| File name: | daemon400.exe |
| Full analysis: | https://app.any.run/tasks/508a2027-20f0-4987-86d4-7b551ce21338 |
| Verdict: | Malicious activity |
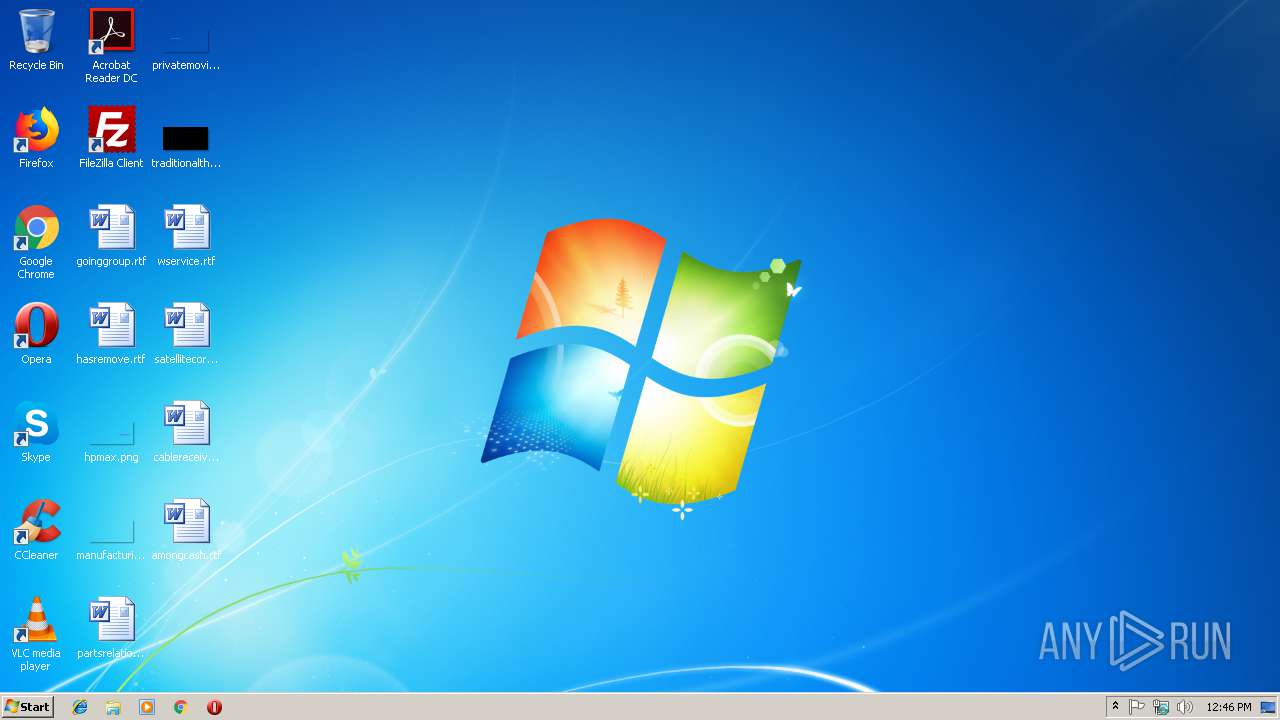
| Analysis date: | January 28, 2019, 12:46:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BF51E181E1C1321D426E9DCA7FD4378F |
| SHA1: | A0037C3C3E60635D1714AC7119EE96693680B973 |
| SHA256: | 6B0D27AE4E4F633D6ED9D81B44DCD1BF9198A5A91D5D1FCDD78CC713038590EB |
| SSDEEP: | 24576:1BJeF06kUGNUjpHJonqg8Th5hkfdfwFIrwA2/vqE4k8DdAp8m/BZwJAnioZ:12RjNTfmpJrX2n8k8DWp8OAyim |
MALICIOUS
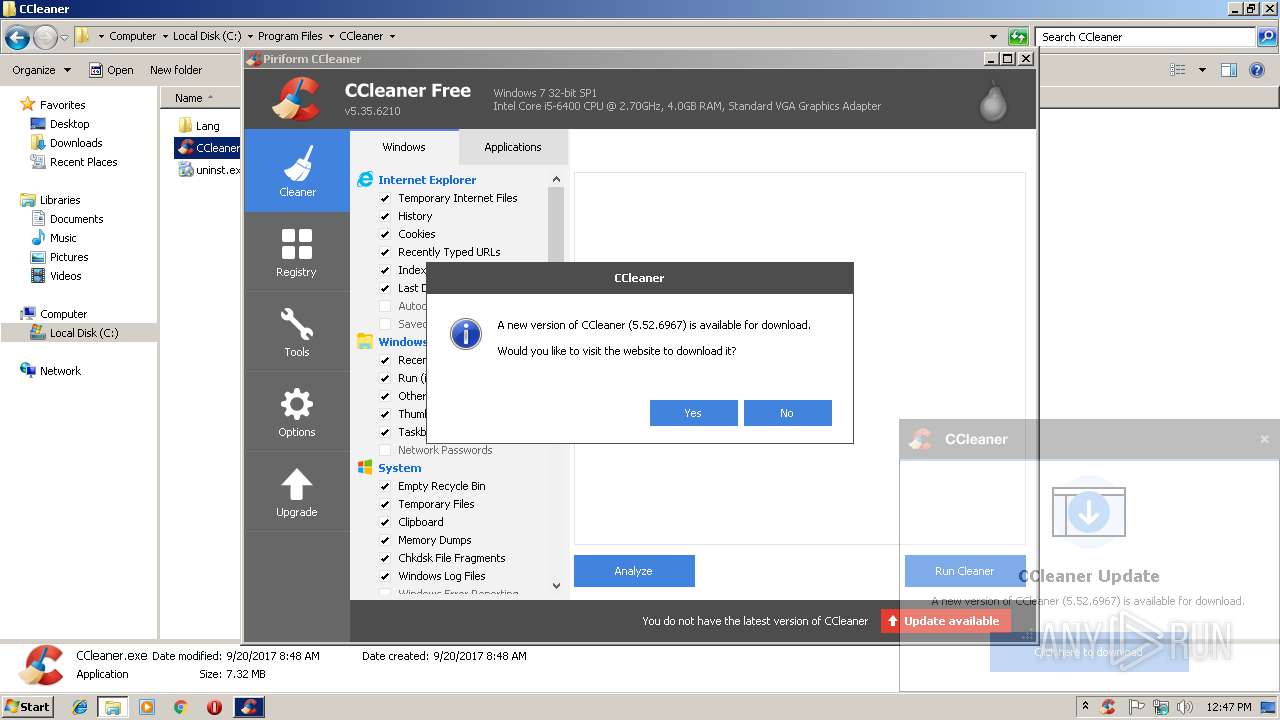
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2328)
- CCleaner.exe (PID: 3168)
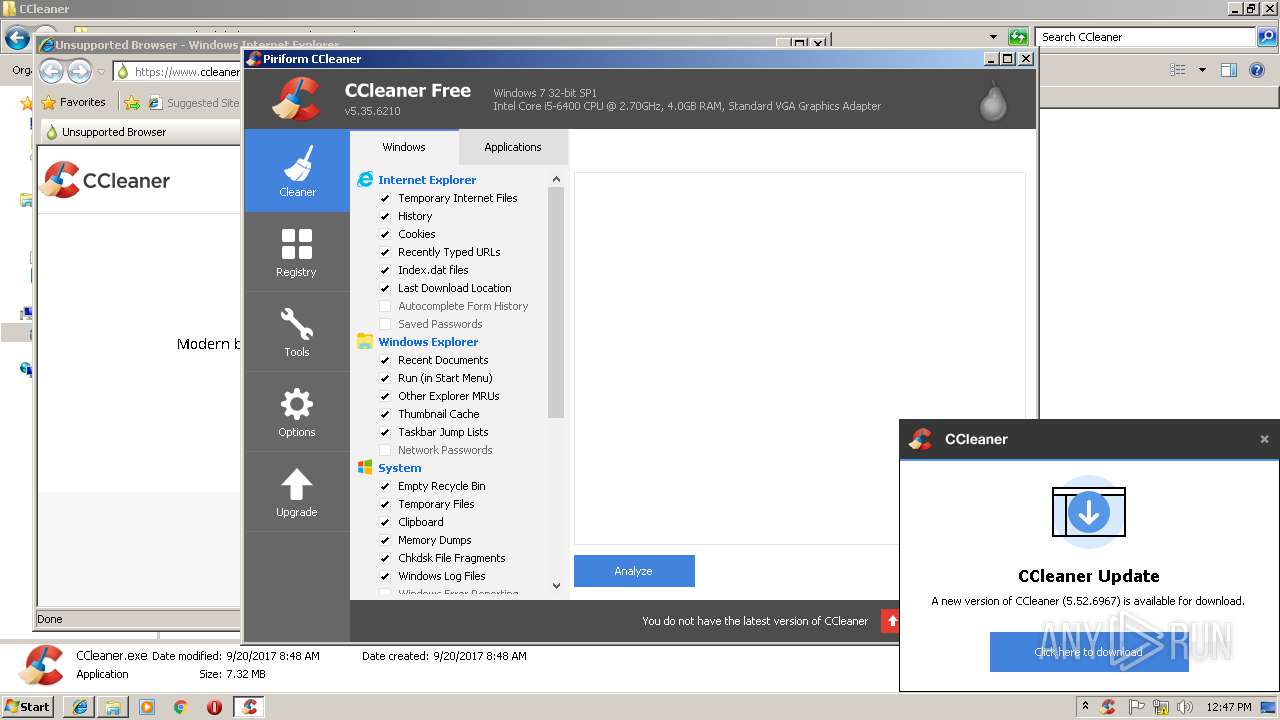
Actions looks like stealing of personal data
- CCleaner.exe (PID: 2496)
- CCleaner.exe (PID: 3168)
Changes the autorun value in the registry
- CCleaner.exe (PID: 3168)
SUSPICIOUS
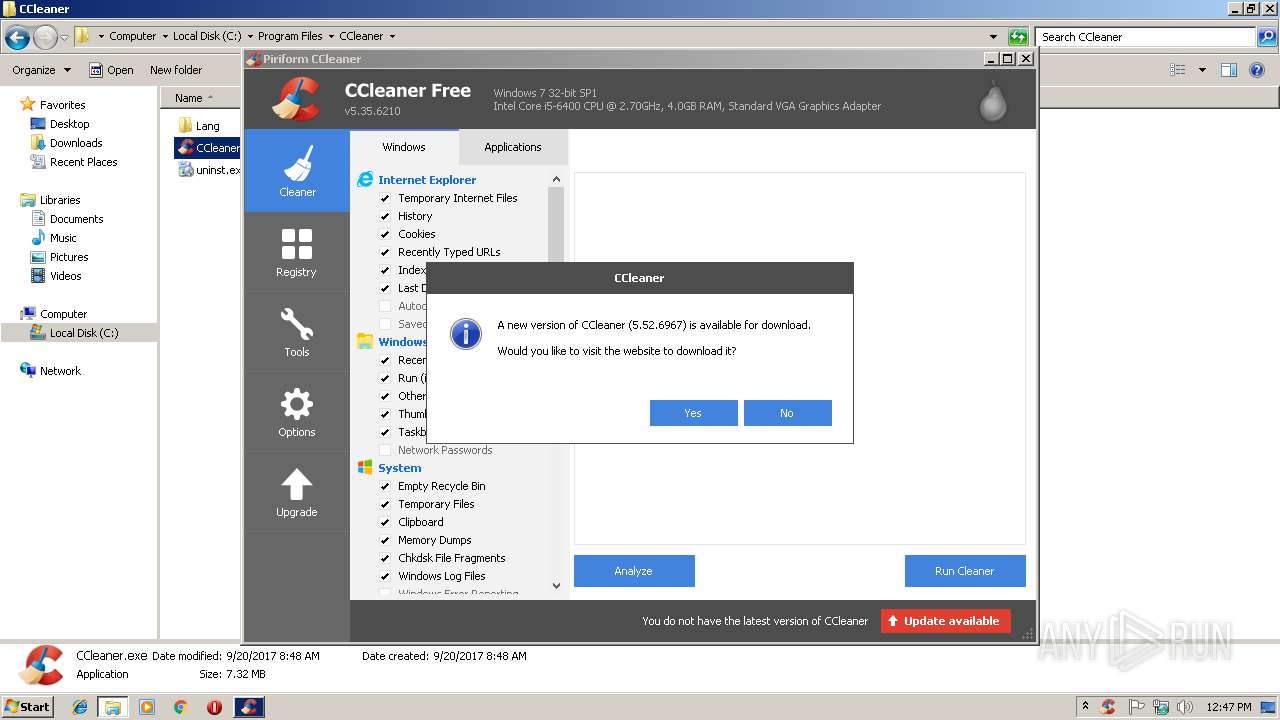
Reads Internet Cache Settings
- CCleaner.exe (PID: 2496)
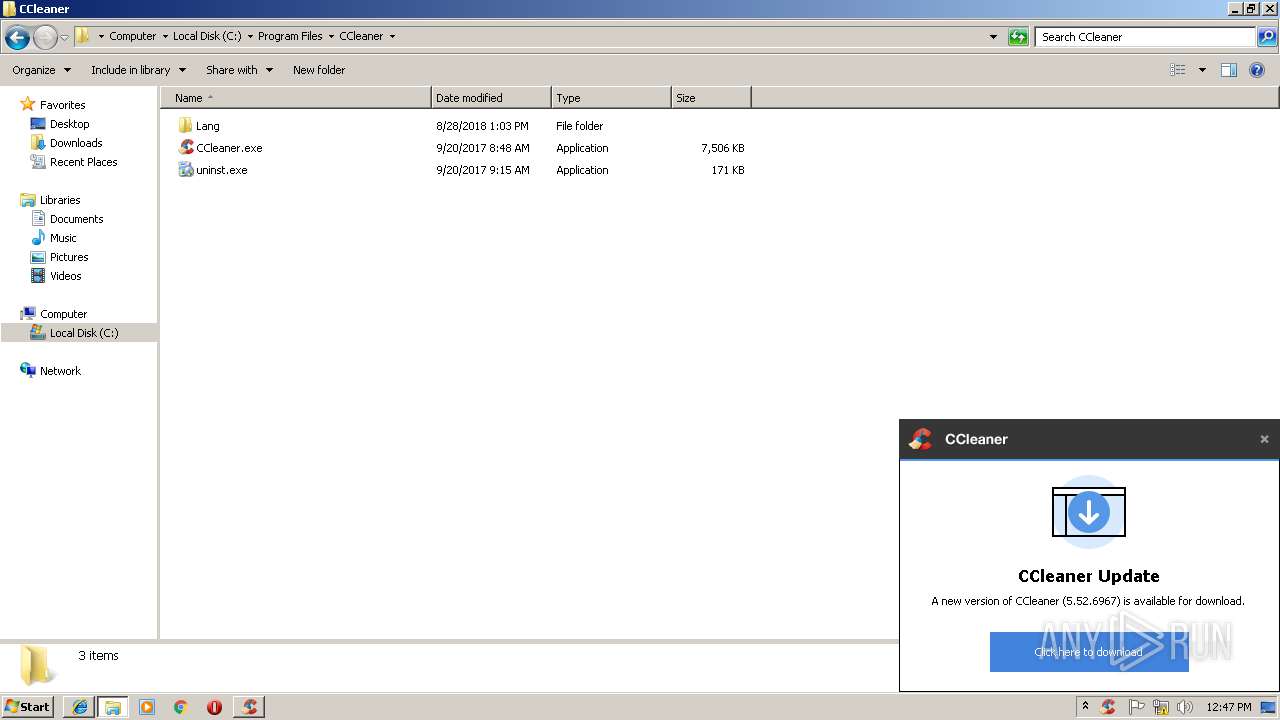
Creates files in the program directory
- pcaui.exe (PID: 2848)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 2496)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 2496)
Creates files in the user directory
- CCleaner.exe (PID: 2496)
Reads internet explorer settings
- CCleaner.exe (PID: 3168)
- CCleaner.exe (PID: 2496)
Application launched itself
- CCleaner.exe (PID: 2496)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 2496)
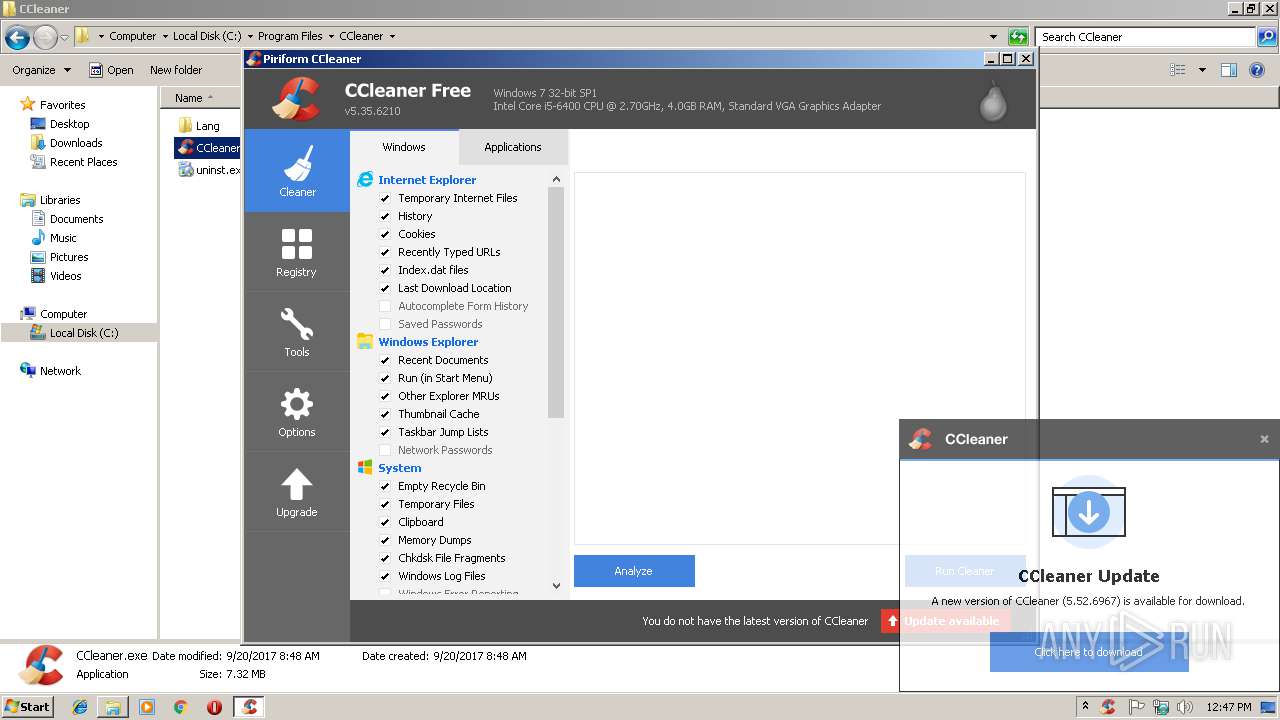
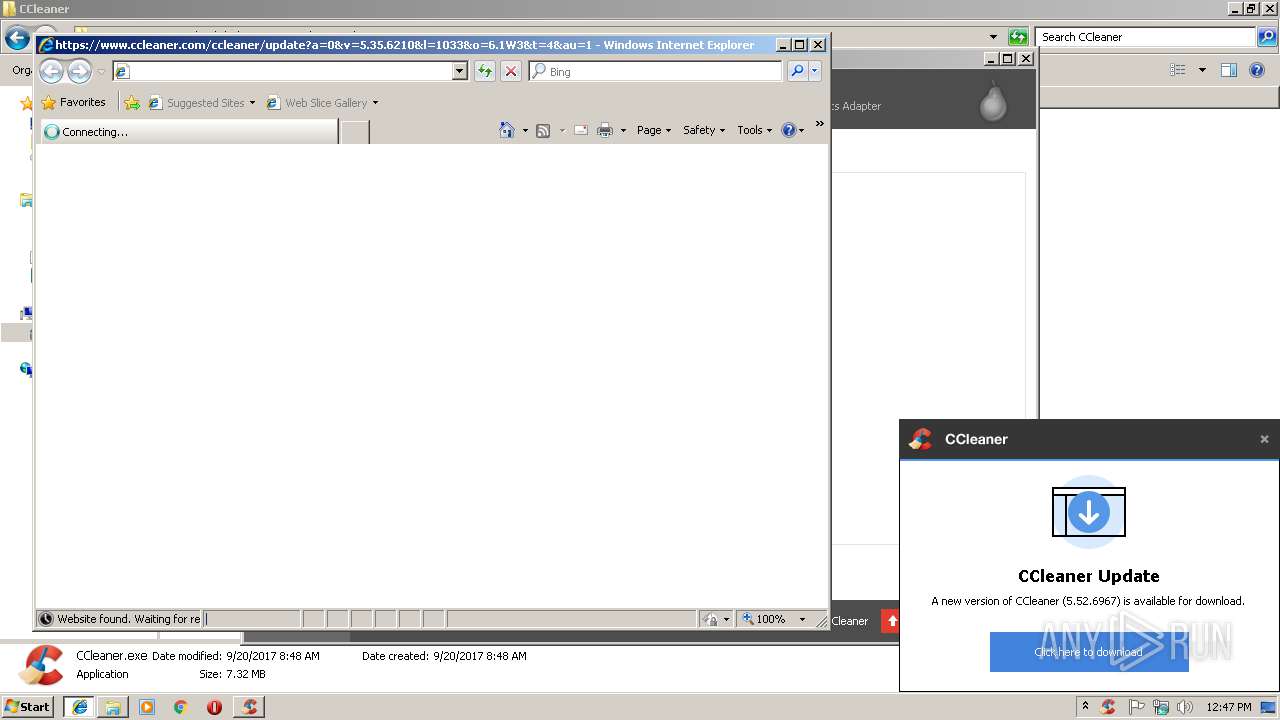
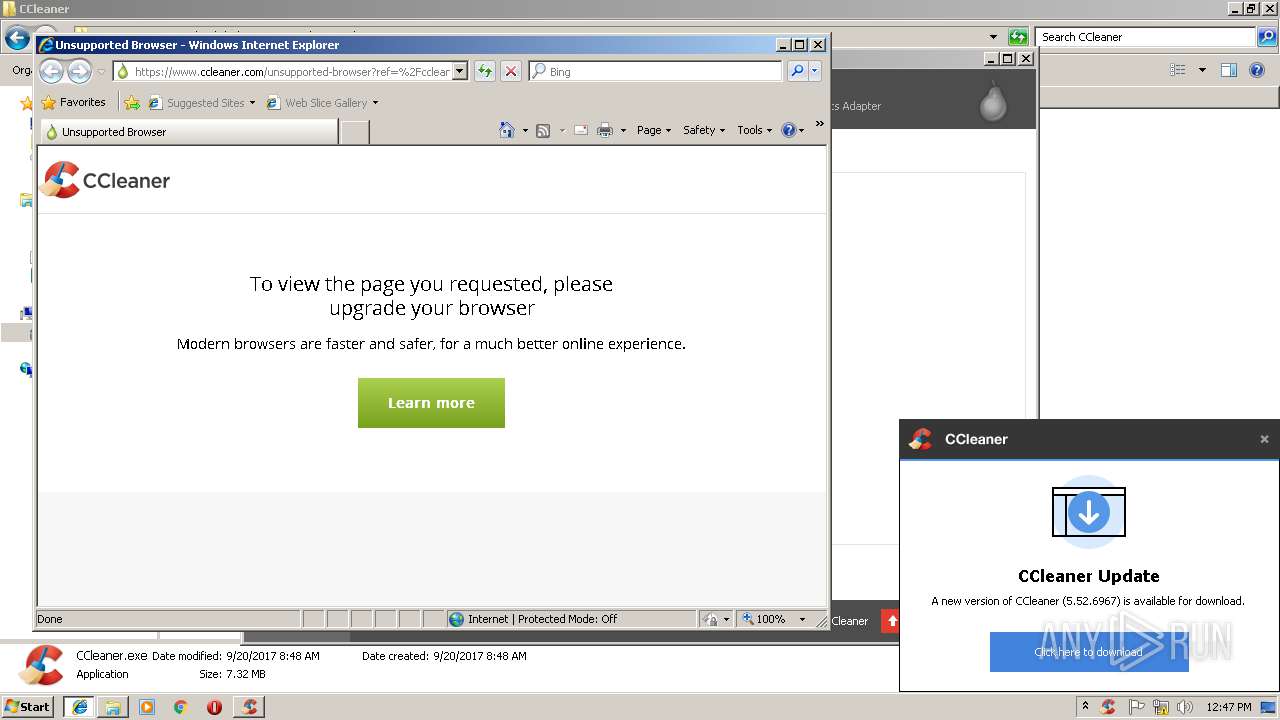
Starts Internet Explorer
- CCleaner.exe (PID: 2496)
INFO
Reads settings of System Certificates
- CCleaner.exe (PID: 2496)
Application launched itself
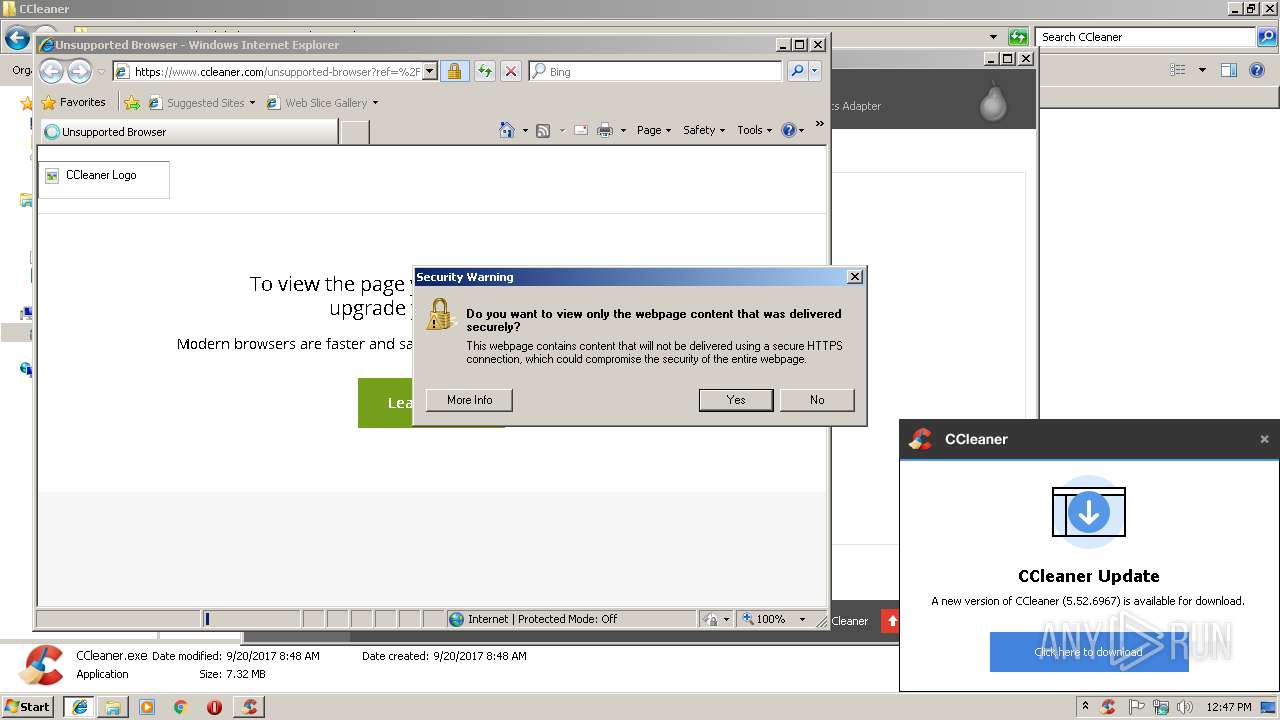
- iexplore.exe (PID: 2688)
Creates files in the user directory
- iexplore.exe (PID: 3656)
Changes internet zones settings
- iexplore.exe (PID: 2688)
Reads internet explorer settings
- iexplore.exe (PID: 3656)
Changes settings of System certificates
- iexplore.exe (PID: 3656)
Reads Internet Cache Settings
- iexplore.exe (PID: 3656)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:11:08 23:02:19+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 23552 |
| InitializedDataSize: | 121344 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3fb9 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | DT Soft Ltd. |
| FileDescription: | DAEMON Tools Setup |
| FileVersion: | 4.00.0.0 |
| InternalName: | daemon400.exe |
| LegalCopyright: | Copyright (C) 2000-2005 |
| OriginalFileName: | daemon400.exe |
| ProductName: | DAEMON Tools |
| ProductVersion: | 4.00.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Nov-2005 22:02:19 |
| Detected languages: |
|
| CompanyName: | DT Soft Ltd. |
| FileDescription: | DAEMON Tools Setup |
| FileVersion: | 4.00.0.0 |
| InternalName: | daemon400.exe |
| LegalCopyright: | Copyright (C) 2000-2005 |
| OriginalFilename: | daemon400.exe |
| ProductName: | DAEMON Tools |
| ProductVersion: | 4.00.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 08-Nov-2005 22:02:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005AA2 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43725 |
.rdata | 0x00007000 | 0x00001444 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08829 |
.data | 0x00009000 | 0x0001B074 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.25221 |
.ndata | 0x00025000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002F000 | 0x0015D200 | 0x0015D200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.9978 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10153 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.28897 | 2216 | UNKNOWN | English - United States | RT_ICON |
102 | 2.69372 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.21733 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.65531 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.67545 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89384 | 248 | UNKNOWN | English - United States | RT_DIALOG |
110 | 2.82633 | 1638 | UNKNOWN | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
45
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
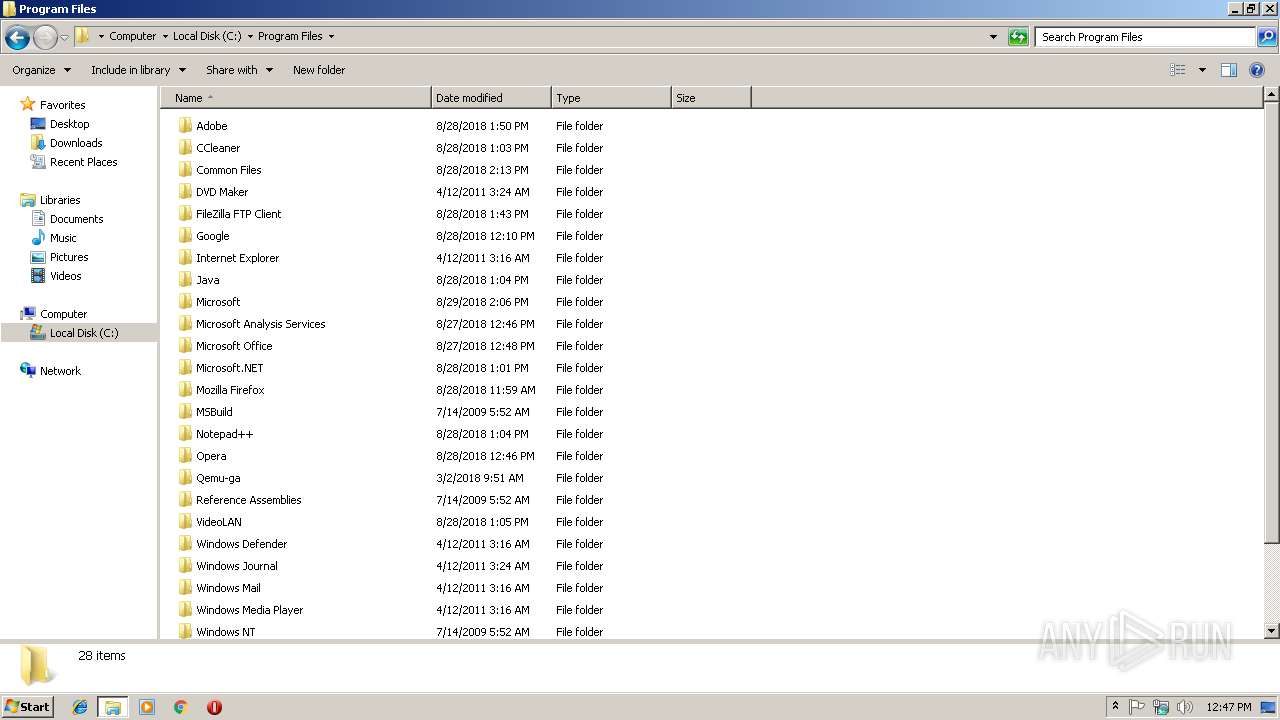
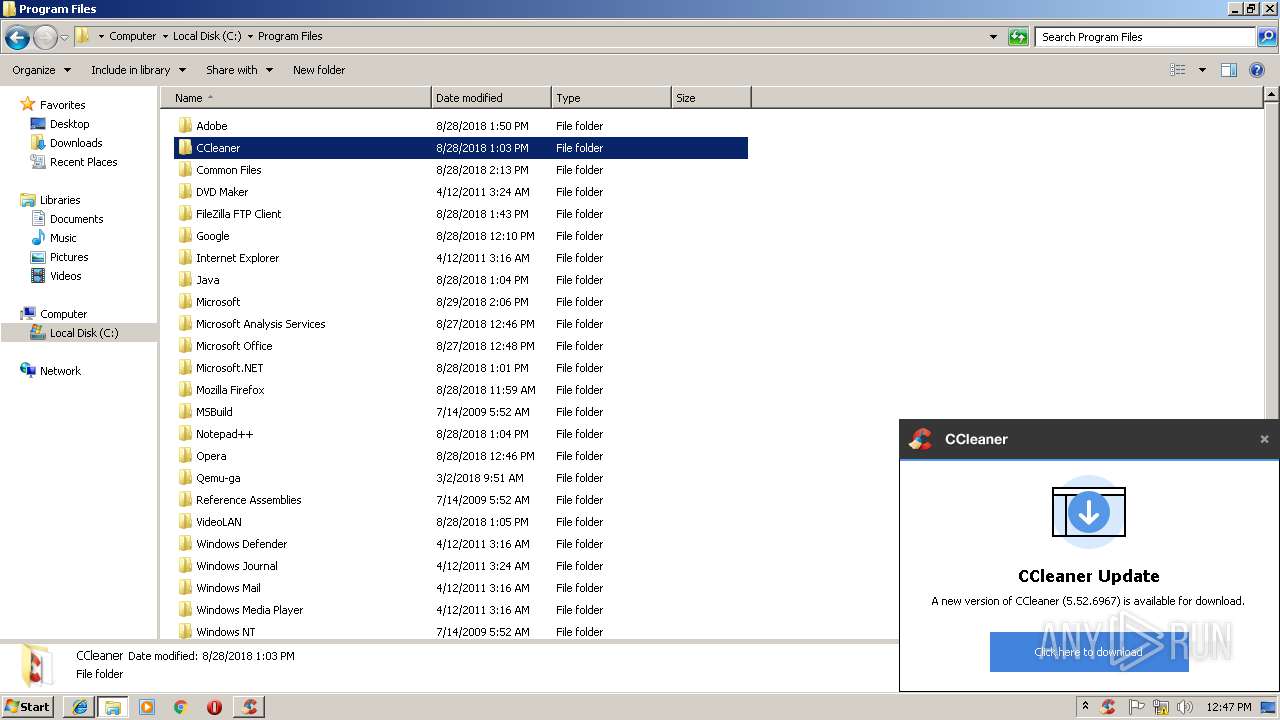
| 2276 | "C:\Users\admin\AppData\Local\Temp\daemon400.exe" | C:\Users\admin\AppData\Local\Temp\daemon400.exe | explorer.exe | ||||||||||||
User: admin Company: DT Soft Ltd. Integrity Level: HIGH Description: DAEMON Tools Setup Exit code: 0 Version: 4.00.0.0 Modules
| |||||||||||||||
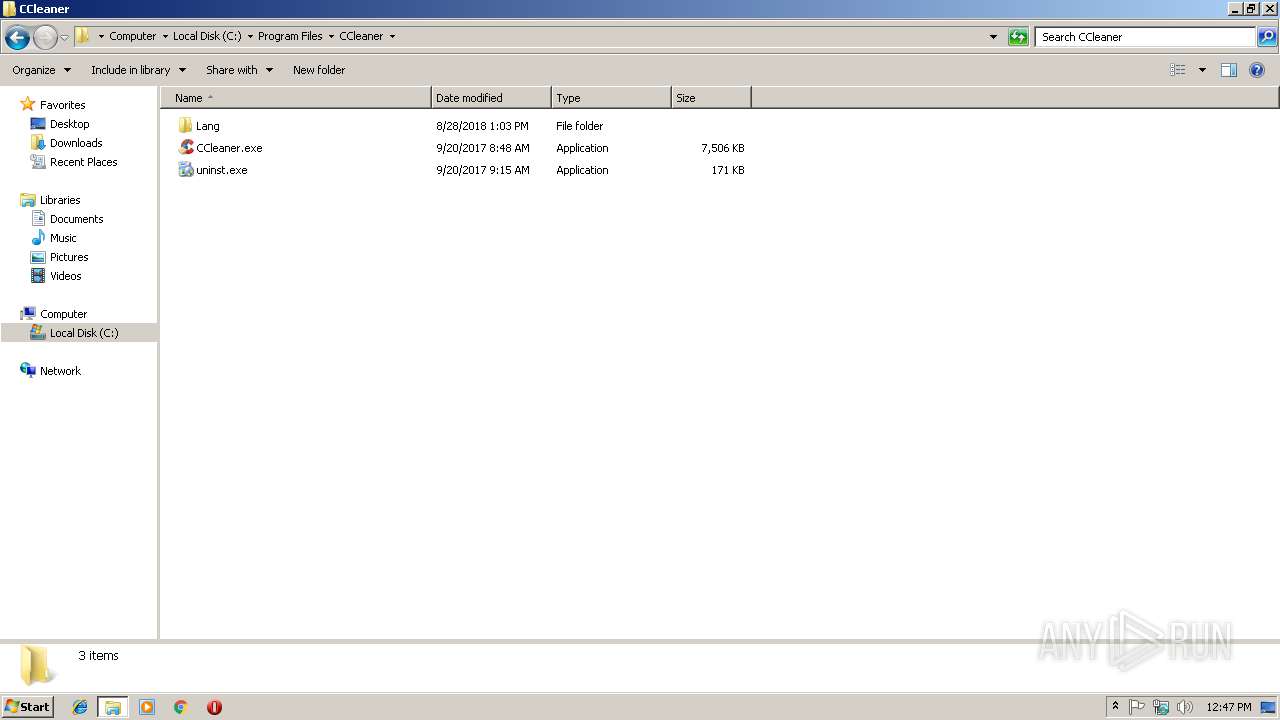
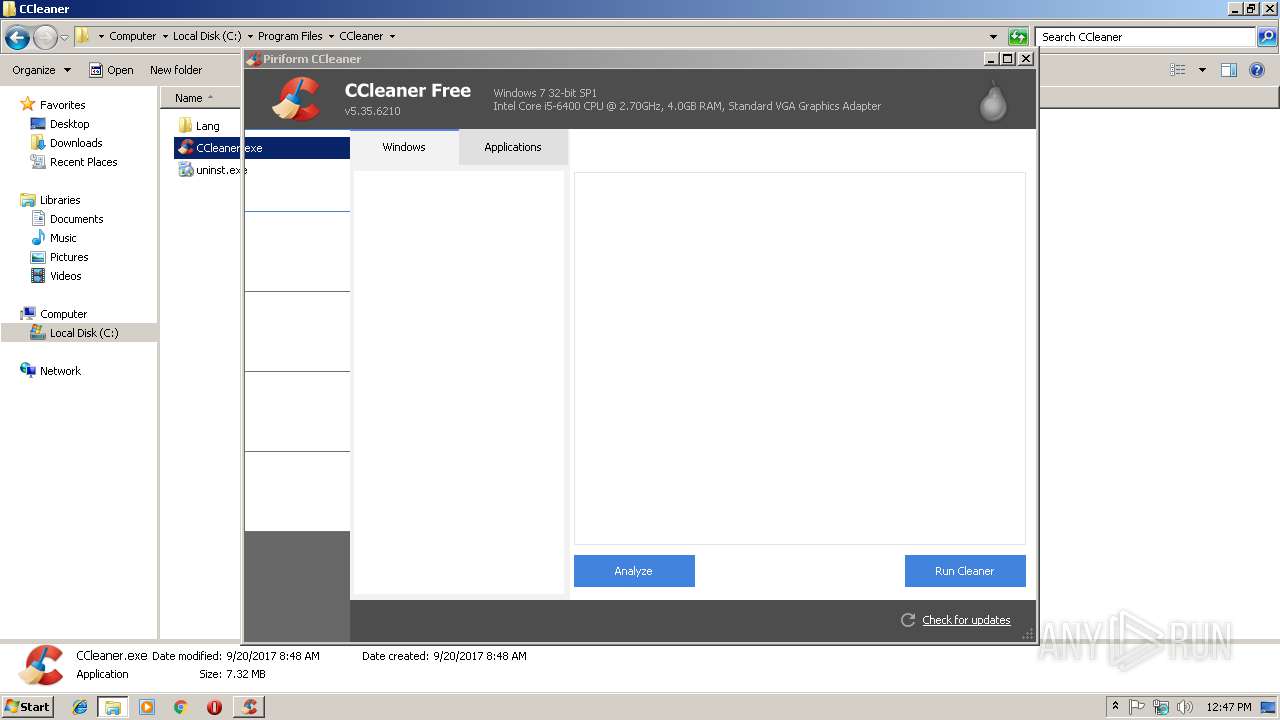
| 2328 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | CCleaner.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
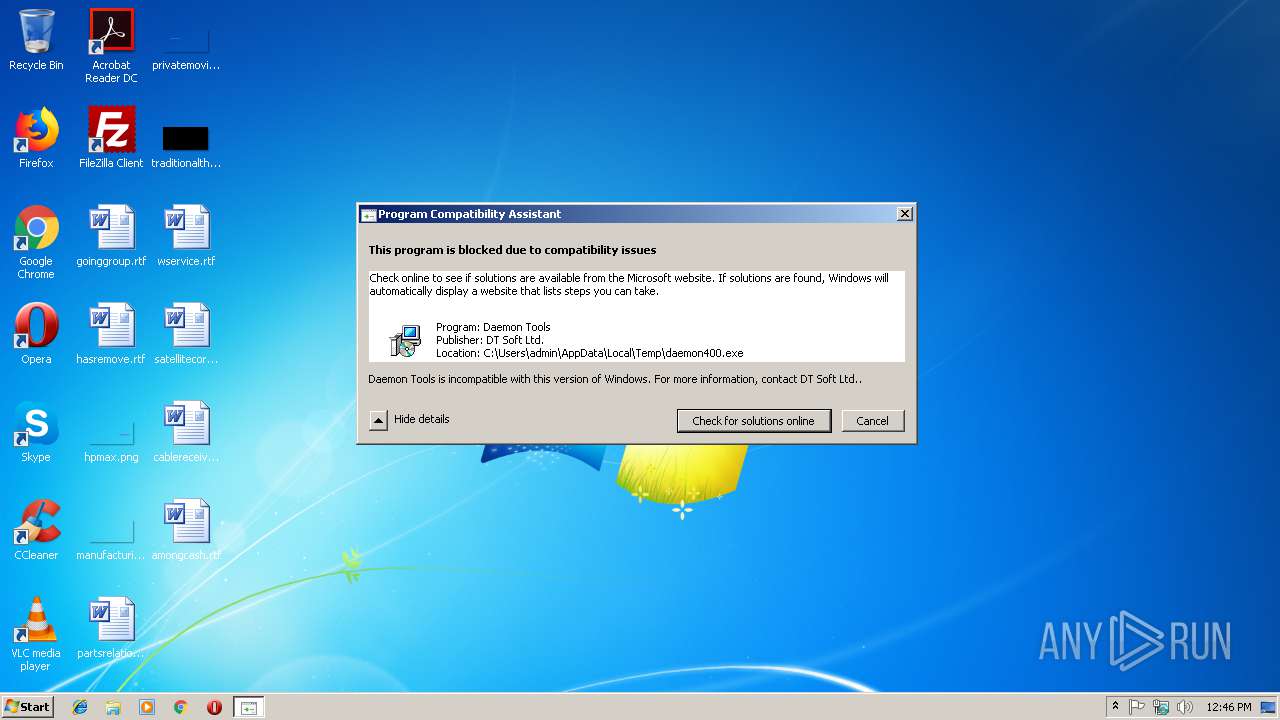
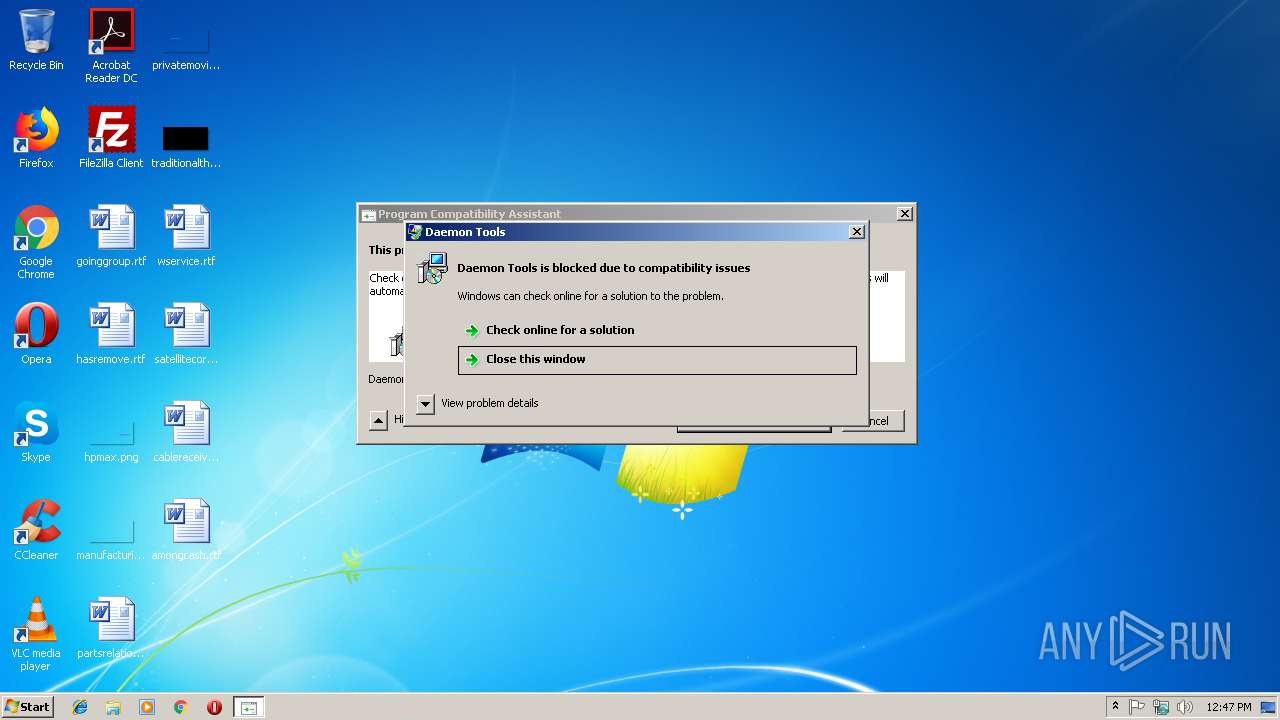
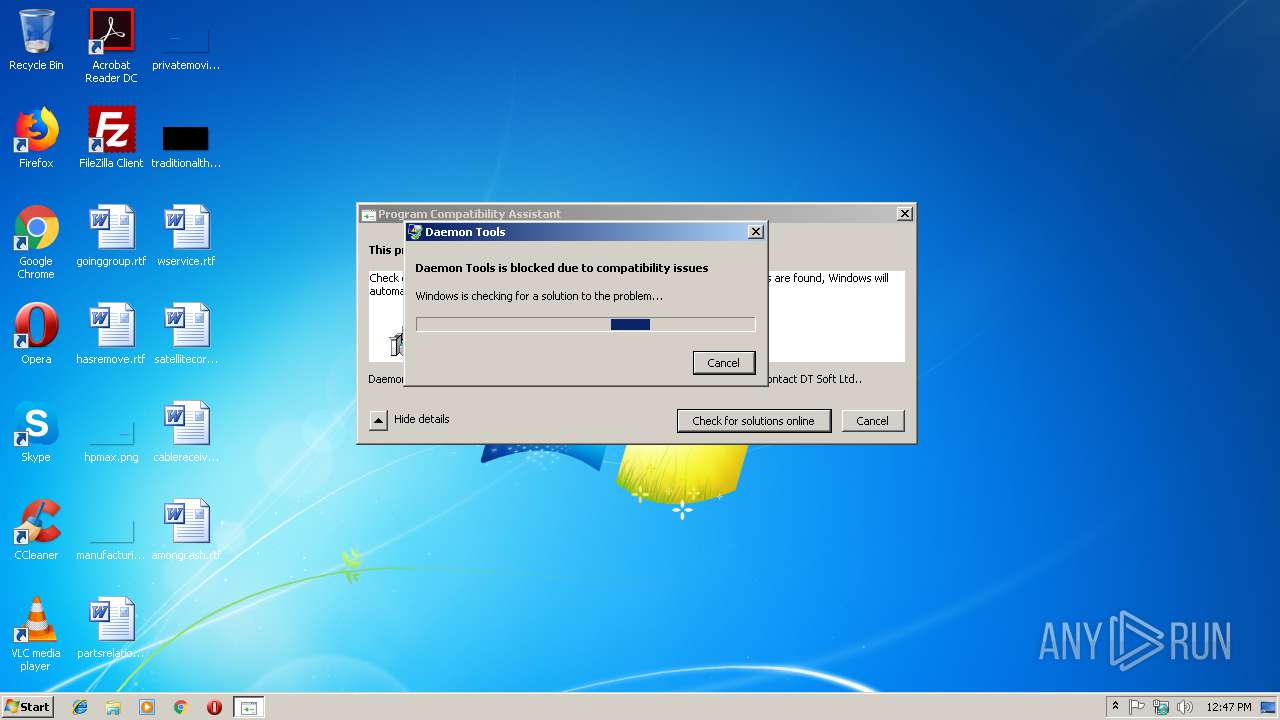
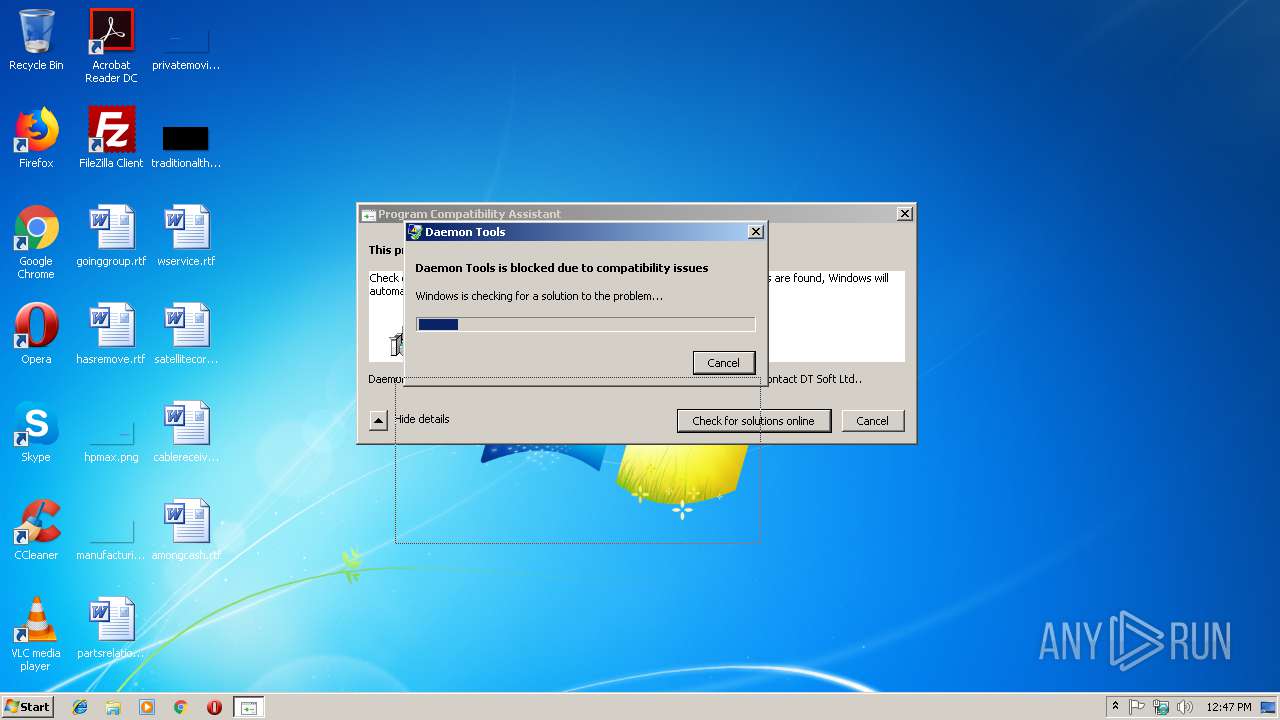
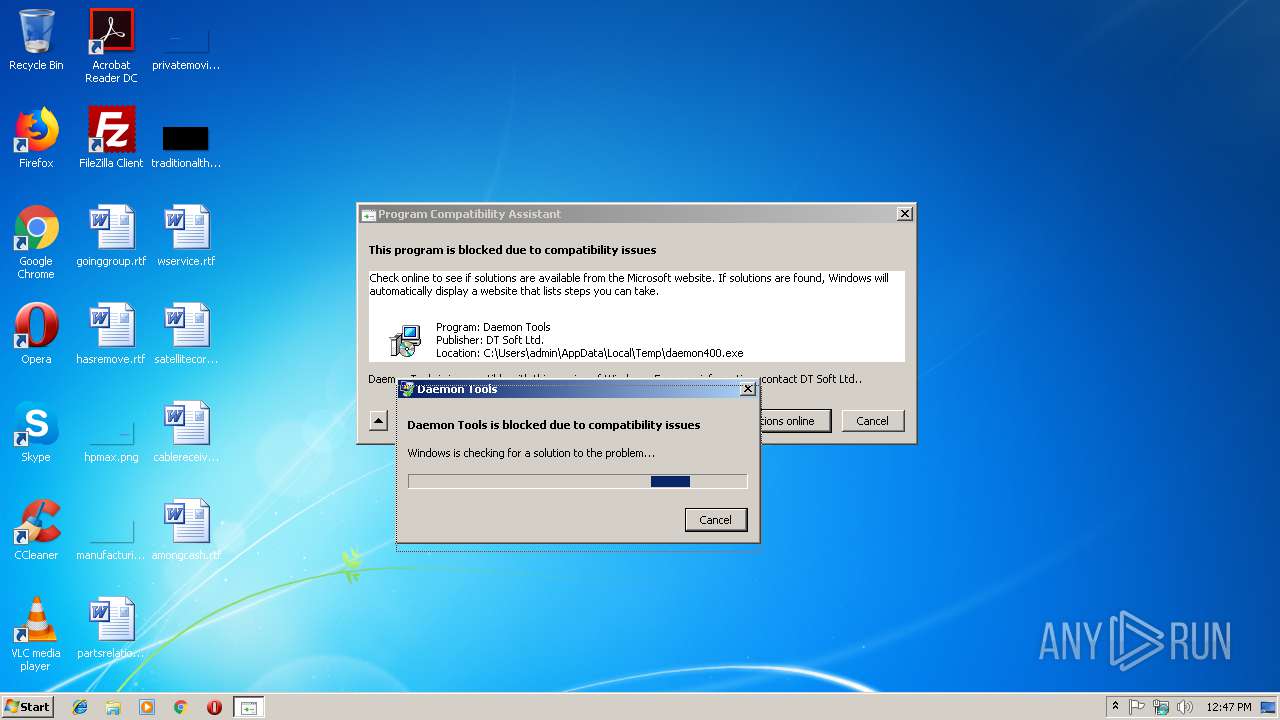
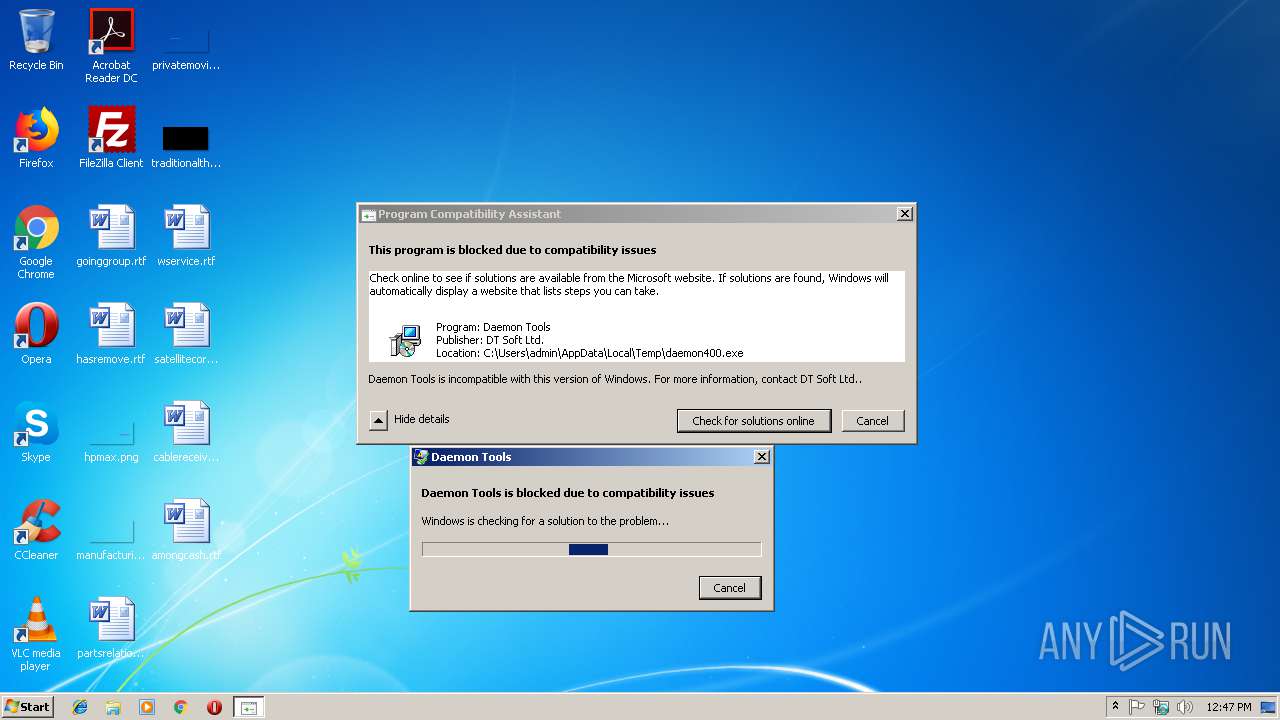
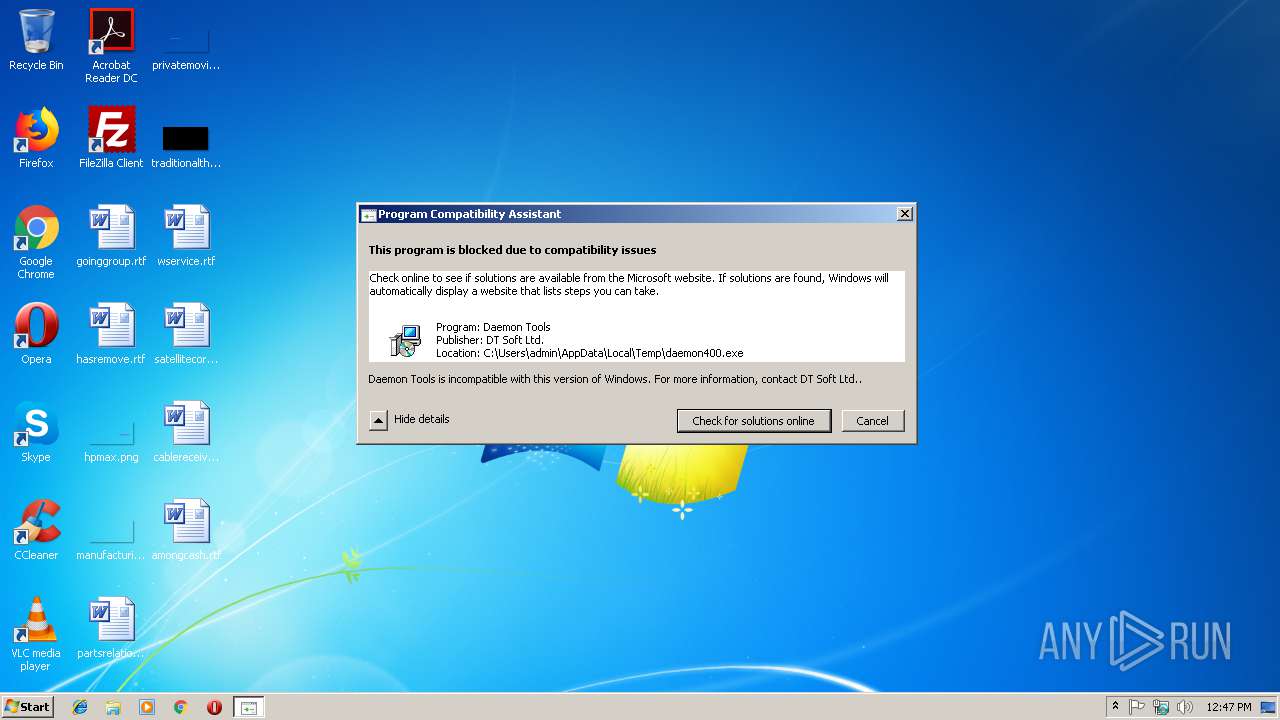
| 2848 | "C:\Windows\System32\pcaui.exe" /g {11111111-1111-1111-1111-111111111111} /x {d4e0cd3e-d8b2-4435-b9cd-bdd575512eee} /a "Daemon Tools" /v "DT Soft Ltd." /s "Daemon Tools is incompatible with this version of Windows. For more information, contact DT Soft Ltd.." /b 2 /e "C:\Users\admin\AppData\Local\Temp\daemon400.exe" | C:\Windows\System32\pcaui.exe | daemon400.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Program Compatibility Assistant User Interface Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\AppData\Local\Temp\daemon400.exe" | C:\Users\admin\AppData\Local\Temp\daemon400.exe | — | explorer.exe | |||||||||||
User: admin Company: DT Soft Ltd. Integrity Level: MEDIUM Description: DAEMON Tools Setup Exit code: 3221226540 Version: 4.00.0.0 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\CCleaner\CCleaner.exe" /monitor | C:\Program Files\CCleaner\CCleaner.exe | CCleaner.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 3656 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2688 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3944 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 420
Read events
1 142
Write events
275
Delete events
3
Modification events
| (PID) Process: | (2496) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | WipeFreeSpaceDrives |
Value: C:\ | |||
| (PID) Process: | (2496) CCleaner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2496) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | CookiesToSave |
Value: *.piriform.com|facebook.com|google.com | |||
| (PID) Process: | (2496) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | RunICS |
Value: 0 | |||
| (PID) Process: | (2496) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | delete value | Name: | AutoICS |
Value: 1 | |||
| (PID) Process: | (2496) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2496) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2496) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | NewVersion |
Value: | |||
| (PID) Process: | (3168) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | Monitoring |
Value: 1 | |||
| (PID) Process: | (3168) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | CCleaner Monitoring |
Value: "C:\Program Files\CCleaner\CCleaner.exe" /MONITOR | |||
Executable files
0
Suspicious files
4
Text files
20
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2496 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\webappsstore.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2496 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IFSY5B0DS1K8GUIZQJZC.temp | — | |
MD5:— | SHA256:— | |||
| 2496 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Y0F8ZS17EYDV4J4SS6WQ.temp | — | |
MD5:— | SHA256:— | |||
| 2496 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FYP64Z0SZZFTJT16M6RM.temp | — | |
MD5:— | SHA256:— | |||
| 2688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2688 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3656 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\update[1].txt | — | |
MD5:— | SHA256:— | |||
| 2848 | pcaui.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\Critical_{11111111-1111-1_7bc61c71355e6e6751a77569baa343a7a3ea7eef_0b39f449\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 3656 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\unsupported-browser[1].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
33
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2848 | pcaui.exe | GET | — | 40.67.186.102:80 | http://watson.microsoft.com/StageOne/Generic/ApphelpHardBlock/%7B11111111-1111-1111-1111-111111111111%7D/%7Bd4e0cd3e-d8b2-4435-b9cd-bdd575512eee%7D.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
2496 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
3656 | iexplore.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/ccleaner/update?a=0&v=5.35.6210&l=1033&o=6.1W3&t=4&au=1 | US | — | — | whitelisted |
2688 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3656 | iexplore.exe | GET | 200 | 151.139.237.73:80 | http://s1.pir.fm/pf/logos--DA8LAgMPCAQ/ccleaner-logo--small.jpg | US | image | 6.34 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3656 | iexplore.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3656 | iexplore.exe | 159.122.87.153:443 | dev.visualwebsiteoptimizer.com | SoftLayer Technologies Inc. | DE | unknown |
2848 | pcaui.exe | 40.67.186.102:80 | watson.microsoft.com | Microsoft Corporation | US | whitelisted |
2496 | CCleaner.exe | 151.101.0.64:443 | www.piriform.com | Fastly | US | whitelisted |
2496 | CCleaner.exe | 151.101.0.64:80 | www.piriform.com | Fastly | US | whitelisted |
2496 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
3656 | iexplore.exe | 151.101.0.64:80 | www.piriform.com | Fastly | US | whitelisted |
2688 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3656 | iexplore.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
3656 | iexplore.exe | 151.139.237.73:80 | s1.pir.fm | netDNA | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |
www.piriform.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.com |
| malicious |
s7.addthis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
dev.visualwebsiteoptimizer.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2848 | pcaui.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |