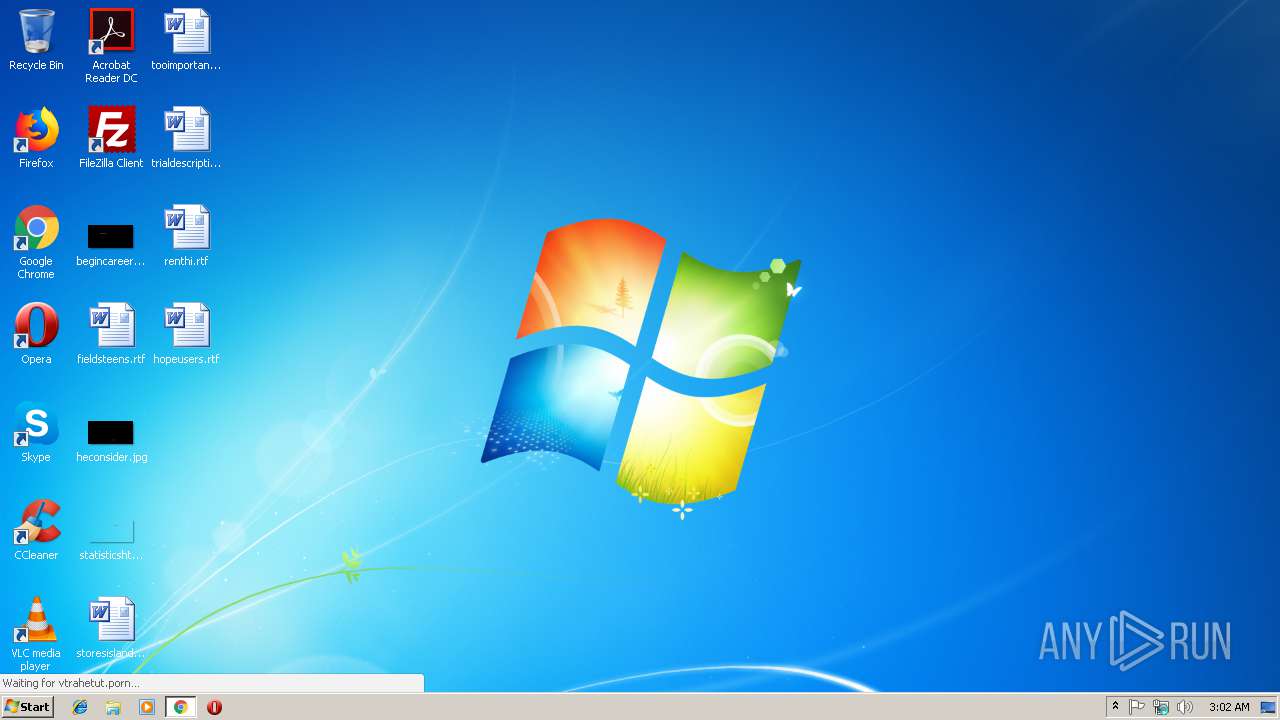
| URL: | http://vtrahetut.porn/2018/01/12/mayk-trahaet-luchshuyu-podrugu-svoey-zheny-i-zalivaet-ee-siski-spermoy.html |
| Full analysis: | https://app.any.run/tasks/42365a9a-7455-4dcf-9196-c291aeda53dc |
| Verdict: | No threats detected |
| Analysis date: | February 16, 2019, 03:01:51 |
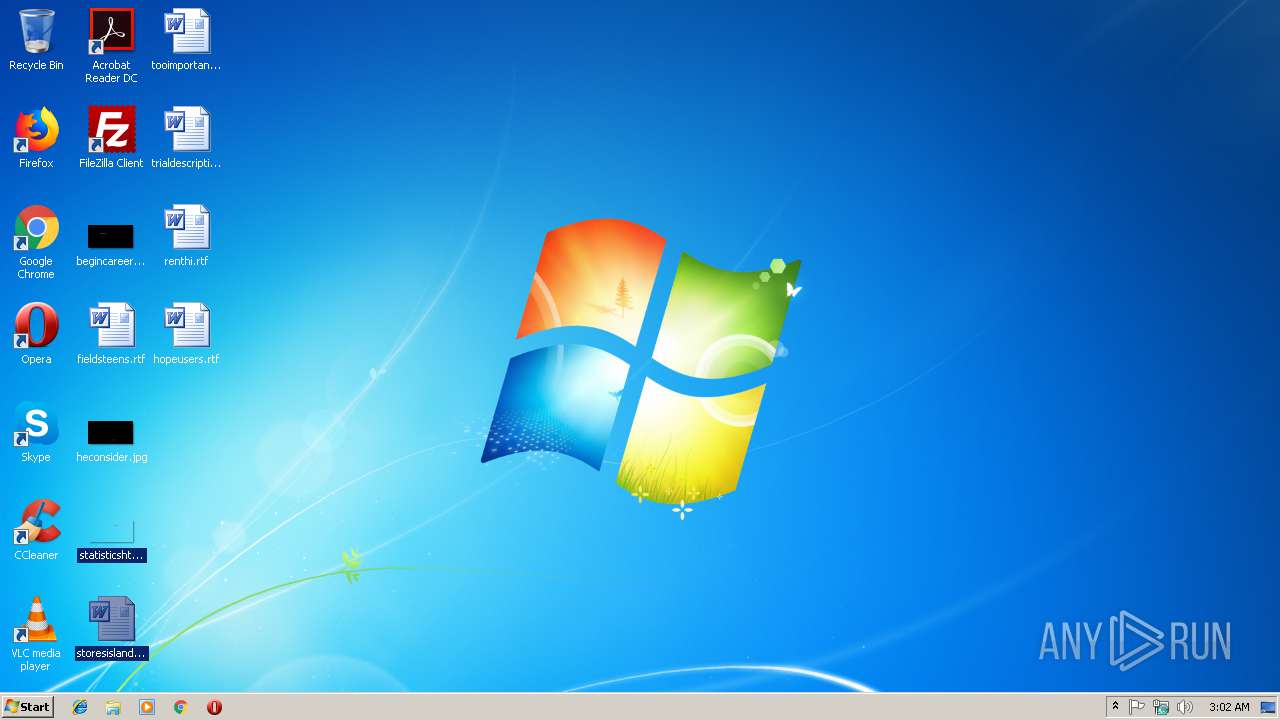
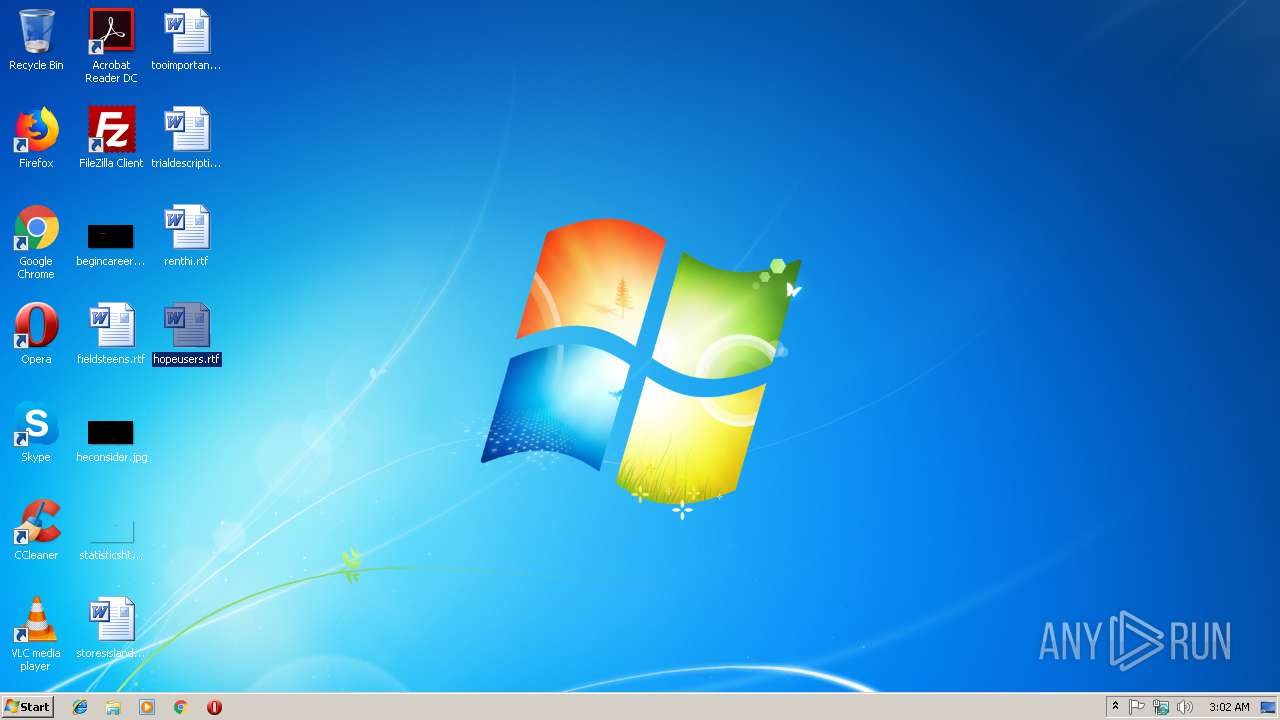
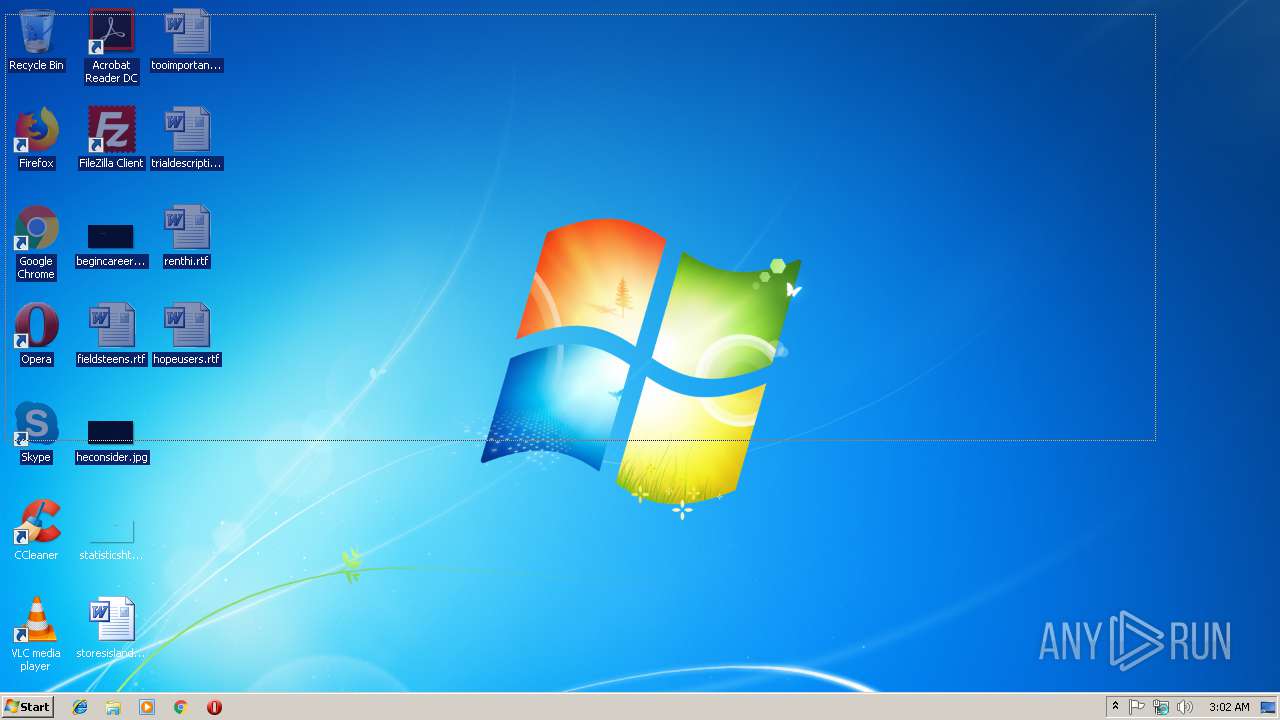
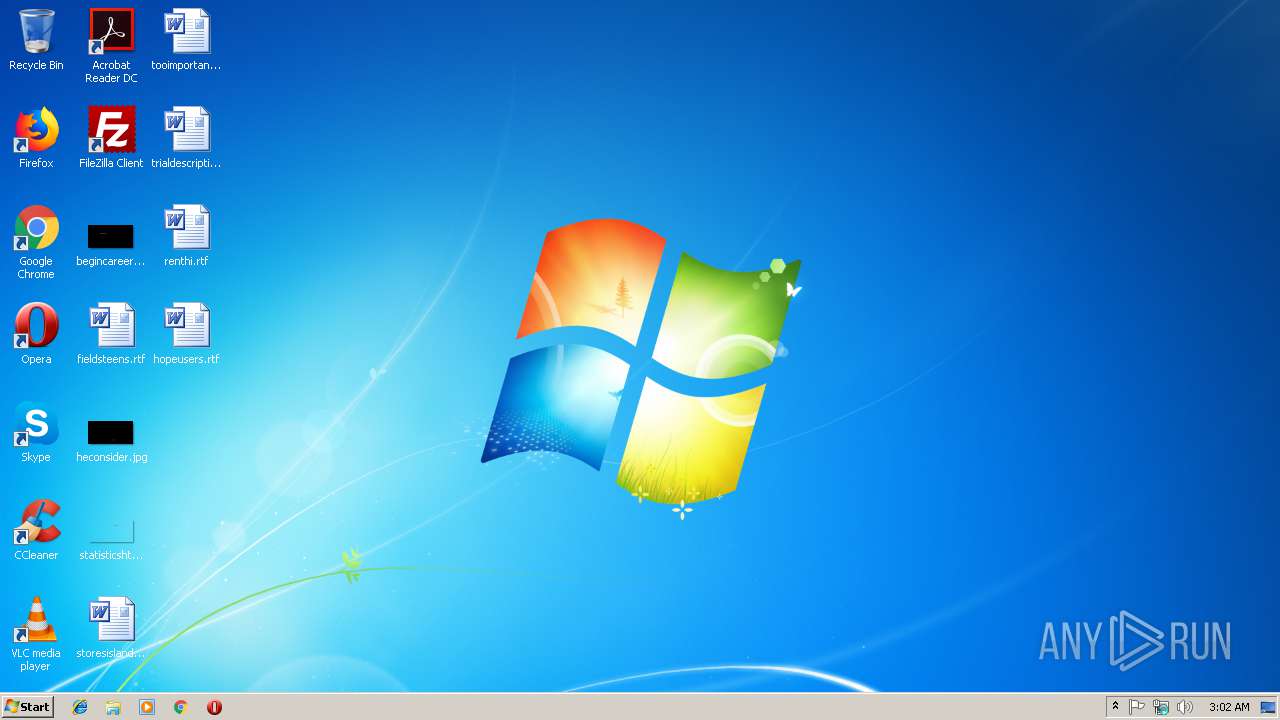
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FDF6A6412D4AEF372A0DE234F562EF2D |
| SHA1: | BF72FAA54F77E0D36F09A8BF5AC53C4D8A0CF7D6 |
| SHA256: | 6AE677AE915ED60345E75401623CBDF2C5015D2FCC5613C70AD20ABBD79FA258 |
| SSDEEP: | 3:N1KIxJ2bud7KUaIhOE0DNQcQxQ/TVmir/VyIKmIJn:CIxJ2G7ODEQ/TVmirdyR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
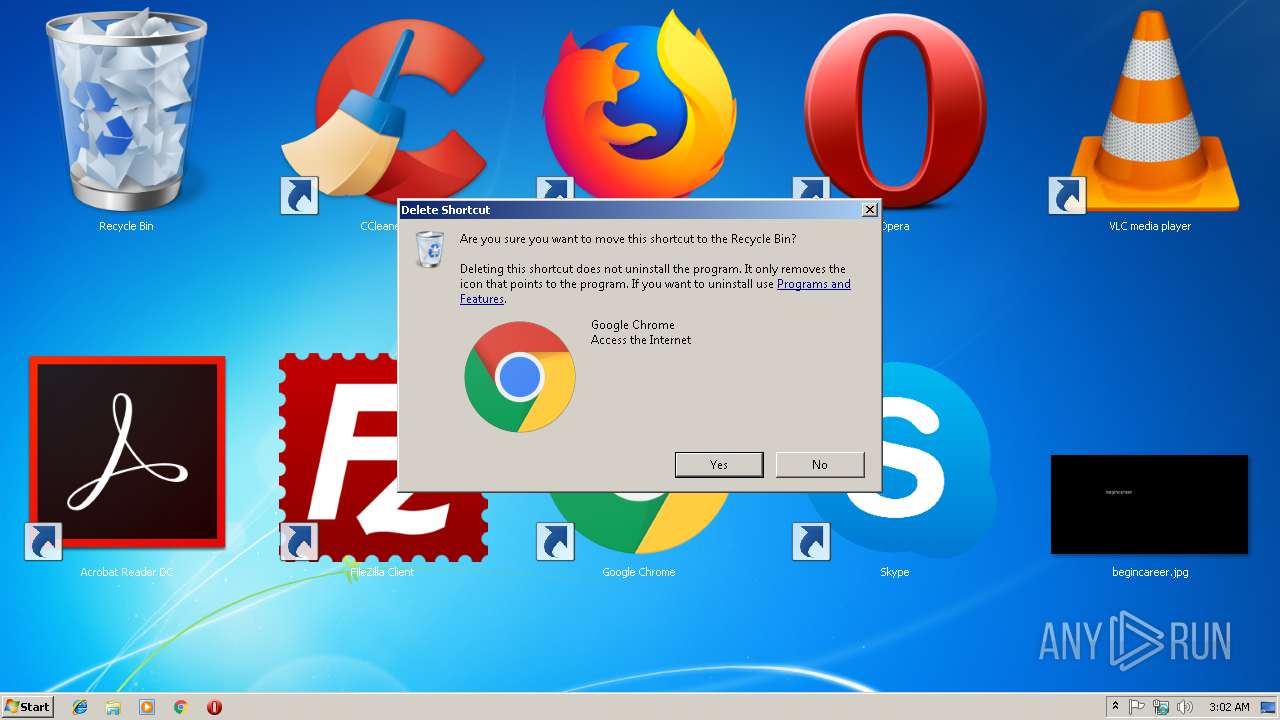
Application launched itself
- chrome.exe (PID: 2964)
Reads settings of System Certificates
- chrome.exe (PID: 2964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
7
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2968 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=852,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AFA405AB13833AF90D6D20D9B4FE3297 --mojo-platform-channel-handle=3868 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=852,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --service-pipe-token=0CF2AC52FD55C275D6739839AA32877D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0CF2AC52FD55C275D6739839AA32877D --renderer-client-id=4 --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://vtrahetut.porn/2018/01/12/mayk-trahaet-luchshuyu-podrugu-svoey-zheny-i-zalivaet-ee-siski-spermoy.html | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=852,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --service-pipe-token=51FCC4DE1B02732CF48AF41457A4022A --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=51FCC4DE1B02732CF48AF41457A4022A --renderer-client-id=3 --mojo-platform-channel-handle=2072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f4300b0,0x6f4300c0,0x6f4300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=852,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=27FA7F2C489BAE057CB7508B5C678935 --mojo-platform-channel-handle=972 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
132
Read events
93
Write events
36
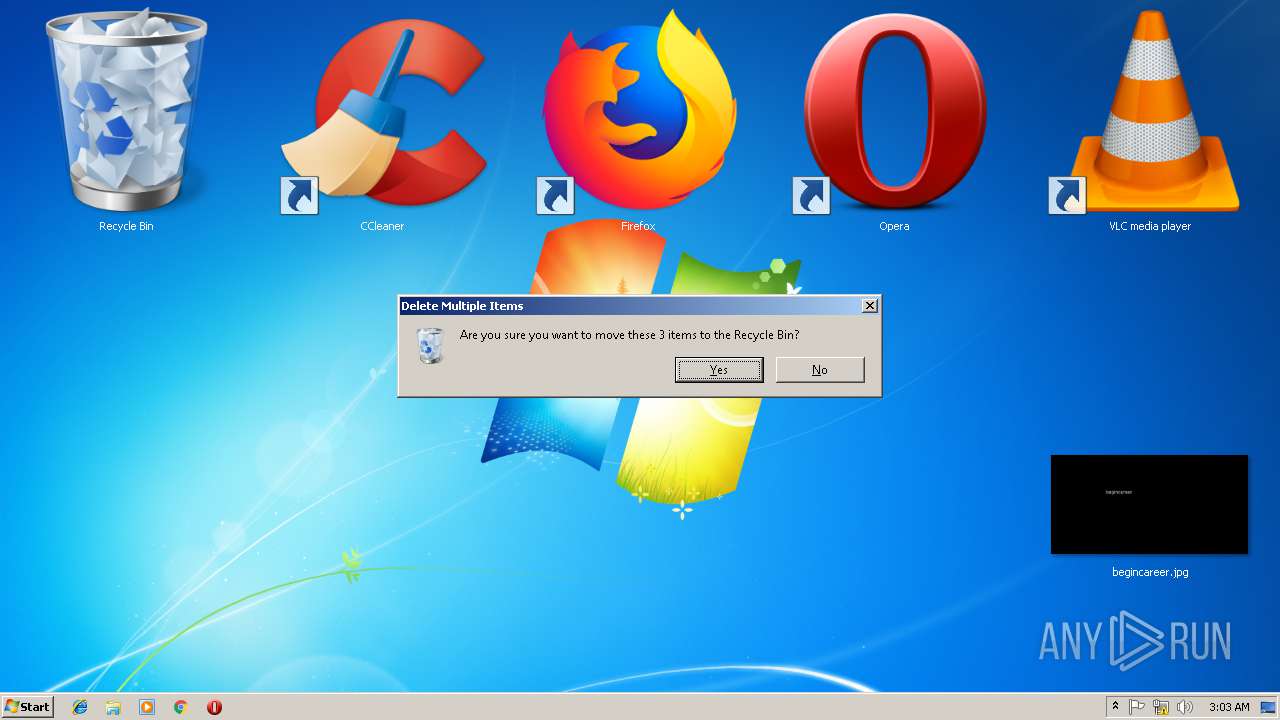
Delete events
3
Modification events
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2964-13194759726887000 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2964-13194759726887000 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
35
Text files
65
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a20503db-345c-43d7-89ca-d3d2c1acdaa2.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e56c3e9b-7988-4c41-bcf8-87f68dc1beae.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF246cc4.TMP | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF246ce3.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
35
DNS requests
14
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2964 | chrome.exe | GET | — | 37.48.125.224:80 | http://vtrpic.com/2018-09/1536101543_2111.jpg | NL | — | — | whitelisted |
2964 | chrome.exe | GET | 200 | 37.48.125.224:80 | http://vtrahetut.porn/img/logo.png?v=1 | NL | image | 5.87 Kb | whitelisted |
2964 | chrome.exe | GET | 200 | 37.48.125.224:80 | http://vtrahetut.porn/player/jwplayerl.js?v=56 | NL | text | 62.2 Kb | whitelisted |
2964 | chrome.exe | GET | 404 | 37.48.125.224:80 | http://vtrahetut.porn/2018/01/12/mayk-trahaet-luchshuyu-podrugu-svoey-zheny-i-zalivaet-ee-siski-spermoy.html | NL | html | 217 b | whitelisted |
2964 | chrome.exe | GET | 200 | 37.48.125.224:80 | http://vtrahetut.porn/2018/01/12/mayk-trahaet-luchshuyu-podrugu-svoey-zheny-i-zalivaet-ee-siski-spermoy.html | NL | html | 7.96 Kb | whitelisted |
2964 | chrome.exe | GET | 200 | 37.48.125.224:80 | http://vtrahetut.porn/style/main.css?v=84 | NL | text | 6.17 Kb | whitelisted |
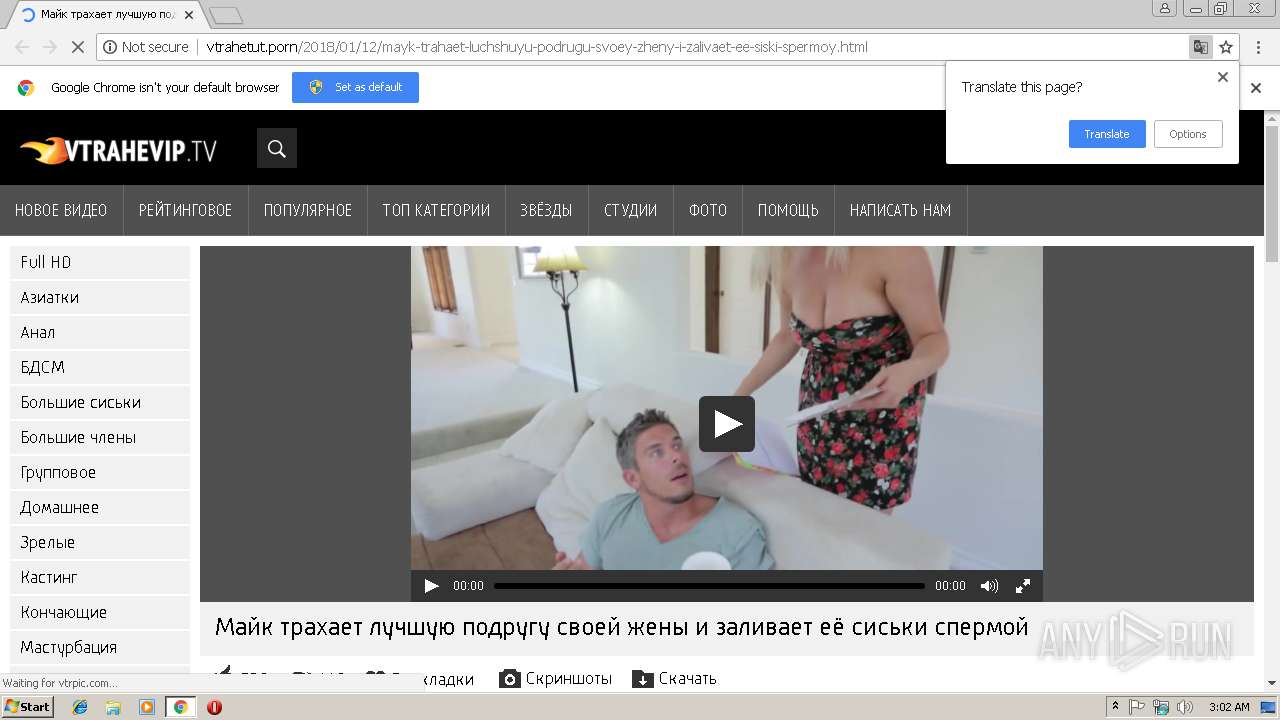
2964 | chrome.exe | GET | 200 | 88.208.25.25:80 | http://i.vtrpic.com/contents/videos_screenshots/14000/14067/240x180/3.jpg | NL | image | 11.4 Kb | unknown |
2964 | chrome.exe | GET | 200 | 37.48.125.224:80 | http://vtrahetut.porn/js/lt.js?v=105 | NL | text | 1.49 Kb | whitelisted |
2964 | chrome.exe | GET | 200 | 37.48.125.224:80 | http://vtrahetut.porn/js/scrsl.js?v=68 | NL | html | 2.72 Kb | whitelisted |
2964 | chrome.exe | GET | 200 | 88.208.25.25:80 | http://i.vtrpic.com/contents/videos_screenshots/14000/14067/240x180/4.jpg | NL | image | 11.5 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | chrome.exe | 37.48.125.224:80 | vtrahetut.porn | LeaseWeb Netherlands B.V. | NL | unknown |
2964 | chrome.exe | 93.184.221.48:80 | ssl.p.jwpcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2964 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 88.208.25.25:80 | i.vtrpic.com | DataWeb Global Group B.V. | NL | unknown |
2964 | chrome.exe | 88.212.196.66:80 | counter.yadro.ru | United Network LLC | RU | unknown |
2964 | chrome.exe | 23.111.18.23:80 | mp-c.info | Servers.com, Inc. | NL | unknown |
2964 | chrome.exe | 52.22.196.225:80 | jwpltx.com | Amazon.com, Inc. | US | unknown |
2964 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
vtrahetut.porn |
| whitelisted |
accounts.google.com |
| shared |
i.vtrpic.com |
| unknown |
vtrpic.com |
| unknown |
ssl.p.jwpcdn.com |
| whitelisted |
counter.yadro.ru |
| whitelisted |
www.liveinternet.ru |
| whitelisted |
mp-c.info |
| unknown |
Threats
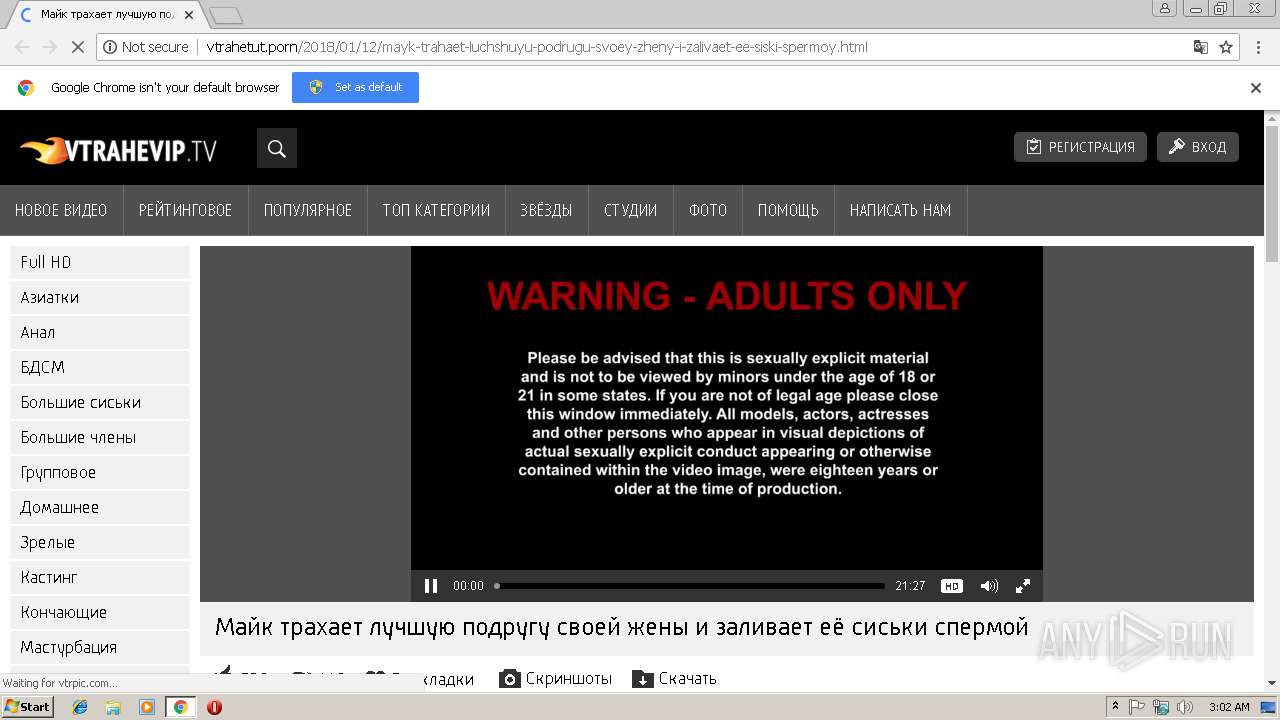
PID | Process | Class | Message |
|---|---|---|---|
2964 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] JS obfuscation (obfuscator.io) |
2964 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Redirection JScript Obfuscated (seen Banload) |