| File name: | DriverAutomationTool.exe |
| Full analysis: | https://app.any.run/tasks/c8dcc932-bd16-4e6b-8b43-36b4dc185fb6 |
| Verdict: | Malicious activity |
| Analysis date: | March 04, 2024, 13:07:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows |
| MD5: | BEB67E29E17CE7E6B59B1E1A4BE2235E |
| SHA1: | 20CC86A3AFF210EC6E662D49336379662C8A16B3 |
| SHA256: | 6B3E8A777BBC567B4BE33BE593D563109CE9EC205BA9A5864F90D6E4AD986B1B |
| SSDEEP: | 6144:JhybfoCZEJdC9epRJrpw+aIC6owSq9yeg/FseYVgq+pmfXZ6Kq5Gs39W3I6ZCq/C:JUbEHRFpw+a1XXeg/FseYVTeOjK |
MALICIOUS
Drops the executable file immediately after the start
- DriverAutomationTool.exe (PID: 5396)
- csc.exe (PID: 2288)
- csc.exe (PID: 6708)
SUSPICIOUS
Reads security settings of Internet Explorer
- DriverAutomationTool.exe (PID: 5396)
Executable content was dropped or overwritten
- csc.exe (PID: 2288)
- csc.exe (PID: 6708)
Checks Windows Trust Settings
- DriverAutomationTool.exe (PID: 5396)
INFO
Checks supported languages
- DriverAutomationTool.exe (PID: 5396)
- csc.exe (PID: 2288)
- cvtres.exe (PID: 1512)
- csc.exe (PID: 6708)
- cvtres.exe (PID: 7060)
Reads the computer name
- DriverAutomationTool.exe (PID: 5396)
Checks proxy server information
- DriverAutomationTool.exe (PID: 5396)
Reads the machine GUID from the registry
- DriverAutomationTool.exe (PID: 5396)
- csc.exe (PID: 2288)
- csc.exe (PID: 6708)
Reads Environment values
- DriverAutomationTool.exe (PID: 5396)
Reads the software policy settings
- DriverAutomationTool.exe (PID: 5396)
Create files in a temporary directory
- csc.exe (PID: 2288)
- DriverAutomationTool.exe (PID: 5396)
- cvtres.exe (PID: 1512)
- cvtres.exe (PID: 7060)
- csc.exe (PID: 6708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:08:15 20:27:34+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 92672 |
| InitializedDataSize: | 2878464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.2.3.0 |
| ProductVersionNumber: | 7.2.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
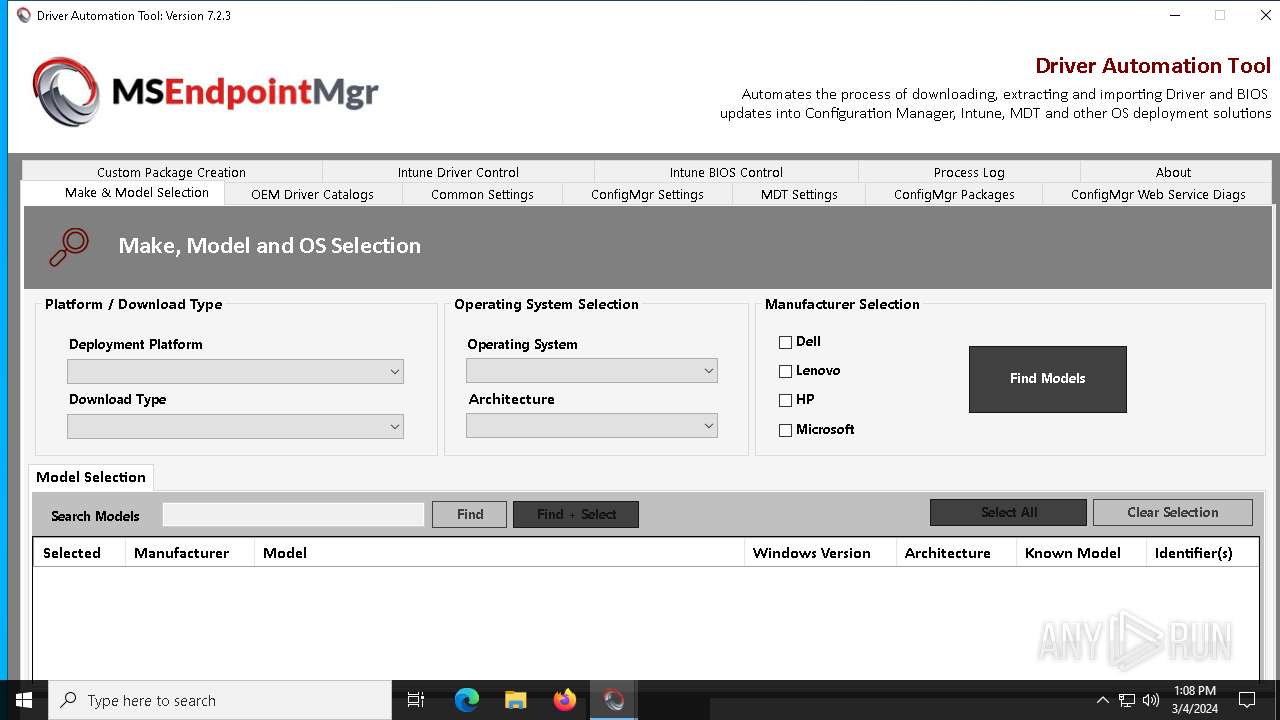
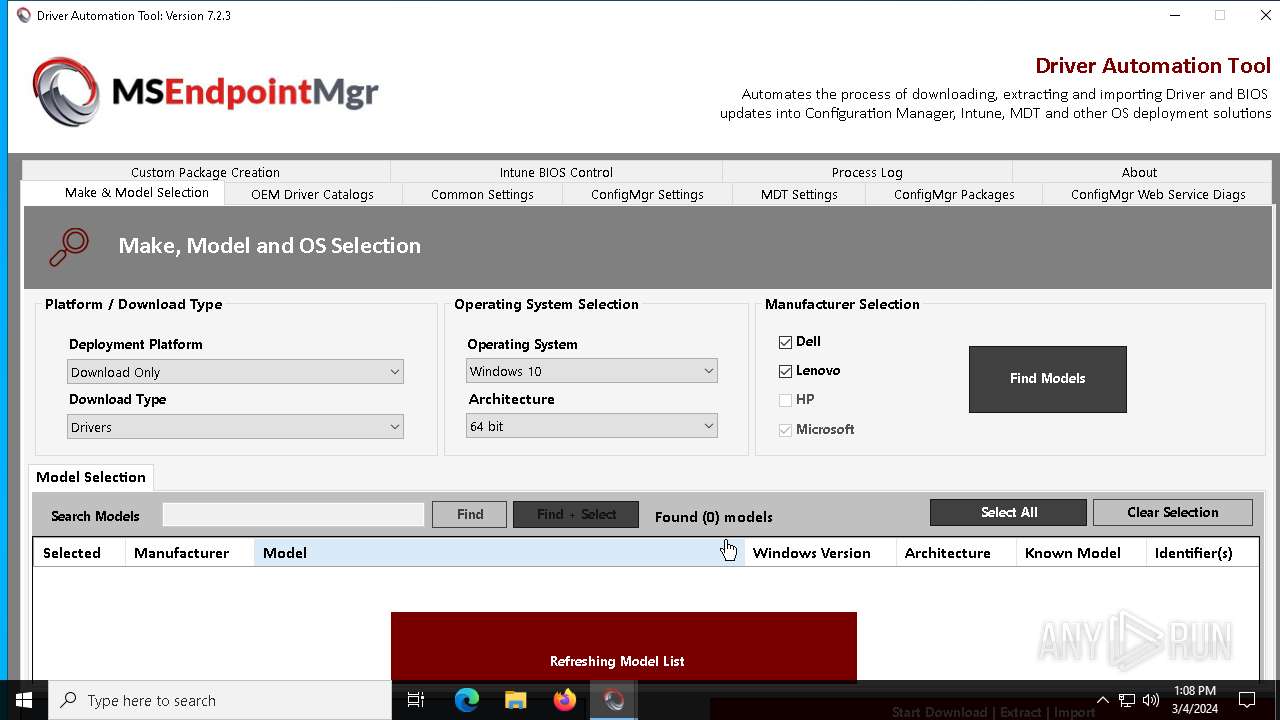
| FileDescription: | Driver Automation Tool |
| FileVersion: | 7.2.3.0 |
| InternalName: | Driver Automation Tool |
| LegalCopyright: | Copyright (c) 2024 All rights reserved |
| OriginalFileName: | DriverAutomationTool |
| ProductVersion: | 7.2.3.0 |
| AssemblyVersion: | 1.1.15.0 |
| CompanyName: | MSEndpointMgr.com |
| ProductName: | Driver Automation Tool |
| Comments: | Automate the process of downloading, extracting and packaging driver & BIOS updates |
Total processes
140
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1512 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES6862.tmp" "c:\Users\admin\AppData\Local\Temp\0xc0cqai\CSC78912AC0B2774476886DDF8172C9539.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2124 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\0xc0cqai\0xc0cqai.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | DriverAutomationTool.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5396 | "C:\Users\admin\AppData\Local\Temp\DriverAutomationTool.exe" | C:\Users\admin\AppData\Local\Temp\DriverAutomationTool.exe | explorer.exe | ||||||||||||
User: admin Company: MSEndpointMgr.com Integrity Level: HIGH Description: Driver Automation Tool Exit code: 0 Version: 7.2.3.0 Modules
| |||||||||||||||
| 6304 | "C:\Users\admin\AppData\Local\Temp\DriverAutomationTool.exe" | C:\Users\admin\AppData\Local\Temp\DriverAutomationTool.exe | — | explorer.exe | |||||||||||
User: admin Company: MSEndpointMgr.com Integrity Level: MEDIUM Description: Driver Automation Tool Exit code: 3221226540 Version: 7.2.3.0 Modules
| |||||||||||||||
| 6696 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6708 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\vnbgwyam\vnbgwyam.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | DriverAutomationTool.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 7060 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES68FE.tmp" "c:\Users\admin\AppData\Local\Temp\vnbgwyam\CSCB00F44C1578F406C88F1D3923C123A5.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
Total events
28 941
Read events
28 914
Write events
27
Delete events
0
Modification events
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DriverAutomationTool_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DriverAutomationTool_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DriverAutomationTool_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DriverAutomationTool_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DriverAutomationTool_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5396) DriverAutomationTool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DriverAutomationTool_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
2
Suspicious files
5
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5396 | DriverAutomationTool.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5afc10qi.hmp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5396 | DriverAutomationTool.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wflfmnpj.0k5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5396 | DriverAutomationTool.exe | C:\Users\admin\AppData\Local\Temp\Logs\DriverAutomationTool.log | text | |
MD5:474D8B211D674EC884FB30F55EE6540C | SHA256:AD249A9A513712BB1309642E71A3E1F0BC49C5CA28E33B8AEF5F7840EFA9D53A | |||
| 5396 | DriverAutomationTool.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ufcdoysp.cli.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5396 | DriverAutomationTool.exe | C:\Users\admin\AppData\Local\Temp\0xc0cqai\0xc0cqai.0.cs | text | |
MD5:EC87517EB8075F38E87D804A4E794729 | SHA256:11FC056C5D10B27143A445372C4931E219522338B01D1C5F5313A7E5172DBBBB | |||
| 2288 | csc.exe | C:\Users\admin\AppData\Local\Temp\0xc0cqai\0xc0cqai.dll | executable | |
MD5:D312299C0657024D83624E693A19C7D5 | SHA256:92A17D309C094352ED821DCE4B1CE4AA394CBAF375487D2723521B2CD25DB28E | |||
| 5396 | DriverAutomationTool.exe | C:\Users\admin\AppData\Local\Temp\0xc0cqai\0xc0cqai.cmdline | text | |
MD5:0638E363CD19369087FE993FDF23493B | SHA256:FF5634DEF5FEF0B94E5B47104782F2953071E4630BE80990503B7FB8F9876267 | |||
| 1512 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES6862.tmp | binary | |
MD5:17DEA46141A455E344DF4A51FBAFECAF | SHA256:52B5DF6BD3908E4B7A37E7748808A87222237054EC04DBC1439029E419D6EF42 | |||
| 5396 | DriverAutomationTool.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sw1ksd43.xik.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5396 | DriverAutomationTool.exe | C:\Users\admin\AppData\Local\Temp\vnbgwyam\vnbgwyam.cmdline | text | |
MD5:B2FE06C45598894F9B0F37E9839920AB | SHA256:A8560E922CCC2AD07C08F9991A39EF9C50E5D370854E3C7027BA5761C0F23CAE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
35
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
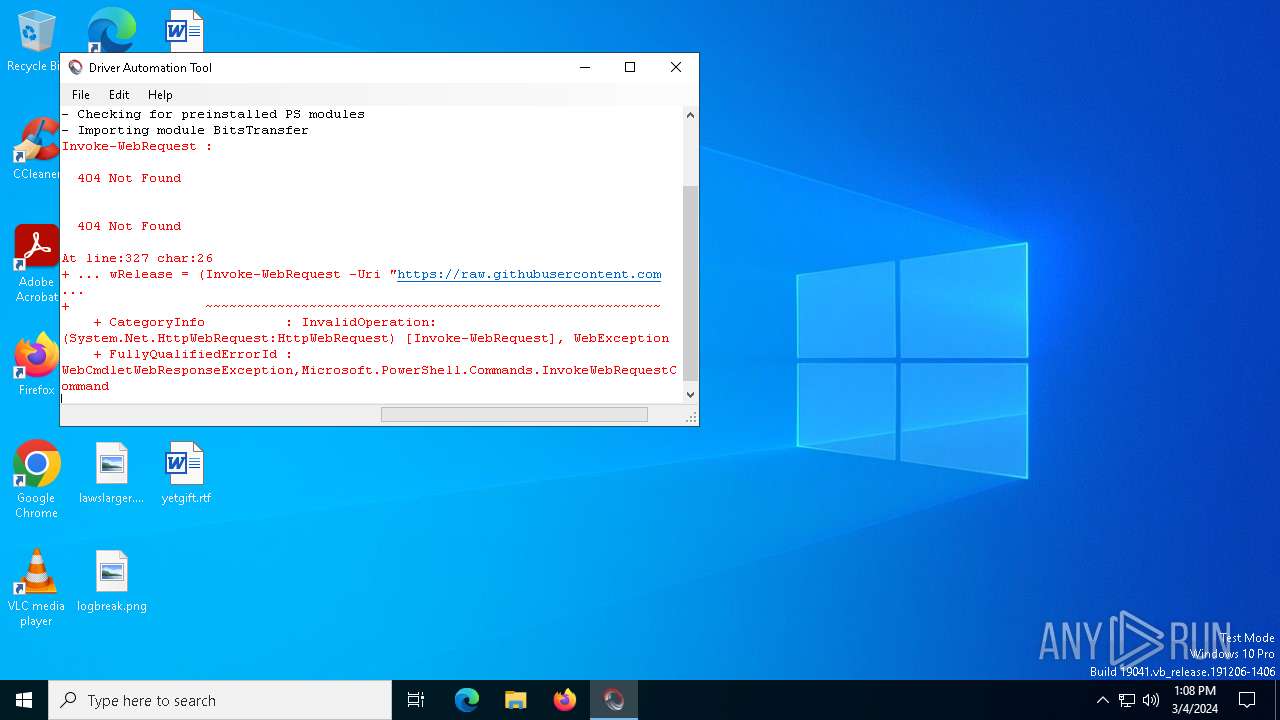
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | xml | 341 b | unknown |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | xml | 341 b | unknown |
— | — | GET | 404 | 49.13.77.253:443 | https://49.13.77.253/maurice-daly/DriverAutomationTool/master/Data//DriverAutomationToolRev.txt | unknown | xml | 341 b | unknown |
— | — | GET | 404 | 49.13.77.253:443 | https://49.13.77.253/maurice-daly/DriverAutomationTool/master/Data/OEMLinks.xml | unknown | xml | 341 b | unknown |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | xml | 341 b | unknown |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | xml | 341 b | unknown |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | xml | 341 b | unknown |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | xml | 341 b | unknown |
— | — | GET | 404 | 49.13.77.253:443 | https://49.13.77.253/maurice-daly/DriverAutomationTool/master/Data/DriverAutomationToolNotes.txt | unknown | xml | 341 b | unknown |
— | — | GET | 404 | 49.13.77.253:443 | https://49.13.77.253/v3/Delivery/Placement?pubid=da63df93-3dbc-42ae-a505-b34988683ac7&pid=280815&adm=2&w=1&h=1&wpx=1&hpx=1&fmt=json&cltp=app&dim=le&rafb=0&nct=1&pm=1&cfmt=text,image,poly&sft=jpeg,png,gif&topt=1&poptin=0&localid=w:AC7699B0-48EA-FD22-C8DC-06A02098A0F0&ctry=US&time=20240304T130802Z&lc=en-US&pl=en-US&idtp=mid&uid=9115d6d1-9f4e-4053-9297-2a8c833b3912&aid=00000000-0000-0000-0000-000000000000&ua=WindowsShellClient%2F9.0.40929.0%20%28Windows%29&asid=493efe13826445afa95c33fbadc98b44&ctmode=MultiSession&arch=x64&betaedgever=0.0.0.0&canedgever=0.0.0.0&cdm=1&cdmver=10.0.19041.1023&currsel=137271744000000000&devedgever=0.0.0.0&devfam=Windows.Desktop&devform=Unknown&devosver=10.0.19044.1288&disphorzres=1280&dispsize=15.3&dispvertres=720&fosver=16299&isu=0&lo=3413107&metered=false&nettype=ethernet&npid=sc-280815&oemName=DELL&oemid=DELL&ossku=Professional&prevosver=15063&smBiosDm=DELL&stabedgever=111.0.1661.62&tl=2&tsu=803637&waasBldFlt=1&waasCfgExp=1&waasCfgSet=1&waasRetail=1&waasRing=&svoffered=2 | unknown | xml | 341 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3848 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
5928 | svchost.exe | 20.190.159.73:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6896 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6432 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5396 | DriverAutomationTool.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
5928 | svchost.exe | 20.190.159.23:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2052 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6828 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5584 | SIHClient.exe | 52.165.165.26:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
15.164.165.52.in-addr.arpa |
| unknown |
d.3.0.0.0.0.0.0.0.0.0.0.0.0.0.0.7.0.0.0.8.0.4.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |