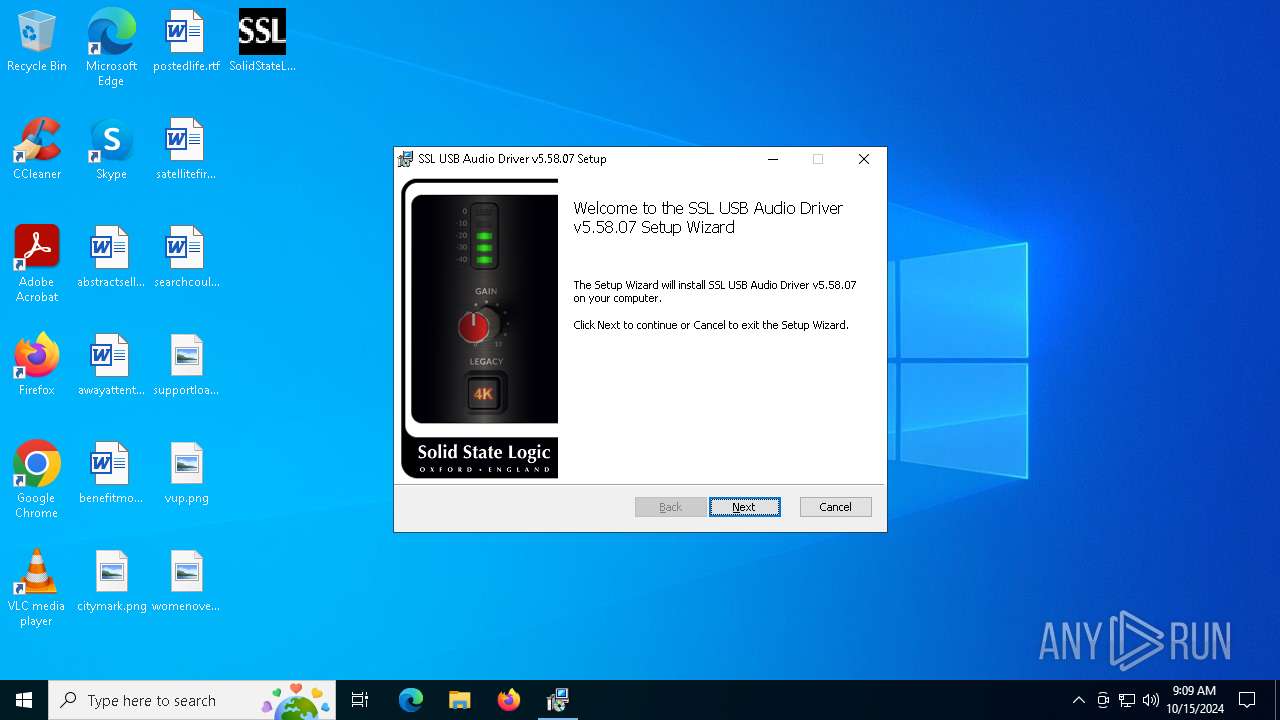
| File name: | SolidStateLogic_UsbAudio_v5.58.07_2023-09-12_setup.exe |
| Full analysis: | https://app.any.run/tasks/c2263151-014a-444e-ad5a-983c1ca94db0 |
| Verdict: | Malicious activity |
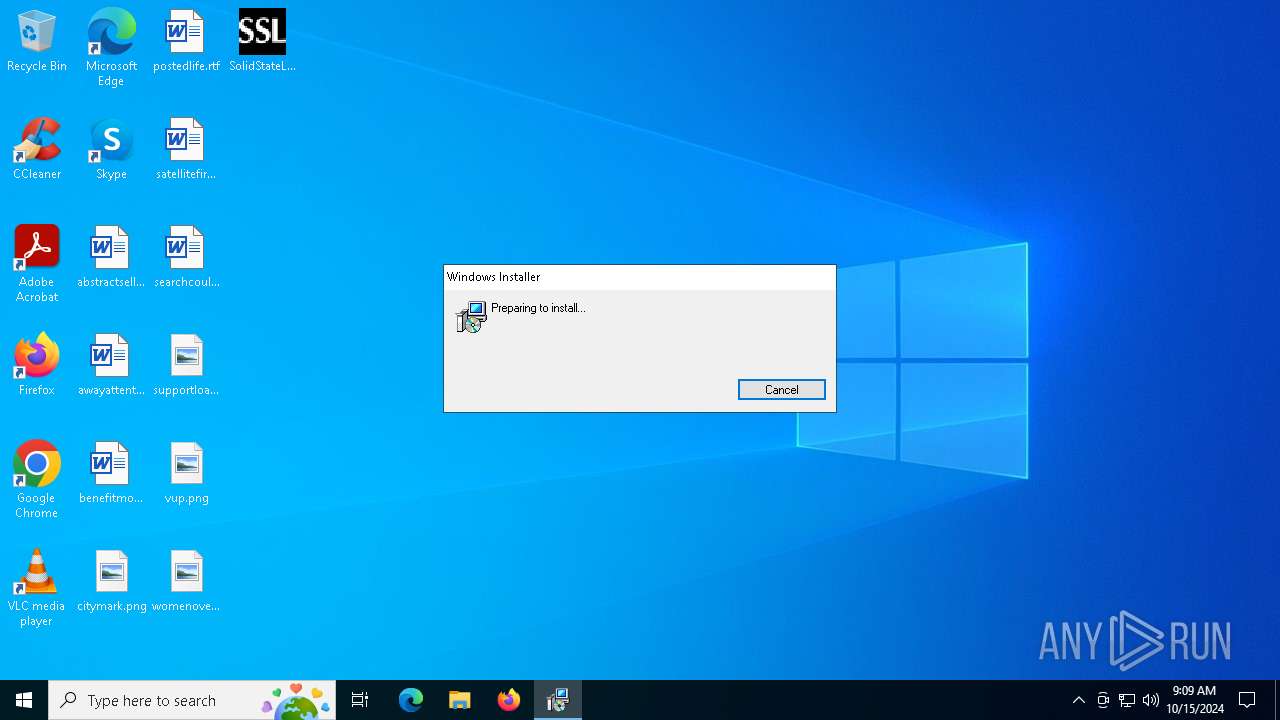
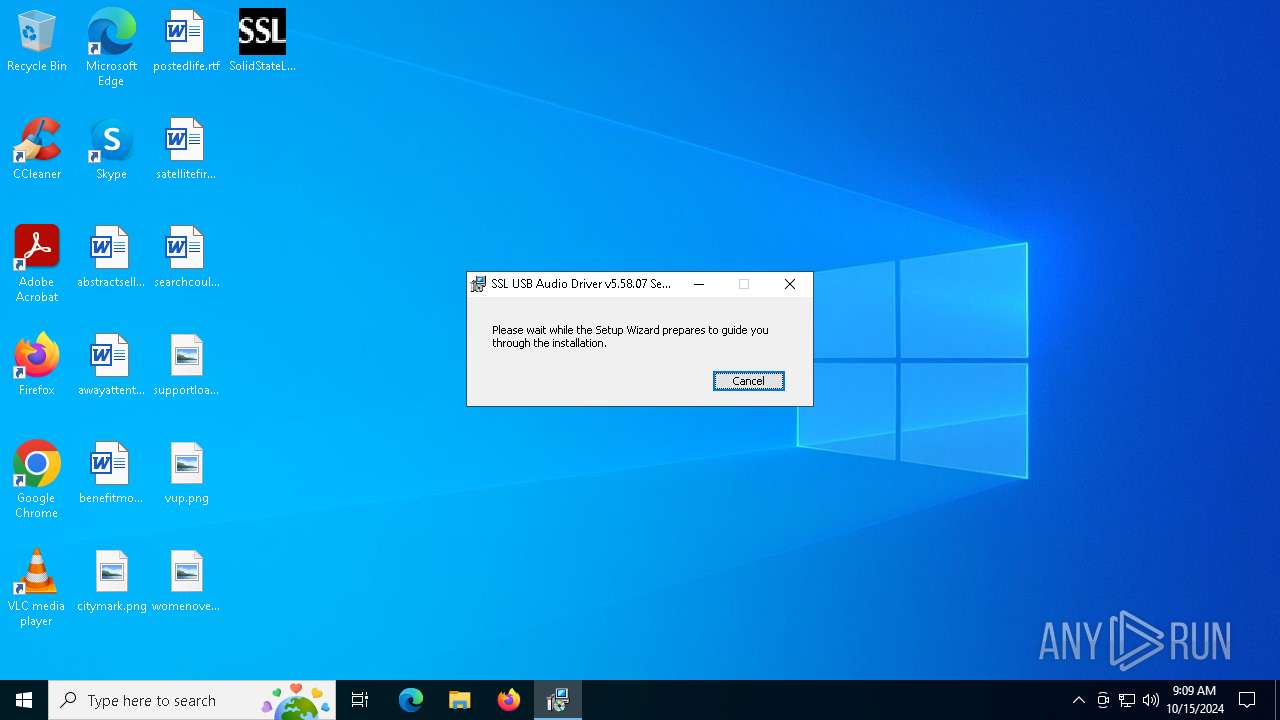
| Analysis date: | October 15, 2024, 09:09:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 073F1C71E85AFC7D88A4B1E4938BC0EC |
| SHA1: | 57AA286A86ADF78D9392E5084EF06A8378CE6D0E |
| SHA256: | 6AEC17E0DCC507282AC93330CD4EC99954811F11EFAF5CE25BC8EDDFC6B30FFA |
| SSDEEP: | 98304:IU25InAqVCMh0Jg1vBIhRg4A009SwEMLY80ABqD+NY9+zzBSEZFx3ZSYH+6/Bp15:DVCfn8KfG7PC0 |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- tlsetupfx.exe (PID: 1084)
- tlsetupfx.exe (PID: 1332)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6316)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 1168)
- msiexec.exe (PID: 3836)
- drvinst.exe (PID: 6456)
- tlsetupfx.exe (PID: 1084)
- drvinst.exe (PID: 5956)
Executable content was dropped or overwritten
- tlsetupfx.exe (PID: 1084)
- drvinst.exe (PID: 6456)
- drvinst.exe (PID: 5956)
INFO
Create files in a temporary directory
- msiexec.exe (PID: 5508)
- SolidStateLogic_UsbAudio_v5.58.07_2023-09-12_setup.exe (PID: 6572)
- msiexec.exe (PID: 4508)
- tlsetupfx.exe (PID: 4292)
Checks supported languages
- SolidStateLogic_UsbAudio_v5.58.07_2023-09-12_setup.exe (PID: 6572)
- msiexec.exe (PID: 1168)
- msiexec.exe (PID: 4508)
- tlsetupfx.exe (PID: 4292)
- tlsetupfx.exe (PID: 6348)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5508)
Reads the computer name
- SolidStateLogic_UsbAudio_v5.58.07_2023-09-12_setup.exe (PID: 6572)
- msiexec.exe (PID: 4508)
- msiexec.exe (PID: 1168)
Creates files or folders in the user directory
- msiexec.exe (PID: 5508)
Checks proxy server information
- msiexec.exe (PID: 5508)
Application launched itself
- msiexec.exe (PID: 1168)
Reads the software policy settings
- msiexec.exe (PID: 5508)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5508)
- msiexec.exe (PID: 4508)
- msiexec.exe (PID: 3836)
- msiexec.exe (PID: 1168)
Reads Environment values
- tlsetupfx.exe (PID: 4292)
Manages system restore points
- SrTasks.exe (PID: 5240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:27 16:17:12+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 696320 |
| InitializedDataSize: | 230912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7505b |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.58.7.0 |
| ProductVersionNumber: | 5.58.7.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
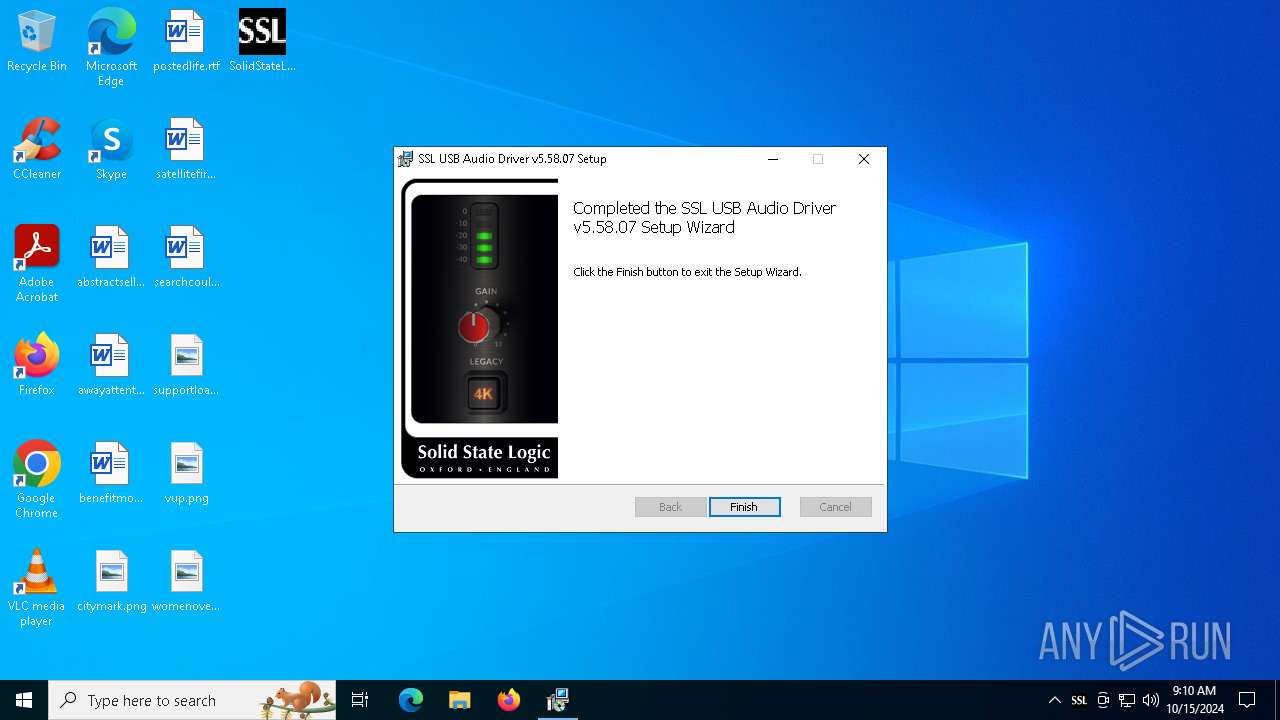
| CompanyName: | Solid State Logic |
| FileDescription: | SolidStateLogic_UsbAudio SFX |
| FileVersion: | 5.58.07 |
| InternalName: | tl-sfxstub.exe |
| LegalCopyright: | © 2009-2023 |
| OriginalFileName: | SolidStateLogic_UsbAudio_v5.58.07_2023-09-12_setup.exe |
| ProductName: | SolidStateLogic_UsbAudio |
| ProductVersion: | 5.58.07 Release |
Total processes
181
Monitored processes
46
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tlsetupfx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | regsvr32 /u /s "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\x64\SSLUSBDriverasio.dll" | C:\Windows\System32\regsvr32.exe | — | tlsetupfx.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe" task LegacyUninstall --cfg "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\x64\tlsetupfx_main.xml" --logfile "C:\Users\admin\AppData\Local\Temp\tlsetupfx.log" --target "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\x64" --result "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\tlsetupfx_result.xml" -v | C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: ToriLogic GmbH & Co. KG Integrity Level: SYSTEM Description: Setup Framework Console Application Exit code: 0 Version: 2.18.0.0 Modules
| |||||||||||||||
| 1008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tlsetupfx.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
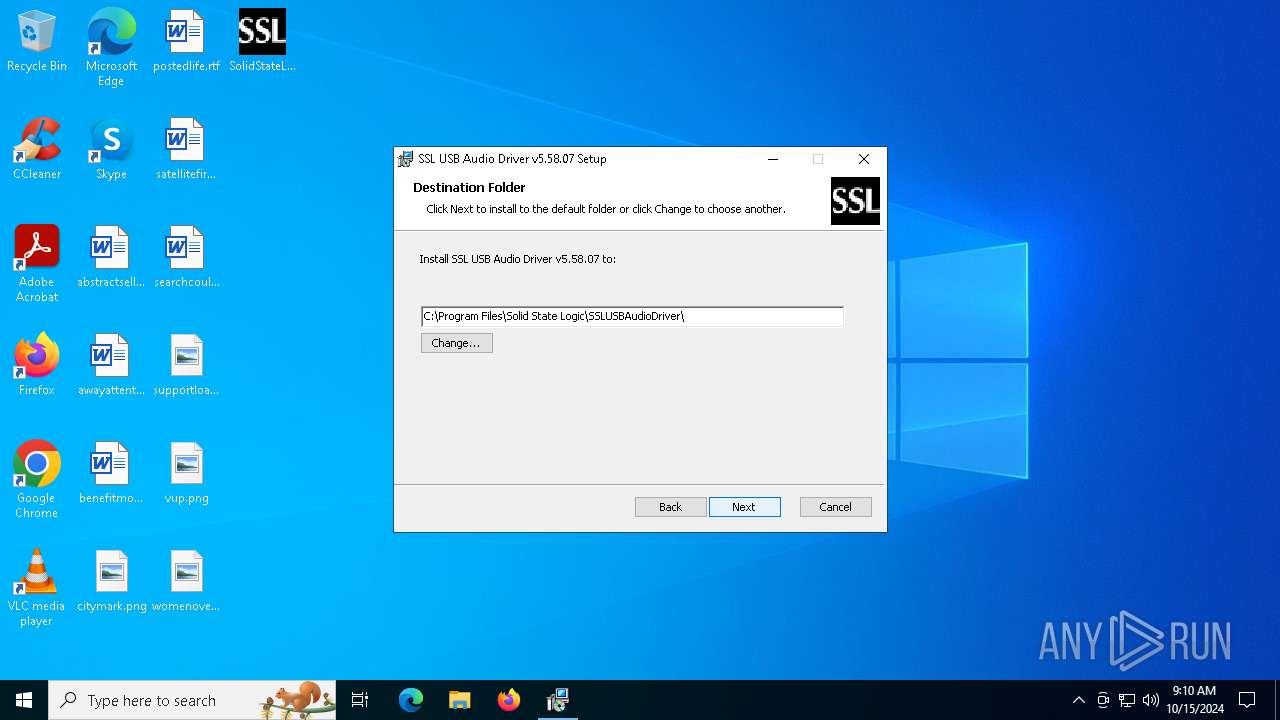
| 1084 | "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe" task Install --cfg "C:\Program Files\Solid State Logic\SSLUSBAudioDriver\x64\tlsetupfx_main.xml" --logfile "C:\Users\admin\AppData\Local\Temp\tlsetupfx.log" --target "C:\Program Files\Solid State Logic\SSLUSBAudioDriver\x64" --result "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\tlsetupfx_result.xml" -v | C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: ToriLogic GmbH & Co. KG Integrity Level: SYSTEM Description: Setup Framework Console Application Exit code: 0 Version: 2.18.0.0 Modules
| |||||||||||||||
| 1168 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe" task PrepareInstall --cfg "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\x64\tlsetupfx_main.xml" --logfile "C:\Users\admin\AppData\Local\Temp\tlsetupfx.log" --target "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\x64" --result "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\tlsetupfx_result.xml" -v | C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: ToriLogic GmbH & Co. KG Integrity Level: SYSTEM Description: Setup Framework Console Application Exit code: 0 Version: 2.18.0.0 Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe" task PostInstall --cfg "C:\Program Files\Solid State Logic\SSLUSBAudioDriver\x64\tlsetupfx_main.xml" --logfile "C:\Users\admin\AppData\Local\Temp\tlsetupfx.log" --target "C:\Program Files\Solid State Logic\SSLUSBAudioDriver\x64" --result "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\tlsetupfx_result.xml" -v | C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe | — | msiexec.exe | |||||||||||
User: admin Company: ToriLogic GmbH & Co. KG Integrity Level: MEDIUM Description: Setup Framework Console Application Exit code: 0 Version: 2.18.0.0 Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe" task IsCurrentSystemSupported --cfg "C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\x64\tlsetupfx_main.xml" --logfile "C:\Users\admin\AppData\Local\Temp\tlsetupfx.log" -v | C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe | — | msiexec.exe | |||||||||||
User: admin Company: ToriLogic GmbH & Co. KG Integrity Level: MEDIUM Description: Setup Framework Console Application Exit code: 0 Version: 2.18.0.0 Modules
| |||||||||||||||
Total events
17 712
Read events
17 338
Write events
357
Delete events
17
Modification events
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000EBFEC809E21EDB0190040000100A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000EBFEC809E21EDB0190040000100A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000005BD5FF09E21EDB0190040000100A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000005BD5FF09E21EDB0190040000100A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000003E39020AE21EDB0190040000100A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000000425070AE21EDB0190040000100A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000FD0C770AE21EDB0190040000100A0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B970790AE21EDB0190040000240E0000E8030000010000000000000000000000C5A458F43C371543AE417824578FBCF900000000000000000000000000000000 | |||
| (PID) Process: | (6316) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000006EC820AE21EDB01AC180000DC1A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
68
Suspicious files
556
Text files
18
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6572 | SolidStateLogic_UsbAudio_v5.58.07_2023-09-12_setup.exe | C:\Users\admin\AppData\Local\Temp\{FFF31EBB-1615-44B0-A8A3-277A85F3CF5E}\x64\SolidStateLogic_UsbAudio_v5.58.07_2023-09-12.msi | — | |
MD5:— | SHA256:— | |||
| 6572 | SolidStateLogic_UsbAudio_v5.58.07_2023-09-12_setup.exe | C:\Users\admin\AppData\Local\Temp\{FFF31EBB-1615-44B0-A8A3-277A85F3CF5E}\x86\SolidStateLogic_UsbAudio_v5.58.07_2023-09-12.msi | — | |
MD5:— | SHA256:— | |||
| 6572 | SolidStateLogic_UsbAudio_v5.58.07_2023-09-12_setup.exe | C:\Users\admin\AppData\Local\Temp\{FFF31EBB-1615-44B0-A8A3-277A85F3CF5E}\x64\de-DE.mst | binary | |
MD5:124DE807F55420AE649B41D2F98B0DA5 | SHA256:F78C86A660C409241CB337ED8AA26692465E7C4F99B845A958E042B236286C60 | |||
| 5508 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B039FEA45CB4CC4BBACFC013C7C55604_50385F8EB1F713E33924A830D7A2A41C | der | |
MD5:DE762C293E77889C50ADCEE4E000FE4E | SHA256:DDA577F61A4E5771964B5DFF53C81AB57093CDF945B59C094007AD4F37323009 | |||
| 5508 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_50385F8EB1F713E33924A830D7A2A41C | binary | |
MD5:63BFB255E3AA6DF810F58E4B9567A228 | SHA256:251F668EE5AEF4A625F9635A2100257050C1798D509F3E281202BF868D4AB6F5 | |||
| 4508 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\tlsetupfx.exe | executable | |
MD5:D23484A26014A99AE5C85FF0F29E2D2C | SHA256:6F3DAB21265DF1BFE9F7B959BEB450ED1AD59CED14B995E898DCCD528A78501C | |||
| 4508 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\x64\tlsetupfx_main.xml | xml | |
MD5:B477937E40F1ABB578AB09A7381D705F | SHA256:3FEEE9AB6C98181B5DC26B0A51660536809C1DFE6709586016FD446E482E0F7A | |||
| 5508 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIBFC2.tmp | executable | |
MD5:52E30BF764B93020F51AA3E8B069C56B | SHA256:AC10FDB3772716AC8872B4FED26E13FDEF4E882ED4B56BCF940FFC23B719A8EB | |||
| 4508 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\x64\tlsetupfx_apps.xml | xml | |
MD5:90B357AD5ABB6B407054831FC1DD6B6F | SHA256:A83FCF1378227D07FEEAA5411C4599DD3B5C916A5FF9617BA04B4B6F74E30DBB | |||
| 4508 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{D3A28E22-4436-47E0-8A8B-EBB22A66260D}\pckA4Womcjf033\x64\tlsetupfx_drv.xml | xml | |
MD5:B8A5AE4F5B173C66301AE179FF265521 | SHA256:F242EEF0175E7BE42662D9960DD0F6B045BF87A3083104B55C42B1496D425539 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
62
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5508 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGEJFcIpBz28BuO60qVQ%3D | unknown | — | — | whitelisted |
5508 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
5508 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDHmwirAvTdPZL1plug%3D%3D | unknown | — | — | whitelisted |
2364 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6340 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
948 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
948 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.32.238.112:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 92.123.104.27:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5508 | msiexec.exe | 104.18.21.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |