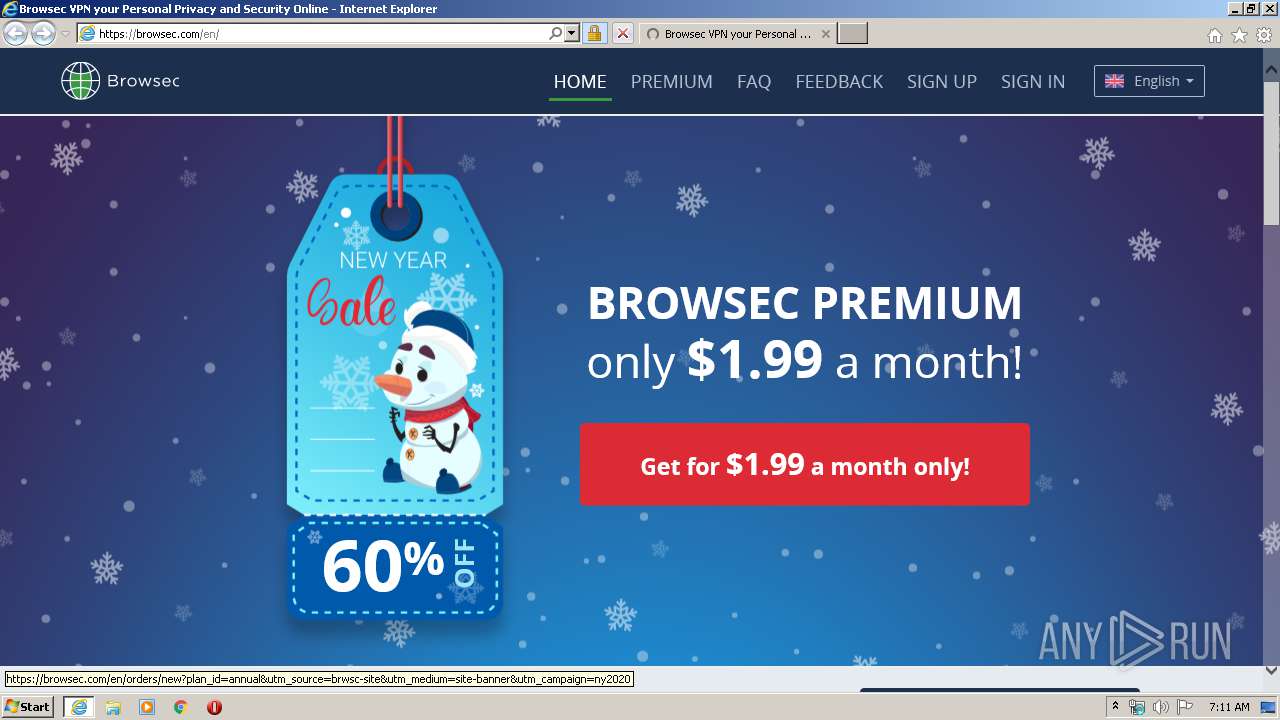
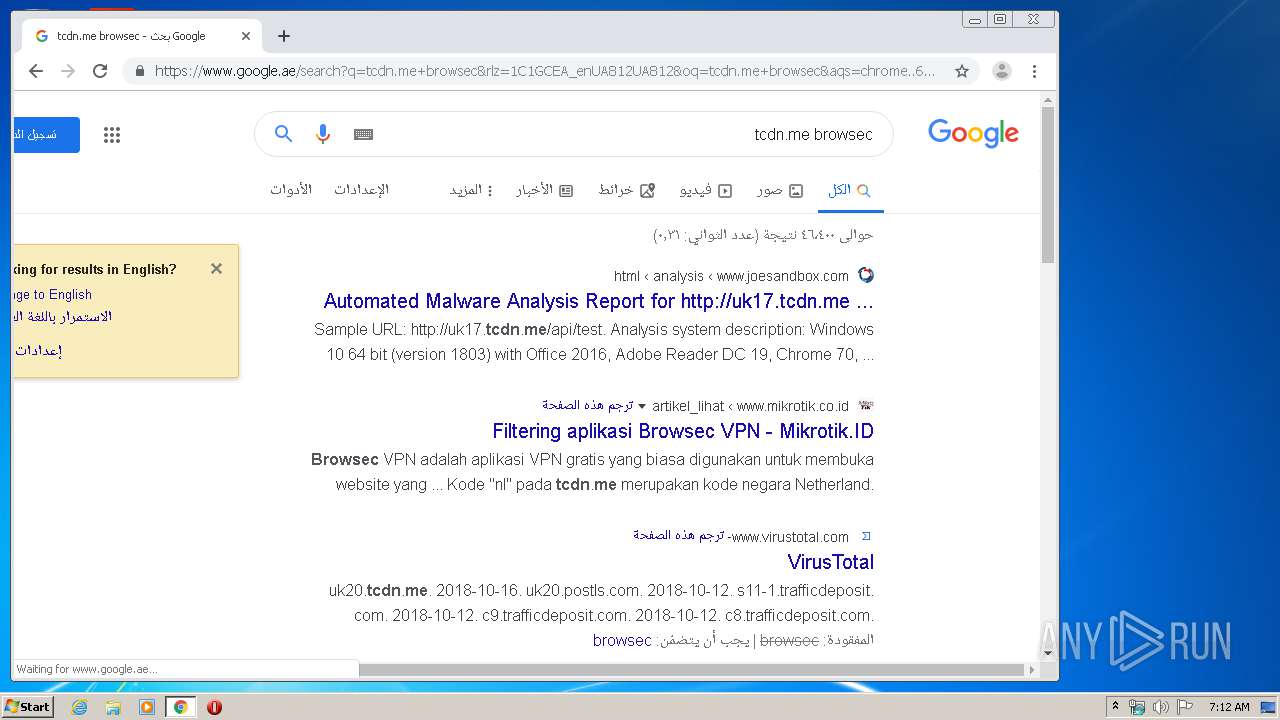
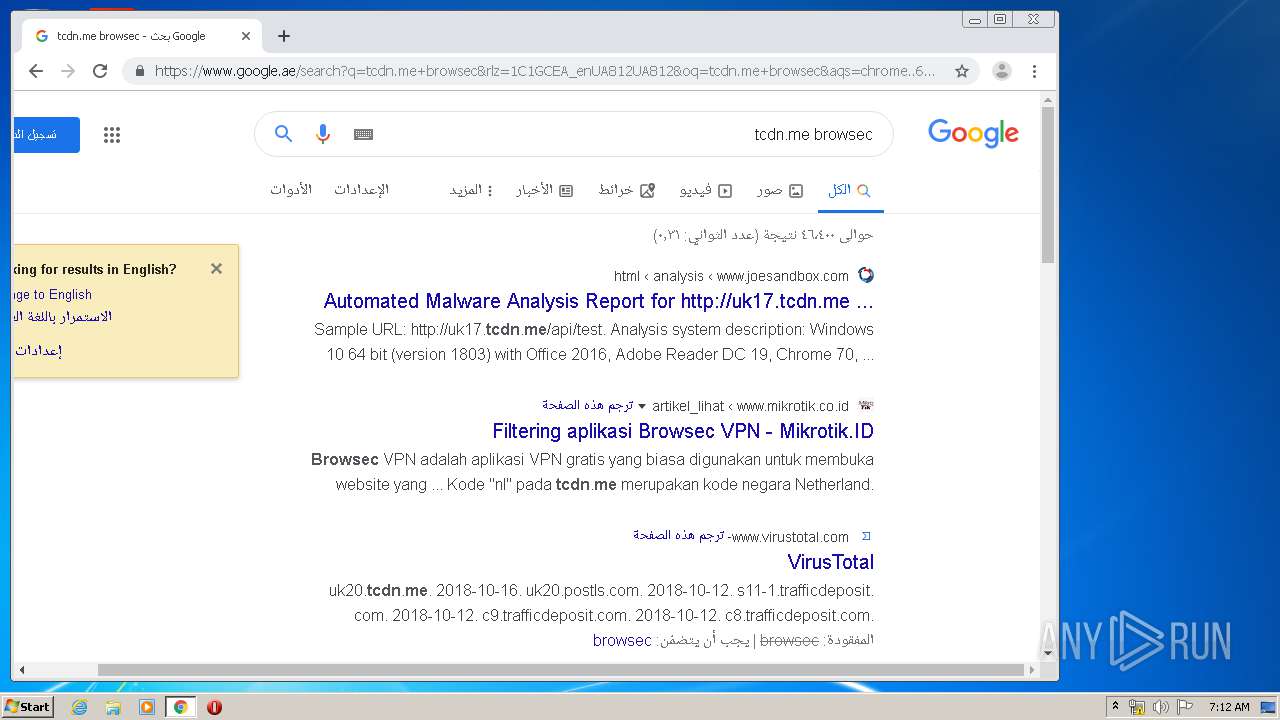
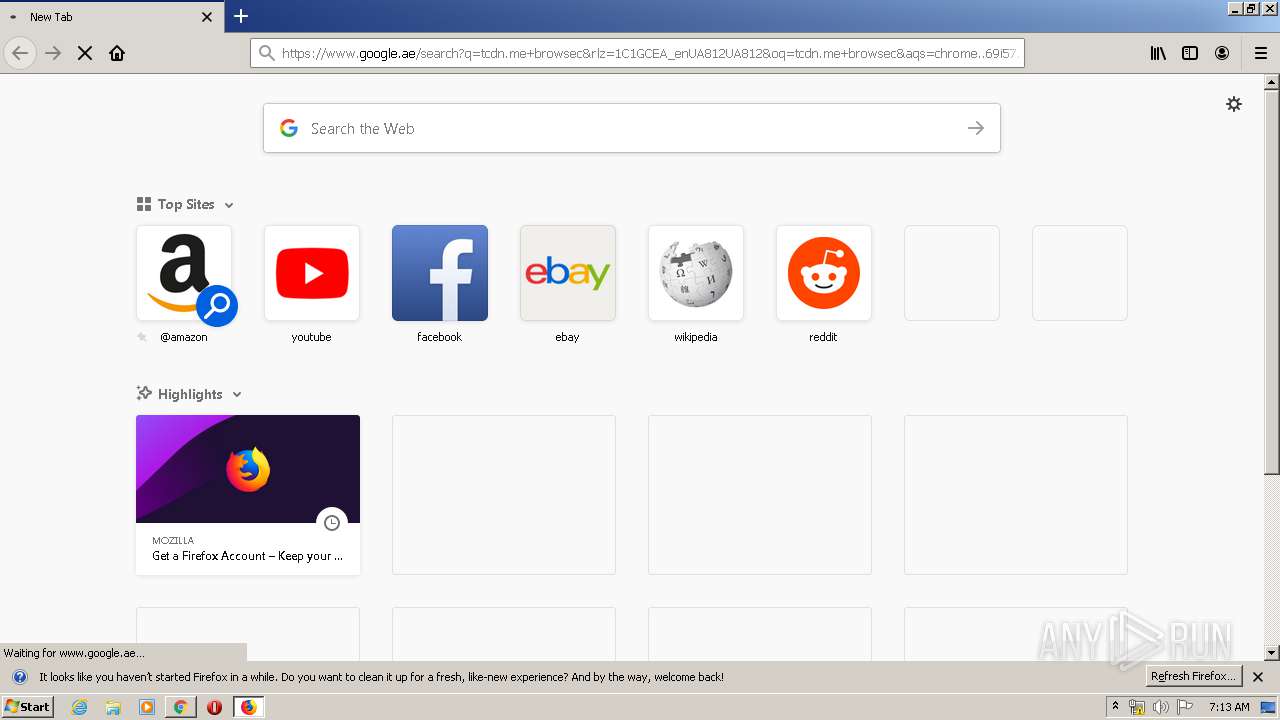
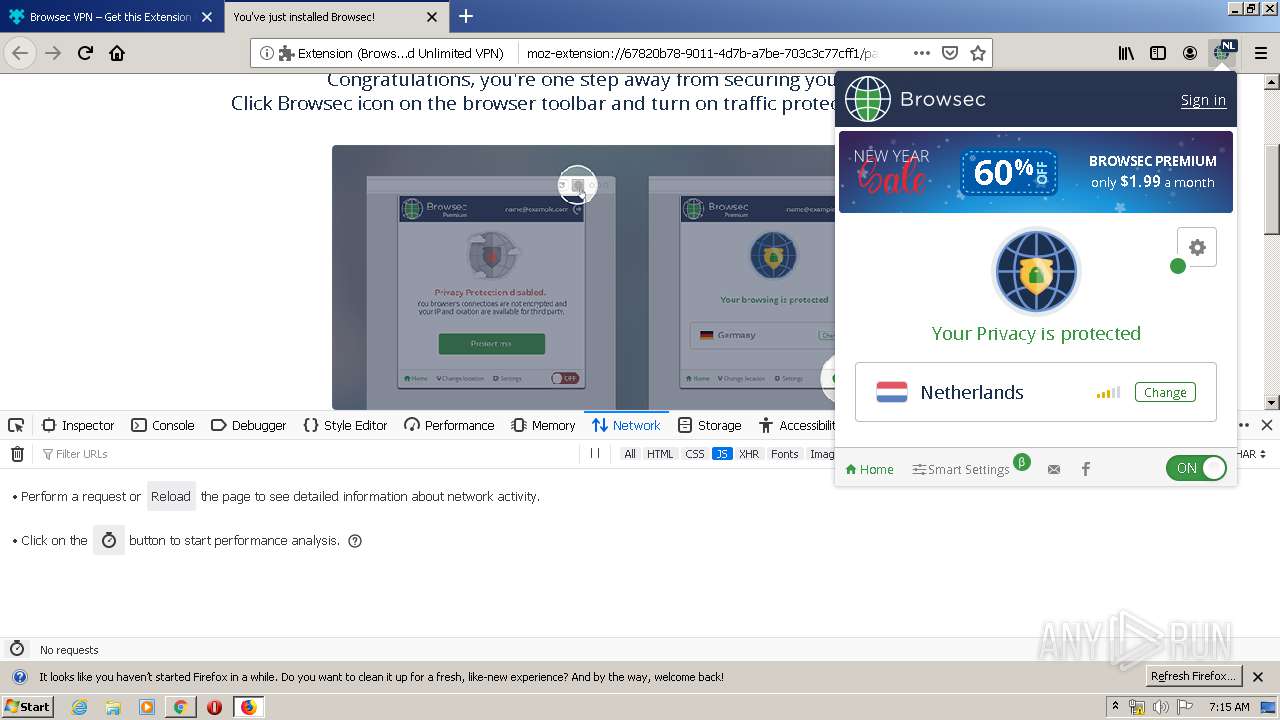
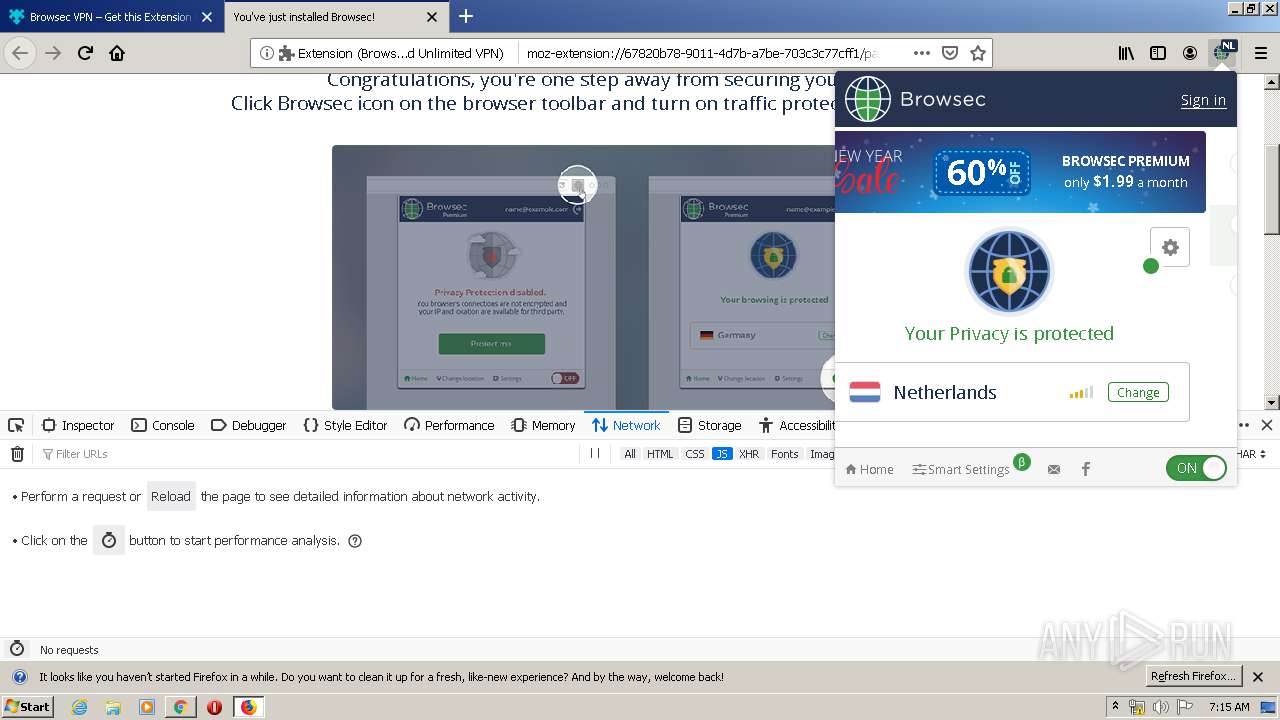
| URL: | http://browsec.com |
| Full analysis: | https://app.any.run/tasks/06249047-3185-418f-8191-03cec0404d67 |
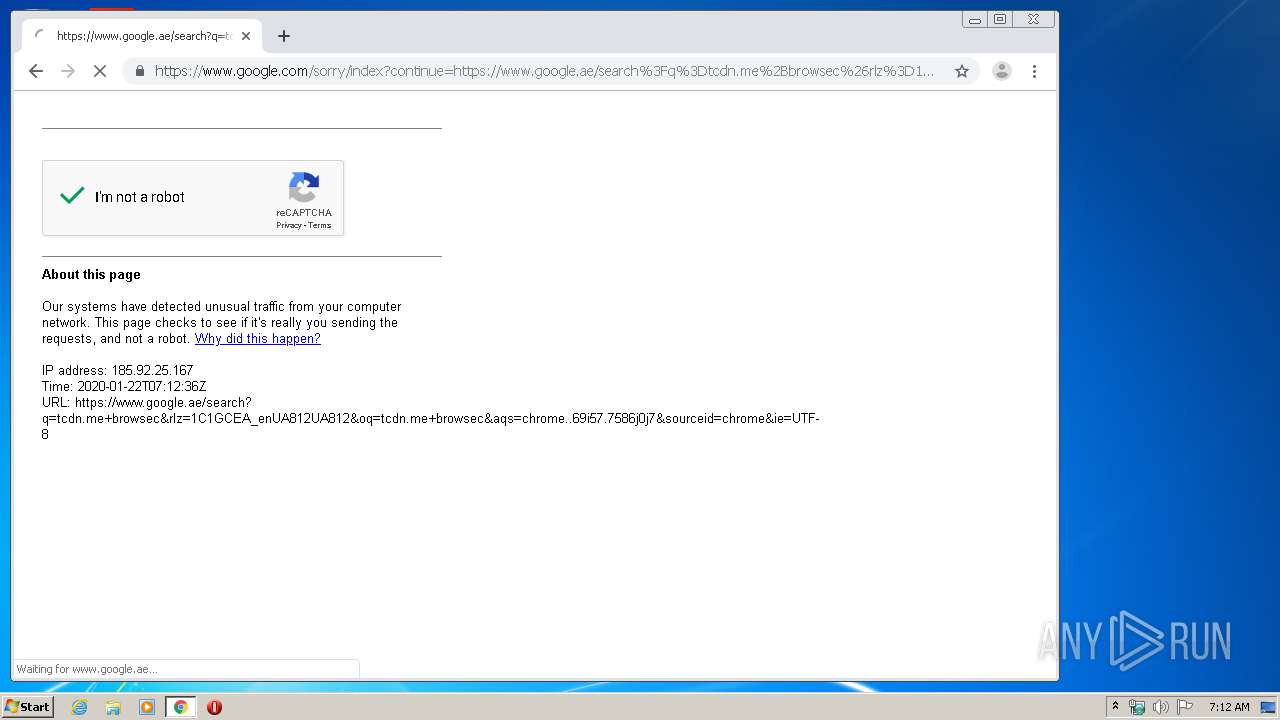
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2020, 07:11:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 05BB2EF82948F6F6617A27E23FF0A21C |
| SHA1: | A624EBEE2D09DF69EDDBD5AD535491B12F54F4CB |
| SHA256: | 6AA8BFCEDD42E4BC73E4736F5B03104D71B80C7B18B81DFD9F5174B5A3E3C81D |
| SSDEEP: | 3:N1KcELKn:CcELKn |
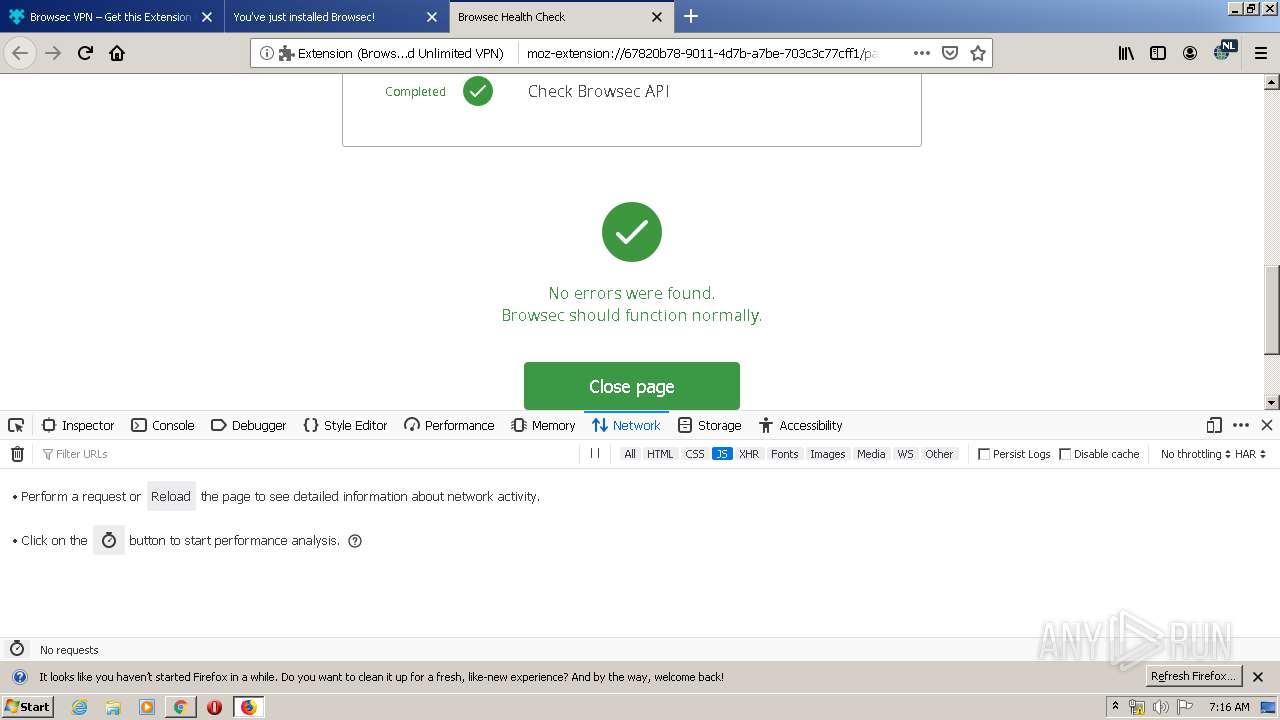
MALICIOUS
No malicious indicators.SUSPICIOUS
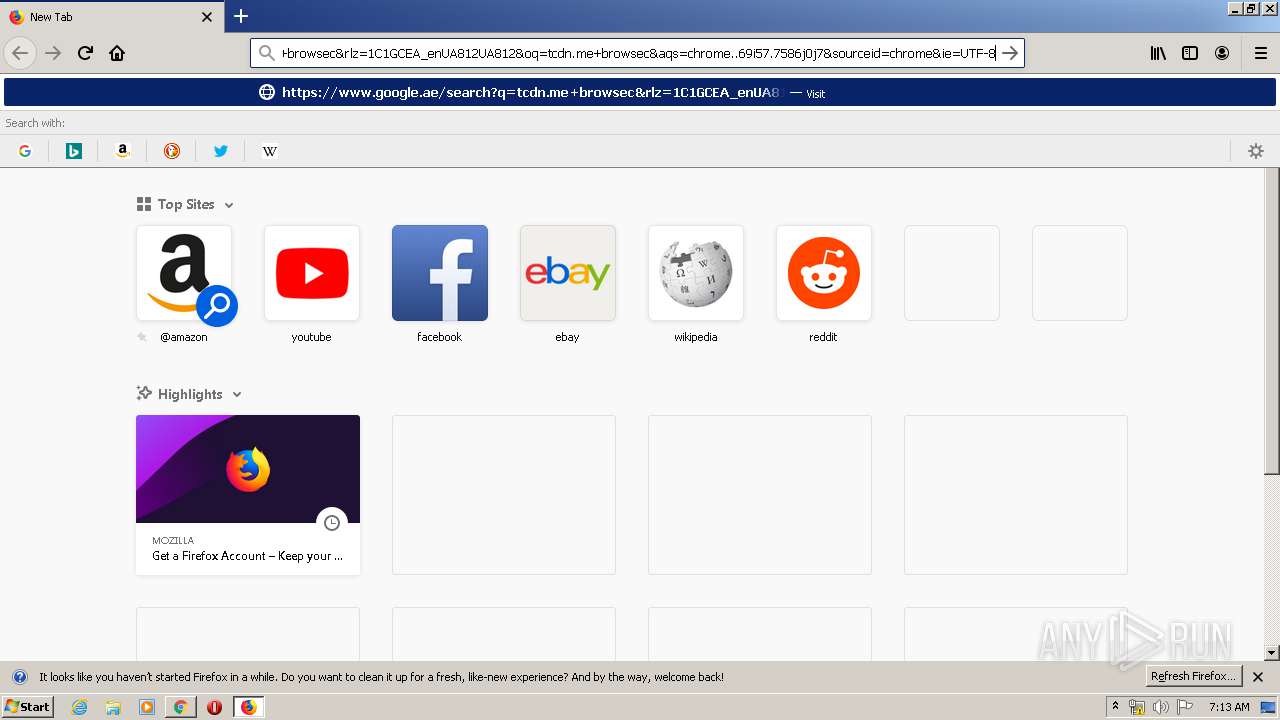
Modifies files in Chrome extension folder
- chrome.exe (PID: 3788)
Creates files in the program directory
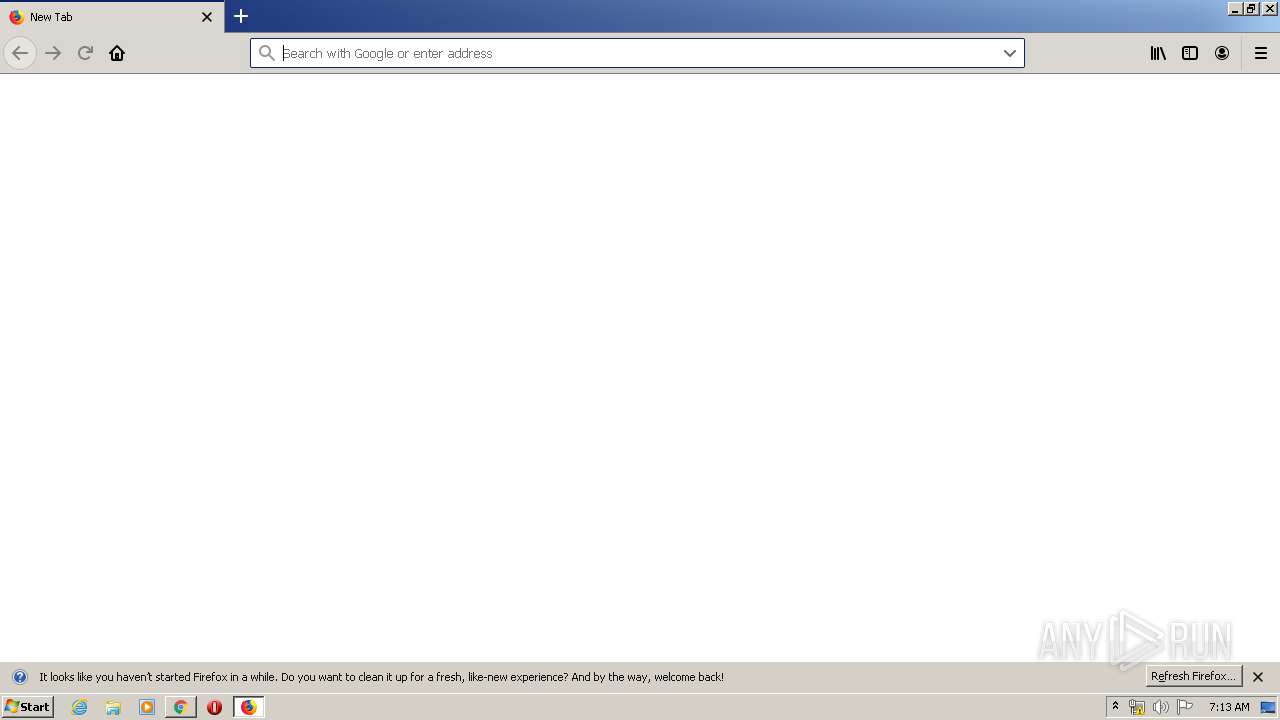
- firefox.exe (PID: 2712)
INFO
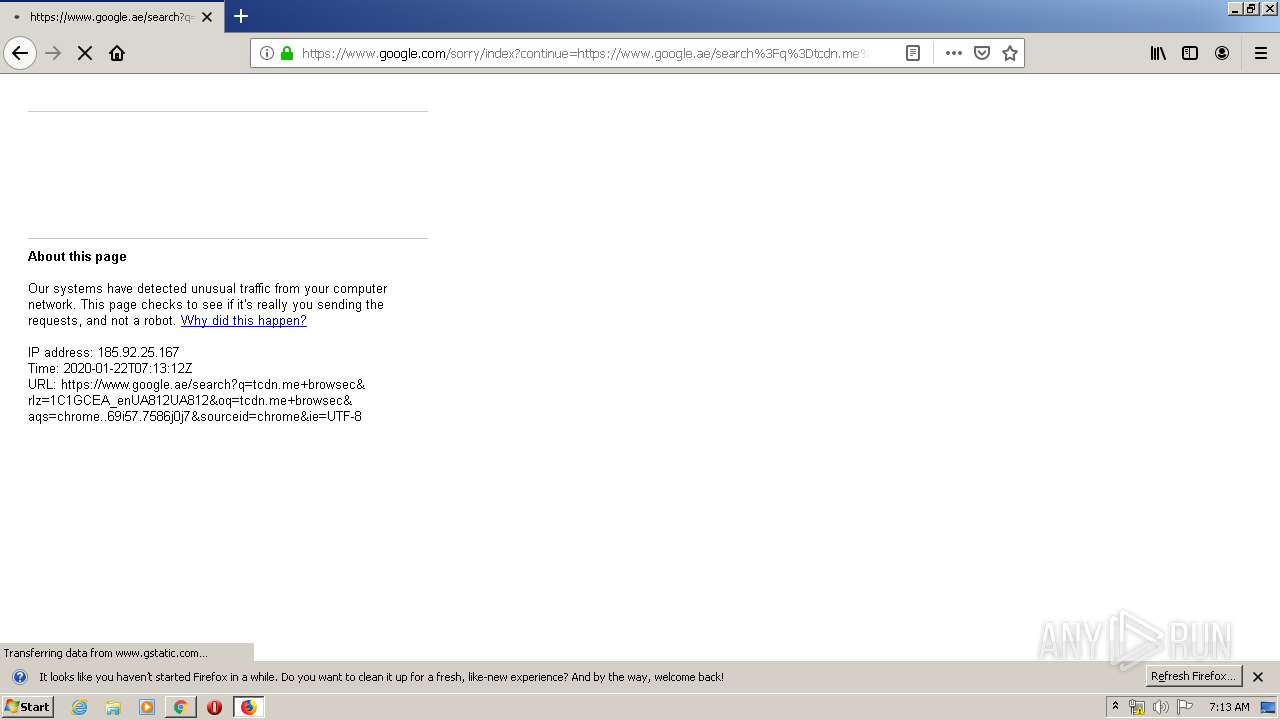
Changes internet zones settings
- iexplore.exe (PID: 2236)
Reads Internet Cache Settings
- iexplore.exe (PID: 2236)
- iexplore.exe (PID: 3896)
- firefox.exe (PID: 2712)
Creates files in the user directory
- iexplore.exe (PID: 3896)
- firefox.exe (PID: 2712)
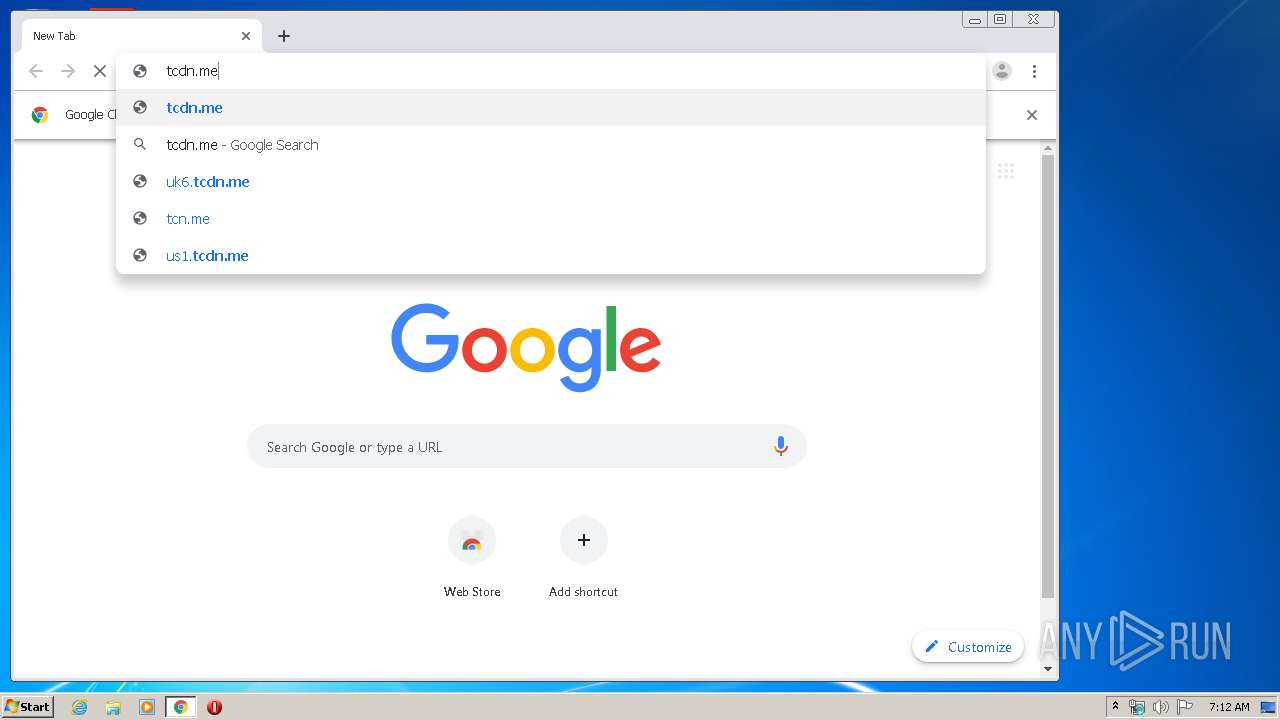
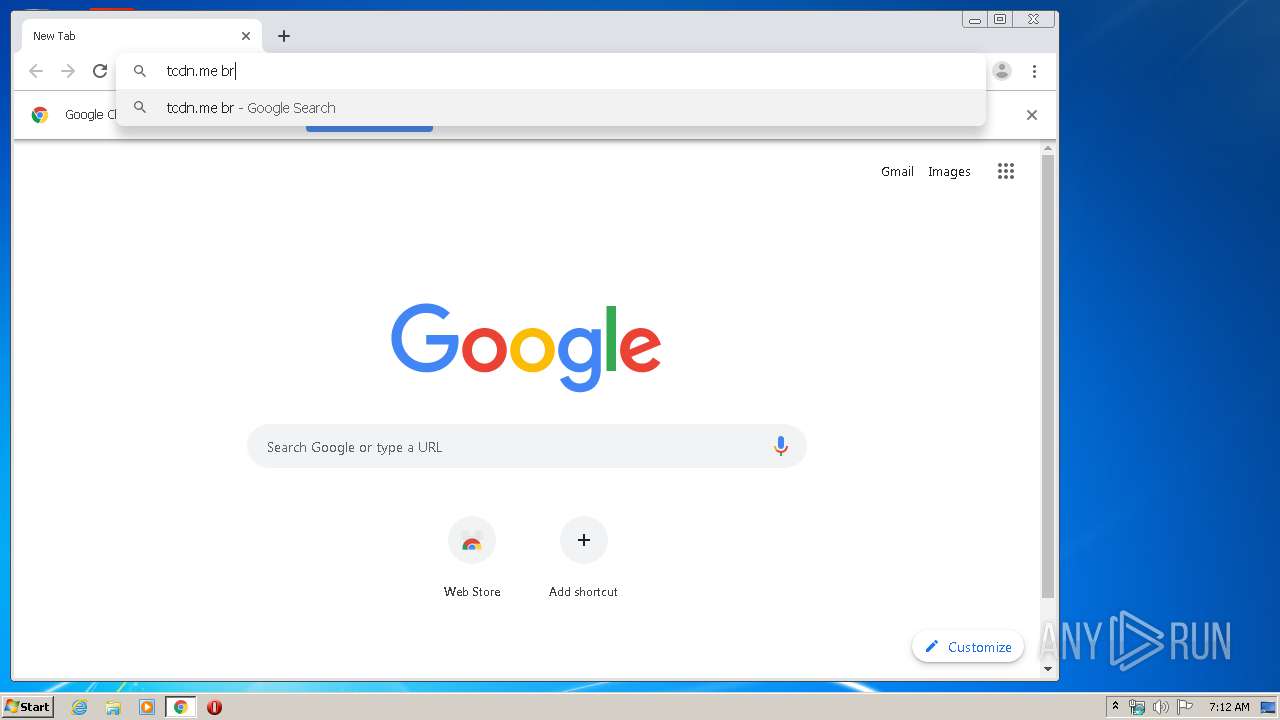
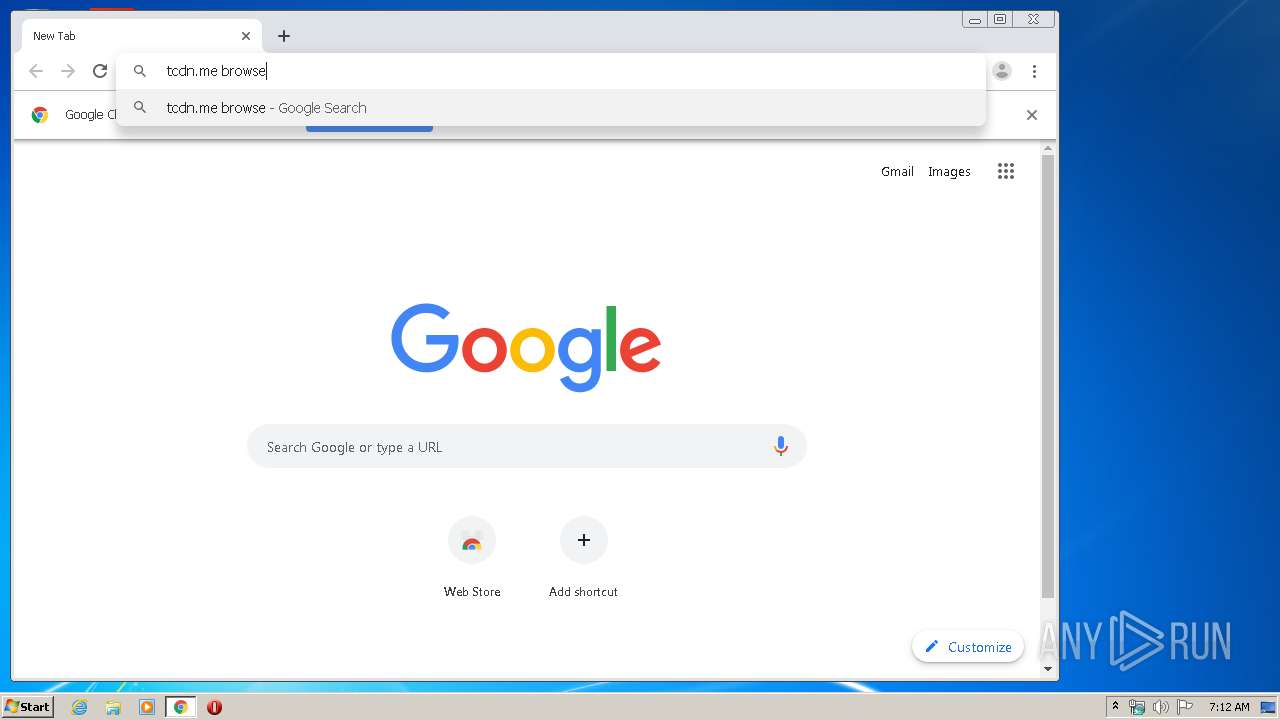
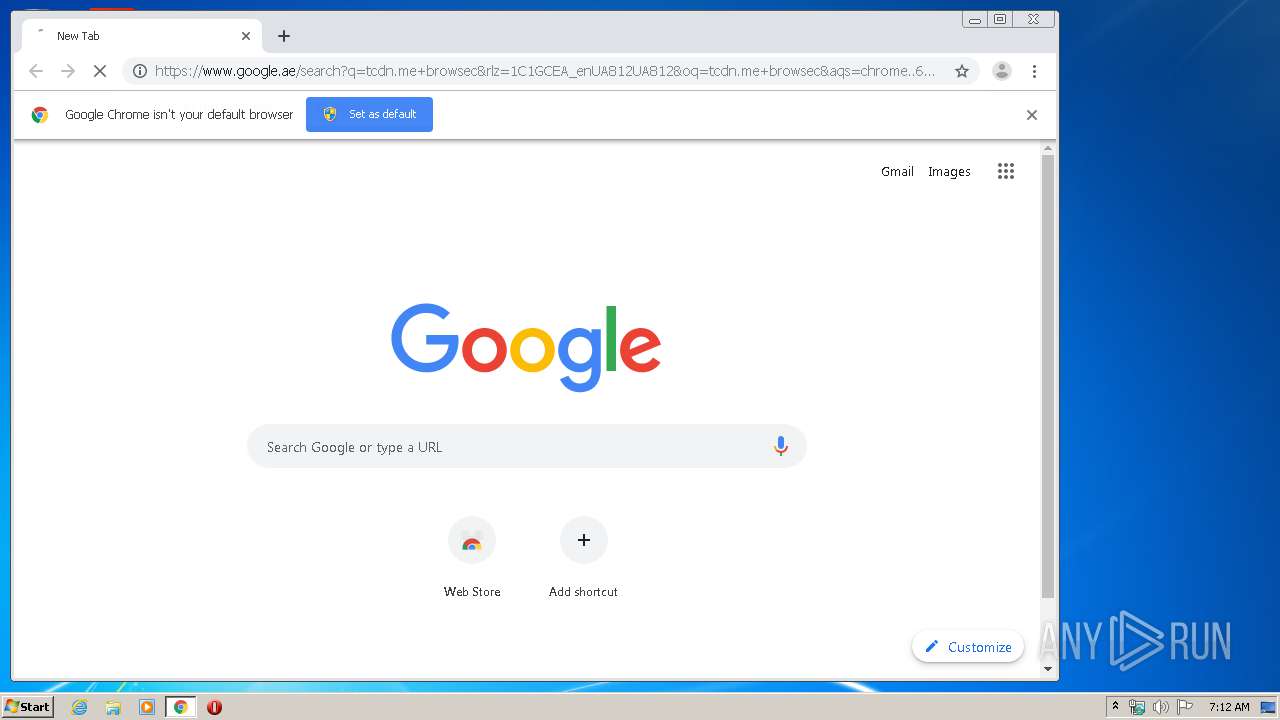
Manual execution by user
- chrome.exe (PID: 3788)
- firefox.exe (PID: 696)
Reads internet explorer settings
- iexplore.exe (PID: 3896)
Reads the hosts file
- chrome.exe (PID: 3788)
- chrome.exe (PID: 1168)
Reads settings of System Certificates
- chrome.exe (PID: 1168)
- iexplore.exe (PID: 2236)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2236)
Changes settings of System certificates
- iexplore.exe (PID: 2236)
Application launched itself
- firefox.exe (PID: 2712)
- chrome.exe (PID: 3788)
Reads CPU info
- firefox.exe (PID: 2712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
41
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,360721057534544025,14194474001147365169,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13246318057108533754 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,360721057534544025,14194474001147365169,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12251789304811774606 --mojo-platform-channel-handle=3680 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,360721057534544025,14194474001147365169,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=793550684383824427 --mojo-platform-channel-handle=3888 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 696 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,360721057534544025,14194474001147365169,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4345030380560079902 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,360721057534544025,14194474001147365169,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5546832071066589829 --mojo-platform-channel-handle=3404 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,360721057534544025,14194474001147365169,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3168395697719377165 --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,360721057534544025,14194474001147365169,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2158345943703557325 --mojo-platform-channel-handle=3292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,360721057534544025,14194474001147365169,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7215699894965263643 --mojo-platform-channel-handle=3780 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ecba9d0,0x6ecba9e0,0x6ecba9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 792
Read events
2 583
Write events
198
Delete events
11
Modification events
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1247888250 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30789875 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A0000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
524
Text files
378
Unknown types
144
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab15F3.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar15F4.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\en[1].htm | html | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\ACF244F1A10D4DBED0D88EBA0C43A9B5_BA1AB6C2BDFDF57799E8116E4002D001 | binary | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\ACF244F1A10D4DBED0D88EBA0C43A9B5_BA1AB6C2BDFDF57799E8116E4002D001 | der | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\N9O80UIU.txt | text | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5457A8CE4B2A7499F8299A013B6E1C7C_CBB16B7A61CE4E298043181730D3CE9B | der | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5457A8CE4B2A7499F8299A013B6E1C7C_CBB16B7A61CE4E298043181730D3CE9B | binary | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\application-8f1cdb00e0d13e3df5b43b44c7f2f38508f2e31a10748a5e4e3460ffe76cdc44[1].js | text | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
203
TCP/UDP connections
312
DNS requests
661
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | iexplore.exe | GET | 301 | 138.201.57.222:80 | http://browsec.com/ | DE | — | — | whitelisted |
3896 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8DYx | US | der | 1.49 Kb | whitelisted |
3896 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEQDF6c2xYT%2F0tw3xvWWvIqbt | US | der | 472 b | whitelisted |
3896 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1168 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1168 | chrome.exe | 172.217.23.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2236 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3896 | iexplore.exe | 138.201.57.222:80 | browsec.com | Hetzner Online GmbH | DE | unknown |
3896 | iexplore.exe | 138.201.57.222:443 | browsec.com | Hetzner Online GmbH | DE | unknown |
3896 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
3896 | iexplore.exe | 104.20.59.238:443 | cdn.paddle.com | Cloudflare Inc | US | shared |
3896 | iexplore.exe | 172.217.18.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3896 | iexplore.exe | 104.18.74.113:443 | static.zdassets.com | Cloudflare Inc | US | shared |
3896 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
browsec.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
cdn.paddle.com |
| whitelisted |
static.zdassets.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ekr.zdassets.com |
| shared |
browsec.zendesk.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
widget-mediator.zopim.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
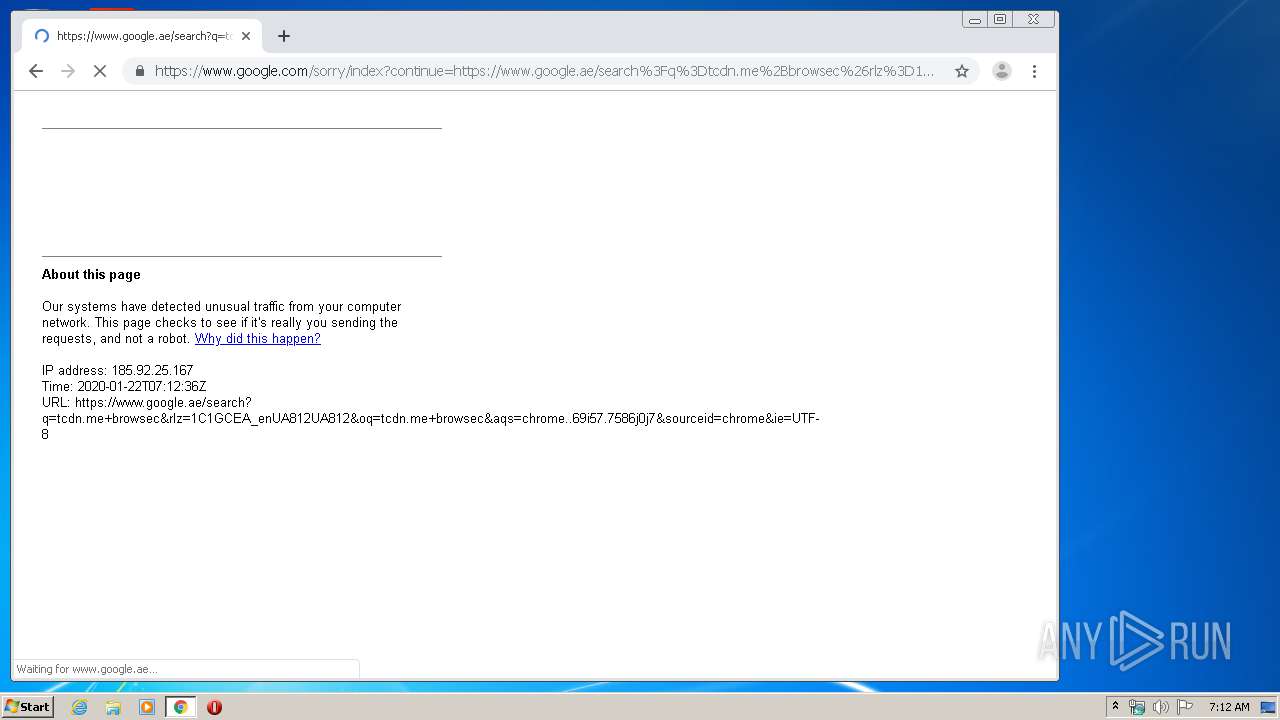
1120 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1120 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
2712 | firefox.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2712 | firefox.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2712 | firefox.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2712 | firefox.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |