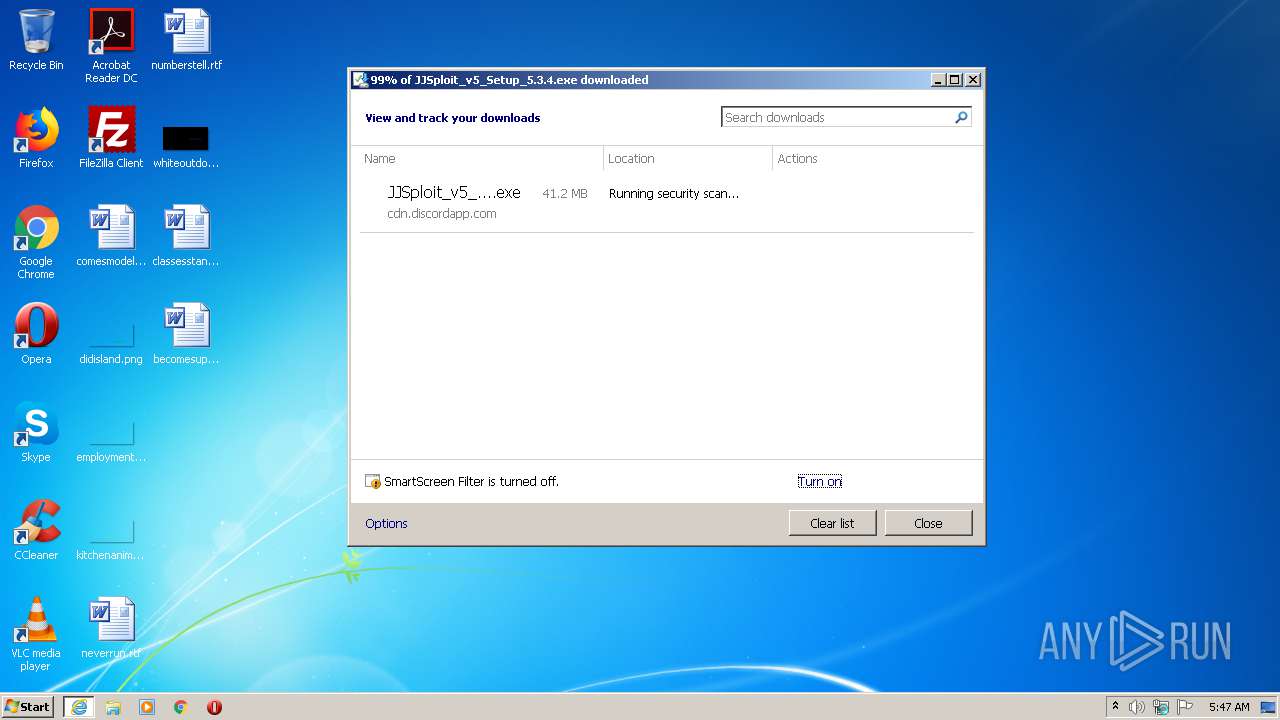
| URL: | https://cdn.discordapp.com/attachments/423644248156667951/783714727318650881/JJSploit_v5_Setup_5.3.4.exe |
| Full analysis: | https://app.any.run/tasks/ba3d5109-bfb4-4b28-892c-ddad176da984 |
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2021, 04:46:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E804A48B0F1553277F14BBCFD7A83929 |
| SHA1: | 9AEC4D57A8FFAEEA8157D38D591A464F53E5F006 |
| SHA256: | 6B56C3B676B7B601A4F4B51E9D25FC465ADDDF2DE062FB20A74518AD21C92C76 |
| SSDEEP: | 3:N8cCWdy6//QdxpRad1BKKKkd0G1A:2cry6XGzRarBKKBK |
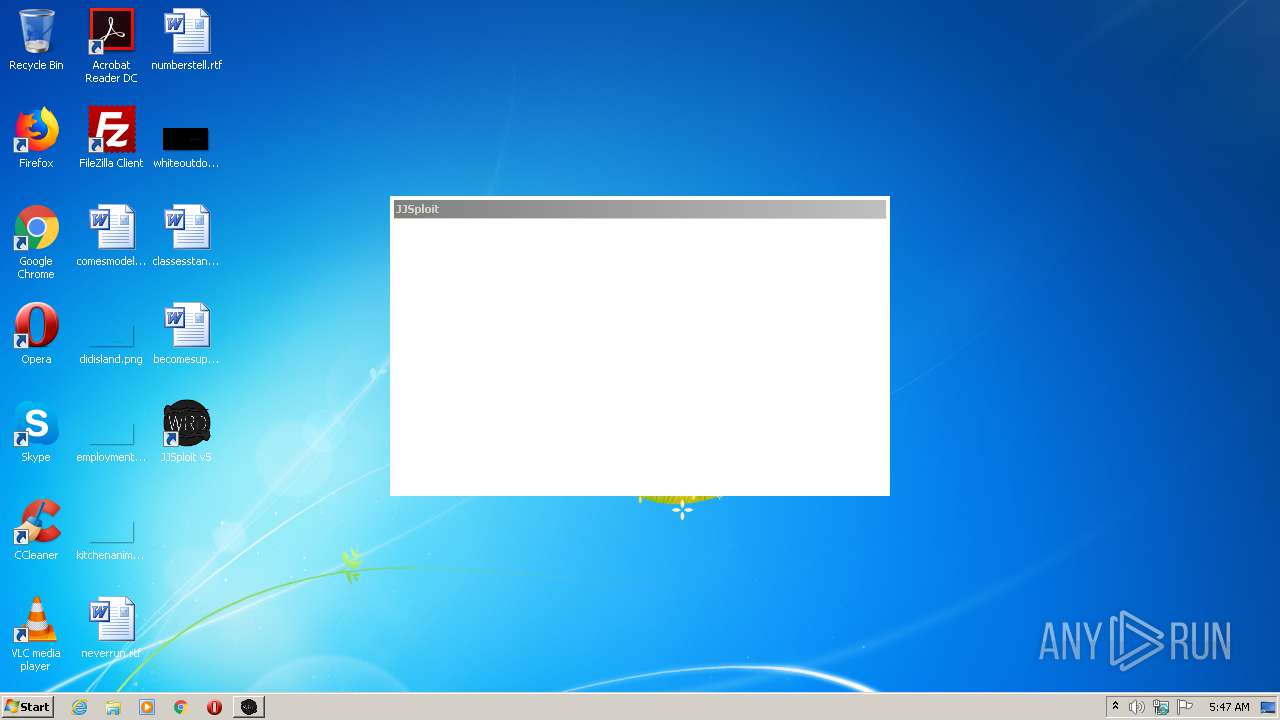
MALICIOUS
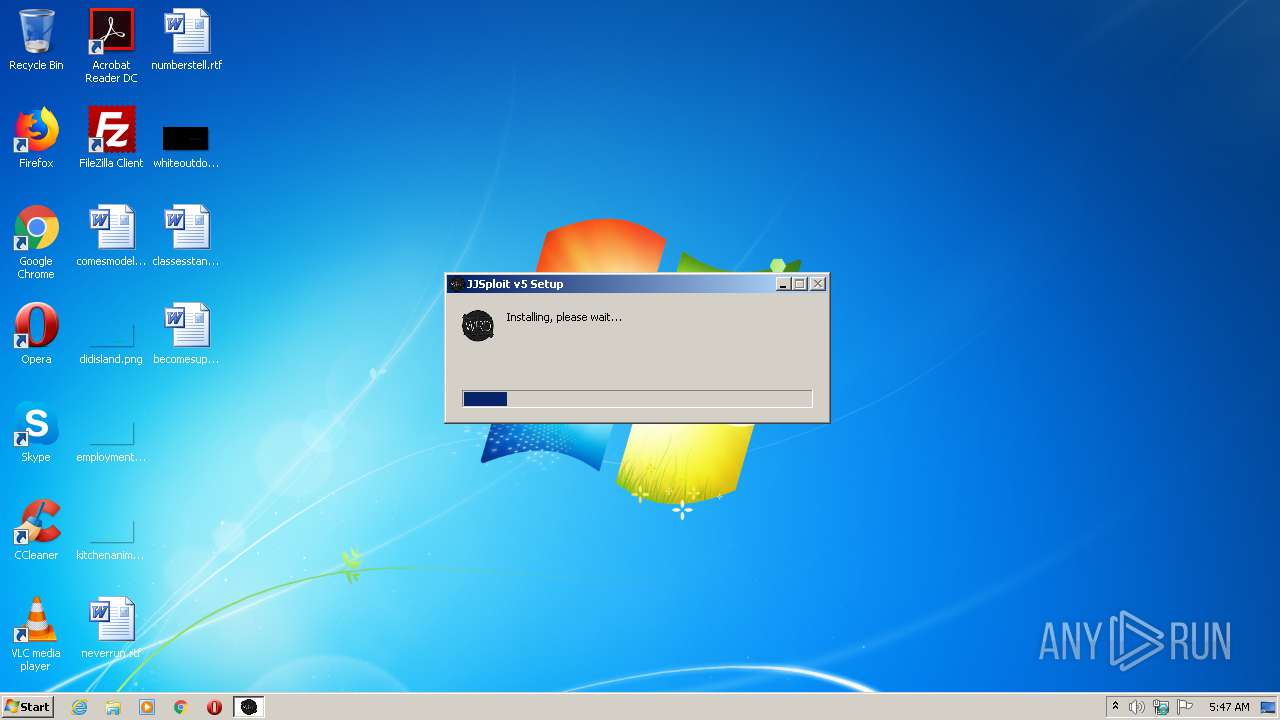
Application was dropped or rewritten from another process
- JJSploit_v5_Setup_5.3.4.exe (PID: 1688)
Loads dropped or rewritten executable
- JJSploit_v5_Setup_5.3.4.exe (PID: 1688)
- JJSploit v5.exe (PID: 3852)
- JJSploit v5.exe (PID: 1800)
- JJSploit v5.exe (PID: 2096)
SUSPICIOUS
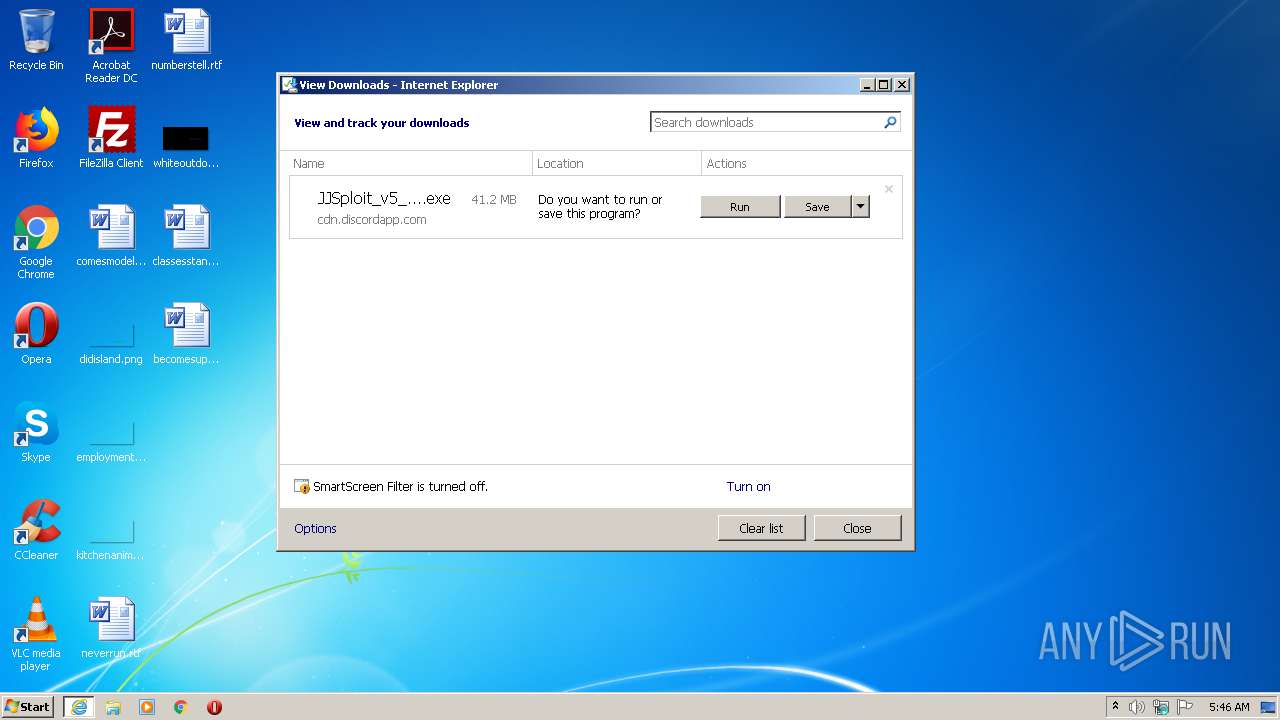
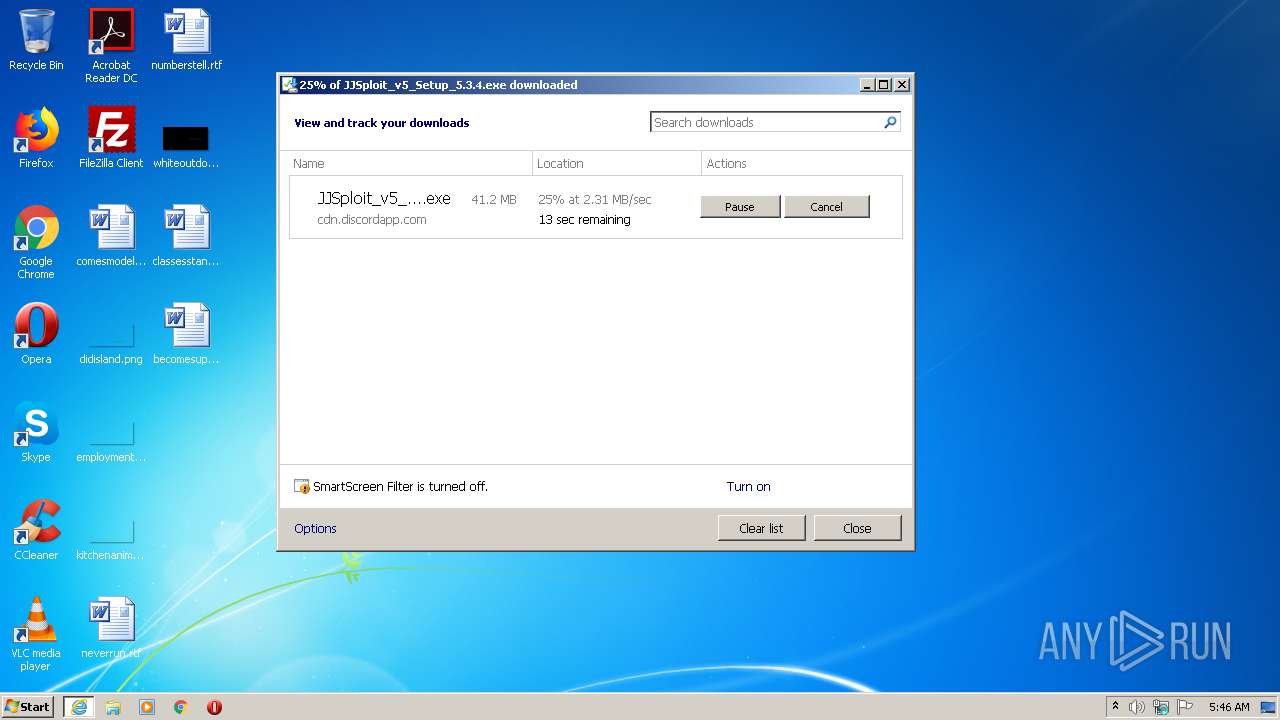
Executable content was dropped or overwritten
- iexplore.exe (PID: 3960)
- JJSploit_v5_Setup_5.3.4.exe (PID: 1688)
- JJSploit v5.exe (PID: 3852)
Creates files in the user directory
- JJSploit_v5_Setup_5.3.4.exe (PID: 1688)
- JJSploit v5.exe (PID: 3852)
Drops a file that was compiled in debug mode
- JJSploit_v5_Setup_5.3.4.exe (PID: 1688)
- JJSploit v5.exe (PID: 3852)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.3.4.exe (PID: 1688)
Drops a file with too old compile date
- JJSploit_v5_Setup_5.3.4.exe (PID: 1688)
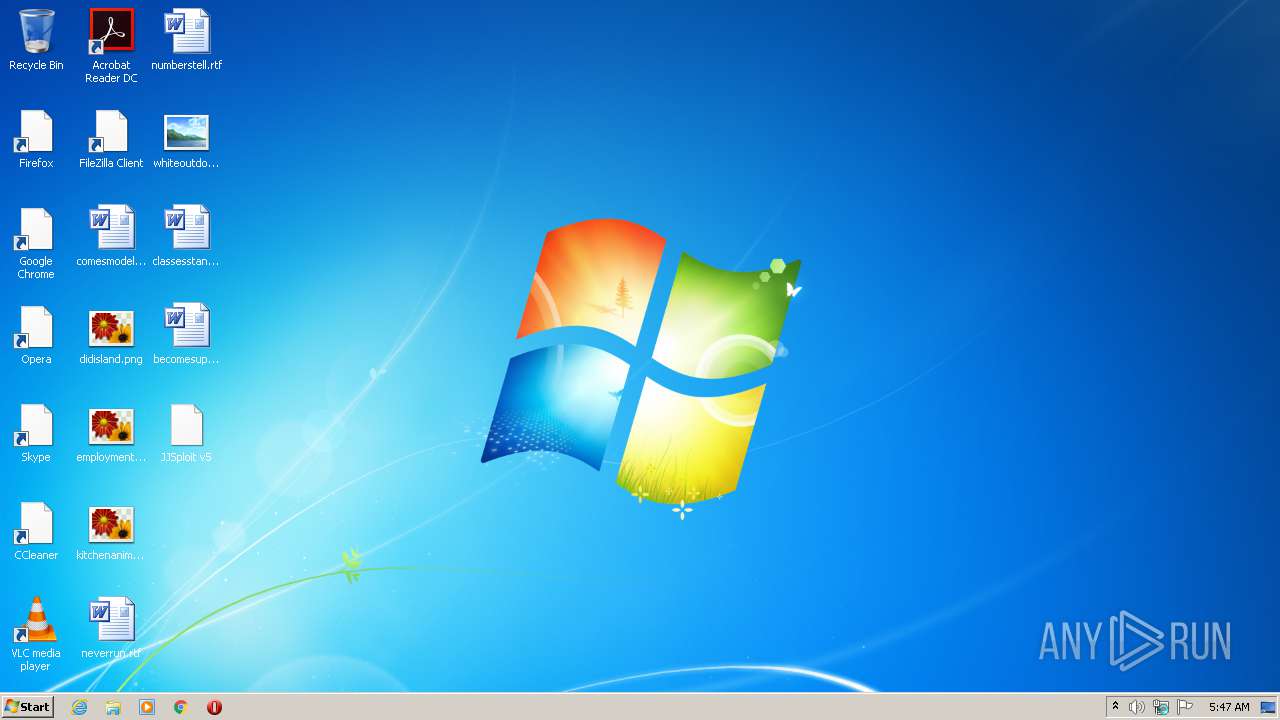
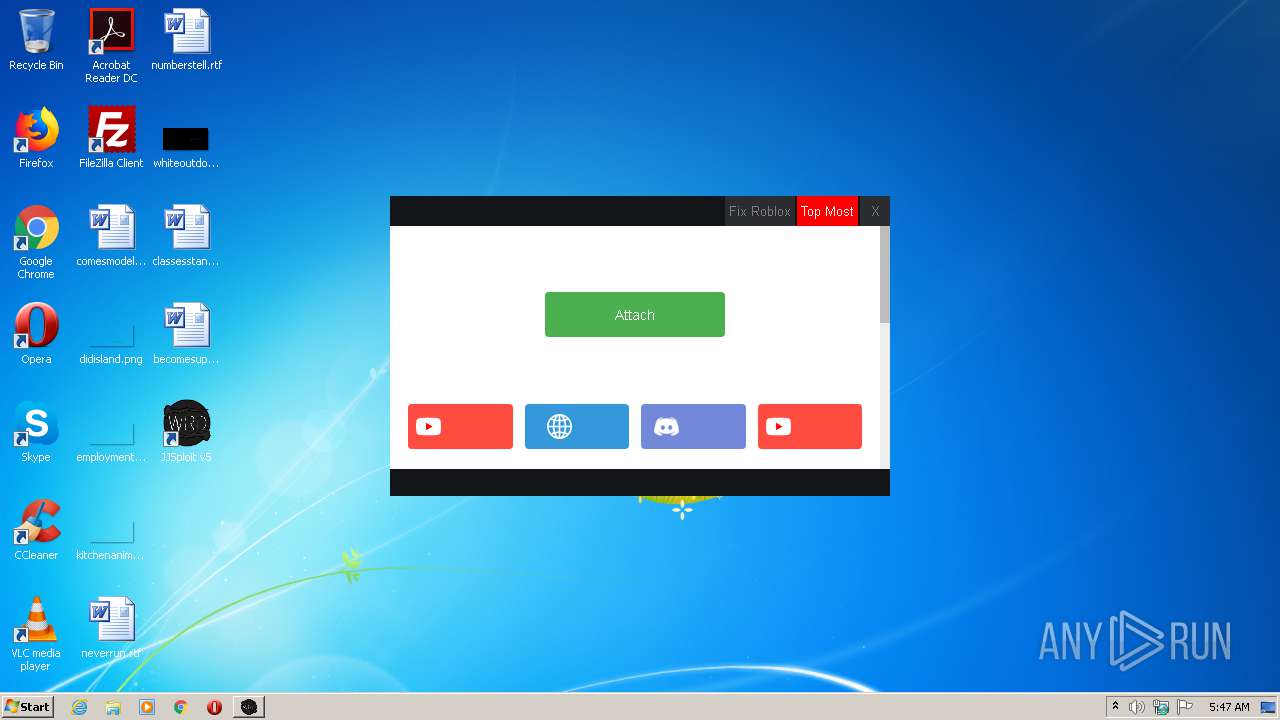
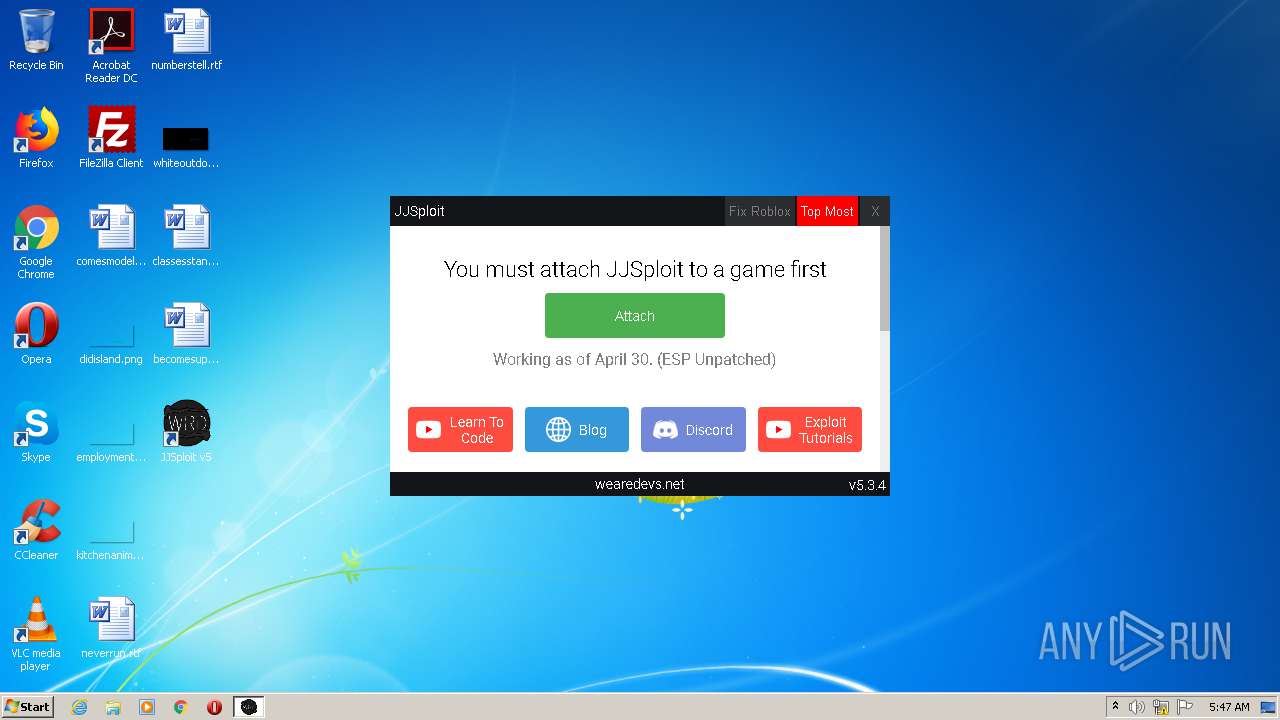
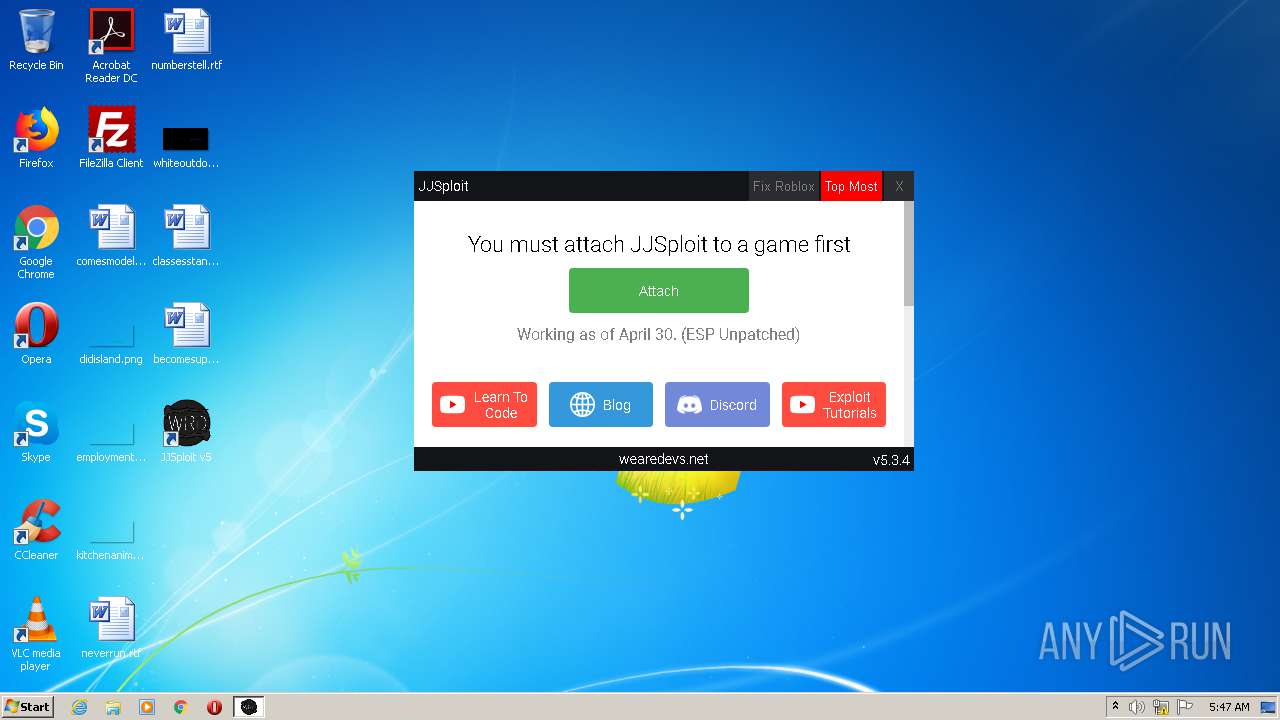
Application launched itself
- JJSploit v5.exe (PID: 3852)
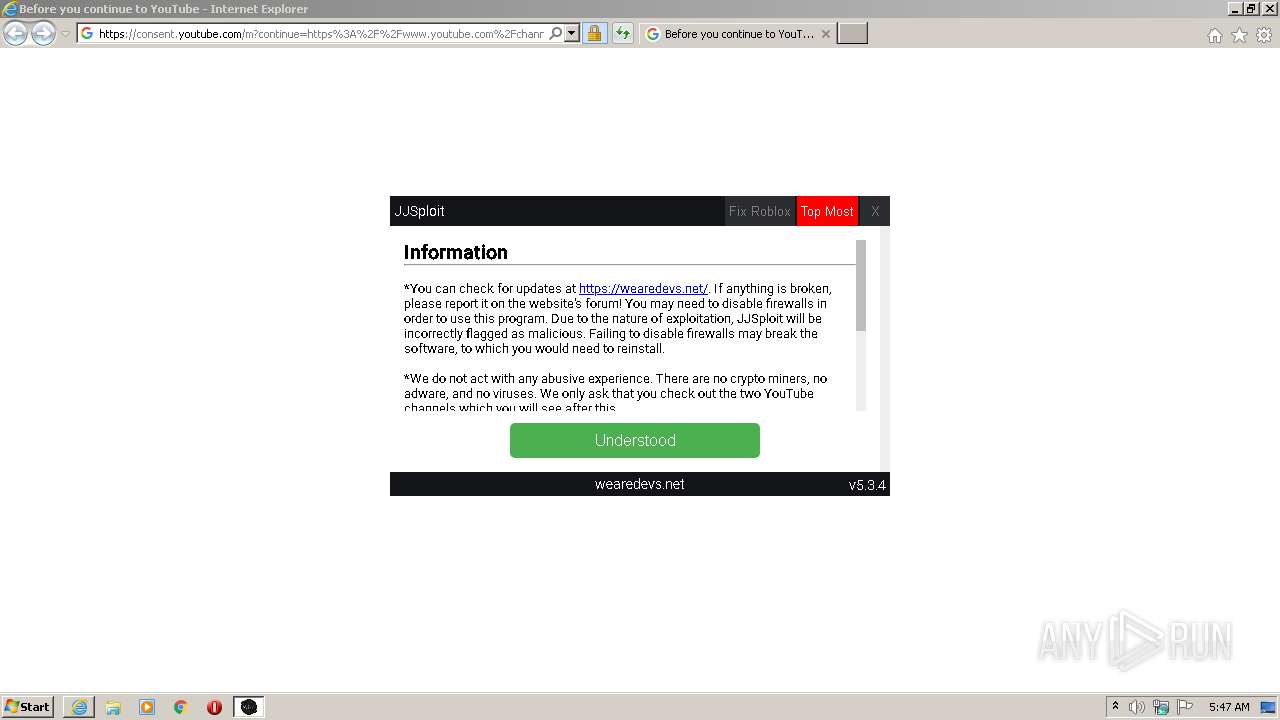
Starts Internet Explorer
- JJSploit v5.exe (PID: 3852)
Drops a file with a compile date too recent
- JJSploit v5.exe (PID: 3852)
INFO
Changes internet zones settings
- iexplore.exe (PID: 992)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 3232)
Creates files in the user directory
- iexplore.exe (PID: 3960)
- opera.exe (PID: 2340)
- iexplore.exe (PID: 924)
Reads settings of System Certificates
- iexplore.exe (PID: 3960)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 924)
Application launched itself
- iexplore.exe (PID: 992)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 3232)
Modifies the phishing filter of IE
- iexplore.exe (PID: 992)
Reads the hosts file
- JJSploit v5.exe (PID: 3852)
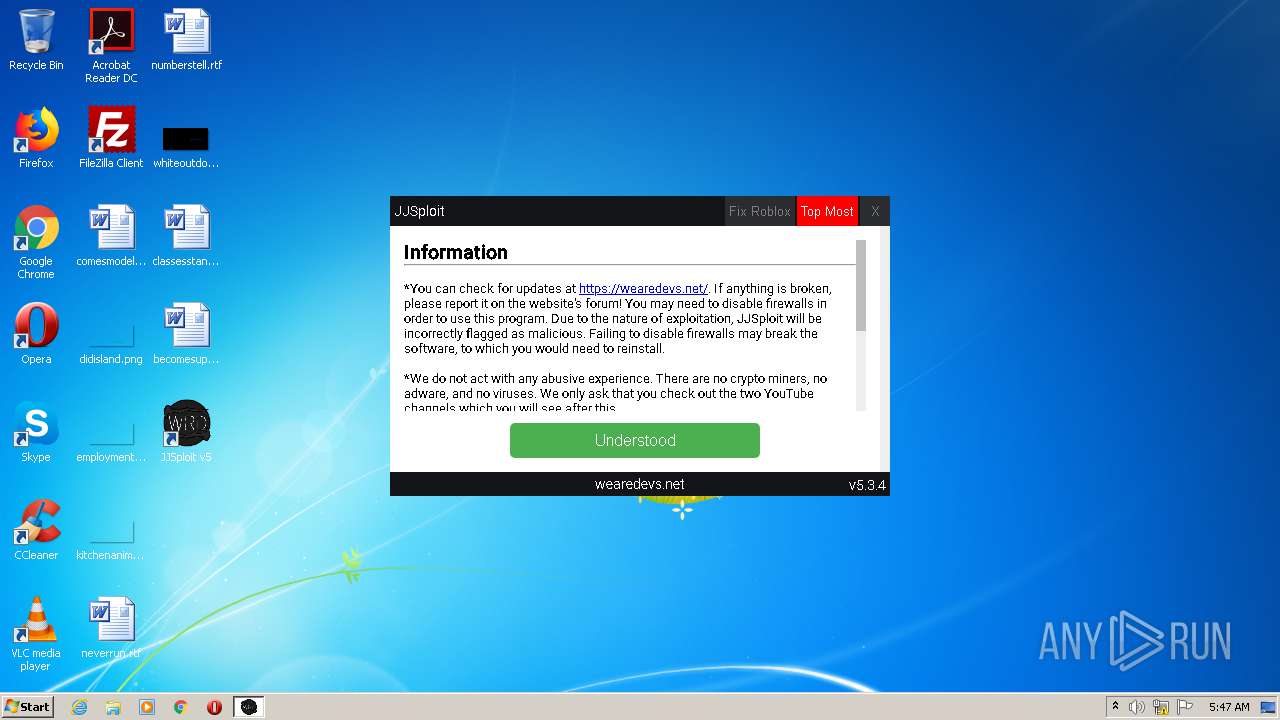
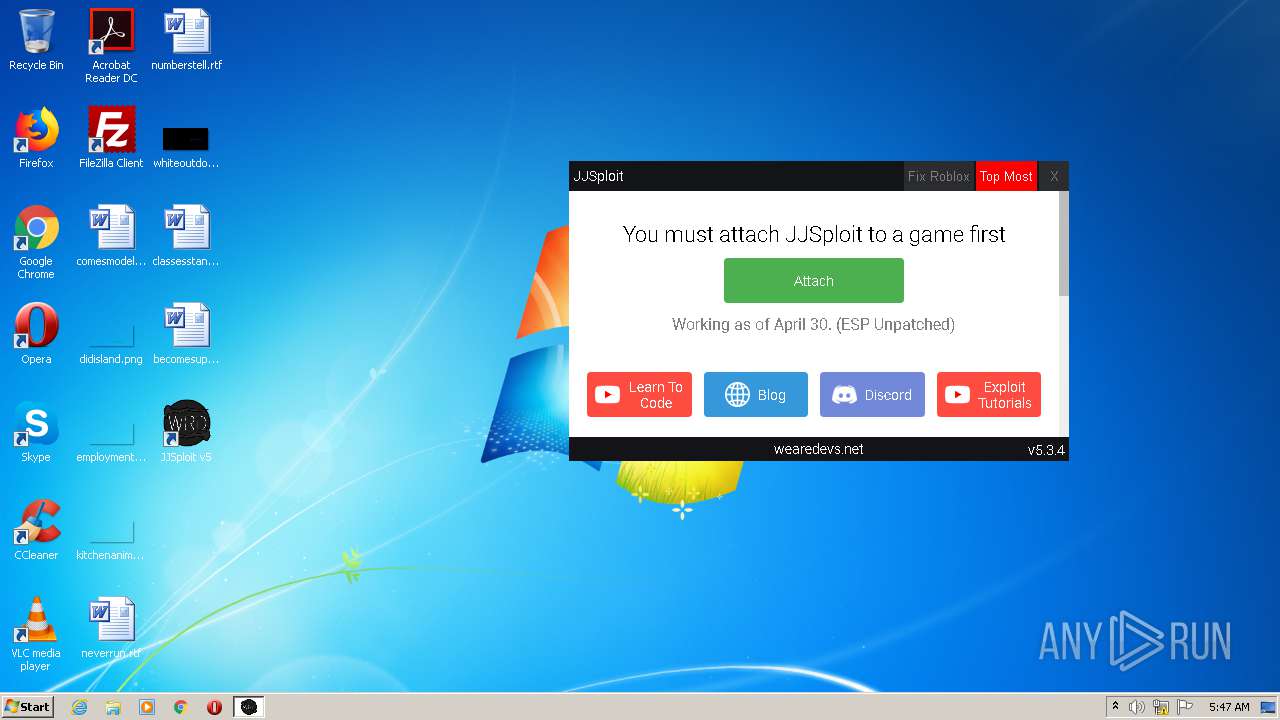
Manual execution by user
- JJSploit v5.exe (PID: 3852)
- opera.exe (PID: 2340)
Reads internet explorer settings
- iexplore.exe (PID: 924)
Changes settings of System certificates
- iexplore.exe (PID: 2632)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
12
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2632 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cdn.discordapp.com/attachments/423644248156667951/783714727318650881/JJSploit_v5_Setup_5.3.4.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1236 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3067794851154464157 --mojo-platform-channel-handle=2432 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 1688 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\JJSploit_v5_Setup_5.3.4.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\JJSploit_v5_Setup_5.3.4.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7548639449721175435 --mojo-platform-channel-handle=1144 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=renderer --disable-features=SpareRendererForSitePerProcess --service-pipe-token=10578085254930404231 --lang=en-US --app-path="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar\build\preload.js" --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10578085254930404231 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1588 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
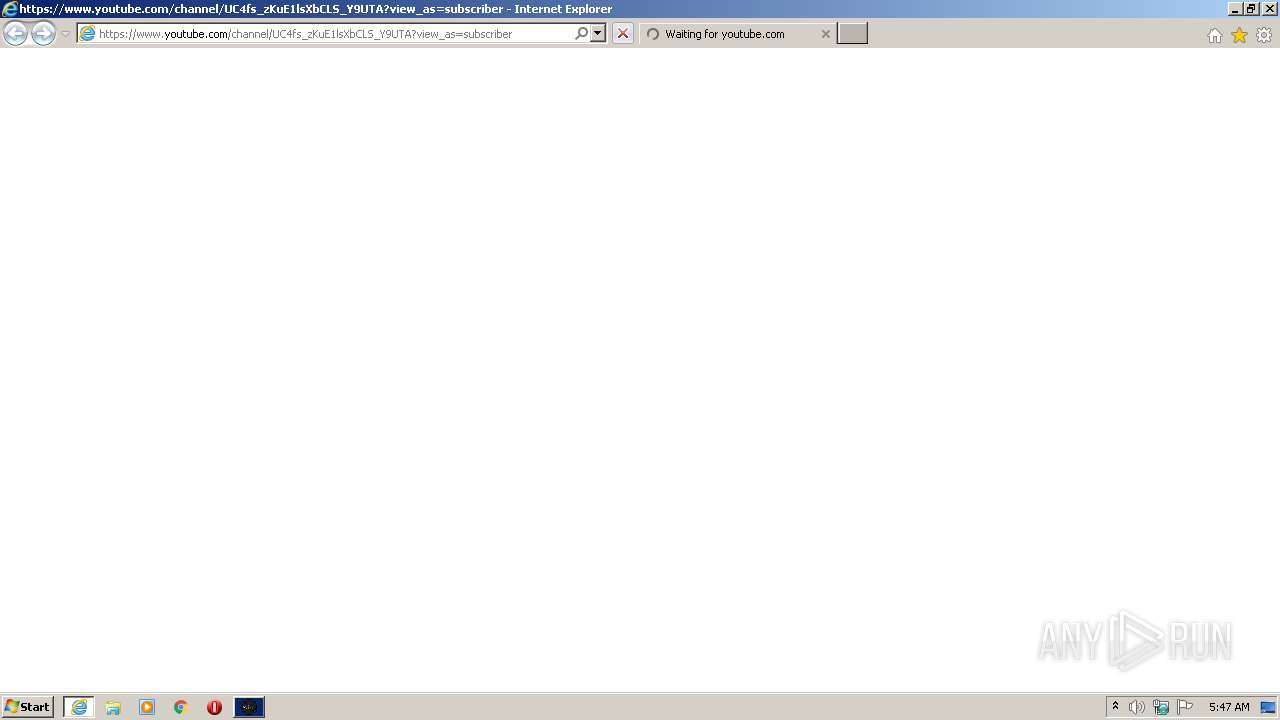
| 2632 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/channel/UC4fs_zKuE1lsXbCLS_Y9UTA?view_as=subscriber | C:\Program Files\Internet Explorer\iexplore.exe | JJSploit v5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3232 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/channel/UC3YNONzSHPW12m3AT48fMHw?view_as=subscriber | C:\Program Files\Internet Explorer\iexplore.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3840 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3232 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 218
Read events
1 963
Write events
249
Delete events
6
Modification events
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 959412742 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30883598 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
19
Suspicious files
74
Text files
31
Unknown types
88
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEA6.tmp | — | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEA7.tmp | — | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\JJSploit_v5_Setup_5.3.4[1].exe | — | |
MD5:— | SHA256:— | |||
| 992 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6040232C4C9CEC59.TMP | — | |
MD5:— | SHA256:— | |||
| 992 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\JJSploit_v5_Setup_5.3.4.exe.0dyke4j.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 992 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\JJSploit_v5_Setup_5.3.4.exe | — | |
MD5:— | SHA256:— | |||
| 1688 | JJSploit_v5_Setup_5.3.4.exe | C:\Users\admin\AppData\Local\Temp\nsx8406.tmp\app-32.7z | — | |
MD5:— | SHA256:— | |||
| 1688 | JJSploit_v5_Setup_5.3.4.exe | C:\Users\admin\AppData\Local\Programs\jjsploitv5\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RMZOGKPG.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
53
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEB4LVgjgb8jnCQAAAABiFe8%3D | US | der | 471 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCU0iXXU3ZZIgkAAAAAYhal | US | der | 472 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEB4LVgjgb8jnCQAAAABiFe8%3D | US | der | 471 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCkR96bLPCPfQoAAAAAw0m5 | US | der | 472 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCkR96bLPCPfQoAAAAAw0m5 | US | der | 472 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCkR96bLPCPfQoAAAAAw0m5 | US | der | 472 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCU0iXXU3ZZIgkAAAAAYhal | US | der | 472 b | whitelisted |
2632 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC6JAYZPXGY0QkAAAAAYhb2 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3960 | iexplore.exe | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
3960 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3852 | JJSploit v5.exe | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3852 | JJSploit v5.exe | 142.250.184.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 173.194.220.101:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3852 | JJSploit v5.exe | 173.194.220.101:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3852 | JJSploit v5.exe | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
— | — | 172.67.71.2:443 | cdn.wearedevs.net | — | US | suspicious |
924 | iexplore.exe | 142.250.185.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
3840 | iexplore.exe | 142.250.185.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.youtube.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
consent.youtube.com |
| whitelisted |
www.gstatic.com |
| whitelisted |