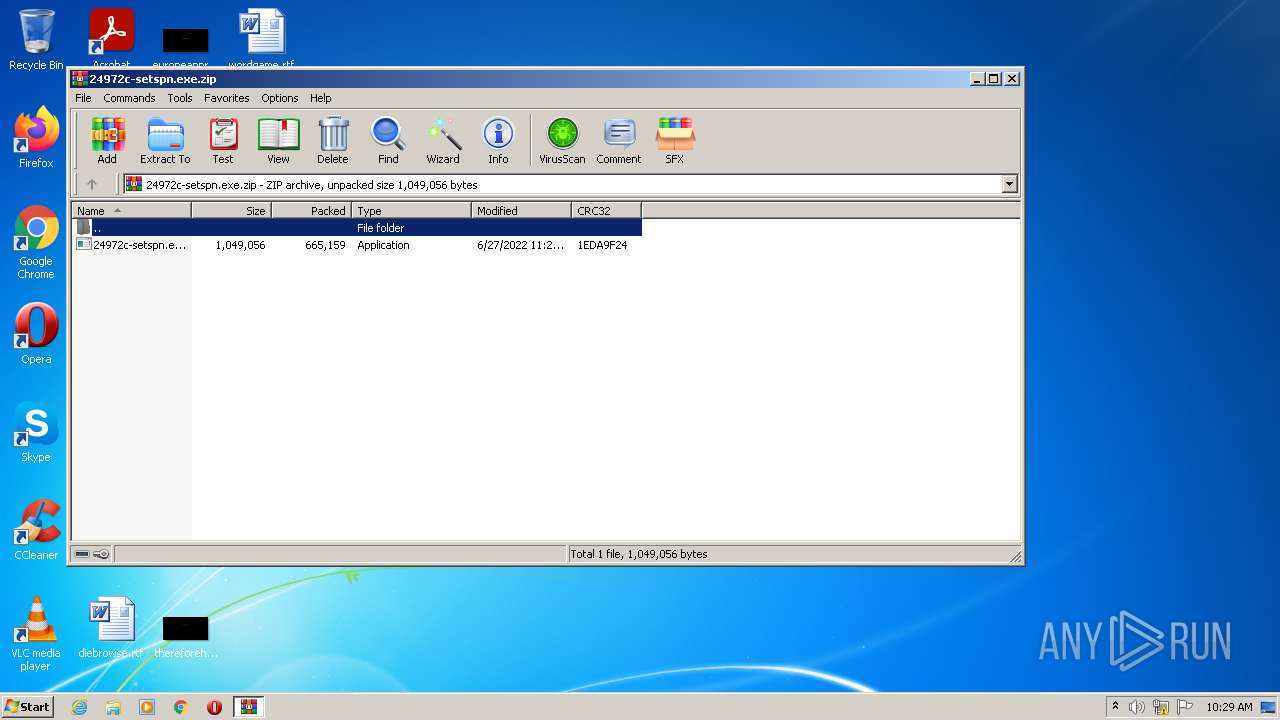
| File name: | 24972c-setspn.exe.zip |
| Full analysis: | https://app.any.run/tasks/80e7a1c5-3462-4f54-9fde-65f19b10b262 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 09:29:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2087AEF94456D7ADF20066FF5F718099 |
| SHA1: | 4CA243DAEE78D417E81D71BD4BDB9972E350D7E5 |
| SHA256: | 6B16FF52CA743BE9CC27E2BBC7FE14B9D9AE43B704B9DA0DFB29729B296217E0 |
| SSDEEP: | 12288:R18BHC25r3AfGgEJMregh2FY3068sOjD+VSLtyDLTJc+2smXsP+/4mpF6+yPq:zSDrx1MKghHrcnpLtyDLTJc+M82/4mSI |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 556)
Application was dropped or rewritten from another process
- 24972c-setspn.exe (PID: 3856)
- 24972c-setspn.exe (PID: 3580)
- 24972c-setspn.exe (PID: 2700)
- 24972c-setspn.exe (PID: 3196)
- 24972c-setspn.exe (PID: 900)
- 24972c-setspn.exe (PID: 3028)
Changes settings of System certificates
- 24972c-setspn.exe (PID: 3856)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 556)
- 24972c-setspn.exe (PID: 3856)
- 24972c-setspn.exe (PID: 3580)
- 24972c-setspn.exe (PID: 900)
- 24972c-setspn.exe (PID: 3028)
Checks supported languages
- WinRAR.exe (PID: 556)
- 24972c-setspn.exe (PID: 3856)
- 24972c-setspn.exe (PID: 3580)
- 24972c-setspn.exe (PID: 900)
- 24972c-setspn.exe (PID: 3028)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 556)
Adds / modifies Windows certificates
- 24972c-setspn.exe (PID: 3856)
Reads Environment values
- 24972c-setspn.exe (PID: 3580)
- 24972c-setspn.exe (PID: 3856)
- 24972c-setspn.exe (PID: 900)
- 24972c-setspn.exe (PID: 3028)
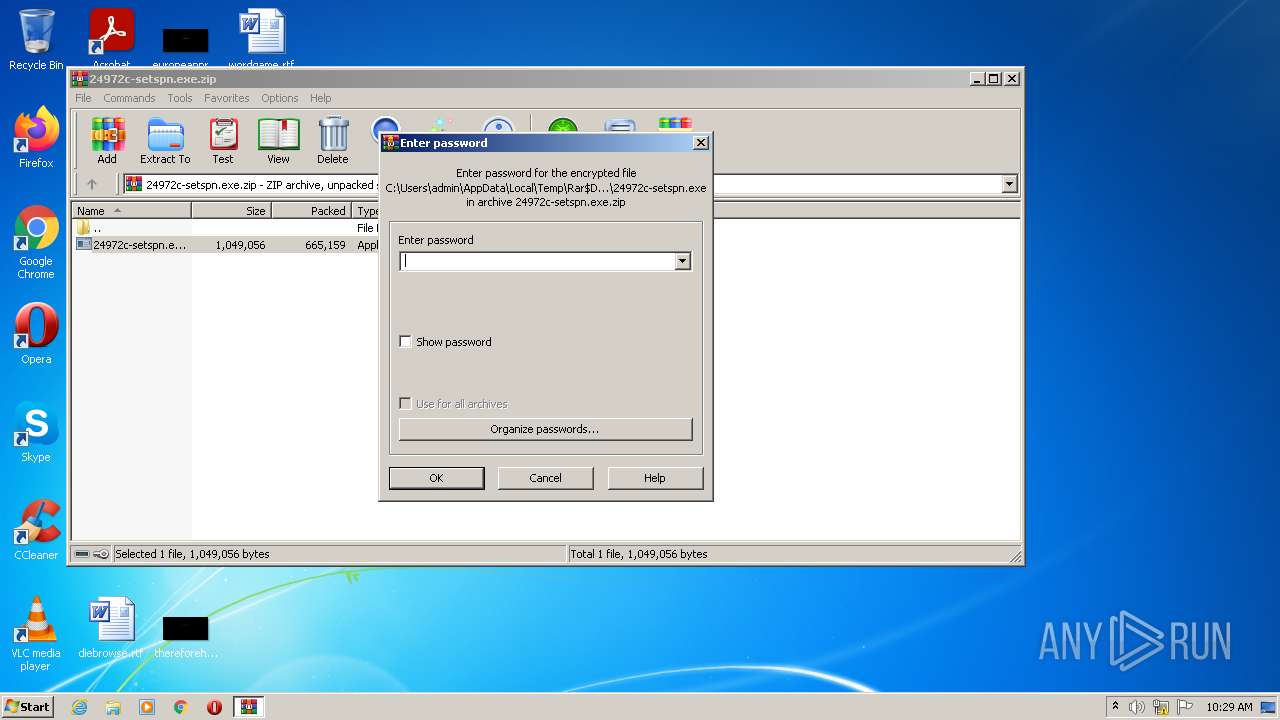
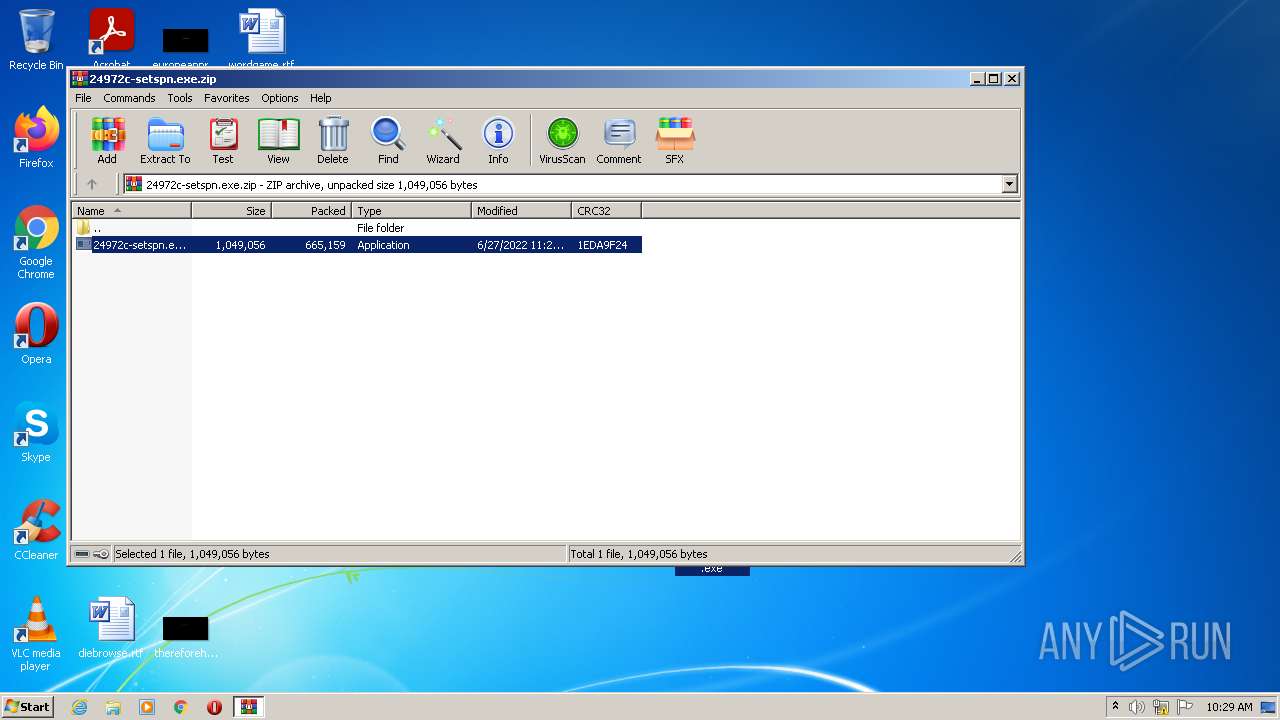
Executable content was dropped or overwritten
- WinRAR.exe (PID: 556)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2972)
INFO
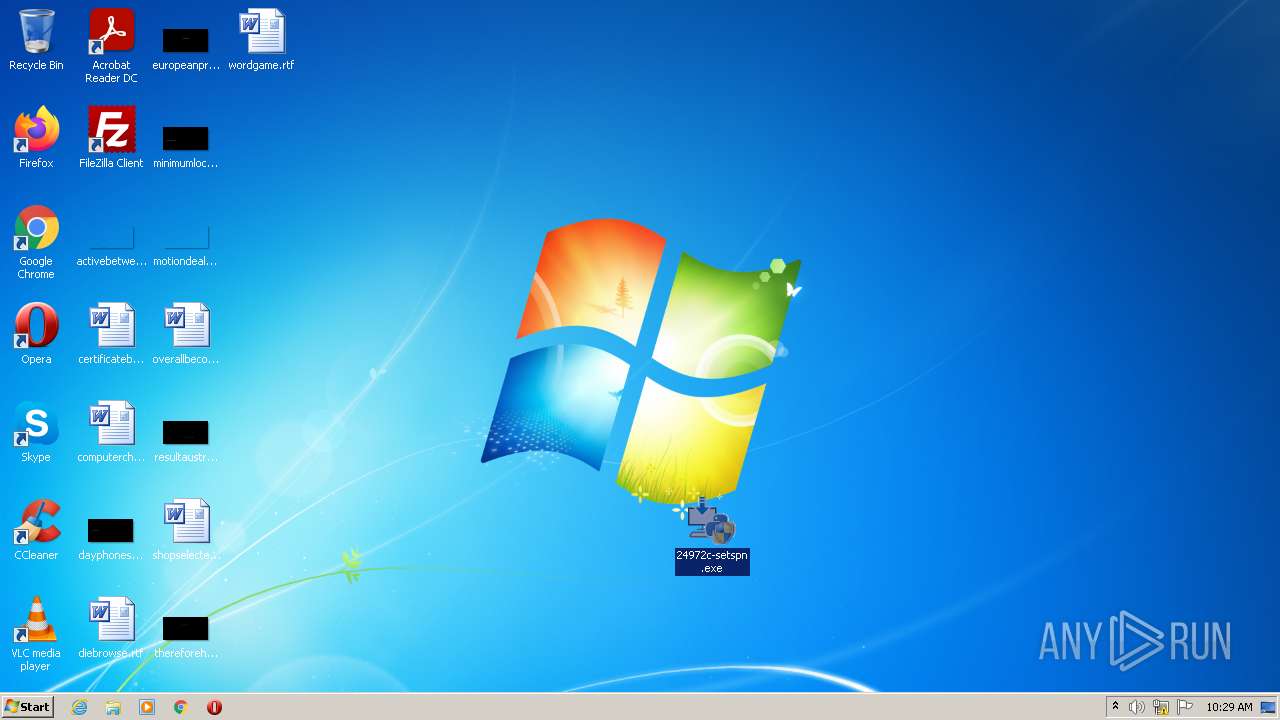
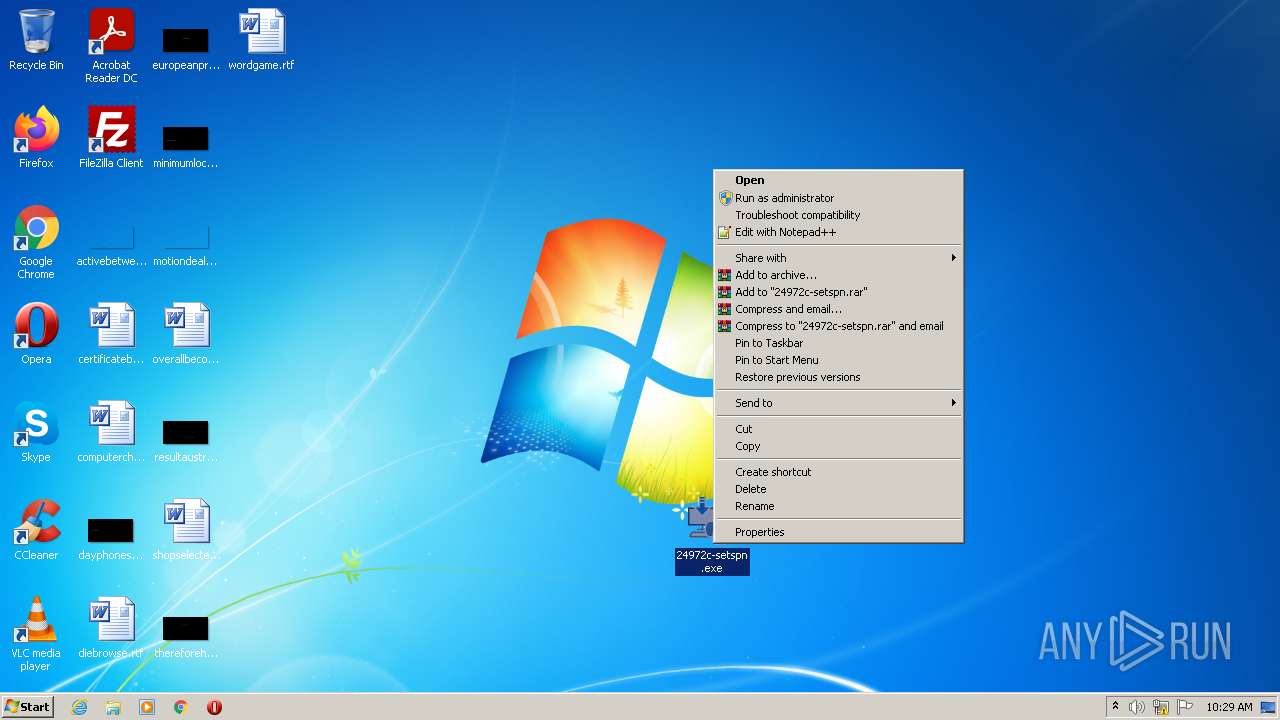
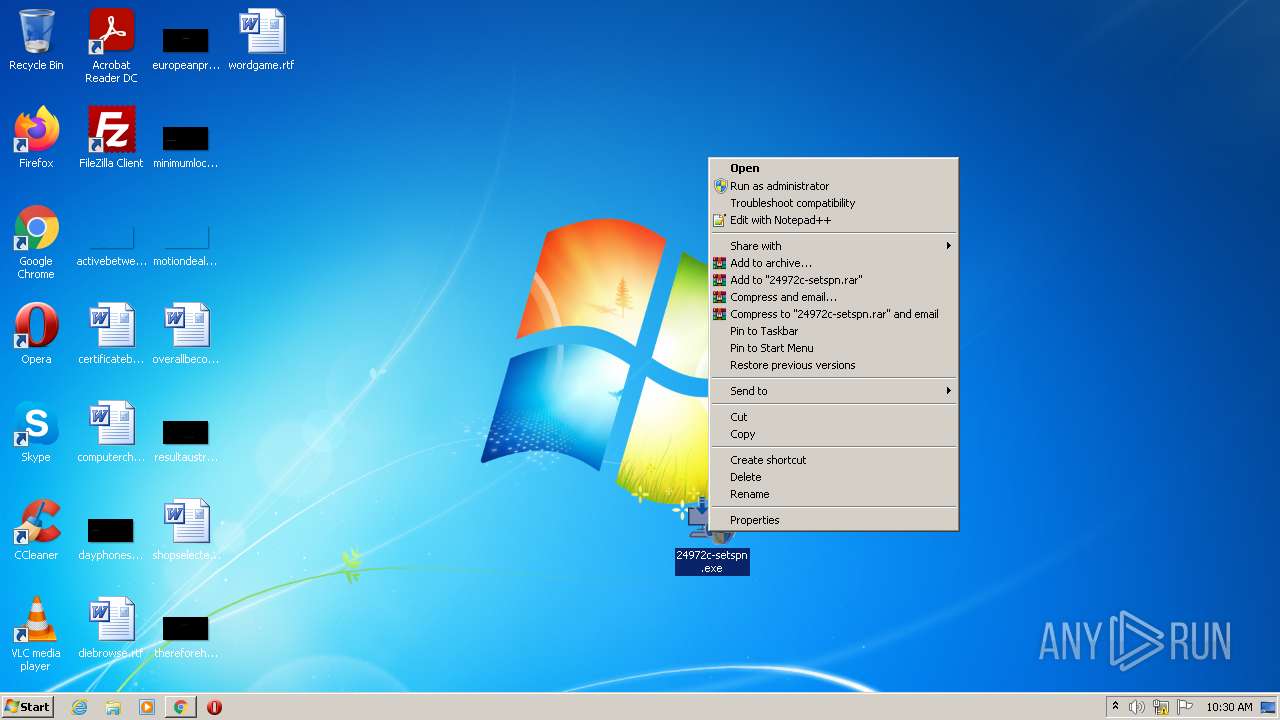
Manual execution by user
- 24972c-setspn.exe (PID: 3856)
- chrome.exe (PID: 2972)
- 24972c-setspn.exe (PID: 2700)
- 24972c-setspn.exe (PID: 3580)
- 24972c-setspn.exe (PID: 3196)
- 24972c-setspn.exe (PID: 900)
- 24972c-setspn.exe (PID: 3028)
Reads settings of System Certificates
- 24972c-setspn.exe (PID: 3856)
- chrome.exe (PID: 1956)
- 24972c-setspn.exe (PID: 3580)
- 24972c-setspn.exe (PID: 900)
- 24972c-setspn.exe (PID: 3028)
Reads the computer name
- chrome.exe (PID: 2972)
- chrome.exe (PID: 1956)
- chrome.exe (PID: 1688)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 2768)
Checks supported languages
- chrome.exe (PID: 2972)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 1688)
- chrome.exe (PID: 1956)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 3304)
Reads the hosts file
- chrome.exe (PID: 2972)
- chrome.exe (PID: 1956)
Application launched itself
- chrome.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | 24972c-setspn.exe |
|---|---|
| ZipUncompressedSize: | 1049056 |
| ZipCompressedSize: | 665159 |
| ZipCRC: | 0x1eda9f24 |
| ZipModifyDate: | 2022:06:27 11:20:17 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0009 |
| ZipRequiredVersion: | 20 |
Total processes
67
Monitored processes
21
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\24972c-setspn.exe.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 900 | "C:\Users\admin\Desktop\24972c-setspn.exe" | C:\Users\admin\Desktop\24972c-setspn.exe | Explorer.EXE | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: HIGH Description: Python 3.9.1 (64-bit) Exit code: 0 Version: 3.9.1150.0 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,15099068944846389740,13123675238246004613,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1028,15099068944846389740,13123675238246004613,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1316 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6dc9d988,0x6dc9d998,0x6dc9d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,15099068944846389740,13123675238246004613,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\Desktop\24972c-setspn.exe" | C:\Users\admin\Desktop\24972c-setspn.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.9.1 (64-bit) Exit code: 3221226540 Version: 3.9.1150.0 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,15099068944846389740,13123675238246004613,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3292 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,15099068944846389740,13123675238246004613,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 613
Read events
23 475
Write events
138
Delete events
0
Modification events
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\24972c-setspn.exe.zip | |||
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
106
Text files
74
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62B9789A-B9C.pma | — | |
MD5:— | SHA256:— | |||
| 556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb556.33845\24972c-setspn.exe | executable | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RFff4e6.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d17ec96a-0aba-44a8-a321-e3afa6c94283.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFff330.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFff340.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
34
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1956 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 591 b | whitelisted |
1956 | chrome.exe | GET | 200 | 74.125.111.8:80 | http://r3---sn-5goeenez.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=196.196.52.6&mm=28&mn=sn-5goeenez&ms=nvh&mt=1656321862&mv=m&mvi=3&pl=24&rmhost=r1---sn-5goeenez.gvt1.com&shardbypass=sd&smhost=r1---sn-5goeen76.gvt1.com | US | crx | 242 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3856 | 24972c-setspn.exe | 142.251.37.100:443 | www.google.com | Google Inc. | US | malicious |
1956 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 142.251.37.100:443 | www.google.com | Google Inc. | US | malicious |
1956 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1956 | chrome.exe | 142.250.184.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
1956 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1956 | chrome.exe | 142.251.36.131:443 | www.gstatic.com | Google Inc. | US | unknown |
1956 | chrome.exe | 142.250.185.110:443 | apis.google.com | Google Inc. | US | whitelisted |
900 | 24972c-setspn.exe | 142.251.37.100:443 | www.google.com | Google Inc. | US | malicious |
1956 | chrome.exe | 142.251.37.99:443 | ssl.gstatic.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |