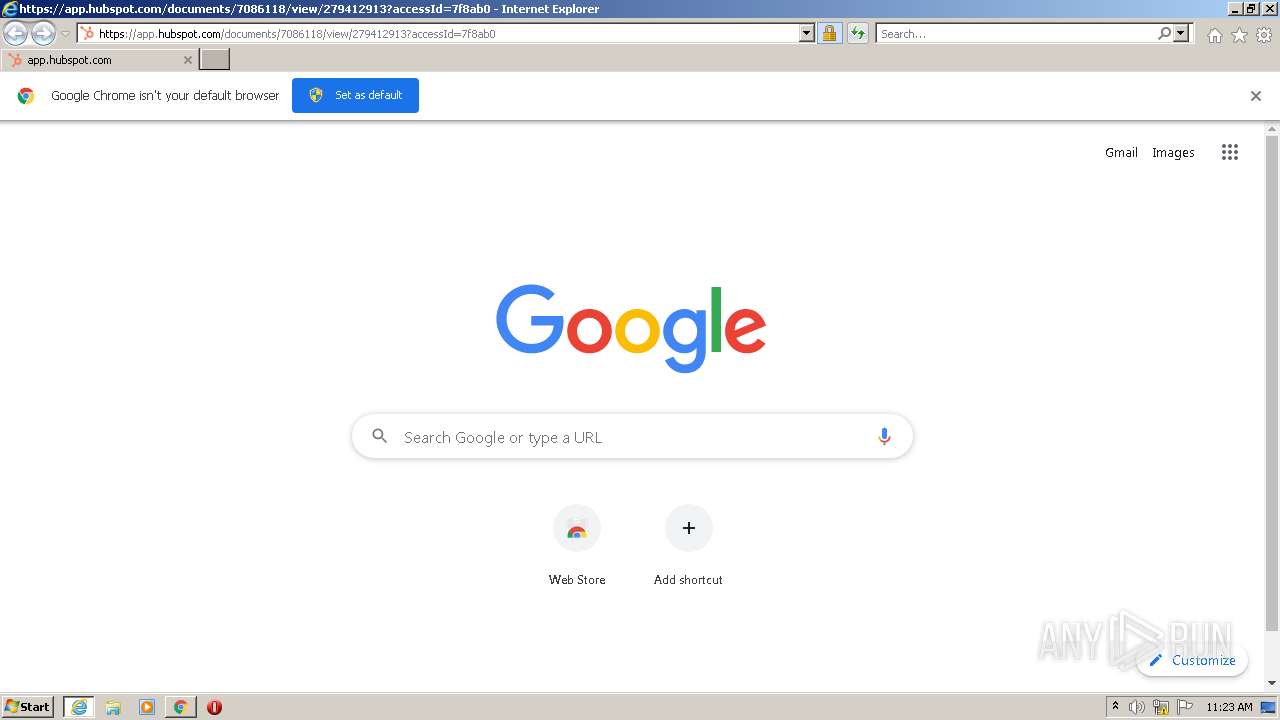
| URL: | https://streaklinks.com/A-Zb-UQCwnV5hpBrZQaxP9EF/https%3A%2F%2Ft.sidekickopen14.com%2Fs3t%2Fc%2F5%2Ff18dQhb0S7kF8bGbY4V7jsn959hl3kW7_k2841CXdp3VPwQX259j2RdW2bzNM566wwtJ101%3Fte%3DW3R5hFj4cm2zwW3R5HxG1JCh31W2-bjVt3M6vVd1W3%26si%3D8000000002853260%26pi%3D21ebc477-1004-4e33-aef2-48d5afbb8319 |
| Full analysis: | https://app.any.run/tasks/42223509-ff84-43ad-862e-53ae56483e9a |
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2022, 11:22:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FC143CC7DE1FD94583FE982532D46DFF |
| SHA1: | D252F3FFF78364139C6FDE277AD1987E4A1C3364 |
| SHA256: | 6B31D93170FAD10A78AA11E37F228DF16DCFDFDE0E3ABBE9D14AB8F0B617EA0B |
| SSDEEP: | 6:2cRPrIWHv9R4z7rYUyTjdvj12+Pd8ODpiJ6j0trP1ThDJIQPm1nO:2cRPrIWHvf4sUyvQ+Pqgi1tFhDJyg |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3480)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1484)
INFO
Reads the computer name
- iexplore.exe (PID: 2848)
- iexplore.exe (PID: 3480)
- chrome.exe (PID: 1484)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 544)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 3844)
- chrome.exe (PID: 3076)
Application launched itself
- iexplore.exe (PID: 2848)
- chrome.exe (PID: 1484)
Changes internet zones settings
- iexplore.exe (PID: 2848)
Checks supported languages
- iexplore.exe (PID: 3480)
- iexplore.exe (PID: 2848)
- chrome.exe (PID: 1484)
- chrome.exe (PID: 448)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 544)
- chrome.exe (PID: 1892)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 940)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 1388)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 3844)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 2796)
Reads settings of System Certificates
- iexplore.exe (PID: 2848)
- iexplore.exe (PID: 3480)
- chrome.exe (PID: 544)
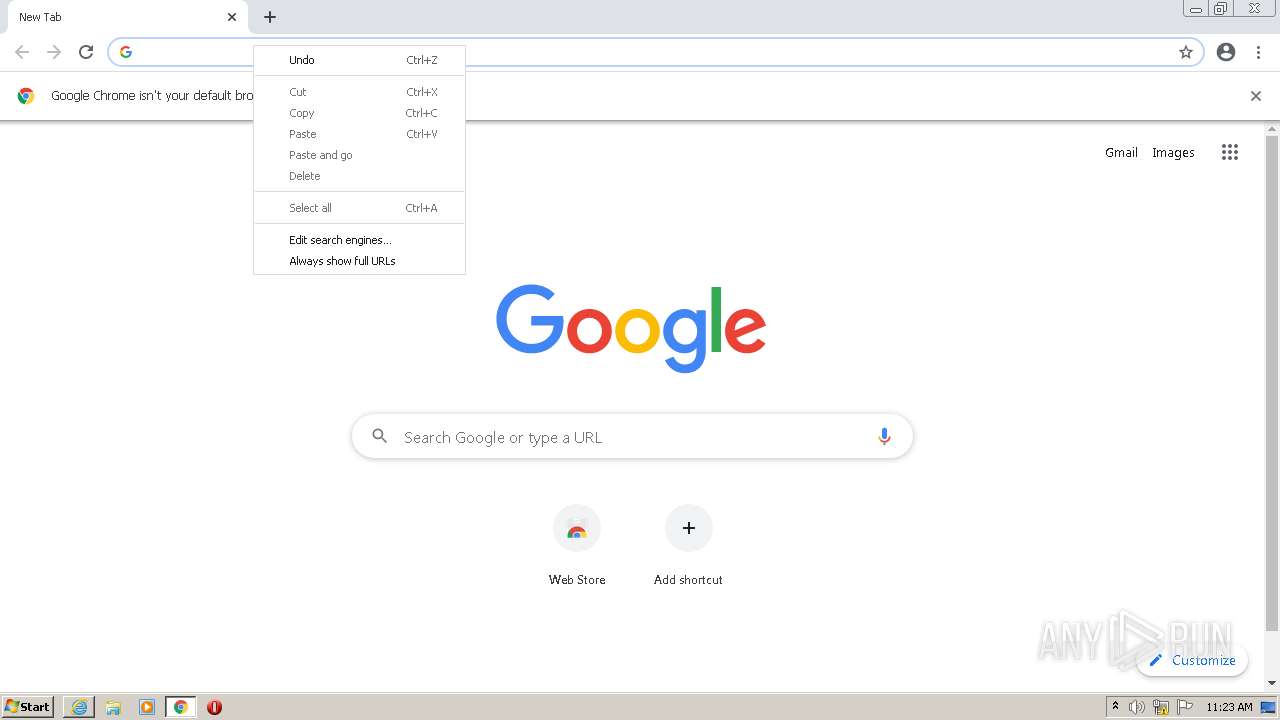
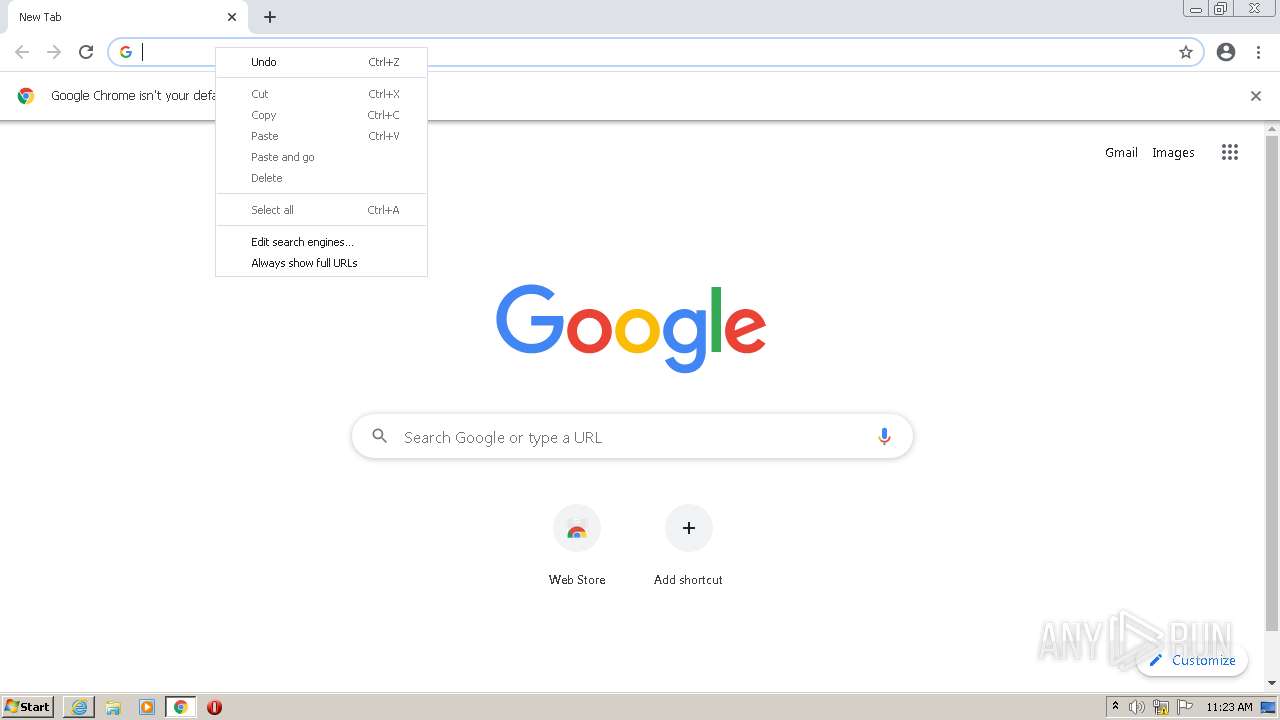
Manual execution by user
- chrome.exe (PID: 1484)
Checks Windows Trust Settings
- iexplore.exe (PID: 3480)
- iexplore.exe (PID: 2848)
Creates files in the user directory
- iexplore.exe (PID: 3480)
- iexplore.exe (PID: 2848)
Reads internet explorer settings
- iexplore.exe (PID: 3480)
Reads the hosts file
- chrome.exe (PID: 1484)
- chrome.exe (PID: 544)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2848)
Changes settings of System certificates
- iexplore.exe (PID: 2848)
Reads the date of Windows installation
- chrome.exe (PID: 3844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6d7cd988,0x6d7cd998,0x6d7cd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1028,525068594247950997,5250322750707809526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1324 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,525068594247950997,5250322750707809526,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,525068594247950997,5250322750707809526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3348 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,525068594247950997,5250322750707809526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,525068594247950997,5250322750707809526,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1048 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,525068594247950997,5250322750707809526,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,525068594247950997,5250322750707809526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3312 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,525068594247950997,5250322750707809526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
26 156
Read events
25 910
Write events
242
Delete events
4
Modification events
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30948026 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30948026 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
139
Text files
143
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | der | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE26C.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B552857B7CEB5355D6C7051DA9C67F8B | der | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE26D.tmp | cat | |
MD5:— | SHA256:— | |||
| 2848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
82
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/chvgfzquqifl6g26355pi36lfi_2785/jflookgnkcckhobaglndicnbbgbonegd_2785_all_a7lwfjuistudq4lqovqwch5bba.crx3 | US | — | — | whitelisted |
884 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/chvgfzquqifl6g26355pi36lfi_2785/jflookgnkcckhobaglndicnbbgbonegd_2785_all_a7lwfjuistudq4lqovqwch5bba.crx3 | US | — | — | whitelisted |
884 | svchost.exe | HEAD | 200 | 74.125.108.202:80 | http://r5---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/chvgfzquqifl6g26355pi36lfi_2785/jflookgnkcckhobaglndicnbbgbonegd_2785_all_a7lwfjuistudq4lqovqwch5bba.crx3?cms_redirect=yes&mh=mk&mip=85.203.45.35&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1647602182&mv=m&mvi=5&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=sd&smhost=r3---sn-1gi7znes.gvt1.com | US | — | — | whitelisted |
3480 | iexplore.exe | GET | 200 | 23.45.105.185:80 | http://x2.c.lencr.org/ | NL | der | 299 b | whitelisted |
3480 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://e1.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBTvkAFw3ViPKmUeIVEf3NC7b1ErqwQUWvPtK%2Fw2wjd5uVIw6lRvz1XLLqwCEgOlH3Qt3c%2Fz6DEeetZIDWQRgw%3D%3D | unknown | der | 345 b | whitelisted |
3480 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAk%2FDxpj2R8qVKwhgRZ1eqY%3D | US | der | 278 b | whitelisted |
3480 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAq8OIHnzLSr2KkUf52Yg8I%3D | US | der | 471 b | whitelisted |
3480 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
2848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3480 | iexplore.exe | 104.21.18.24:443 | streaklinks.com | Cloudflare Inc | US | unknown |
3480 | iexplore.exe | 23.45.105.185:80 | x1.c.lencr.org | Akamai International B.V. | NL | unknown |
2848 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3480 | iexplore.exe | 2.16.186.10:80 | e1.o.lencr.org | Akamai International B.V. | — | whitelisted |
2848 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3480 | iexplore.exe | 104.18.16.69:443 | t.sidekickopen14.com | Cloudflare Inc | US | unknown |
3480 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3480 | iexplore.exe | 104.19.154.83:443 | app.hubspot.com | Cloudflare Inc | US | suspicious |
3480 | iexplore.exe | 104.17.212.204:443 | js.hs-scripts.com | Cloudflare Inc | US | shared |
— | — | 104.17.129.171:443 | js.hscollectedforms.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
streaklinks.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
e1.o.lencr.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
t.sidekickopen14.com |
| unknown |
hubs.ly |
| whitelisted |