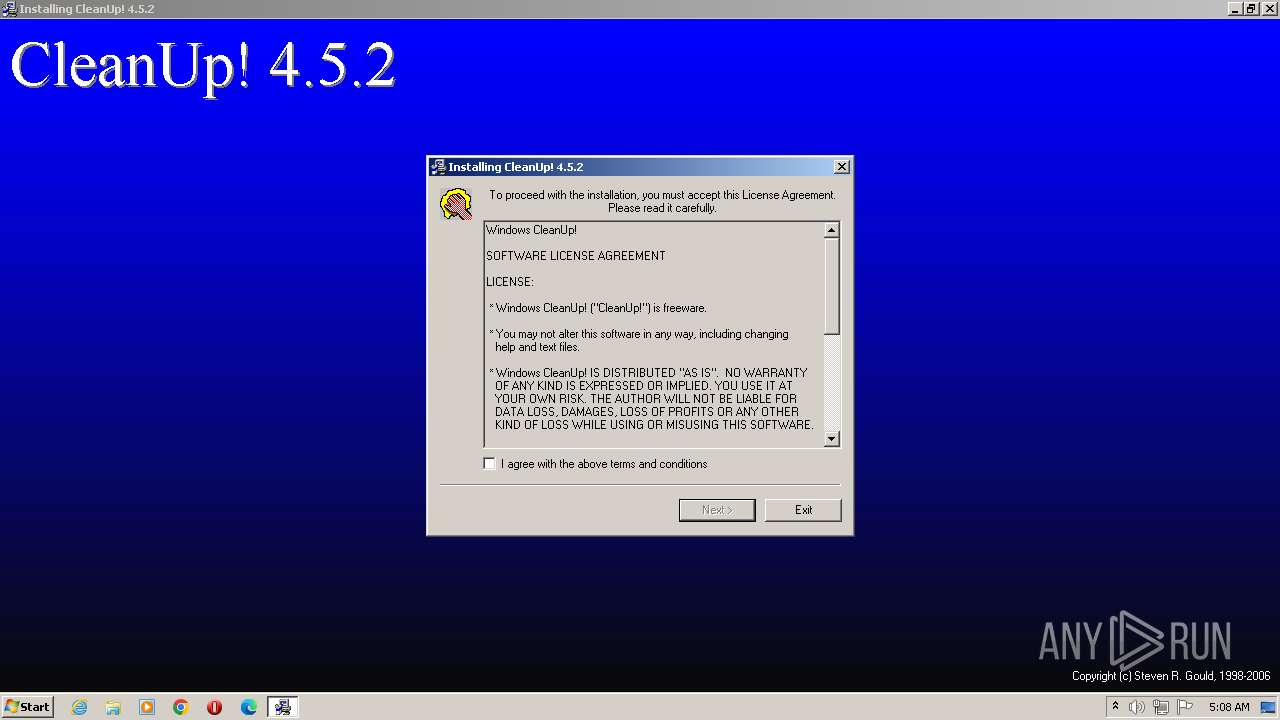
| File name: | CleanUp452.exe |
| Full analysis: | https://app.any.run/tasks/36241e33-a77f-491b-93a4-21b56e4a354c |
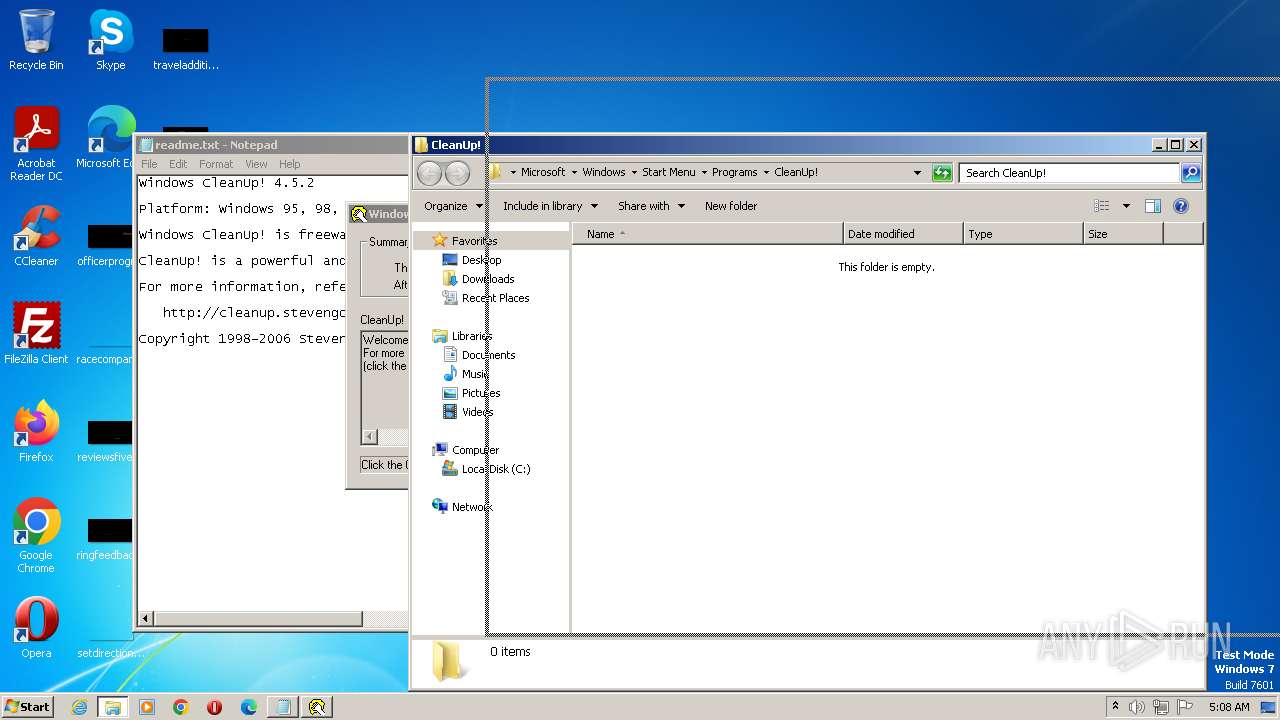
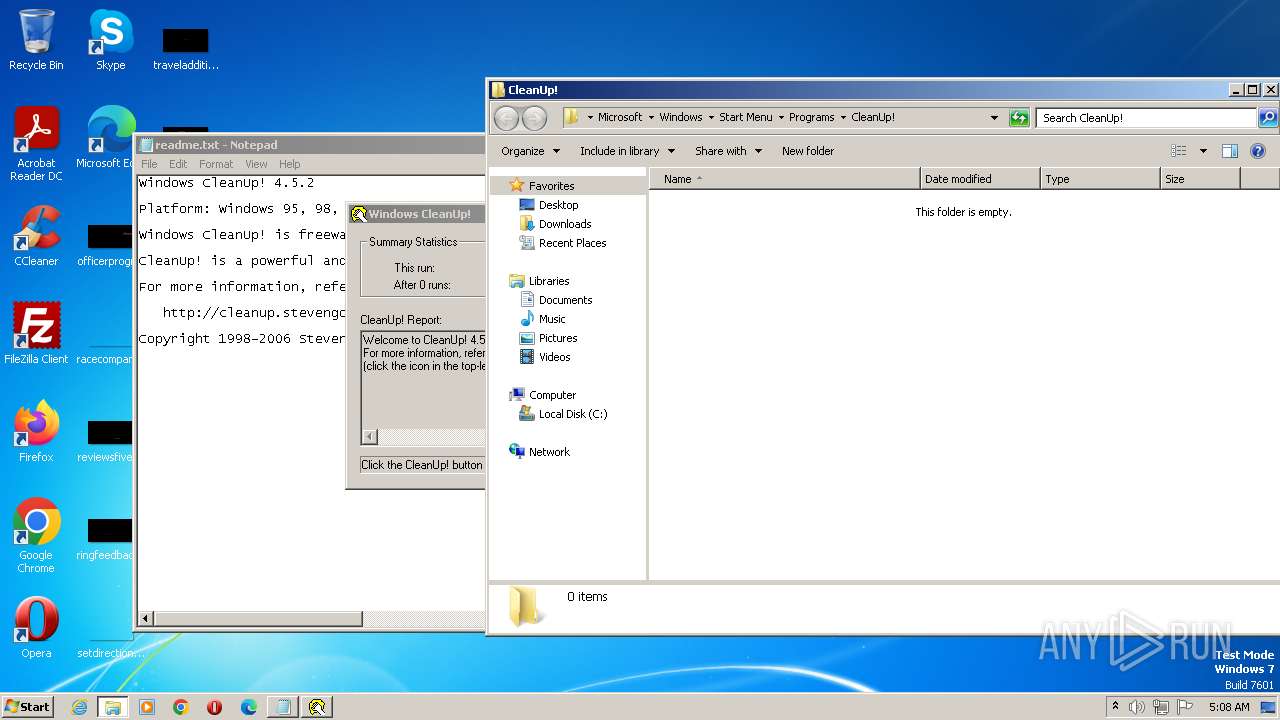
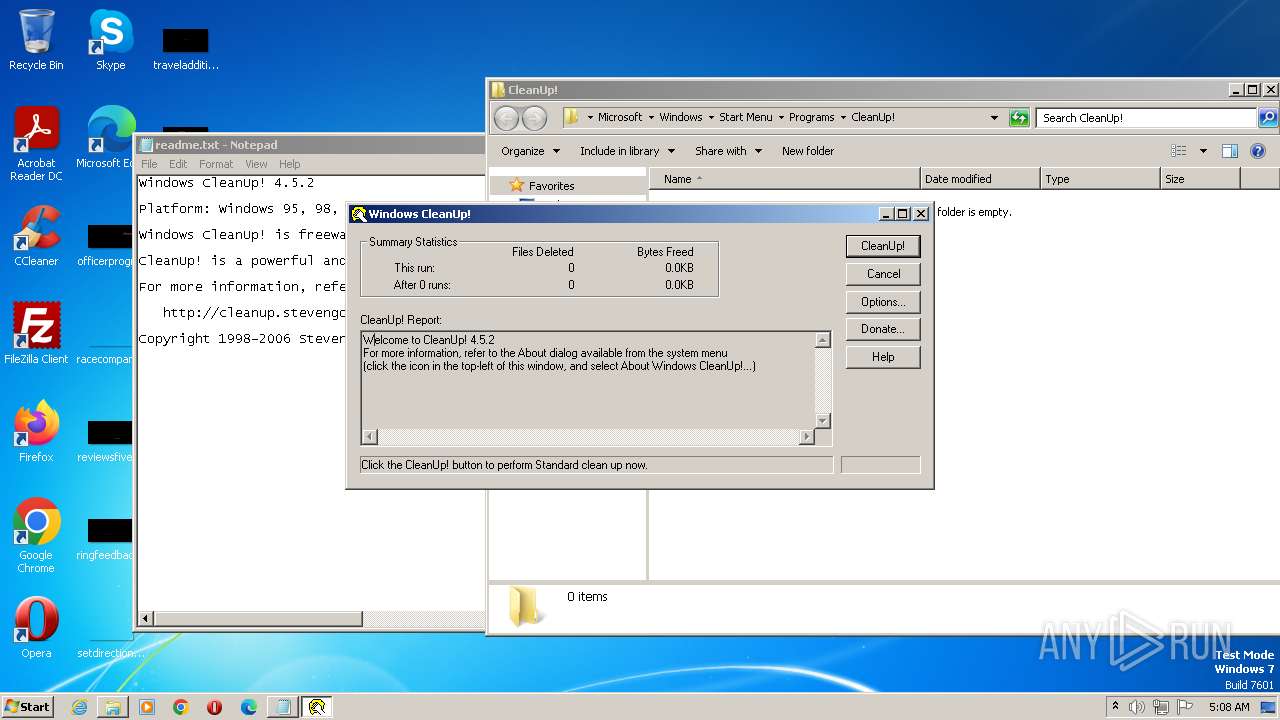
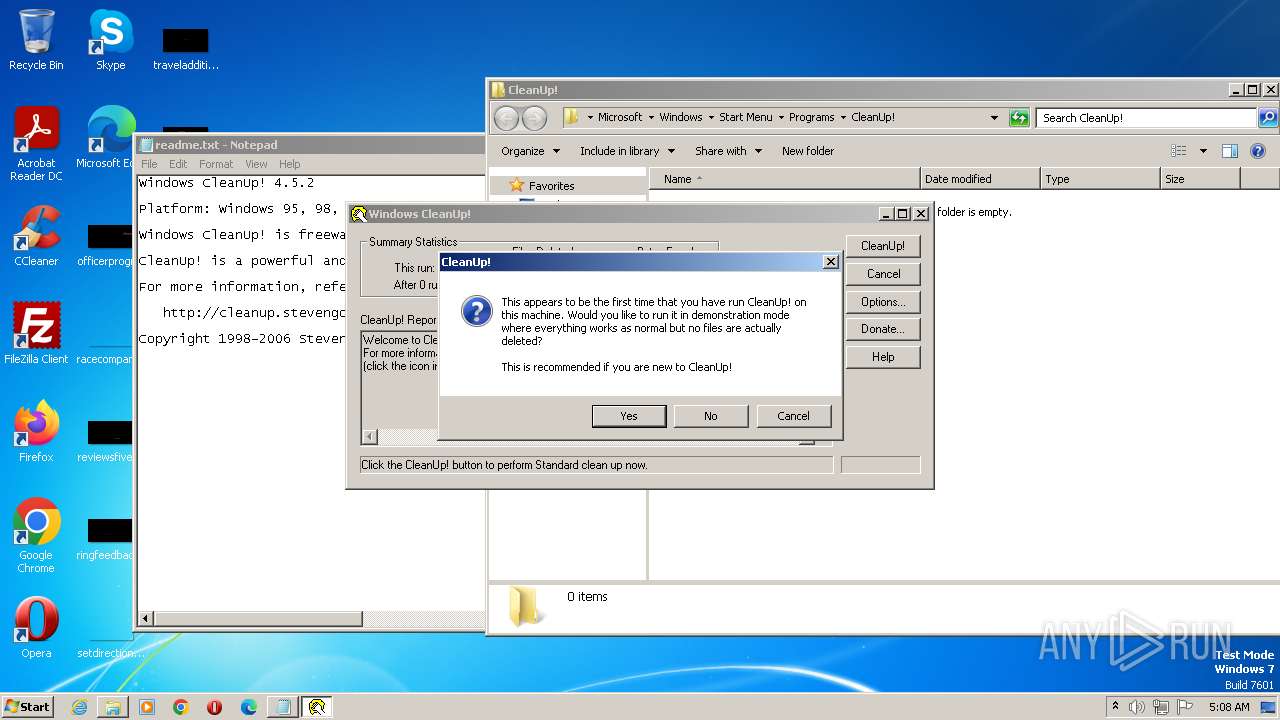
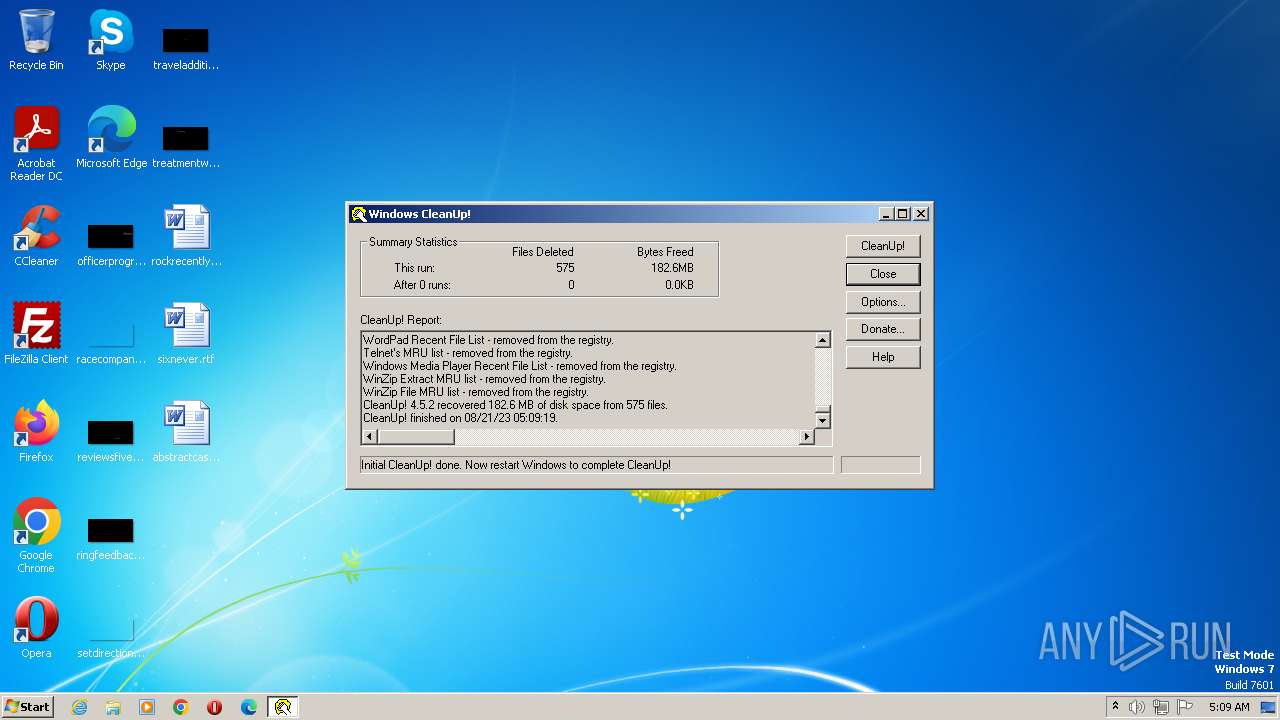
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2023, 04:08:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 362FEB532129FC33A0405786CAB9847D |
| SHA1: | 12A56F13DA5F4B7B8B4390174D780157D08129A9 |
| SHA256: | 6AC7576C0B48DDEE292F85724C7917E11360927FF8E5C5A8D795577A4241C131 |
| SSDEEP: | 6144:IAQItQfxi1R6gkqJGoNkat7RMiuQbuizsGGANKUbczrHA4I9FZot5GltBeZfY3/d:B3t1vNMoS2juUjs9xU4znI9oezMs |
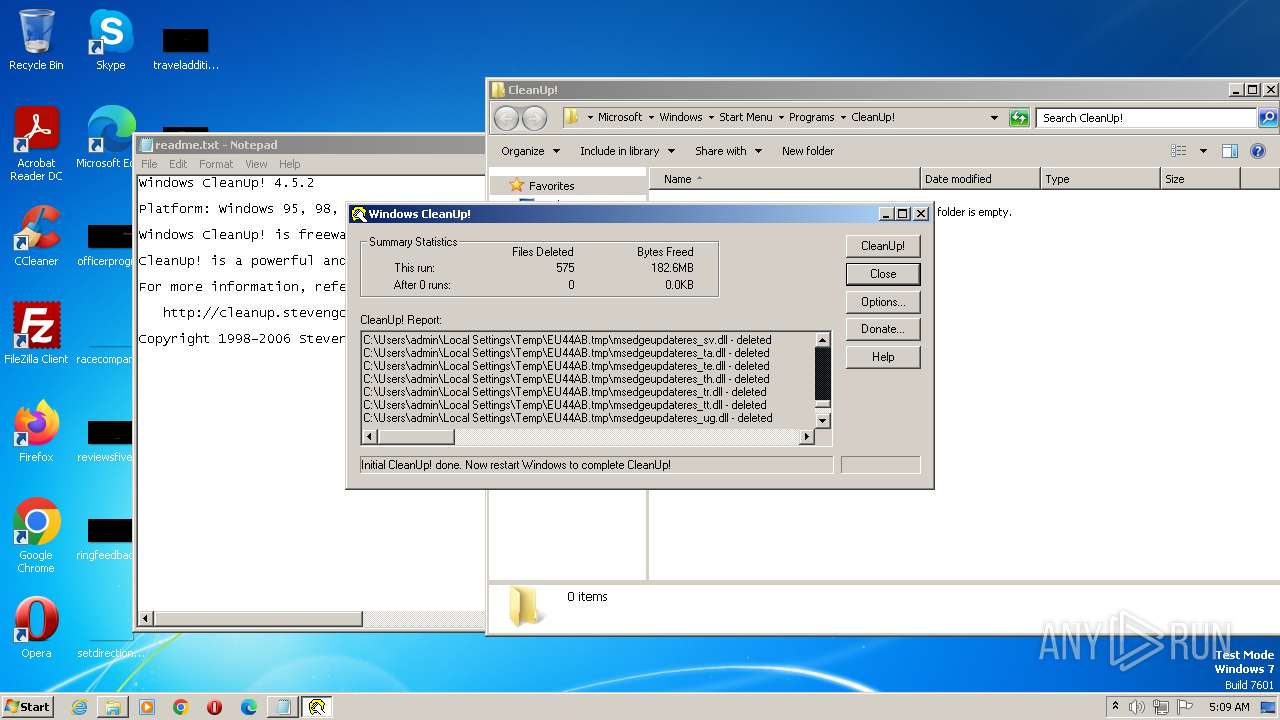
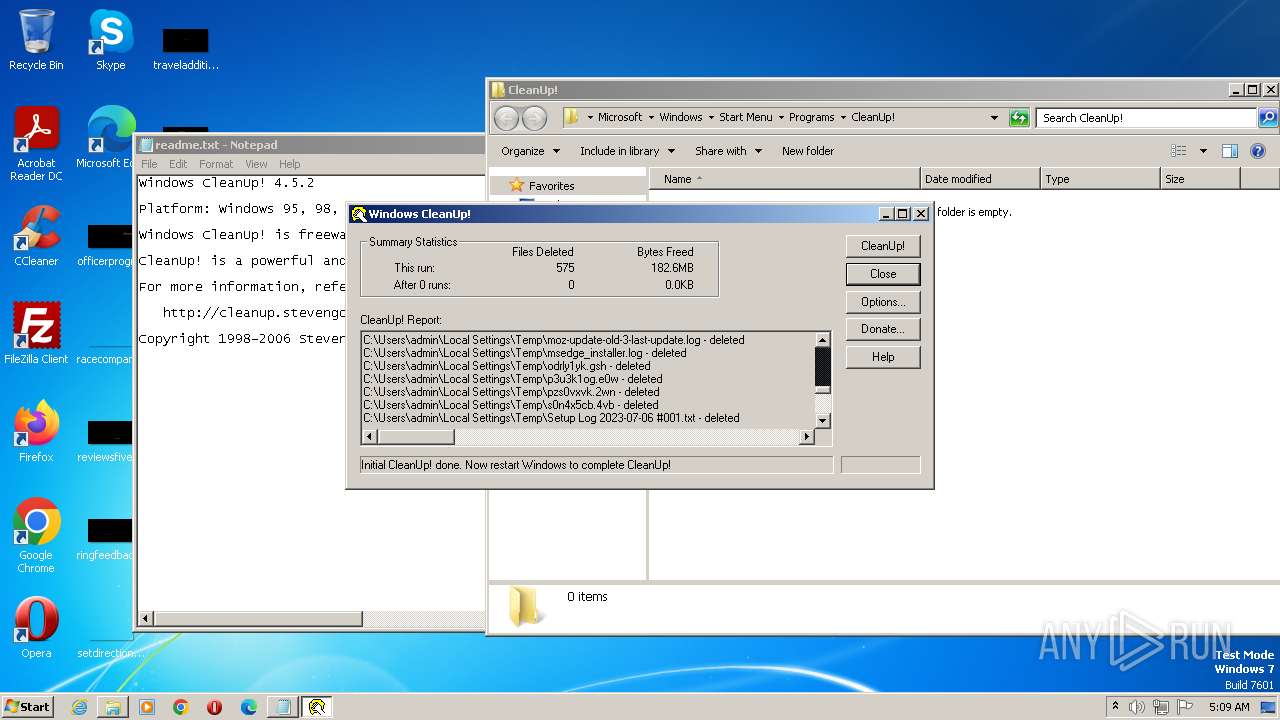
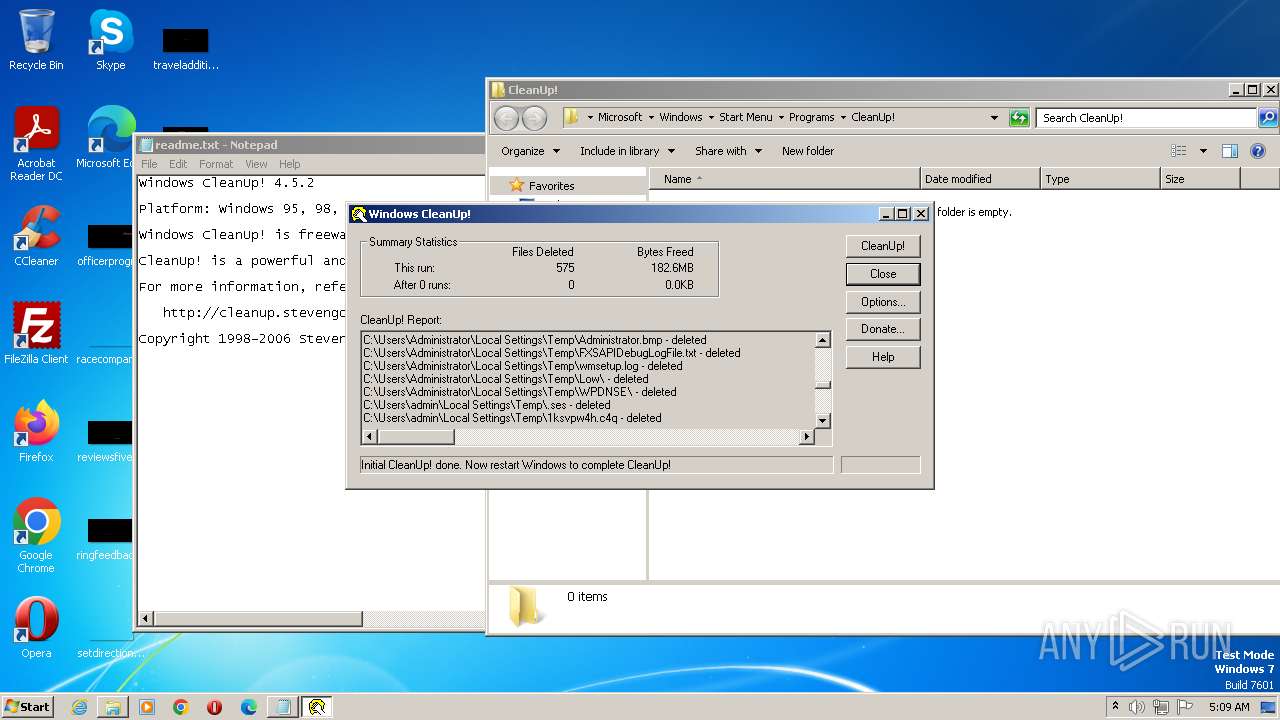
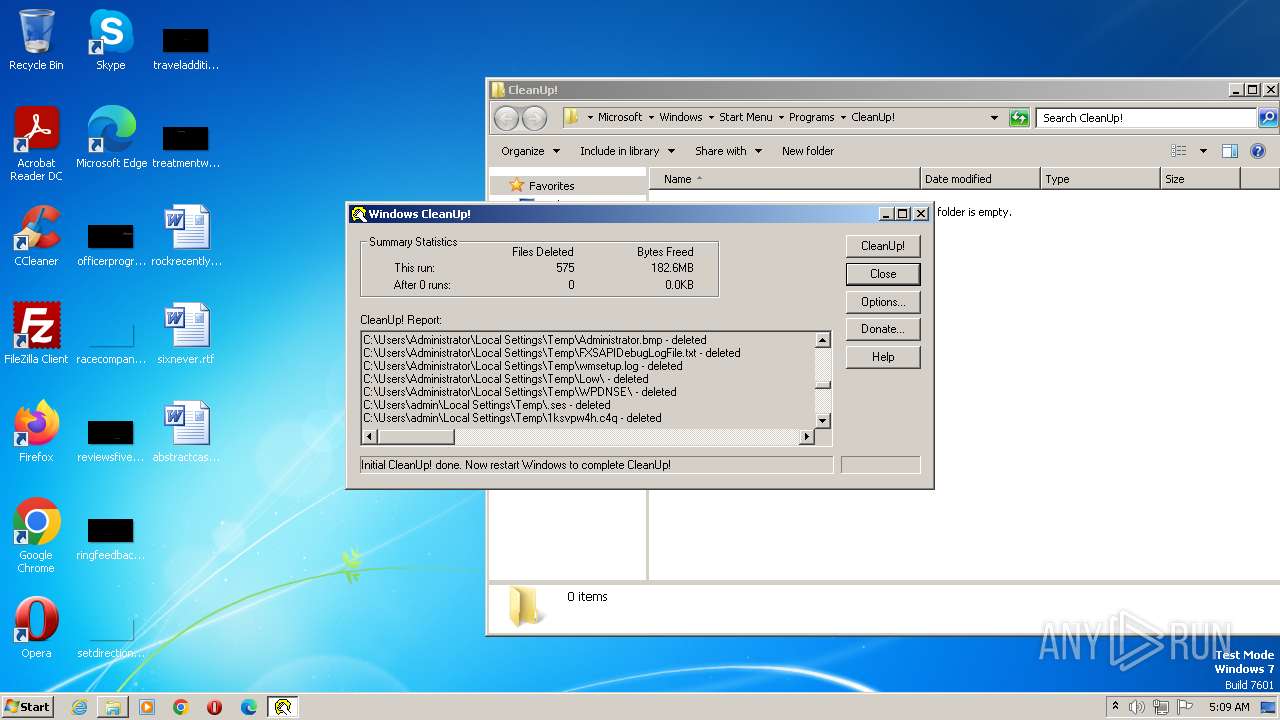
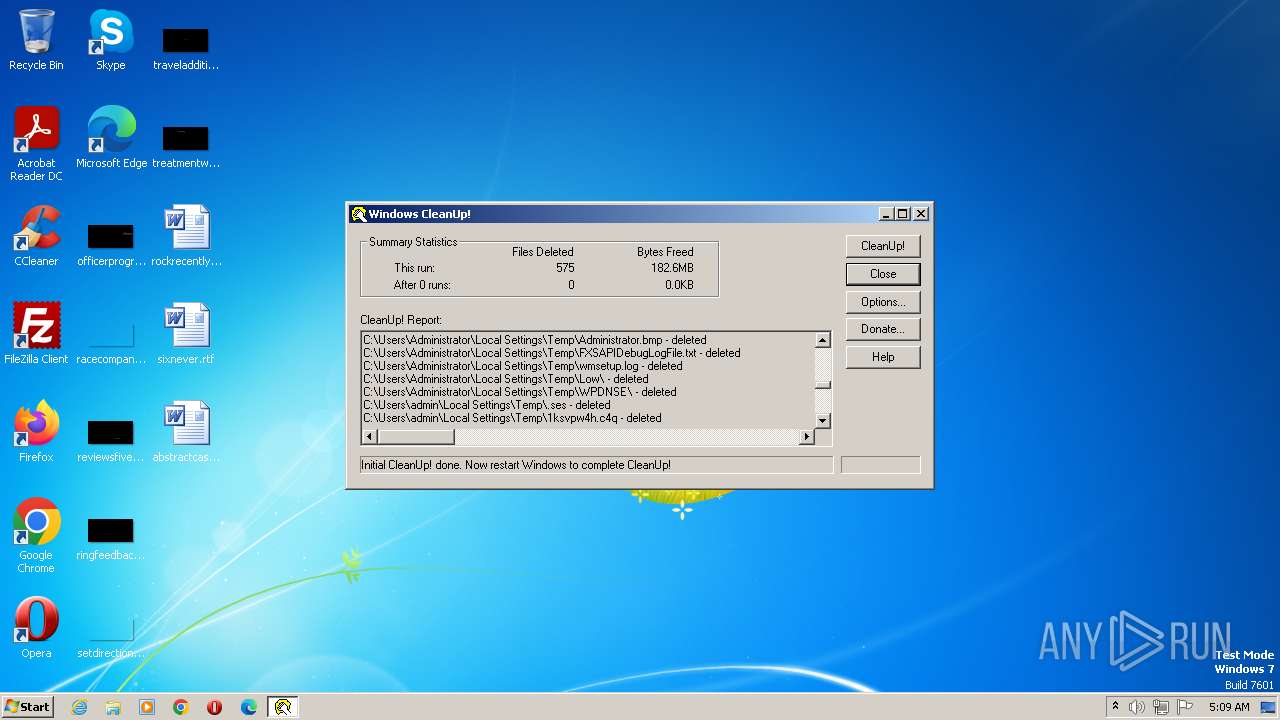
MALICIOUS
Application was dropped or rewritten from another process
- Cleanup.exe (PID: 3048)
Steals credentials from Web Browsers
- Cleanup.exe (PID: 3048)
SUSPICIOUS
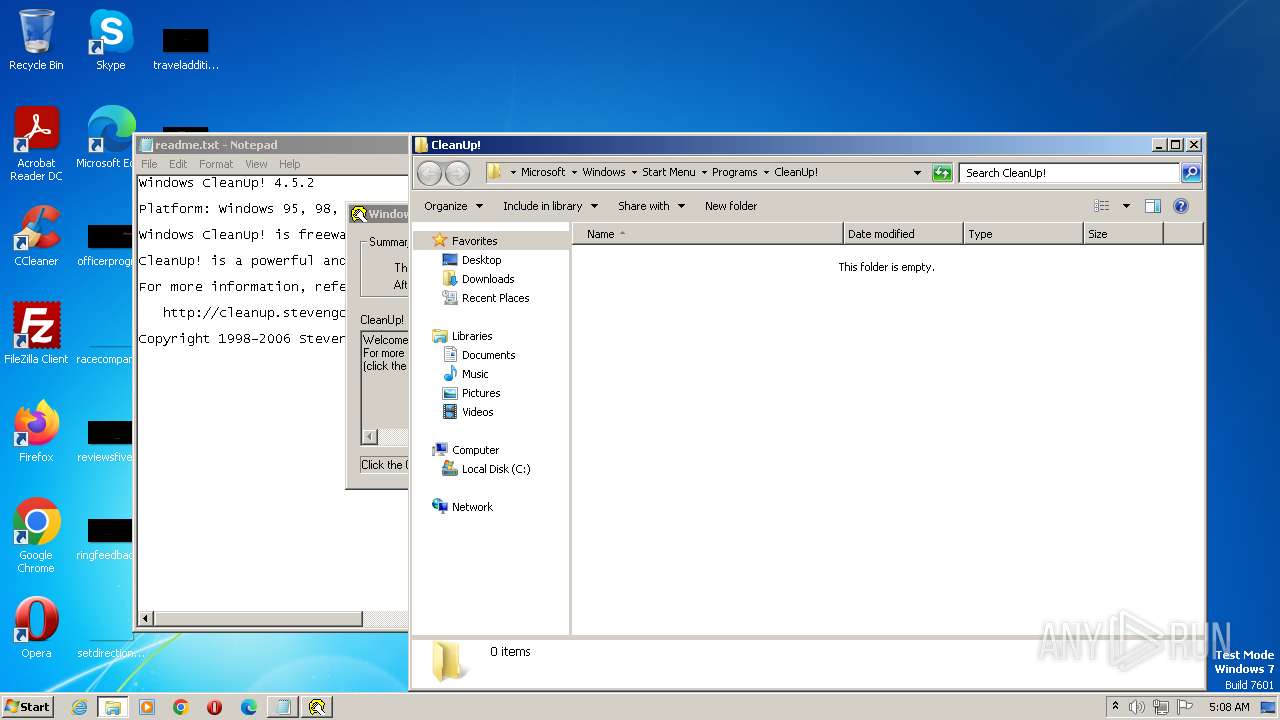
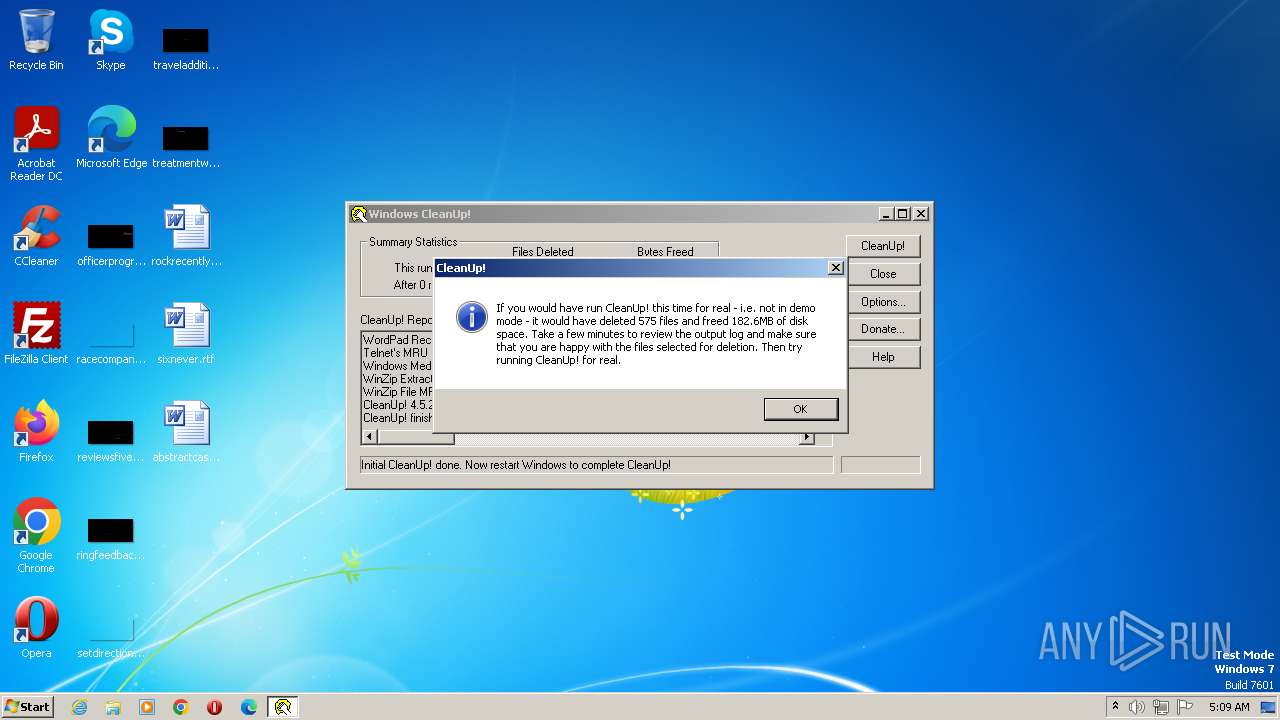
Start notepad (likely ransomware note)
- CleanUp452.exe (PID: 2908)
Executable content was dropped or overwritten
- CleanUp452.exe (PID: 2908)
Reads the Internet Settings
- Cleanup.exe (PID: 3048)
Detected use of alternative data streams (AltDS)
- Cleanup.exe (PID: 3048)
INFO
Checks supported languages
- CleanUp452.exe (PID: 2908)
- Cleanup.exe (PID: 3048)
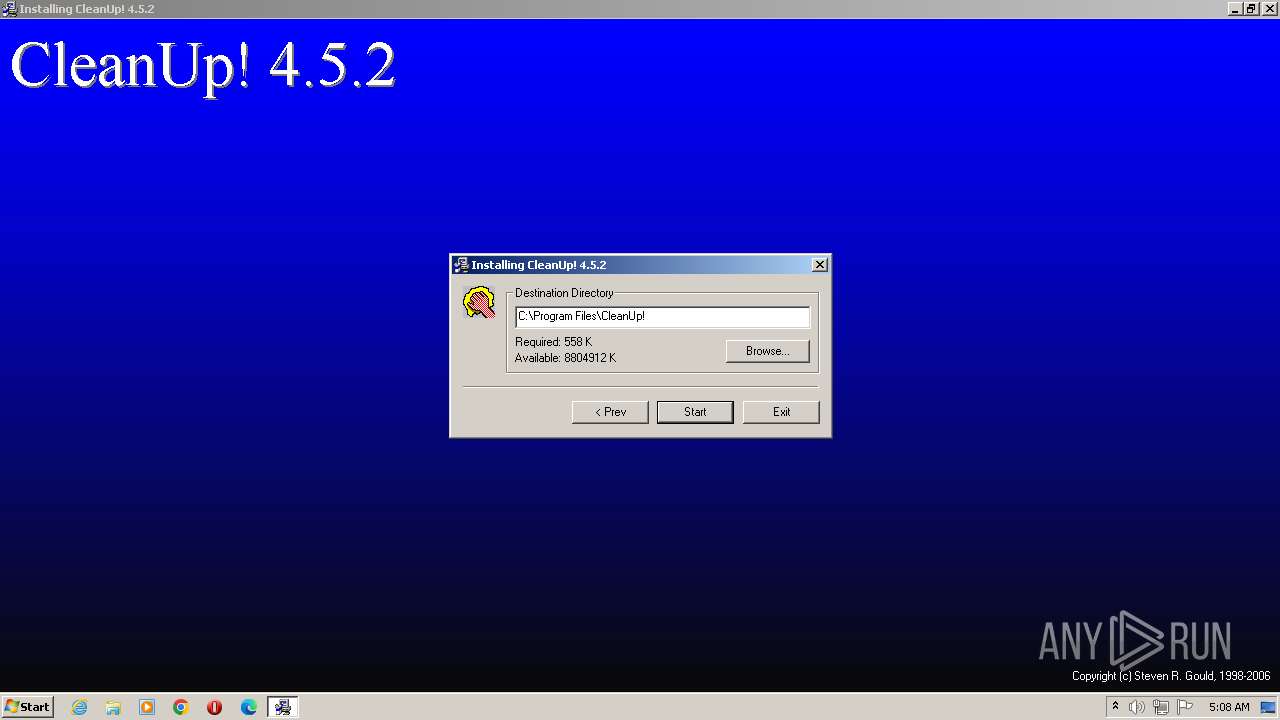
Creates files in the program directory
- CleanUp452.exe (PID: 2908)
Reads the machine GUID from the registry
- CleanUp452.exe (PID: 2908)
Reads the computer name
- CleanUp452.exe (PID: 2908)
- Cleanup.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1020 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4608 |
| CodeSize: | 2560 |
| LinkerVersion: | 3 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 1999:10:06 10:33:39+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Oct-1999 10:33:39 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 06-Oct-1999 10:33:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000009F8 | 0x00000A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.27597 |
.rdata | 0x00002000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0407808 |
.data | 0x00003000 | 0x0000025C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.07382 |
.idata | 0x00004000 | 0x000002FE | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83057 |
.Shared | 0x00005000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0.0659144 |
.rsrc | 0x00006000 | 0x0000039C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.189 |
.reloc | 0x00007000 | 0x000001B2 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.36734 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.38813 | 744 | UNKNOWN | English - United States | RT_ICON |
101 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1048 | "C:\Users\admin\AppData\Local\Temp\CleanUp452.exe" | C:\Users\admin\AppData\Local\Temp\CleanUp452.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2304 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\CleanUp!\readme.txt | C:\Windows\System32\notepad.exe | — | CleanUp452.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2908 | "C:\Users\admin\AppData\Local\Temp\CleanUp452.exe" | C:\Users\admin\AppData\Local\Temp\CleanUp452.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
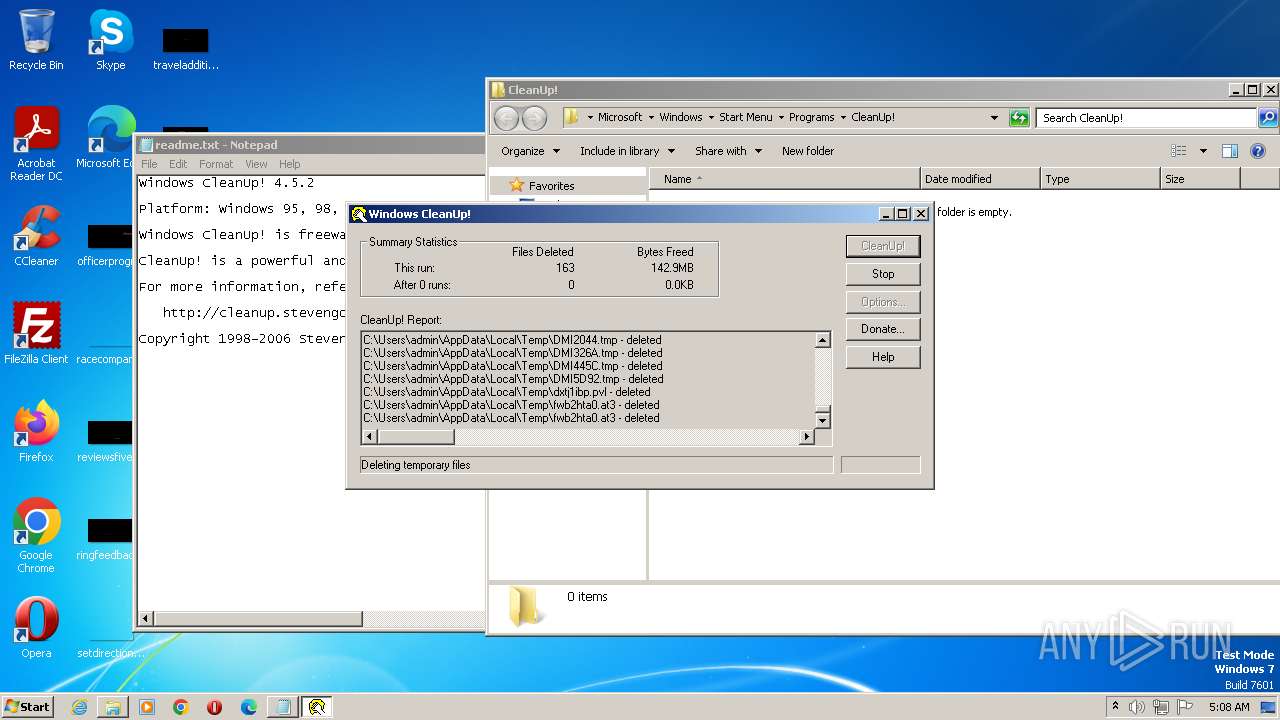
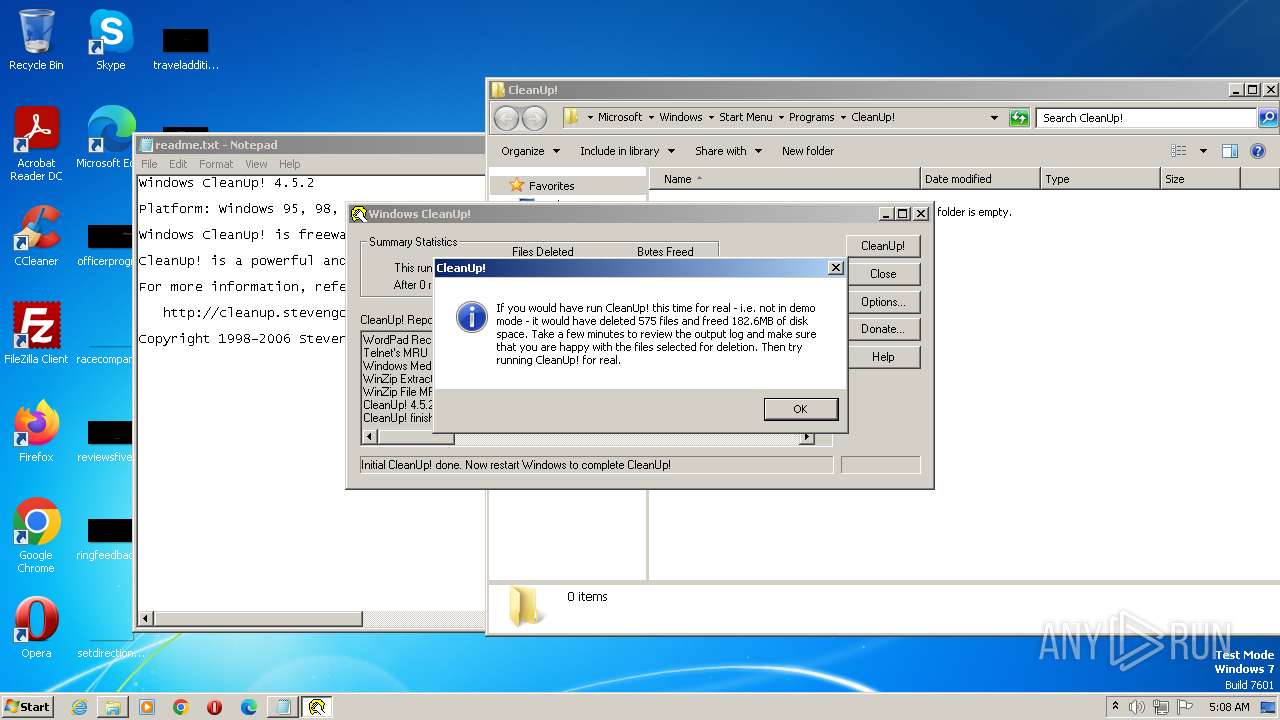
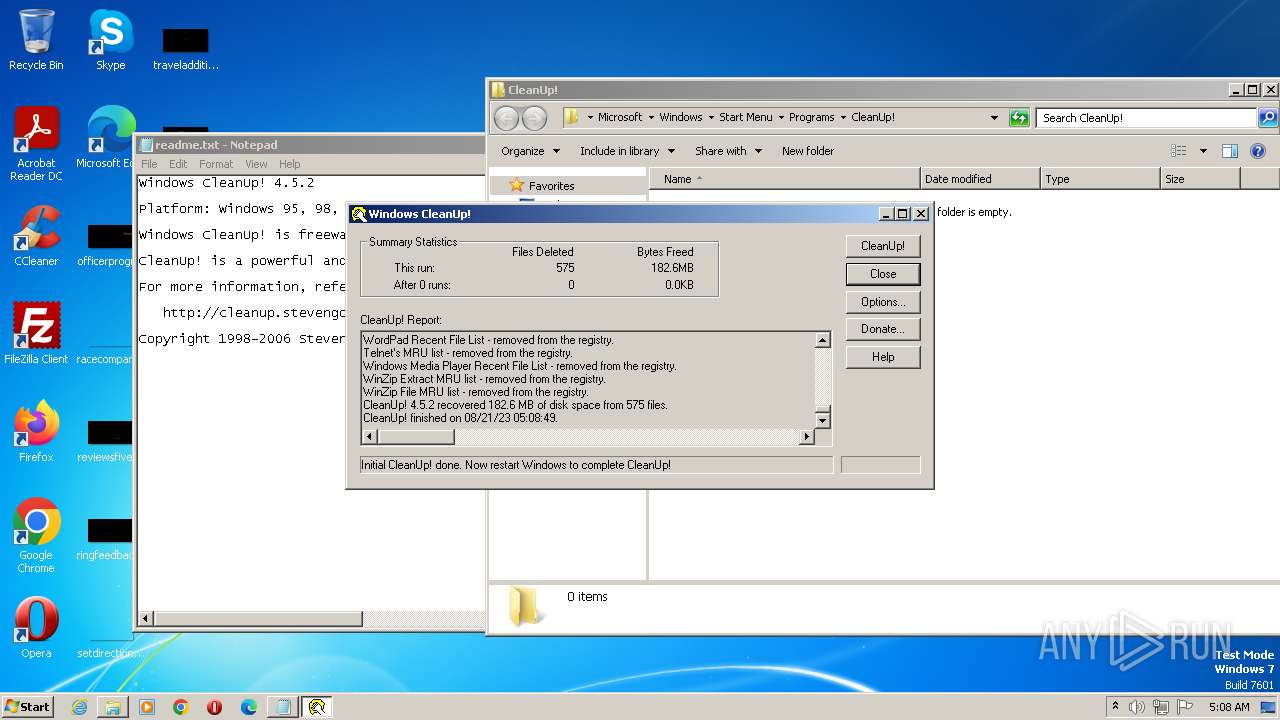
| 3048 | C:\PROGRA~1\CleanUp!\cleanup.exe | C:\Program Files\CleanUp!\Cleanup.exe | CleanUp452.exe | ||||||||||||
User: admin Company: Steven R. Gould Integrity Level: HIGH Description: Removes temporary files. Frees disk space and helps protect privacy! :-) Exit code: 2 Version: 4.5.2 Modules
| |||||||||||||||
Total events
1 025
Read events
1 019
Write events
6
Delete events
0
Modification events
| (PID) Process: | (3048) Cleanup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3048) Cleanup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2304) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 132 | |||
| (PID) Process: | (2304) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 132 | |||
| (PID) Process: | (2304) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (2304) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
Executable files
3
Suspicious files
6
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2908 | CleanUp452.exe | C:\temp\Setup.bmp | image | |
MD5:4F239303278E8A88E4B91AC14FAD72EF | SHA256:D16BC1BE3893B4AE5F8B2C064C40F9D15091A47728D15FB6C98F779DCD0CAC9A | |||
| 2908 | CleanUp452.exe | C:\Program Files\CleanUp!\CleanUp.hlp | binary | |
MD5:DE9F66C9080BDAB45A391CEE29E42522 | SHA256:C34A71966FA436F42521A44A68901478502E90ADBDA9AB5F7B987F418DBB56BF | |||
| 2908 | CleanUp452.exe | C:\Program Files\CleanUp!\CleanUp.cnt | text | |
MD5:323816A3AA84E444713BAD22119ABD22 | SHA256:BC7228BEA82FD7875CA5ED4D5EC7FB7F14B9AEB60E76AA6176497D00979BF9B9 | |||
| 2908 | CleanUp452.exe | C:\Program Files\CleanUp!\license.txt | text | |
MD5:FB3033EA6F872179BAAD639172D89B68 | SHA256:635AFC3AD967E04865B2D6F0B1DCBDA90BC41E48BA6FED314592C762D7111B0A | |||
| 2908 | CleanUp452.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CleanUp!\CleanUp!.lnk | binary | |
MD5:9FBAAD0EC3A1E68E047DB5A8D990F385 | SHA256:64E8140FDDB678777E88592056BA4DA7DC9909C687D87EAC058BF0064DDD725A | |||
| 2908 | CleanUp452.exe | C:\ginstall.dll | executable | |
MD5:909D7CBC60915BB280DDE2C706F86AE4 | SHA256:0B76CC6506A41BC34A054AA55581E7E6E982F630A100967A9D2F00CA631F3A37 | |||
| 2908 | CleanUp452.exe | C:\temp\license.txt | text | |
MD5:FB3033EA6F872179BAAD639172D89B68 | SHA256:635AFC3AD967E04865B2D6F0B1DCBDA90BC41E48BA6FED314592C762D7111B0A | |||
| 2908 | CleanUp452.exe | C:\Program Files\CleanUp!\Cleanup.exe | executable | |
MD5:12F98E1AD522BC705B80F4A1F7377915 | SHA256:4CF76AA17531E190C9D7E34C3D8A4D7466386DAF3F94D8126AFA2841A091A6B4 | |||
| 2908 | CleanUp452.exe | C:\Program Files\CleanUp!\CleanUp! Web Site.url | text | |
MD5:BEF57486B75F2FA90F7F6AD269FBB26C | SHA256:57EFFE2B06F31E96C1B67F5A7FB1D5B142F00595516614DB850786DB75B43C2E | |||
| 2908 | CleanUp452.exe | C:\Program Files\CleanUp!\uninstall.exe | executable | |
MD5:4C765359AD026088738AD16BE589F027 | SHA256:304A1D9A196F2286933897CC7AFC8AB52EF37E48ABB65ECF792D3C5311A7E017 | |||
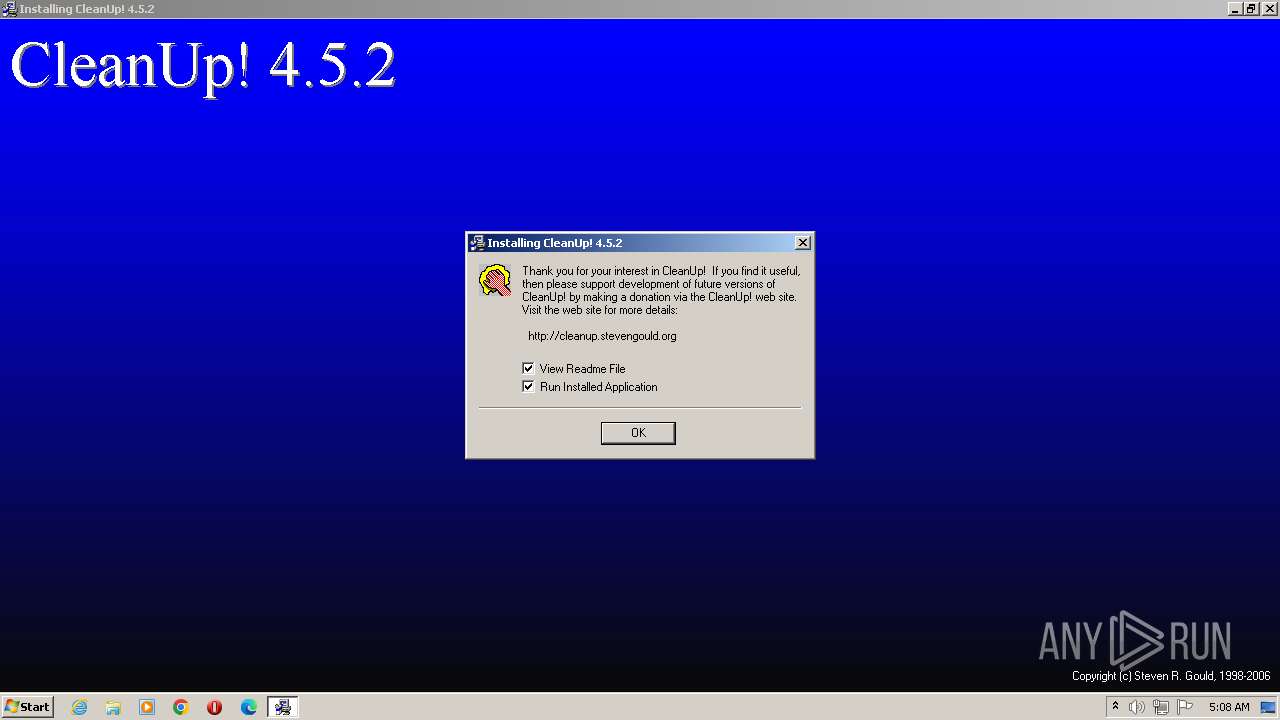
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |