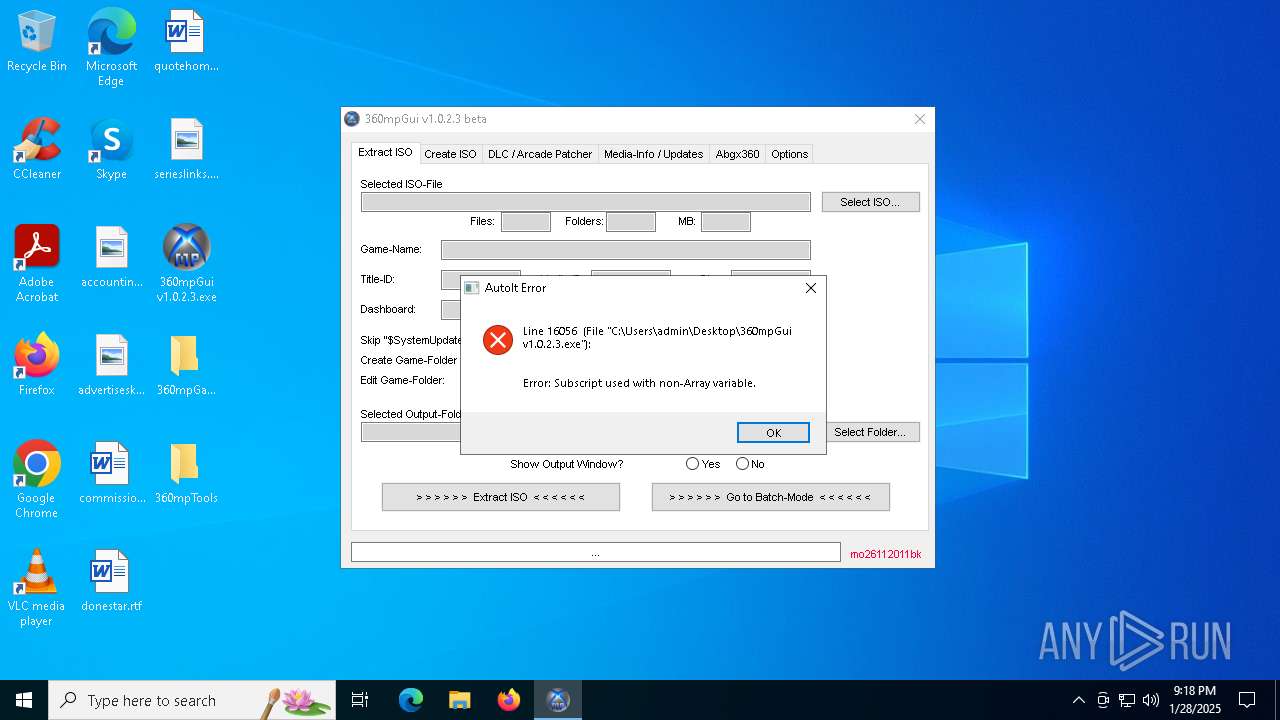
| File name: | 360mpGui v1.0.2.3.exe |
| Full analysis: | https://app.any.run/tasks/d55525e1-f7f7-42c4-953e-112dfbb1bfd1 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2025, 21:18:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 2F7D693C3FB2AAF67AD8FE10469FFBF3 |
| SHA1: | 269C8C72AD388AB4C8665015AC52FD2E5559E4AB |
| SHA256: | 6ACE0AE70EF3B8DB3C327172919D5704EFD4CC58D5E9D633E4CD75754269ABD2 |
| SSDEEP: | 49152:WEVUcjhUJH0b931LvEMX8x7ZR0Dy0hVaV+:WE3jIUb15hMFZR0rCg |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- 360mpGui v1.0.2.3.exe (PID: 5640)
- 360mpGui v1.0.2.3.exe (PID: 6220)
Application launched itself
- 360mpGui v1.0.2.3.exe (PID: 5640)
Executable content was dropped or overwritten
- 360mpGui v1.0.2.3.exe (PID: 6220)
There is functionality for taking screenshot (YARA)
- 360mpGui v1.0.2.3.exe (PID: 6220)
INFO
Reads mouse settings
- 360mpGui v1.0.2.3.exe (PID: 5640)
- 360mpGui v1.0.2.3.exe (PID: 6220)
Process checks computer location settings
- 360mpGui v1.0.2.3.exe (PID: 5640)
The sample compiled with english language support
- 360mpGui v1.0.2.3.exe (PID: 5640)
Checks supported languages
- 360mpGui v1.0.2.3.exe (PID: 5640)
- 360mpGui v1.0.2.3.exe (PID: 6220)
Reads the computer name
- 360mpGui v1.0.2.3.exe (PID: 5640)
- 360mpGui v1.0.2.3.exe (PID: 6220)
Create files in a temporary directory
- 360mpGui v1.0.2.3.exe (PID: 6220)
The process uses AutoIt
- 360mpGui v1.0.2.3.exe (PID: 6220)
Checks proxy server information
- 360mpGui v1.0.2.3.exe (PID: 6220)
UPX packer has been detected
- 360mpGui v1.0.2.3.exe (PID: 6220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:01:29 21:32:28+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 274432 |
| InitializedDataSize: | 188416 |
| UninitializedDataSize: | 638976 |
| EntryPoint: | 0xdeec0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.2.3 |
| ProductVersionNumber: | 3.3.8.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.2.3 |
| Comments: | 360mpGui |
| FileDescription: | 360mpGui |
| LegalCopyright: | 360mpGui |
Total processes
125
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5640 | "C:\Users\admin\Desktop\360mpGui v1.0.2.3.exe" | C:\Users\admin\Desktop\360mpGui v1.0.2.3.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 360mpGui Exit code: 0 Version: 1.0.2.3 Modules
| |||||||||||||||
| 6220 | "C:\Users\admin\Desktop\360mpGui v1.0.2.3.exe" | C:\Users\admin\Desktop\360mpGui v1.0.2.3.exe | 360mpGui v1.0.2.3.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 360mpGui Exit code: 1 Version: 1.0.2.3 Modules
| |||||||||||||||
Total events
567
Read events
565
Write events
0
Delete events
2
Modification events
| (PID) Process: | (6220) 360mpGui v1.0.2.3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (6220) 360mpGui v1.0.2.3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
Executable files
2
Suspicious files
5
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\AppData\Local\Temp\ovjymoc | text | |
MD5:011F329A4A4FA05657AC4D3432F73085 | SHA256:963C24C25C3607385DF12D79C82EAA26FBA740324E78318A596AC0065A0DD80D | |||
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\AppData\Local\Temp\aut6D92.tmp | binary | |
MD5:13D38A8BC4AA3BABDB168D62C8A04EB4 | SHA256:F074D5569BBBC731F33D43CD7F172DEBFBE3688A9E2261569BC4B52FC1E2AA55 | |||
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\AppData\Local\Temp\~DF6CFF1A77072E6E75.TMP | binary | |
MD5:39C43E3D1C8A1B59FC3EDC106D79C643 | SHA256:19B04507515A81C27F2110EF490D28BAA8271C642E81149F1F96EB364B6C053E | |||
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\AppData\Local\Temp\360mpGui\360mpGui.ico | image | |
MD5:91B29221D10EFD2B557238E55E12DF3A | SHA256:95AF49E7A45AB8E478838AFE1E31E6BA8DD653E7EC9C41A13CBF7665FFAAF57D | |||
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\Desktop\360mpTools\abgx360.exe | executable | |
MD5:8517D987B5055F3D5CCAC49022201406 | SHA256:9C4E43769267EEF915A642B0012FF45BB8A9A352BB8A315828BF0C9EC129347D | |||
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\AppData\Local\Temp\360mpGui\BootLogo.jpg | image | |
MD5:951662223E04D035BD1C1056C4516EDD | SHA256:F7C722BD68277A078AB50E10FB2E99179666821850FBC56673DDBDEB4DBA1C91 | |||
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\AppData\Local\Temp\aut744C.tmp | binary | |
MD5:ACB3C381D01B87390E32E3A135AF65E6 | SHA256:40B2AA6B908CAC91451E2D87A7E34A1057994E7E63C5419A4502CB92215B5DFD | |||
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\AppData\Local\Temp\aut73ED.tmp | binary | |
MD5:7EC9C03A4DE7124E206F1CA41B3CC60D | SHA256:6051D962638DE1961AB534DD440F2A49334B288B9289F373E43922BA3A436FF5 | |||
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\AppData\Local\Temp\aut6EAC.tmp | image | |
MD5:951662223E04D035BD1C1056C4516EDD | SHA256:F7C722BD68277A078AB50E10FB2E99179666821850FBC56673DDBDEB4DBA1C91 | |||
| 6220 | 360mpGui v1.0.2.3.exe | C:\Users\admin\Desktop\360mpTools\exiso.exe | executable | |
MD5:83A50D2131F9ED6F1CF10C61ACDD19D6 | SHA256:293C152CE3C06368E7C16E75EE43A00551570910A90BEFCC633F06CDDB2E72DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
18
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
— | — | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 23.38.73.129:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4160 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.19.80.27:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |