| File name: | 680467c7f952e4407c159e89174ef5acc7162cd9.exe |
| Full analysis: | https://app.any.run/tasks/ab9ed939-cee3-41cc-a7fc-7fc01a7c4908 |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2019, 09:16:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D9DA8871F5888ED669F9F4171B7562EB |
| SHA1: | 680467C7F952E4407C159E89174EF5ACC7162CD9 |
| SHA256: | 6AF1BDDD7239C0FF3F12A0CD112FCA41618BE64064E6826A21B05B479673B7FF |
| SSDEEP: | 49152:3O1WBdAXN8W2c2Ywo+8reWV237lSGsY+BGgmRAMMiu+pj/Pxh7kQpN35O:3kWTAXNrH+rWqxqY+kb0iVpj/ZmQVO |
MALICIOUS
Application was dropped or rewritten from another process
- pack.exe (PID: 2988)
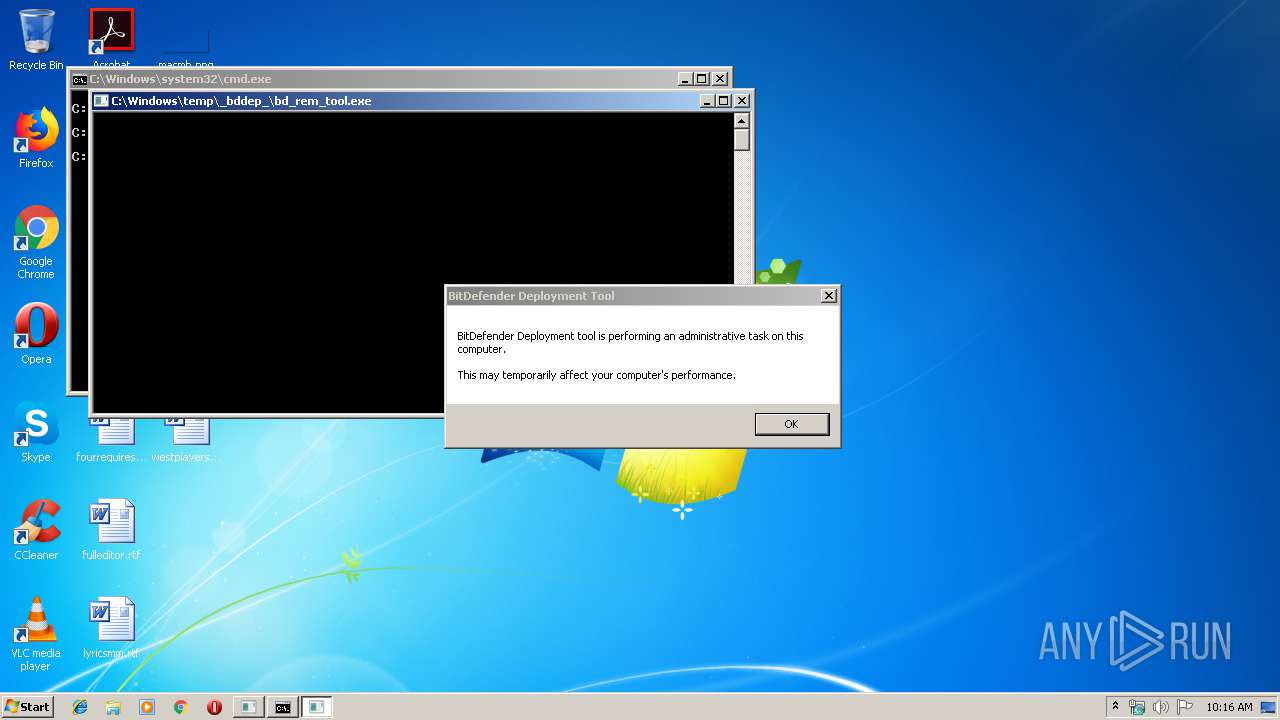
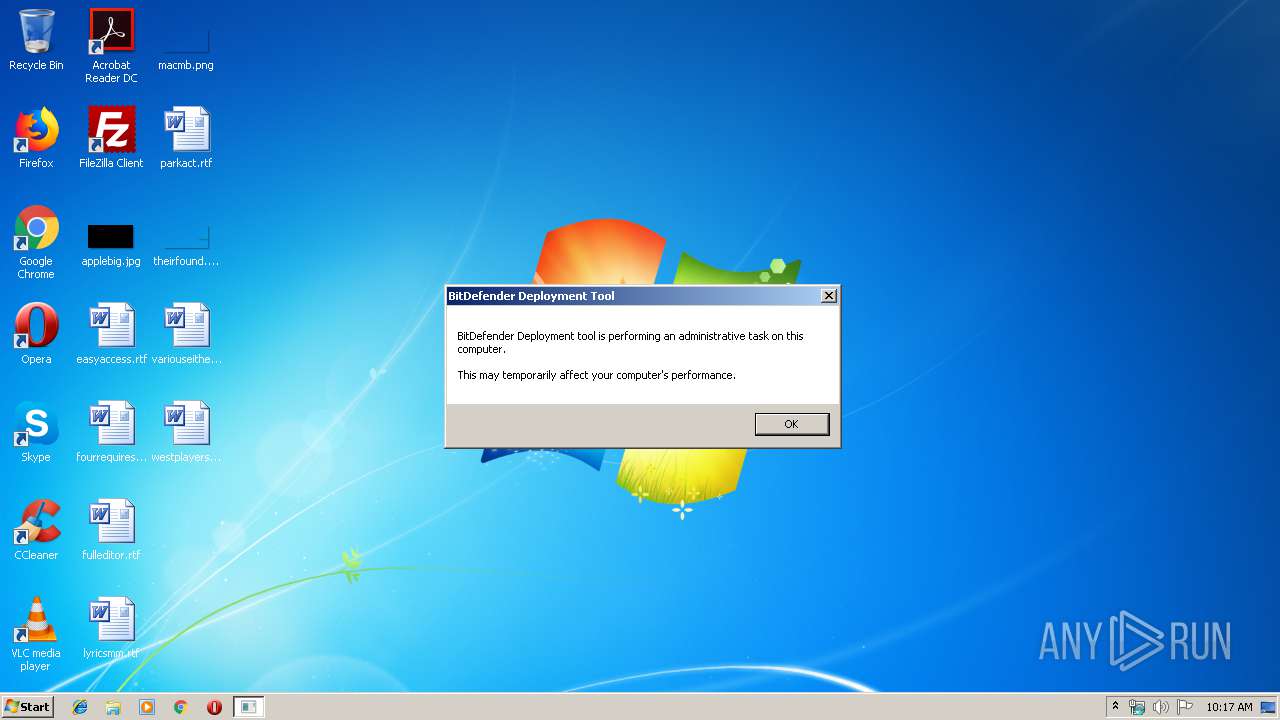
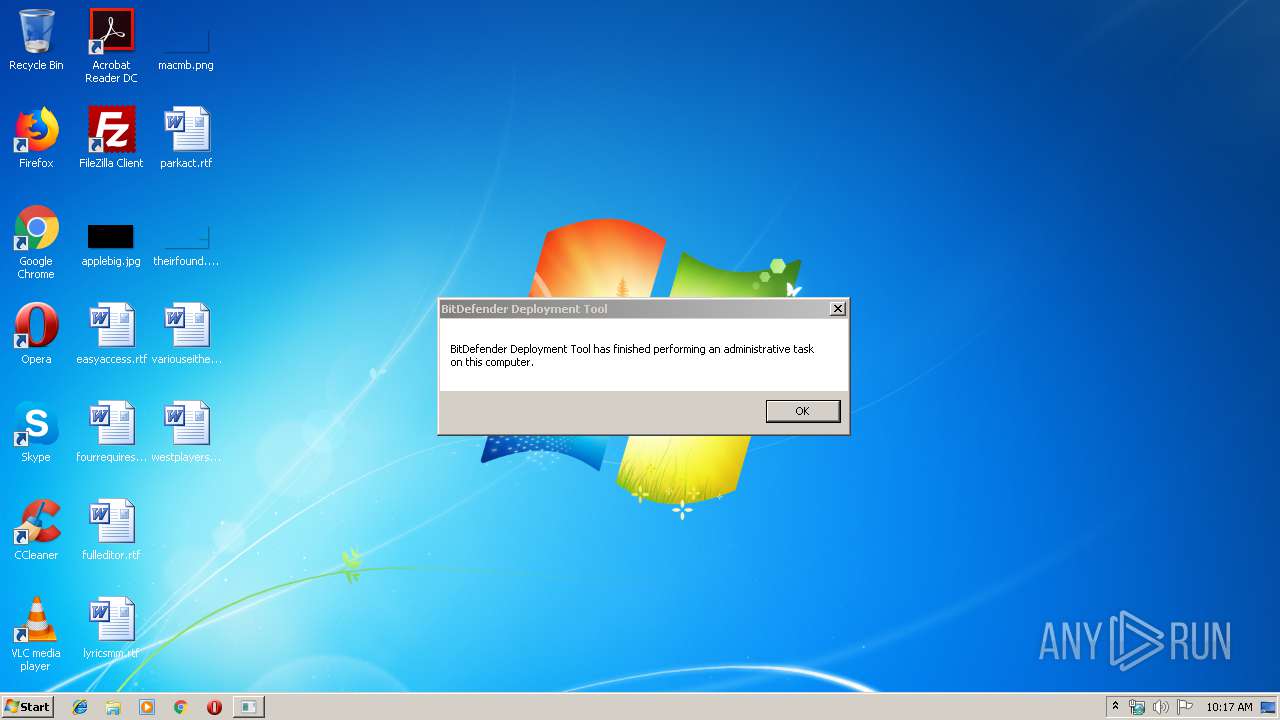
- bd_rem_tool.exe (PID: 2820)
Loads dropped or rewritten executable
- bd_rem_tool.exe (PID: 2820)
SUSPICIOUS
Creates files in the Windows directory
- 680467c7f952e4407c159e89174ef5acc7162cd9.exe (PID: 3648)
- pack.exe (PID: 2988)
Starts CMD.EXE for commands execution
- 680467c7f952e4407c159e89174ef5acc7162cd9.exe (PID: 3648)
Removes files from Windows directory
- pack.exe (PID: 2988)
- 680467c7f952e4407c159e89174ef5acc7162cd9.exe (PID: 3648)
Executable content was dropped or overwritten
- 680467c7f952e4407c159e89174ef5acc7162cd9.exe (PID: 3648)
- pack.exe (PID: 2988)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:03:12 13:16:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 102400 |
| InitializedDataSize: | 2818048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa09b |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Mar-2009 12:16:57 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 12-Mar-2009 12:16:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001887B | 0x00019000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61255 |
.rdata | 0x0001A000 | 0x00006498 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.37053 |
.data | 0x00021000 | 0x00003A54 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.37113 |
.rsrc | 0x00025000 | 0x002A63EC | 0x002A7000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98266 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.65542 | 86 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.60579 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.9907 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.32412 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.7695 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.30896 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.69457 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.60579 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.9907 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.32412 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHLWAPI.dll |
USER32.dll |
WTSAPI32.dll |
Total processes
37
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2336 | cmd /c C:\Windows\TEMP\_bddep_\run.bat | C:\Windows\system32\cmd.exe | — | 680467c7f952e4407c159e89174ef5acc7162cd9.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2820 | C:\Windows\temp\_bddep_\bd_rem_tool.exe | C:\Windows\temp\_bddep_\bd_rem_tool.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2988 | C:\Windows\temp\_bddep_\pack.exe | C:\Windows\temp\_bddep_\pack.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3648 | "C:\Users\admin\AppData\Local\Temp\680467c7f952e4407c159e89174ef5acc7162cd9.exe" | C:\Users\admin\AppData\Local\Temp\680467c7f952e4407c159e89174ef5acc7162cd9.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
57
Read events
57
Write events
0
Delete events
0
Modification events
Executable files
5
Suspicious files
13
Text files
71
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3648 | 680467c7f952e4407c159e89174ef5acc7162cd9.exe | C:\windows\temp\_bddep_\1970fe6a.bhv | text | |
MD5:— | SHA256:— | |||
| 3648 | 680467c7f952e4407c159e89174ef5acc7162cd9.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\bddep.log | text | |
MD5:— | SHA256:— | |||
| 2988 | pack.exe | C:\Windows\Temp\_bddep_\plugins\ceva_dll.cvd | binary | |
MD5:38117AD1558A7B5523658BA6F4F9B1F8 | SHA256:24B0AE0CF1A8BE5C7A0477678097FA81D41141951254F7F50A6A5121BB716ACD | |||
| 2988 | pack.exe | C:\Windows\Temp\_bddep_\plugins.htm | text | |
MD5:6E551B74C99E6425C2DF03E6ED93263E | SHA256:BA64E429005E817F5C2BE8FDF3F347E25D087A6359D59290F254107783DA70EB | |||
| 2988 | pack.exe | C:\Windows\Temp\_bddep_\plugins\ceva_emu.cvd | xmd | |
MD5:609DF546556B12BBCB1B5DD9EBDB5189 | SHA256:3EDB43B17AEF5DAB16BAF54074A9A691E8BAE514A501BD951C1D9BB36893AD67 | |||
| 2988 | pack.exe | C:\Windows\Temp\_bddep_\plugins\cevakrnl.ivd | pva | |
MD5:A9CB3F64E05E383B580C981F8E169986 | SHA256:A17046BE5FE816F4D8C127D63D4AF8597F3B55FD19FB51772D0D9B4592C5382B | |||
| 2988 | pack.exe | C:\Windows\Temp\_bddep_\plugins\cevakrnl.rvd | xmd | |
MD5:95F086C4B1C9818EE4E5C9FE9E6D669F | SHA256:DE9CC19D7BB43497D83E81D5E8EB9EED00470E58D0BF2241A6C997562BAD0712 | |||
| 2988 | pack.exe | C:\Windows\Temp\_bddep_\plugins\cevakrnl.xmd | xmd | |
MD5:C6D6971F05A6CB96A1600D215EEE5659 | SHA256:7F072E754C7F245AE048CC0A7AEDB32A0CB2F049A94470629AAB190F6AFD973C | |||
| 2988 | pack.exe | C:\Windows\Temp\_bddep_\plugins\ceva_vfs.ivd | binary | |
MD5:4CFE5C943B28174BA34DDF7F3801750F | SHA256:AE1EB54F7859D558112BB1CD14172C0D480F11E5DC75ECE6F53D99505BA74C62 | |||
| 2988 | pack.exe | C:\Windows\Temp\_bddep_\plugins\cevakrnl.cvd | pva | |
MD5:C0C7861C6A845E3763A1AC778BC0B4F0 | SHA256:747CC0628055449F9D9F17FD0AFBA6B65AB6BE1B80F0E8CFAB18A1D60B095FA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
680467c7f952e4407c159e89174ef5acc7162cd9.exe | dummy
|
680467c7f952e4407c159e89174ef5acc7162cd9.exe | dummy
|
680467c7f952e4407c159e89174ef5acc7162cd9.exe |
-------------------------------- new session ----------------------------------------
bddep_main -> starting...
|
680467c7f952e4407c159e89174ef5acc7162cd9.exe |
-------------------------------- new session ----------------------------------------
bddep_main -> starting...
|
680467c7f952e4407c159e89174ef5acc7162cd9.exe | bddep_main -> createtempdir
|
680467c7f952e4407c159e89174ef5acc7162cd9.exe | bddep_main -> init dropper
|
680467c7f952e4407c159e89174ef5acc7162cd9.exe | RESOURCEENUMERATOR: RES = [BDDROPPERCFGTYPE].[BDDROPPERCFGNAME]
|
680467c7f952e4407c159e89174ef5acc7162cd9.exe | RESOURCEENUMERATOR: RES = [BDDROPPERCMD].[NUMECMD]
|
680467c7f952e4407c159e89174ef5acc7162cd9.exe | RESOURCEENUMERATOR: RES = [BDDROPPEREXE].[1970FE6A.BHV]
|
680467c7f952e4407c159e89174ef5acc7162cd9.exe | RESOURCEENUMERATOR: RES = [BDDROPPEREXE].[PACK.EXE]
|