| File name: | 포토#8840.exe |
| Full analysis: | https://app.any.run/tasks/4d976231-6ab3-4945-98e5-78b43691c226 |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2020, 14:40:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | F19FFC1926D64611303B4ECB386F9D5C |
| SHA1: | 8FA6CC541C83BA51D3EE85E8588C48891E7540D0 |
| SHA256: | 6AB6E6DD0CDE22180DA093F2E80E37BF429373B4259FBBDBEB8E45A2B6B4EC7C |
| SSDEEP: | 3072:0PMBeE/SHrzf7NgdbzjV/FnbhkILGD1iWXmW0kYY6DsQV9Y6DsQV9J2:4NE/szfJgdn1ksk1PXmWsHgQVFgQVW |
MALICIOUS
No malicious indicators.SUSPICIOUS
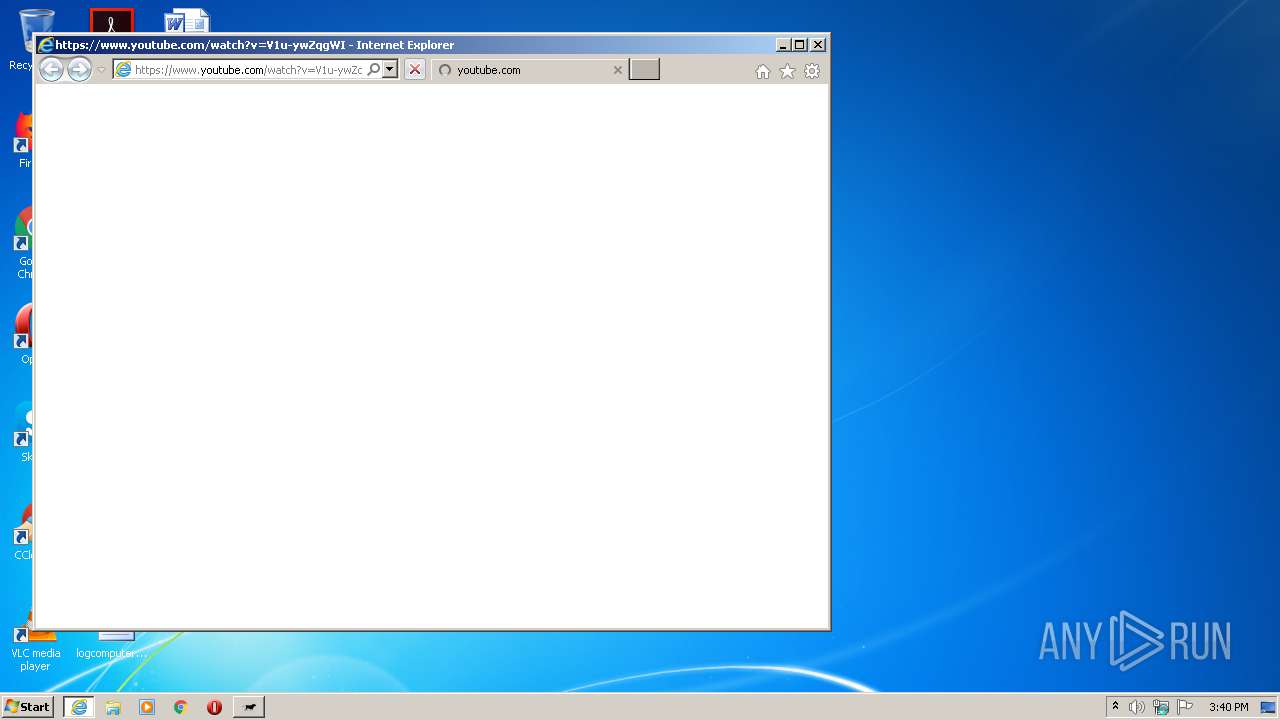
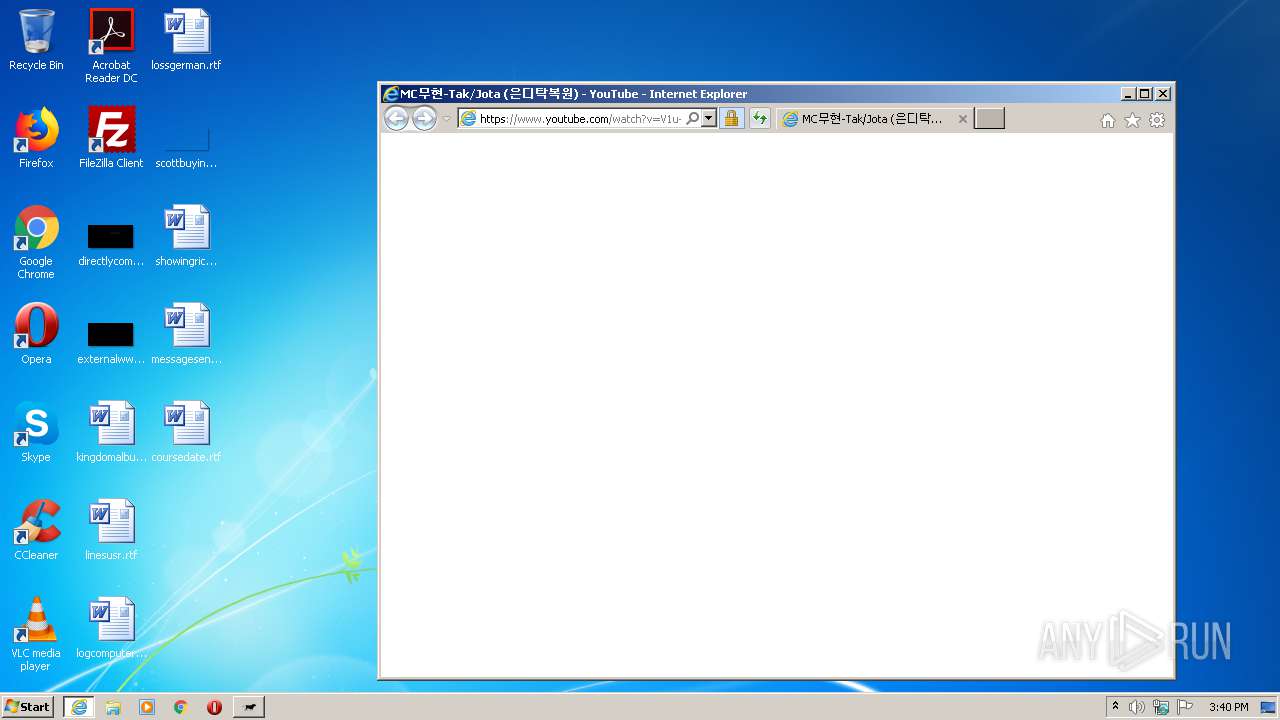
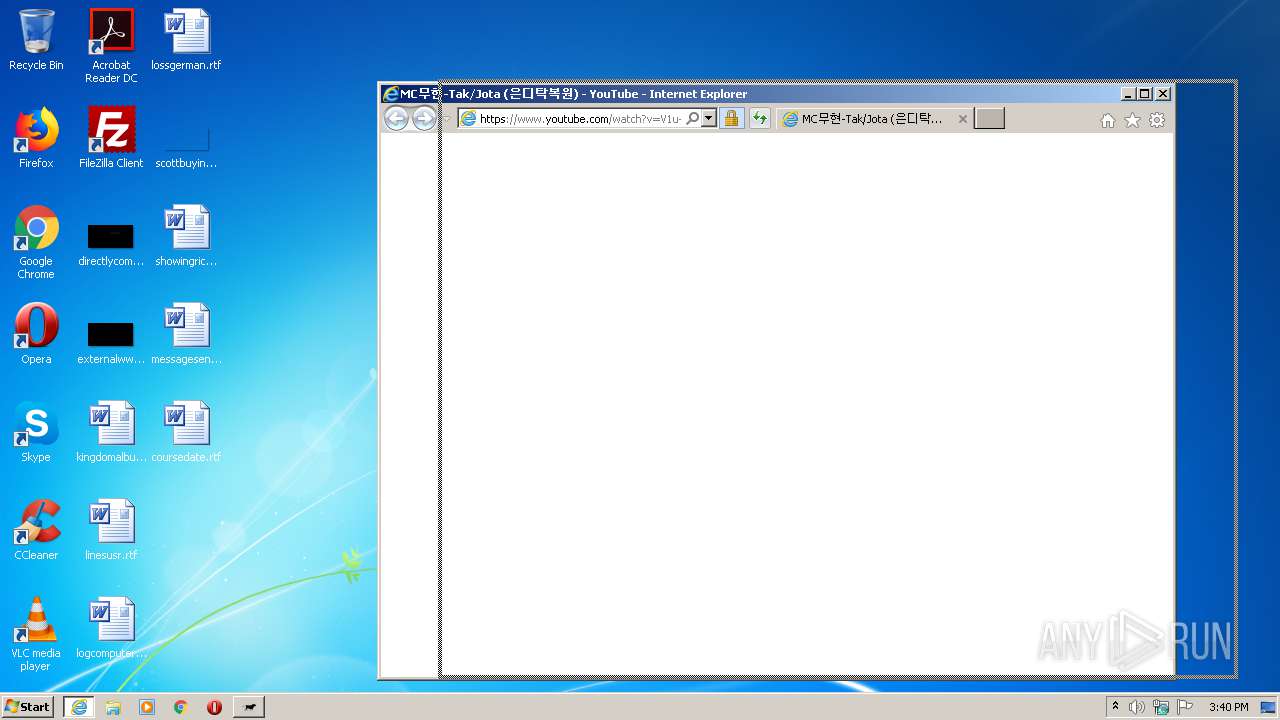
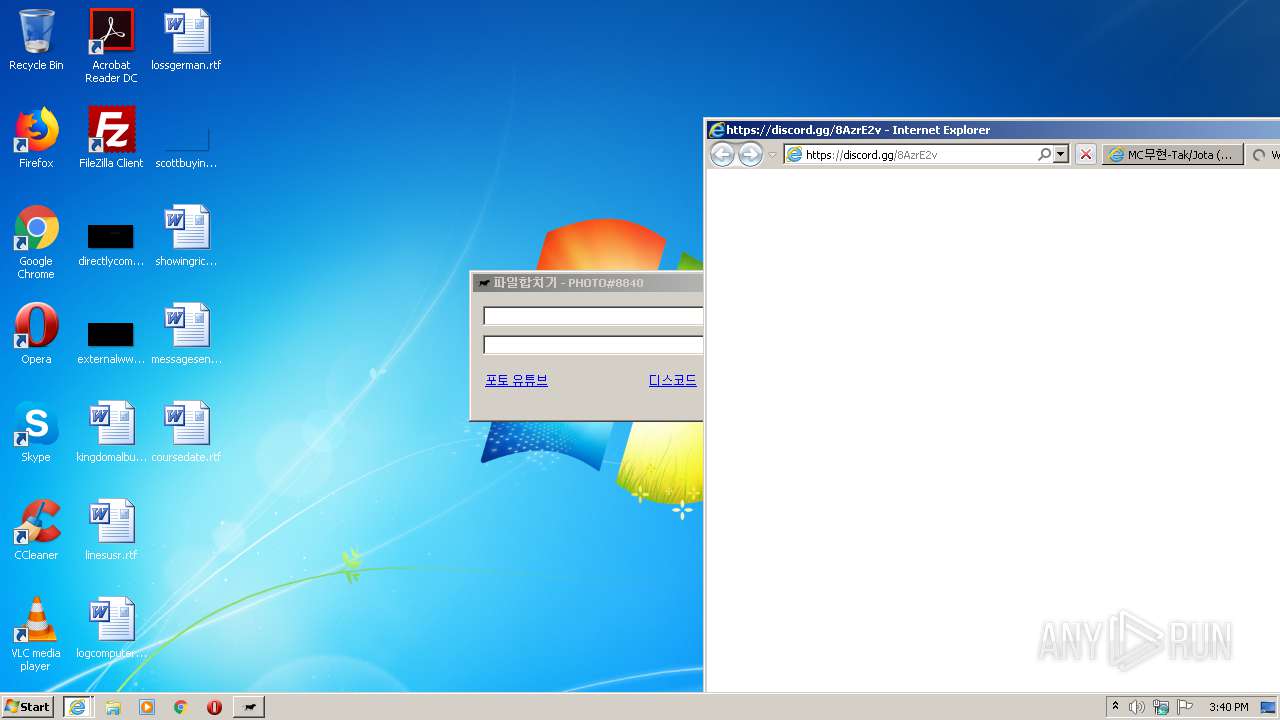
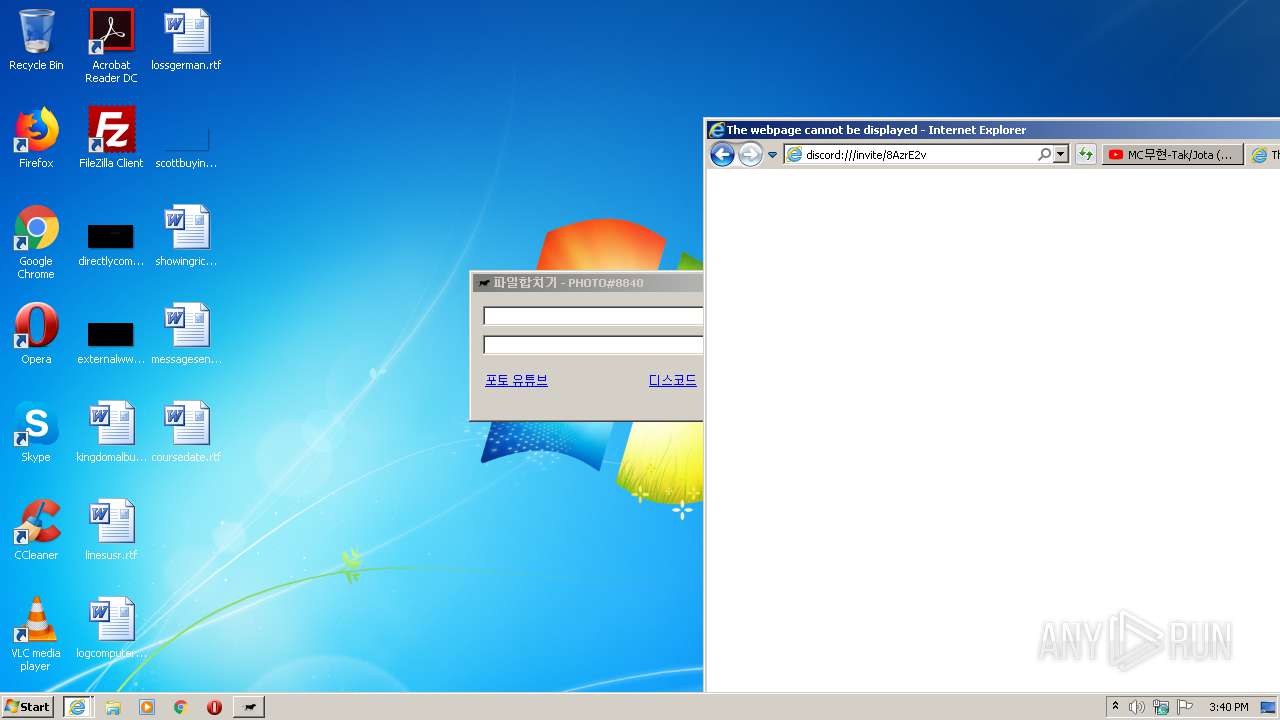
Starts Internet Explorer
- 포토#8840.exe (PID: 2164)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 2720)
- iexplore.exe (PID: 340)
Changes internet zones settings
- iexplore.exe (PID: 2720)
Creates files in the user directory
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 2720)
- iexplore.exe (PID: 340)
Application launched itself
- iexplore.exe (PID: 2720)
Reads internet explorer settings
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 340)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 340)
Reads settings of System Certificates
- iexplore.exe (PID: 2720)
Changes settings of System certificates
- iexplore.exe (PID: 2720)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.8) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:13 16:39:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 100864 |
| InitializedDataSize: | 918016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a8be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
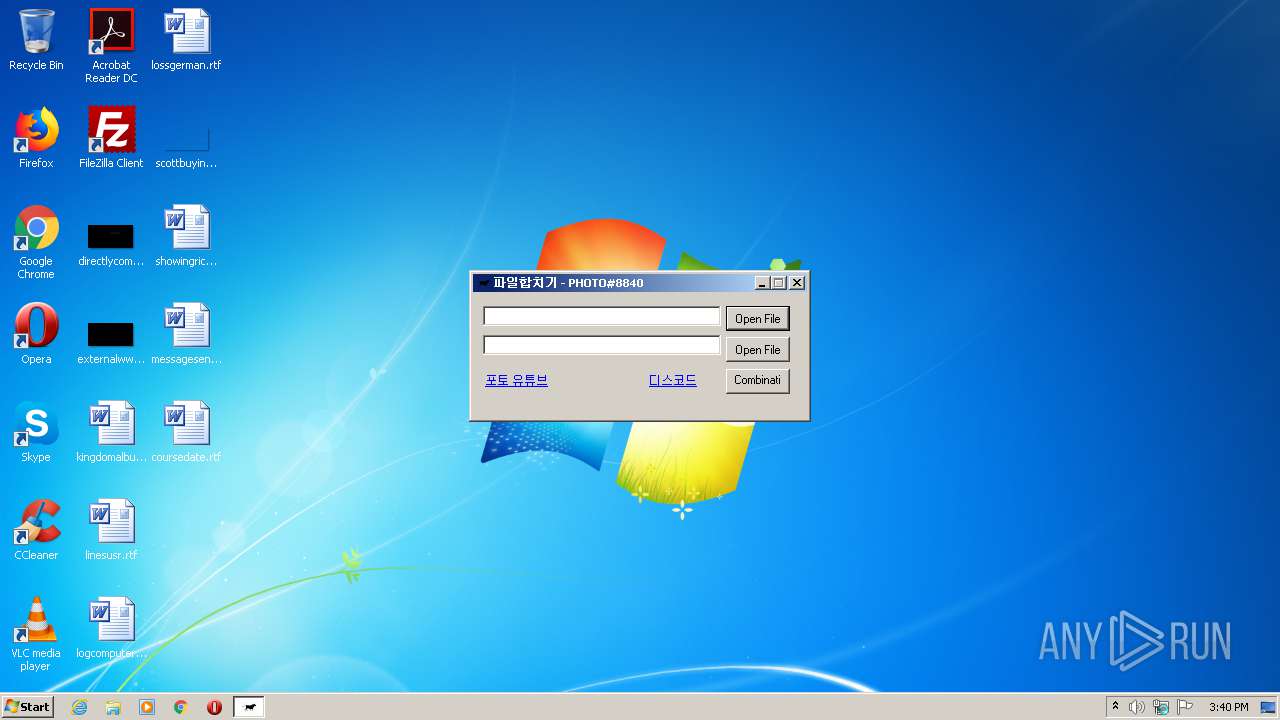
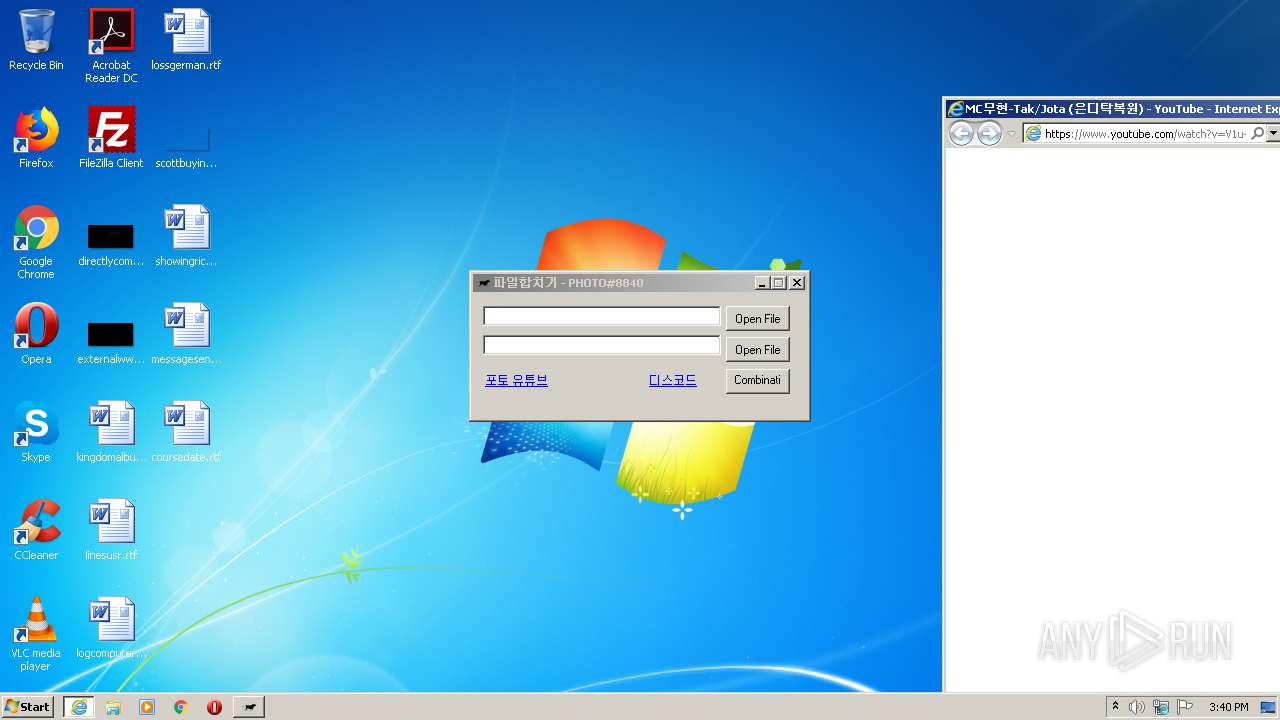
| Comments: | Combining files |
| CompanyName: | Combining files |
| FileDescription: | 독도#4911 |
| FileVersion: | 1.0.0.0 |
| InternalName: | Combining files |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | 독도#4911 |
| ProductName: | 독도#4911 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
37
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2720 CREDAT:3675414 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2164 | "C:\Users\admin\AppData\Local\Temp\포토#8840.exe" | C:\Users\admin\AppData\Local\Temp\포토#8840.exe | — | explorer.exe | |||||||||||
User: admin Company: Combining files Integrity Level: MEDIUM Description: 독도#4911 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2720 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/watch?v=V1u-ywZqgWI | C:\Program Files\Internet Explorer\iexplore.exe | 포토#8840.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 049
Read events
790
Write events
3 540
Delete events
1 719
Modification events
| (PID) Process: | (2164) 포토#8840.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000D42D51949041D601 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2789441866 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30818704 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
0
Suspicious files
45
Text files
56
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE180.tmp | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE181.tmp | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6XFZY1E0.txt | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\FNEUYE88.txt | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\C5NQNA82.txt | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_361E3A337474CF5AAD1F109F55F06A02 | der | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\ServiceLogin[1].htm | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_2E11ECD2011DB169365384C6FF99FC49 | binary | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BE8B021F9E811DFC8C8A28572A17C05A_2E11ECD2011DB169365384C6FF99FC49 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
56
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2464 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFb63M0OvvAcCAAAAABDVec%3D | US | der | 471 b | whitelisted |
2464 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDYtsl5jxUVpgIAAAAAayEm | US | der | 472 b | whitelisted |
340 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEDsJGKKiFxWJllawuNqPxXw%3D | US | der | 279 b | whitelisted |
340 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
340 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEDsJGKKiFxWJllawuNqPxXw%3D | US | der | 279 b | whitelisted |
340 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 312 b | whitelisted |
2464 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2464 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDBz%2BWSF2BSZwIAAAAAayBs | US | der | 472 b | whitelisted |
340 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEQCML6NXQdejdBJDG5j4aa9U | US | der | 281 b | whitelisted |
340 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEQCML6NXQdejdBJDG5j4aa9U | US | der | 281 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | iexplore.exe | 172.217.23.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
2464 | iexplore.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2464 | iexplore.exe | 74.125.153.27:443 | r5---sn-hpa7zned.googlevideo.com | Google Inc. | US | whitelisted |
2464 | iexplore.exe | 216.58.205.226:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 74.125.153.27:443 | r5---sn-hpa7zned.googlevideo.com | Google Inc. | US | whitelisted |
2464 | iexplore.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2464 | iexplore.exe | 216.58.205.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2464 | iexplore.exe | 173.194.182.106:443 | r5---sn-4g5ednld.googlevideo.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
r5---sn-hpa7zned.googlevideo.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
r5---sn-4g5ednld.googlevideo.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |