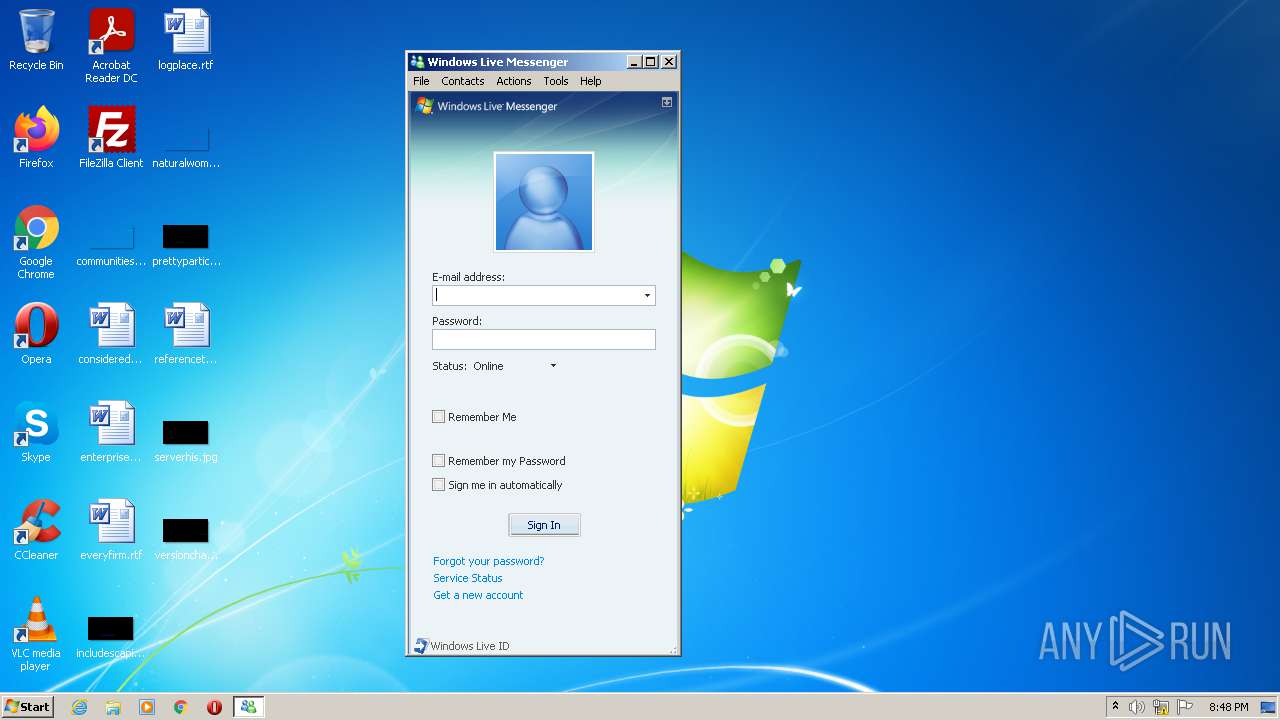
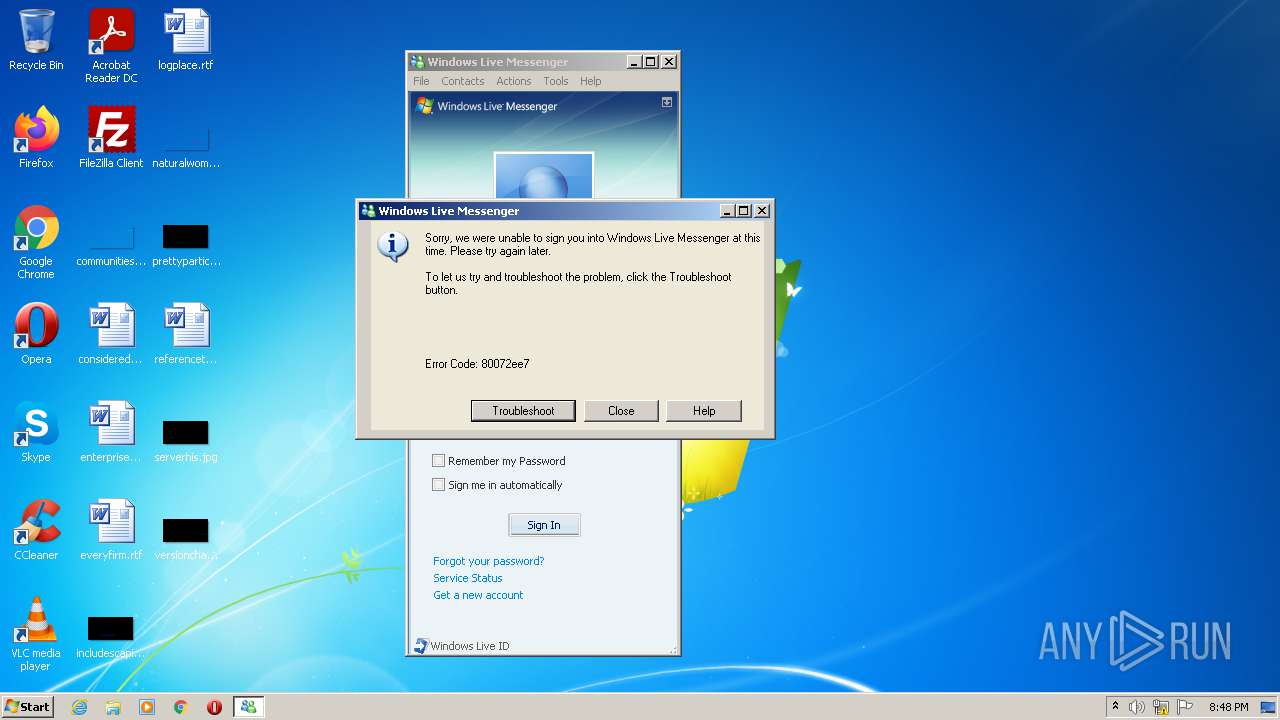
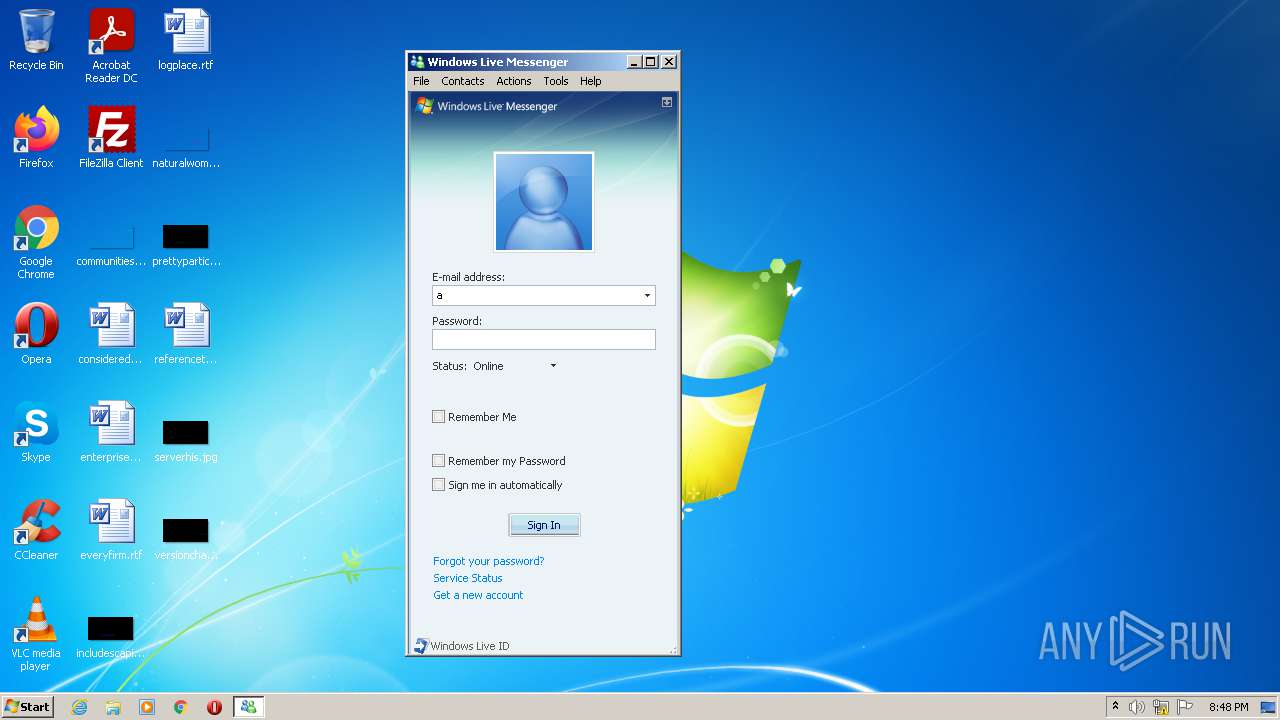
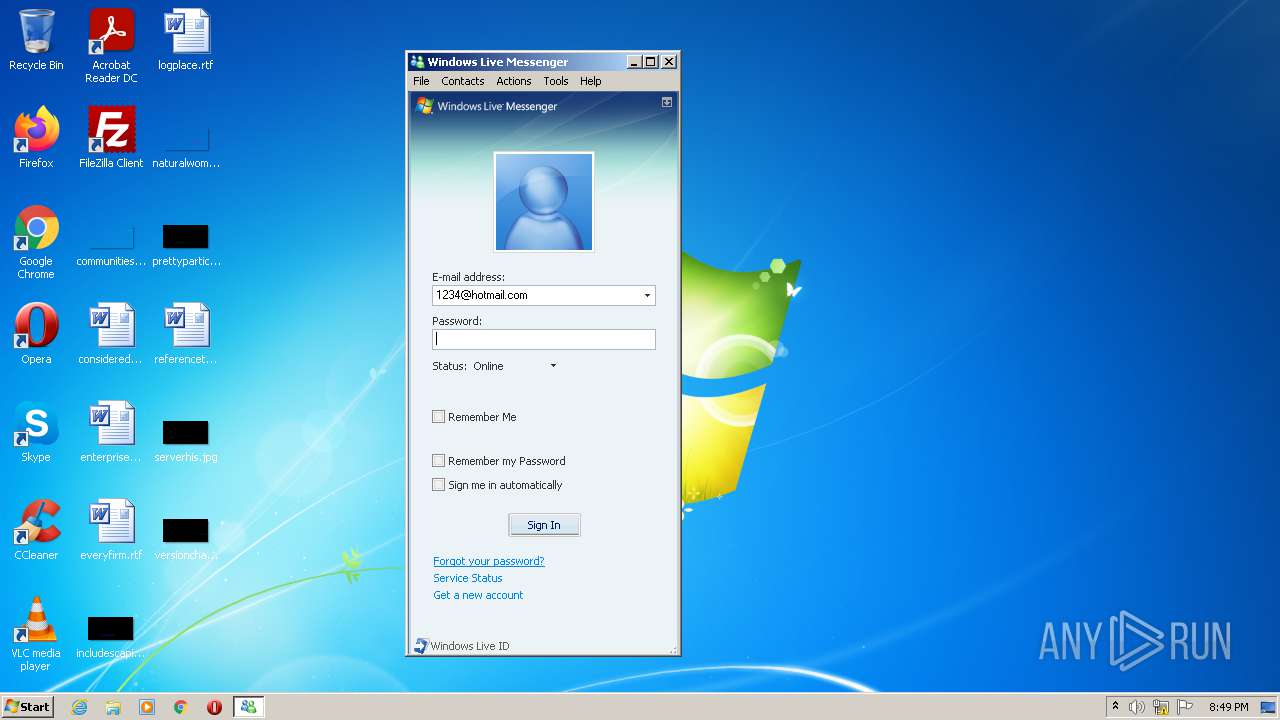
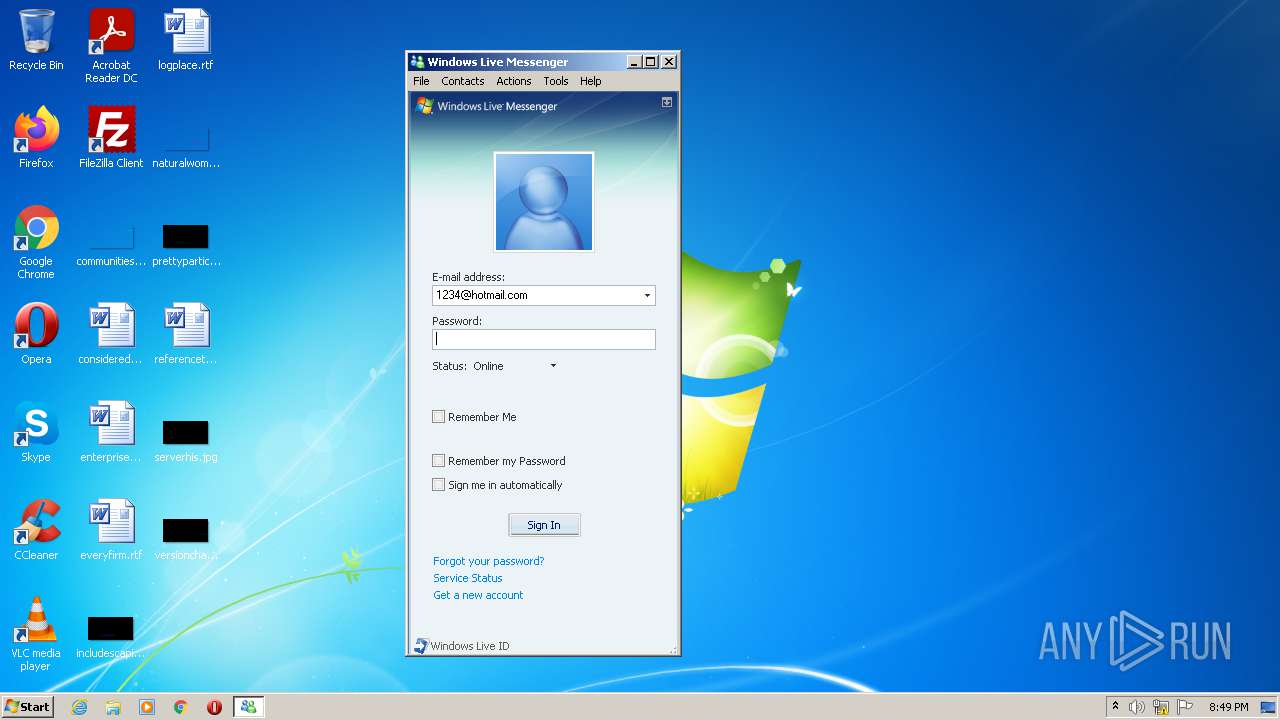
| File name: | Fake Windows Live Messenger.exe |
| Full analysis: | https://app.any.run/tasks/30990b92-2bbe-4c94-b8c4-6836342dac02 |
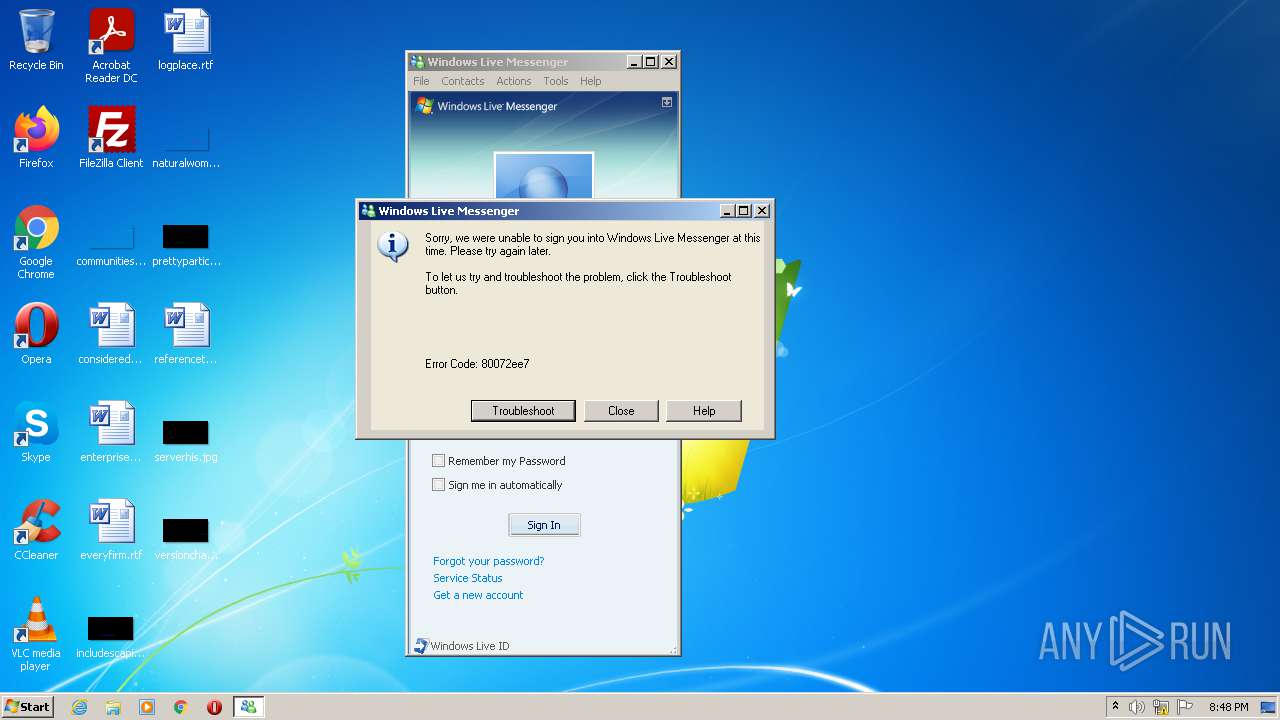
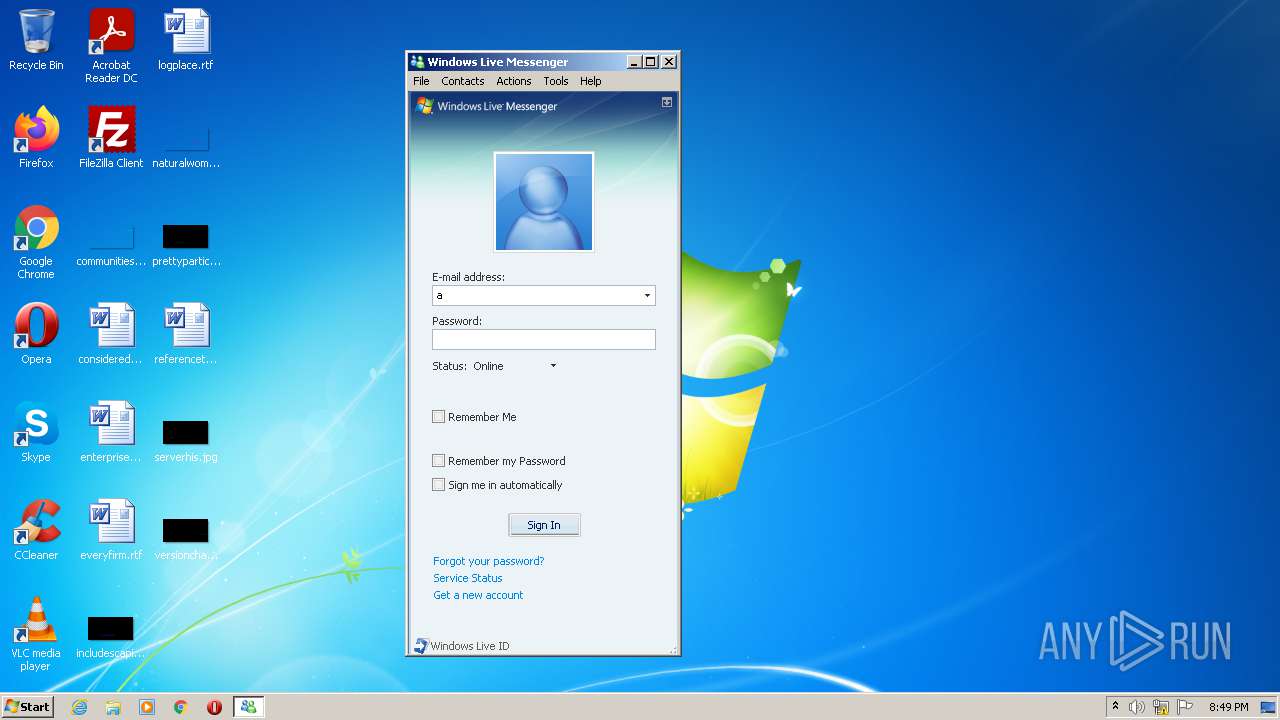
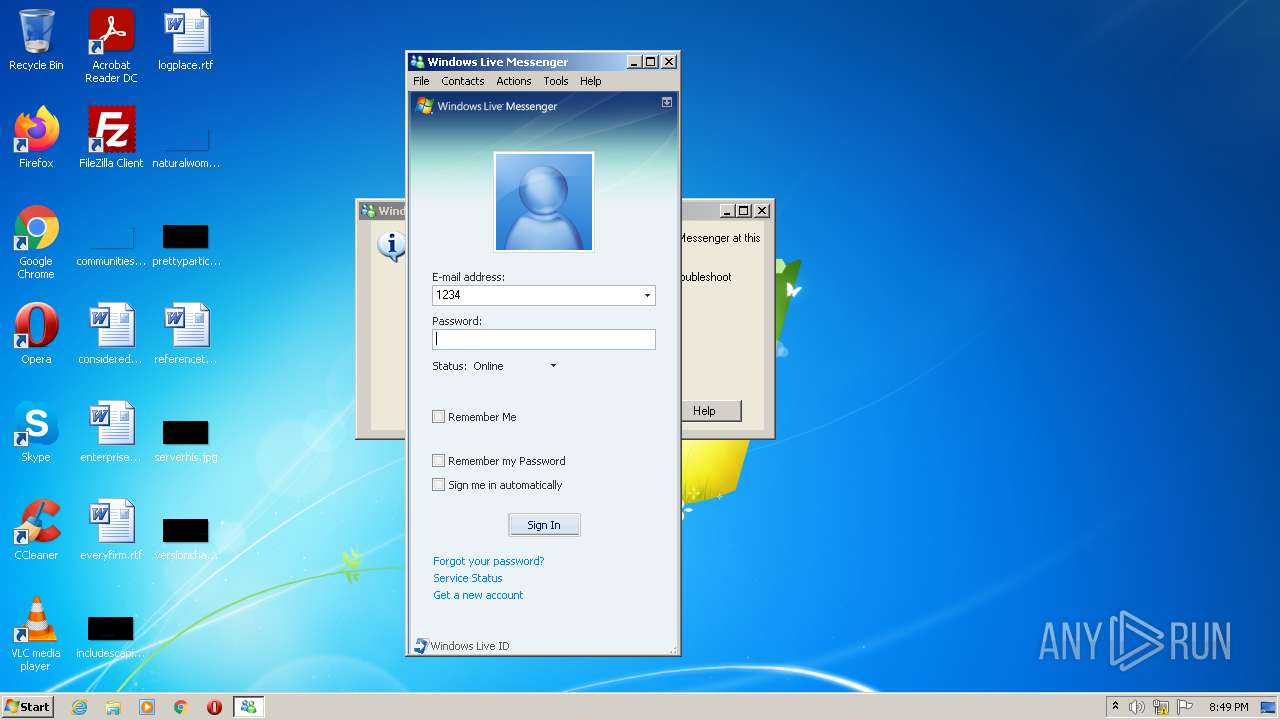
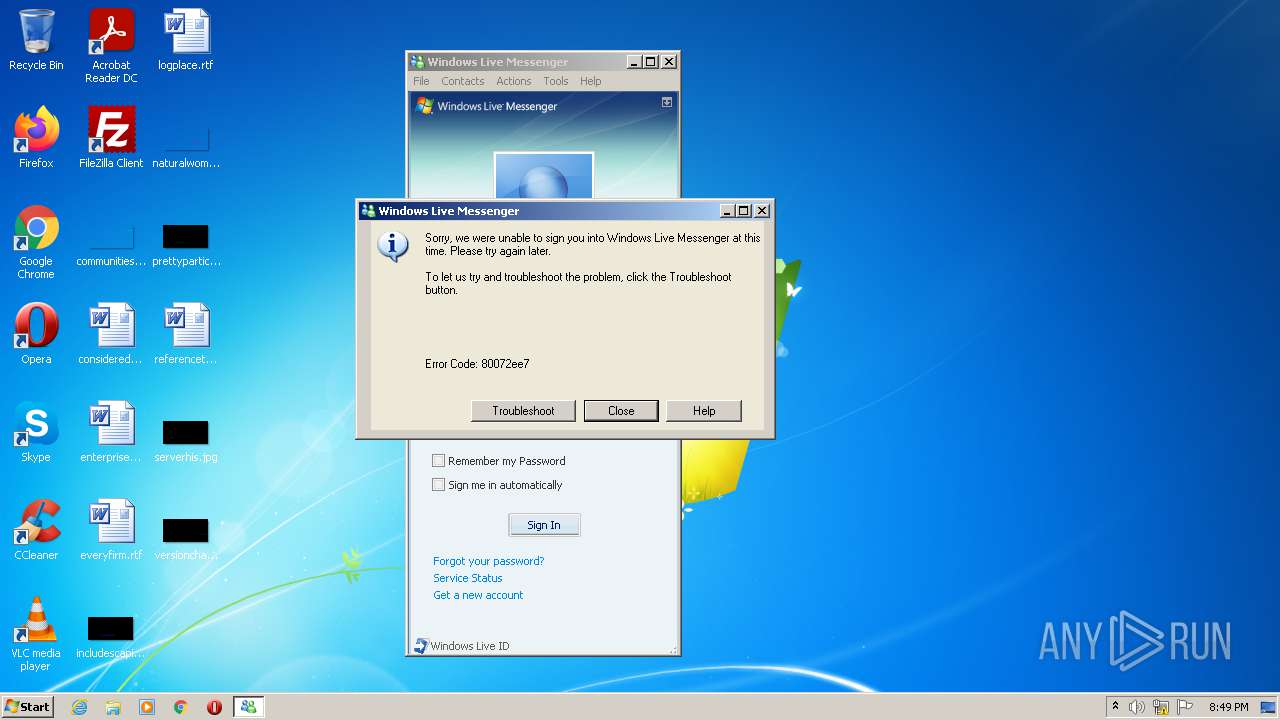
| Verdict: | Malicious activity |
| Analysis date: | November 03, 2021, 20:48:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A7A75A56B4B960C8532C37D3C705F88F |
| SHA1: | E69D26DB431E383131826FAB5DB213559EE68814 |
| SHA256: | 6B34CF6100AC5BF4479250048D61CC4D873DD84AF74E5B2771B3205E2DBF0D22 |
| SSDEEP: | 12288:ebcuIcRD7ZPotep+8dG0Kxi+M9IrQscUjMRWENBui09YAaAWapJOhzqzW1:eYdsZPNJ5QEN4eABpJOg |
MALICIOUS
No malicious indicators.SUSPICIOUS
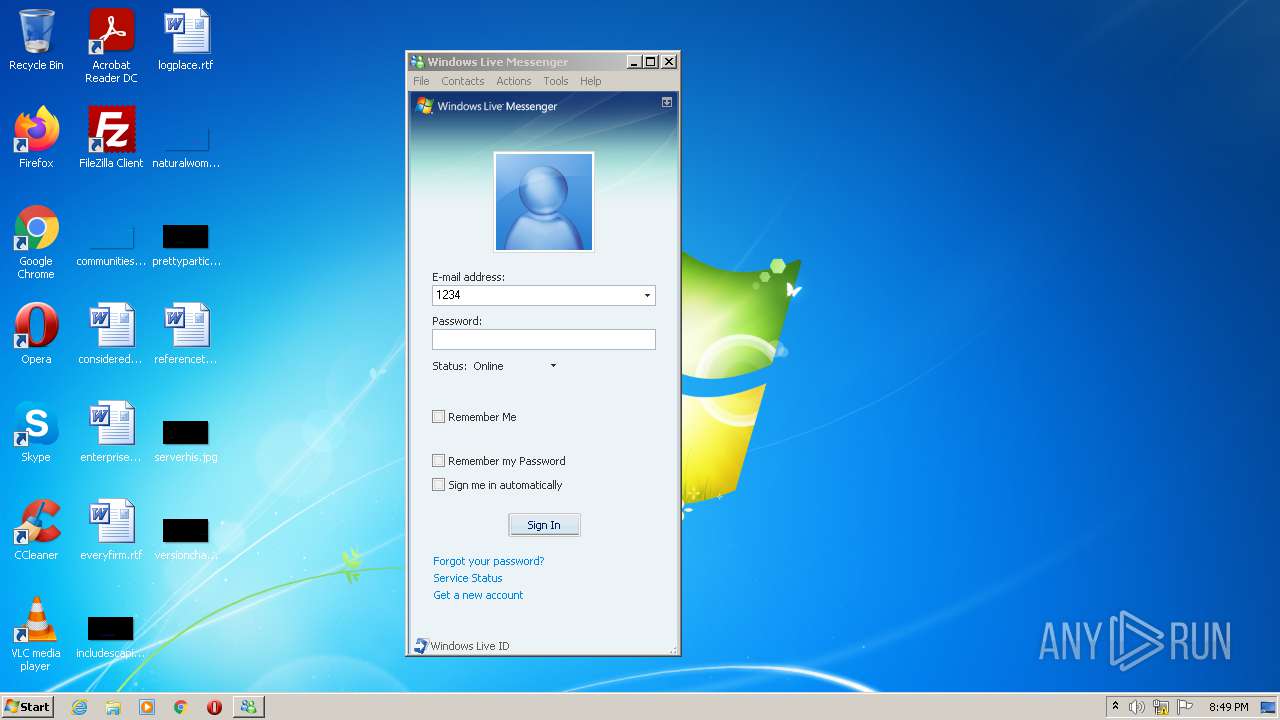
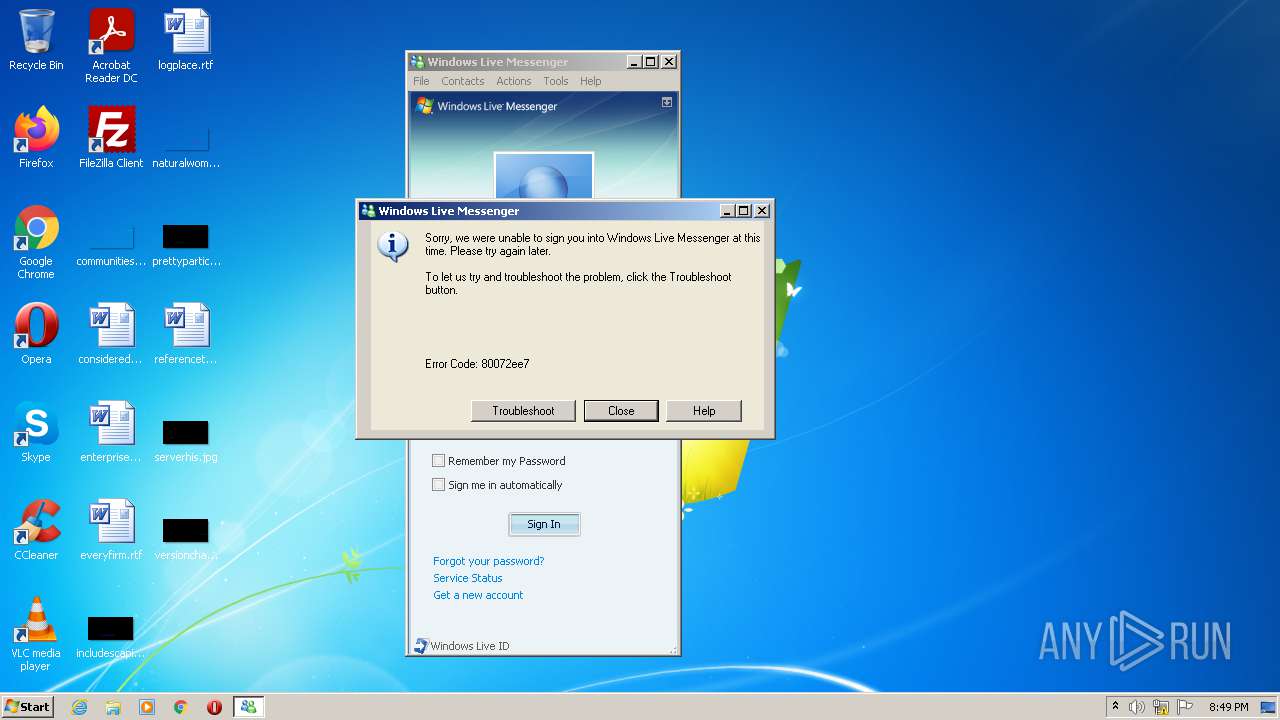
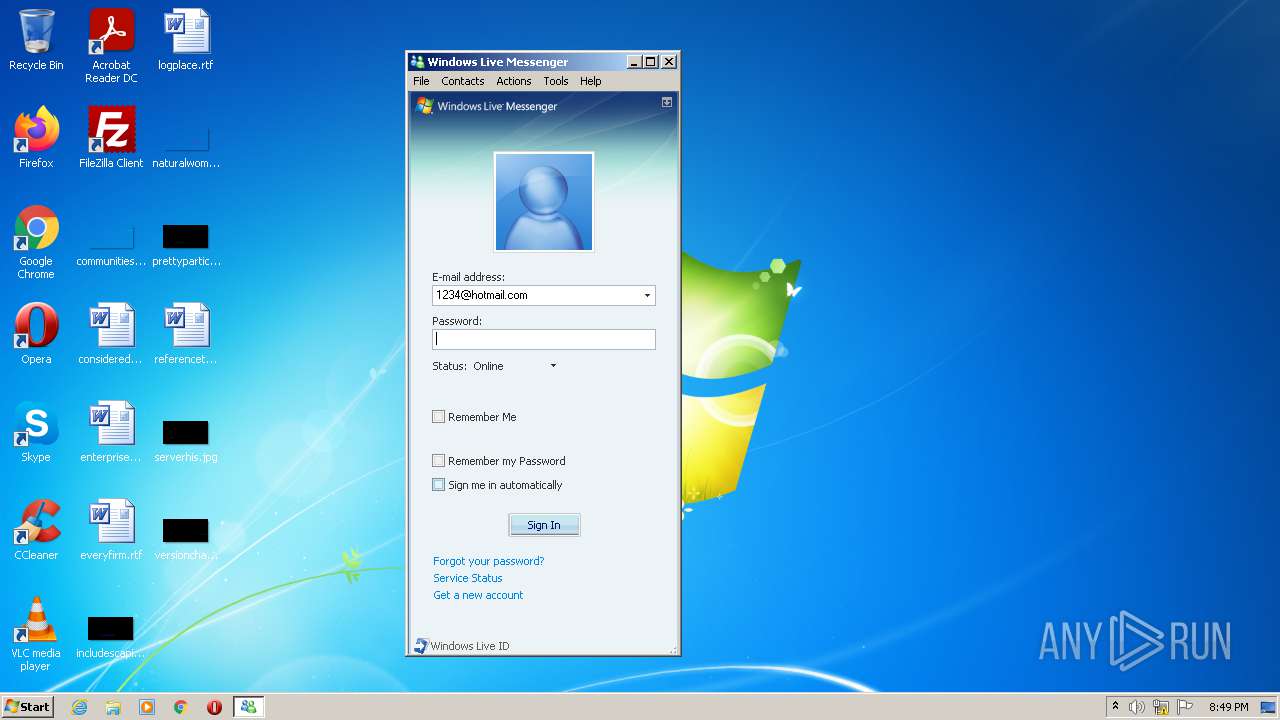
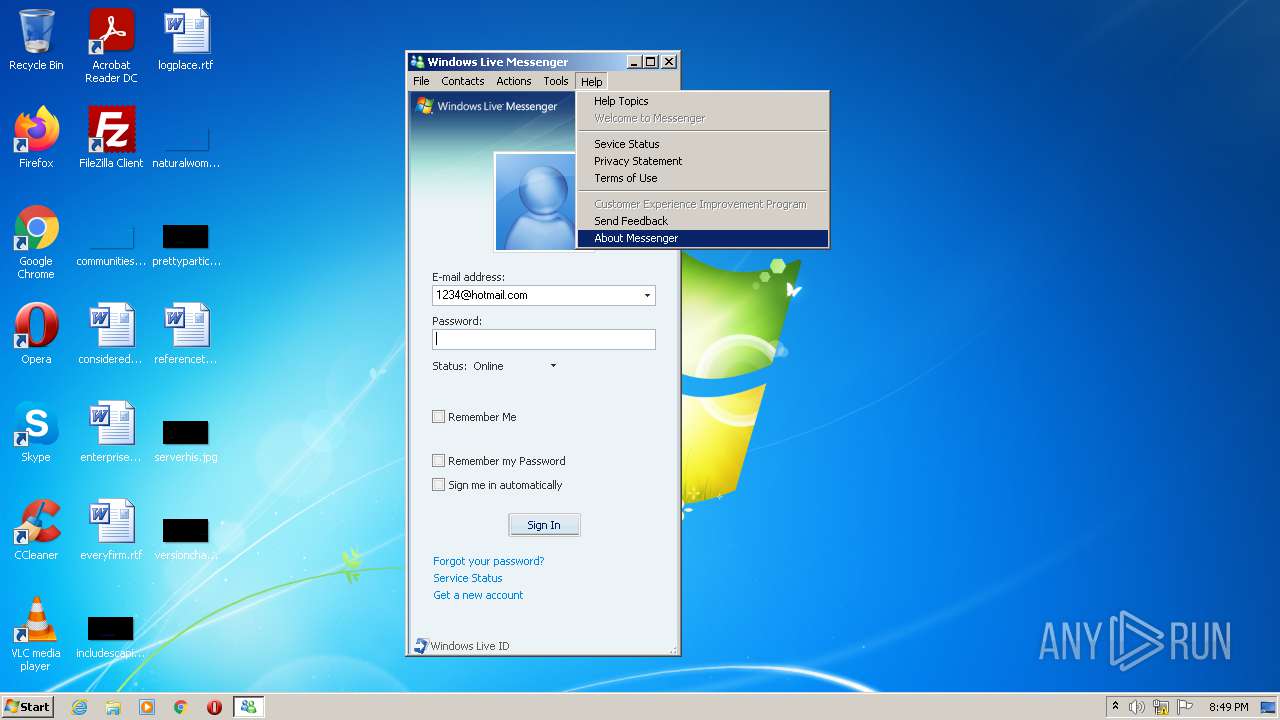
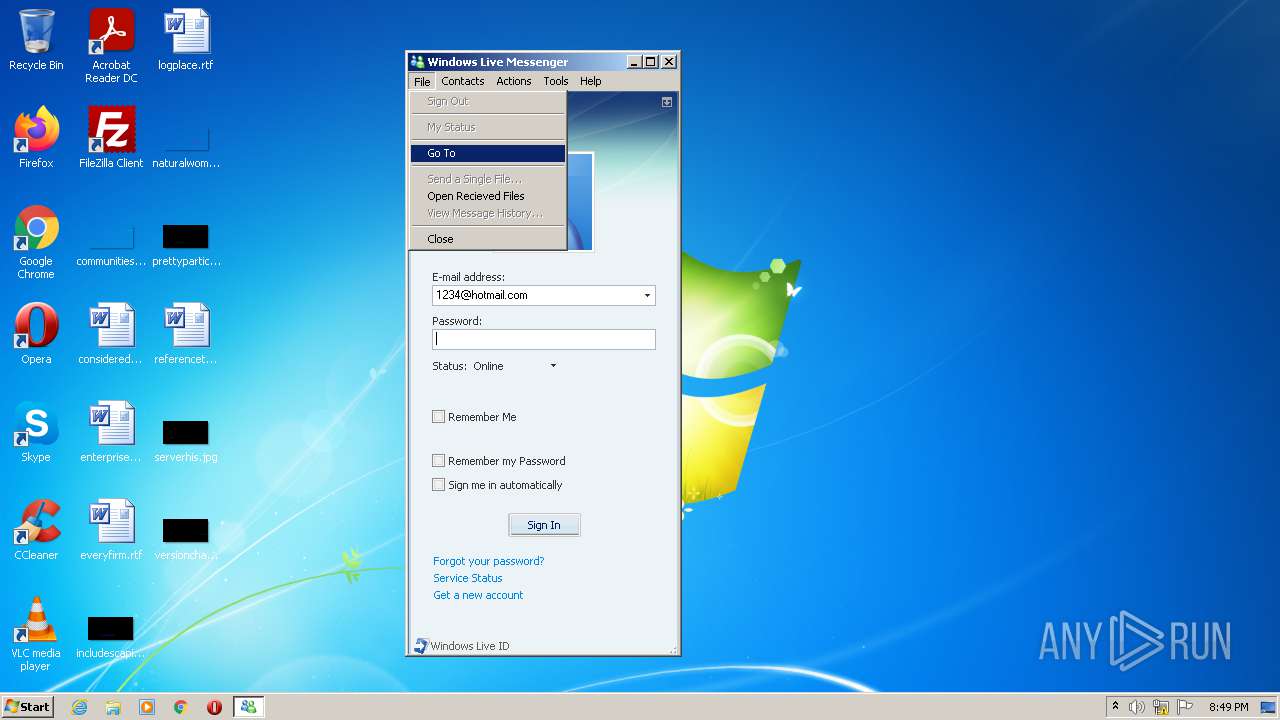
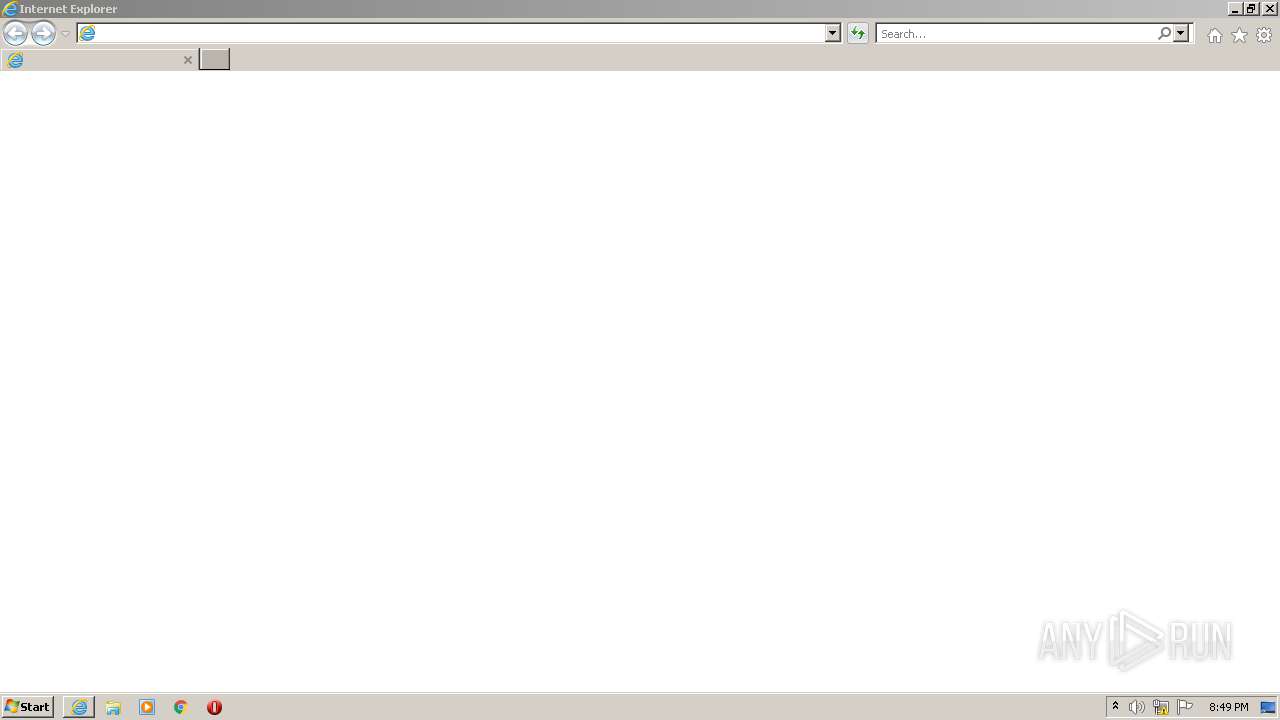
Starts Internet Explorer
- Fake Windows Live Messenger.exe (PID: 2932)
Reads the computer name
- Fake Windows Live Messenger.exe (PID: 2932)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3500)
- iexplore.exe (PID: 1044)
Checks supported languages
- Fake Windows Live Messenger.exe (PID: 2932)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 1792)
Reads the computer name
- iexplore.exe (PID: 1044)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 1792)
- iexplore.exe (PID: 3500)
Checks Windows Trust Settings
- iexplore.exe (PID: 1044)
- iexplore.exe (PID: 3500)
- iexplore.exe (PID: 1792)
Reads settings of System Certificates
- iexplore.exe (PID: 1044)
- iexplore.exe (PID: 3500)
- iexplore.exe (PID: 1792)
Application launched itself
- iexplore.exe (PID: 1792)
- iexplore.exe (PID: 3676)
Checks supported languages
- iexplore.exe (PID: 1044)
- iexplore.exe (PID: 3500)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 1792)
Reads the date of Windows installation
- iexplore.exe (PID: 3676)
Creates files in the user directory
- iexplore.exe (PID: 3500)
Reads internet explorer settings
- iexplore.exe (PID: 3500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (69.8) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 6 (27.5) |
| .exe | | | Win32 Executable Delphi generic (1.4) |
| .exe | | | Win32 Executable (generic) (0.4) |
| .exe | | | Win16/32 Executable Delphi generic (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 616960 |
| InitializedDataSize: | 895488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x978cc |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (Australian) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00096944 | 0x00096A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52596 |
DATA | 0x00098000 | 0x00002334 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.67346 |
BSS | 0x0009B000 | 0x0000128D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0009D000 | 0x00002724 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98391 |
.tls | 0x000A0000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000A1000 | 0x00000031 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.613322 |
.reloc | 0x000A2000 | 0x0000B614 | 0x0000B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.62207 |
.rsrc | 0x000AE000 | 0x000CA400 | 0x000CA400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.66013 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.95218 | 581 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.1978 | 744 | UNKNOWN | English - Australia | RT_ICON |
3 | 3.27962 | 488 | UNKNOWN | English - Australia | RT_ICON |
4 | 3.1513 | 296 | UNKNOWN | English - Australia | RT_ICON |
5 | 5.07571 | 3752 | UNKNOWN | English - Australia | RT_ICON |
6 | 5.61607 | 2216 | UNKNOWN | English - Australia | RT_ICON |
7 | 5.34187 | 1736 | UNKNOWN | English - Australia | RT_ICON |
8 | 3.93856 | 1384 | UNKNOWN | English - Australia | RT_ICON |
9 | 4.56555 | 9640 | UNKNOWN | English - Australia | RT_ICON |
10 | 4.61153 | 4264 | UNKNOWN | English - Australia | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
40
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3676 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
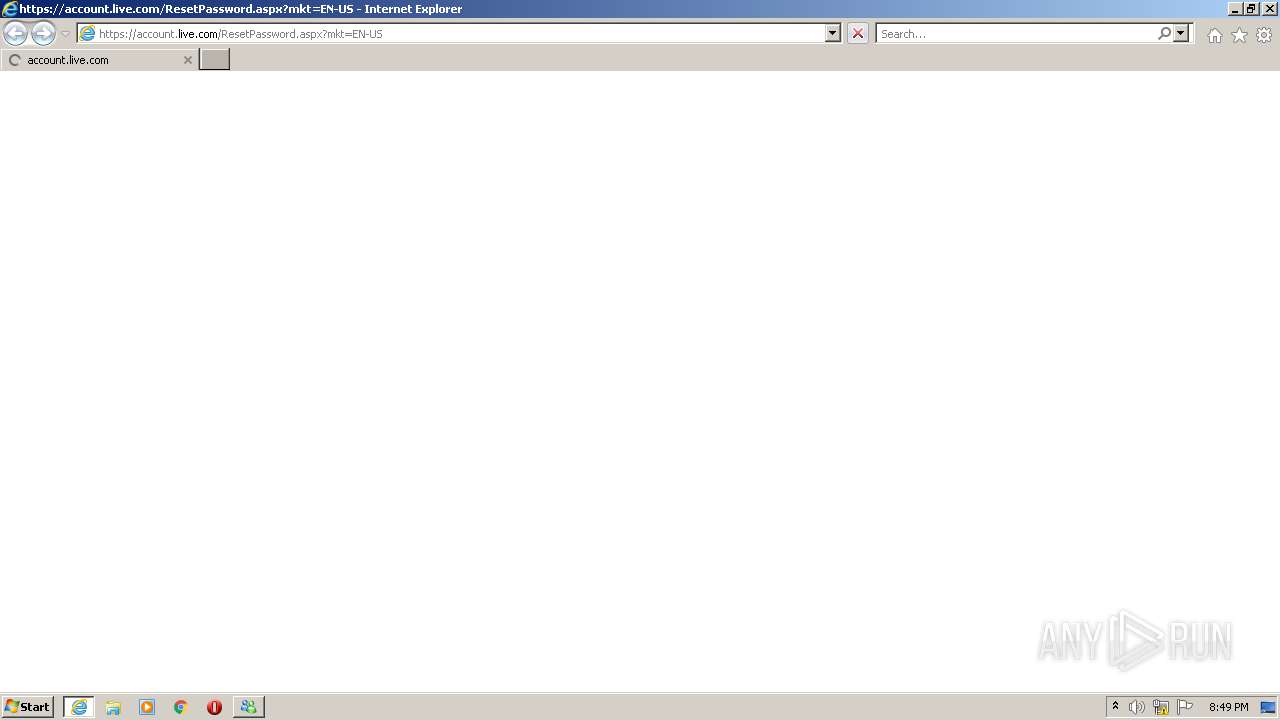
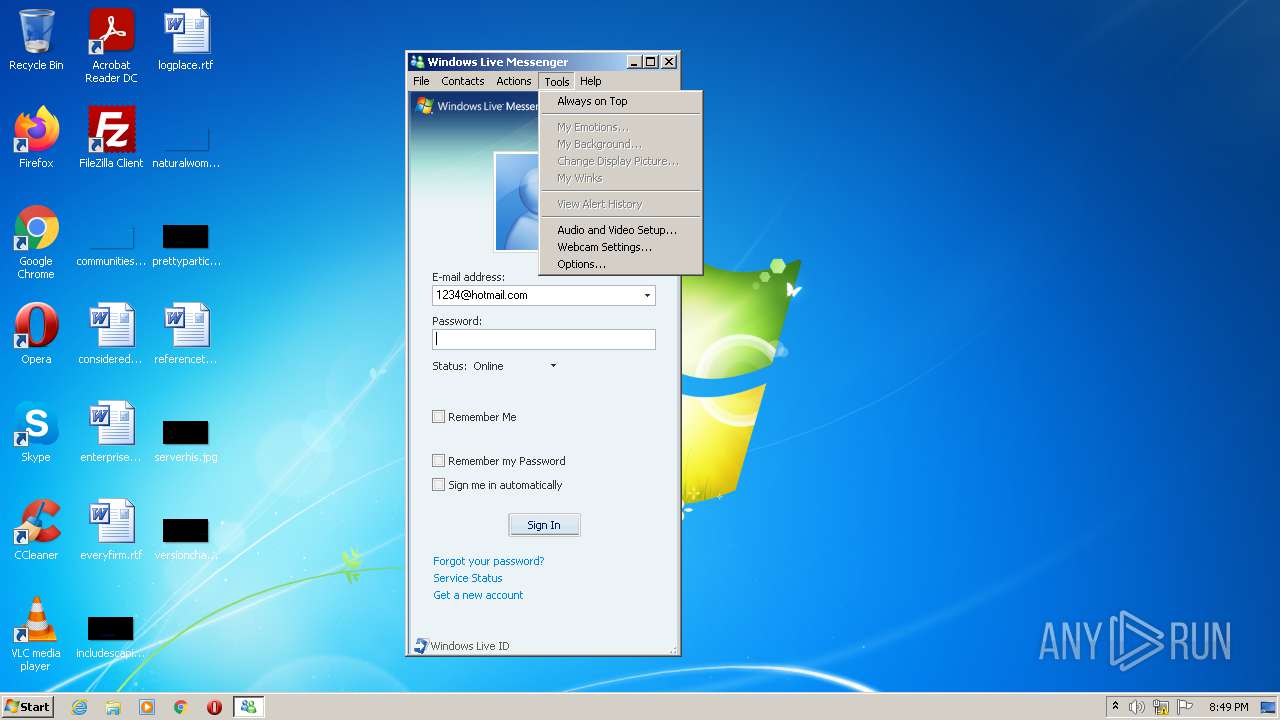
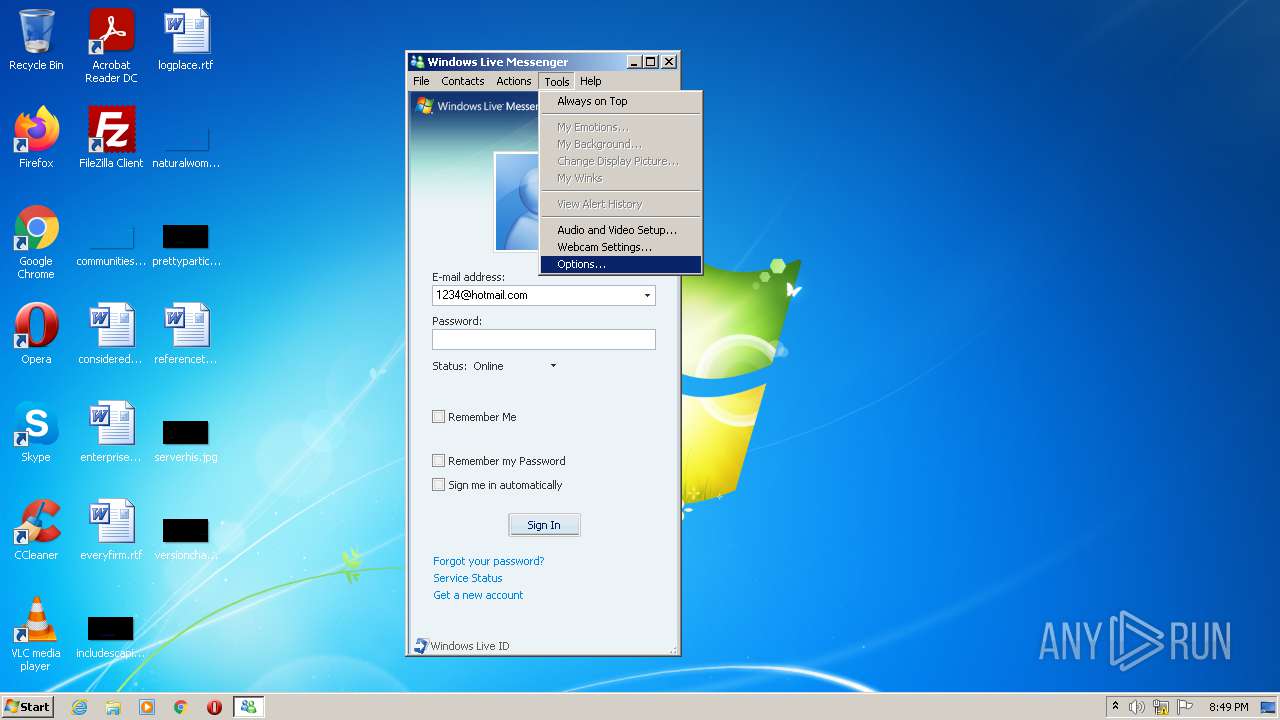
| 1792 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.ourgodfather.com/ | C:\Program Files\Internet Explorer\iexplore.exe | Fake Windows Live Messenger.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2932 | "C:\Users\admin\AppData\Local\Temp\Fake Windows Live Messenger.exe" | C:\Users\admin\AppData\Local\Temp\Fake Windows Live Messenger.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3500 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1792 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3676 | "C:\Program Files\Internet Explorer\iexplore.exe" https://account.live.com/ResetPassword.aspx?mkt=EN-US | C:\Program Files\Internet Explorer\iexplore.exe | — | Fake Windows Live Messenger.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
18 769
Read events
18 641
Write events
126
Delete events
2
Modification events
| (PID) Process: | (2932) Fake Windows Live Messenger.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30920948 | |||
| (PID) Process: | (3676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30920948 | |||
| (PID) Process: | (3676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
0
Suspicious files
13
Text files
13
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4A3CA6A2AA940668.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{809C5EEE-3CE7-11EC-A58D-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{809C5EED-3CE7-11EC-A58D-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{809C5EEB-3CE7-11EC-A58D-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3500 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\3B3GJ7OM.htm | html | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF93DA586498CF918F.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF74C99680AC46FE96.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7BF5D19E60EC5675.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
27
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3500 | iexplore.exe | GET | 302 | 103.224.212.222:80 | http://www.ourgodfather.com/ | AU | — | — | malicious |
1792 | iexplore.exe | GET | 200 | 199.59.242.153:80 | http://ww25.ourgodfather.com/favicon.ico | US | — | — | malicious |
3500 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDz5qDIB%2BmEgCgAAAAEQNfA%3D | US | der | 471 b | whitelisted |
3500 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAiWJA%2FUYGrvCgAAAAEQNk8%3D | US | der | 471 b | whitelisted |
3500 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDSrFfrqDWYRQoAAAABCK7b | US | der | 472 b | whitelisted |
3500 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3500 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3500 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC4L7mL%2BbzHKwoAAAABCK3S | US | der | 472 b | whitelisted |
1044 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7d1cfc22eb5ca9e5 | US | compressed | 4.70 Kb | whitelisted |
3500 | iexplore.exe | GET | 200 | 199.59.242.153:80 | http://ww25.ourgodfather.com/px.gif?ch=1&rn=7.879676339747634 | US | image | 42 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1044 | iexplore.exe | 13.107.42.22:443 | account.live.com | Microsoft Corporation | US | suspicious |
1044 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1044 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3500 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3500 | iexplore.exe | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1792 | iexplore.exe | 199.59.242.153:80 | ww25.ourgodfather.com | Bodis, LLC | US | malicious |
3500 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3500 | iexplore.exe | 142.250.186.33:443 | afs.googleusercontent.com | Google Inc. | US | whitelisted |
3500 | iexplore.exe | 172.66.40.199:443 | parking.bodiscdn.com | — | US | suspicious |
1792 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
account.live.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.ourgodfather.com |
| malicious |
ww25.ourgodfather.com |
| malicious |
parking.bodiscdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
ocsp.pki.goog |
| whitelisted |
afs.googleusercontent.com |
| whitelisted |