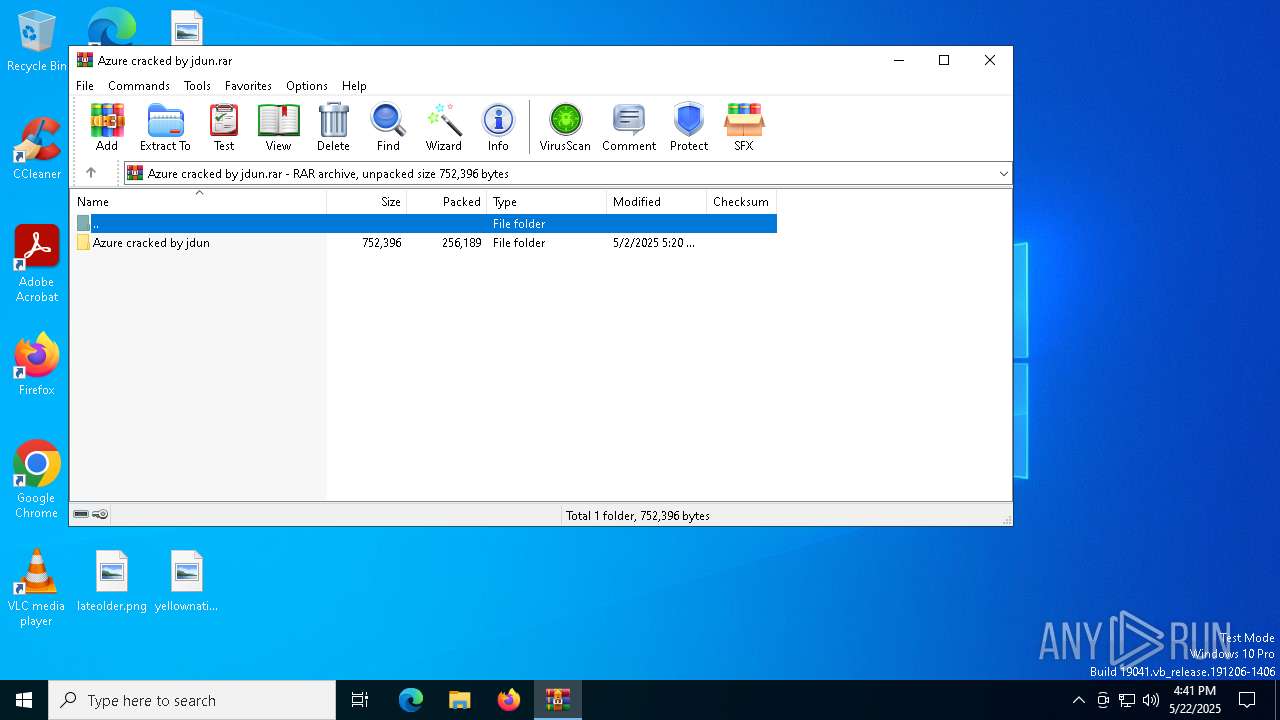
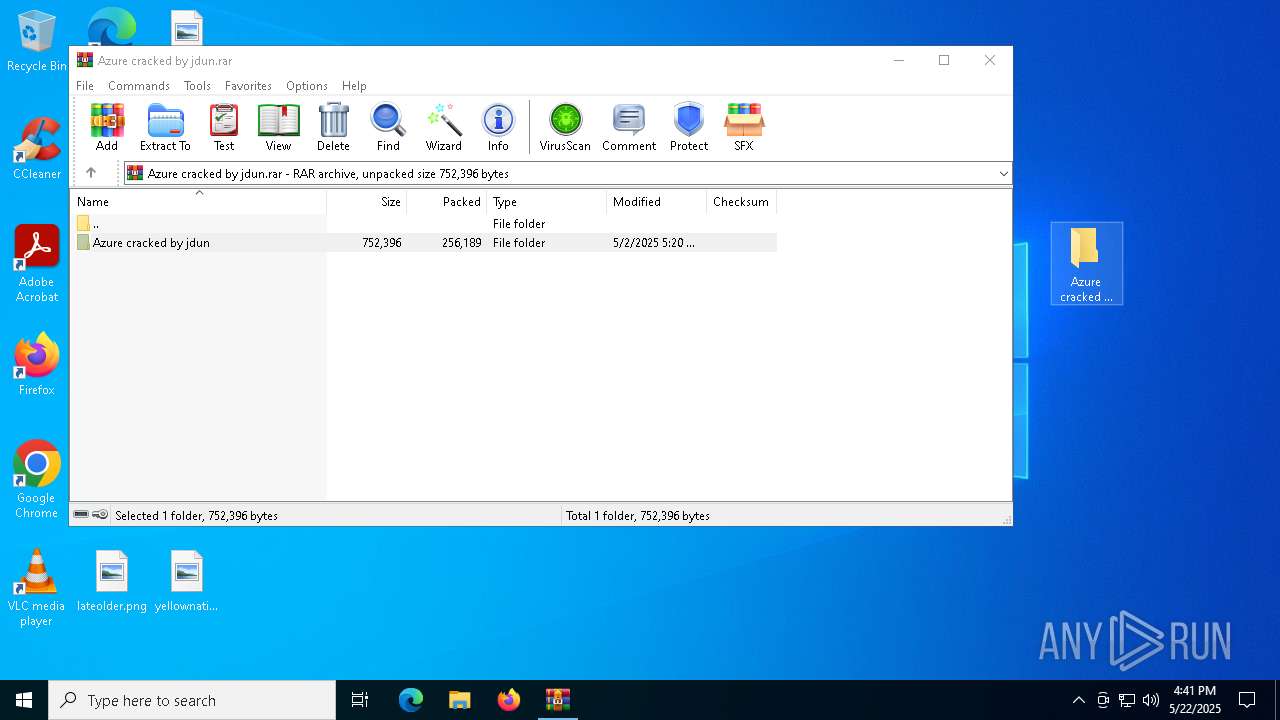
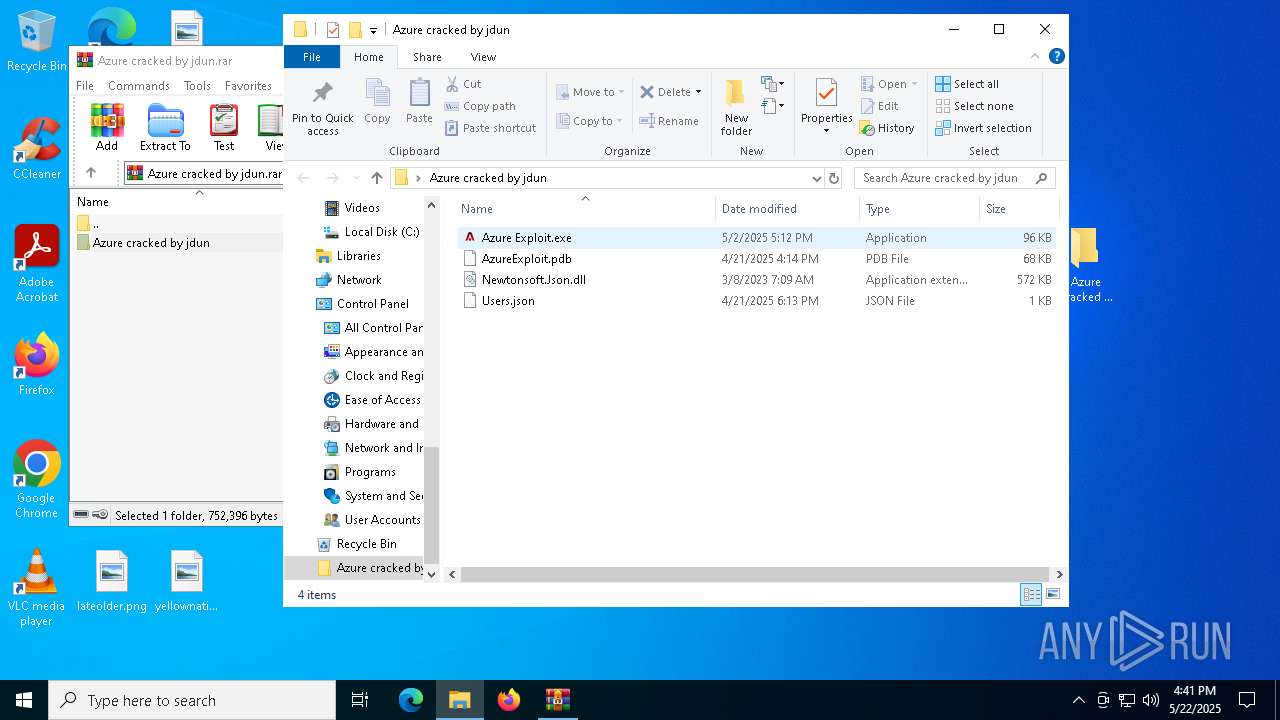
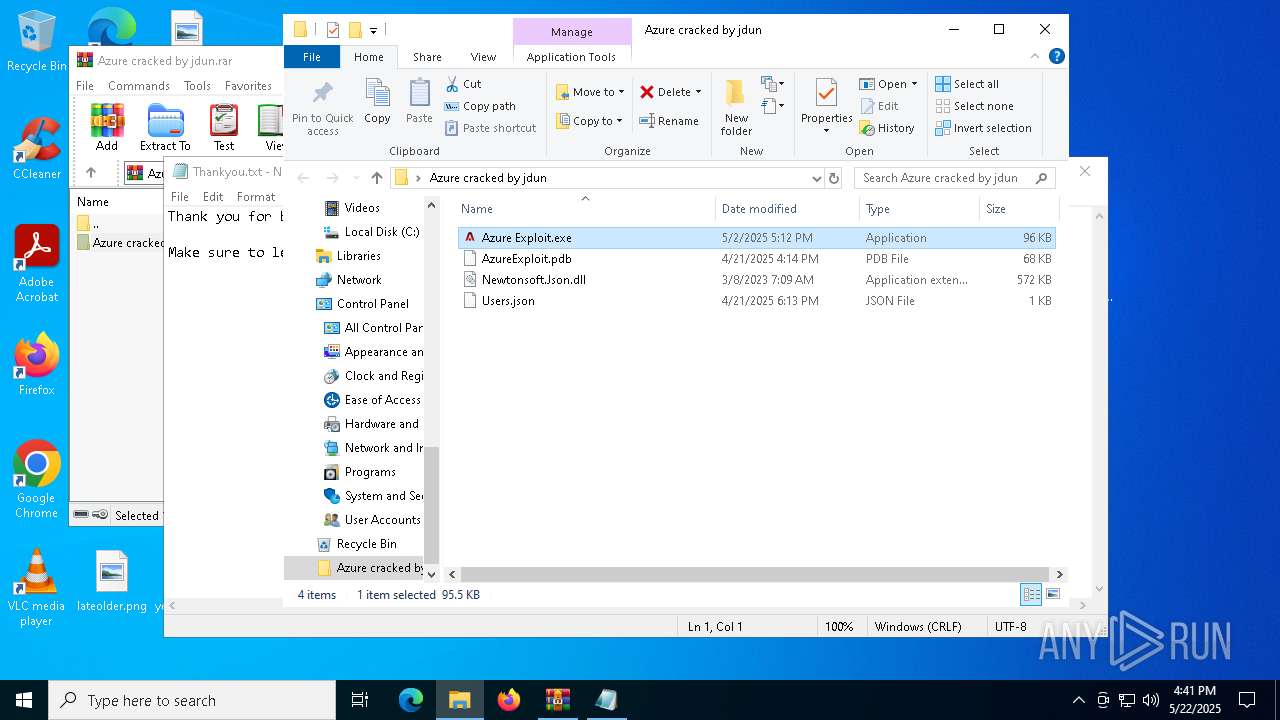
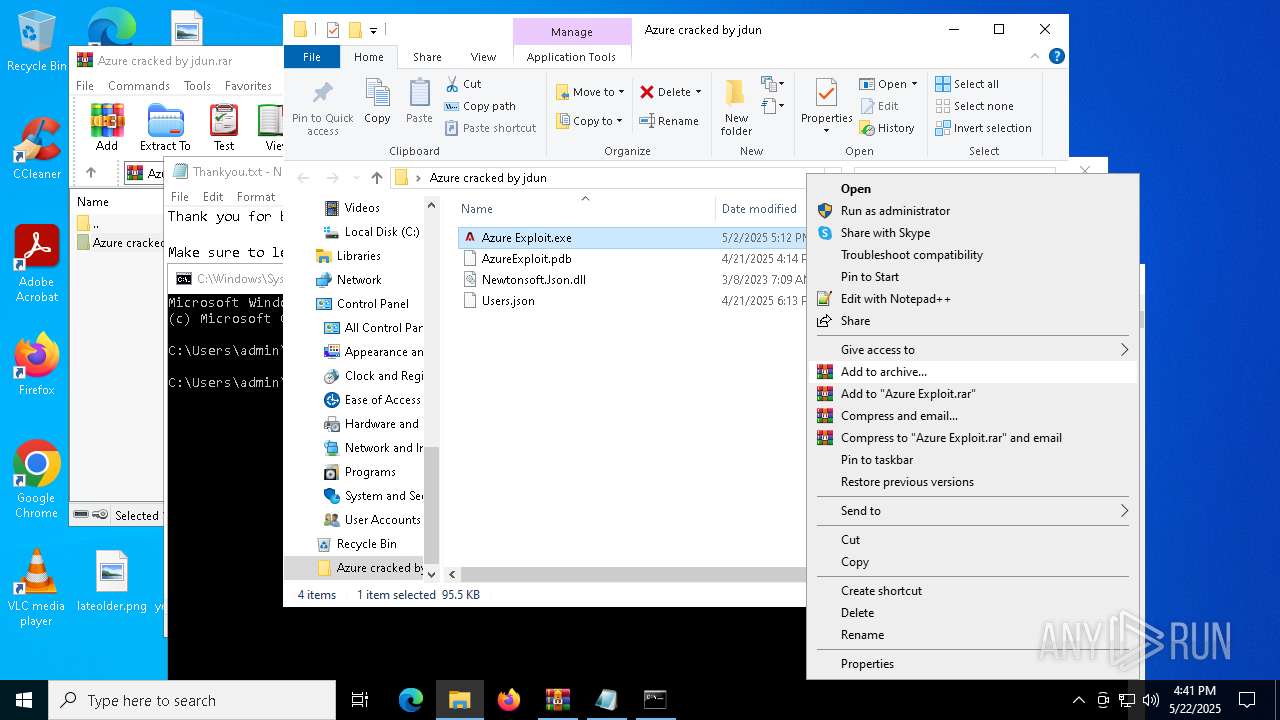
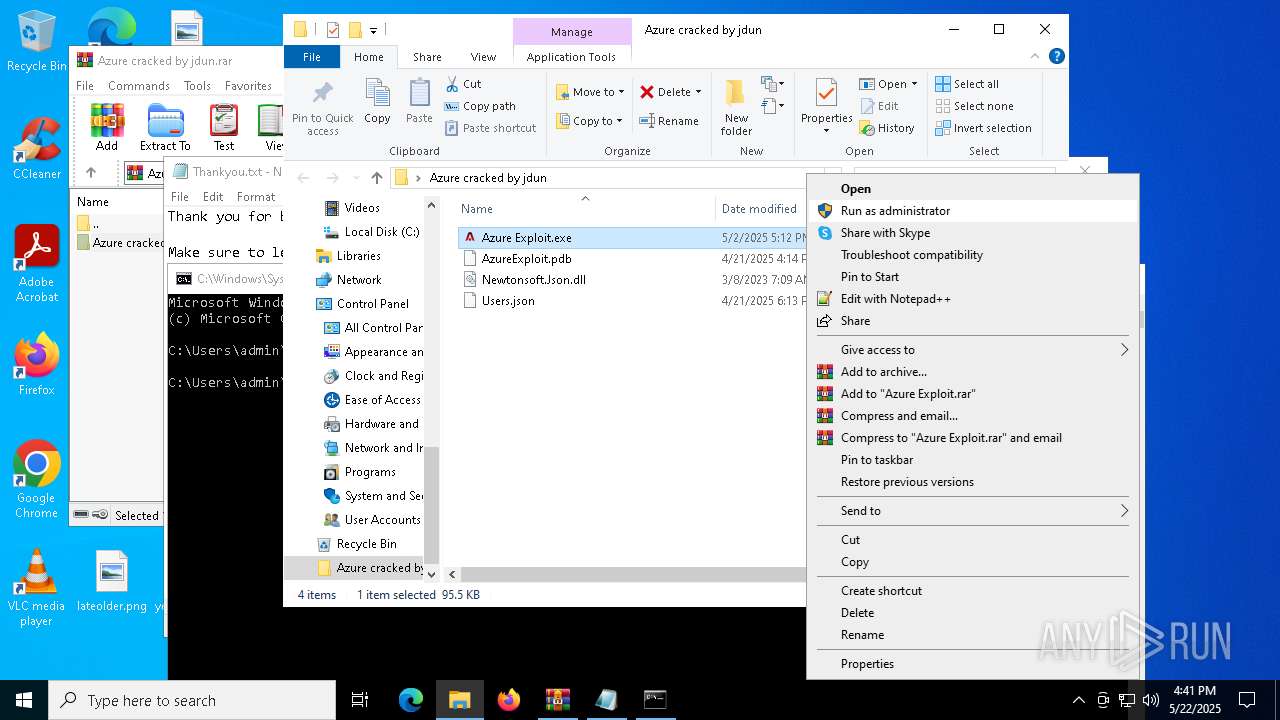
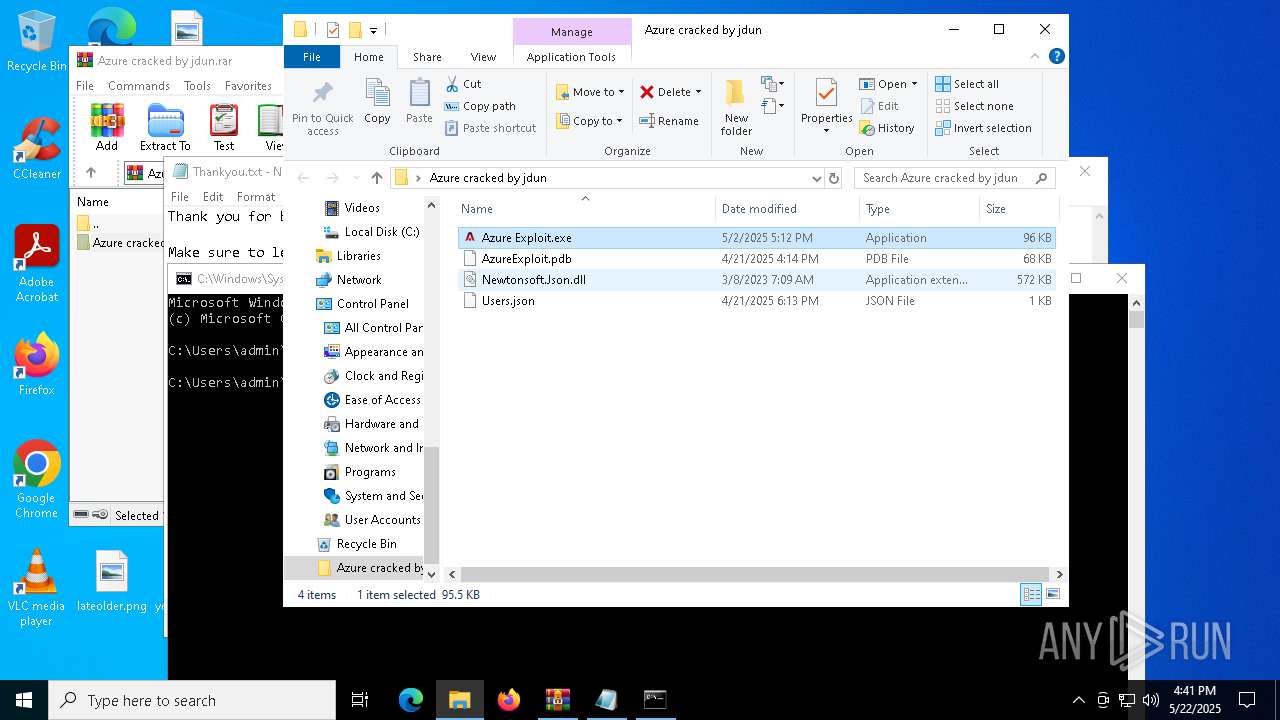
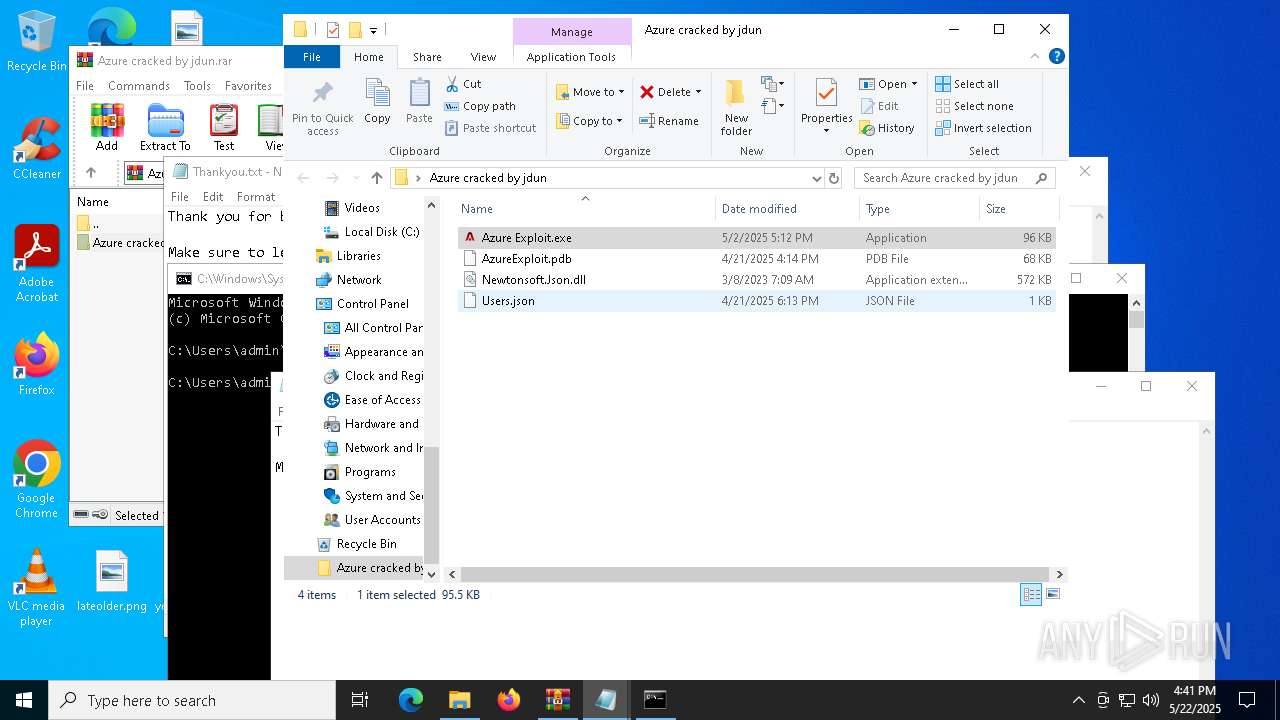
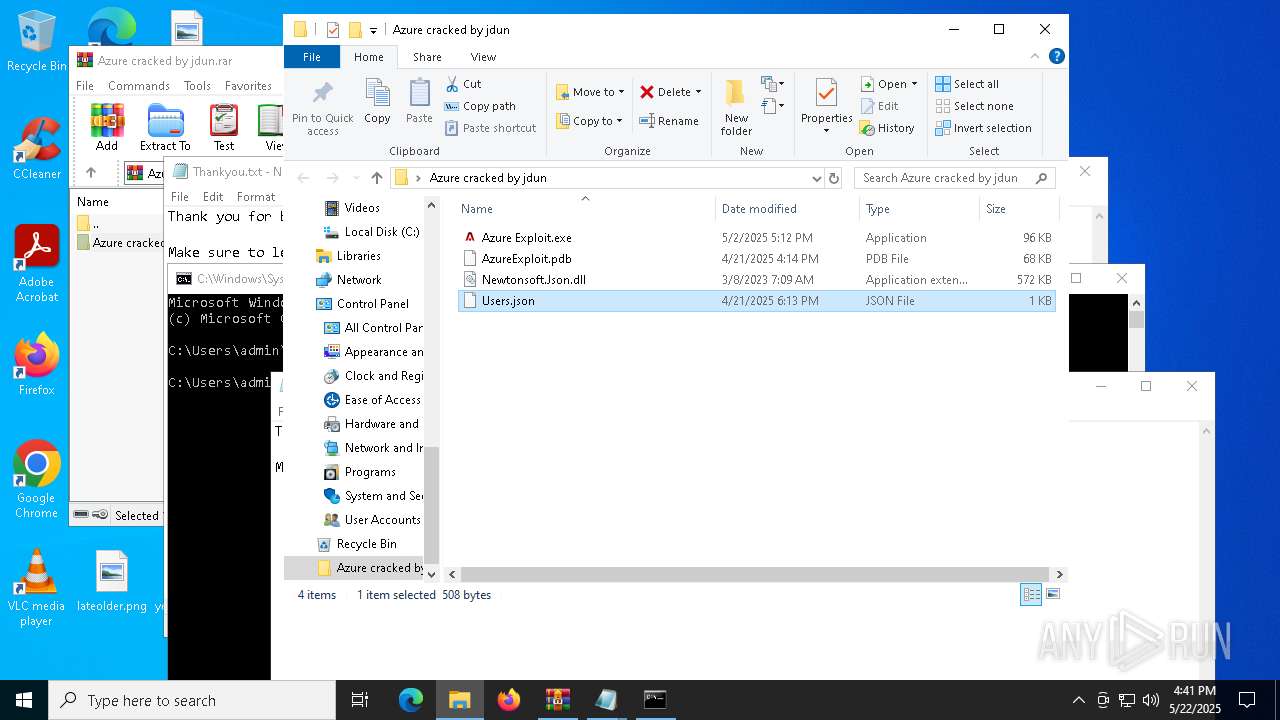
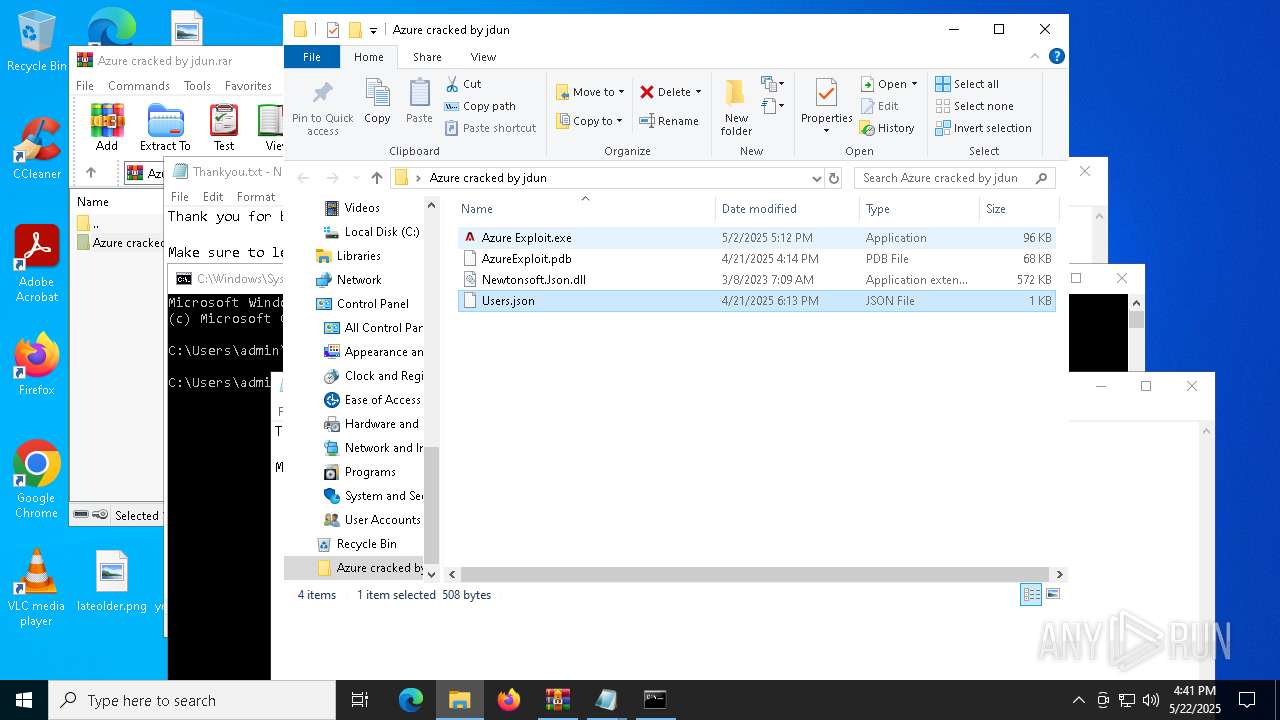
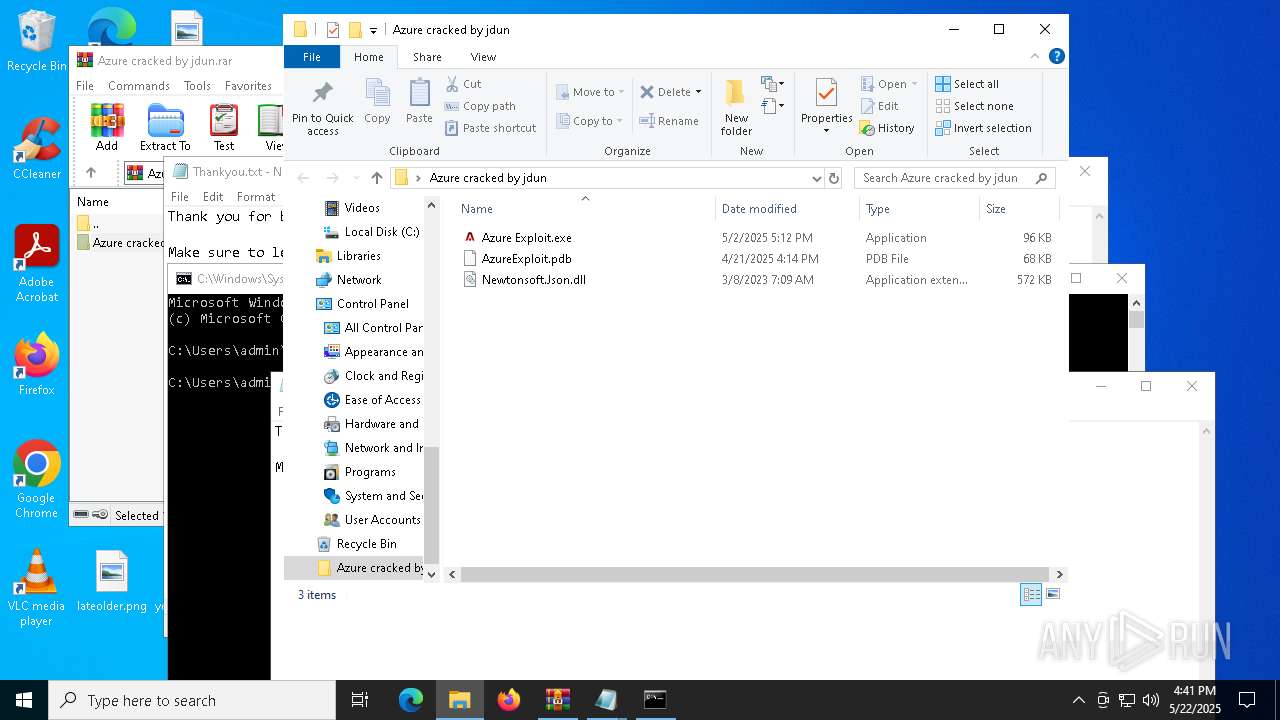
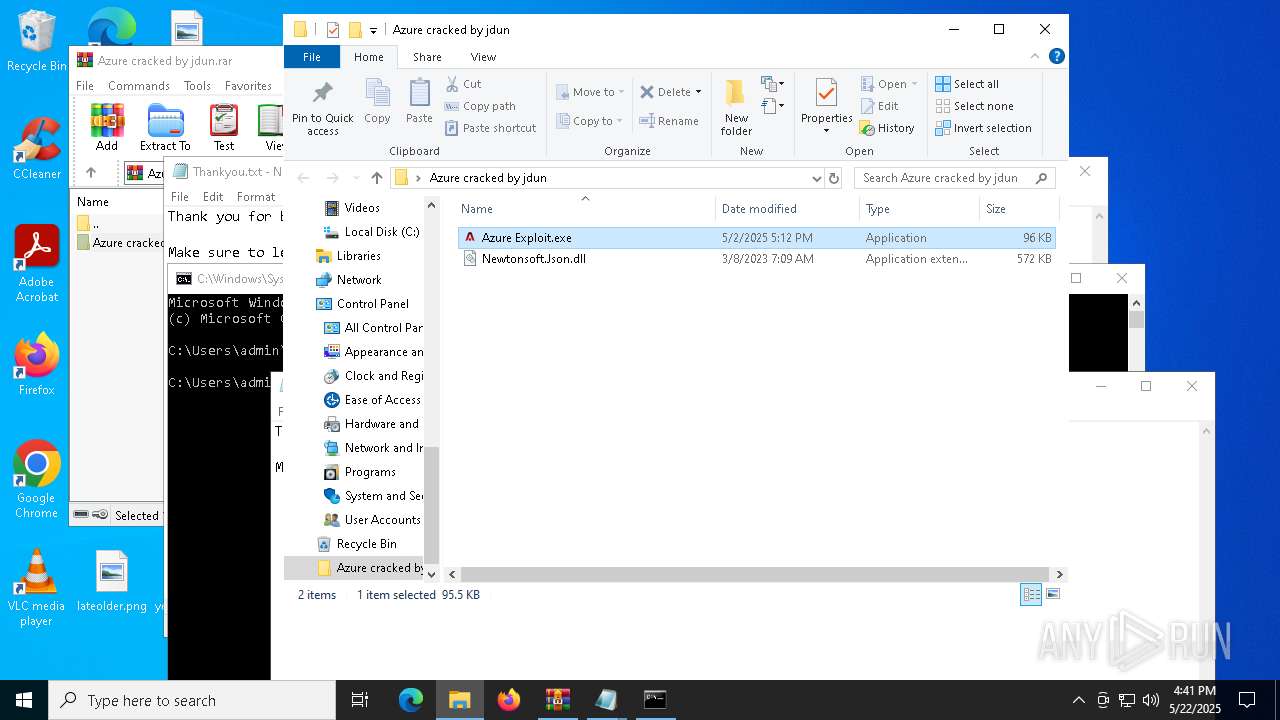
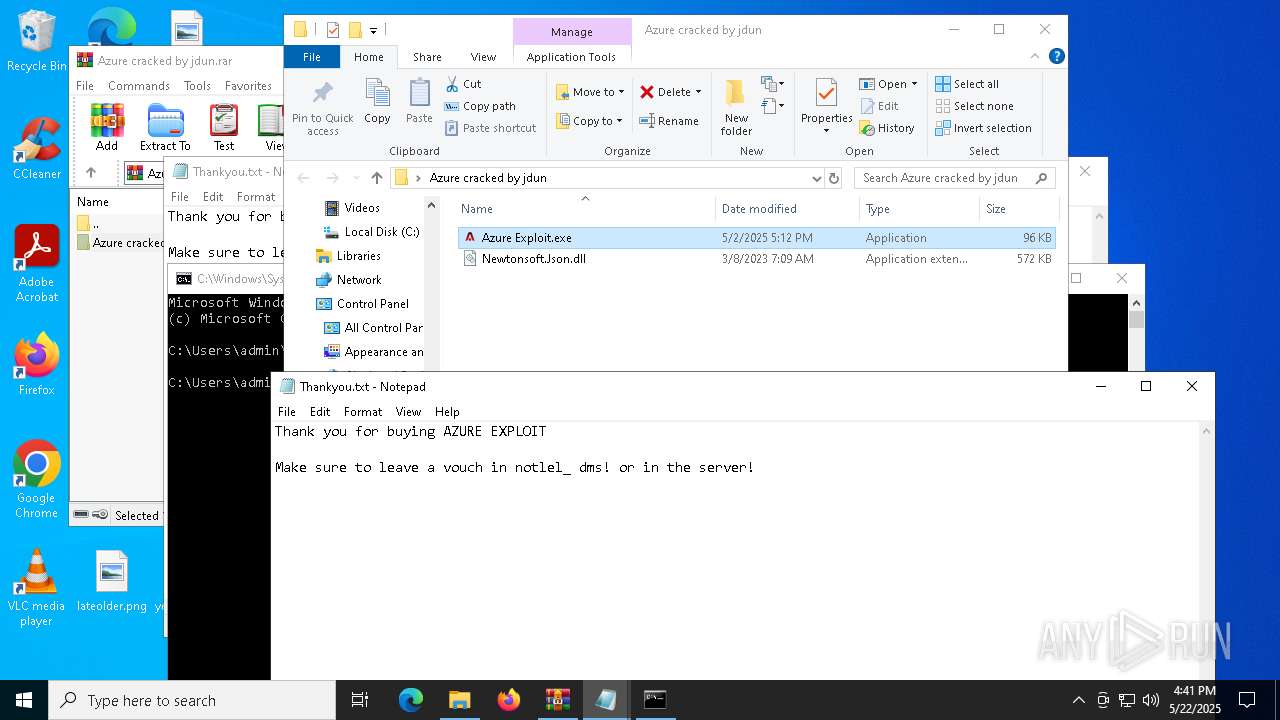
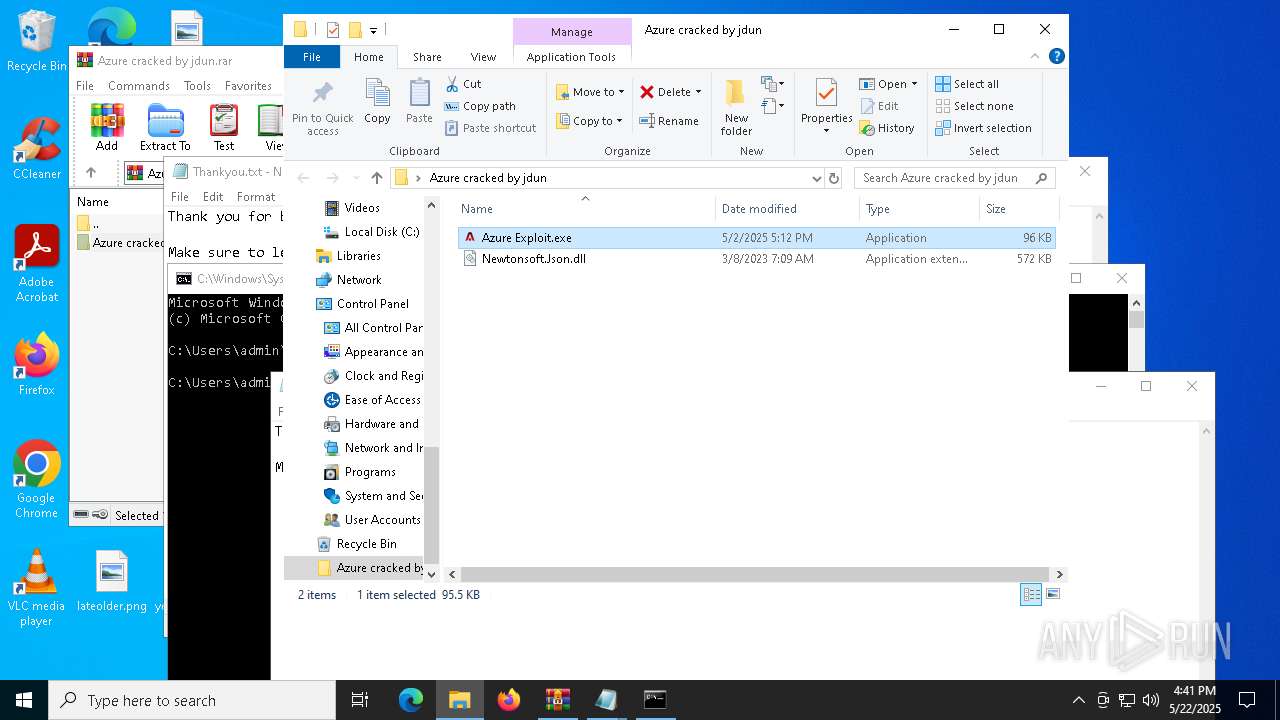
| File name: | Azure cracked by jdun.rar |
| Full analysis: | https://app.any.run/tasks/21a1edbc-2e18-4764-8c2b-8594fa2a5710 |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2025, 16:40:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | AB9B5AF6CDA29F2EACFEF7654CDE9B00 |
| SHA1: | 26230FF95E73E1DACCAB420473856417DAC024CD |
| SHA256: | 6B1642A20128D8E89E70C4D9C905358D0B0C86D4EDF76B6BC740105D3E371EB8 |
| SSDEEP: | 12288:jZrRMaWt0bhuvT8vOI1Yc6QIEqb/ADwEVljK:jZlU0bhuvT8vOI1YgIEqLAkEVM |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6944)
SUSPICIOUS
Reads security settings of Internet Explorer
- Azure Exploit.exe (PID: 4724)
- Azure Exploit.exe (PID: 208)
- Azure Exploit.exe (PID: 6972)
- Azure Exploit.exe (PID: 6112)
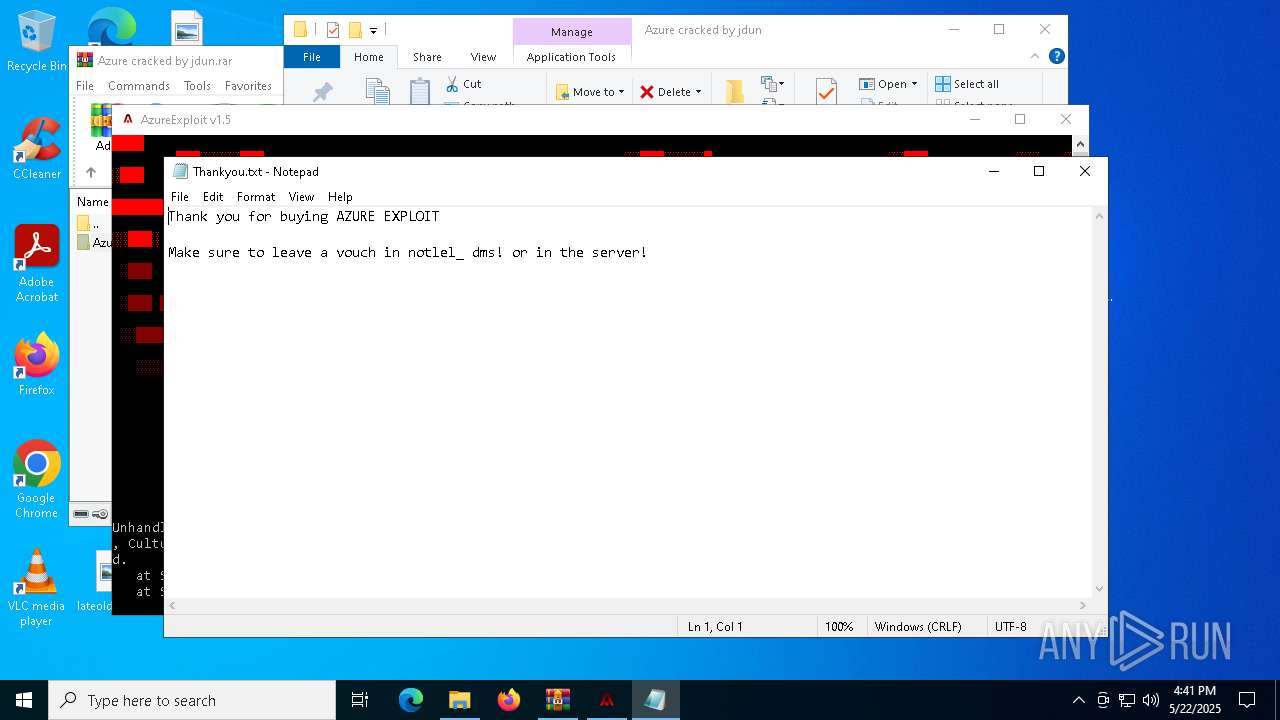
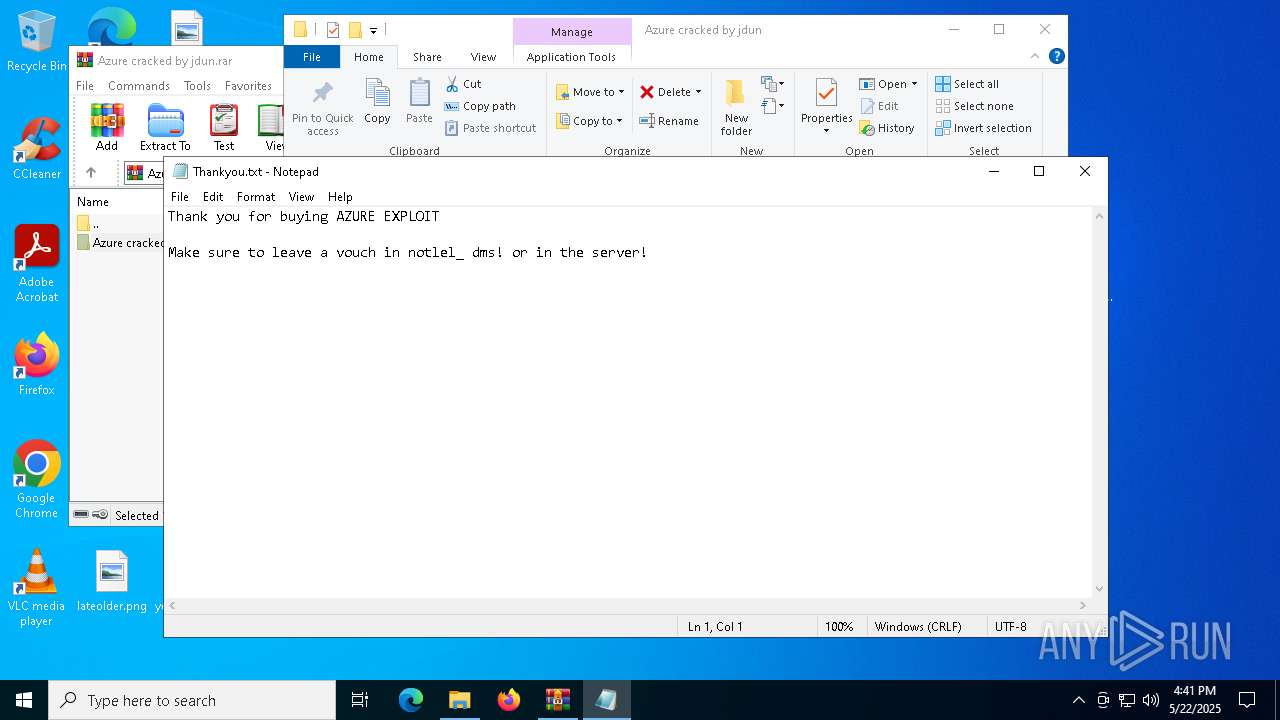
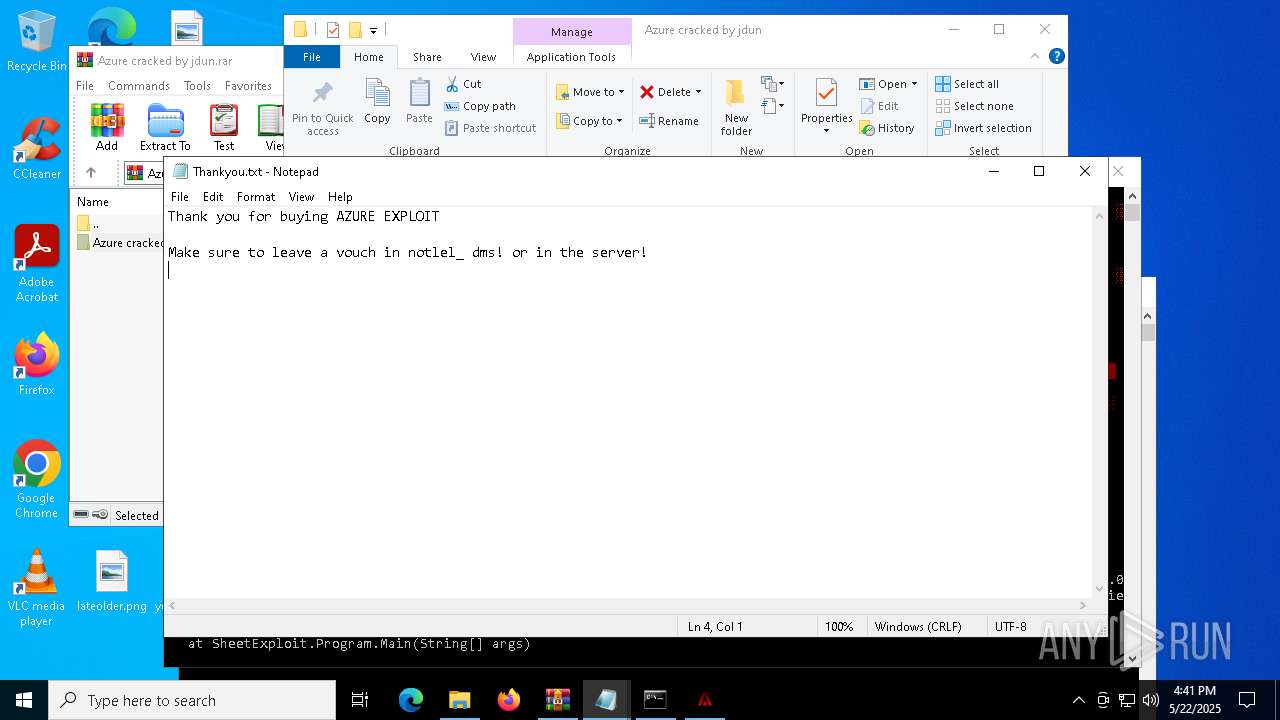
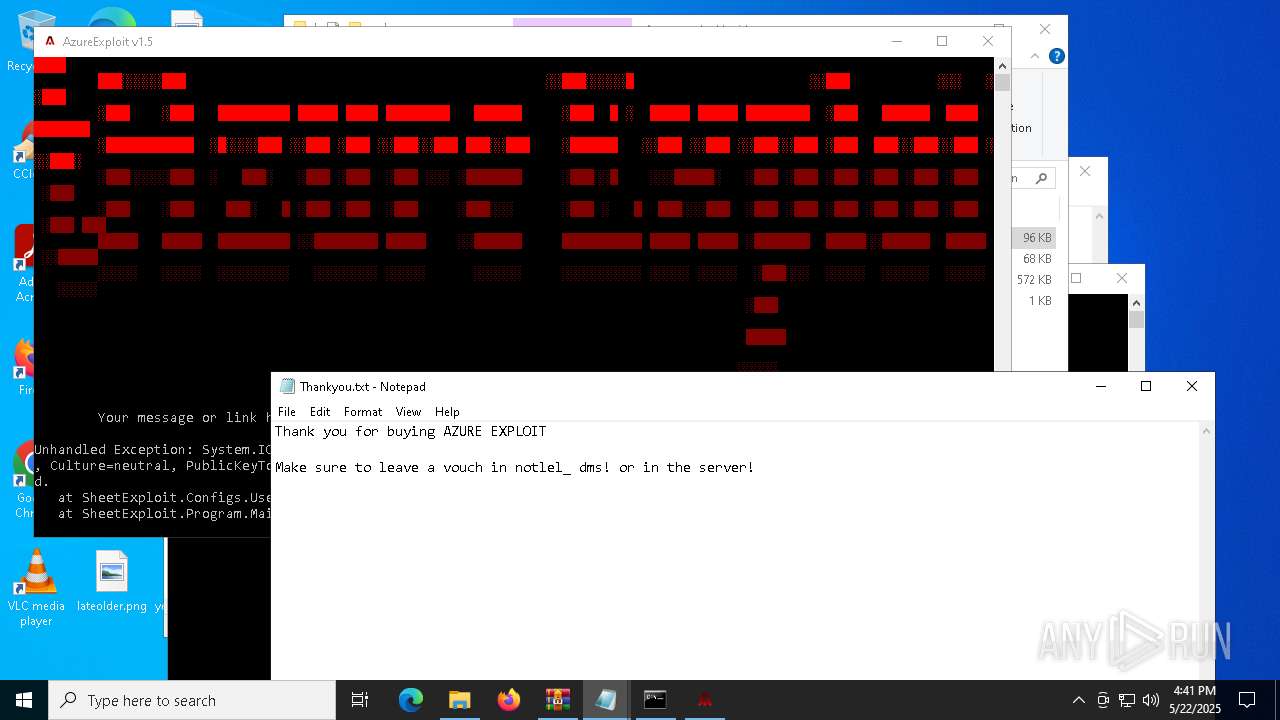
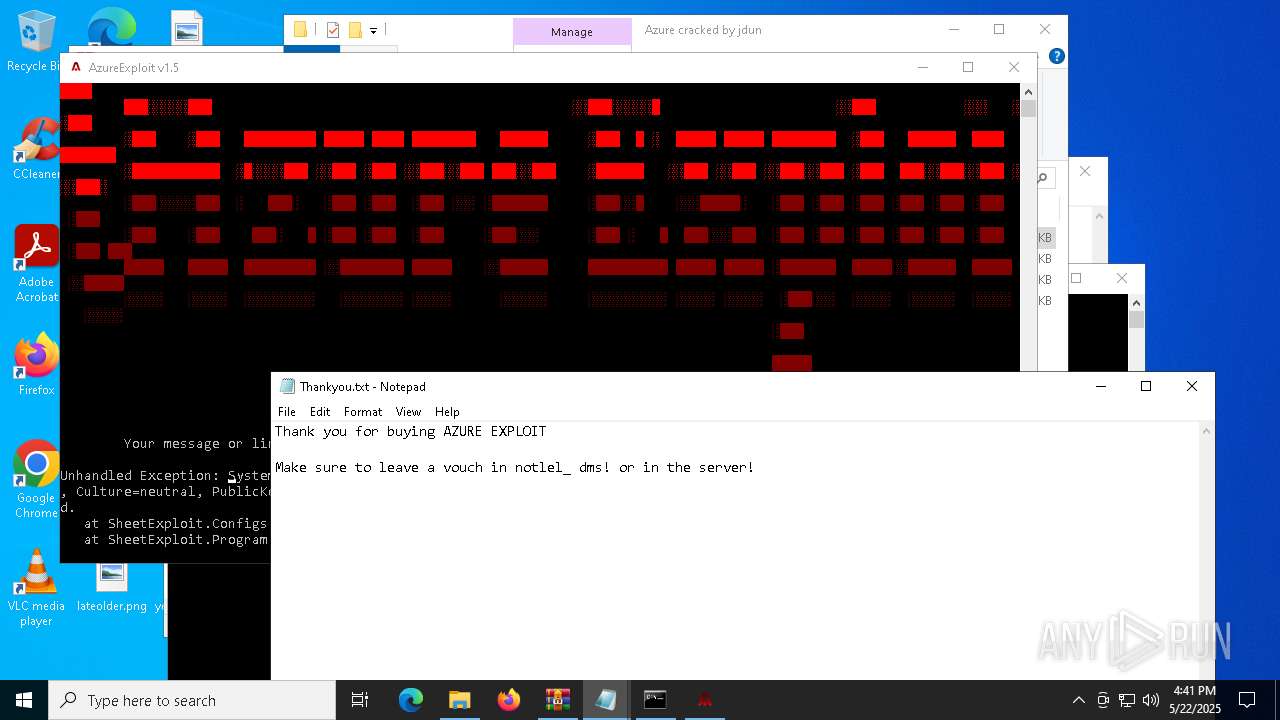
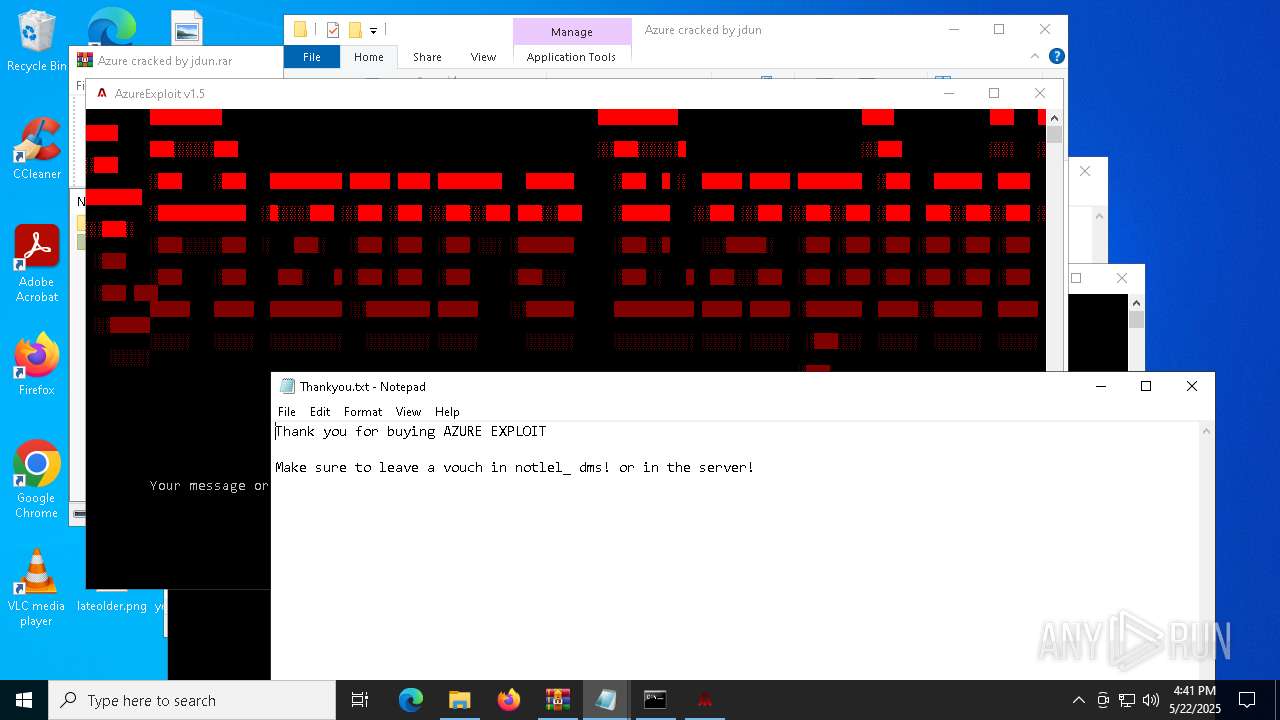
Start notepad (likely ransomware note)
- Azure Exploit.exe (PID: 4724)
- Azure Exploit.exe (PID: 208)
- Azure Exploit.exe (PID: 6972)
- Azure Exploit.exe (PID: 5576)
- Azure Exploit.exe (PID: 6112)
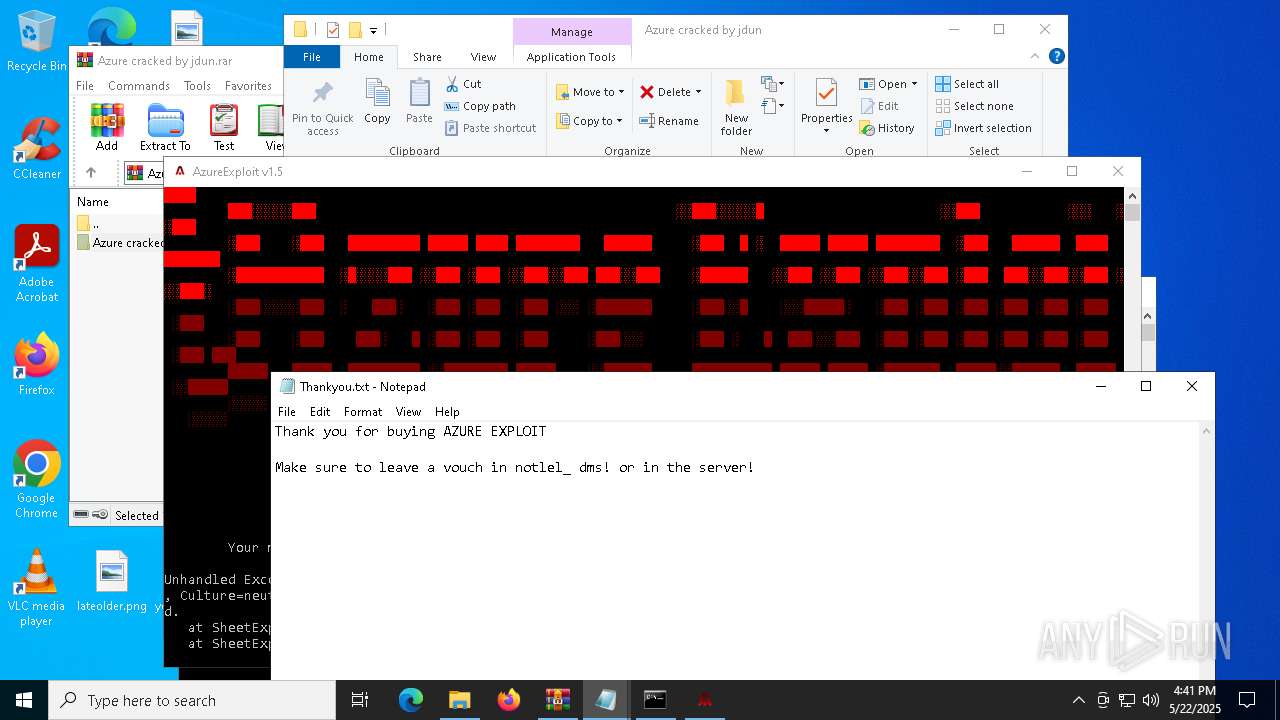
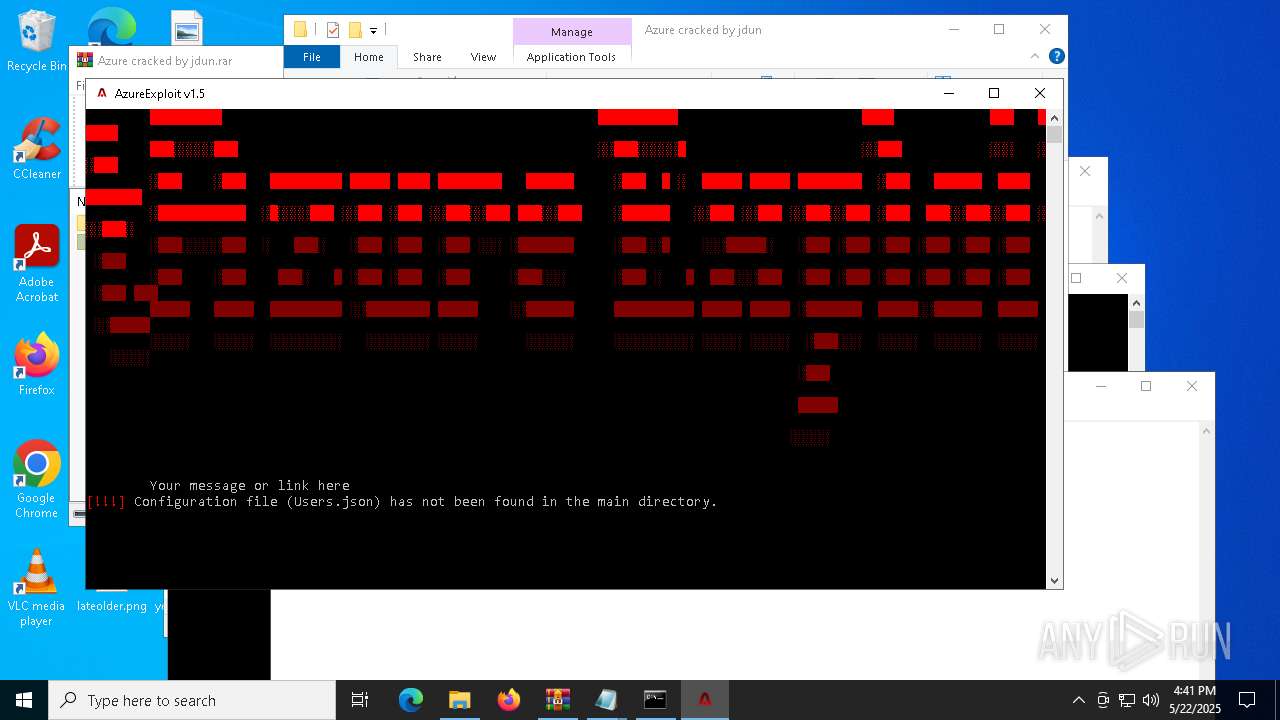
Executes application which crashes
- AzureExploit.exe (PID: 1812)
- AzureExploit.exe (PID: 5048)
- AzureExploit.exe (PID: 4272)
- AzureExploit.exe (PID: 736)
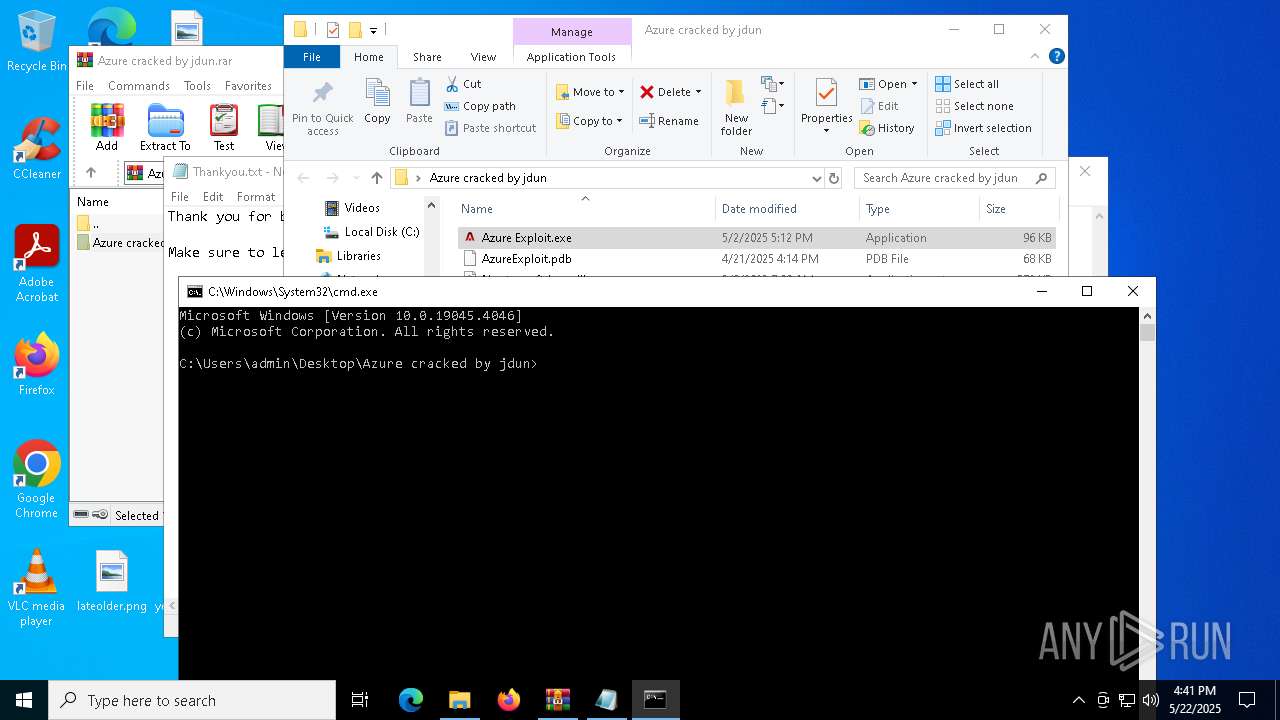
Executable content was dropped or overwritten
- Azure Exploit.exe (PID: 4724)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6944)
Checks supported languages
- AzureExploit.exe (PID: 1812)
- Azure Exploit.exe (PID: 4724)
- Azure Exploit.exe (PID: 208)
- Azure Exploit.exe (PID: 6972)
- AzureExploit.exe (PID: 5048)
- AzureExploit.exe (PID: 4272)
- Azure Exploit.exe (PID: 6112)
- AzureExploit.exe (PID: 736)
Reads the computer name
- Azure Exploit.exe (PID: 4724)
- AzureExploit.exe (PID: 1812)
- Azure Exploit.exe (PID: 208)
- AzureExploit.exe (PID: 5048)
- Azure Exploit.exe (PID: 6972)
- AzureExploit.exe (PID: 4272)
- Azure Exploit.exe (PID: 6112)
- AzureExploit.exe (PID: 736)
Reads the machine GUID from the registry
- AzureExploit.exe (PID: 1812)
- AzureExploit.exe (PID: 5048)
- AzureExploit.exe (PID: 4272)
- AzureExploit.exe (PID: 736)
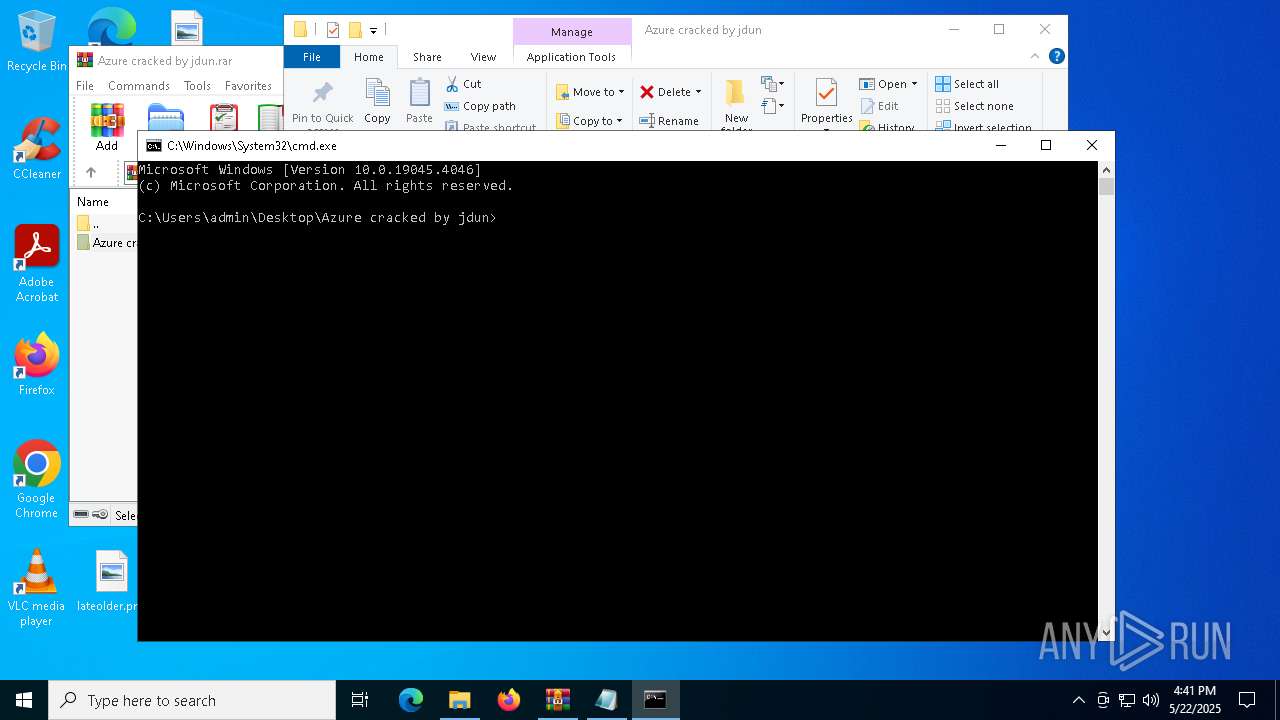
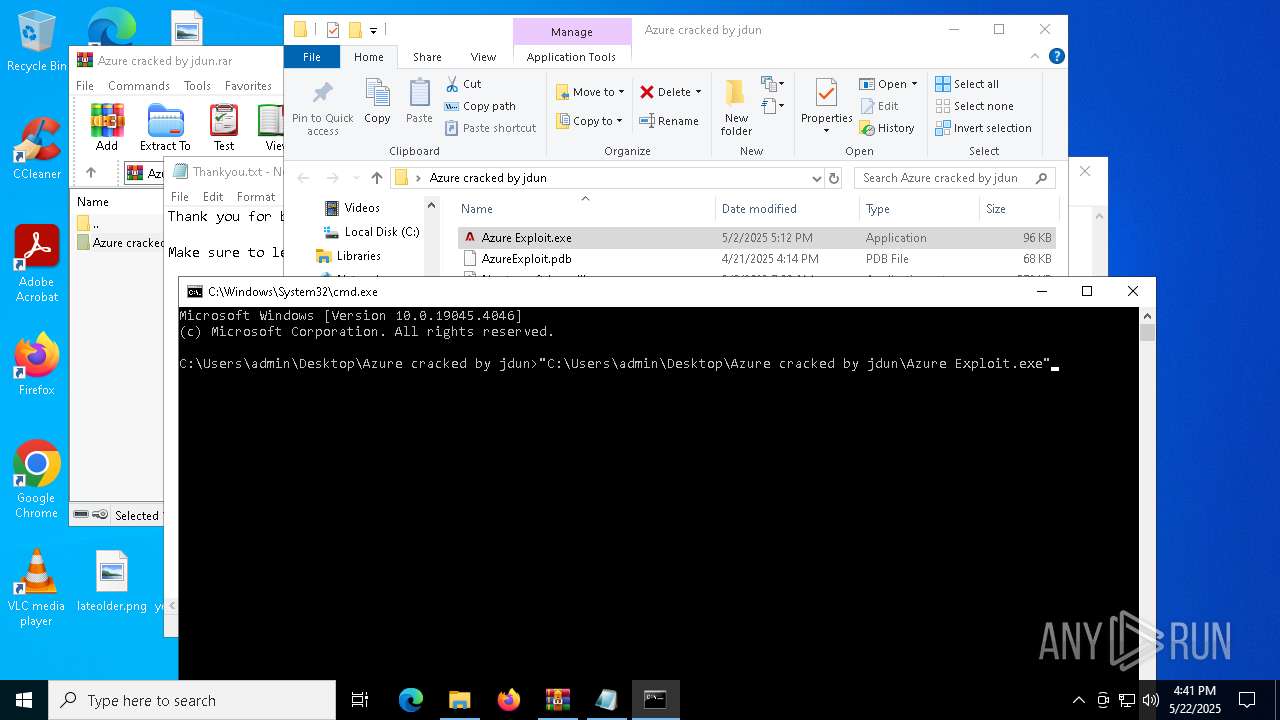
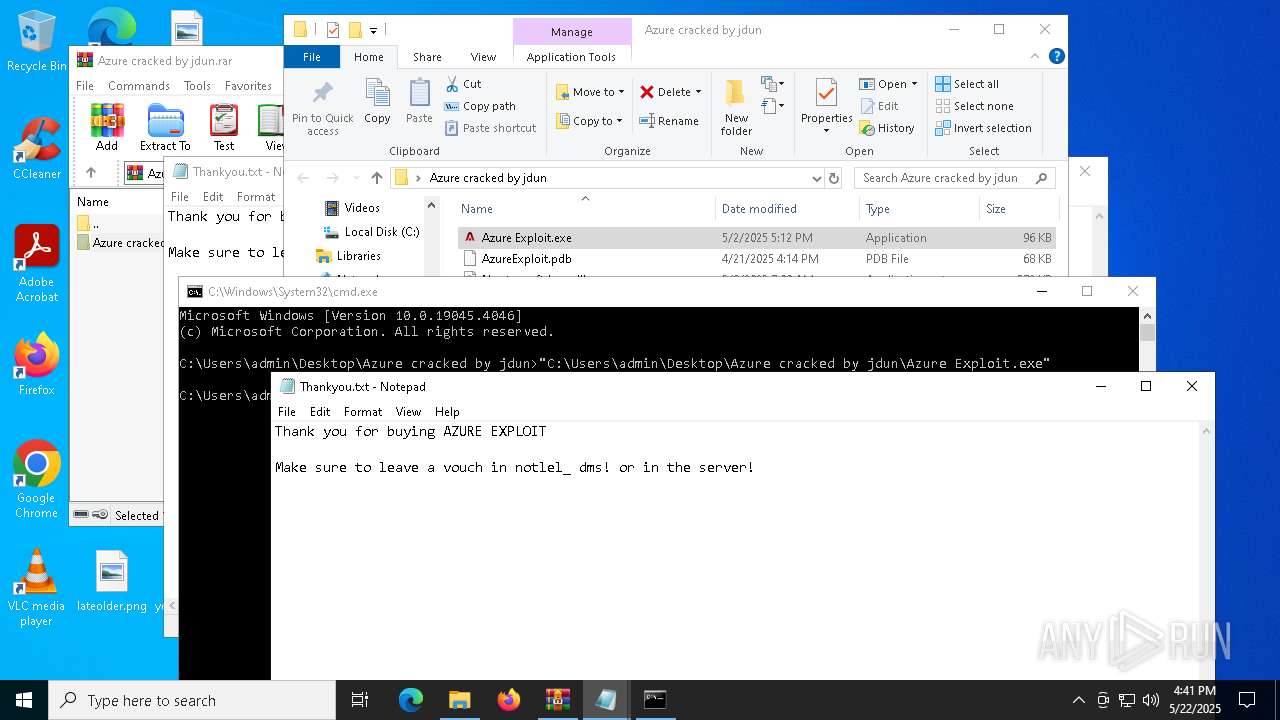
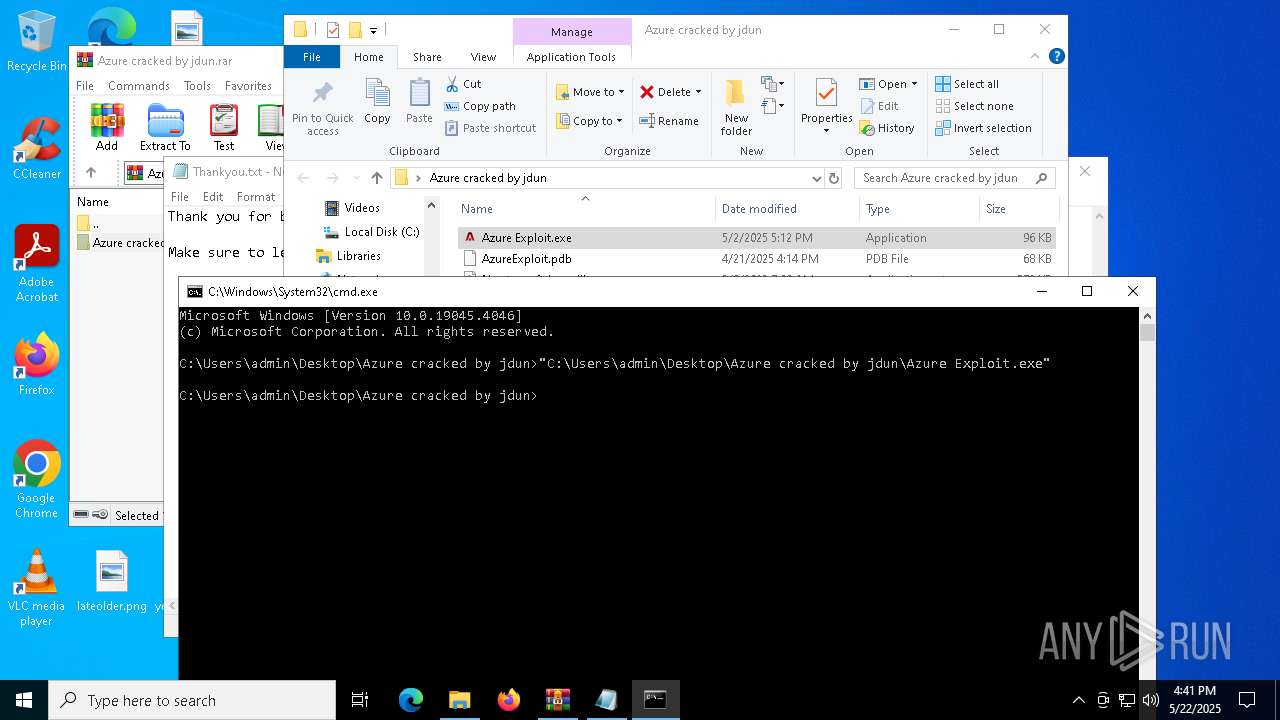
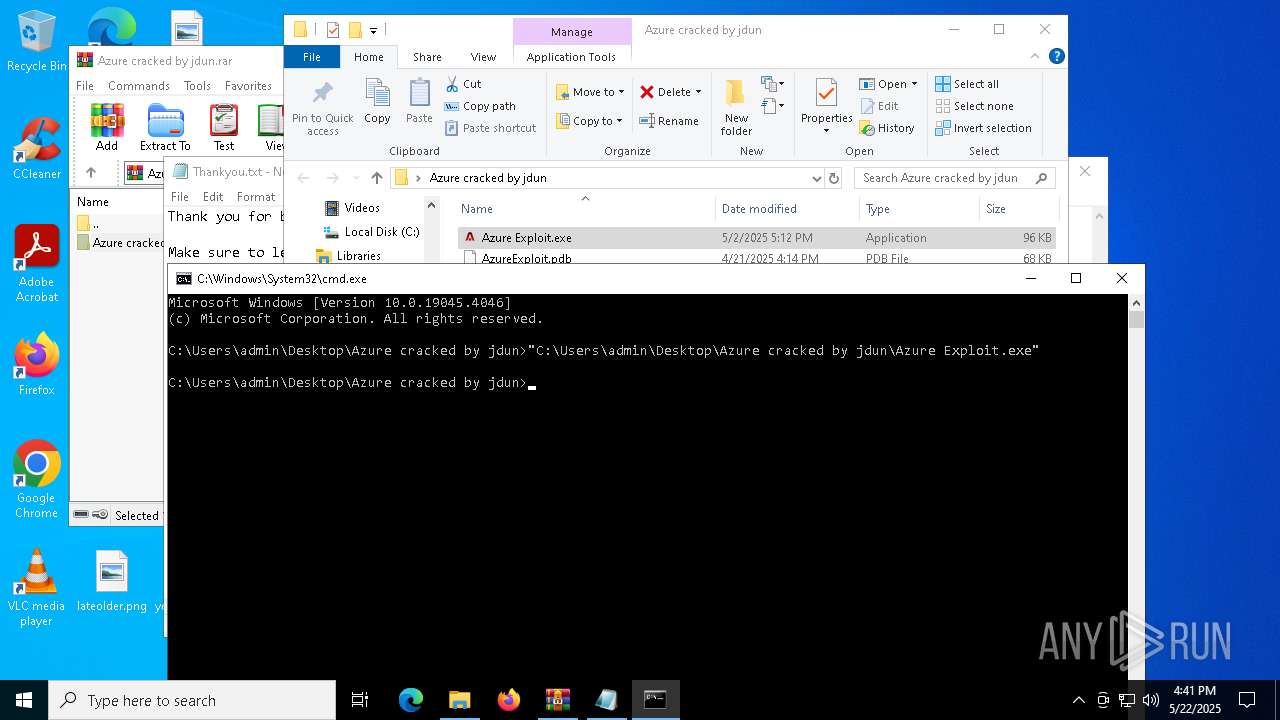
Manual execution by a user
- Azure Exploit.exe (PID: 4724)
- cmd.exe (PID: 5984)
- Azure Exploit.exe (PID: 6972)
- Azure Exploit.exe (PID: 6112)
- Azure Exploit.exe (PID: 5576)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5404)
- notepad.exe (PID: 6184)
- notepad.exe (PID: 3096)
- notepad.exe (PID: 3300)
Create files in a temporary directory
- Azure Exploit.exe (PID: 4724)
- Azure Exploit.exe (PID: 208)
- Azure Exploit.exe (PID: 6972)
- Azure Exploit.exe (PID: 6112)
Process checks computer location settings
- Azure Exploit.exe (PID: 4724)
- Azure Exploit.exe (PID: 208)
- Azure Exploit.exe (PID: 6972)
- Azure Exploit.exe (PID: 6112)
Creates files or folders in the user directory
- WerFault.exe (PID: 3888)
- WerFault.exe (PID: 3240)
- WerFault.exe (PID: 732)
- WerFault.exe (PID: 6036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 44974 |
| UncompressedSize: | 97792 |
| OperatingSystem: | Win32 |
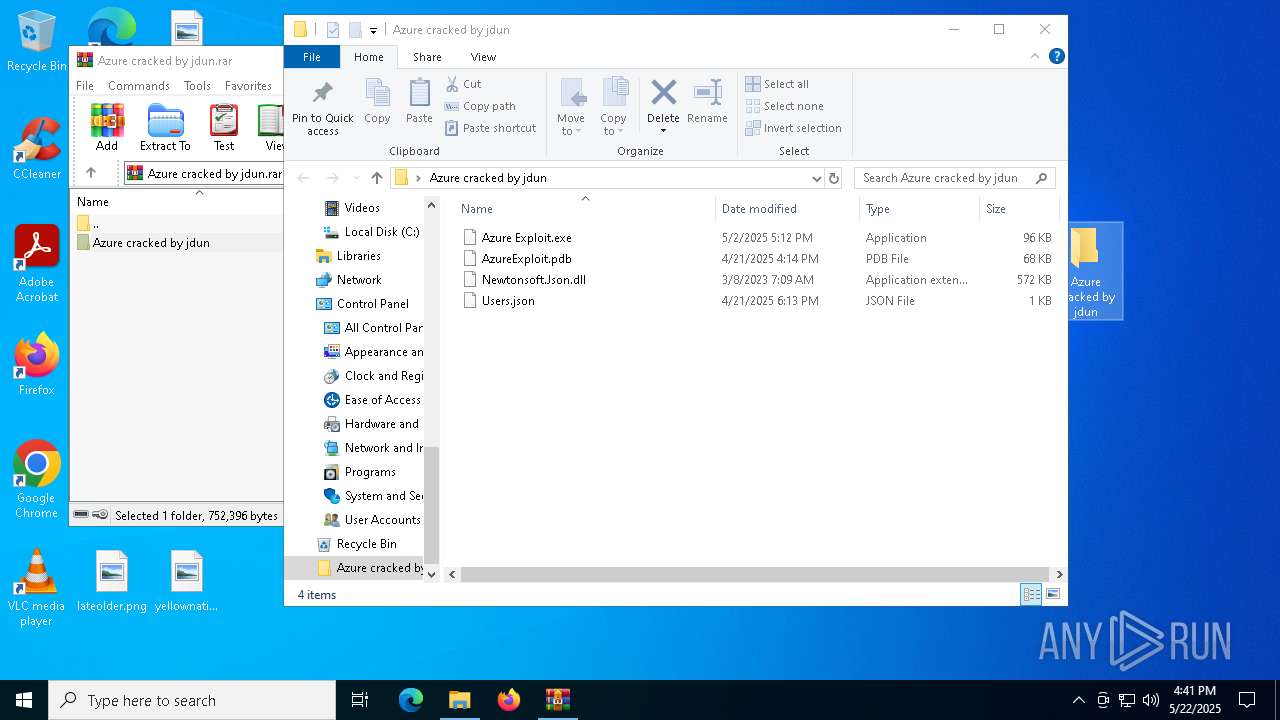
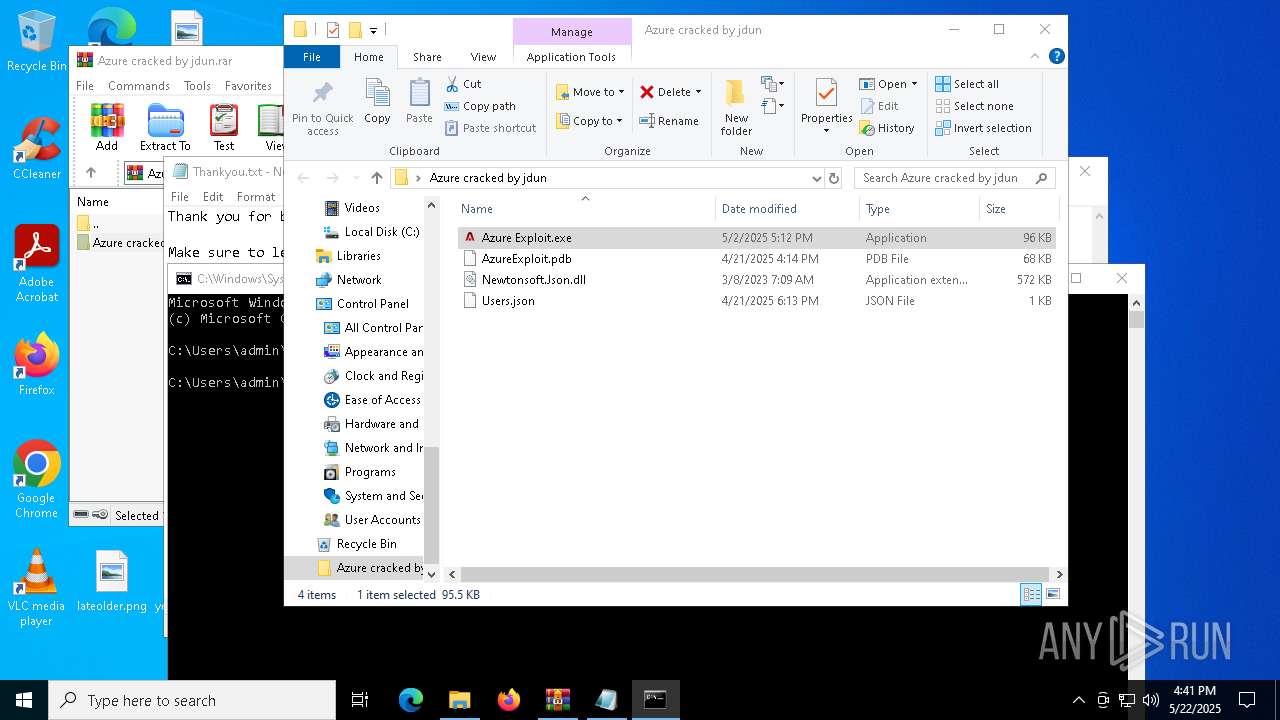
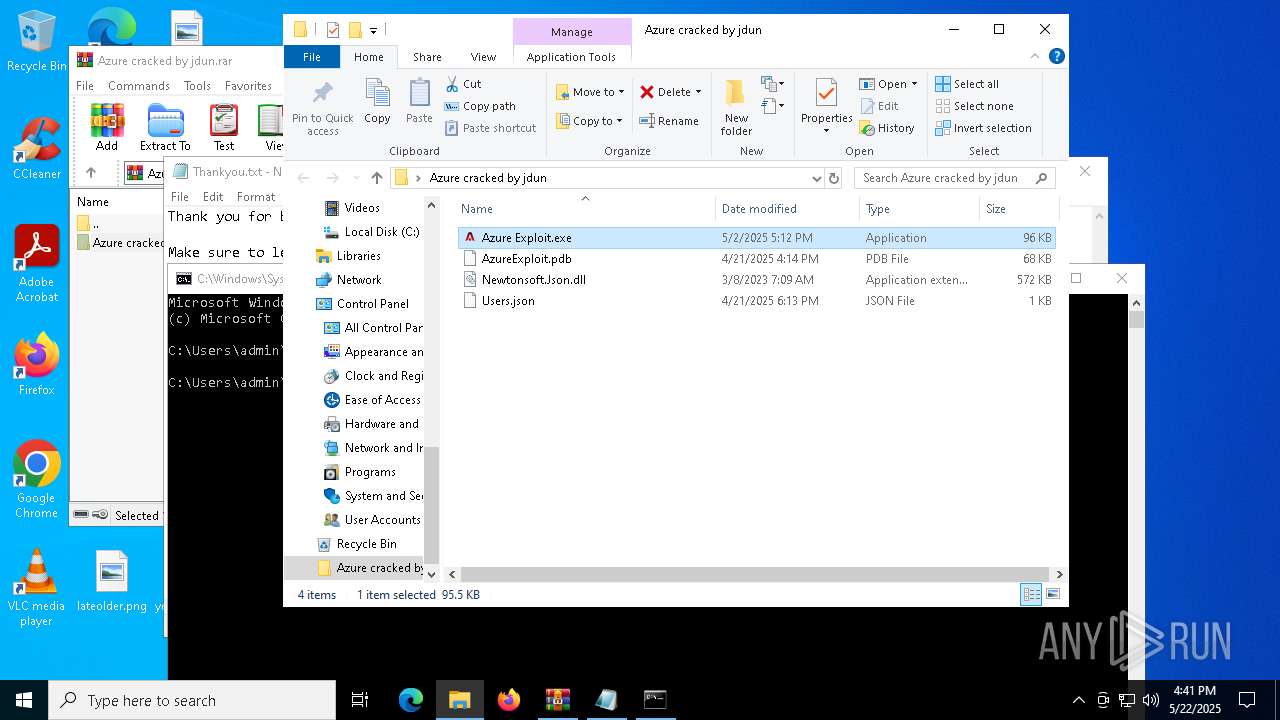
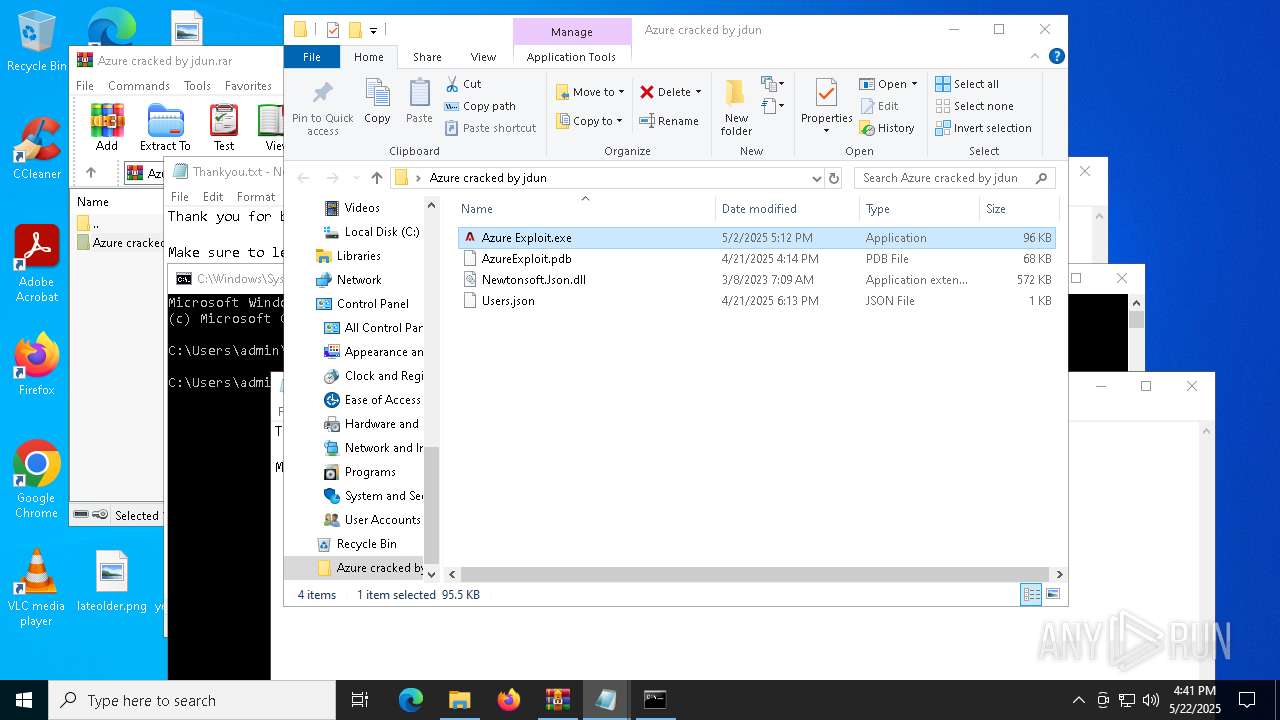
| ArchivedFileName: | Azure cracked by jdun/Azure Exploit.exe |
Total processes
163
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\Desktop\Azure cracked by jdun\Azure Exploit.exe" | C:\Users\admin\Desktop\Azure cracked by jdun\Azure Exploit.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AzureExploit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | C:\WINDOWS\system32\WerFault.exe -u -p 736 -s 760 | C:\Windows\System32\WerFault.exe | — | AzureExploit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Users\admin\AppData\Local\Temp\AzureExploit.exe" | C:\Users\admin\AppData\Local\Temp\AzureExploit.exe | Azure Exploit.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AzureExploit Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 920 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AzureExploit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | "C:\Users\admin\AppData\Local\Temp\AzureExploit.exe" | C:\Users\admin\AppData\Local\Temp\AzureExploit.exe | Azure Exploit.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AzureExploit Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AzureExploit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3096 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Thankyou.txt | C:\Windows\SysWOW64\notepad.exe | — | Azure Exploit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 621
Read events
14 566
Write events
52
Delete events
3
Modification events
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Azure cracked by jdun.rar | |||
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4724) Azure Exploit.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (4724) Azure Exploit.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
Executable files
3
Suspicious files
6
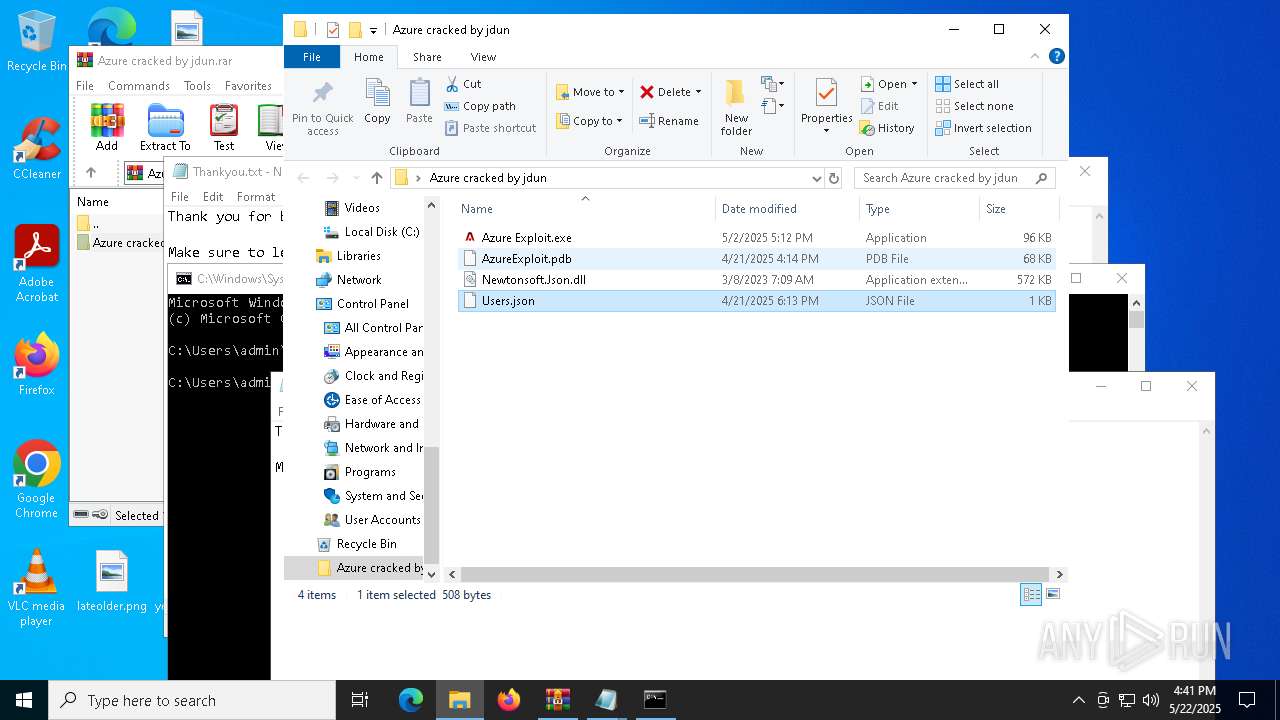
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_AzureExploit.exe_9fdd92193e4c94f93bfa02a189087587ba088e2_605a36a7_adf88c3c-fd2f-4928-aa9d-3d6881a7fe5e\Report.wer | — | |
MD5:— | SHA256:— | |||
| 3888 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\AzureExploit.exe.1812.dmp | — | |
MD5:— | SHA256:— | |||
| 3240 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_AzureExploit.exe_9fdd92193e4c94f93bfa02a189087587ba088e2_605a36a7_4dc4ac56-da65-4c45-bf61-13ad606f06f5\Report.wer | — | |
MD5:— | SHA256:— | |||
| 3240 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\AzureExploit.exe.5048.dmp | — | |
MD5:— | SHA256:— | |||
| 6036 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_AzureExploit.exe_9fdd92193e4c94f93bfa02a189087587ba088e2_605a36a7_37b0fcab-3528-4ce9-9178-9577917d1fc0\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6036 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\AzureExploit.exe.4272.dmp | — | |
MD5:— | SHA256:— | |||
| 732 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_AzureExploit.exe_9fdd92193e4c94f93bfa02a189087587ba088e2_605a36a7_63c4e44f-6676-42f6-b1d3-b6b65f1b3c9d\Report.wer | — | |
MD5:— | SHA256:— | |||
| 732 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\AzureExploit.exe.736.dmp | — | |
MD5:— | SHA256:— | |||
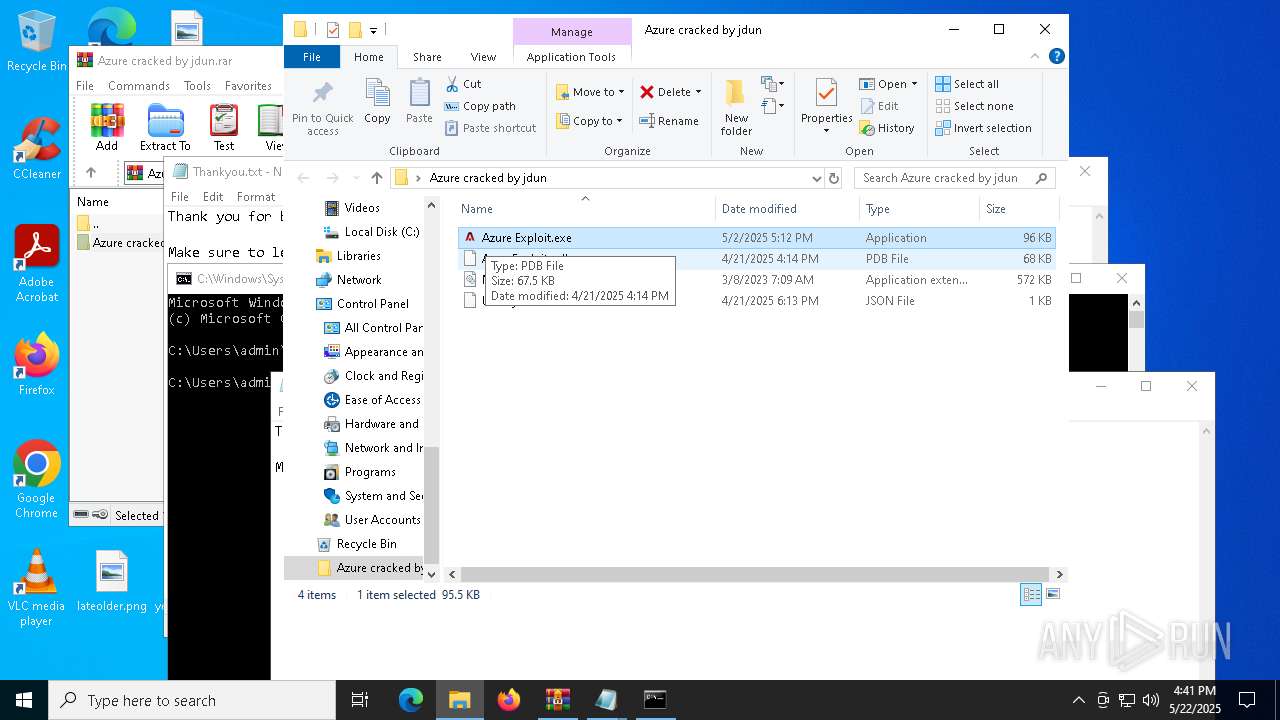
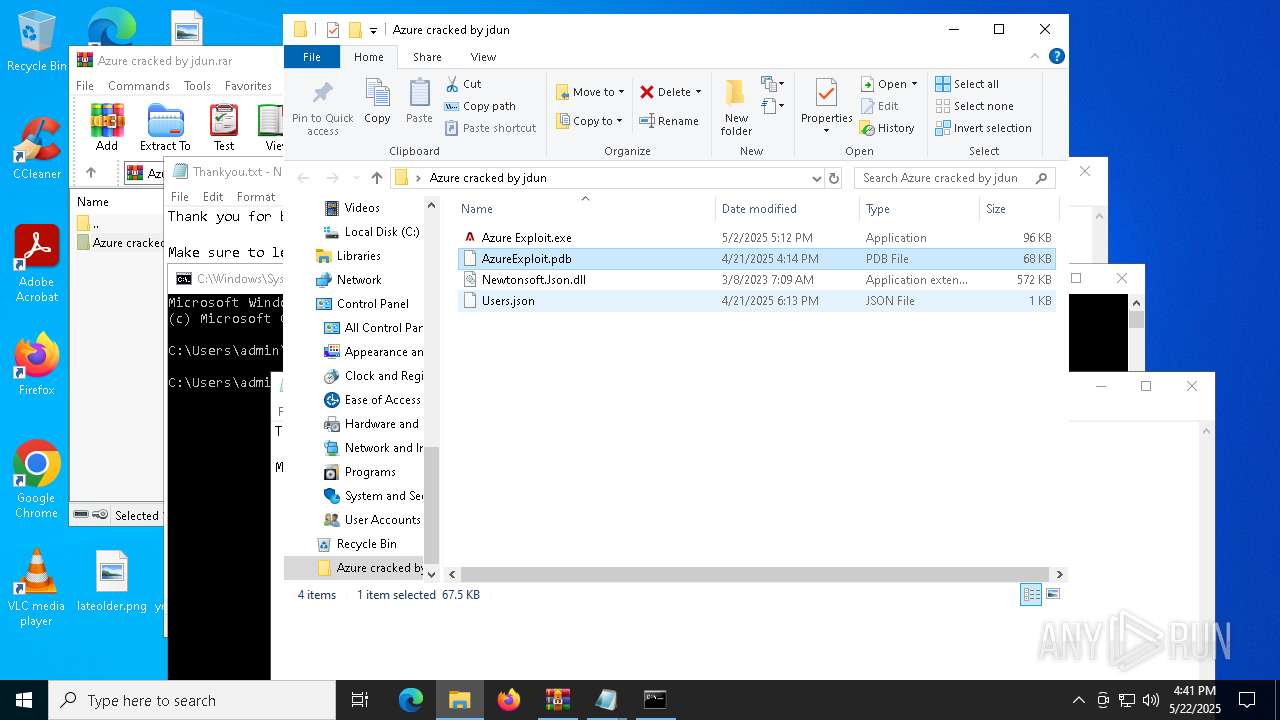
| 6944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6944.37468\Azure cracked by jdun\AzureExploit.pdb | binary | |
MD5:FD8D6B7A29F31FC4A6FAEB93B000A082 | SHA256:E7ADA33BC6D2D08AEB66553DC8A9AD219287E009EAFC04A4CE6E309FB70F4A05 | |||
| 3888 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERF32E.tmp.xml | xml | |
MD5:9B2EA6AD43EA06F2B1DC60E9C9C0754D | SHA256:54BB6984CA96176E43BCDB50A882BBCD0DE2BEB21B99CAA3939D23FA0F63E943 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
18
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5552 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5552 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5552 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |