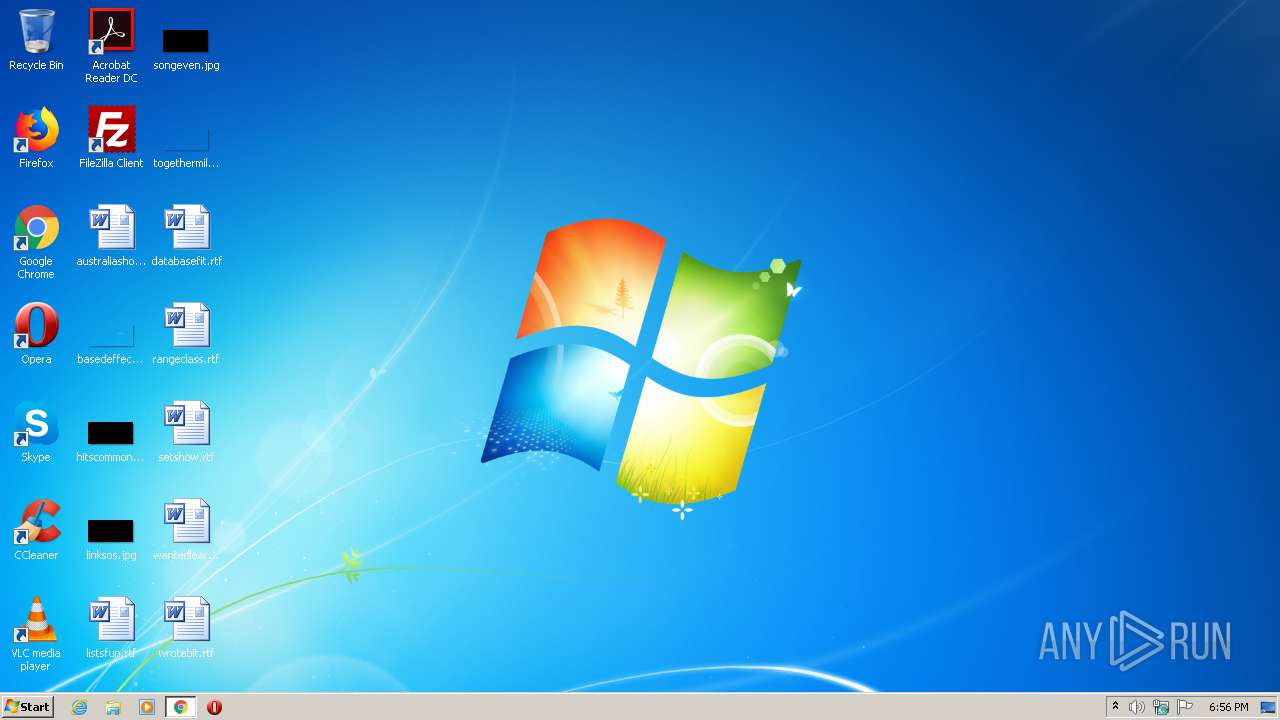
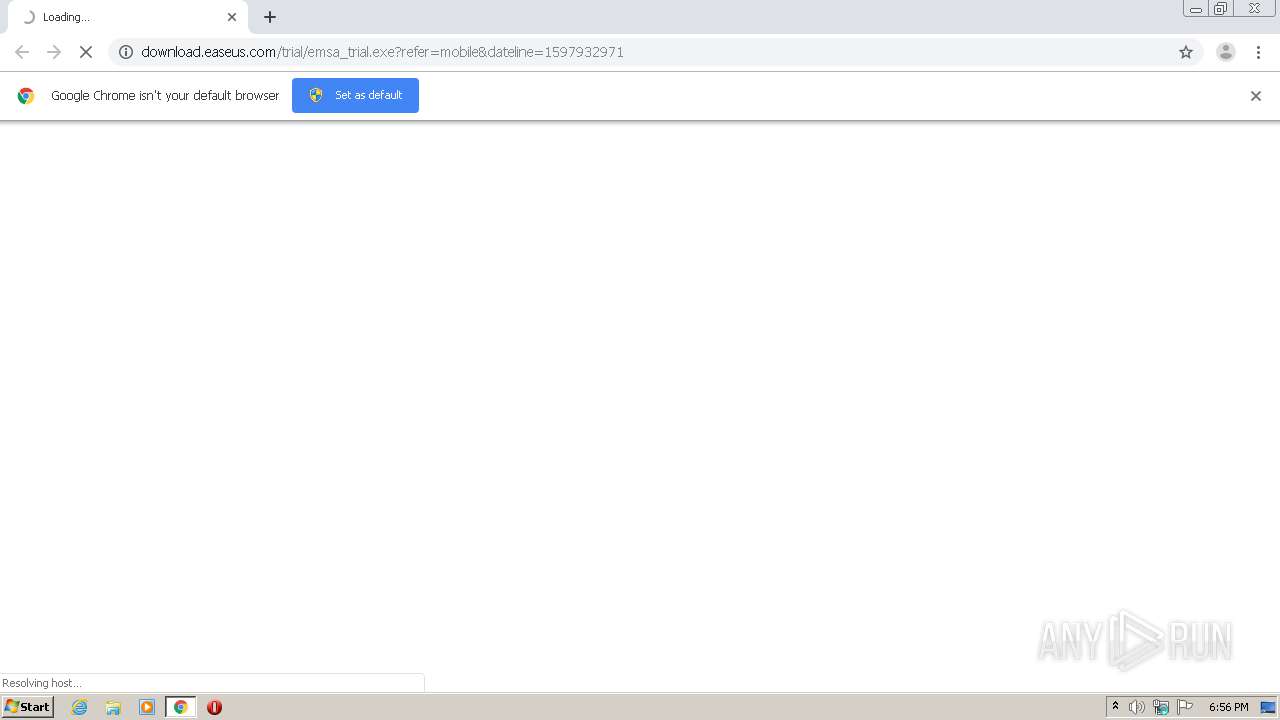
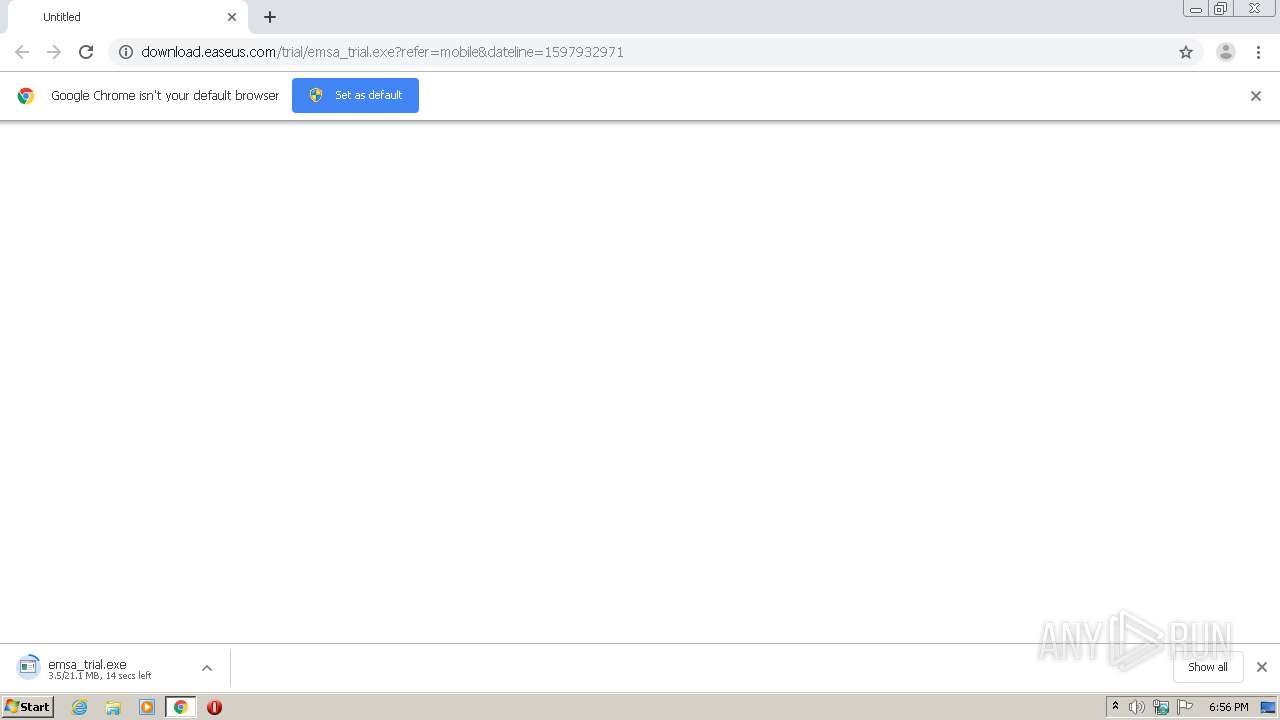
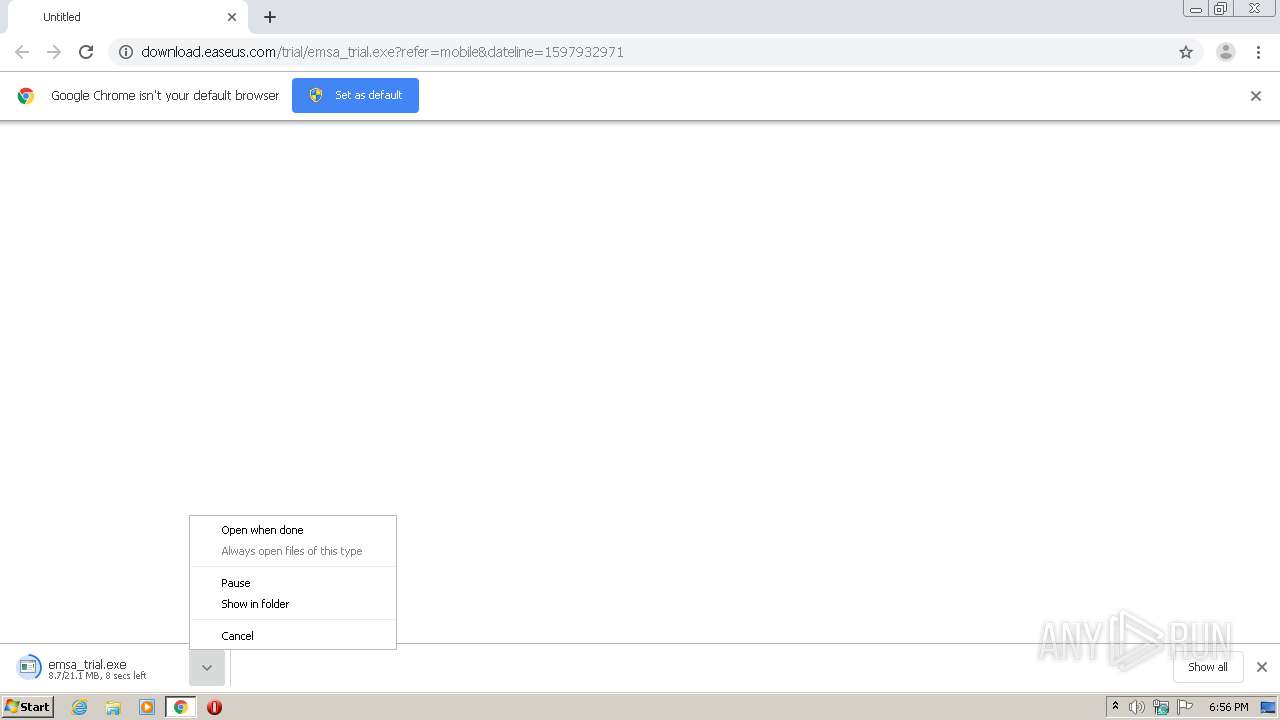
| URL: | http://download.easeus.com/trial/emsa_trial.exe?refer=mobile&dateline=1597932971 |
| Full analysis: | https://app.any.run/tasks/ae7d7fc0-7f7e-4c29-922e-cbbcb4f67dca |
| Verdict: | Malicious activity |
| Analysis date: | August 20, 2020, 17:56:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 388CE7E55C56ED7896E1DBEBC2D2F208 |
| SHA1: | 95276A5B88B57D2AFC8E5FAF77CB7F3D0BF4D6E4 |
| SHA256: | 6B4411B77071B7EE8195CA66563EED4655B52A2E6F48A59914ED7A8CD68F3FBB |
| SSDEEP: | 3:N1KaKElBXMEENGF4AaXAc0VvQcnn:Ca5aESGFIXApCcnn |
MALICIOUS
Application was dropped or rewritten from another process
- emsa_trial.exe (PID: 2056)
- emsa_trial.exe (PID: 1296)
- SpyInstall.exe (PID: 2872)
Loads dropped or rewritten executable
- SpyInstall.exe (PID: 2872)
SUSPICIOUS
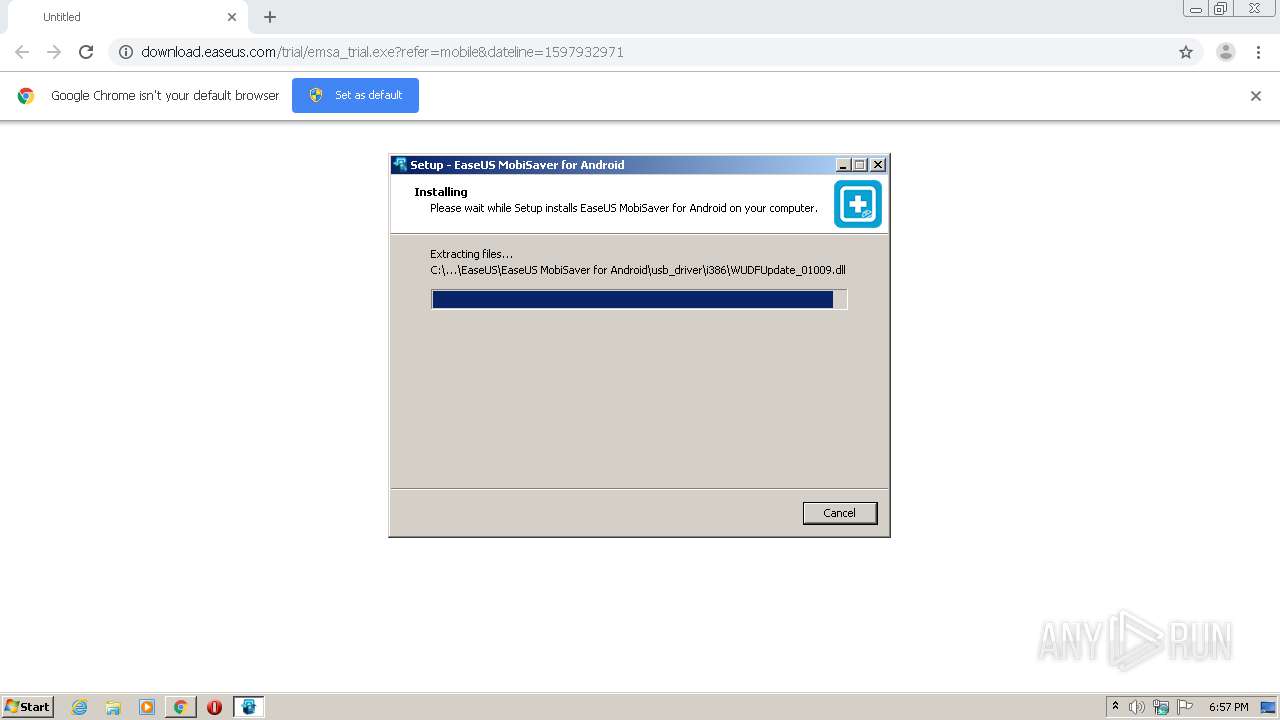
Creates files in the program directory
- SpyInstall.exe (PID: 2872)
Executable content was dropped or overwritten
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2676)
- emsa_trial.exe (PID: 1296)
- emsa_trial.tmp (PID: 4024)
Reads the Windows organization settings
- emsa_trial.tmp (PID: 4024)
Reads Windows owner or organization settings
- emsa_trial.tmp (PID: 4024)
Reads Internet Cache Settings
- SpyInstall.exe (PID: 2872)
INFO
Application launched itself
- chrome.exe (PID: 2676)
Reads the hosts file
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2676)
Application was dropped or rewritten from another process
- emsa_trial.tmp (PID: 4024)
Creates a software uninstall entry
- emsa_trial.tmp (PID: 4024)
Reads Internet Cache Settings
- chrome.exe (PID: 2676)
Creates files in the program directory
- emsa_trial.tmp (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
14
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
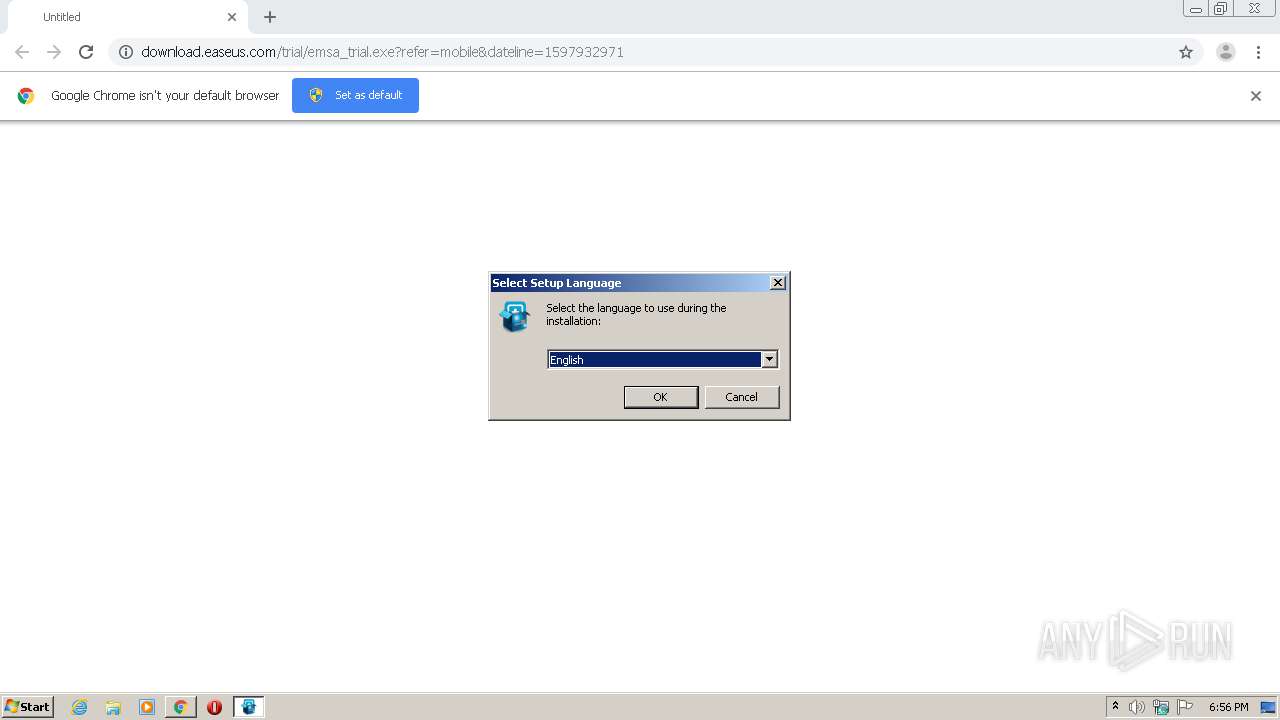
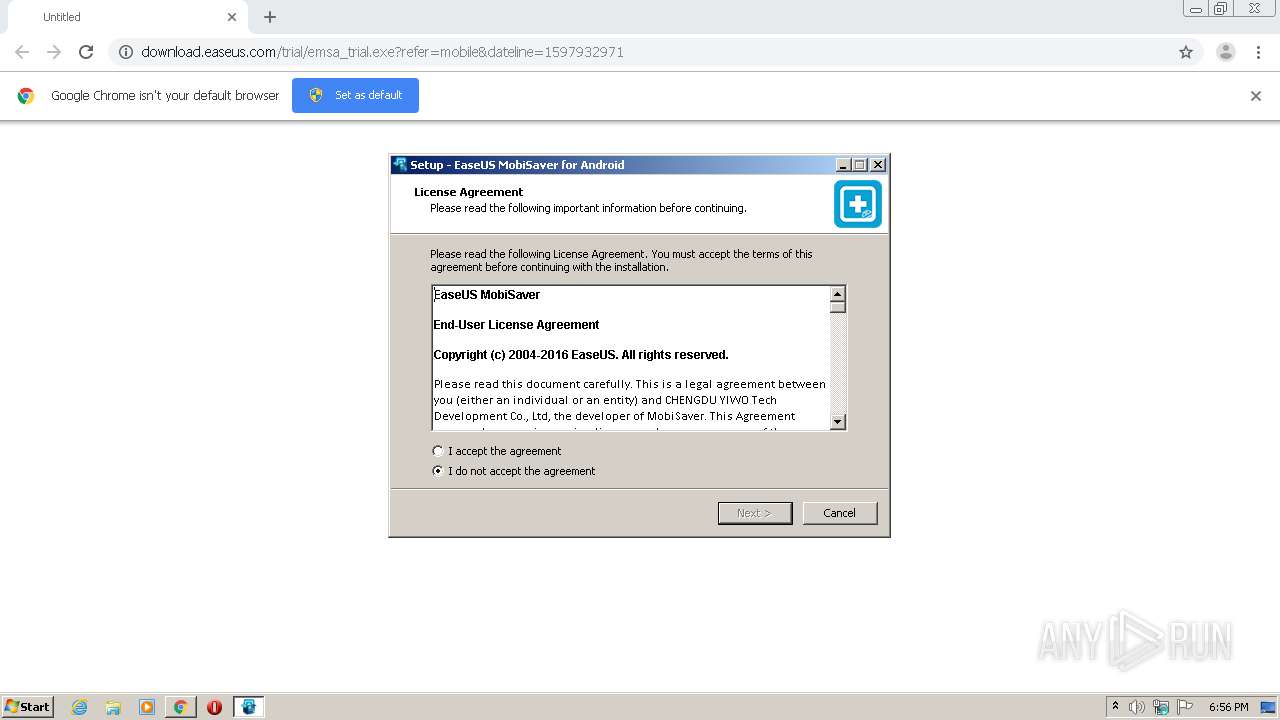
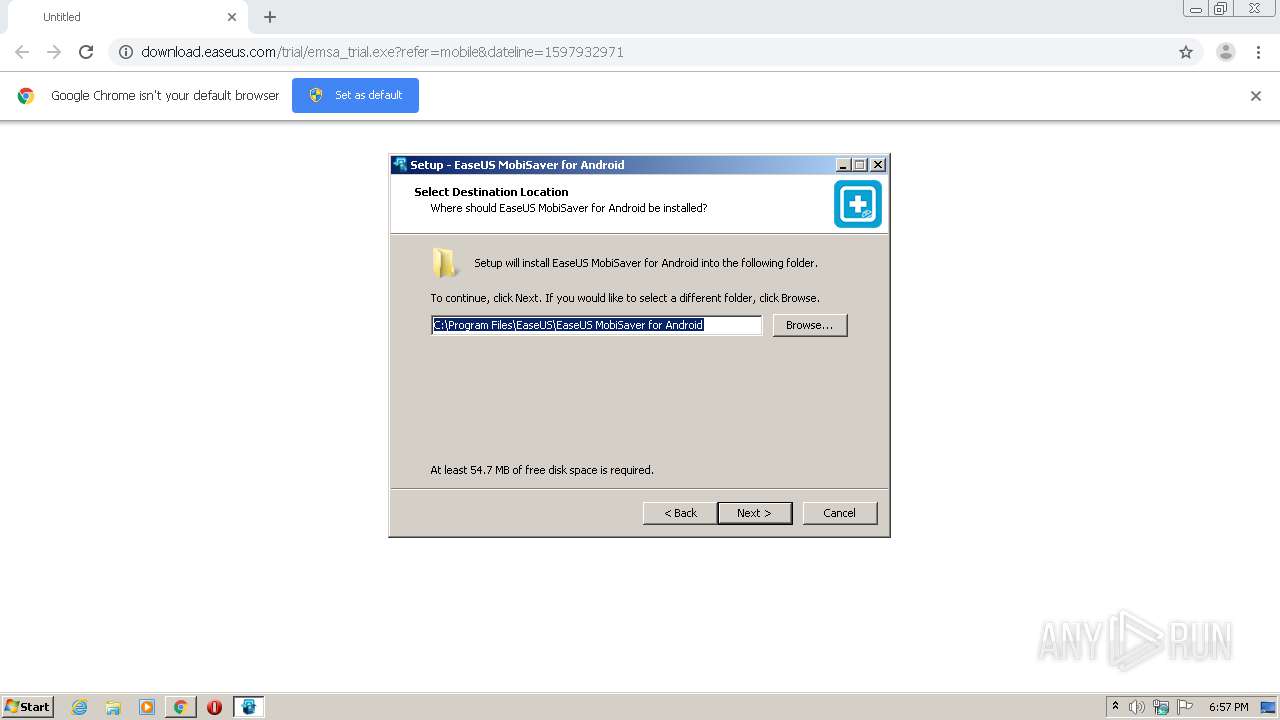
| 1296 | "C:\Users\admin\Downloads\emsa_trial.exe" | C:\Users\admin\Downloads\emsa_trial.exe | chrome.exe | ||||||||||||
User: admin Company: CHENGDU YIWO Tech Development Co., Ltd. Integrity Level: HIGH Description: EaseUS MobiSaver for Android Setup Exit code: 0 Version: 5.0 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,457109290869830169,17567124663129957619,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4327447428755607035 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,457109290869830169,17567124663129957619,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11781457776136428795 --mojo-platform-channel-handle=3520 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=960 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\Downloads\emsa_trial.exe" | C:\Users\admin\Downloads\emsa_trial.exe | — | chrome.exe | |||||||||||
User: admin Company: CHENGDU YIWO Tech Development Co., Ltd. Integrity Level: MEDIUM Description: EaseUS MobiSaver for Android Setup Exit code: 3221226540 Version: 5.0 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,457109290869830169,17567124663129957619,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15158920976152792199 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,457109290869830169,17567124663129957619,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17896868186446111467 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://download.easeus.com/trial/emsa_trial.exe?refer=mobile&dateline=1597932971" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,457109290869830169,17567124663129957619,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16318544142191775209 --mojo-platform-channel-handle=1596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\EaseUS\EaseUS MobiSaver for Android\bin\SpyInstall.exe" 0\trial500 | C:\Program Files\EaseUS\EaseUS MobiSaver for Android\bin\SpyInstall.exe | emsa_trial.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 166
Read events
1 060
Write events
103
Delete events
3
Modification events
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2676-13242419783658000 |
Value: 259 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
90
Suspicious files
12
Text files
194
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\03c7b7c5-9398-47e3-ad5b-1c45f644c705.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFdc729.TMP | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFdc5e1.TMP | text | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFdc7c5.TMP | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
12
DNS requests
7
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2872 | SpyInstall.exe | POST | — | 216.92.47.198:80 | http://track.easeus.com/product/index.php/?a=statistics&p_type=m_mobi_android_userinfos | US | — | — | suspicious |
2872 | SpyInstall.exe | POST | 200 | 216.92.47.198:80 | http://track.easeus.com/product/index.php/?a=statistics&p_type=m_mobi_android_userinfos | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 205.185.216.42:80 | download.easeus.com | Highwinds Network Group, Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.21.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2872 | SpyInstall.exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.easeus.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
track.easeus.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2752 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2872 | SpyInstall.exe | Misc activity | SUSPICIOUS [PTsecurity] RiskTool.EaseUS.Dnotua.arv Exfiltration host system data |
Process | Message |
|---|---|
SpyInstall.exe | install spy argc = 2, isjoined = 1 |
SpyInstall.exe | C:\Program Files\EaseUS\EaseUS MobiSaver for Android\bin\SpyInstall.exe |
SpyInstall.exe | 0\trial500 |
SpyInstall.exe | 2020-08-20 18:57:16:099[UE] --Info. try send=1
|
SpyInstall.exe | 2020-08-20 18:57:16:099[UE] --Info. top num =0
|
SpyInstall.exe | 2020-08-20 18:57:16:099[UE] --Info. top num =0
|
SpyInstall.exe | 2020-08-20 18:57:16:099[UE] --Info. SetText. id=0x3 (3), text=1, inst=013D0C58
|
SpyInstall.exe | 2020-08-20 18:57:16:099[UE] --Info. log level=3
|
SpyInstall.exe | 2020-08-20 18:57:16:099[UE] --Info. InstallSpy. inst=013D0C58
|
SpyInstall.exe | 2020-08-20 18:57:16:115[UE] --Info. server=track.easeus.com, object=/product/index.php/?a=statistics&p_type=m_mobi_android_userinfos
|