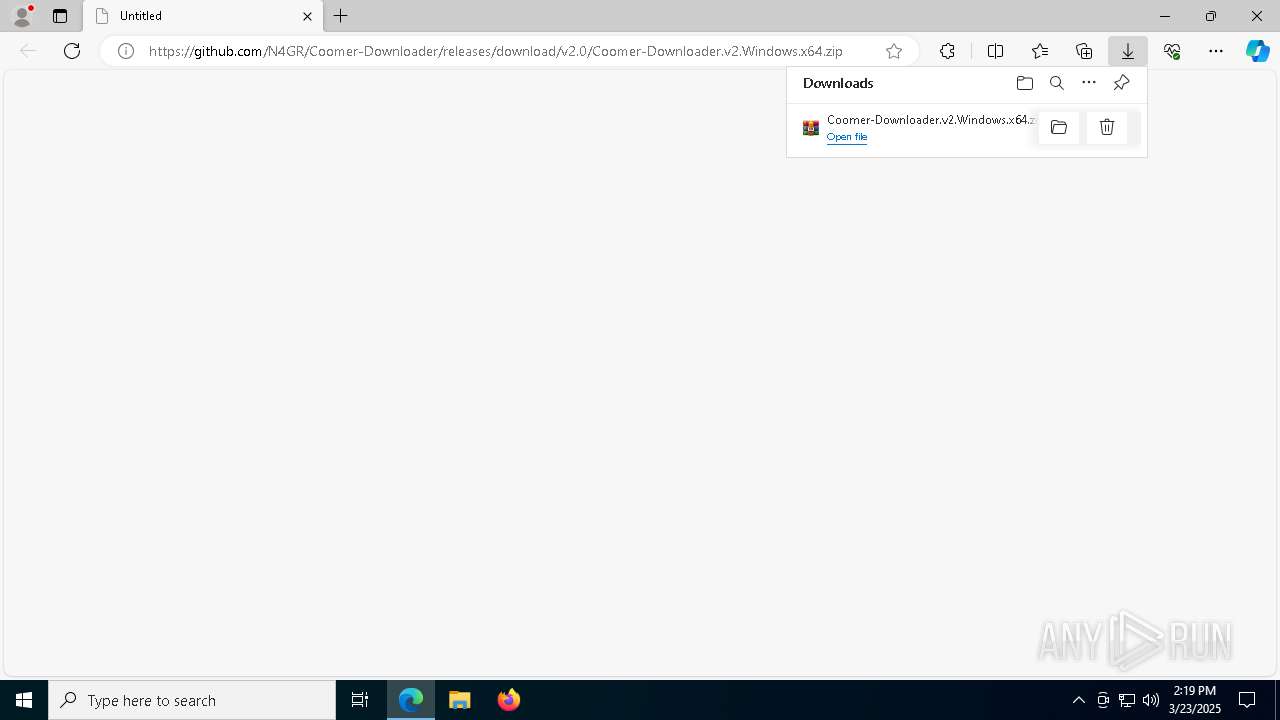
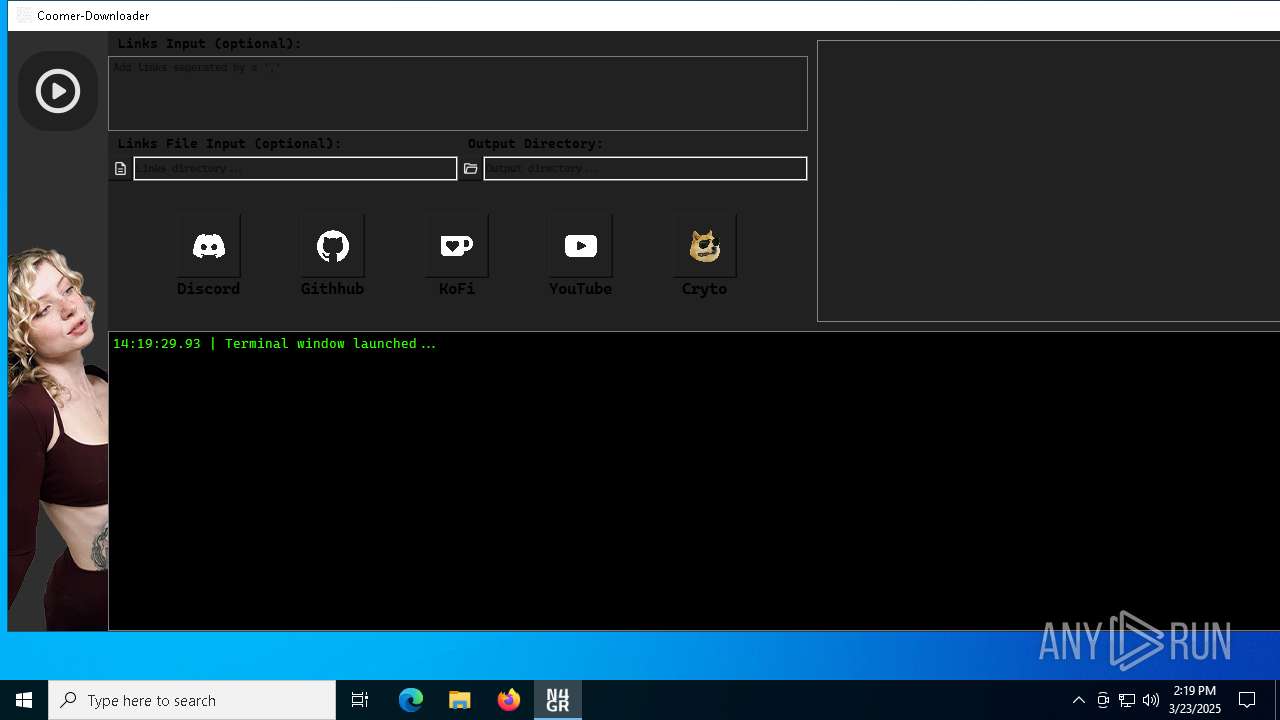
| URL: | https://github.com/N4GR/Coomer-Downloader/releases/download/v2.0/Coomer-Downloader.v2.Windows.x64.zip |
| Full analysis: | https://app.any.run/tasks/fd6d280d-77a7-4df3-a201-1cafbc0ac652 |
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2025, 14:18:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FF967C3CAA87F17E45B0E13669631D75 |
| SHA1: | 3666662609C1F8AF349F51897F3ACEE14E3C3EAA |
| SHA256: | 6B54CBDCBD815C37BA36015D06A91353DA39797DB4DA14F55C5712E64EF036A0 |
| SSDEEP: | 3:N8tEdxp3EE2XBJAE2kCY9Tb3EE2XnXLyaJyMV:2u53toJArsb3tsyaJfV |
MALICIOUS
No malicious indicators.SUSPICIOUS
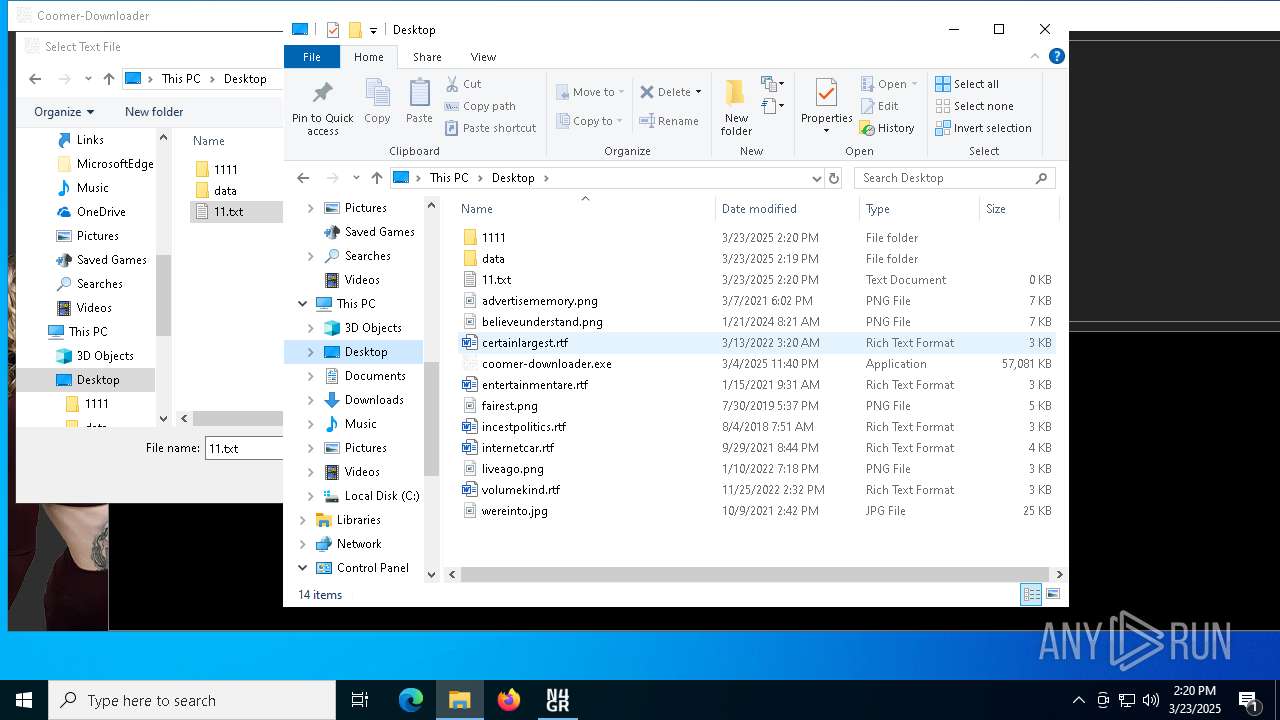
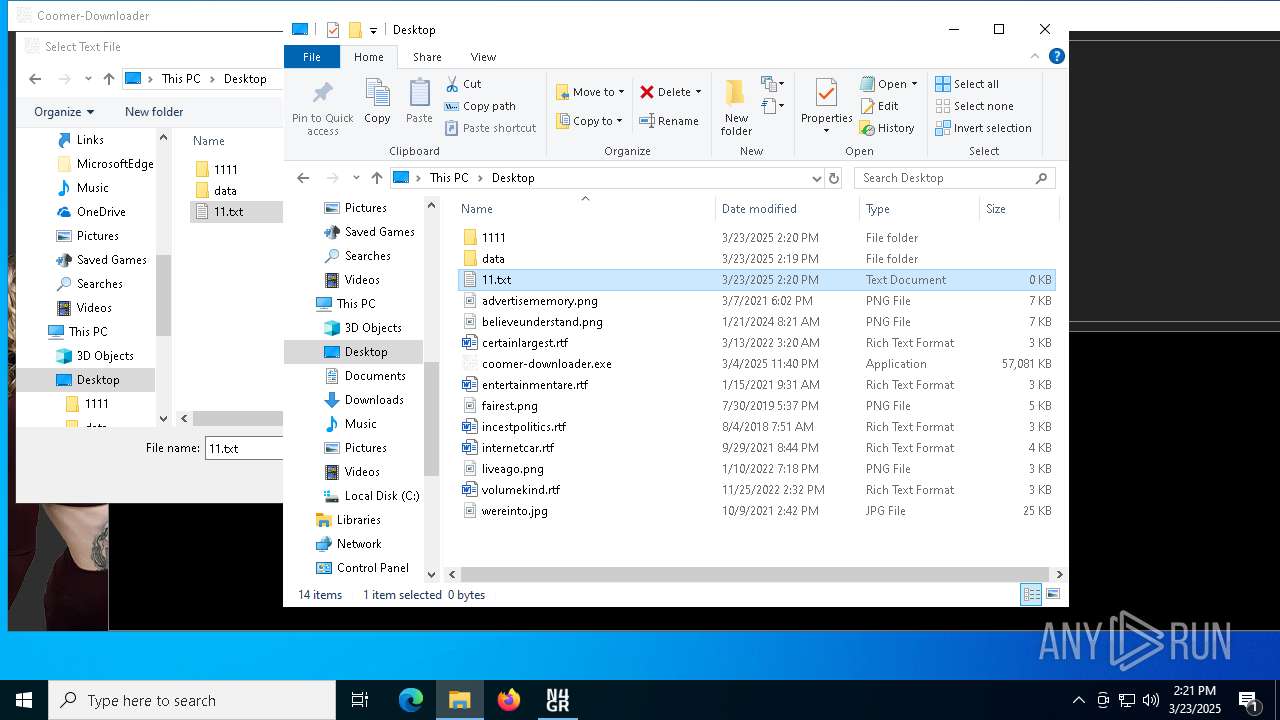
Process drops legitimate windows executable
- coomer-downloader.exe (PID: 2108)
Executable content was dropped or overwritten
- coomer-downloader.exe (PID: 2108)
The process drops C-runtime libraries
- coomer-downloader.exe (PID: 2108)
Process drops python dynamic module
- coomer-downloader.exe (PID: 2108)
Loads Python modules
- coomer-downloader.exe (PID: 7448)
Application launched itself
- coomer-downloader.exe (PID: 2108)
There is functionality for taking screenshot (YARA)
- coomer-downloader.exe (PID: 2108)
Reads security settings of Internet Explorer
- coomer-downloader.exe (PID: 7448)
- ShellExperienceHost.exe (PID: 2552)
INFO
Application launched itself
- msedge.exe (PID: 7204)
- msedge.exe (PID: 920)
Reads the computer name
- identity_helper.exe (PID: 8284)
- identity_helper.exe (PID: 1300)
- coomer-downloader.exe (PID: 2108)
- coomer-downloader.exe (PID: 7448)
- ShellExperienceHost.exe (PID: 2552)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7204)
Checks supported languages
- identity_helper.exe (PID: 1300)
- identity_helper.exe (PID: 8284)
- coomer-downloader.exe (PID: 2108)
- coomer-downloader.exe (PID: 7448)
- ShellExperienceHost.exe (PID: 2552)
Reads Environment values
- identity_helper.exe (PID: 8284)
- identity_helper.exe (PID: 1300)
Autorun file from Downloads
- msedge.exe (PID: 9180)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 2960)
- BackgroundTransferHost.exe (PID: 7180)
- BackgroundTransferHost.exe (PID: 7612)
- BackgroundTransferHost.exe (PID: 7020)
- BackgroundTransferHost.exe (PID: 8312)
- notepad.exe (PID: 7584)
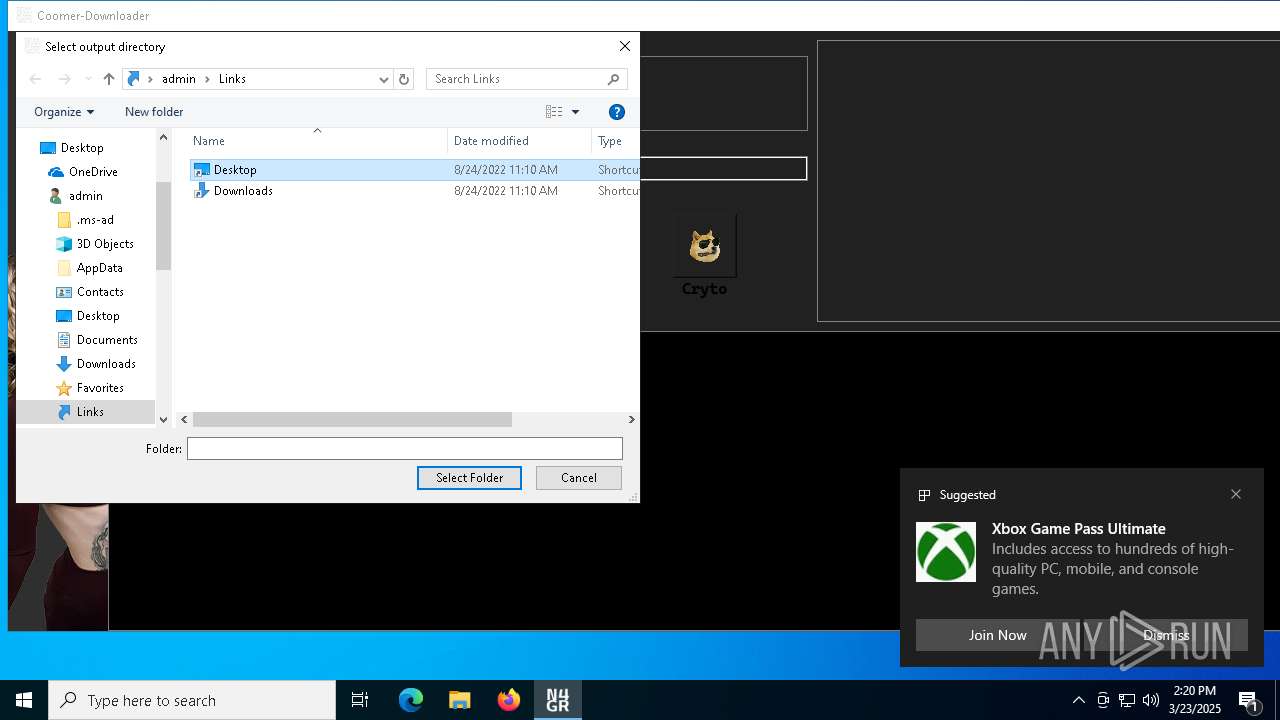
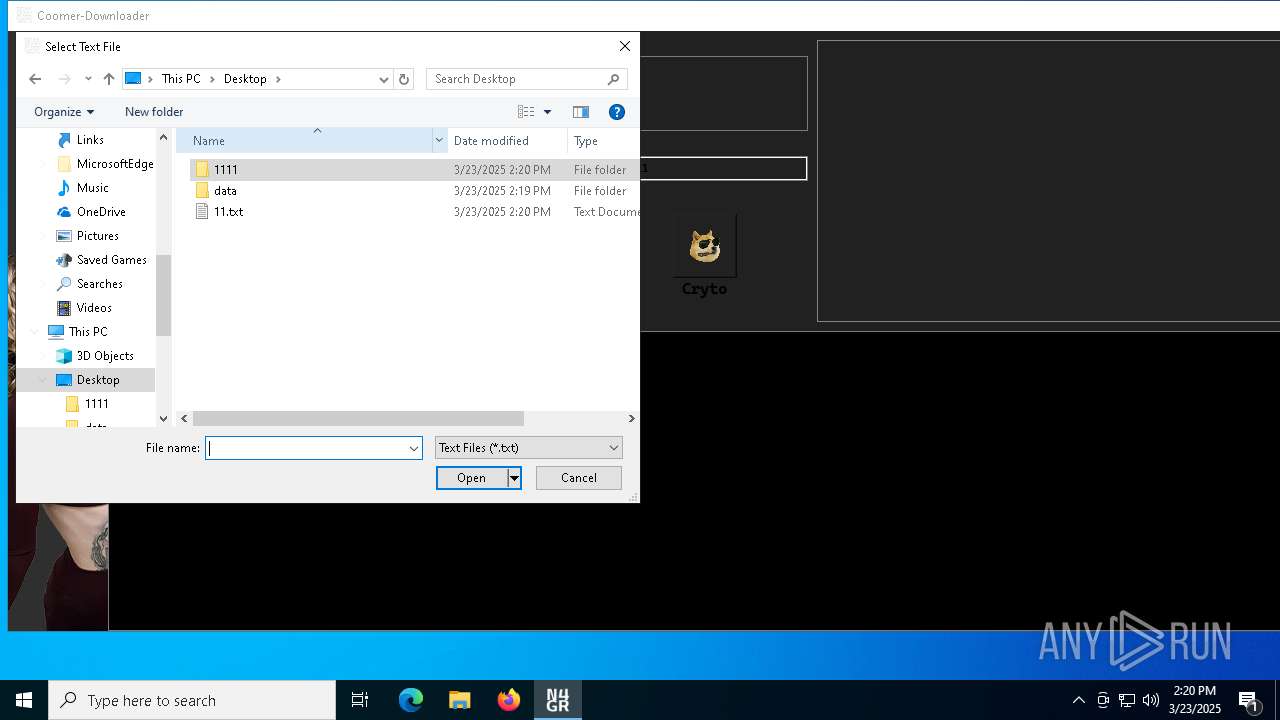
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7020)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7020)
- slui.exe (PID: 8412)
- slui.exe (PID: 9184)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7020)
- coomer-downloader.exe (PID: 7448)
- slui.exe (PID: 9184)
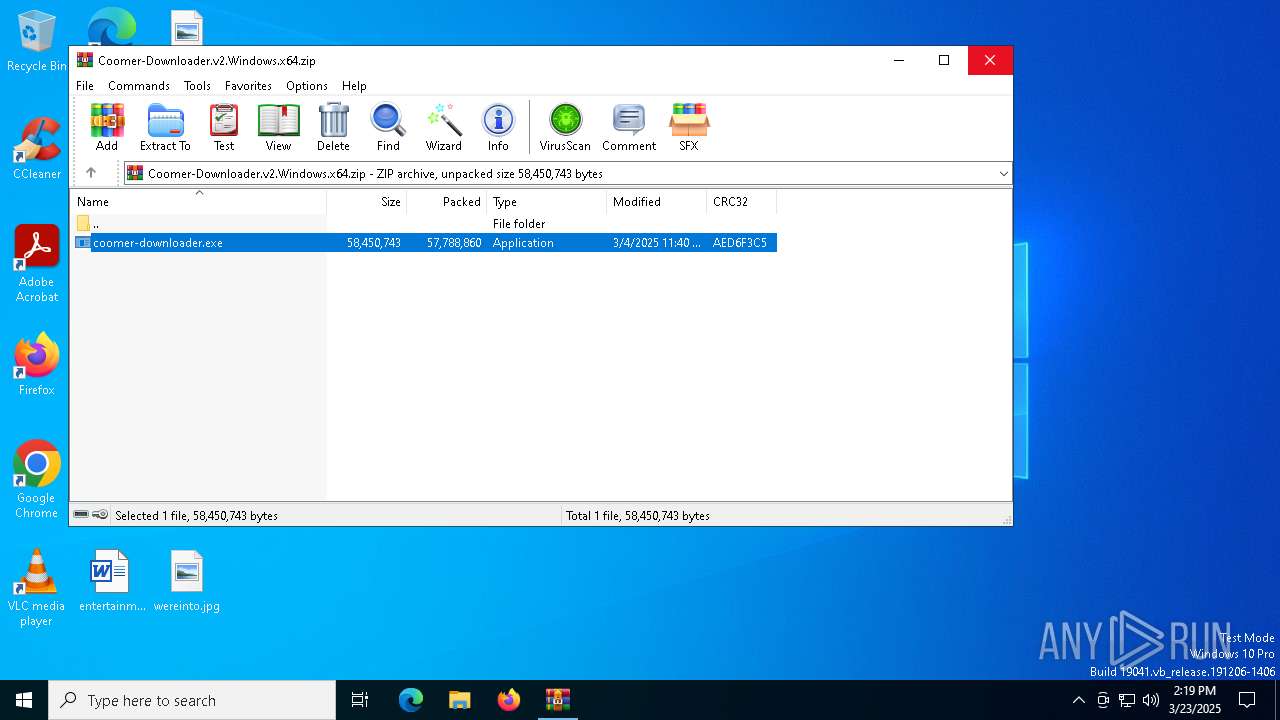
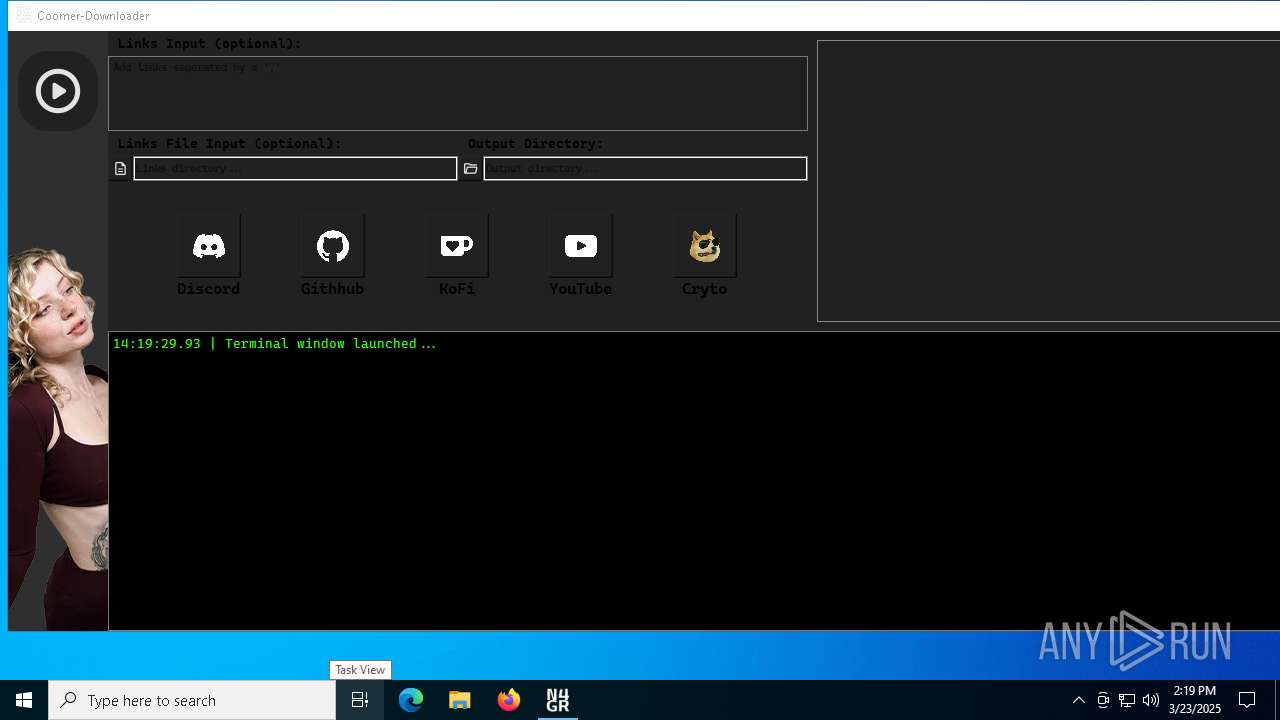
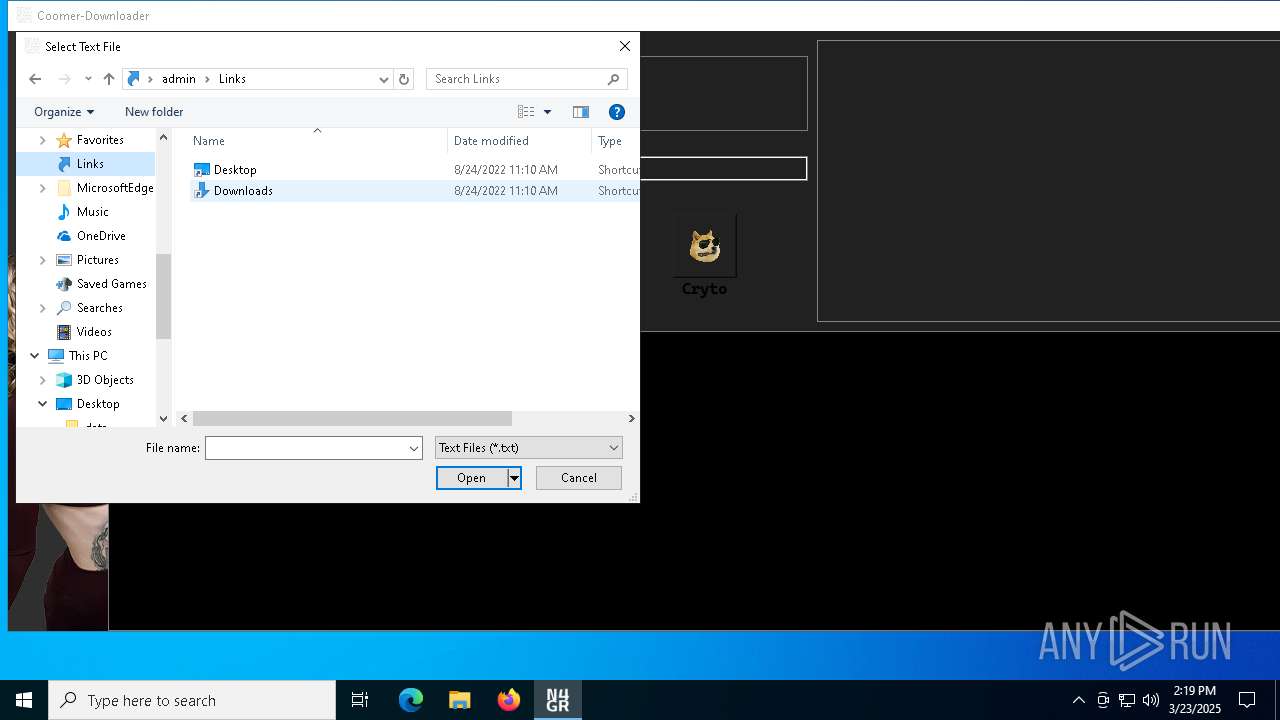
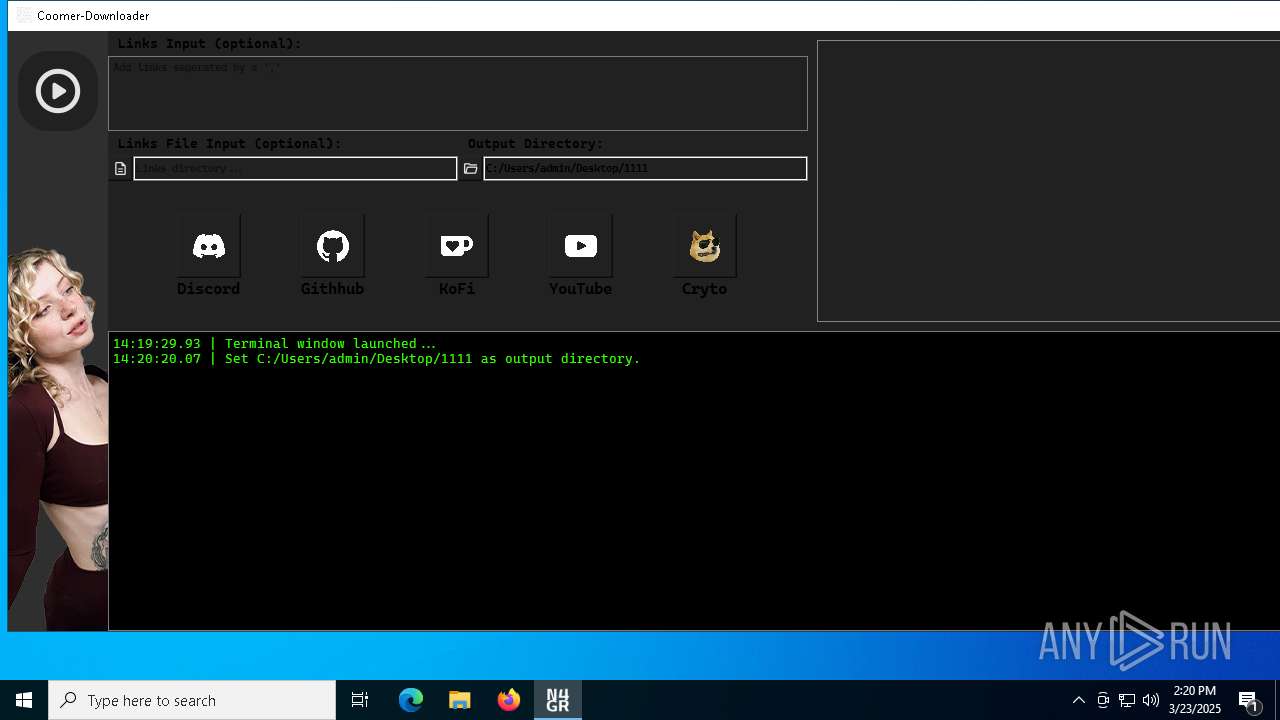
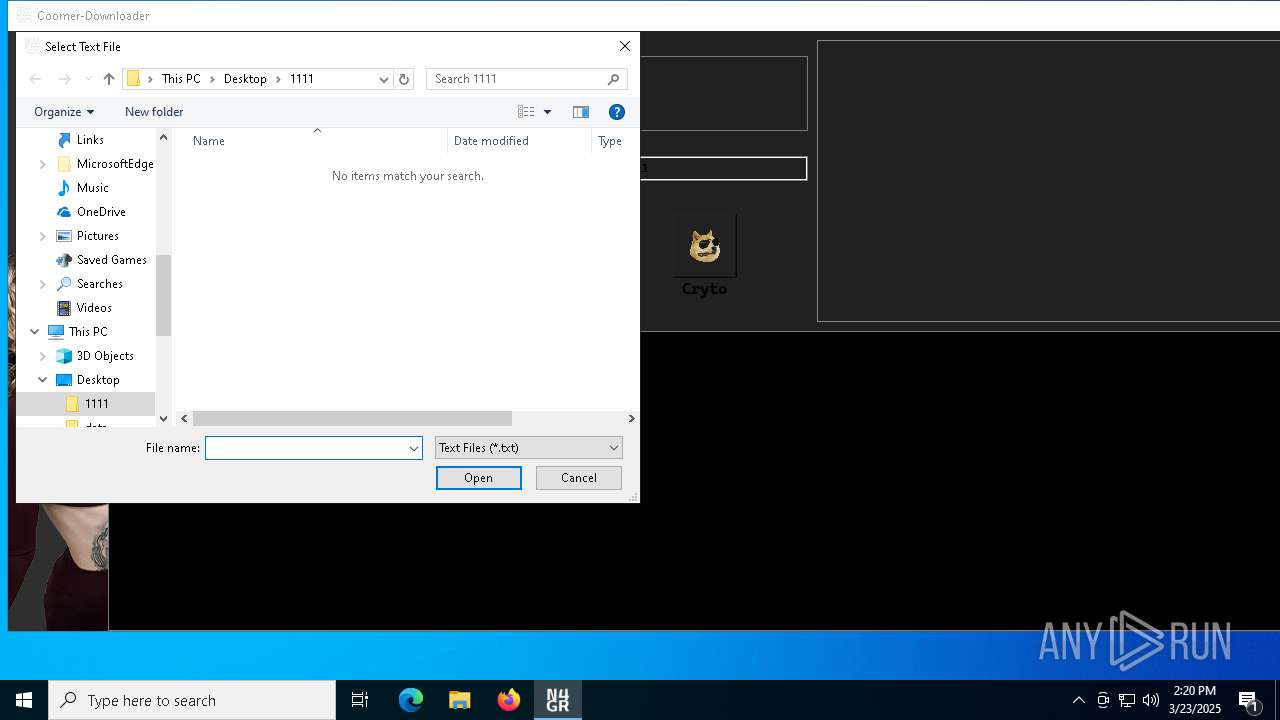
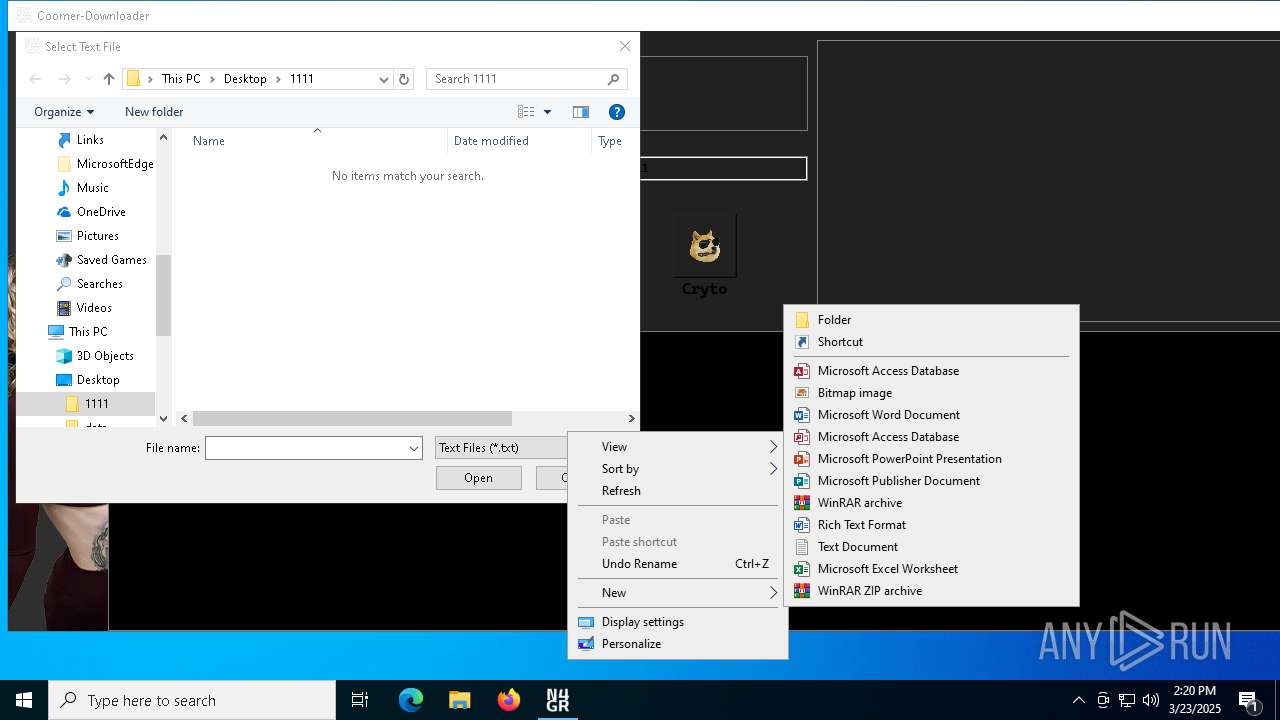
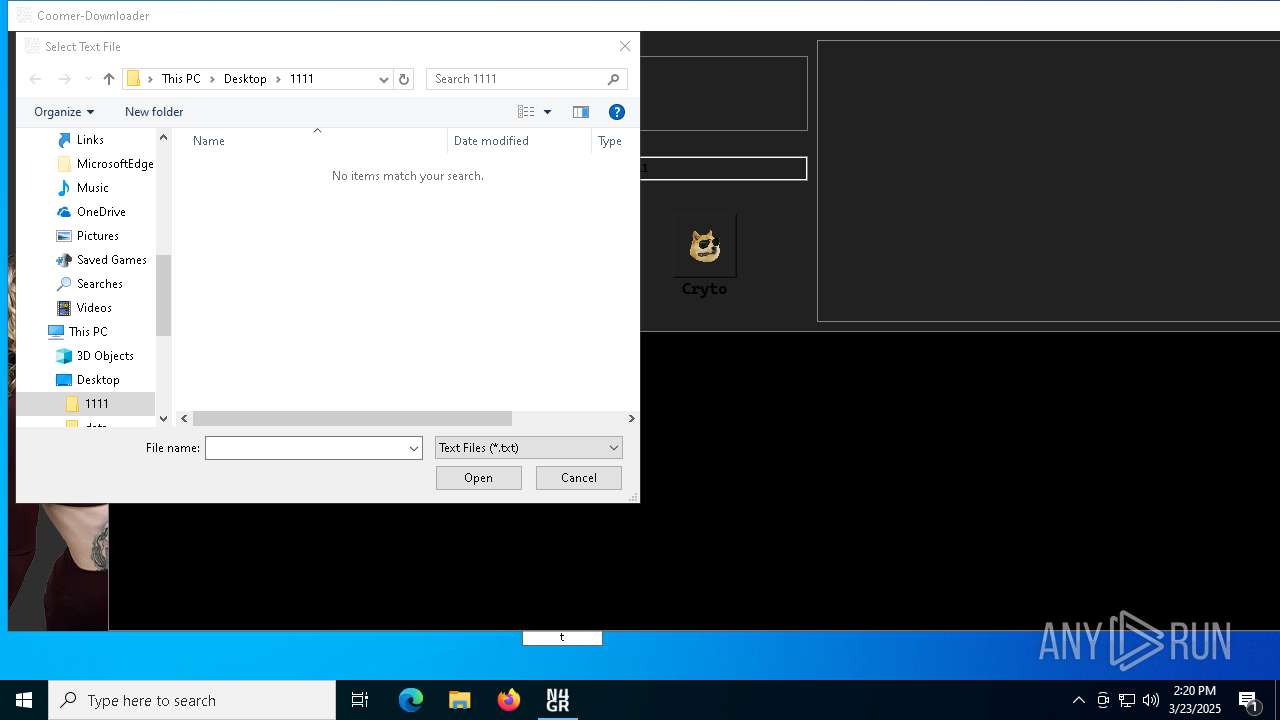
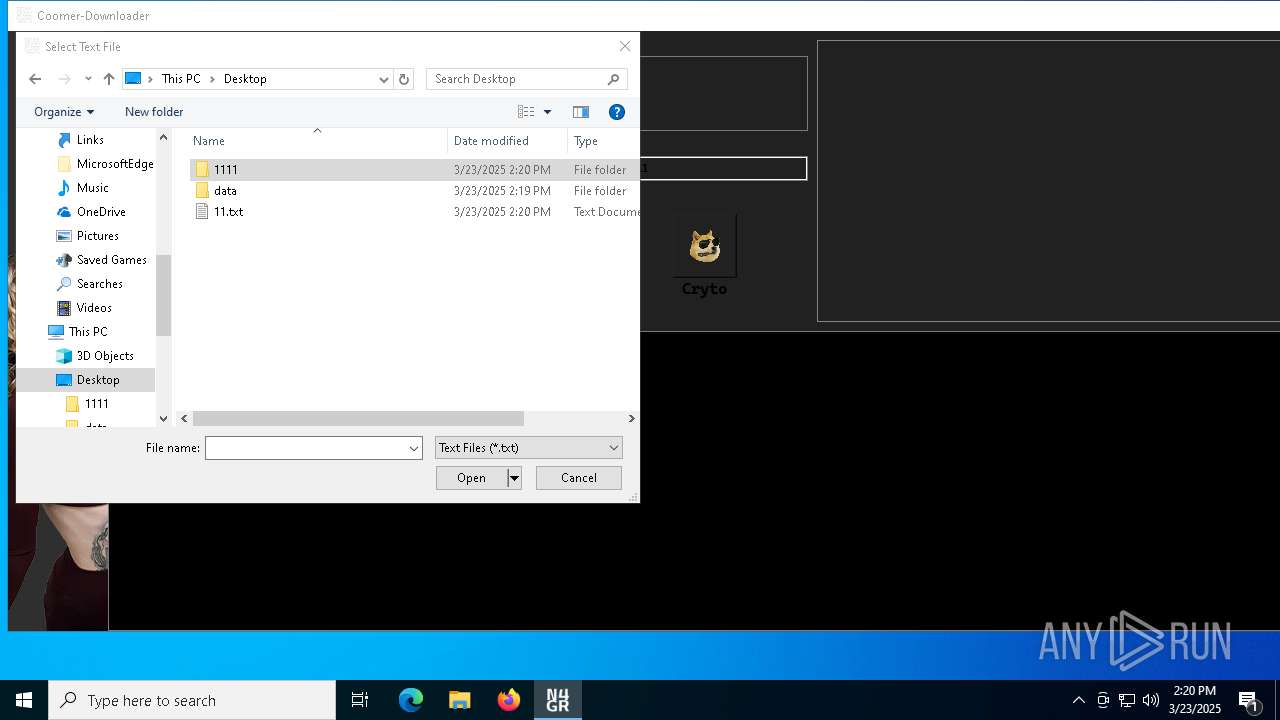
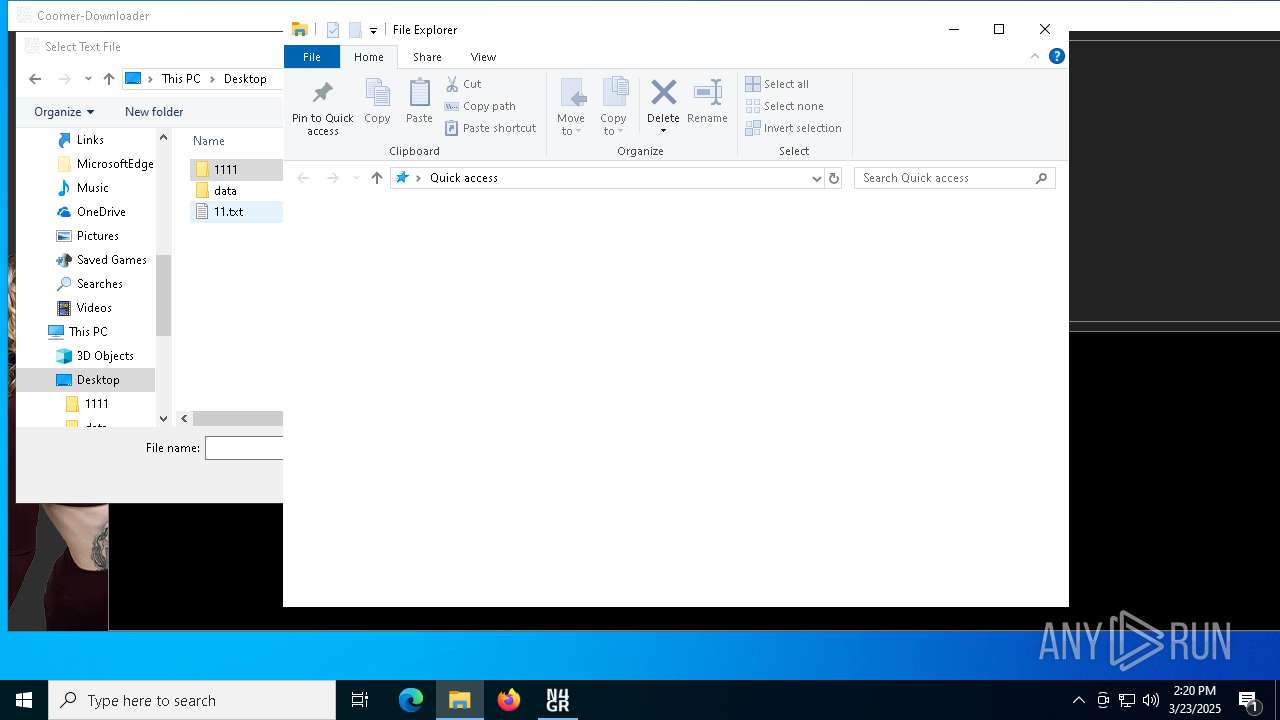
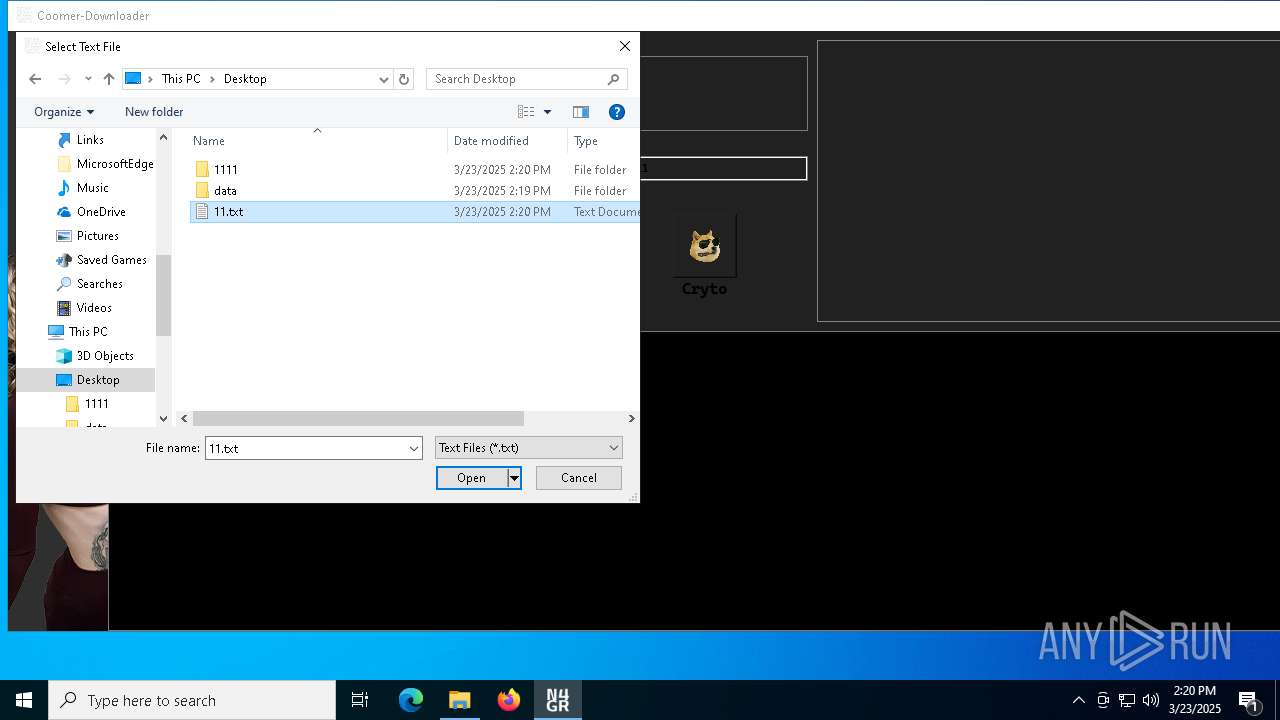
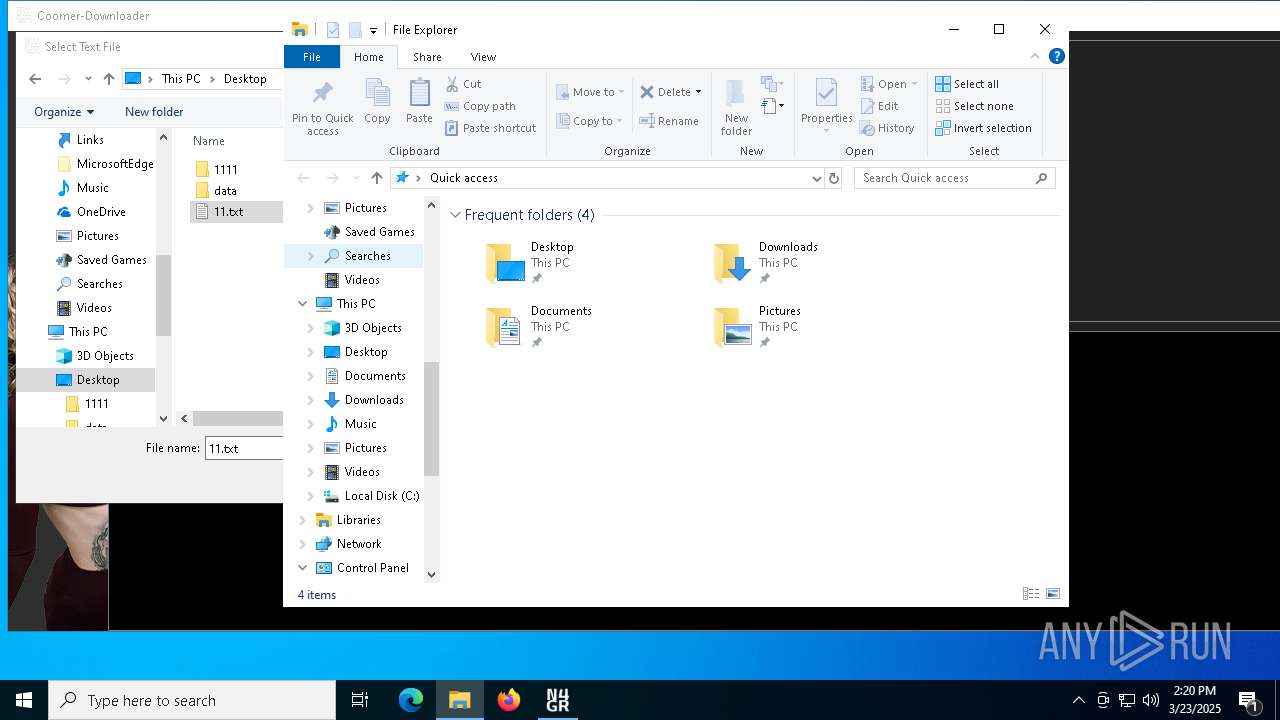
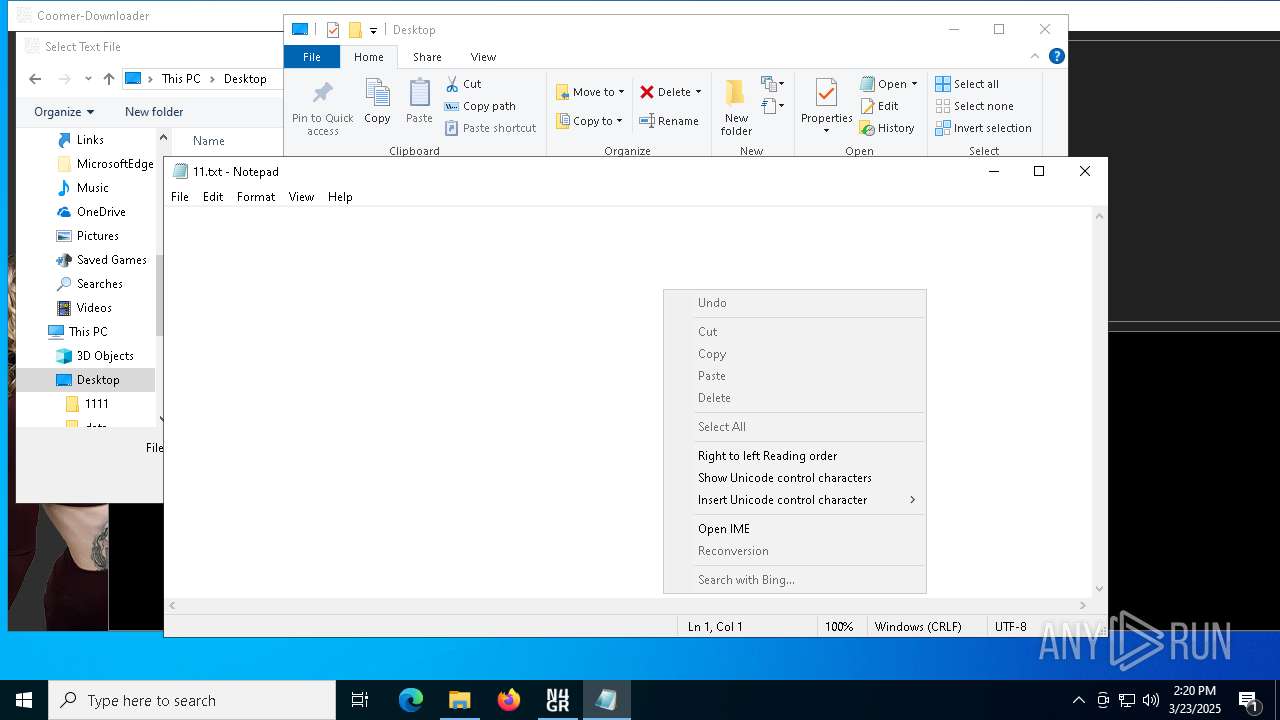
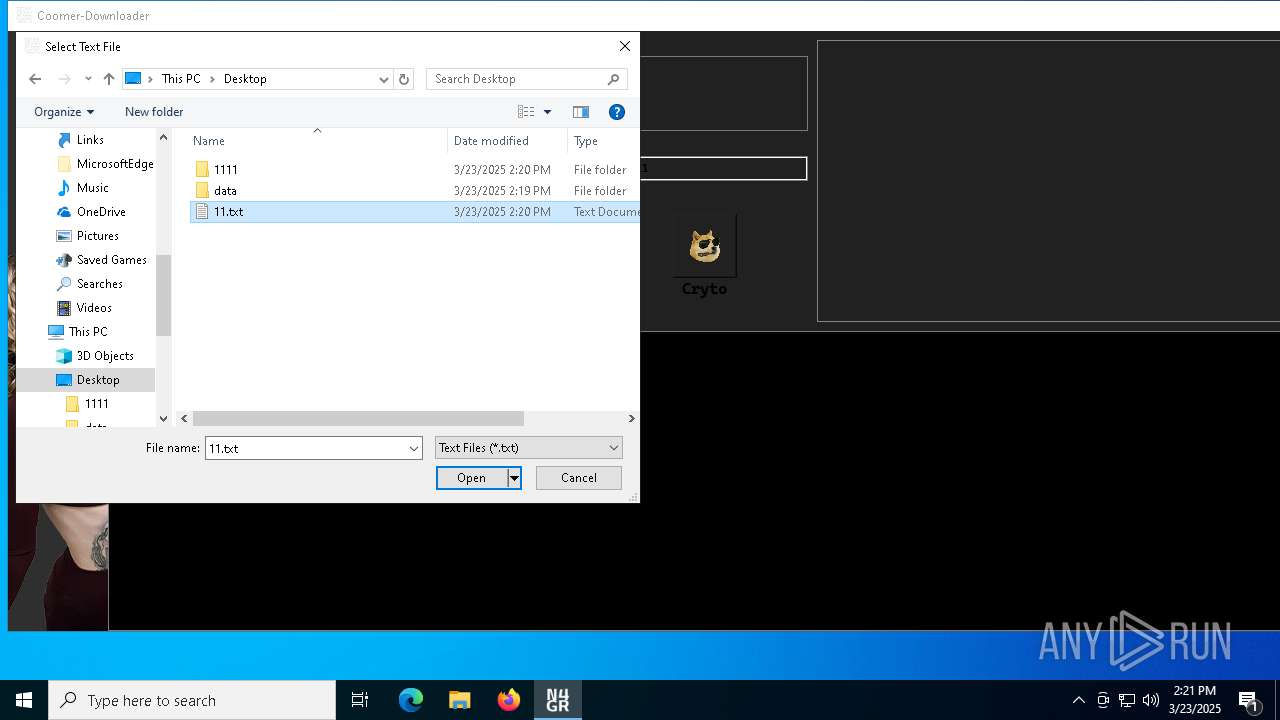
Manual execution by a user
- coomer-downloader.exe (PID: 2108)
- notepad.exe (PID: 7584)
Create files in a temporary directory
- coomer-downloader.exe (PID: 2108)
The sample compiled with english language support
- coomer-downloader.exe (PID: 2108)
PyInstaller has been detected (YARA)
- coomer-downloader.exe (PID: 2108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
195
Monitored processes
58
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5872 --field-trial-handle=2336,i,5103474070097200416,17623896491048528138,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2264 --field-trial-handle=2396,i,14737364073864895951,2099381090478791635,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2108 | "C:\Users\admin\Desktop\coomer-downloader.exe" | C:\Users\admin\Desktop\coomer-downloader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2552 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5320 --field-trial-handle=2396,i,14737364073864895951,2099381090478791635,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2960 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3020 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2264 --field-trial-handle=2396,i,14737364073864895951,2099381090478791635,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
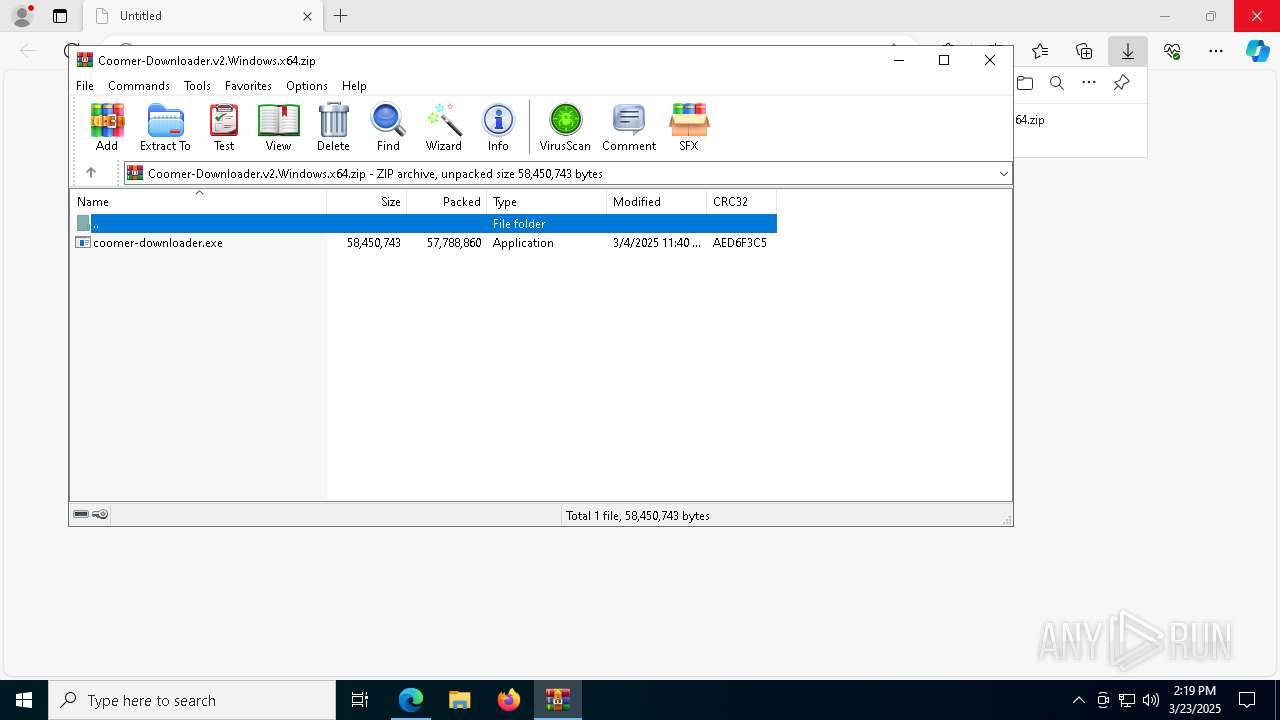
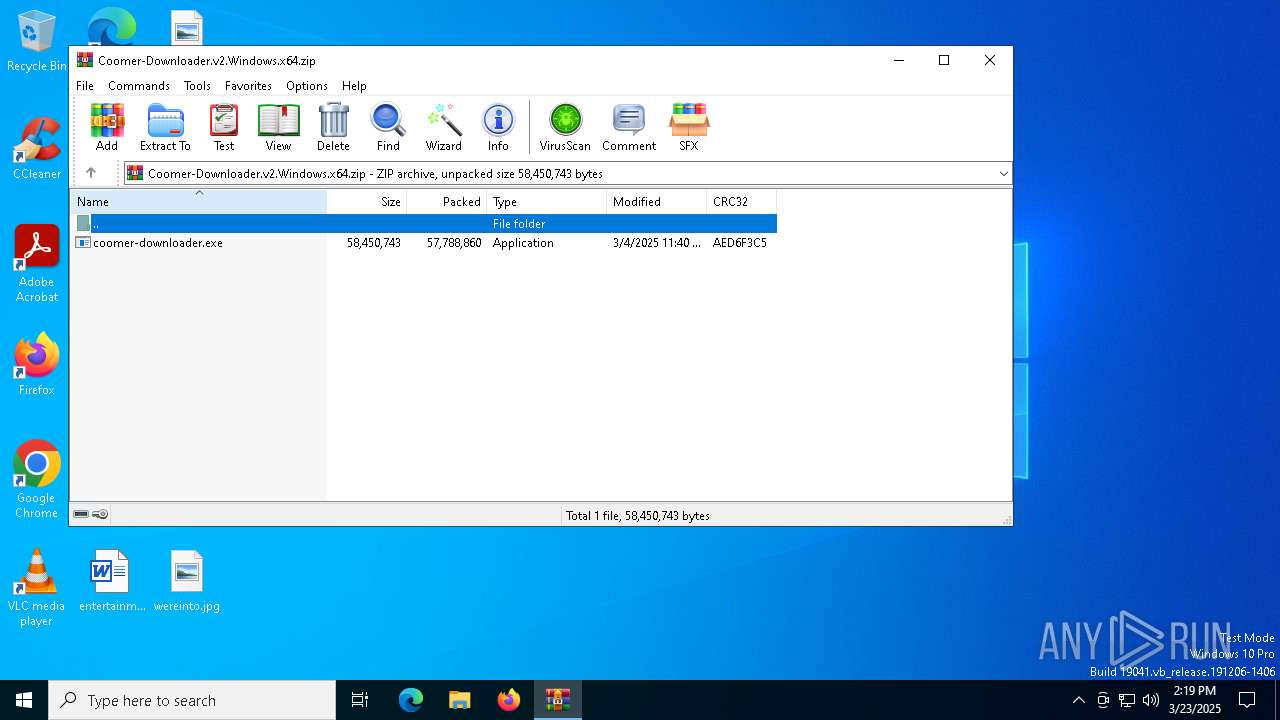
| 4892 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Coomer-Downloader.v2.Windows.x64.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
23 608
Read events
23 322
Write events
276
Delete events
10
Modification events
| (PID) Process: | (5512) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5512) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5512) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5512) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5512) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5512) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7204) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7204) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7204) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7204) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
127
Suspicious files
244
Text files
86
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bb05.TMP | — | |
MD5:— | SHA256:— | |||
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bb24.TMP | — | |
MD5:— | SHA256:— | |||
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bb34.TMP | — | |
MD5:— | SHA256:— | |||
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bb34.TMP | — | |
MD5:— | SHA256:— | |||
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bb43.TMP | — | |
MD5:— | SHA256:— | |||
| 7204 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
57
DNS requests
62
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8160 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7020 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7760 | svchost.exe | HEAD | 200 | 2.22.242.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742999461&P2=404&P3=2&P4=ItHa0891IgCwA9%2bqByW3uCvEb3PkPOIdHQiTHmP5Cug2dWXydoSCJCrRw1sMn%2fa8OzAsheM7R6boguYS72zNaA%3d%3d | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7760 | svchost.exe | GET | 206 | 2.22.242.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742999461&P2=404&P3=2&P4=ItHa0891IgCwA9%2bqByW3uCvEb3PkPOIdHQiTHmP5Cug2dWXydoSCJCrRw1sMn%2fa8OzAsheM7R6boguYS72zNaA%3d%3d | unknown | — | — | whitelisted |
7760 | svchost.exe | GET | 206 | 2.22.242.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742999461&P2=404&P3=2&P4=ItHa0891IgCwA9%2bqByW3uCvEb3PkPOIdHQiTHmP5Cug2dWXydoSCJCrRw1sMn%2fa8OzAsheM7R6boguYS72zNaA%3d%3d | unknown | — | — | whitelisted |
7760 | svchost.exe | GET | 206 | 2.22.242.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742999461&P2=404&P3=2&P4=ItHa0891IgCwA9%2bqByW3uCvEb3PkPOIdHQiTHmP5Cug2dWXydoSCJCrRw1sMn%2fa8OzAsheM7R6boguYS72zNaA%3d%3d | unknown | — | — | whitelisted |
7760 | svchost.exe | GET | 206 | 2.22.242.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742999461&P2=404&P3=2&P4=ItHa0891IgCwA9%2bqByW3uCvEb3PkPOIdHQiTHmP5Cug2dWXydoSCJCrRw1sMn%2fa8OzAsheM7R6boguYS72zNaA%3d%3d | unknown | — | — | whitelisted |
7760 | svchost.exe | GET | 206 | 2.22.242.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742999461&P2=404&P3=2&P4=ItHa0891IgCwA9%2bqByW3uCvEb3PkPOIdHQiTHmP5Cug2dWXydoSCJCrRw1sMn%2fa8OzAsheM7R6boguYS72zNaA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7440 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7204 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7440 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7440 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |