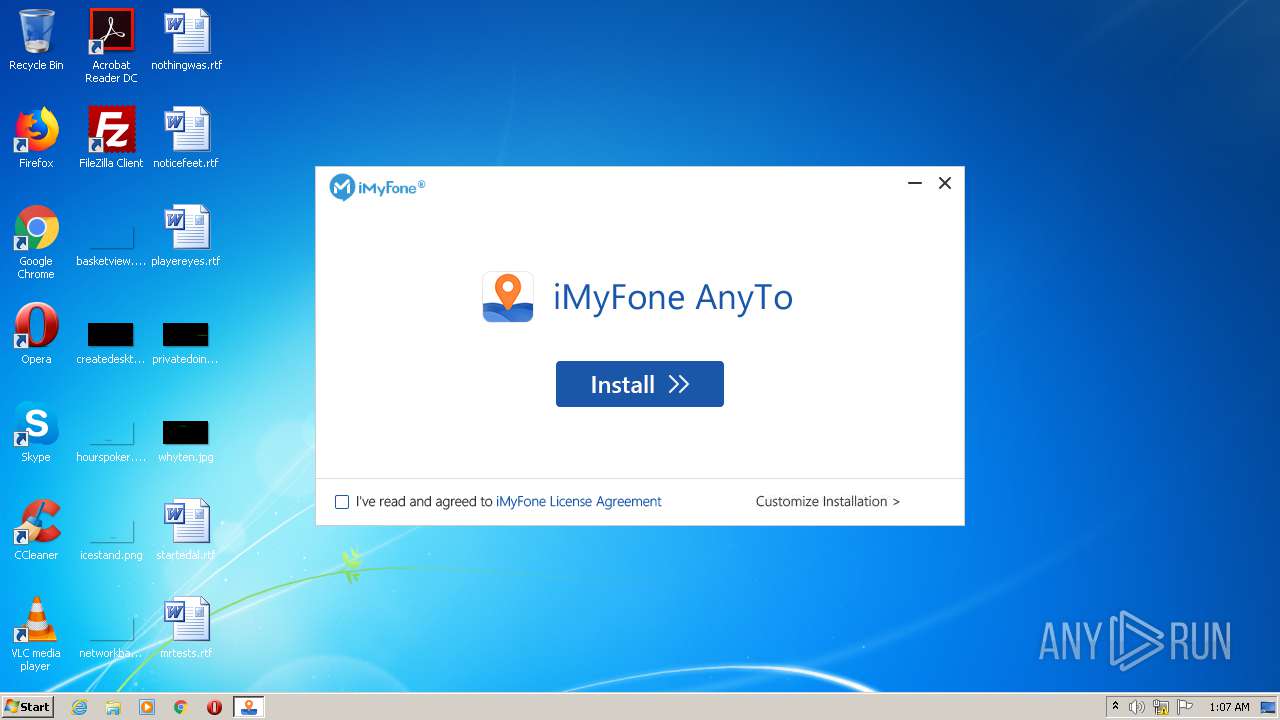
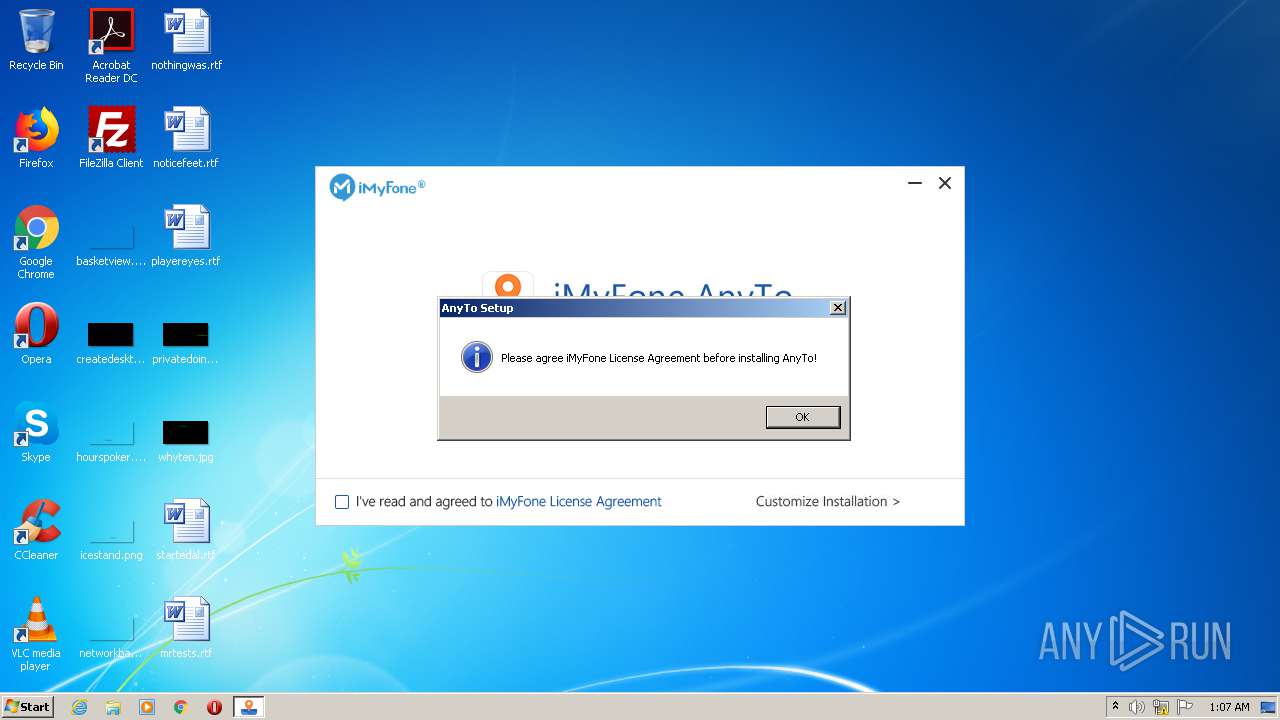
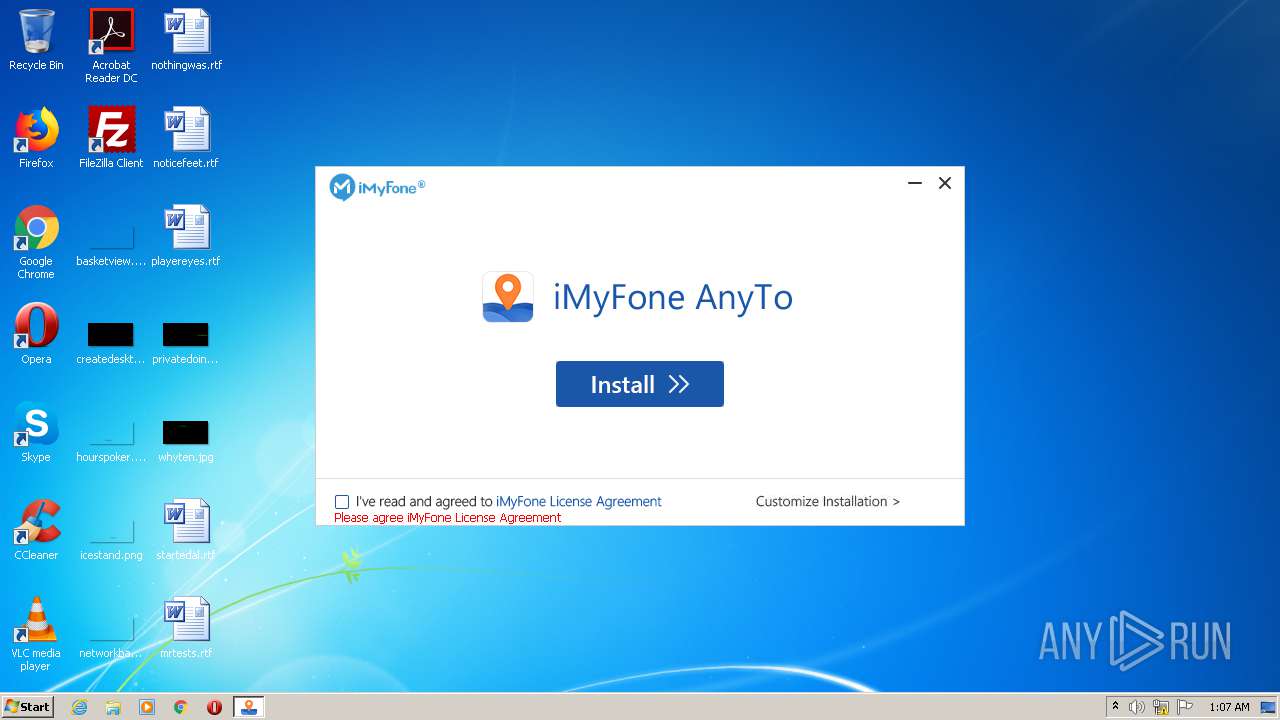
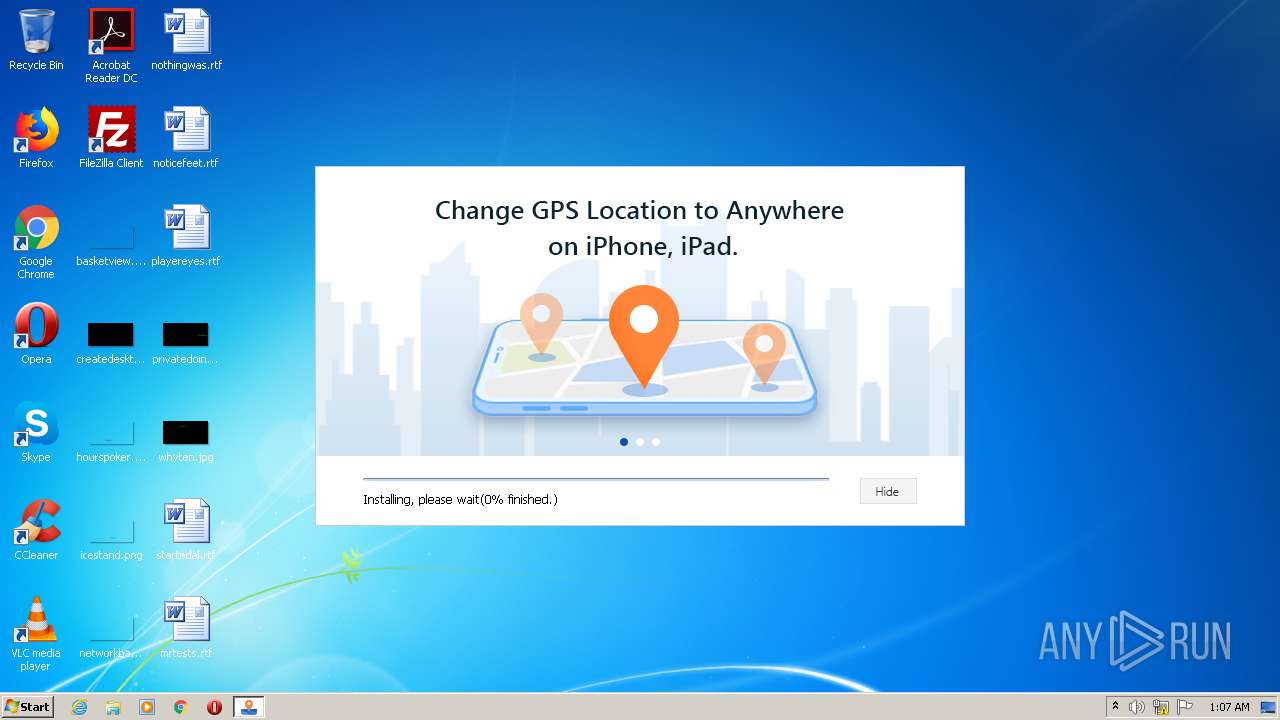
| File name: | imyfone-anyto_setup.exe |
| Full analysis: | https://app.any.run/tasks/c51c8d6f-bd7b-437f-bd65-1e3bd7a1b4b8 |
| Verdict: | Malicious activity |
| Analysis date: | October 28, 2020, 01:07:14 |
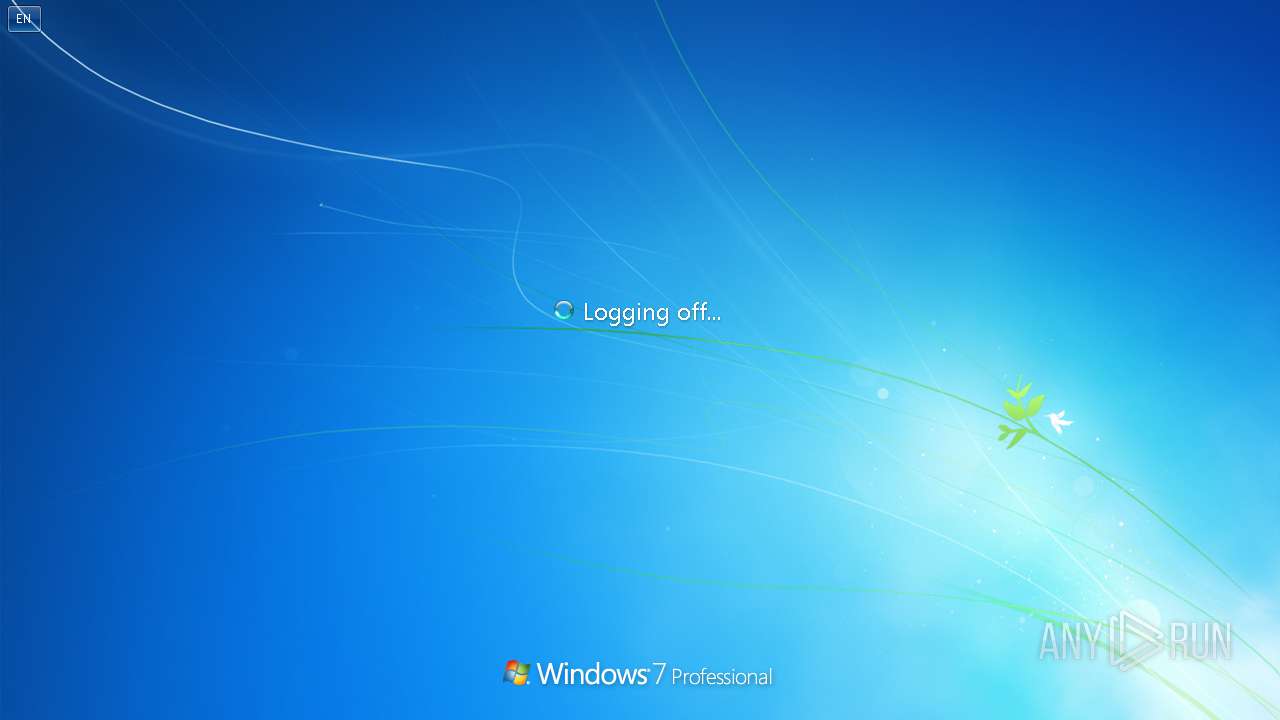
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A46CB7B536A201470893D45CF47EB595 |
| SHA1: | 821A12E5C4D26D51E3F181E4B402CC2B9A16943F |
| SHA256: | 6A9AE616193623FF6440C55F44BC712250F84FEB5DE3D75D6E0F1A56067DCEEB |
| SSDEEP: | 24576:9eurEQNcxz2hdt6TGEiSpbR5xot2pVDEARMXOb8invy:9V4kmqt6TGlSZXEARMXc/vy |
MALICIOUS
Loads dropped or rewritten executable
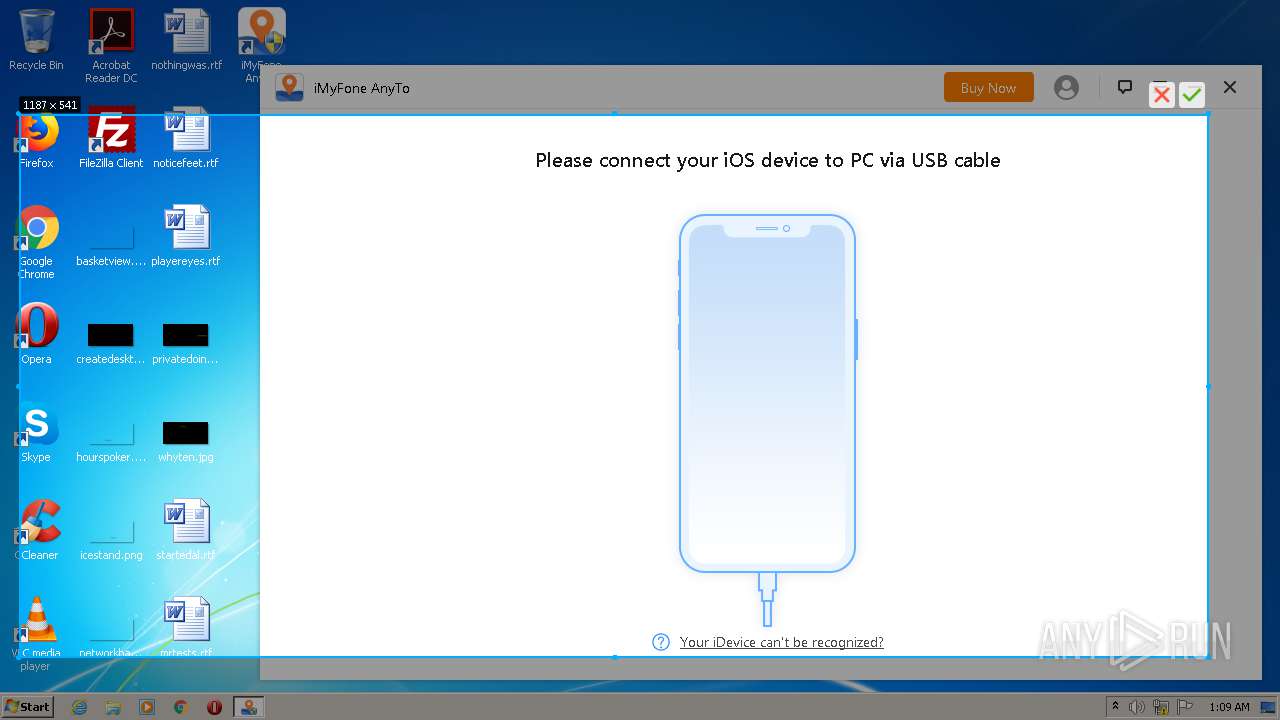
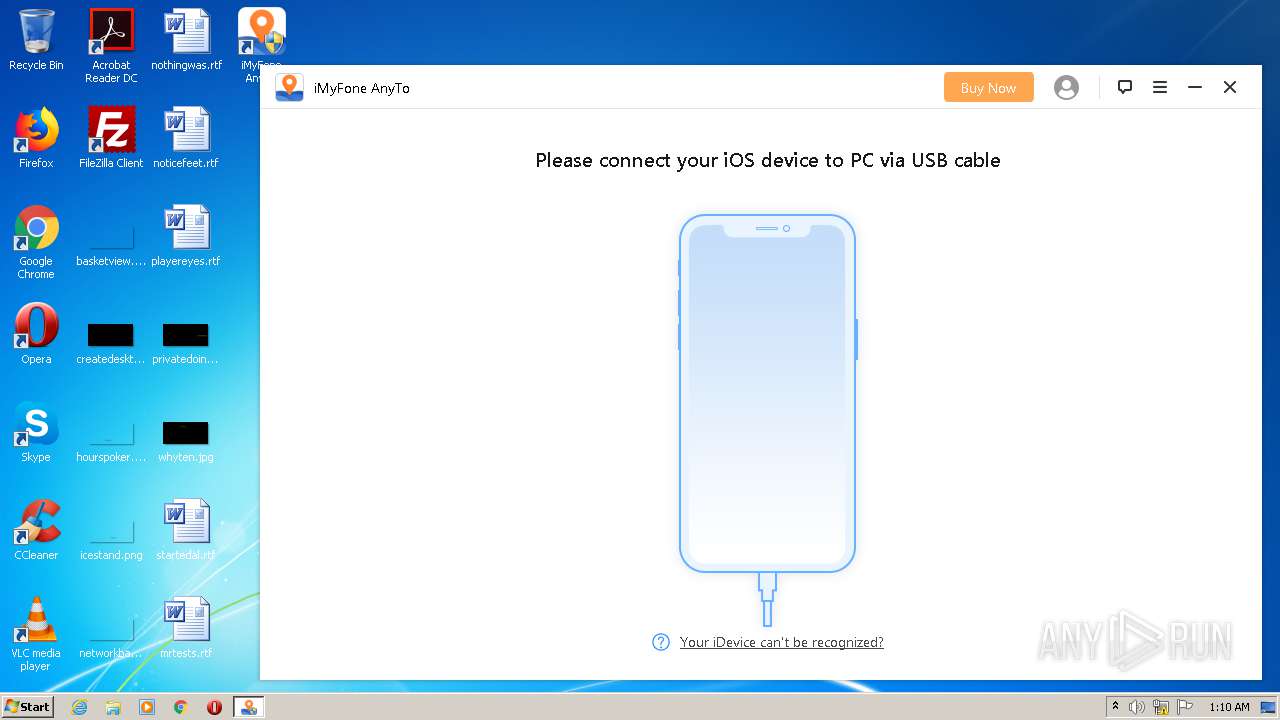
- host.exe (PID: 444)
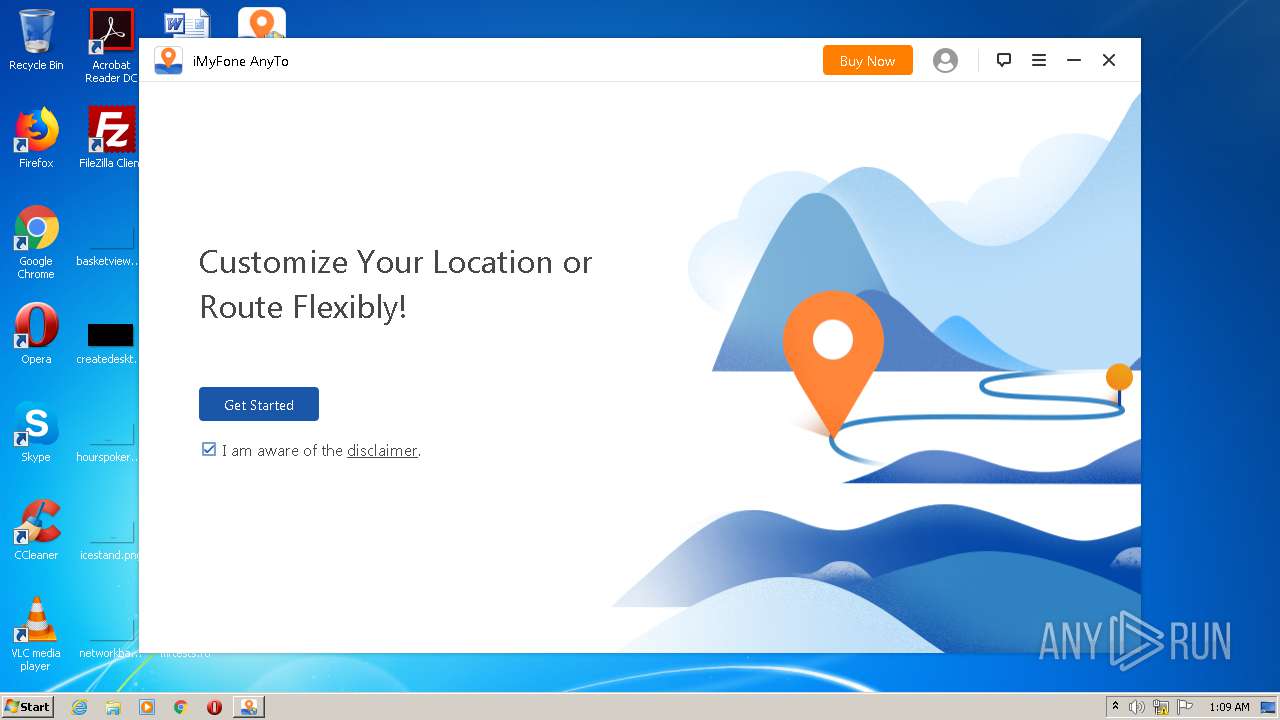
- AnyTo.exe (PID: 3736)
- ProServers.exe (PID: 2432)
- AppleMobileService.exe (PID: 3636)
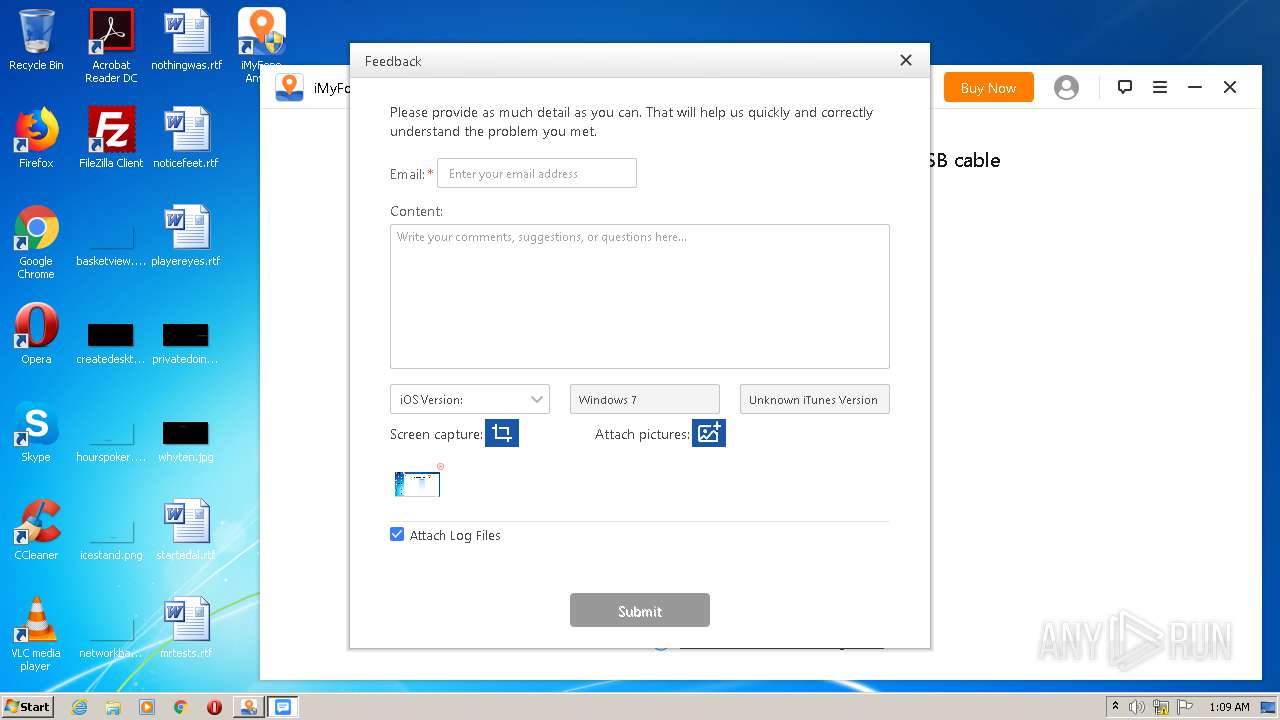
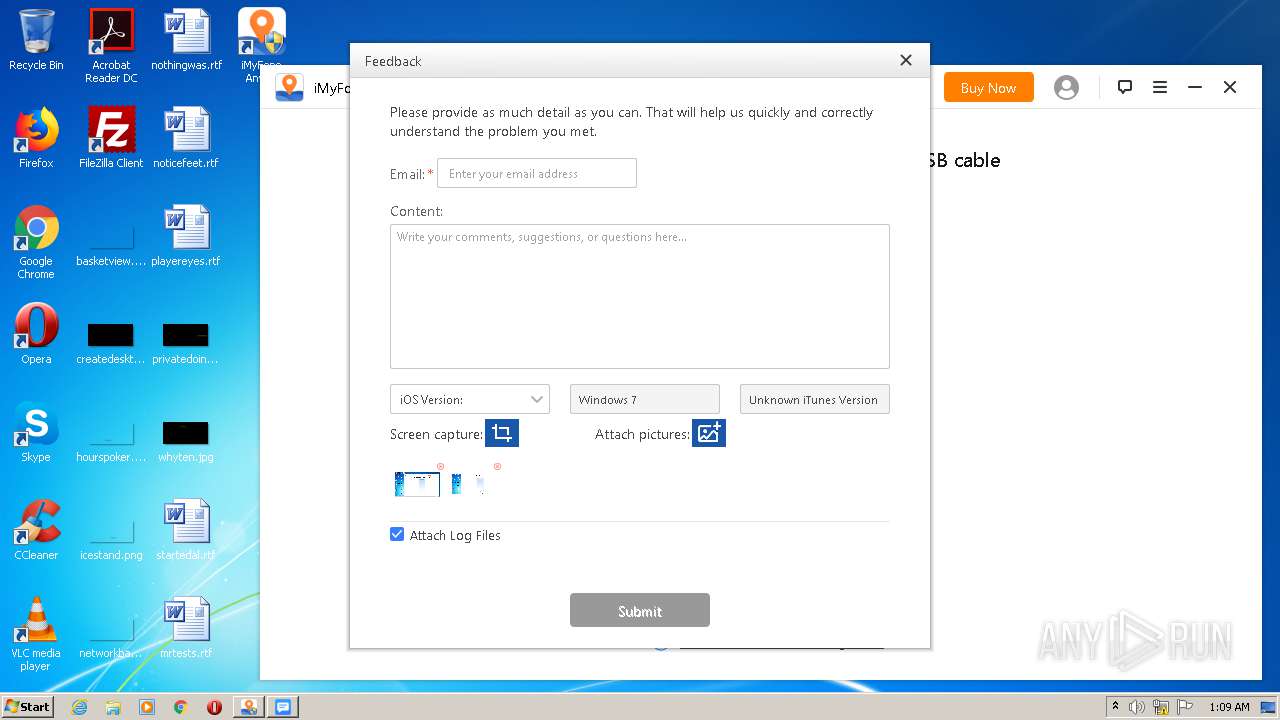
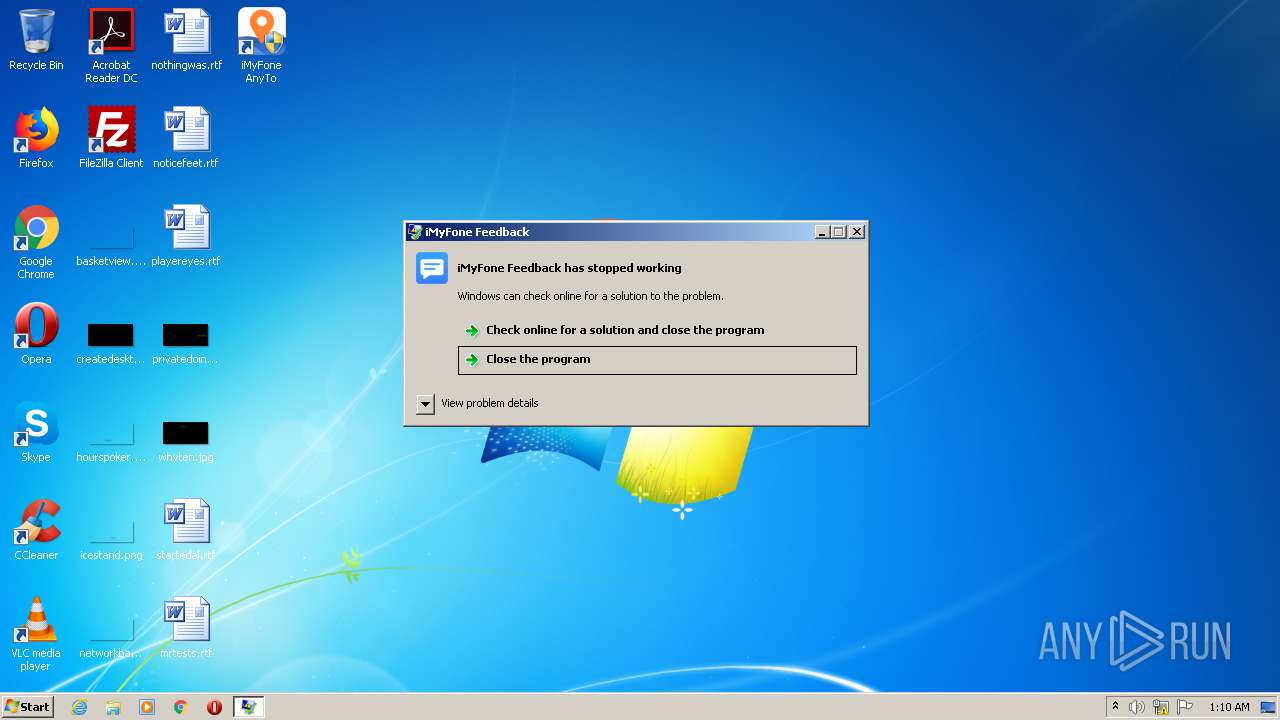
- Feedback.exe (PID: 1960)
- WerFault.exe (PID: 1436)
Changes settings of System certificates
- imyfone-anyto_setup.exe (PID: 3416)
Application was dropped or rewritten from another process
- AnyTo.exe (PID: 3736)
- ProServers.exe (PID: 2432)
- AppleMobileService.exe (PID: 3636)
- Feedback.exe (PID: 1960)
SUSPICIOUS
Reads Internet Cache Settings
- imyfone-anyto_setup.exe (PID: 3416)
Reads the Windows organization settings
- imyfone-anyto.tmp (PID: 1396)
Executable content was dropped or overwritten
- imyfone-anyto.exe (PID: 3976)
- imyfone-anyto.tmp (PID: 1396)
Creates files in the user directory
- imyfone-anyto.tmp (PID: 1396)
Creates files in the program directory
- imyfone-anyto_setup.exe (PID: 3416)
- AnyTo.exe (PID: 3736)
- WerFault.exe (PID: 1436)
- Feedback.exe (PID: 1960)
Reads Windows owner or organization settings
- imyfone-anyto.tmp (PID: 1396)
Adds / modifies Windows certificates
- imyfone-anyto_setup.exe (PID: 3416)
Starts Internet Explorer
- imyfone-anyto.tmp (PID: 1396)
INFO
Dropped object may contain Bitcoin addresses
- imyfone-anyto.tmp (PID: 1396)
Reads Internet Cache Settings
- iexplore.exe (PID: 548)
- iexplore.exe (PID: 2440)
Reads internet explorer settings
- iexplore.exe (PID: 2440)
Creates a software uninstall entry
- imyfone-anyto.tmp (PID: 1396)
Application launched itself
- iexplore.exe (PID: 548)
Changes internet zones settings
- iexplore.exe (PID: 548)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 548)
Reads settings of System Certificates
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 548)
Changes settings of System certificates
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 548)
Creates files in the program directory
- imyfone-anyto.tmp (PID: 1396)
Application was dropped or rewritten from another process
- imyfone-anyto.tmp (PID: 1396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:22 12:09:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 142848 |
| InitializedDataSize: | 1238016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12948 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.0.1 |
| ProductVersionNumber: | 3.5.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | iMyFone AnyTo |
| FileVersion: | 3.5.0.1 |
| InternalName: | AnyTo_Setup |
| LegalCopyright: | Copyright © 2020 iMyFone. All rights reserved. |
| OriginalFileName: | AnyTo_Setup.exe |
| ProductName: | iMyFone AnyTo |
| ProductVersion: | 3.5.0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Aug-2020 10:09:39 |
| Detected languages: |
|
| FileDescription: | iMyFone AnyTo |
| FileVersion: | 3.5.0.1 |
| InternalName: | AnyTo_Setup |
| LegalCopyright: | Copyright © 2020 iMyFone. All rights reserved. |
| OriginalFilename: | AnyTo_Setup.exe |
| ProductName: | iMyFone AnyTo |
| ProductVersion: | 3.5.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 22-Aug-2020 10:09:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00022D1B | 0x00022E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55757 |
.rdata | 0x00024000 | 0x00009A54 | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.83409 |
.data | 0x0002E000 | 0x000043C0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.23349 |
.rsrc | 0x00033000 | 0x0011DE70 | 0x0011E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.94988 |
.reloc | 0x00151000 | 0x00002390 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60589 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06216 | 651 | UNKNOWN | English - United States | RT_MANIFEST |
9 | 1.56933 | 56 | UNKNOWN | English - United States | RT_STRING |
100 | 3.42408 | 266 | UNKNOWN | English - United States | RT_DIALOG |
128 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
129 | 3.18924 | 684 | UNKNOWN | English - United States | RT_DIALOG |
202 | 6.47154 | 1129 | UNKNOWN | Chinese - PRC | PNG |
207 | 5.99748 | 238 | UNKNOWN | Chinese - PRC | PNG |
213 | 7.7512 | 1814 | UNKNOWN | Chinese - PRC | PNG |
214 | 7.90646 | 6835 | UNKNOWN | Chinese - PRC | PNG |
215 | 6.13634 | 1002 | UNKNOWN | Chinese - PRC | PNG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINHTTP.dll |
WININET.dll |
Total processes
58
Monitored processes
12
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "host.exe" | C:\Windows\system32\host.exe | — | srvpost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.imyfone.com/thankyou/install-ios-location-changer/ | C:\Program Files\Internet Explorer\iexplore.exe | imyfone-anyto.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1396 | "C:\Users\admin\AppData\Local\Temp\is-R3GC7.tmp\imyfone-anyto.tmp" /SL5="$A0142,81012829,125952,C:\Users\Public\Documents\iMyFone\imyfone-anyto.exe" /verysilent /imyfone_down /wait_run /path="C:\Program Files" | C:\Users\admin\AppData\Local\Temp\is-R3GC7.tmp\imyfone-anyto.tmp | imyfone-anyto.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1436 | C:\Windows\system32\WerFault.exe -u -p 1960 -s 200 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1960 | "C:\Program Files\iMyFone\iMyFone AnyTo\Feedback.exe" feedback@imyfone.com "C:/Program Files/iMyFone/iMyFone AnyTo/AnyTo.exe" "" anyto@imyfone.com anyTo@#$imyF 1 | C:\Program Files\iMyFone\iMyFone AnyTo\Feedback.exe | AnyTo.exe | ||||||||||||
User: admin Company: Shenzhen iMyFone Technology Co., Ltd. Integrity Level: HIGH Description: iMyFone Feedback Exit code: 3221225477 Version: 2.0.3.4 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\iMyFone\iMyFone AnyTo\ProServers.exe" AnyTo.exe feedback@imyfone.com "C:/Program Files/iMyFone/iMyFone AnyTo" "" anyto@imyfone.com anyTo@#$imyF | C:\Program Files\iMyFone\iMyFone AnyTo\ProServers.exe | — | AnyTo.exe | |||||||||||
User: admin Company: Shenzhen iMyFone Technology Co., Ltd. Integrity Level: HIGH Description: iMyFone Daemons Exit code: 0 Version: 2.0.2.0 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:548 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\Temp\imyfone-anyto_setup.exe" | C:\Users\admin\AppData\Local\Temp\imyfone-anyto_setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: iMyFone AnyTo Exit code: 3221226540 Version: 3.5.0.1 Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\imyfone-anyto_setup.exe" | C:\Users\admin\AppData\Local\Temp\imyfone-anyto_setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: iMyFone AnyTo Exit code: 1000 Version: 3.5.0.1 Modules
| |||||||||||||||
| 3636 | "C:\Program Files\iMyFone\iMyFone AnyTo\AppleService\AppleMobileService.exe" | C:\Program Files\iMyFone\iMyFone AnyTo\AppleService\AppleMobileService.exe | — | AnyTo.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
Total events
1 499
Read events
1 340
Write events
152
Delete events
7
Modification events
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (444) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
110
Suspicious files
27
Text files
708
Unknown types
68
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | imyfone-anyto_setup.exe | C:\Users\admin\AppData\Local\Temp\Cab8B2E.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | imyfone-anyto_setup.exe | C:\Users\admin\AppData\Local\Temp\Tar8B2F.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | imyfone-anyto_setup.exe | C:\Users\Public\Documents\iMyFone\imyfone-anyto.down | — | |
MD5:— | SHA256:— | |||
| 3416 | imyfone-anyto_setup.exe | C:\Users\Public\Documents\iMyFone\imyfone-anyto.exe | — | |
MD5:— | SHA256:— | |||
| 1396 | imyfone-anyto.tmp | C:\Program Files\iMyFone\iMyFone AnyTo\is-M9CCC.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | imyfone-anyto.tmp | C:\Program Files\iMyFone\iMyFone AnyTo\is-KVN7I.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | imyfone-anyto.tmp | C:\Program Files\iMyFone\iMyFone AnyTo\is-4KEUP.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | imyfone-anyto.tmp | C:\Program Files\iMyFone\iMyFone AnyTo\is-6CKV5.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | imyfone-anyto.tmp | C:\Program Files\iMyFone\iMyFone AnyTo\is-GC7U7.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | imyfone-anyto.tmp | C:\Program Files\iMyFone\iMyFone AnyTo\AnyTo.ilk | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
82
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2440 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDopzvCvNaHRggAAAAAXcGw | US | der | 472 b | whitelisted |
3416 | imyfone-anyto_setup.exe | HEAD | 200 | 216.58.206.14:80 | http://www.google-analytics.com/collect?v=1&t=event&tid=UA-65522660-14&cid=598FD63C-3F10-4288-9D47-CA94196BB7F7&ec=iMyFone%20AnyTo%20(Windows%20version)&ea=Downloader_Installed&el=598FD63C-3F10-4288-9D47-CA94196BB7F7 | US | — | — | whitelisted |
548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3736 | AnyTo.exe | GET | 200 | 34.217.190.60:80 | http://apianyto.imyfone.club/anyto/gettoken | US | text | 170 b | suspicious |
548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3416 | imyfone-anyto_setup.exe | HEAD | 200 | 216.58.206.14:80 | http://www.google-analytics.com/collect?v=1&t=event&tid=UA-65522660-14&cid=598FD63C-3F10-4288-9D47-CA94196BB7F7&ec=iMyFone%20AnyTo%20(Windows%20version)&ea=Downloader_Start_Install&el=598FD63C-3F10-4288-9D47-CA94196BB7F7 | US | — | — | whitelisted |
3416 | imyfone-anyto_setup.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
1052 | svchost.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/GTSGIAG3/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCCB1hFTiyruqn | US | binary | 5 b | whitelisted |
2440 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3416 | imyfone-anyto_setup.exe | 216.58.206.14:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3416 | imyfone-anyto_setup.exe | 99.86.2.64:443 | download.imyfone.com | AT&T Services, Inc. | US | suspicious |
3416 | imyfone-anyto_setup.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3416 | imyfone-anyto_setup.exe | 99.86.2.94:443 | download.imyfone.com | AT&T Services, Inc. | US | unknown |
2440 | iexplore.exe | 47.246.43.206:443 | static.imyfone.com | — | US | malicious |
2440 | iexplore.exe | 99.86.2.27:443 | www.imyfone.com | AT&T Services, Inc. | US | malicious |
2440 | iexplore.exe | 104.18.11.39:80 | cacerts.geotrust.com | Cloudflare Inc | US | shared |
2440 | iexplore.exe | 172.217.18.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3736 | AnyTo.exe | 34.217.190.60:443 | apianyto.imyfone.club | Amazon.com, Inc. | US | suspicious |
548 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
download.imyfone.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
www.imyfone.com |
| whitelisted |
static.imyfone.com |
| malicious |
cacerts.geotrust.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
AnyTo.exe | Failed to load and resolve WGL/OpenGL functions
|
AnyTo.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
AnyTo.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
AnyTo.exe | Failed to load opengl32sw.dll (The specified module could not be found.)
|
AnyTo.exe | QCssParser::parseHexColor: Unknown color name '#gray'
|
AnyTo.exe | QCssParser::parseHexColor: Unknown color name '#gray'
|
AnyTo.exe | QCssParser::parseHexColor: Unknown color name '#gray'
|
AnyTo.exe | QCssParser::parseHexColor: Unknown color name '#gray'
|
AnyTo.exe | QCssParser::parseHexColor: Unknown color name '#elecff'
|
AnyTo.exe | appPath=========================== "C:/Program Files/iMyFone/iMyFone AnyTo"
|