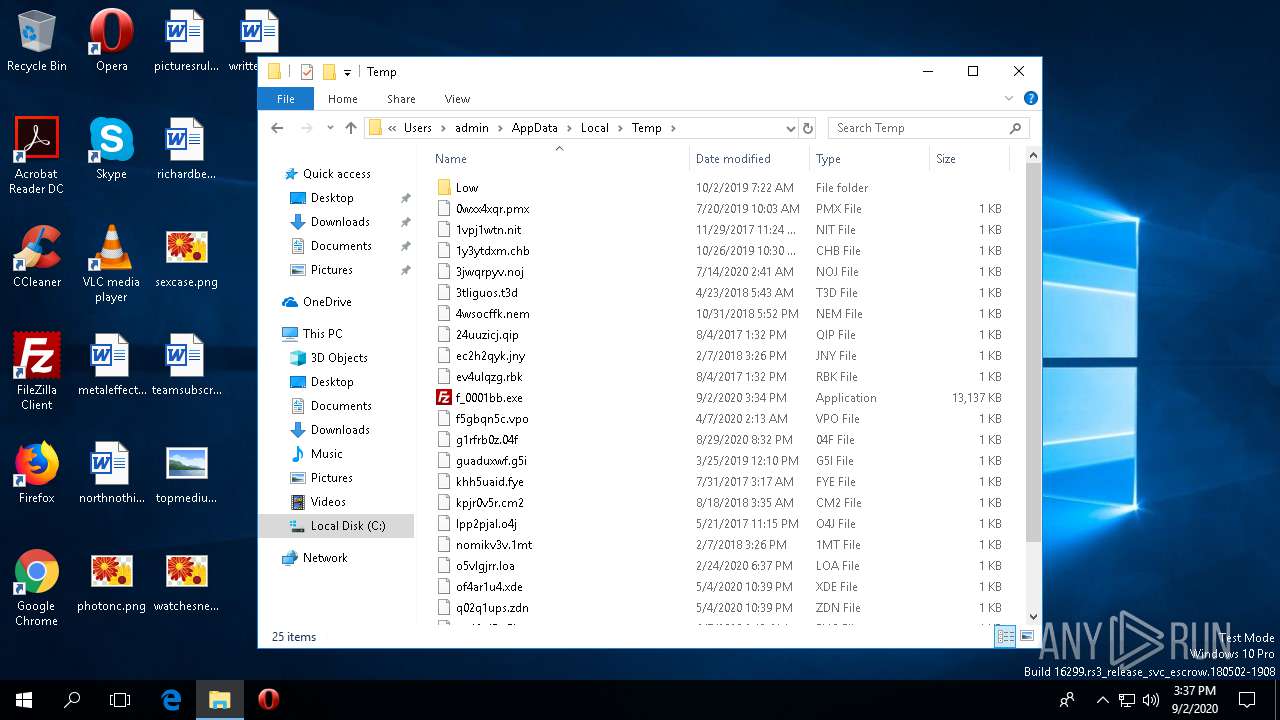
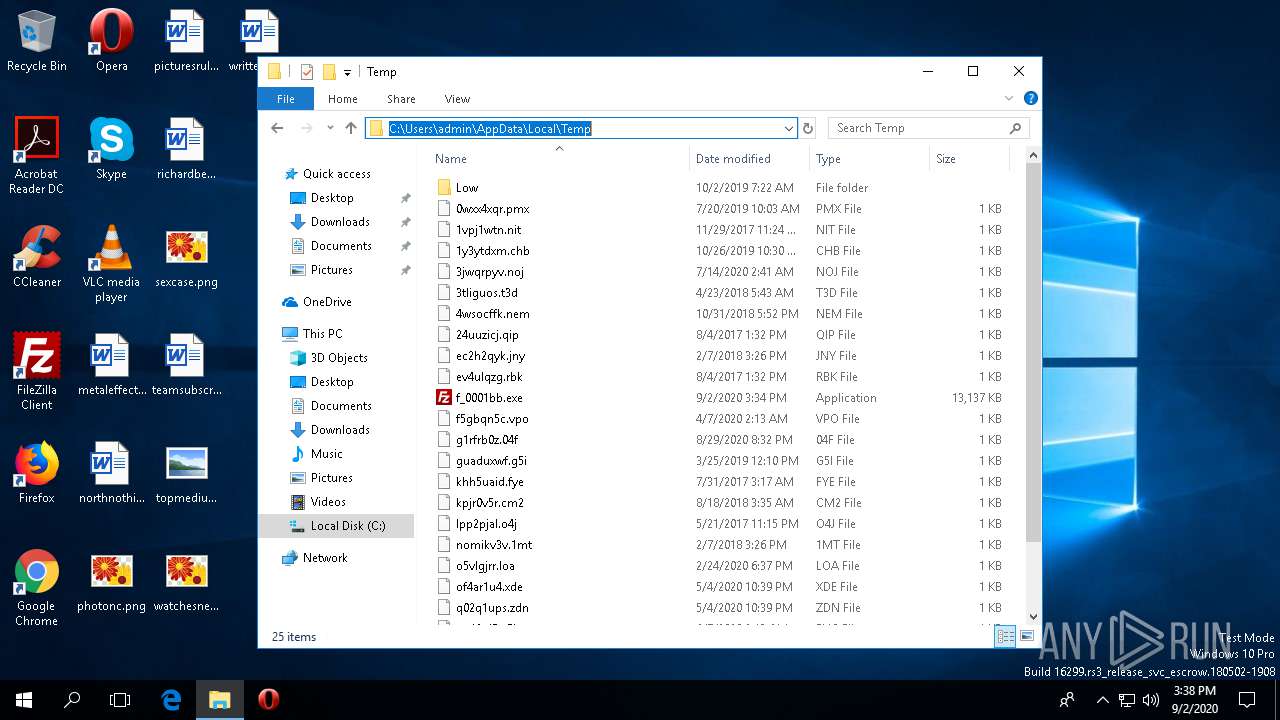
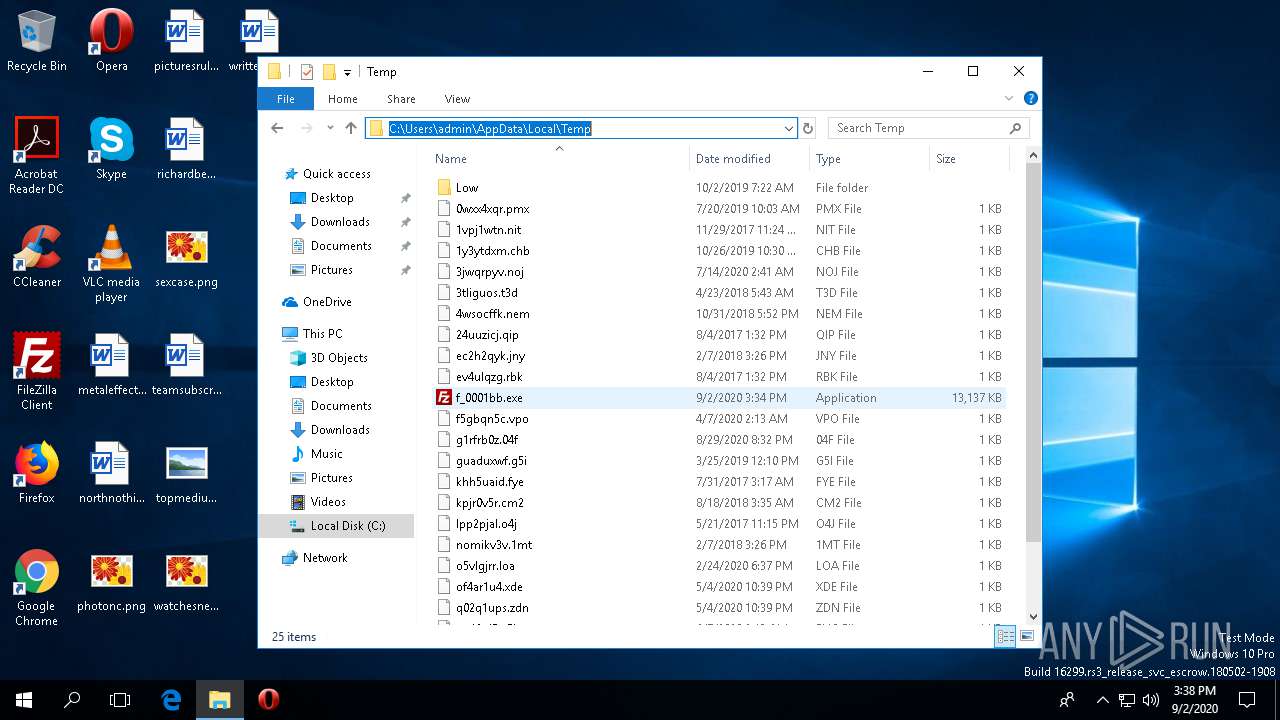
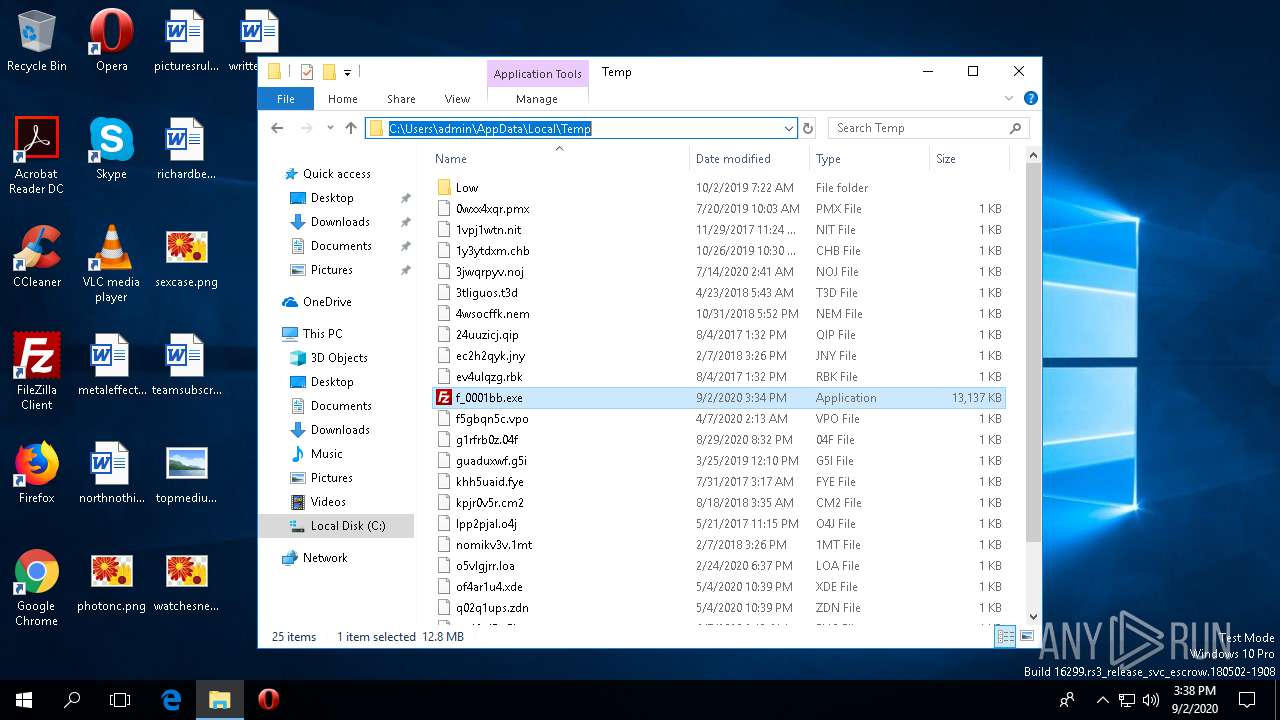
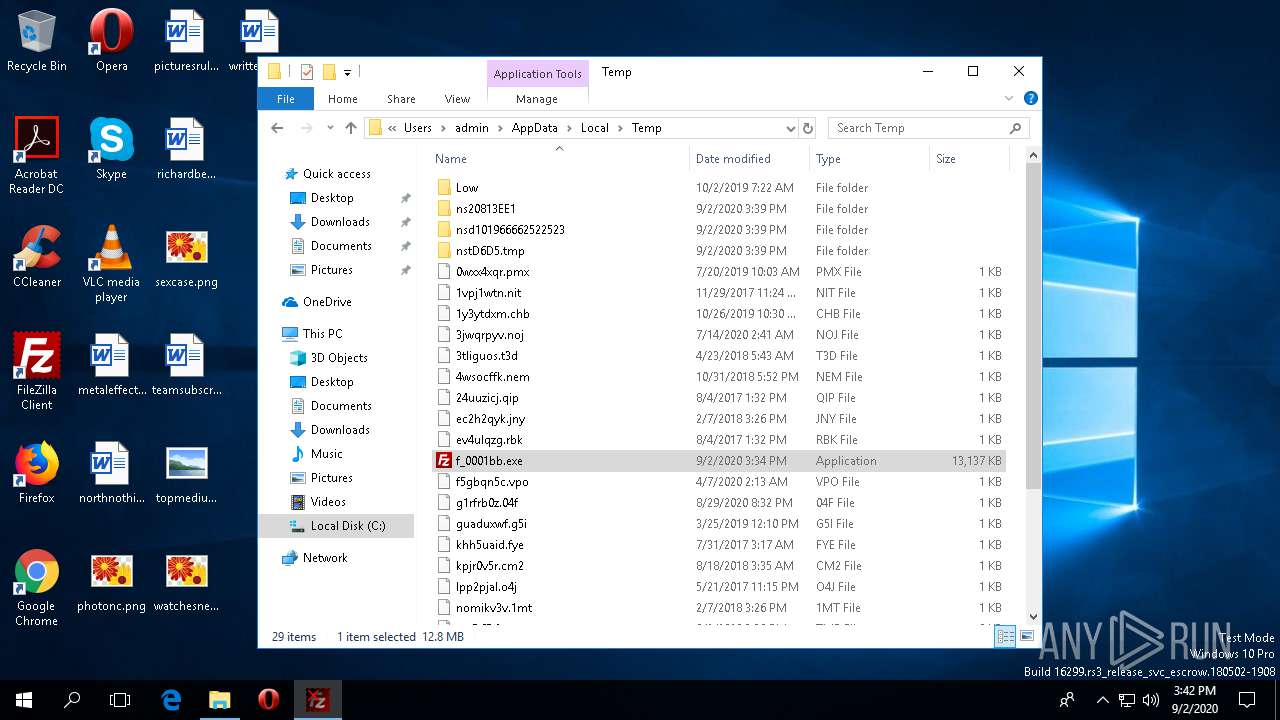
| File name: | f_0001bb |
| Full analysis: | https://app.any.run/tasks/c07be996-24bc-413e-8742-7707e914415a |
| Verdict: | Malicious activity |
| Analysis date: | September 02, 2020, 15:34:26 |
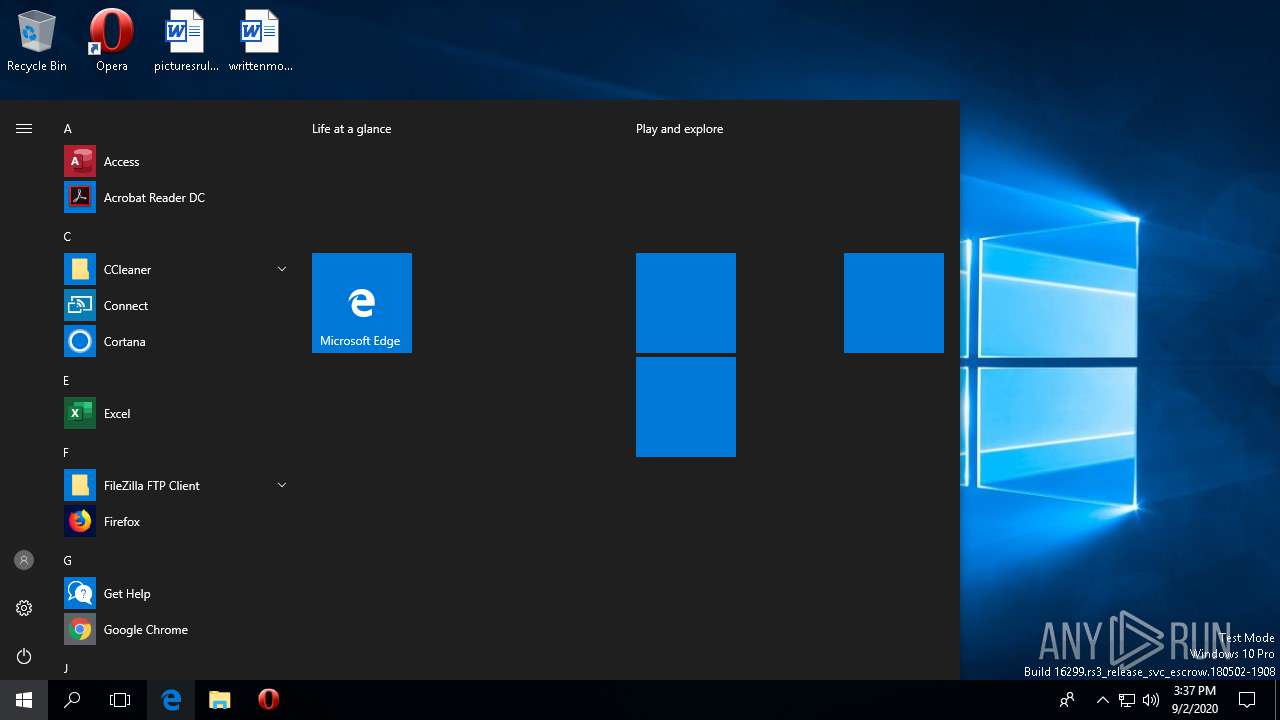
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 731E32035ECFB985B927771DB212C9F2 |
| SHA1: | FD6A107F7BA64396A9B955D56921FEA1E35C11CC |
| SHA256: | 6A9F568C8FD5FDB3D7F72829BCE7BDDE0117D5395AC9890F6EA45EAC4C9DB315 |
| SSDEEP: | 196608:4I3Lv0/lBHmKct/9WACHcCOxL3vrRTKrlheLcfy5jwv613/BnU3vP91rAYkNO7rh:4I7AmKcHWXcL1TK7u0ypwE3pYNwNOh |
MALICIOUS
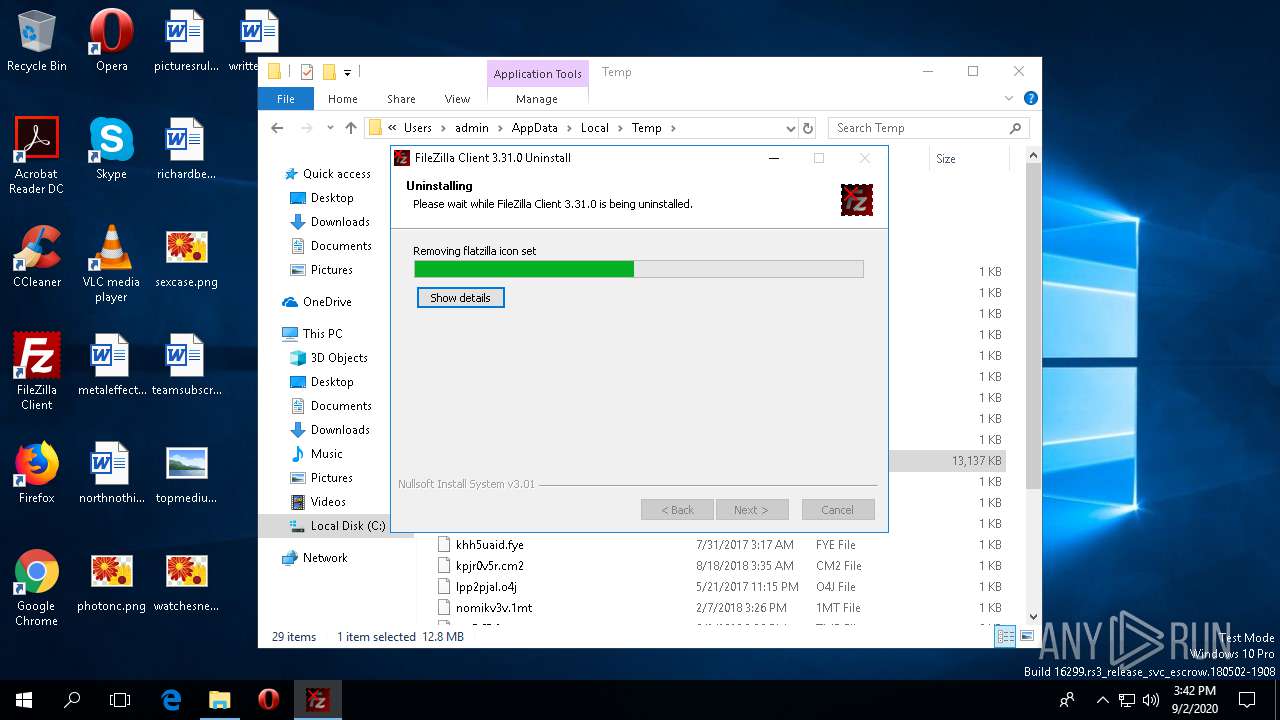
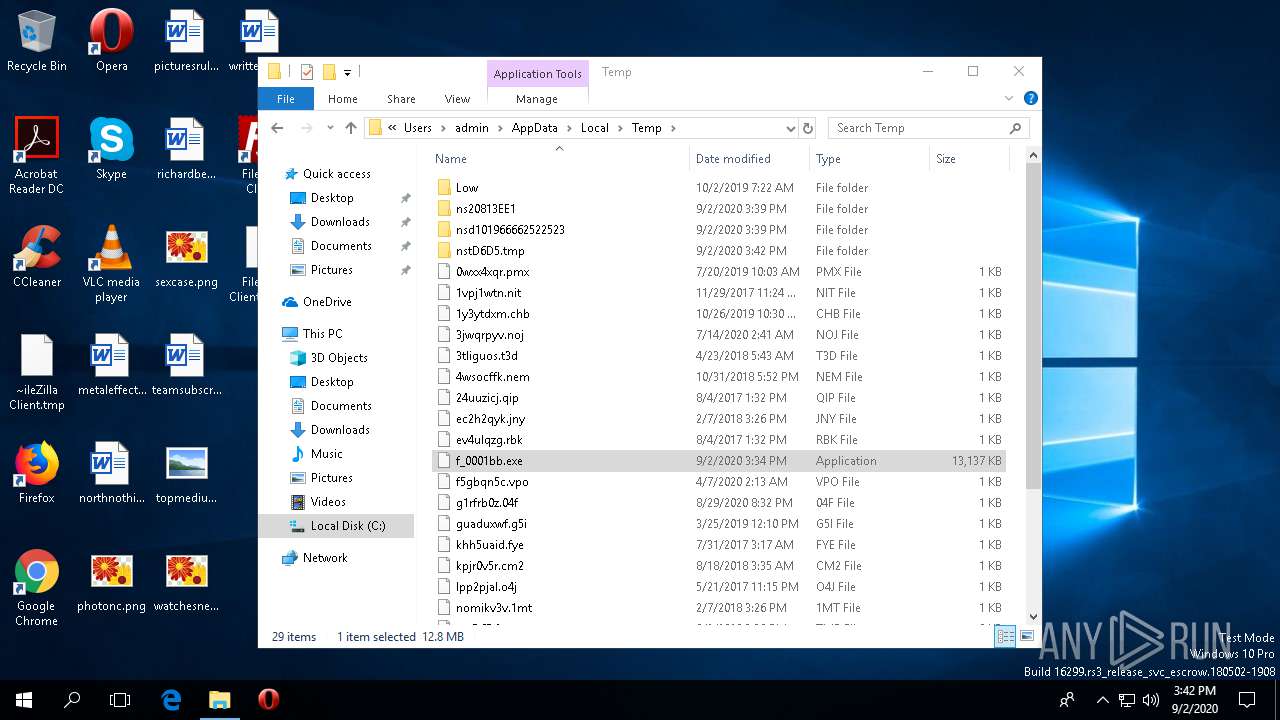
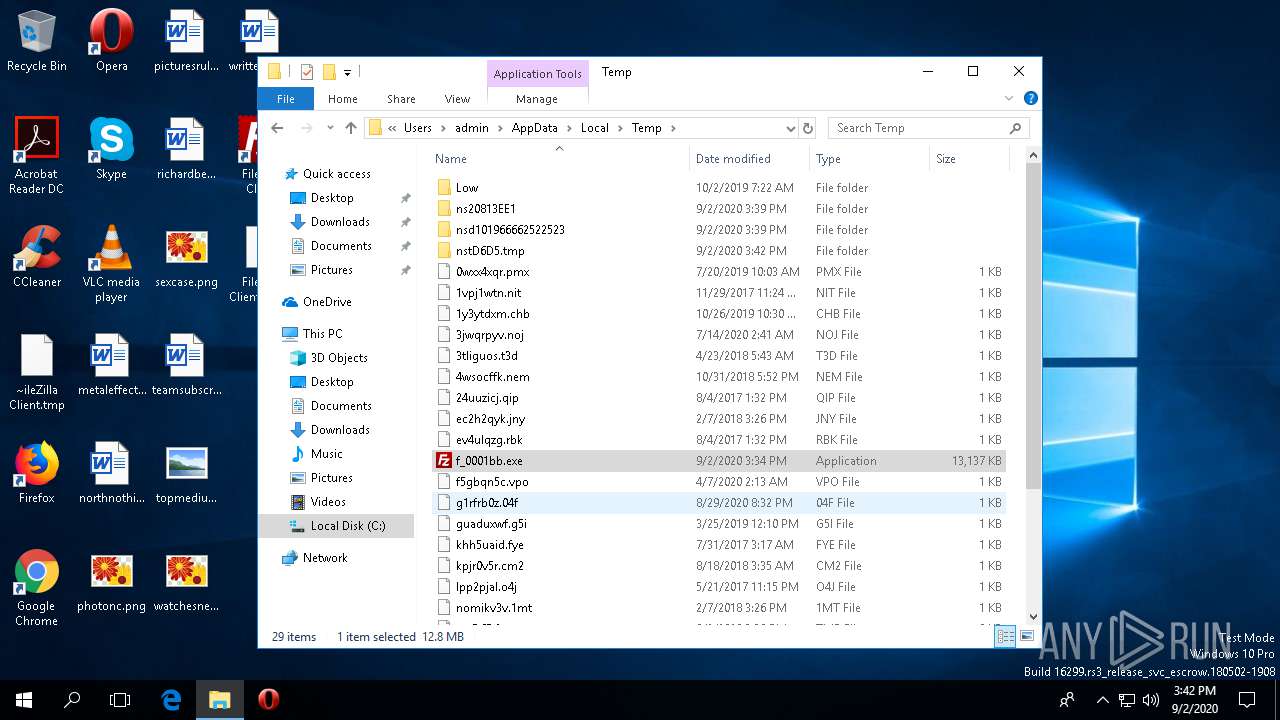
Loads dropped or rewritten executable
- f_0001bb.exe (PID: 2520)
- f_0001bb.exe (PID: 1968)
- filezilla.exe (PID: 2348)
- regsvr32.exe (PID: 4308)
- uninstall.exe (PID: 1872)
Registers / Runs the DLL via REGSVR32.EXE
- f_0001bb.exe (PID: 1968)
- uninstall.exe (PID: 1872)
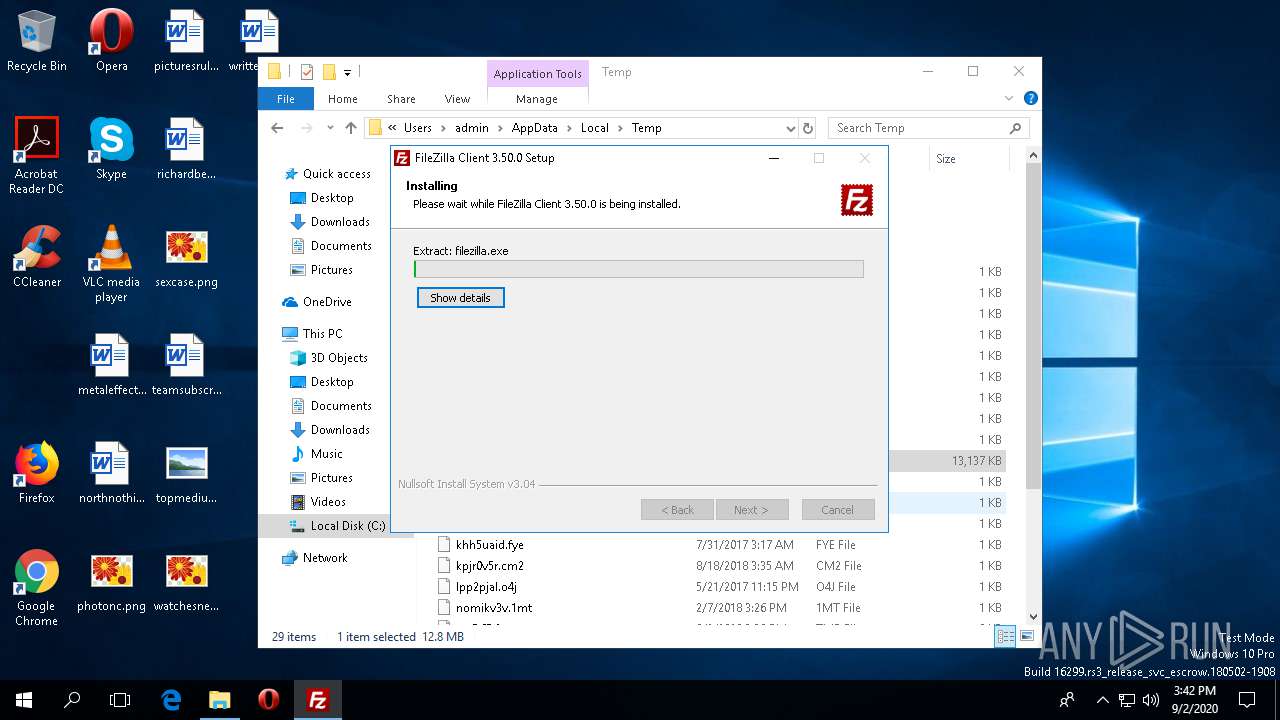
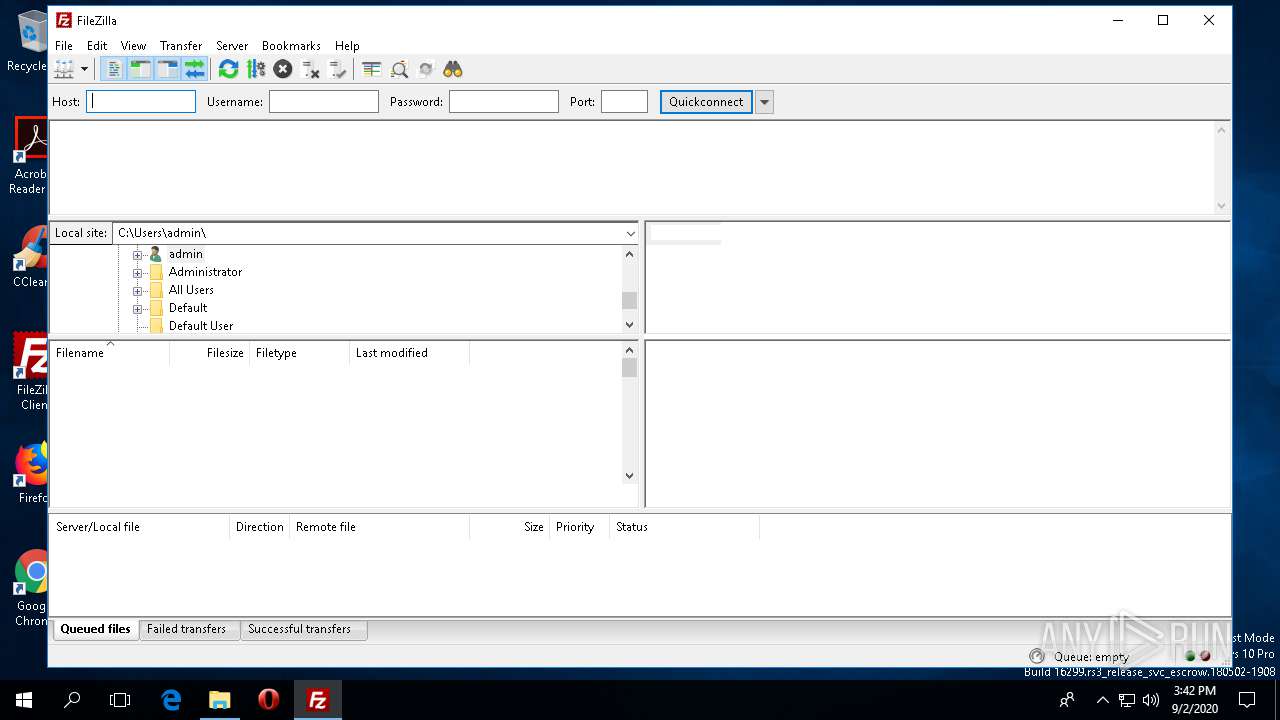
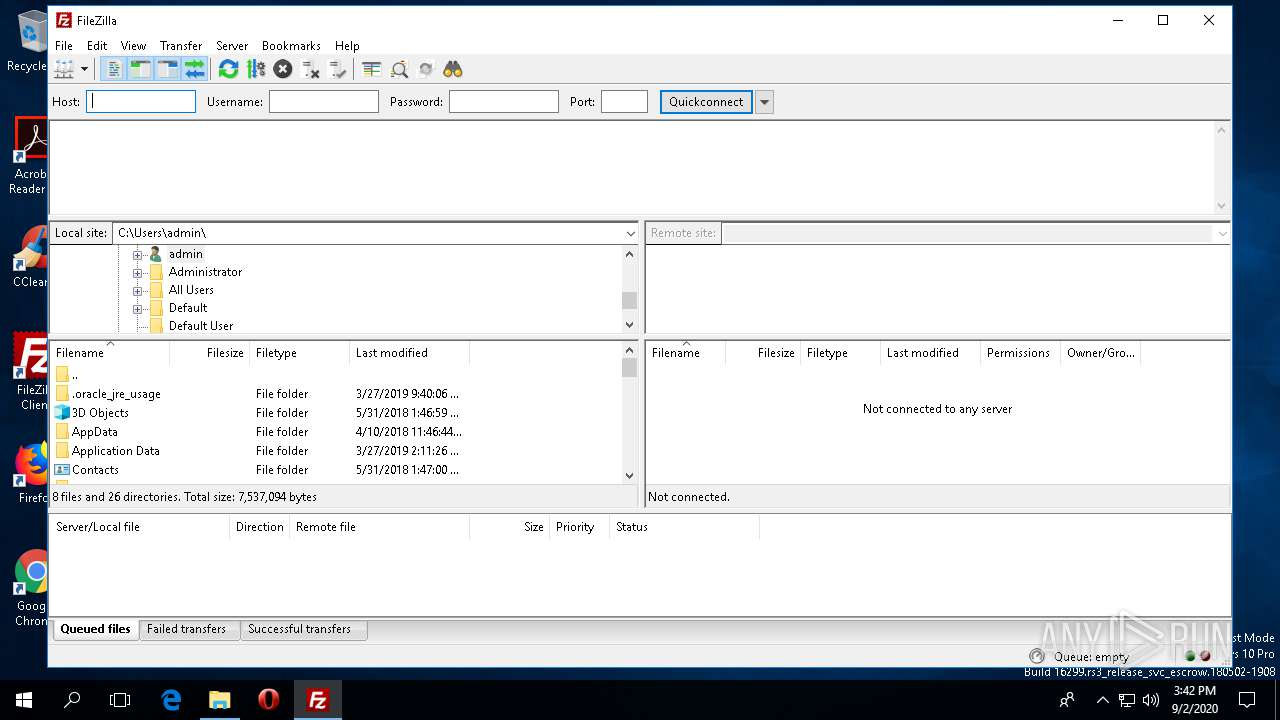
Application was dropped or rewritten from another process
- filezilla.exe (PID: 2348)
Actions looks like stealing of personal data
- f_0001bb.exe (PID: 1968)
SUSPICIOUS
Creates a software uninstall entry
- f_0001bb.exe (PID: 1968)
Executed via COM
- DllHost.exe (PID: 3820)
- DllHost.exe (PID: 5068)
- rundll32.exe (PID: 2076)
Executable content was dropped or overwritten
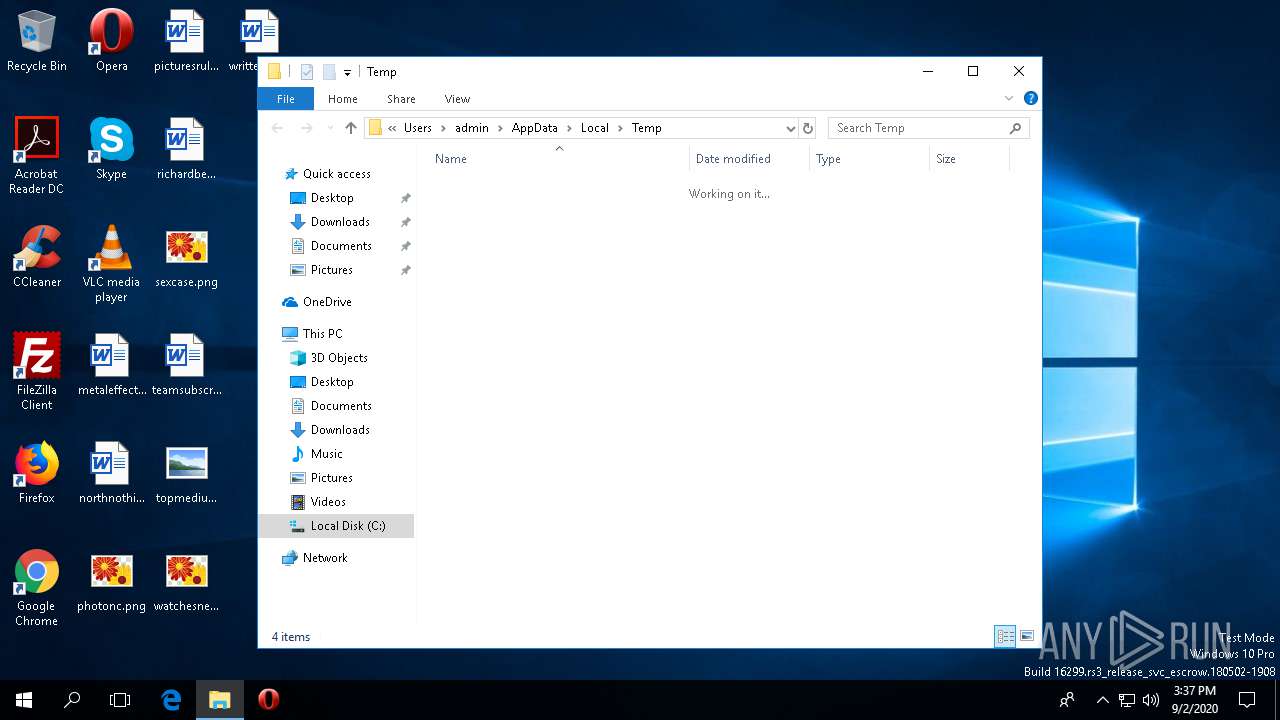
- f_0001bb.exe (PID: 2520)
- f_0001bb.exe (PID: 1968)
- uninstall.exe (PID: 1872)
Reads Environment values
- f_0001bb.exe (PID: 1968)
Reads internet explorer settings
- f_0001bb.exe (PID: 1968)
Reads the machine GUID from the registry
- f_0001bb.exe (PID: 1968)
- filezilla.exe (PID: 2348)
Creates COM task schedule object
- regsvr32.exe (PID: 4308)
- f_0001bb.exe (PID: 1968)
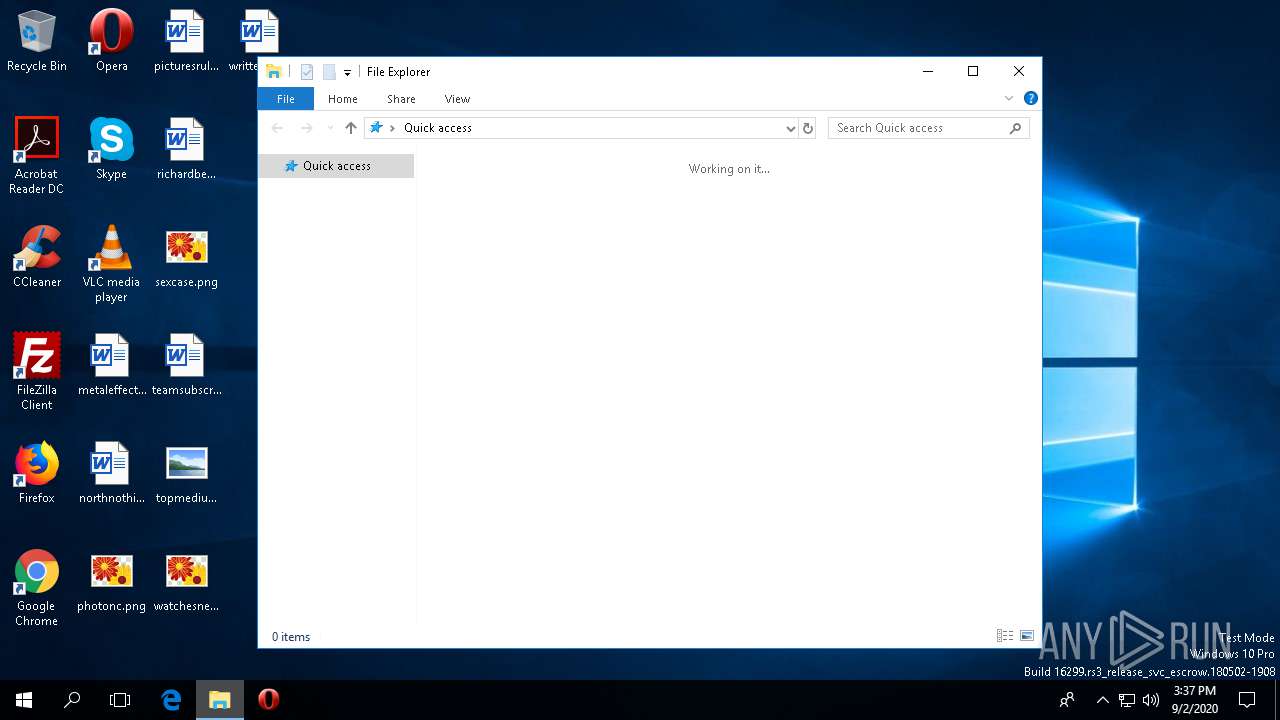
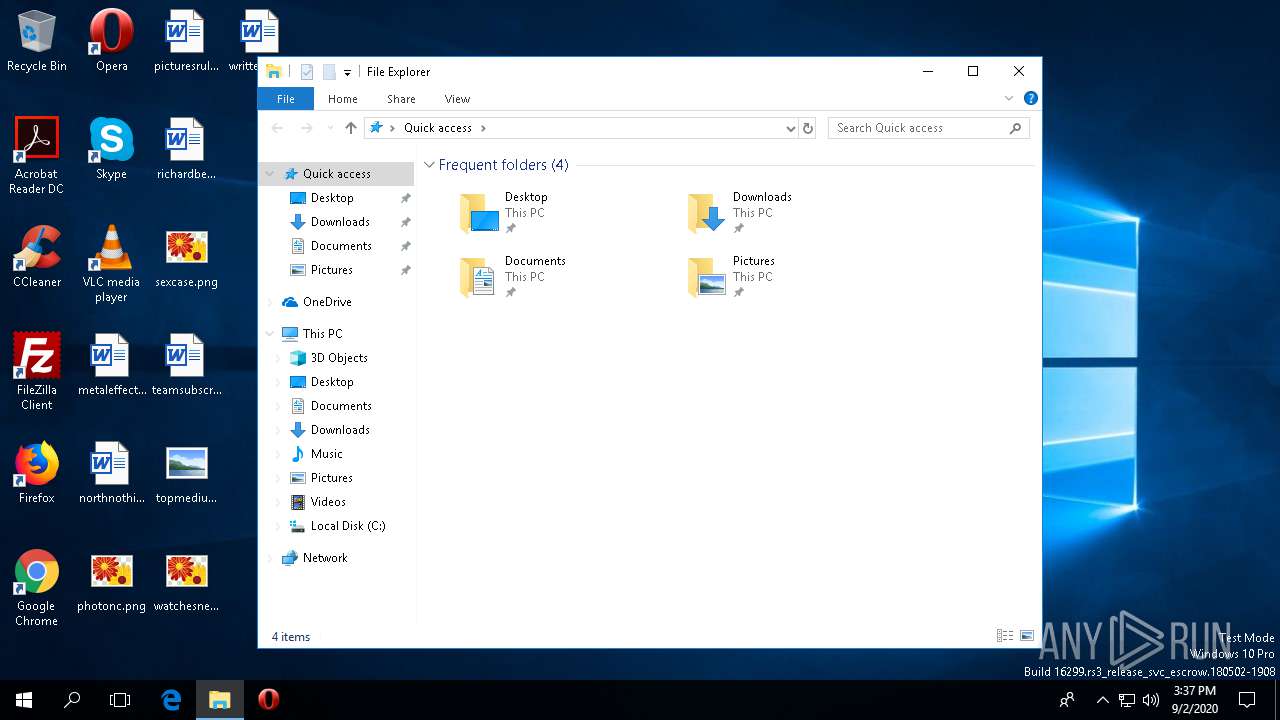
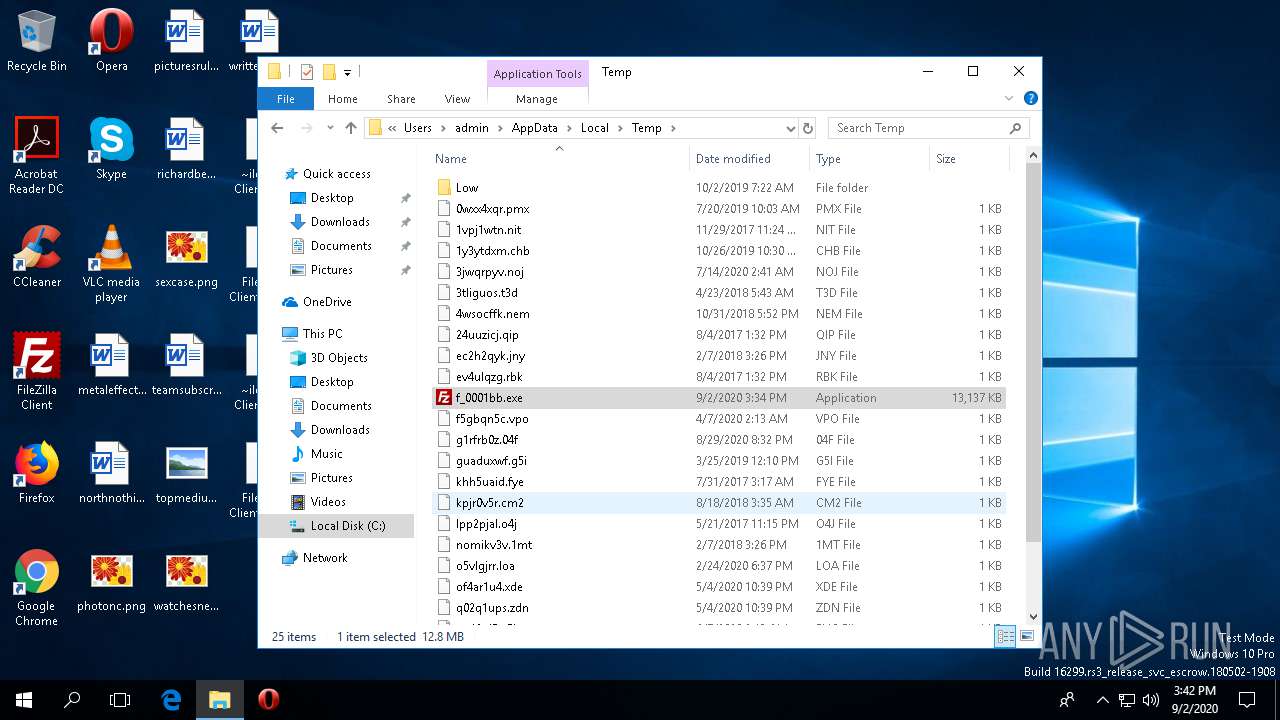
Creates files in the user directory
- filezilla.exe (PID: 2348)
Creates files in the program directory
- f_0001bb.exe (PID: 1968)
INFO
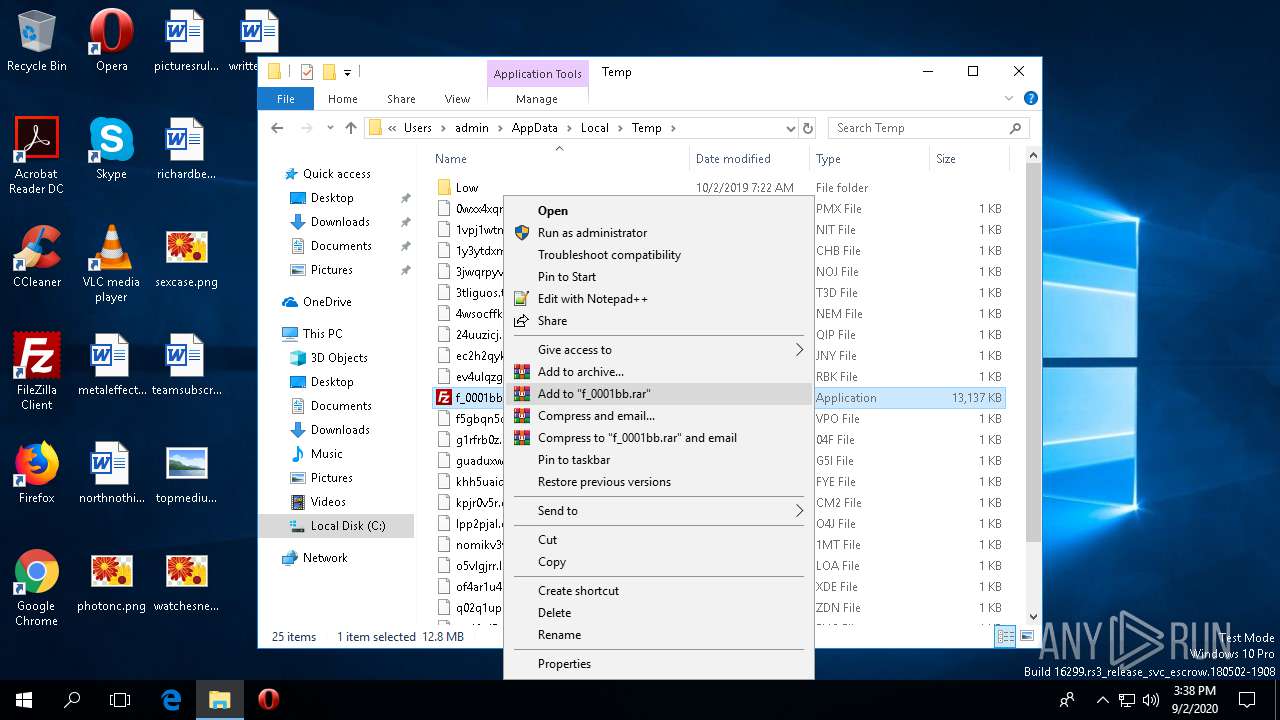
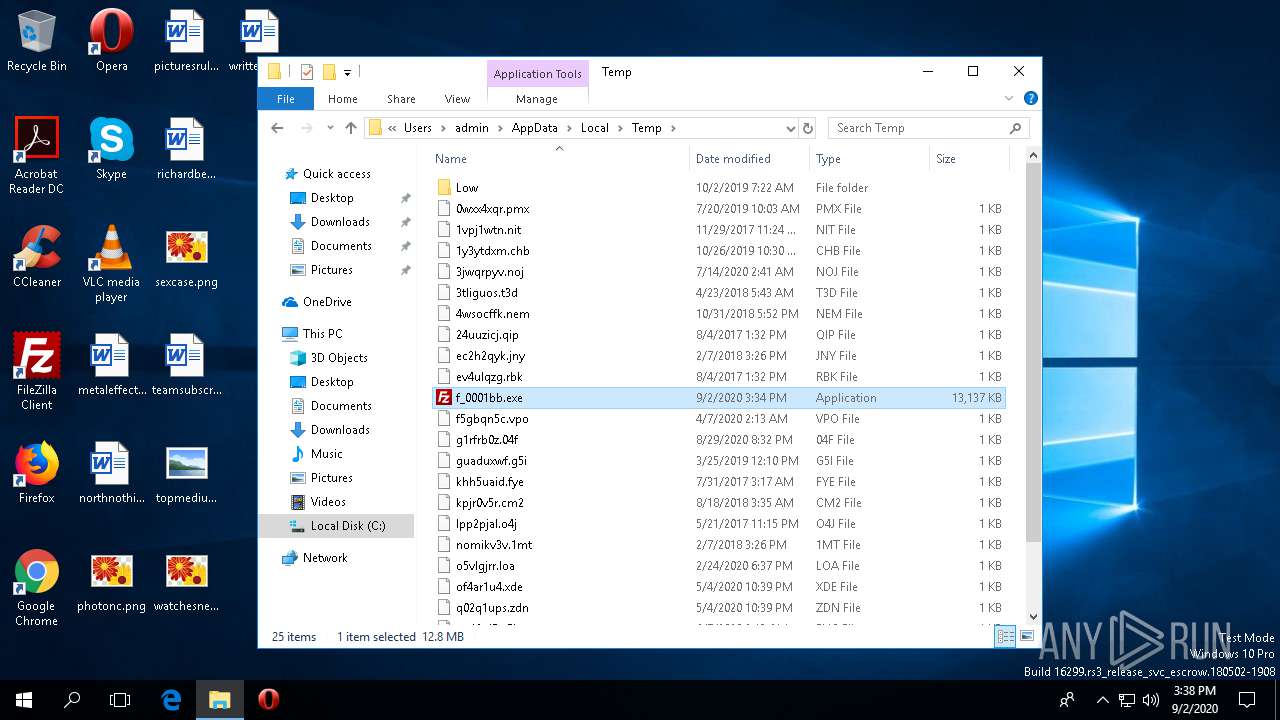
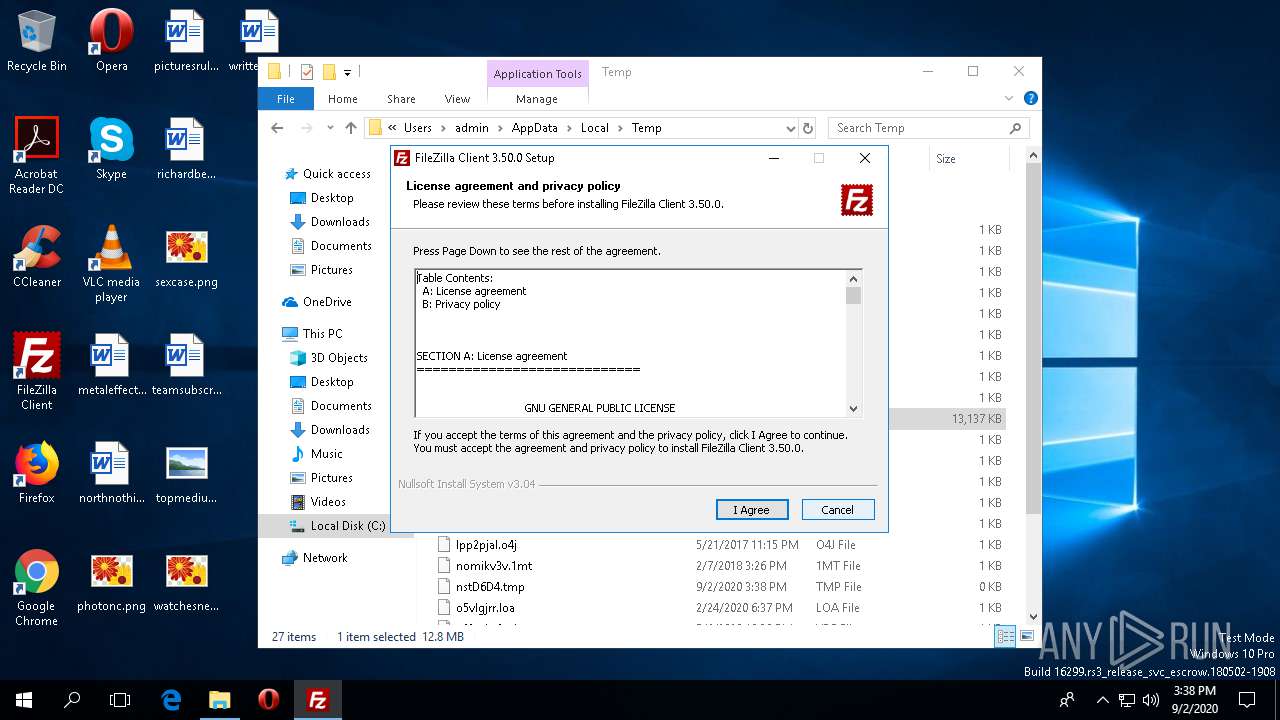
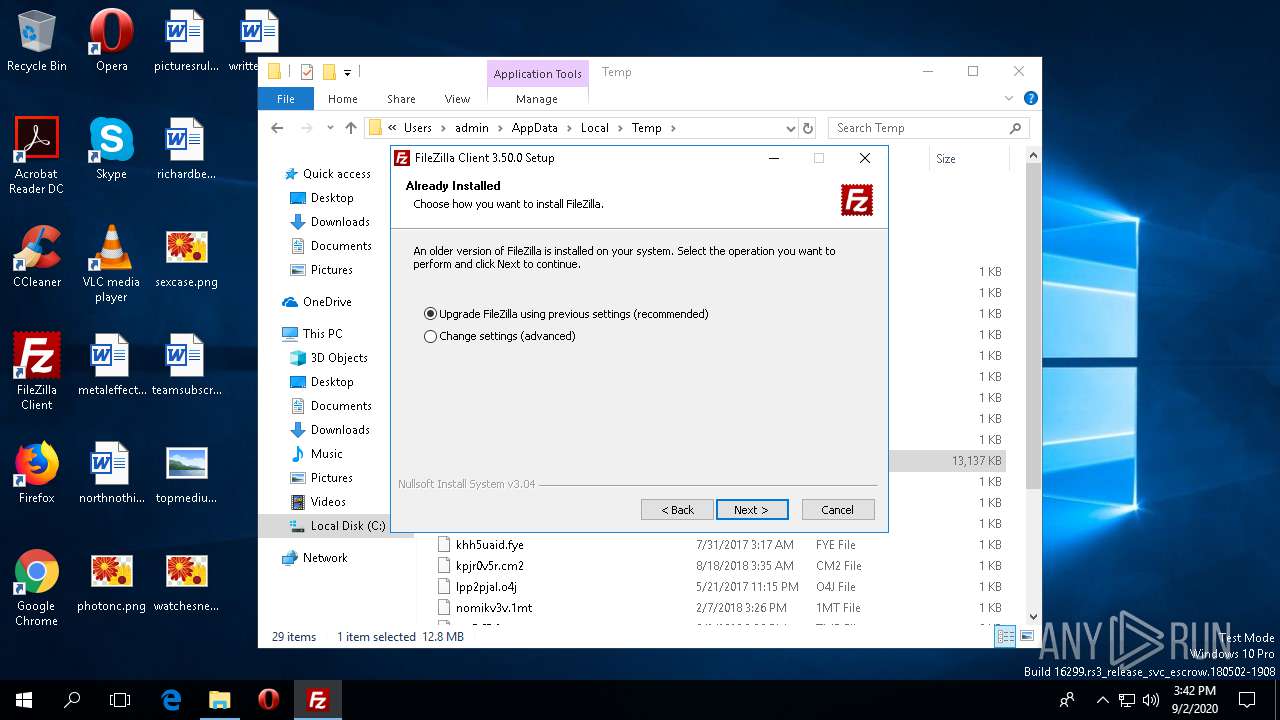
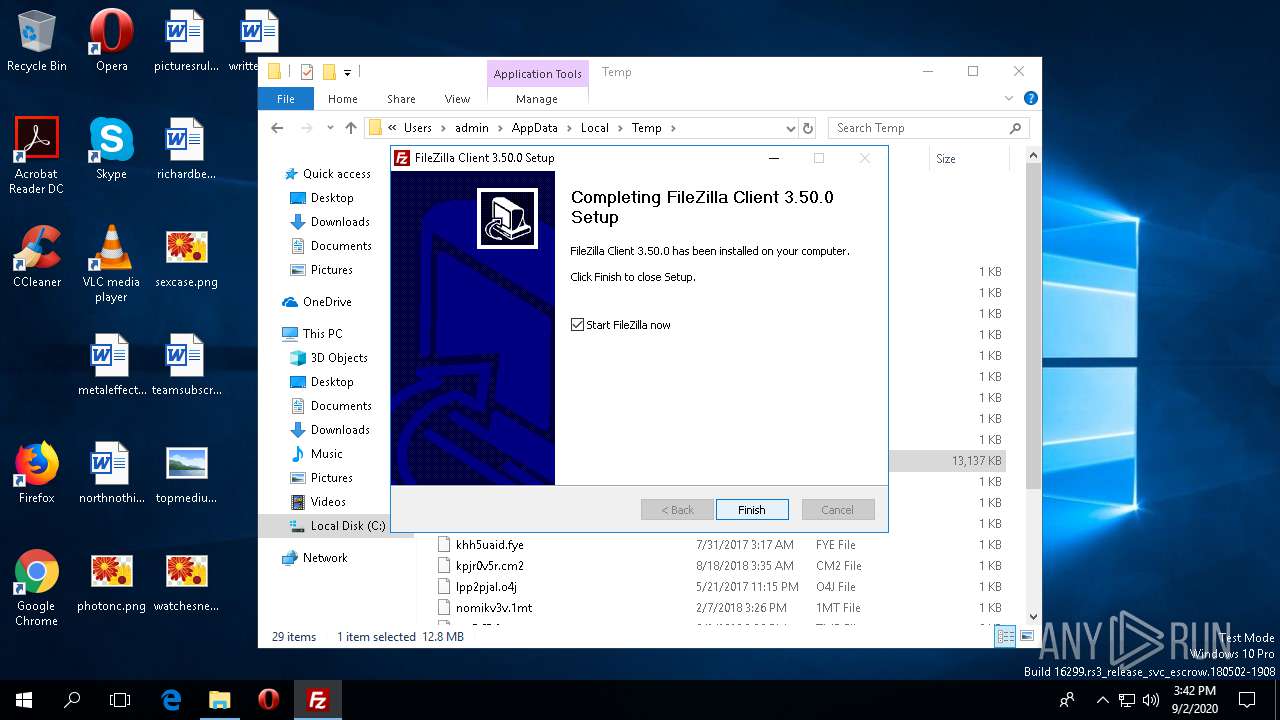
Manual execution by user
- f_0001bb.exe (PID: 1968)
Reads settings of System Certificates
- filezilla.exe (PID: 2348)
Dropped object may contain Bitcoin addresses
- f_0001bb.exe (PID: 1968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x34a5 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
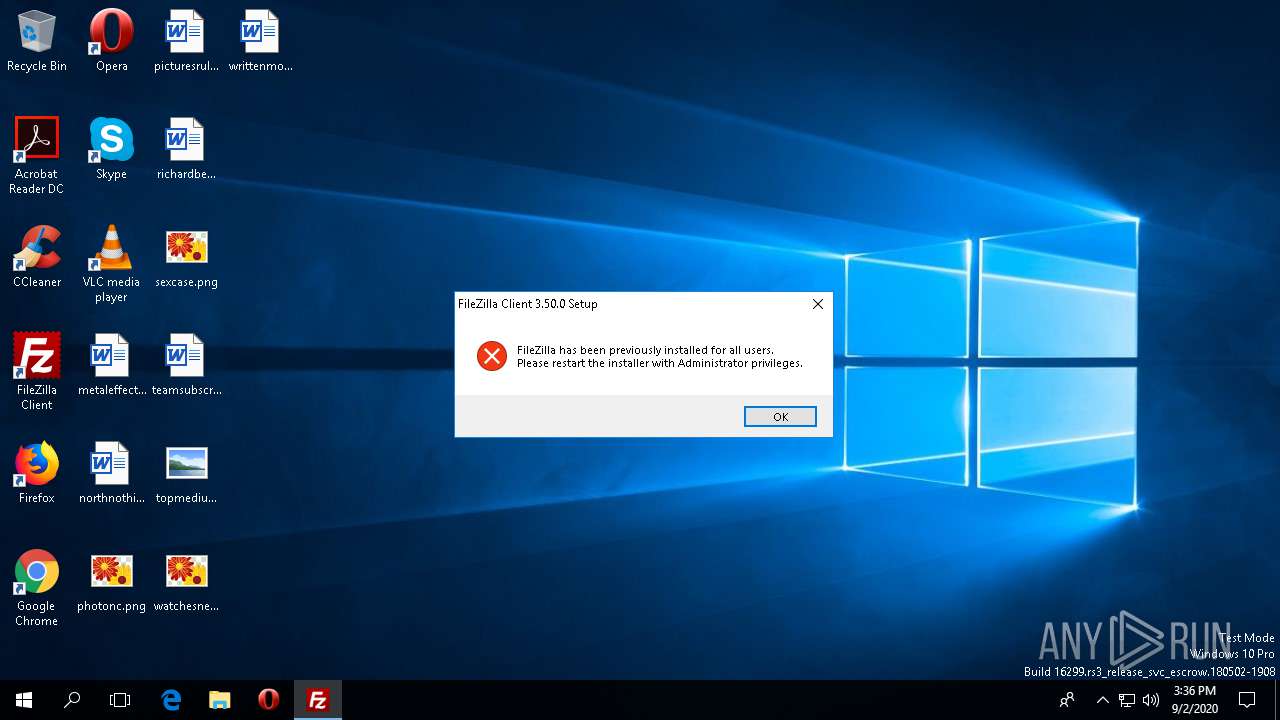
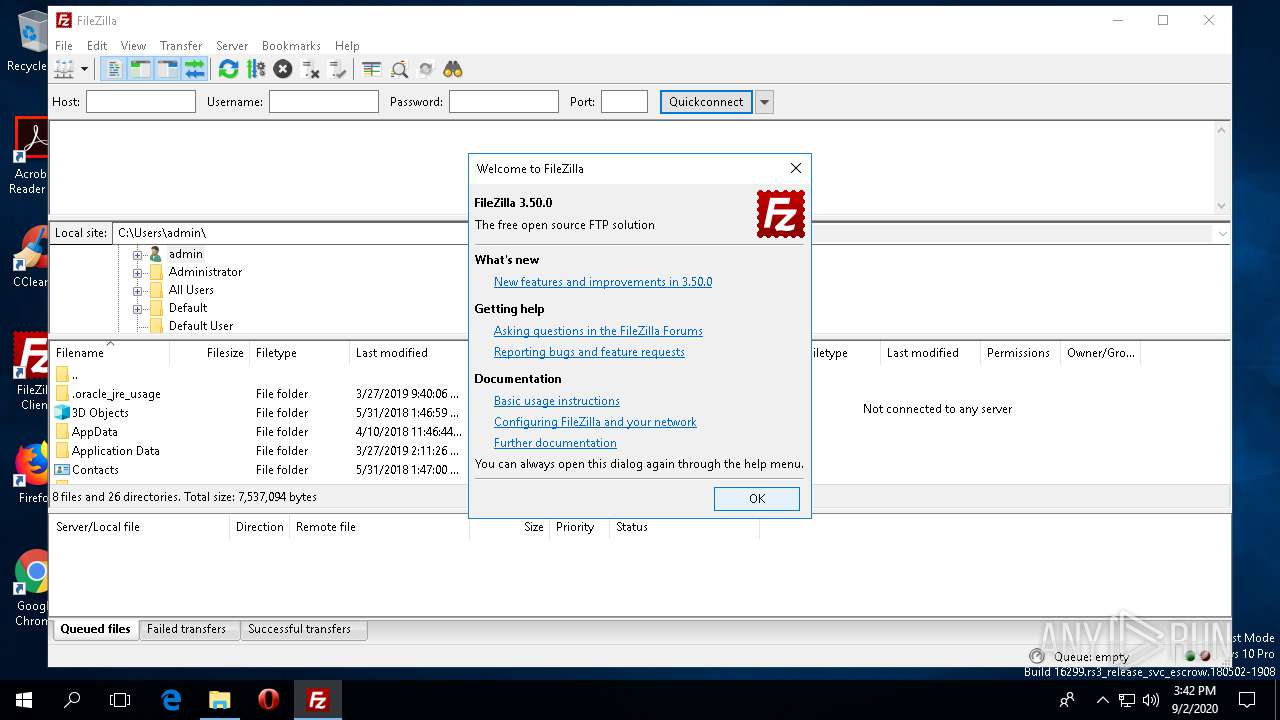
| FileVersionNumber: | 3.50.0.0 |
| ProductVersionNumber: | 3.50.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Tim Kosse |
| FileDescription: | FileZilla FTP Client |
| FileVersion: | 3.50.0 |
| LegalCopyright: | Tim Kosse |
| OriginalFileName: | FileZilla_3.50.0_win32-setup.exe |
| ProductName: | FileZilla |
| ProductVersion: | 3.50.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:36 |
| Detected languages: |
|
| CompanyName: | Tim Kosse |
| FileDescription: | FileZilla FTP Client |
| FileVersion: | 3.50.0 |
| LegalCopyright: | Tim Kosse |
| OriginalFilename: | FileZilla_3.50.0_win32-setup.exe |
| ProductName: | FileZilla |
| ProductVersion: | 3.50.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006409 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41619 |
.rdata | 0x00008000 | 0x00001396 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15491 |
.data | 0x0000A000 | 0x00020358 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0044 |
.ndata | 0x0002B000 | 0x00040000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0006B000 | 0x0000A3A0 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.57303 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29611 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.69314 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.16834 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.66044 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.91531 | 1384 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.63186 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70411 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
106
Monitored processes
9
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\WINDOWS\system32\regsvr32.exe" /s /u "C:\Program Files (x86)\FileZilla FTP Client\fzshellext_64.dll" | C:\WINDOWS\system32\regsvr32.exe | — | uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1872 | "C:\Program Files (x86)\FileZilla FTP Client\uninstall.exe" /frominstall /keepstartmenudir _?=C:\Program Files (x86)\FileZilla FTP Client | C:\Program Files (x86)\FileZilla FTP Client\uninstall.exe | f_0001bb.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3.31.0 Modules
| |||||||||||||||
| 1968 | "C:\Users\admin\AppData\Local\Temp\f_0001bb.exe" | C:\Users\admin\AppData\Local\Temp\f_0001bb.exe | explorer.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3.50.0 Modules
| |||||||||||||||
| 2076 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\WINDOWS\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | "C:\Program Files (x86)\FileZilla FTP Client\filezilla.exe" | C:\Program Files (x86)\FileZilla FTP Client\filezilla.exe | — | f_0001bb.exe | |||||||||||
User: admin Company: FileZilla Project Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3, 50, 0, 0 Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Local\Temp\f_0001bb.exe" | C:\Users\admin\AppData\Local\Temp\f_0001bb.exe | explorer.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: MEDIUM Description: FileZilla FTP Client Exit code: 2 Version: 3.50.0 Modules
| |||||||||||||||
| 3820 | C:\WINDOWS\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F} | C:\WINDOWS\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4308 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\FileZilla FTP Client\fzshellext_64.dll" | C:\WINDOWS\system32\regsvr32.exe | — | f_0001bb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5068 | C:\WINDOWS\system32\DllHost.exe /Processid:{7966B4D8-4FDC-4126-A10B-39A3209AD251} | C:\WINDOWS\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 484
Read events
1 379
Write events
83
Delete events
22
Modification events
| (PID) Process: | (1968) f_0001bb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1968) f_0001bb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1968) f_0001bb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1968) f_0001bb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1968) f_0001bb.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\19c\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1968) f_0001bb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1968) f_0001bb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1968) f_0001bb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1872) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Directory\shellex\CopyHookHandlers\FileZilla3CopyHook |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1872) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{DB70412E-EEC9-479C-BBA9-BE36BFDDA41B}\InProcServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
33
Suspicious files
120
Text files
791
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2520 | f_0001bb.exe | C:\Users\admin\AppData\Local\Temp\nsh8B34.tmp | — | |
MD5:— | SHA256:— | |||
| 3820 | DllHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\AppData\Indexed DB\IndexedDB.edb | — | |
MD5:— | SHA256:— | |||
| 3820 | DllHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\AppData\Indexed DB\IndexedDB.jfm | — | |
MD5:— | SHA256:— | |||
| 3820 | DllHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\AppData\Indexed DB\edb.log | — | |
MD5:— | SHA256:— | |||
| 1968 | f_0001bb.exe | C:\Users\admin\AppData\Local\Temp\3CC6E0C1.log | — | |
MD5:— | SHA256:— | |||
| 3820 | DllHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\AppData\Indexed DB\edb.chk | binary | |
MD5:— | SHA256:— | |||
| 1968 | f_0001bb.exe | C:\Users\admin\AppData\Local\Temp\nstD6D5.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
| 2520 | f_0001bb.exe | C:\Users\admin\AppData\Local\Temp\nsw8B44.tmp\UserInfo.dll | executable | |
MD5:9EB662F3B5FBDA28BFFE020E0AB40519 | SHA256:9AA388C7DE8E96885ADCB4325AF871B470AC50EDB60D4B0D876AD43F5332FFD1 | |||
| 2520 | f_0001bb.exe | C:\Users\admin\AppData\Local\Temp\nsw8B44.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 2520 | f_0001bb.exe | C:\Users\admin\AppData\Local\Temp\nsw8B44.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
12
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1968 | f_0001bb.exe | GET | 200 | 13.227.150.65:80 | http://cloud.nitehe-nutete.com/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1968 | f_0001bb.exe | 49.12.121.47:443 | offers.filezilla-project.org | — | IN | suspicious |
1968 | f_0001bb.exe | 13.227.150.93:443 | remote.nitehe-nutete.com | — | US | unknown |
1968 | f_0001bb.exe | 13.227.150.65:80 | cloud.nitehe-nutete.com | — | US | unknown |
1968 | f_0001bb.exe | 13.227.150.38:443 | ww1.nitehe-nutete.com | — | US | unknown |
2584 | svchost.exe | 20.191.48.196:443 | settings-win-ppe.data.microsoft.com | Microsoft Corporation | US | unknown |
1968 | f_0001bb.exe | 13.227.150.65:443 | cloud.nitehe-nutete.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
nexusrules.officeapps.live.com |
| whitelisted |
offers.filezilla-project.org |
| whitelisted |
cloud.nitehe-nutete.com |
| whitelisted |
remote.nitehe-nutete.com |
| shared |
ww1.nitehe-nutete.com |
| shared |
settings-win-ppe.data.microsoft.com |
| whitelisted |