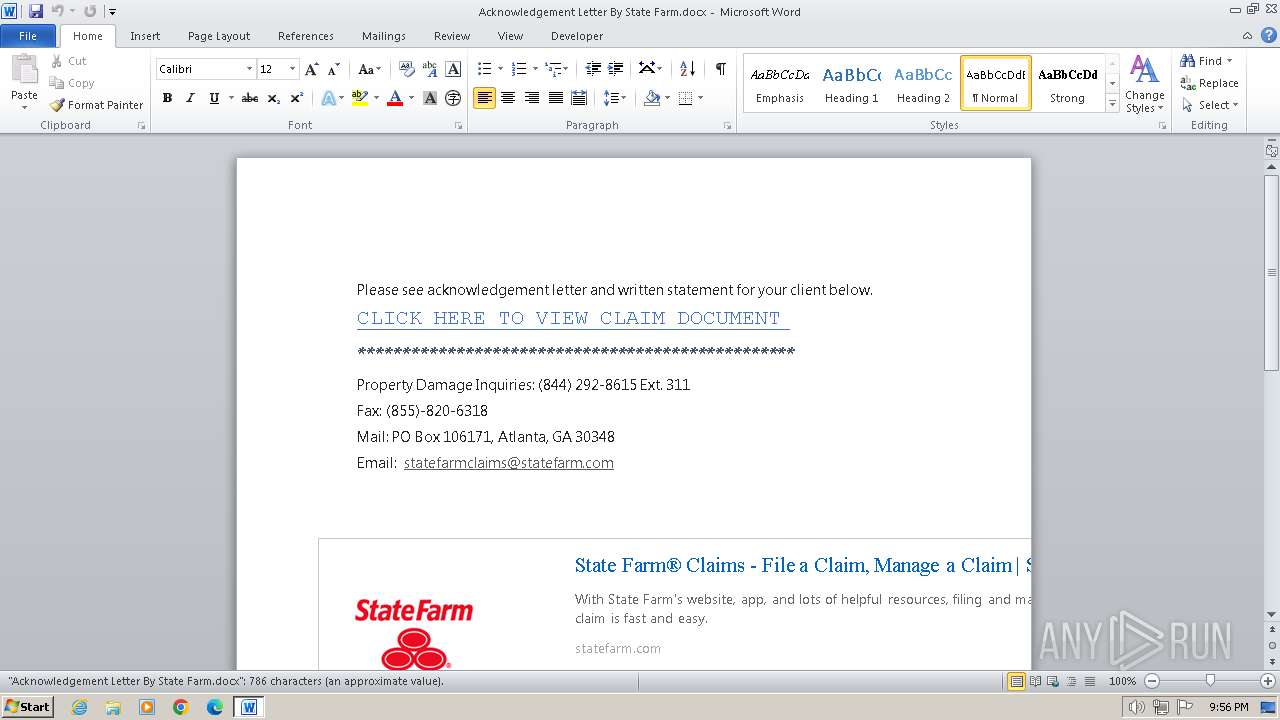
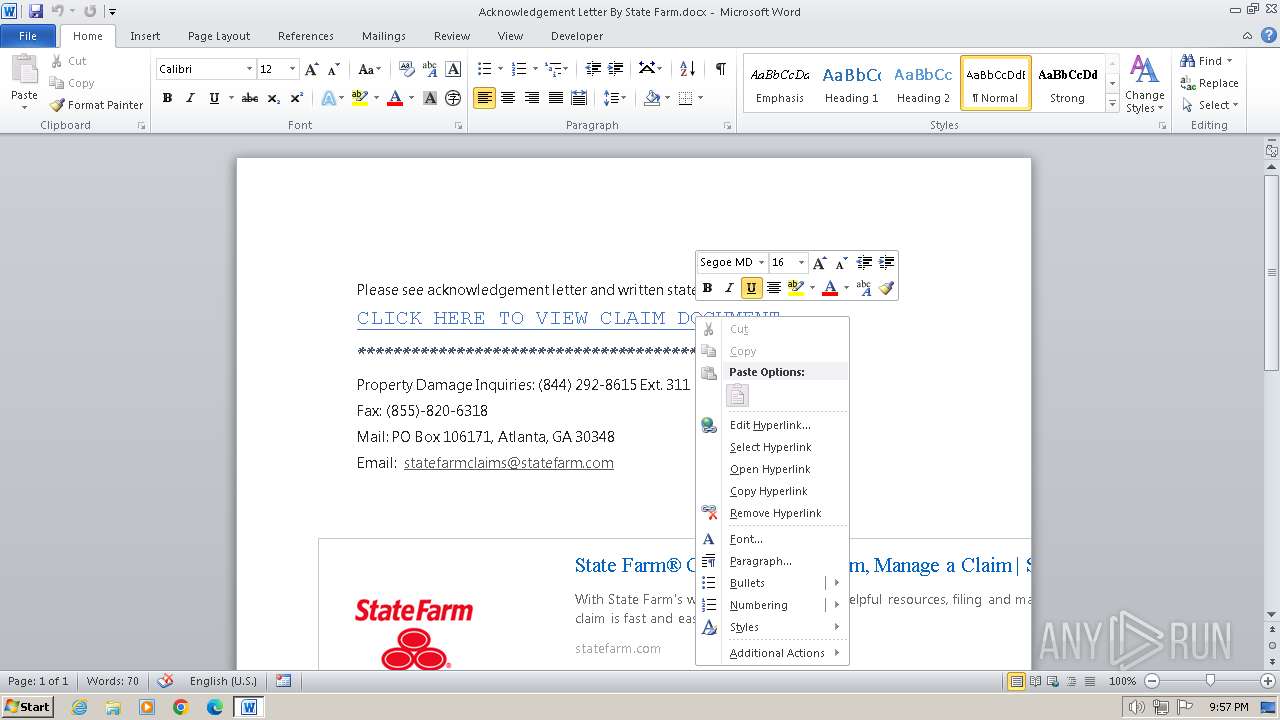
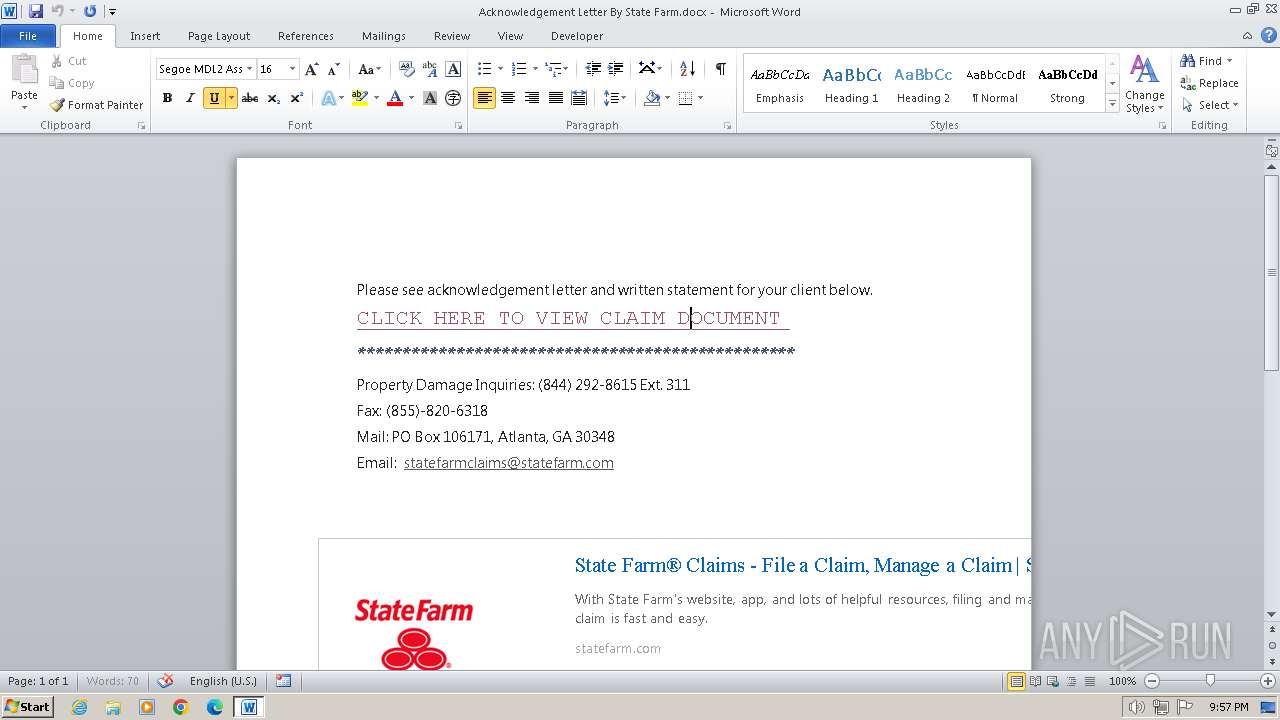
| File name: | Acknowledgement Letter By State Farm.docx |
| Full analysis: | https://app.any.run/tasks/3ea599fd-669a-4c61-bbc9-55215e98b37b |
| Verdict: | Malicious activity |
| Analysis date: | April 02, 2024, 20:56:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 27B43024A8DC753D4580934D091C75AB |
| SHA1: | 7F47244B2726878ACFECD79E1D8AB36EAA319D0F |
| SHA256: | 6B1518CA6DC4D4C9392A42DA01542047D602F81F3566BD98B25C02AD3356092A |
| SSDEEP: | 768:90RCic3UMPSZQpGhoh2v5NkAqgZxjzV9yaMy6A/aHsxA:mUX6QpZh2v5yMxjzeaM7A/y |
MALICIOUS
Connection from MS Office application
- WINWORD.EXE (PID: 3212)
SUSPICIOUS
Non-standard symbols in registry
- WINWORD.EXE (PID: 3212)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 1576)
Reads the computer name
- wmpnscfg.exe (PID: 1576)
Manual execution by a user
- wmpnscfg.exe (PID: 1576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2012:07:02 09:52:14 |
| ZipCRC: | 0x6c8be8b9 |
| ZipCompressedSize: | 368 |
| ZipUncompressedSize: | 1350 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Lines: | - |
| Paragraphs: | - |
| TotalEditTime: | 7 minutes |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| Application: | WPS Office_12.2.0.13489_F1E327BC-269C-435d-A152-05C5408002CA |
| DocSecurity: | None |
| CreateDate: | 2024:04:02 20:07:00Z |
| LastModifiedBy: | Administrator |
| ModifyDate: | 2024:04:02 20:16:29Z |
| RevisionNumber: | 1 |
| KSOProductBuildVer: | 1033-12.2.0.13489 |
| ICV: | 1E1781493D1D45469857E73EA1E6A1AF_11 |
XMP
| Creator: | Administrator |
|---|
Total processes
42
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1576 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3212 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Acknowledgement Letter By State Farm.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
10 647
Read events
9 357
Write events
967
Delete events
323
Modification events
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z}' |
Value: 7A7D27008C0C0000010000000000000000000000 | |||
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3212) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
3
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3212 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR21FA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3212 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:— | SHA256:— | |||
| 3212 | WINWORD.EXE | C:\Users\admin\Desktop\~$knowledgement Letter By State Farm.docx | binary | |
MD5:— | SHA256:— | |||
| 3212 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Acknowledgement Letter By State Farm.docx.LNK | binary | |
MD5:— | SHA256:— | |||
| 3212 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3212 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:— | SHA256:— | |||
| 3212 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\profiles.bin | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
9
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3212 | WINWORD.EXE | GET | 404 | 23.216.77.75:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a55b9264166522a9 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 404 | 23.216.77.74:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0754c686571bd23f | unknown | — | — | unknown |
1080 | svchost.exe | GET | 404 | 23.216.77.74:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3e412f7b4eff0943 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 404 | 23.216.77.74:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e2ddf83a2417bb20 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 404 | 23.216.77.74:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fc91d912a85a08d5 | unknown | — | — | unknown |
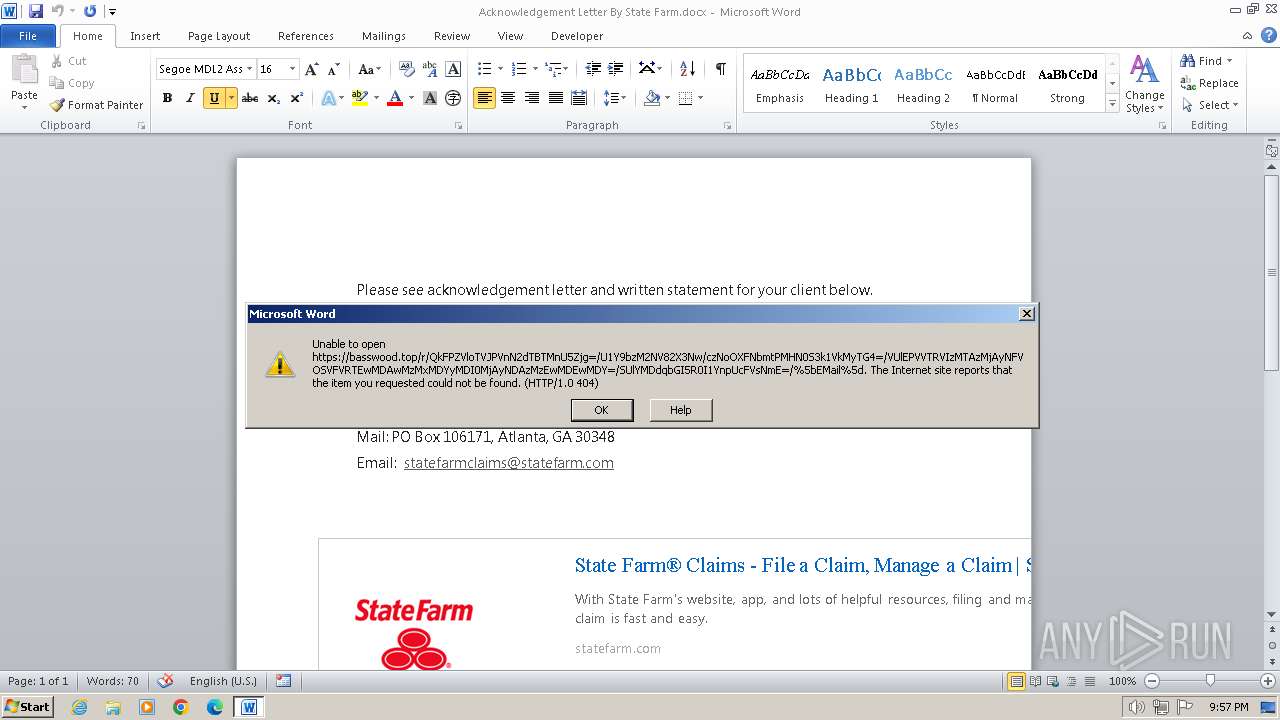
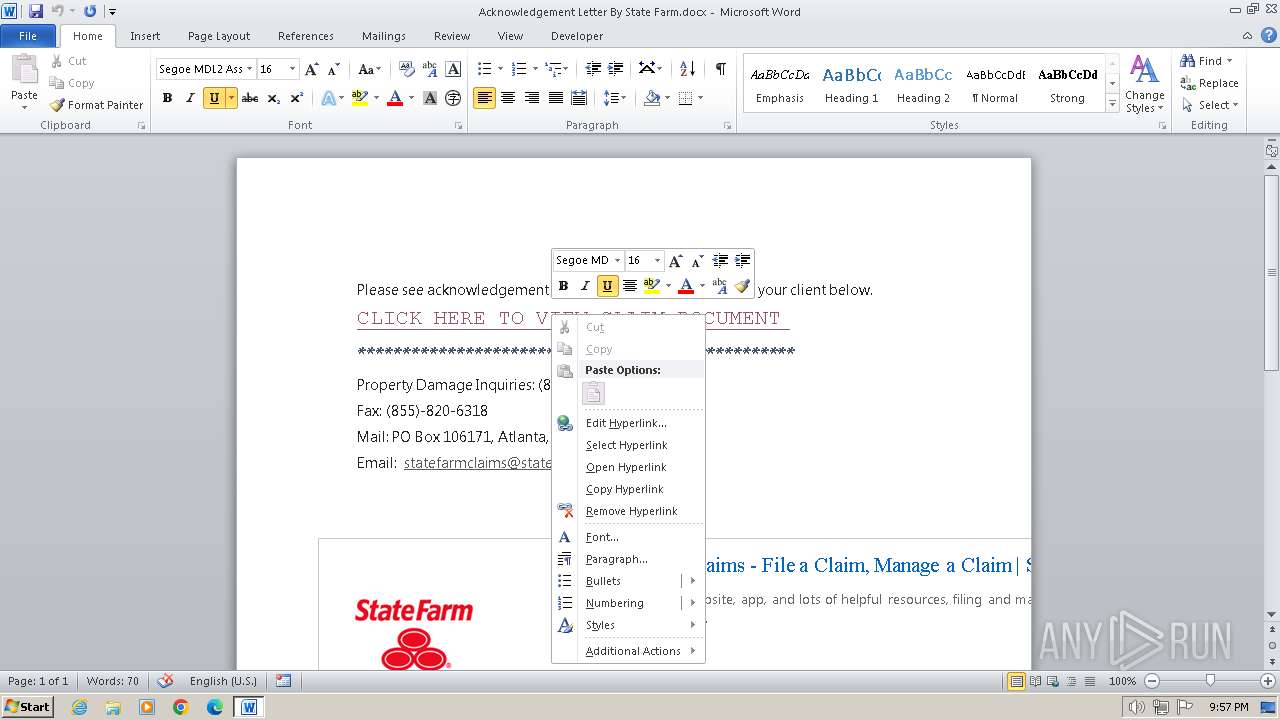
— | — | GET | 404 | 49.13.77.253:443 | https://49.13.77.253/r/QkFPZVloTVJPVnN2dTBTMnU5Zjg=/U1Y9bzM2NV82X3Nw/czNoOXFNbmtPMHN0S3k1VkMyTG4=/VUlEPVVTRVIzMTAzMjAyNFVOSVFVRTEwMDAwMzMxMDYyMDI0MjAyNDAzMzEwMDEwMDY=/SUlYMDdqbGI5R0I1YnpUcFVsNmE=/%5bEMail%5d | unknown | xml | 341 b | unknown |
— | — | GET | 404 | 49.13.77.253:443 | https://49.13.77.253/r/QkFPZVloTVJPVnN2dTBTMnU5Zjg=/U1Y9bzM2NV82X3Nw/czNoOXFNbmtPMHN0S3k1VkMyTG4=/VUlEPVVTRVIzMTAzMjAyNFVOSVFVRTEwMDAwMzMxMDYyMDI0MjAyNDAzMzEwMDEwMDY=/SUlYMDdqbGI5R0I1YnpUcFVsNmE=/%5bEMail%5d | unknown | xml | 341 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3212 | WINWORD.EXE | 188.114.96.3:443 | basswood.top | CLOUDFLARENET | NL | unknown |
3212 | WINWORD.EXE | 23.216.77.75:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 23.216.77.74:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
basswood.top |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |