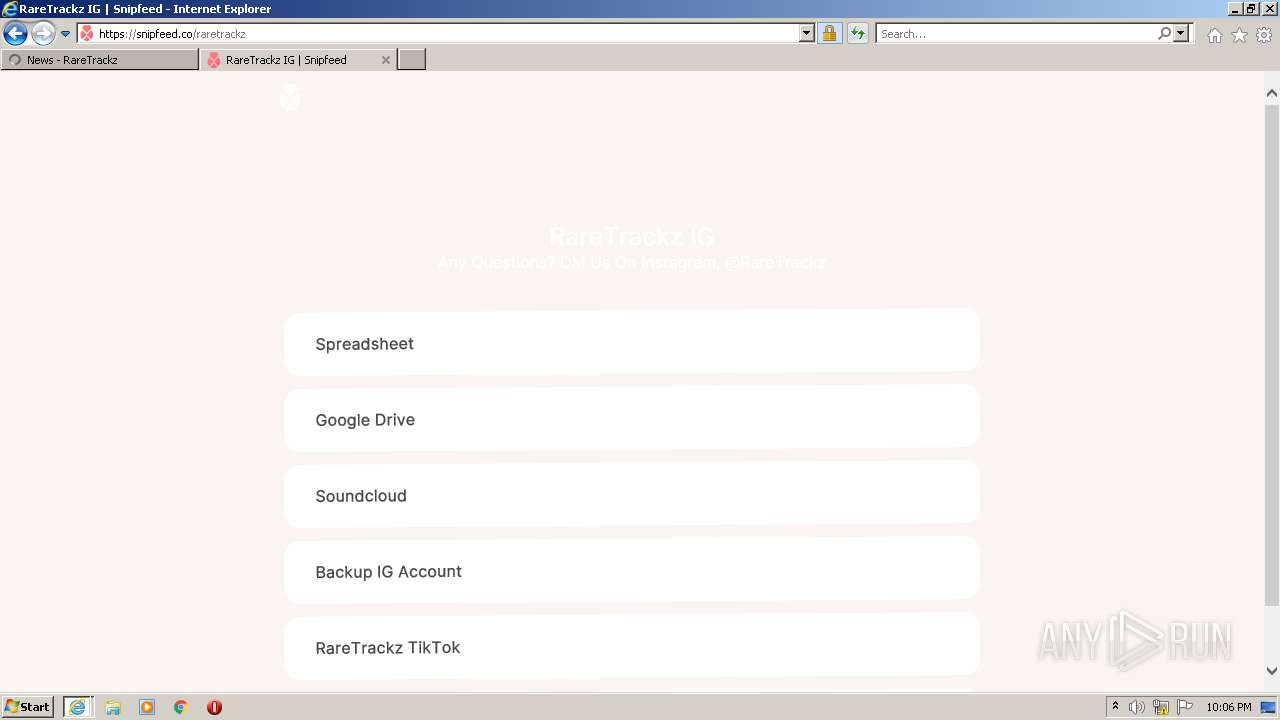
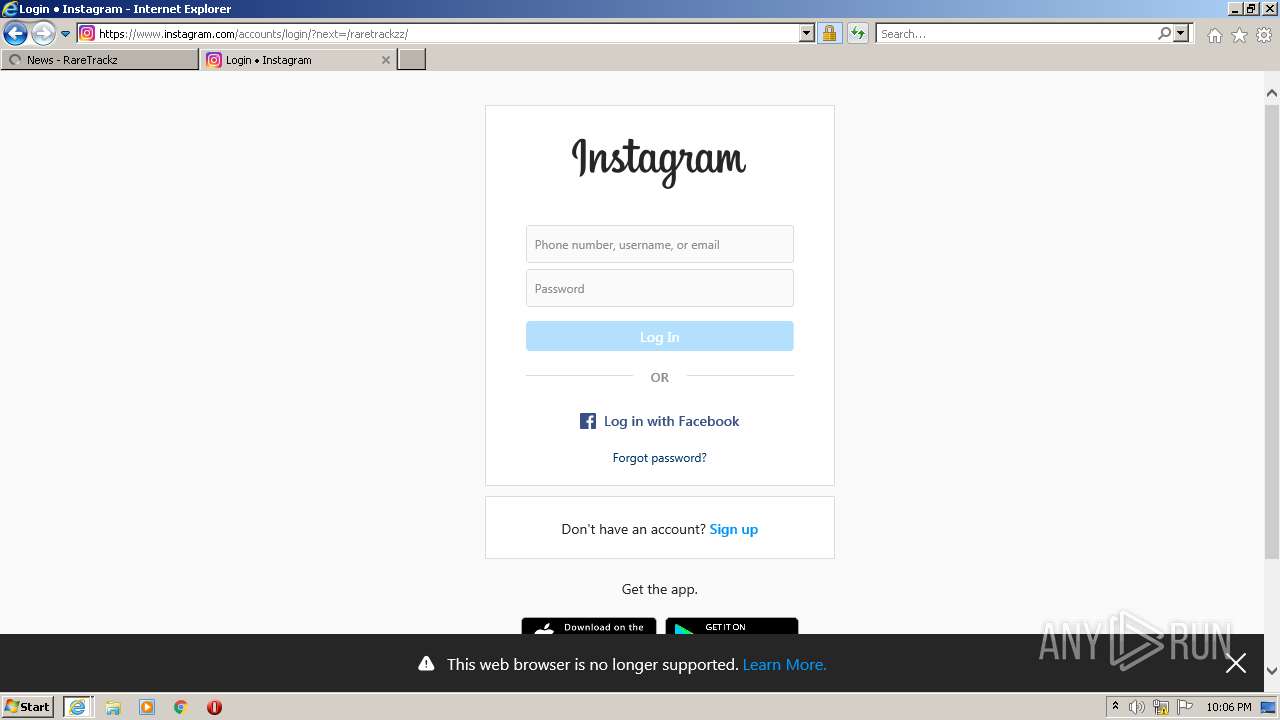
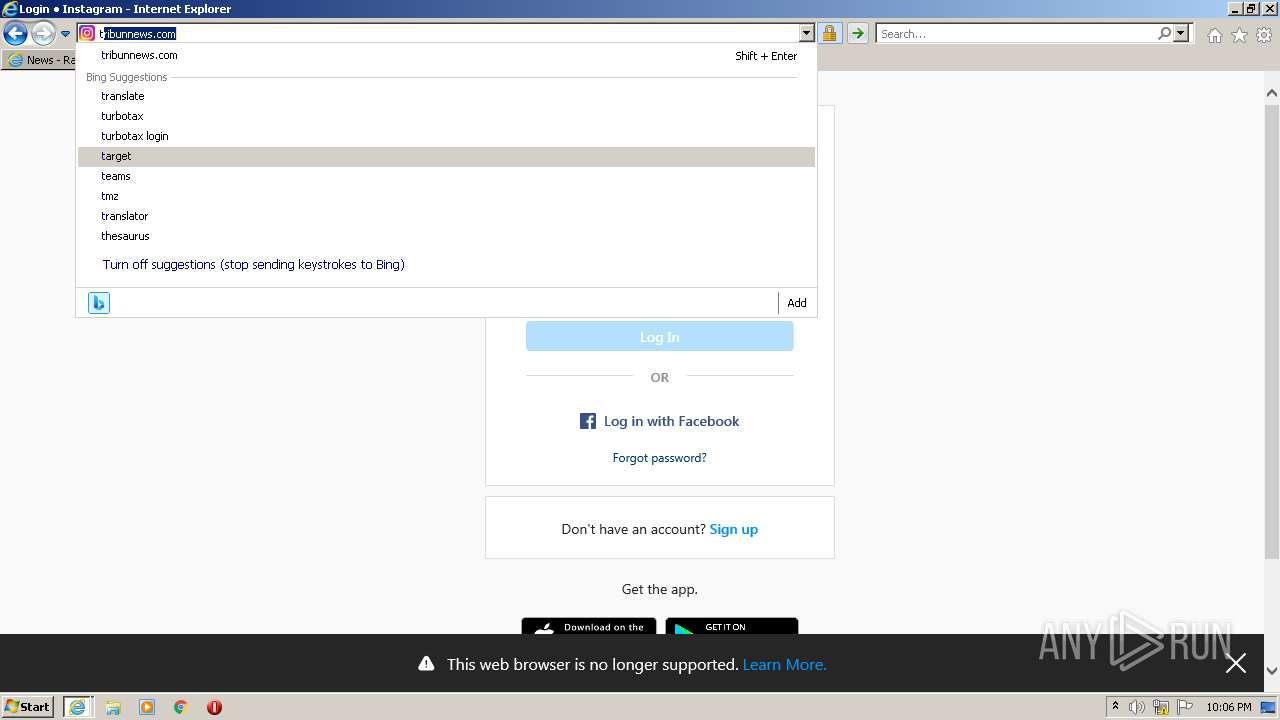
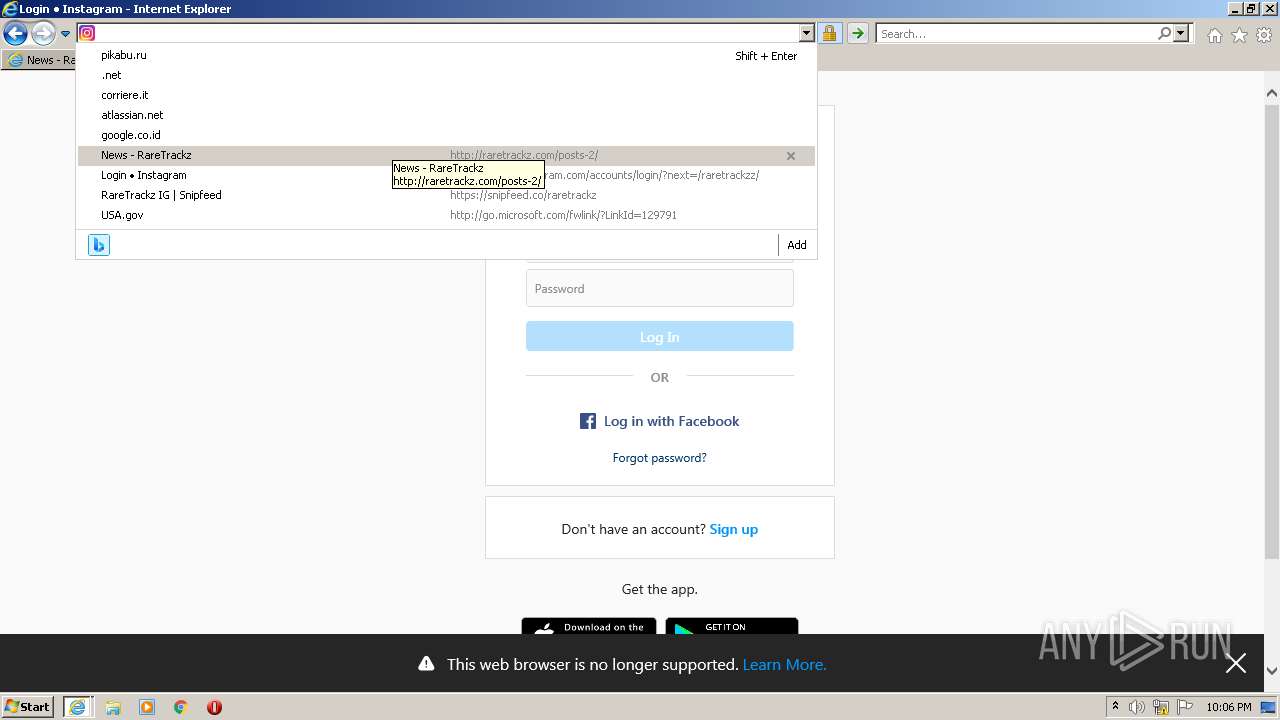
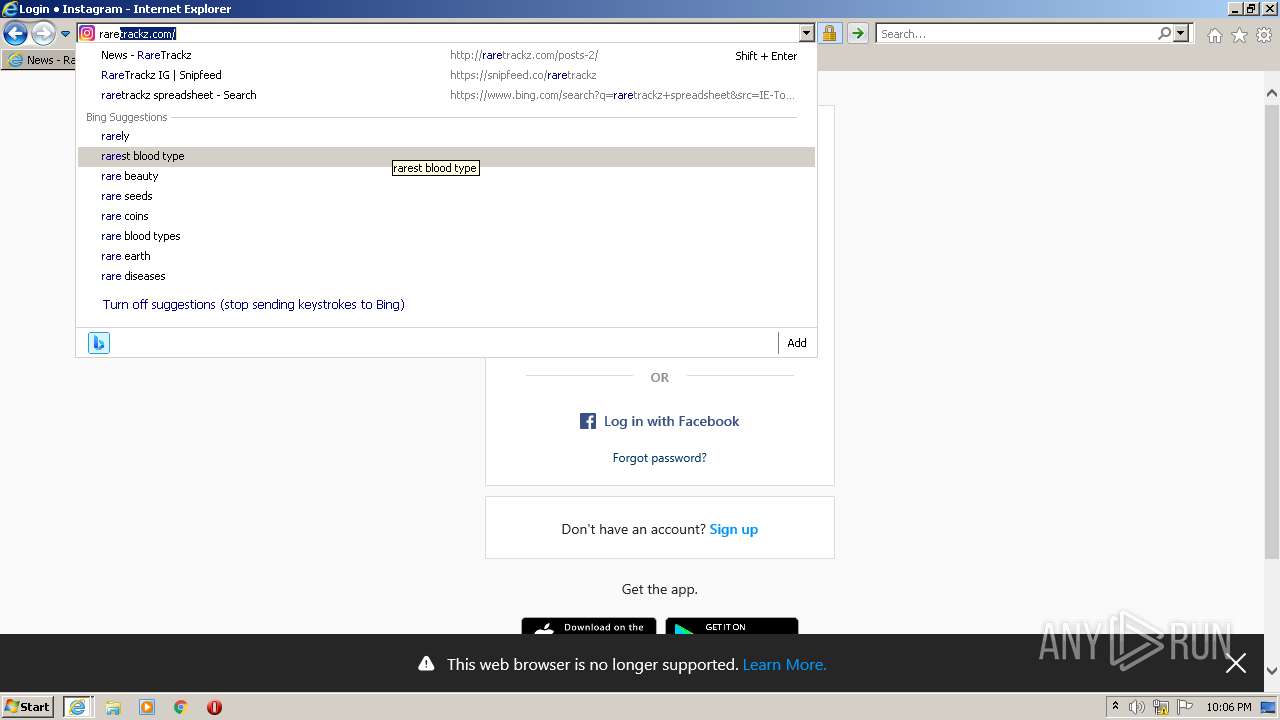
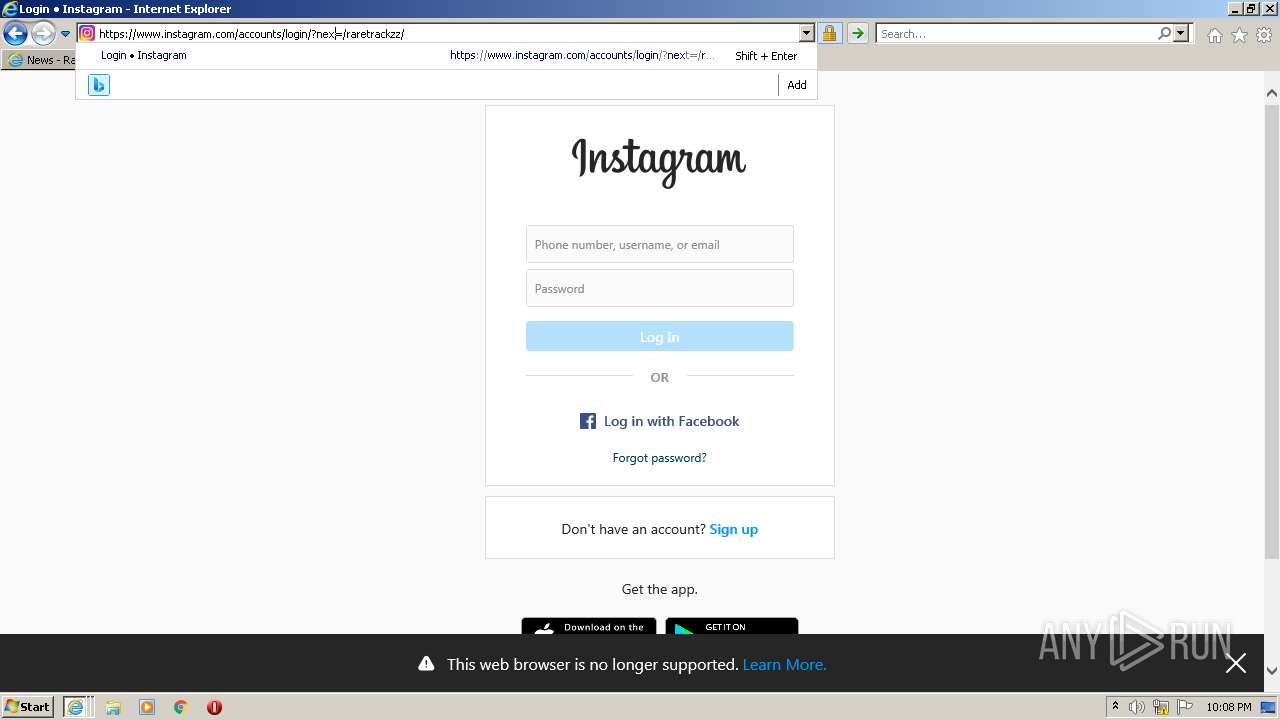
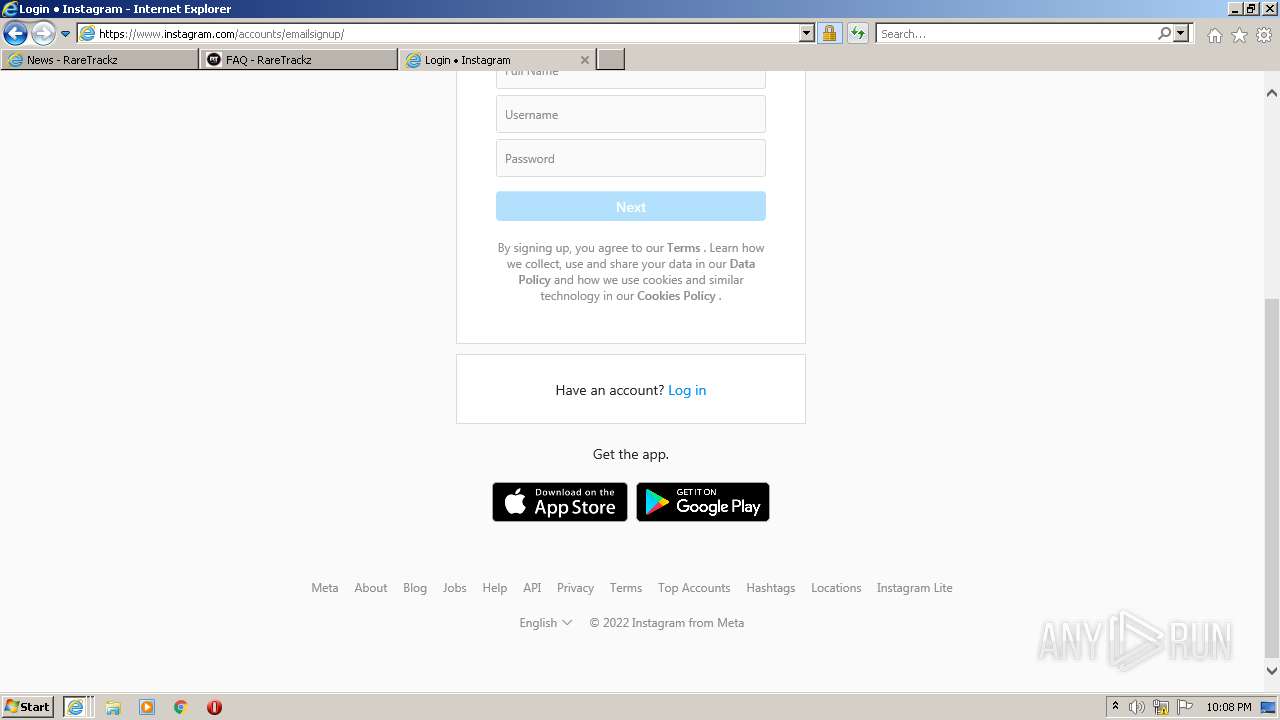
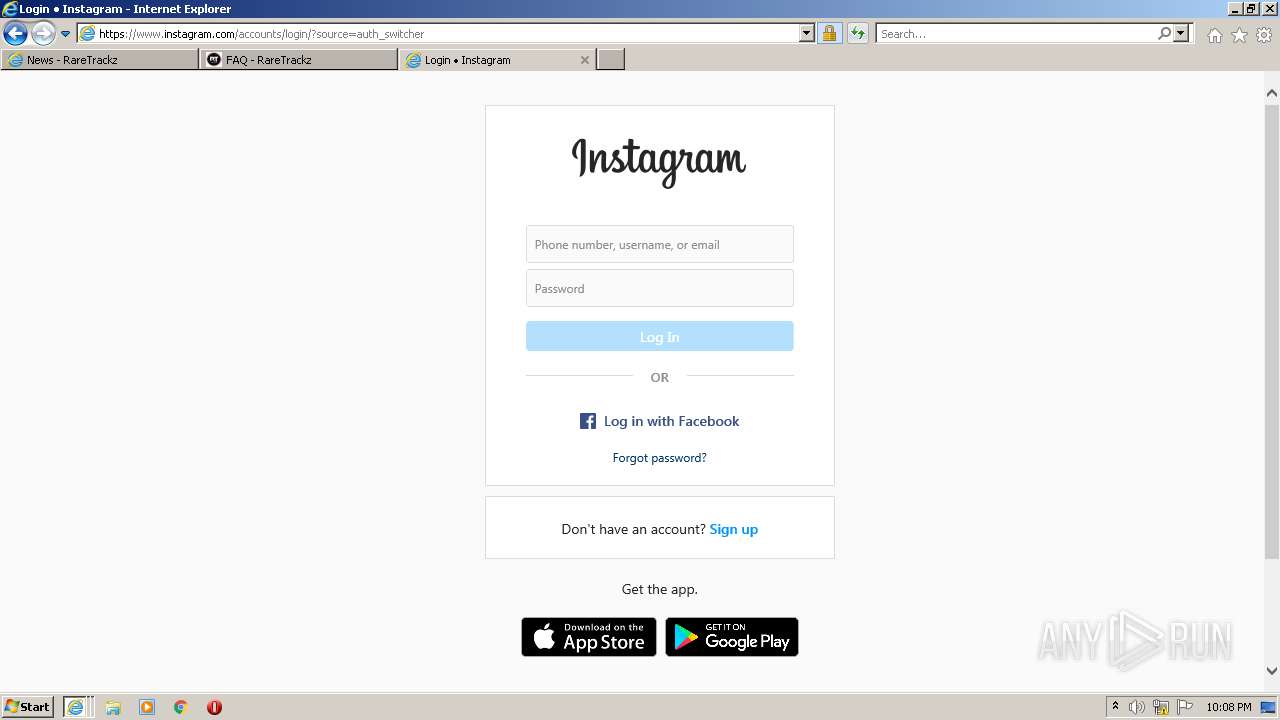
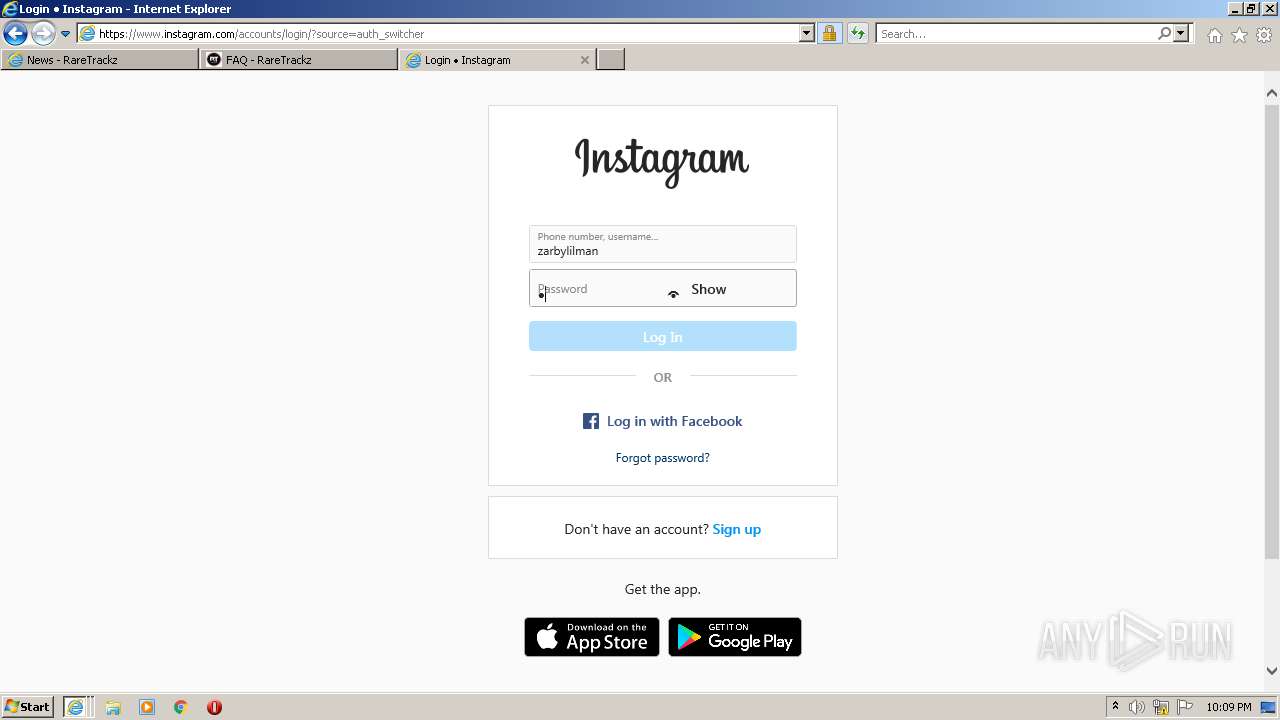
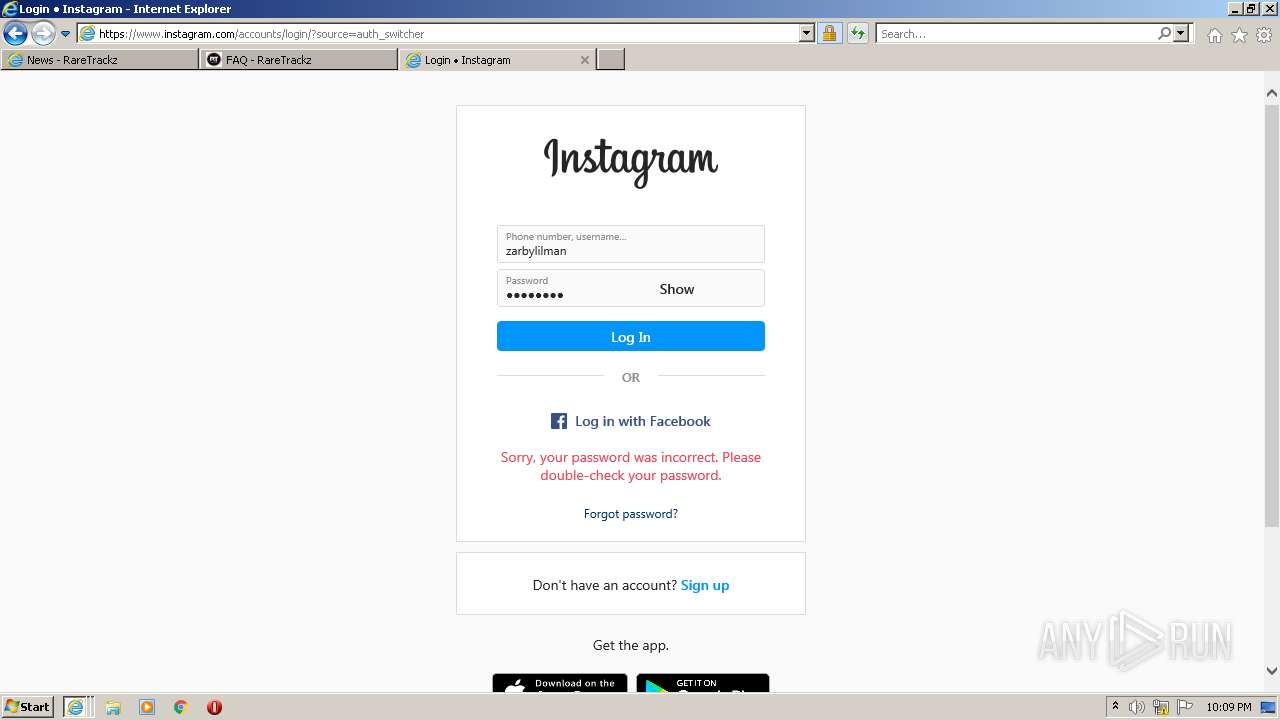
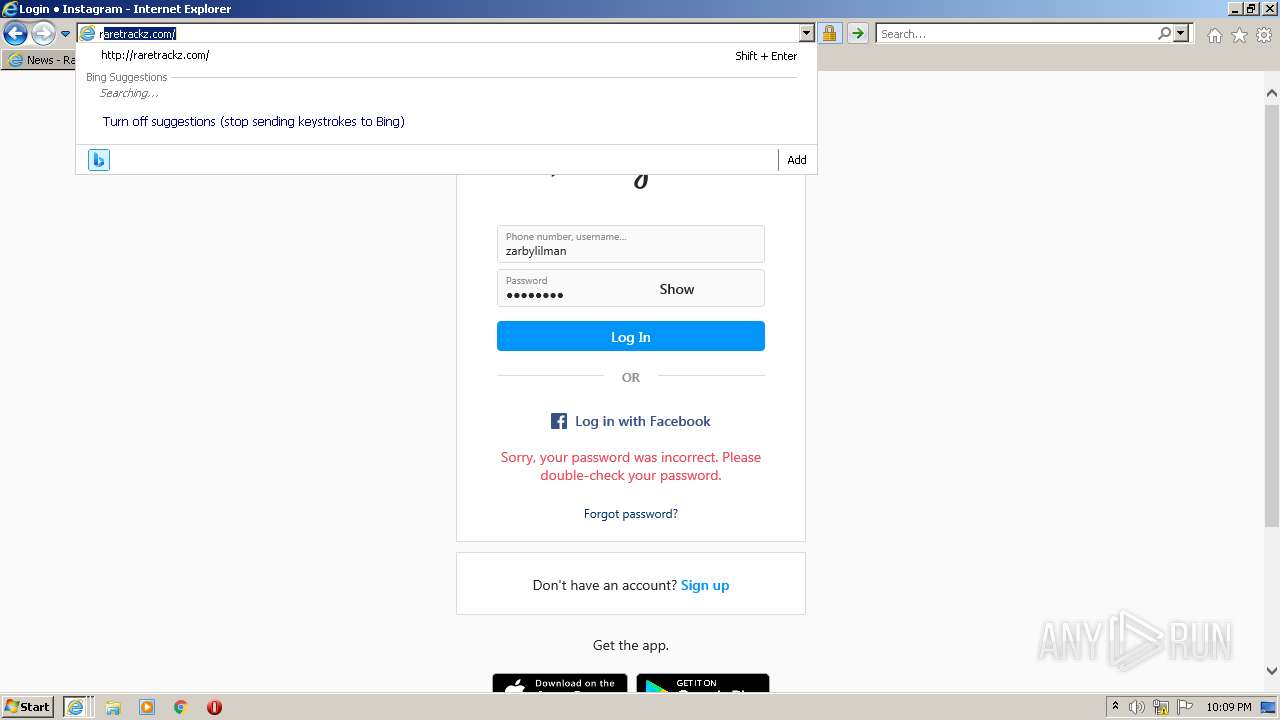
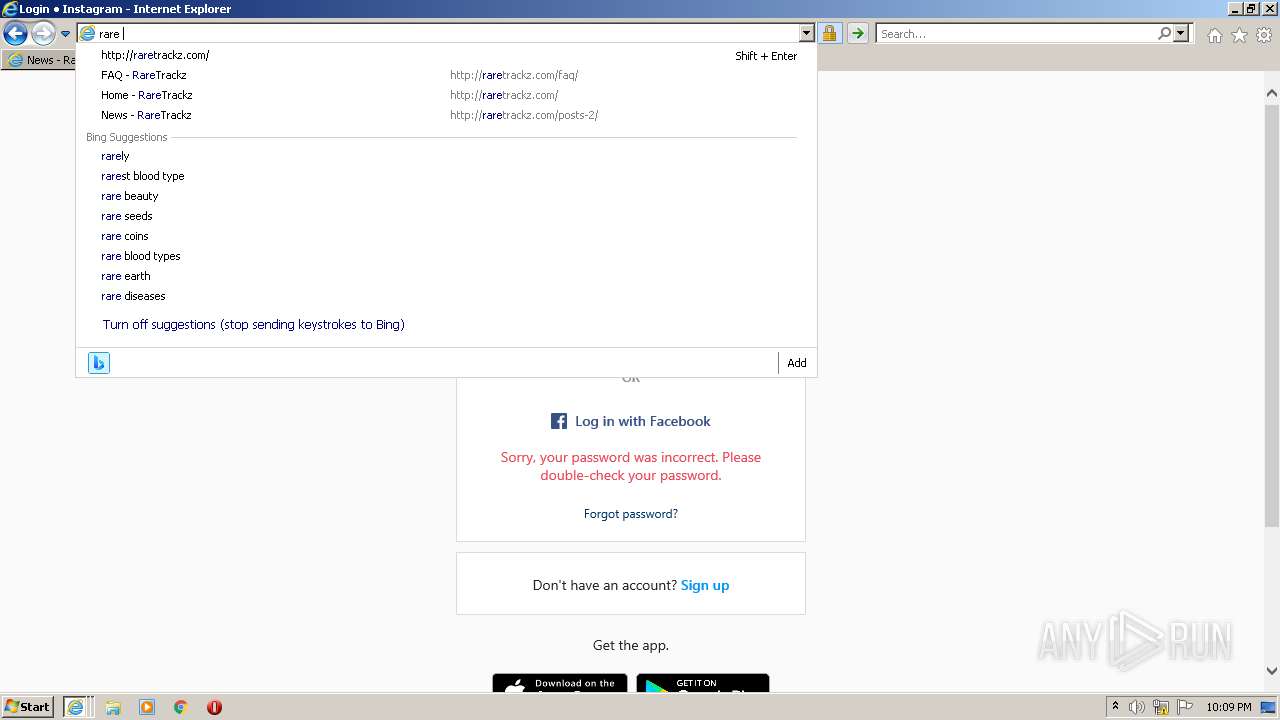
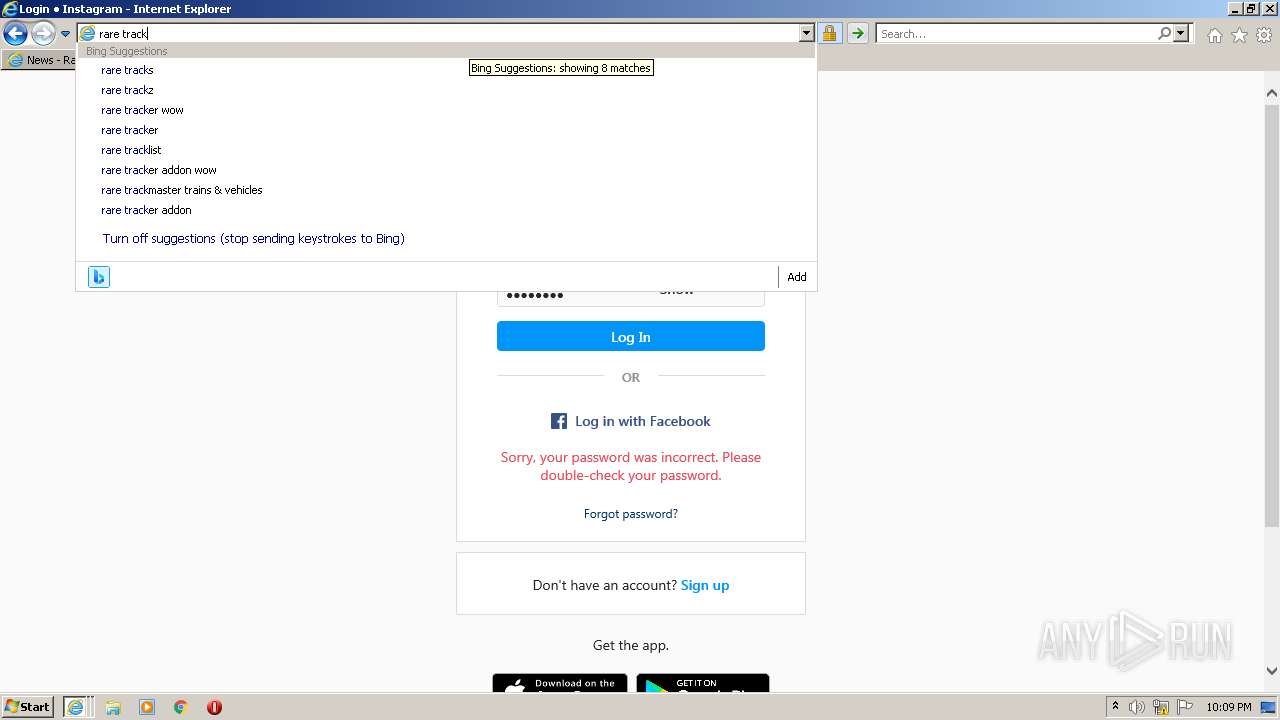
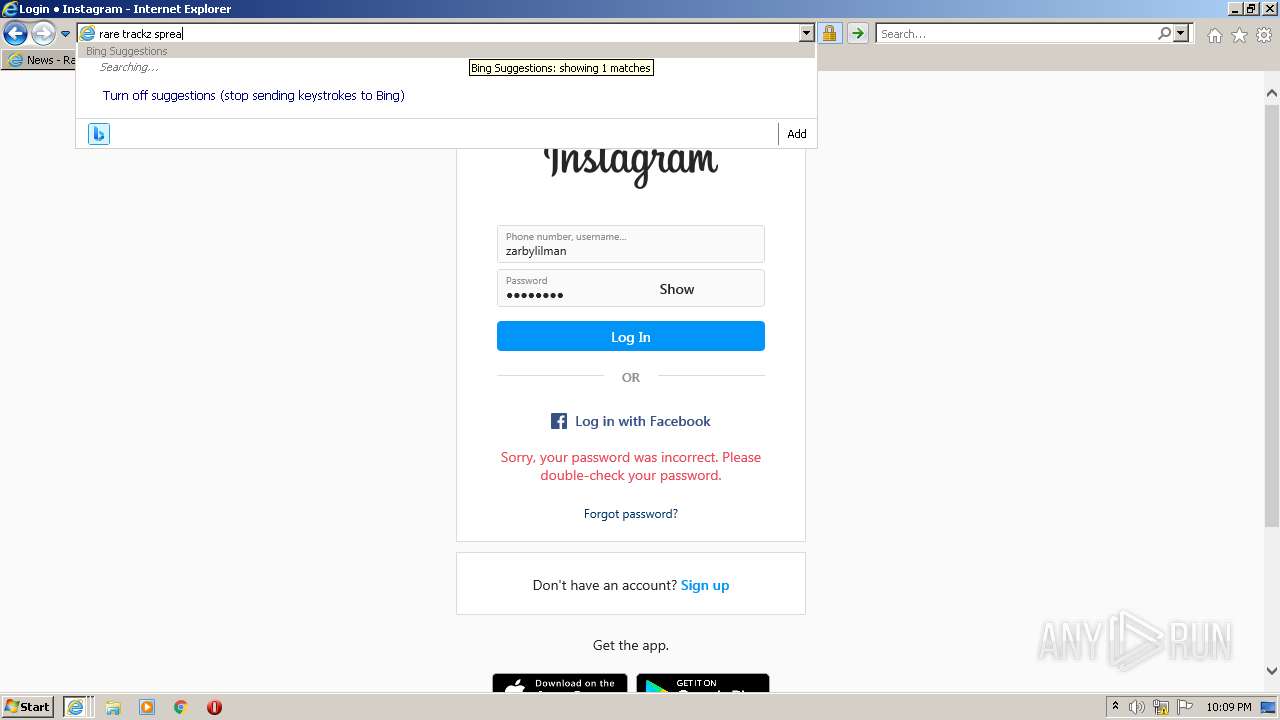
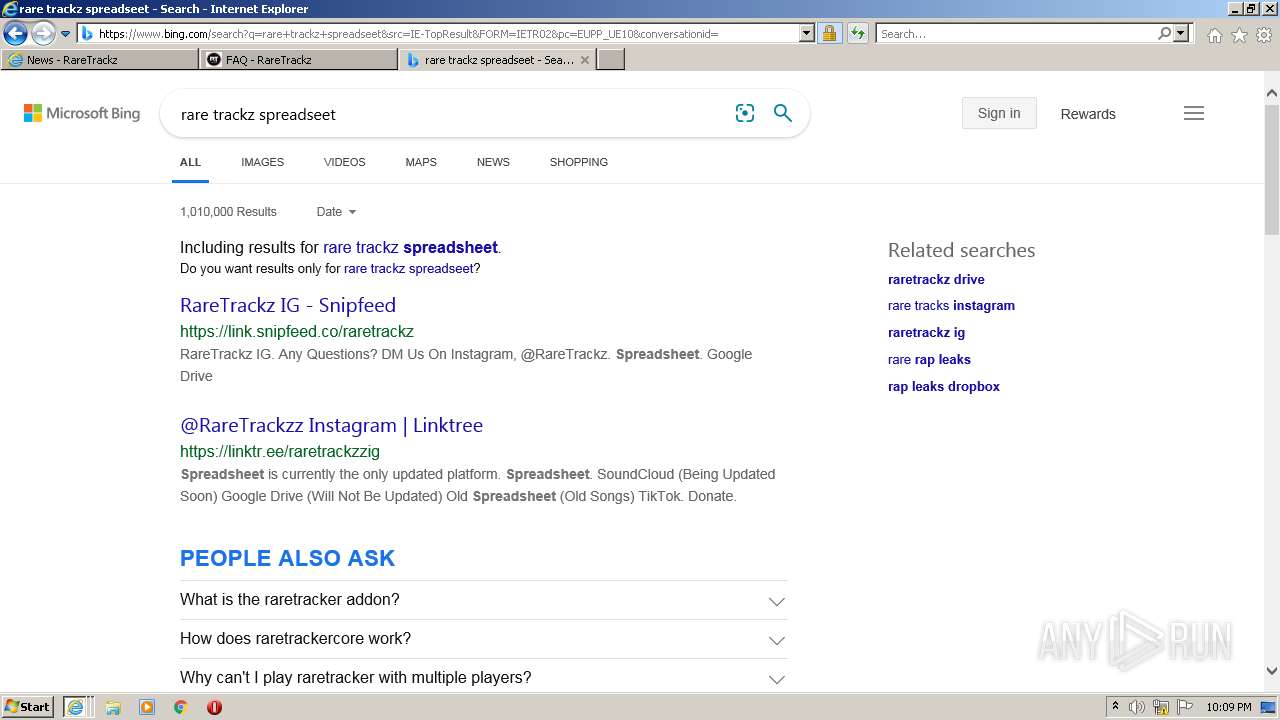
| URL: | http://raretrackz.com/posts-2/ |
| Full analysis: | https://app.any.run/tasks/644dddbe-080b-43d3-a39f-19162f9a0c87 |
| Verdict: | Malicious activity |
| Analysis date: | February 04, 2022, 22:05:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3C9980EA5E57B690BD9DF3EB312E76CA |
| SHA1: | 94B56F14A7CC236AC4D7593750C0C9FB95F26BB2 |
| SHA256: | 6B586E61AC73B979B555CE99206C1DC26E01C44E9E6102D501406E2ADBDFA259 |
| SSDEEP: | 3:N1KMqZVVKRIa:CMqZVgRIa |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 480)
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 2200)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2840)
Reads the computer name
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 480)
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 2200)
Checks supported languages
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 480)
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 2200)
Reads settings of System Certificates
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 480)
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 2200)
Application launched itself
- iexplore.exe (PID: 2840)
Checks Windows Trust Settings
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 2200)
- iexplore.exe (PID: 480)
Reads internet explorer settings
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 480)
- iexplore.exe (PID: 2200)
Creates files in the user directory
- iexplore.exe (PID: 480)
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 2200)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2688)
Changes settings of System certificates
- iexplore.exe (PID: 2840)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:791849 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:3872008 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://raretrackz.com/posts-2/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
46 243
Read events
45 754
Write events
480
Delete events
9
Modification events
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30939667 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30939667 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
45
Text files
377
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:2D60219813B16A8D4B3EB05D231E45C5 | SHA256:BAE0E5169341F37F13A591D5D1D85074CD9DD6147B46B2BF6E63D9AF062C2ACF | |||
| 480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:A3F7D4220F444601B1840523A27207A8 | SHA256:393FAD1427441DE412A25DFADA99A026B5A13C12370F6DD51048F9E7FB5F1893 | |||
| 480 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WJO135P7.txt | text | |
MD5:D0E092582B6BBF1402AE10E79E5B53B1 | SHA256:80355D1F809EC3F912C582CC2958403ECAE077EDC810C1729ECE6BB325567FEA | |||
| 480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EFAFCCB605EB82F3FD853B92547B1658 | SHA256:48BC6C7C86A1801584A0E6748F89FC963A1868B71A5176C098B7A0EF80382E94 | |||
| 480 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0AUY4AN3.txt | text | |
MD5:2C3FE170F6CEA1E4A3871D3F9F3FA627 | SHA256:EE5CA5F3F1F404DB1ACB724BDC1FCFF4CEB83AC0BB15896BF717288FBC9E52E3 | |||
| 480 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\B0VCLJCG.txt | text | |
MD5:ED8CD50BDCDE471FBBD4CBB4B7E9473A | SHA256:D9A73F0156341B3BCC91D088C9683F3C2C58BC00AA1178C5D012438C3BD2AE58 | |||
| 480 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WOB7PVCC.txt | text | |
MD5:153D1540DA9E822B498EEE3814F12316 | SHA256:50C38C0C14DAA4B409D03D943F54D0492107FFAF5627411E9D00419E745E45EC | |||
| 480 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\KAWRB0FG.txt | text | |
MD5:8FD7507201C036FA69D98AF2581369AD | SHA256:DA338603940A10477F1305219A9ECE722CDE13BBE2F618B454BE437BAFFF5CA3 | |||
| 480 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\QJUUTEVV.txt | text | |
MD5:135F0EFC6BF9E9B9CC02F676D0DE24E7 | SHA256:6E8310F913E11463E49302EFB83302BBB678779CE4B2CBAB7D560D13EF31DE1C | |||
| 480 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\A798KXUX.txt | text | |
MD5:4EBF2E893CE2969A716A068734C4F813 | SHA256:8353C9DDBE70EB1481C843B8CA4DF3403B78F93C99446193386FA520C8E551D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
86
TCP/UDP connections
234
DNS requests
73
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | iexplore.exe | GET | 200 | 41.63.96.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9a145581da912bfe | ZA | compressed | 4.70 Kb | whitelisted |
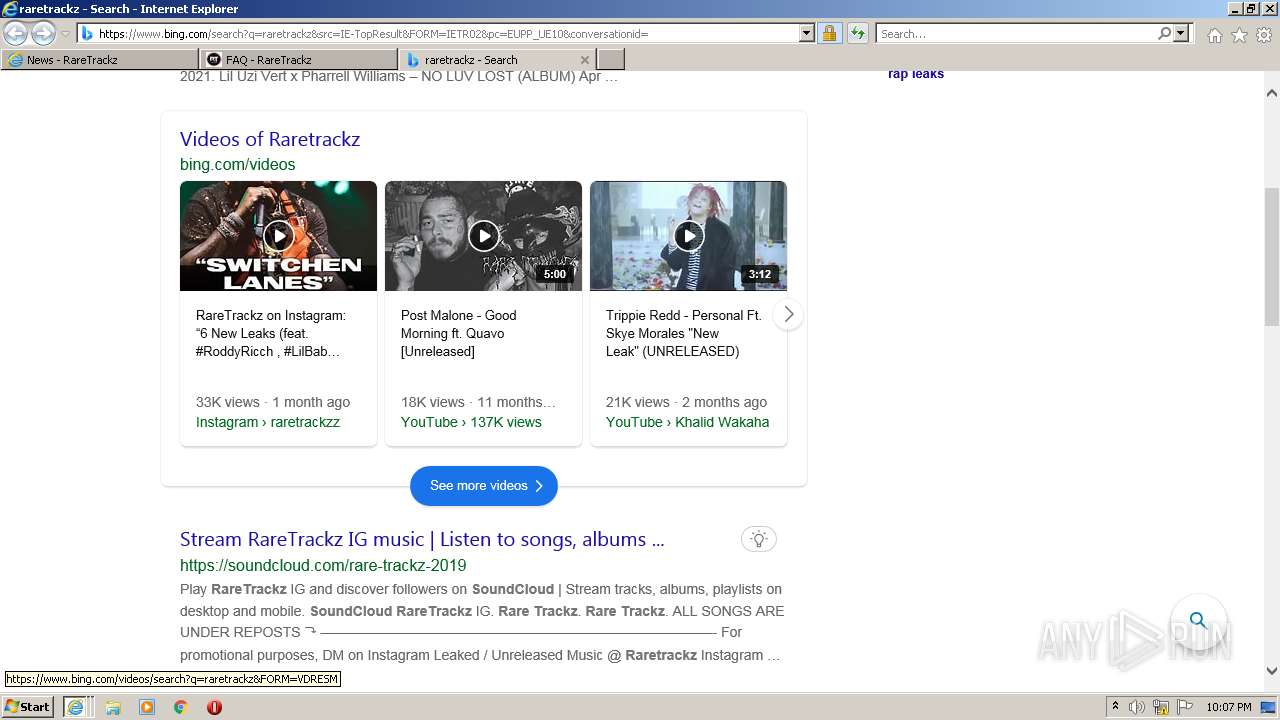
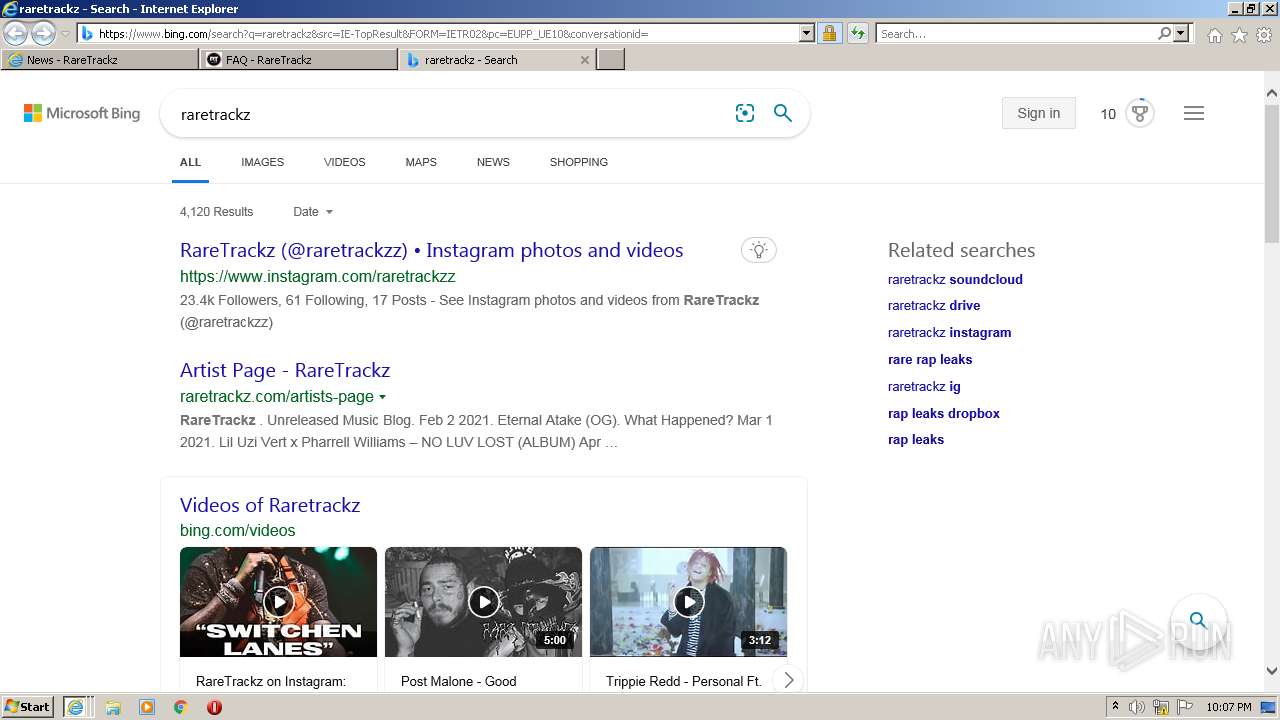
480 | iexplore.exe | GET | 200 | 63.250.43.16:80 | http://raretrackz.com/posts-2/ | US | compressed | 11.0 Kb | malicious |
480 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2840 | iexplore.exe | GET | 200 | 41.63.96.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a55319b5e67b1851 | ZA | compressed | 4.70 Kb | whitelisted |
480 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEHtC0qziDpvsyMENugzYxjk%3D | US | der | 471 b | whitelisted |
2688 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
480 | iexplore.exe | GET | 200 | 63.250.43.16:80 | http://raretrackz.com/wp-content/plugins/clever-fox/inc/fiona-blog/images/logo.png | US | image | 4.77 Kb | malicious |
2688 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2688 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
480 | iexplore.exe | GET | 200 | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2123feaa62d5b57a | ZA | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
480 | iexplore.exe | 63.250.43.15:80 | raretrackz.com | Frontline Data Services, Inc | US | malicious |
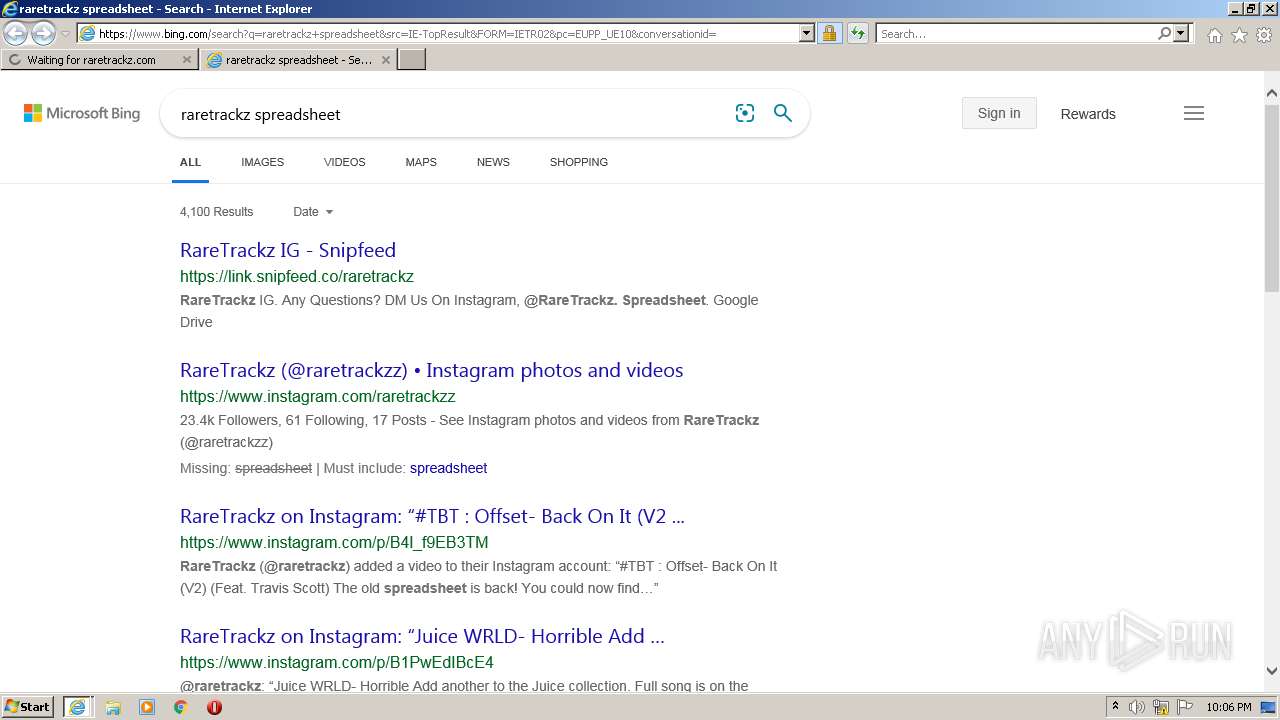
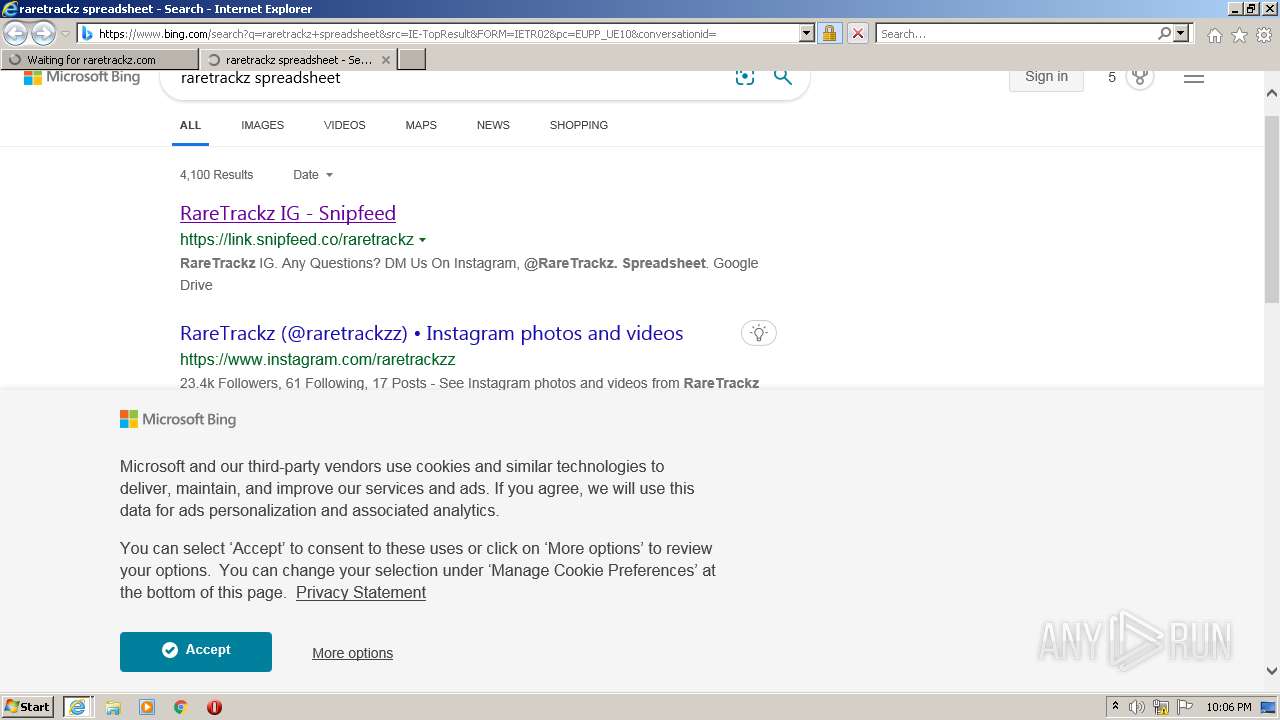
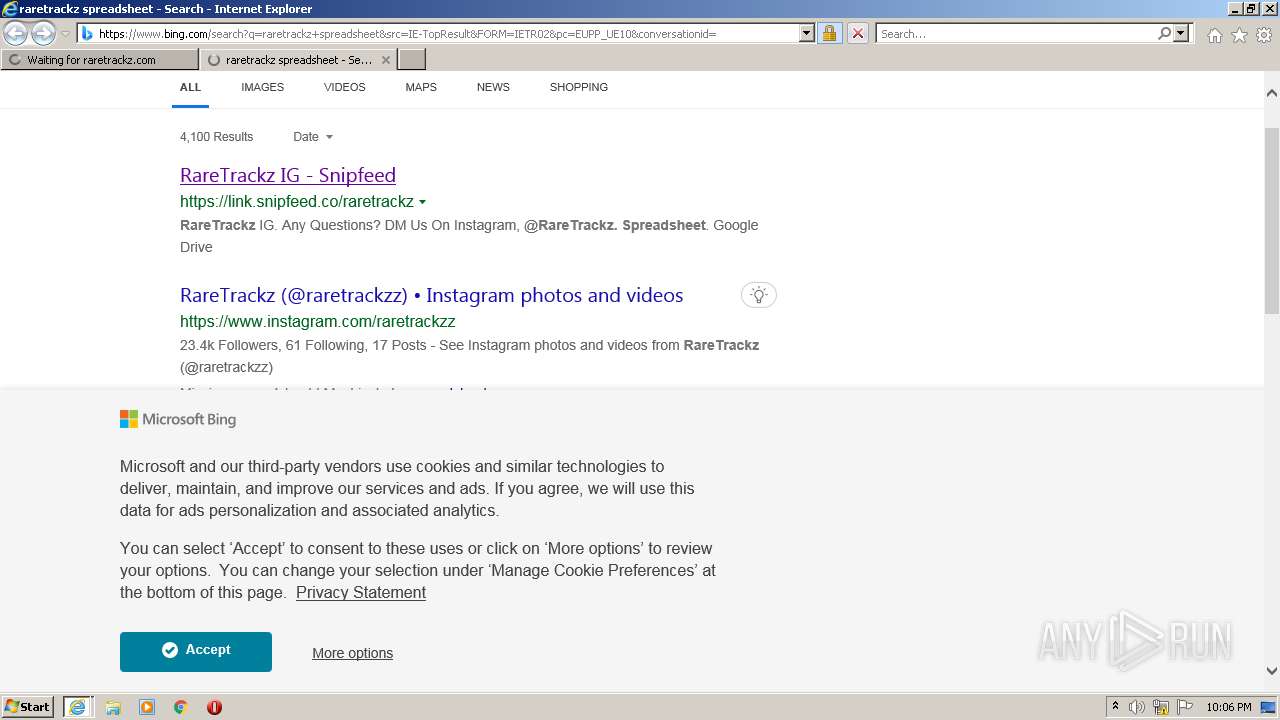
2840 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2840 | iexplore.exe | 41.63.96.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
480 | iexplore.exe | 13.107.13.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
480 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2688 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
480 | iexplore.exe | 41.63.96.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
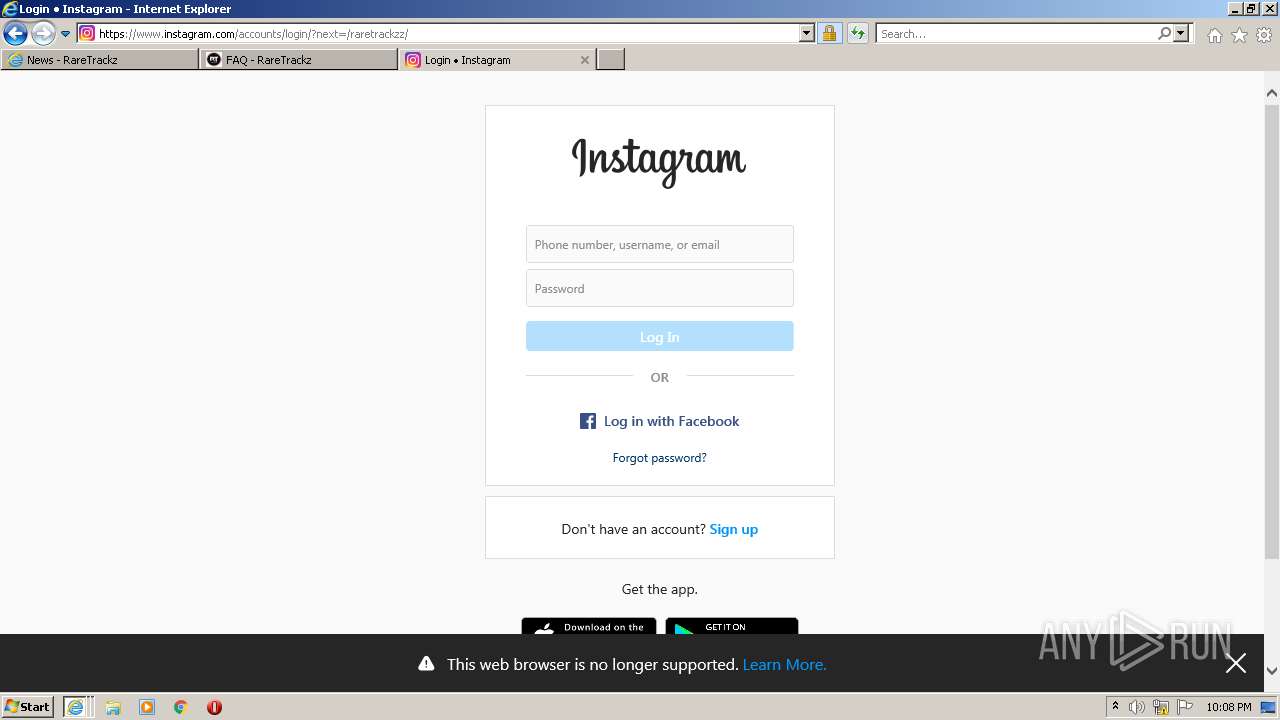
2688 | iexplore.exe | 20.190.151.8:443 | login.live.com | Microsoft Corporation | US | suspicious |
2688 | iexplore.exe | 20.190.154.16:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
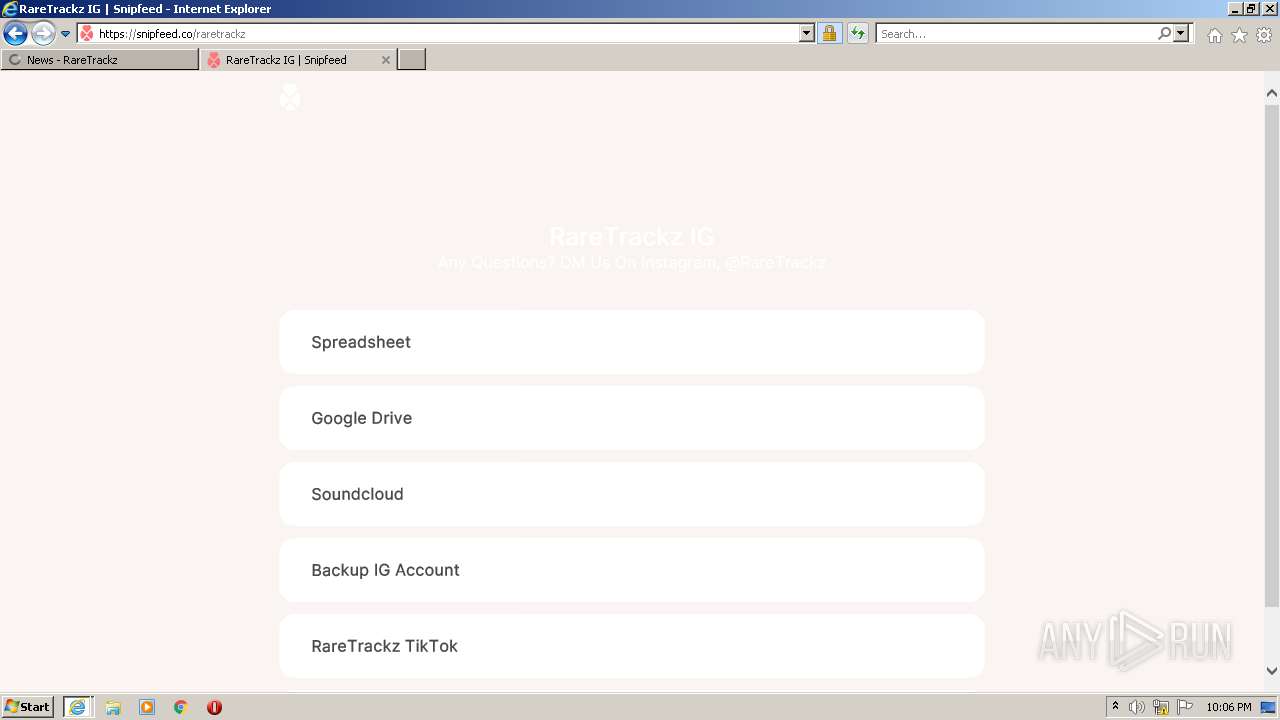
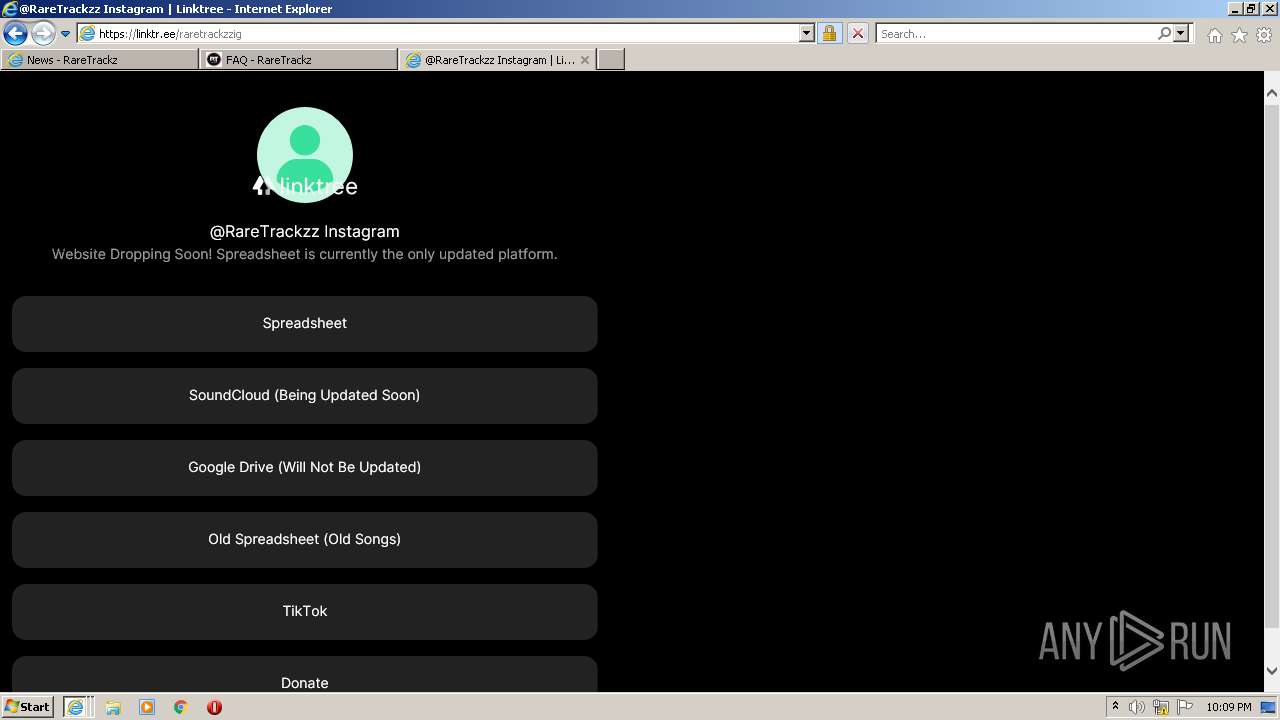
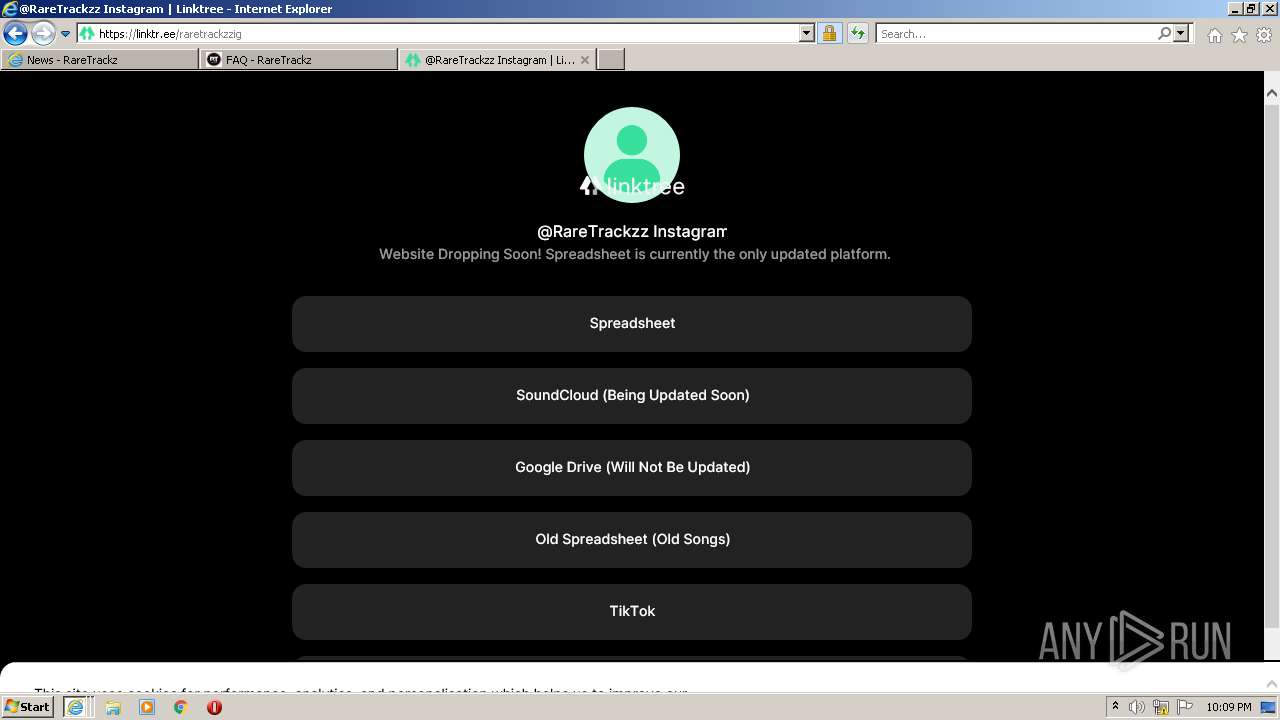
2688 | iexplore.exe | 76.223.126.88:443 | link.snipfeed.co | AT&T Services, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
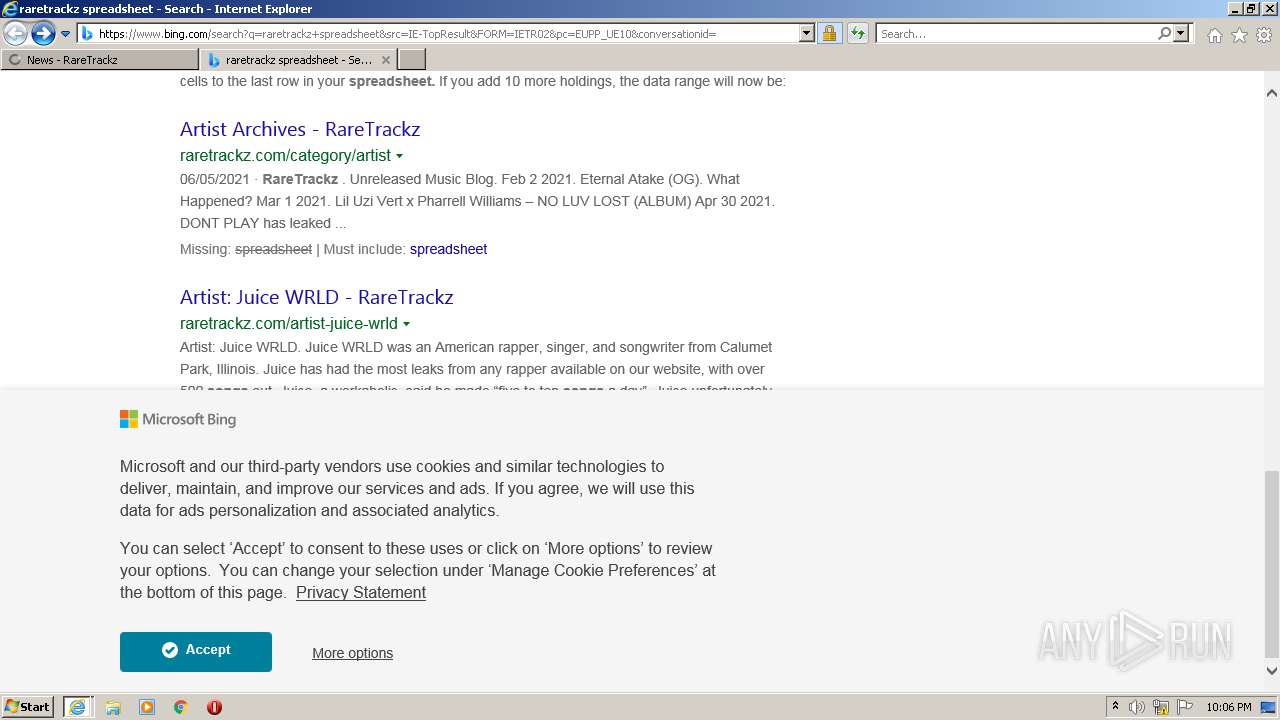
raretrackz.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
link.snipfeed.co |
| malicious |
x1.c.lencr.org |
| whitelisted |
snipfeed.co |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
480 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |