| File name: | SPAM2.zip |
| Full analysis: | https://app.any.run/tasks/1090c7ea-e4bd-47e6-b7a5-e3d58515ad83 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 12:42:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7634D55251DFF9511B6552D7BF229FAC |
| SHA1: | 679CC7F4511A1D6433F51EBE5EFA0D84FC186B86 |
| SHA256: | 6B2362F0644A425CE0287FE590F3FC15DEC81616207FA42B54630F8C5B0CD872 |
| SSDEEP: | 6144:qAz36yWdiksDRpeu1ls/qZ2Ei1ElHmFl7Az36yWdiksDRpeu1ls/qZ2Ei1ElHm8U:l2YxYu1lGRVmhq82YxYu1lGRVmhVW |
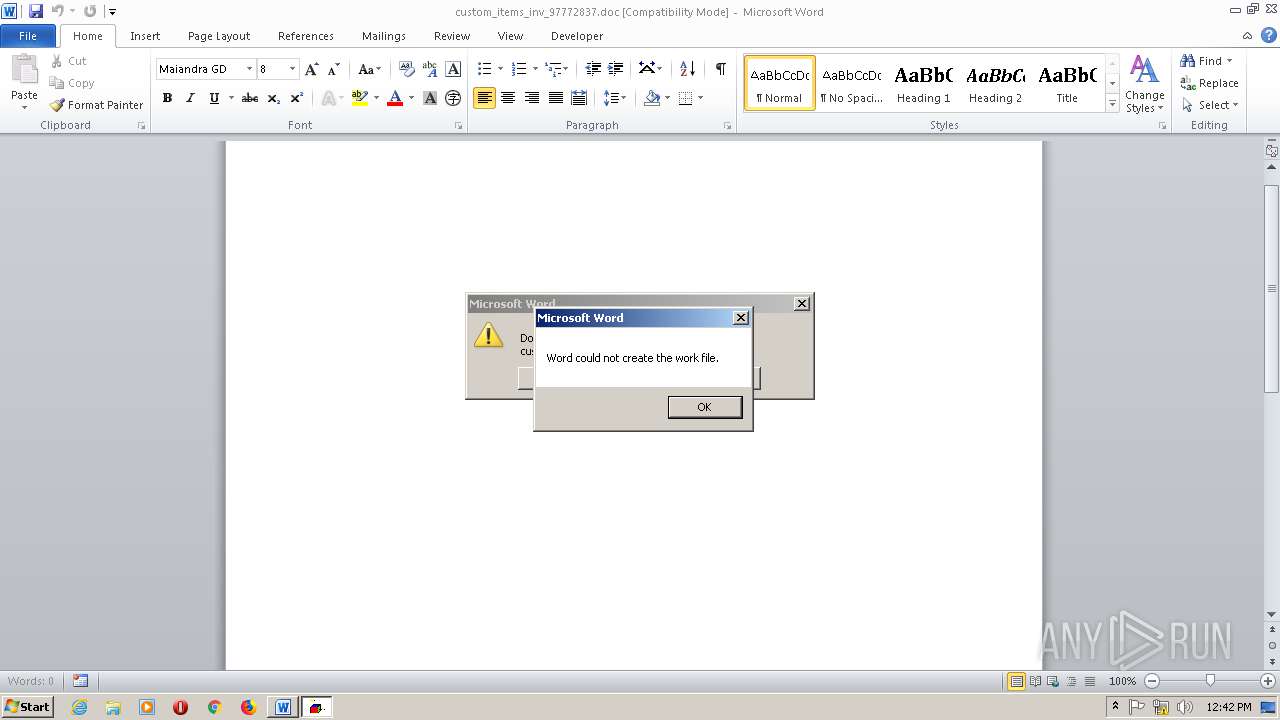
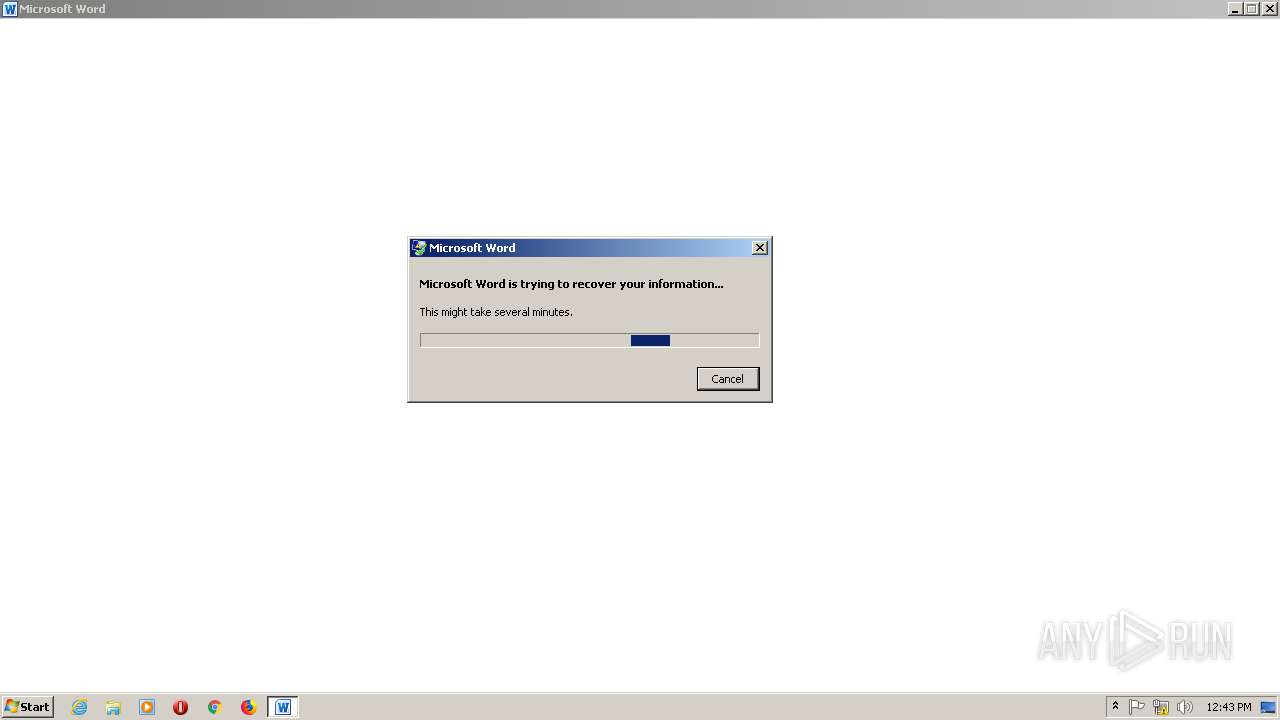
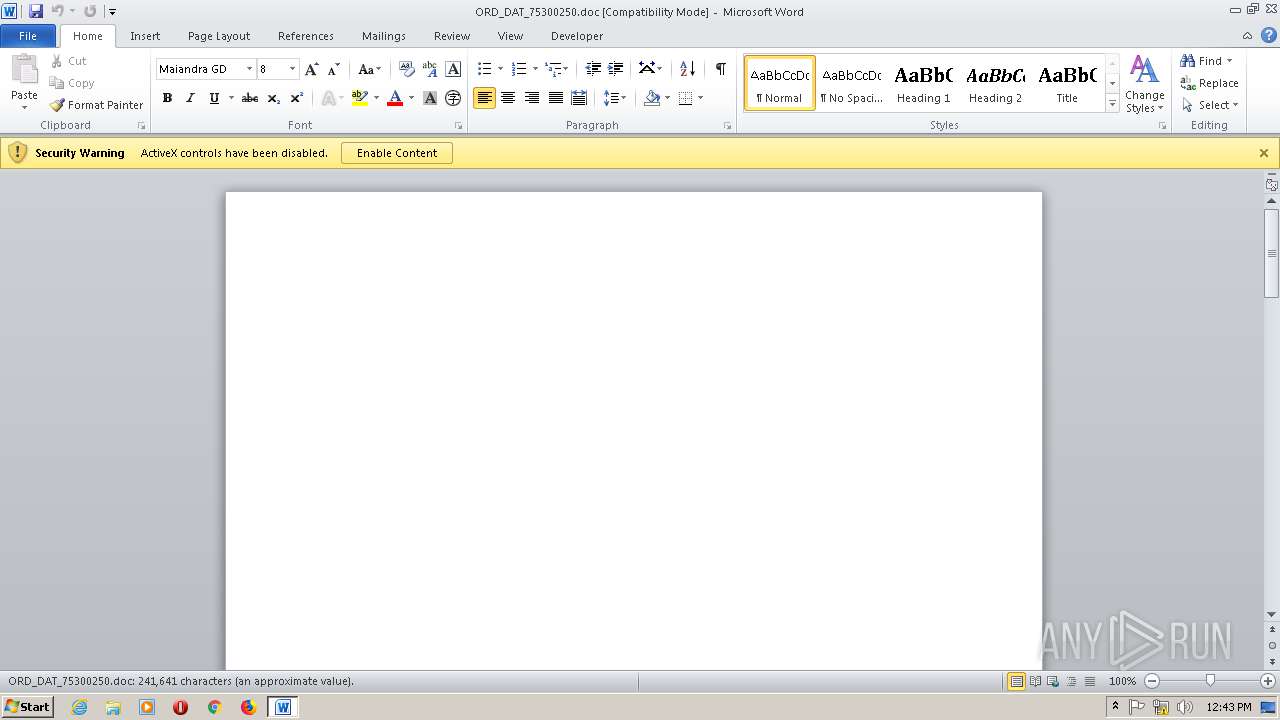
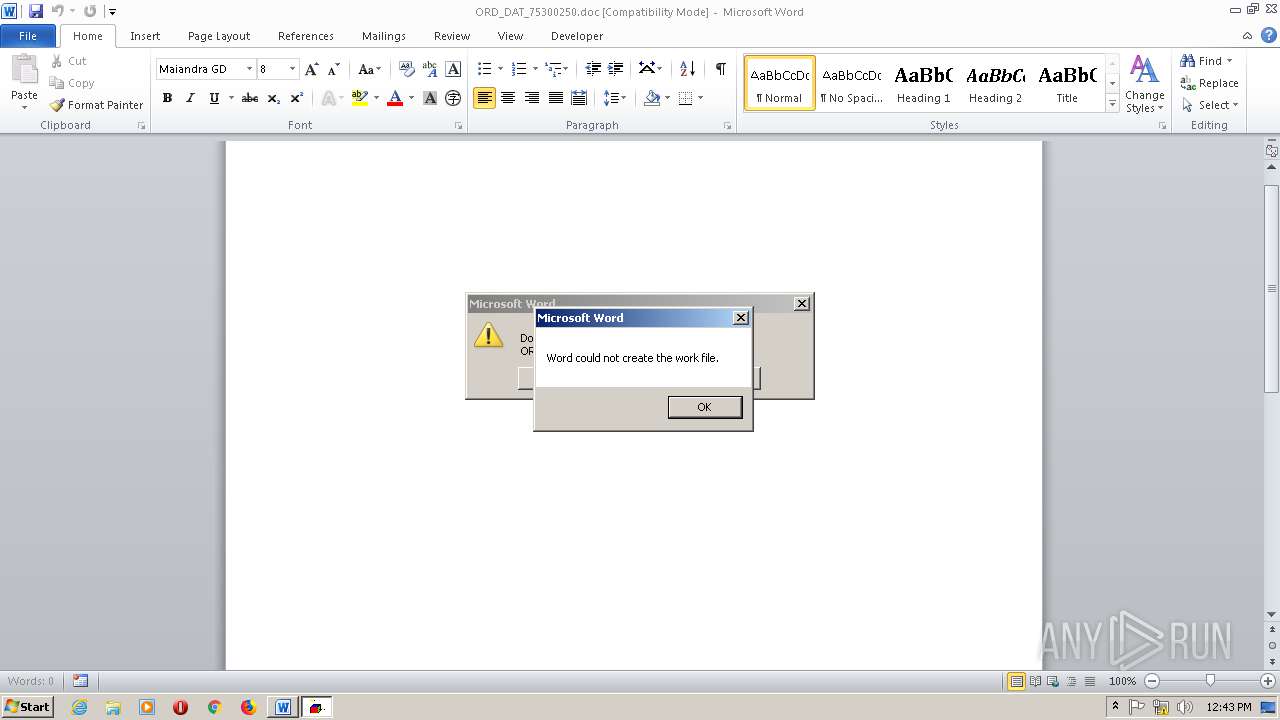
MALICIOUS
Executes scripts
- WINWORD.EXE (PID: 2880)
- WINWORD.EXE (PID: 2472)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2880)
- WINWORD.EXE (PID: 2472)
SUSPICIOUS
Reads the machine GUID from the registry
- WinRAR.exe (PID: 964)
- WScript.exe (PID: 1360)
- WScript.exe (PID: 2376)
INFO
Manual execution by user
- WINWORD.EXE (PID: 2880)
- WINWORD.EXE (PID: 2472)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2880)
- WINWORD.EXE (PID: 2472)
Creates files in the user directory
- WINWORD.EXE (PID: 2880)
- WINWORD.EXE (PID: 2472)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2472)
- WINWORD.EXE (PID: 2880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
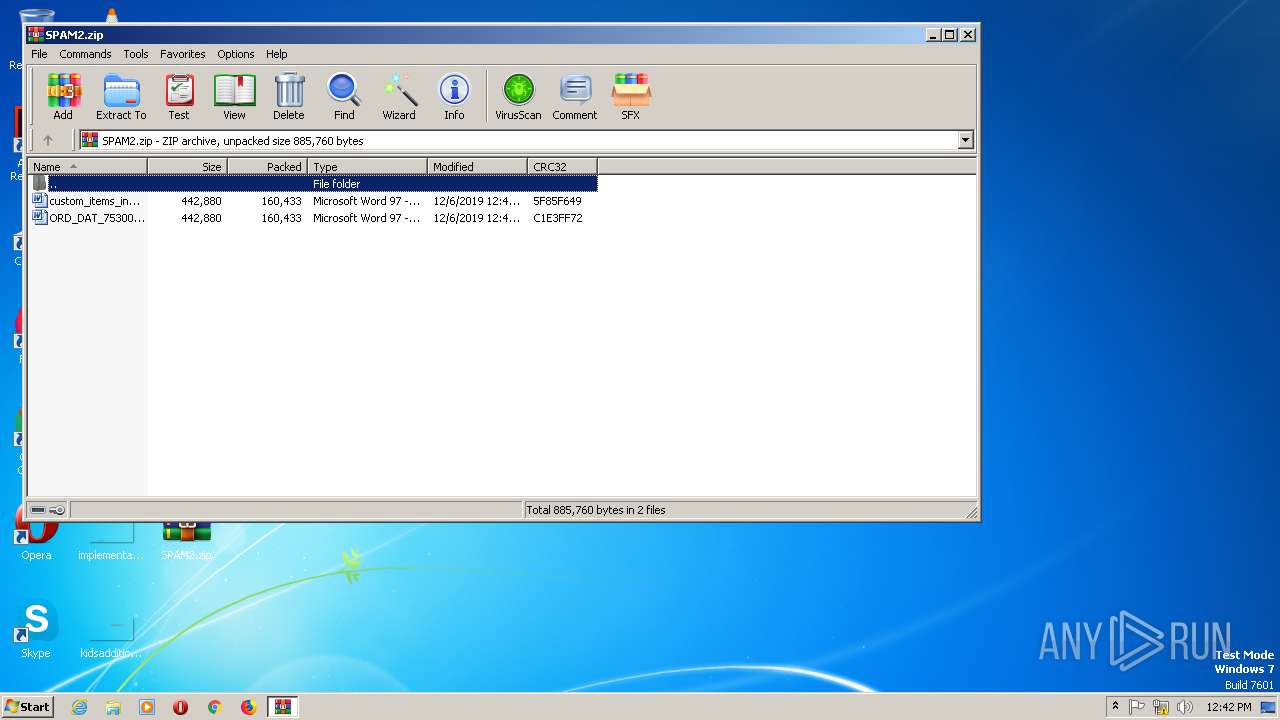
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:06 13:41:18 |
| ZipCRC: | 0x5f85f649 |
| ZipCompressedSize: | 160433 |
| ZipUncompressedSize: | 442880 |
| ZipFileName: | custom_items_inv_97772837.doc |
Total processes
46
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | C:\Windows\system32\dwwin.exe -x -s 424 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 964 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\SPAM2.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1360 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Word\Activ\Life.jse" 1 | C:\Windows\System32\WScript.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
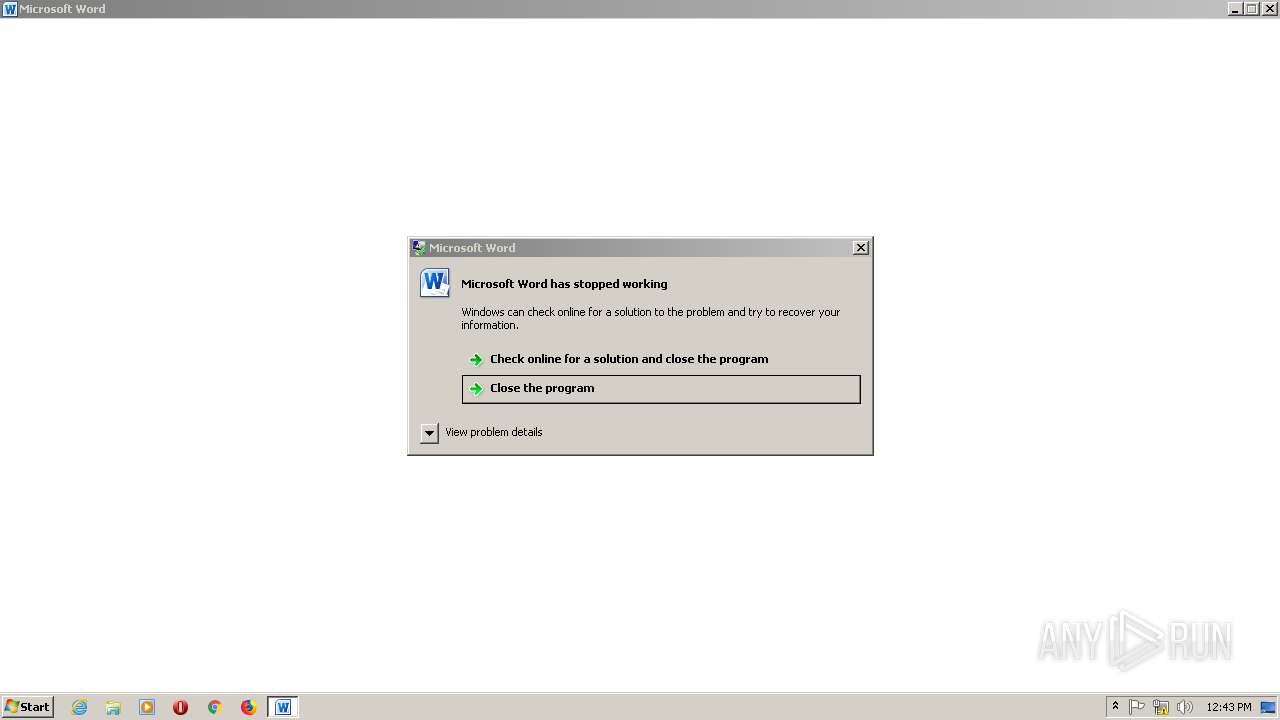
| 2248 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 424 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 2376 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Word\Activ\Life.jse" 1 | C:\Windows\System32\WScript.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\ORD_DAT_75300250.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2792 | C:\Windows\system32\dwwin.exe -x -s 424 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\custom_items_inv_97772837.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2896 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 424 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
Total events
3 782
Read events
2 865
Write events
561
Delete events
356
Modification events
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SPAM2.zip | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF1600000016000000D60300000B020000 | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
8
Text files
4
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 964 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa964.16835\custom_items_inv_97772837.doc | — | |
MD5:— | SHA256:— | |||
| 964 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa964.16835\ORD_DAT_75300250.doc | — | |
MD5:— | SHA256:— | |||
| 2880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6704.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\174FEC.wmf | — | |
MD5:— | SHA256:— | |||
| 2880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1FD5F8DA.wmf | — | |
MD5:— | SHA256:— | |||
| 2880 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF119E8721DA334CFF.TMP | — | |
MD5:— | SHA256:— | |||
| 2880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF2963F55C52E10DE.TMP | — | |
MD5:— | SHA256:— | |||
| 2880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{951DC69E-DCB1-4734-8A3A-7D4F3E98B944}.tmp | — | |
MD5:— | SHA256:— | |||
| 2880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF68ABE06B5AE207DD.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report