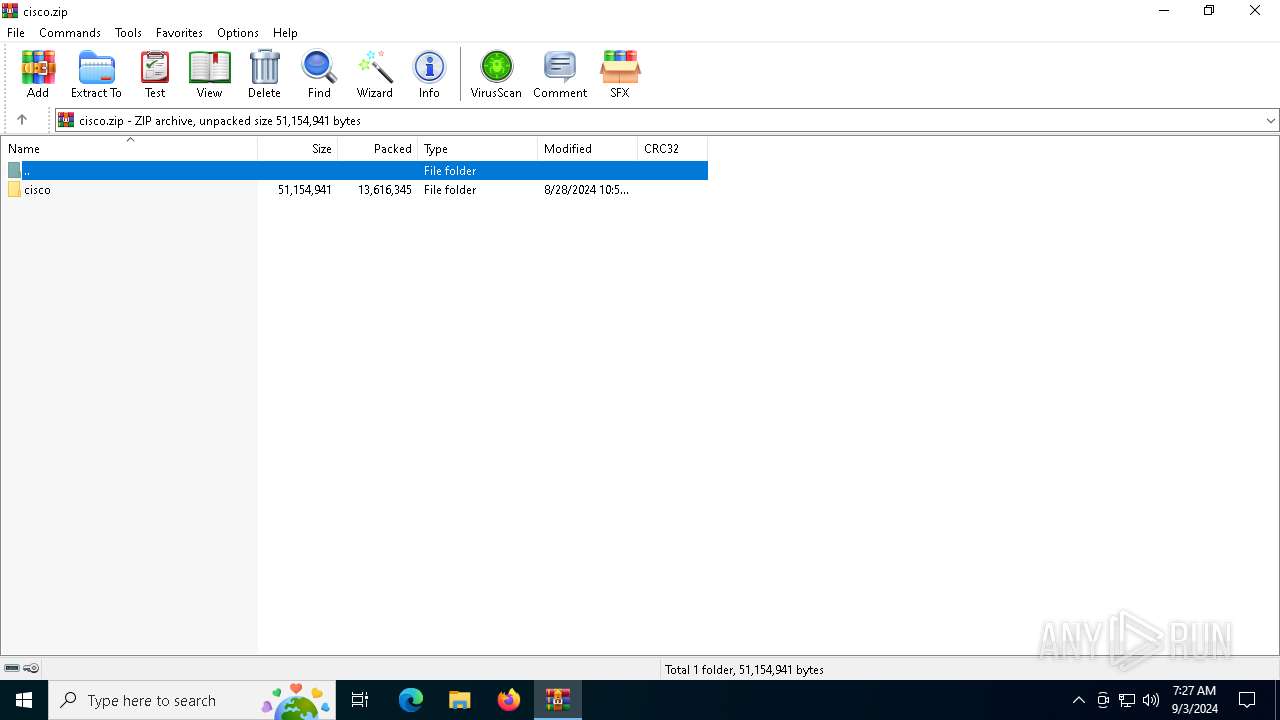
| File name: | cisco.zip |
| Full analysis: | https://app.any.run/tasks/cf93f134-b4d7-4573-b903-fd1d94213c20 |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2024, 07:27:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 736817F4097E37B72024B7C8140C3643 |
| SHA1: | E540BE783A120A1F13C78F457F722593554D0759 |
| SHA256: | 6A7E7EA7B178CAEE826C0DC4D1E701DE4019F3981D9A03F73D63C2D1025B11D2 |
| SSDEEP: | 196608:JYlo9KI3C9sk2Ym8l7nkGdwpgLFOTpaBP:J0IS9rT5k7LNal |
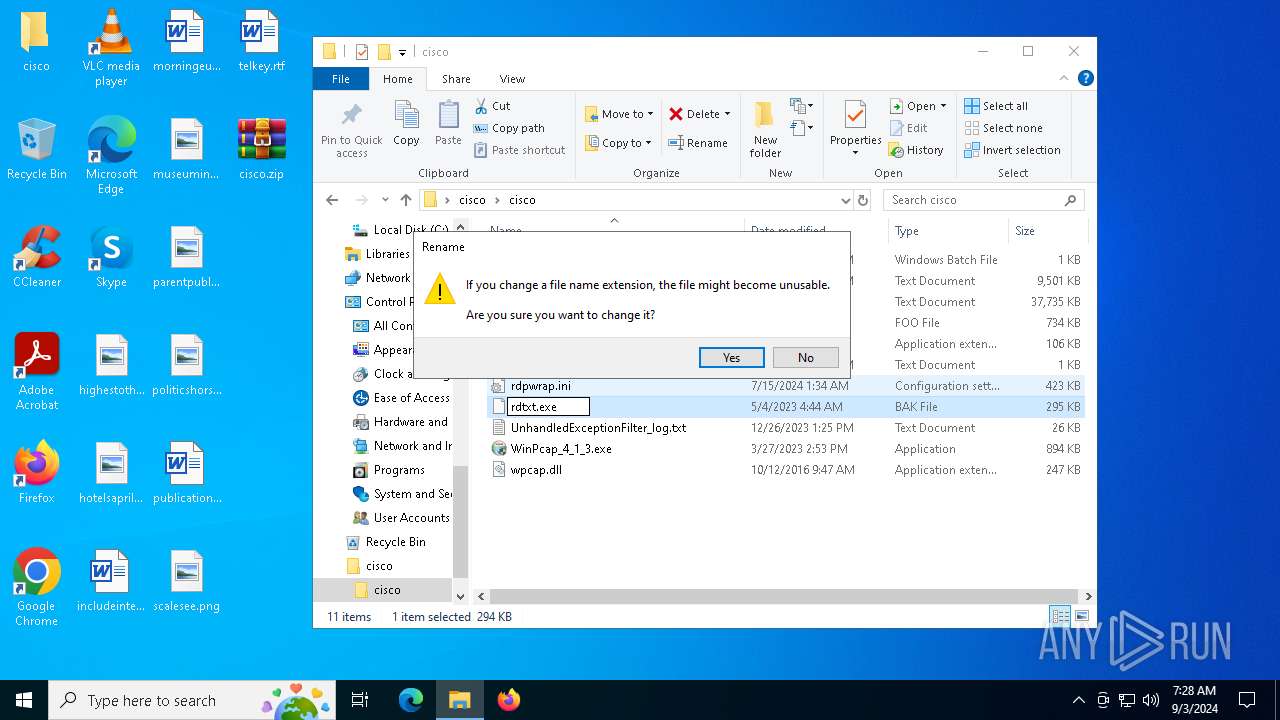
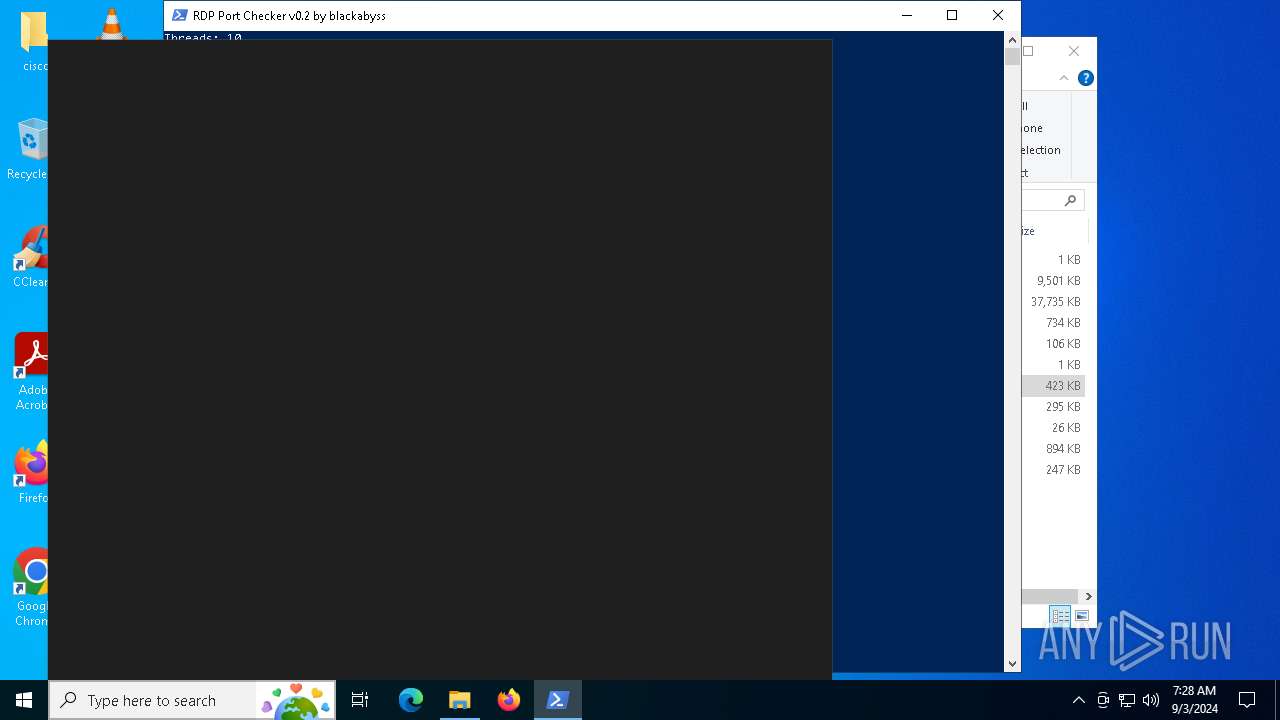
MALICIOUS
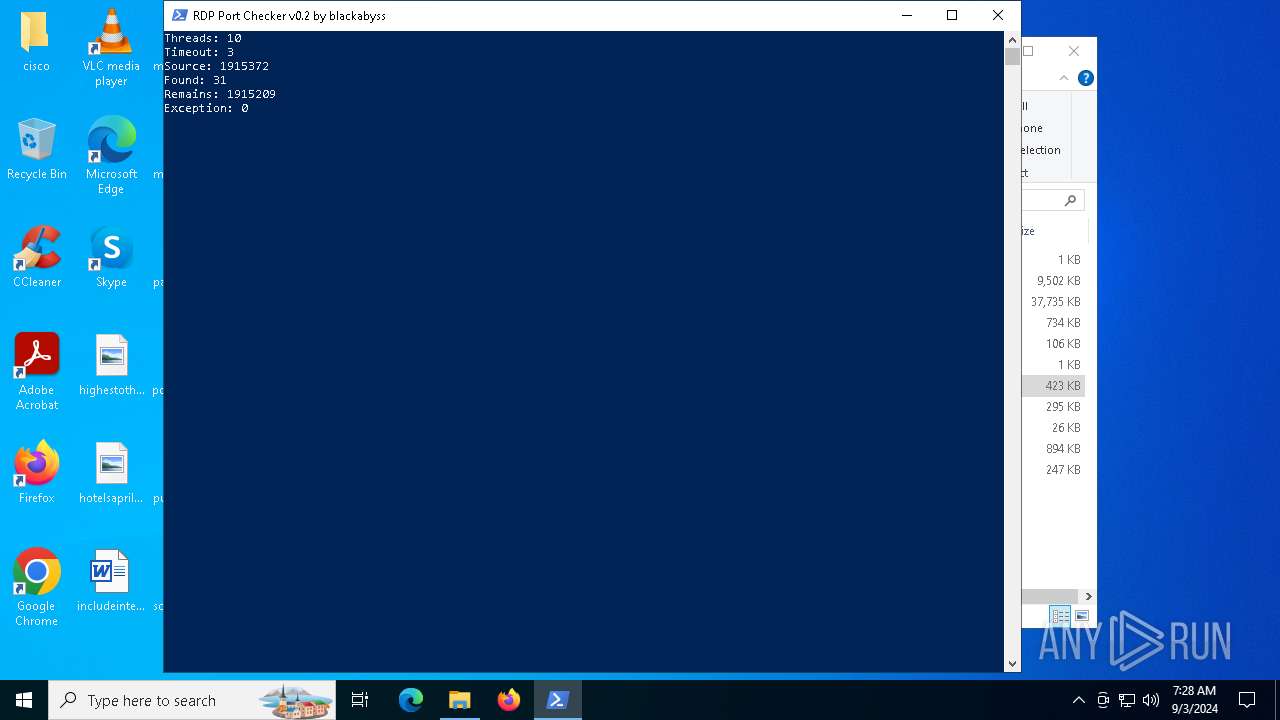
An attempt to connect via RDP was detected
- rdtxt.exe (PID: 5940)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3376)
Potential Corporate Privacy Violation
- rdtxt.exe (PID: 5940)
Connects to unusual port
- rdtxt.exe (PID: 5940)
INFO
The process uses the downloaded file
- powershell.exe (PID: 6052)
- WinRAR.exe (PID: 3376)
- powershell.exe (PID: 2524)
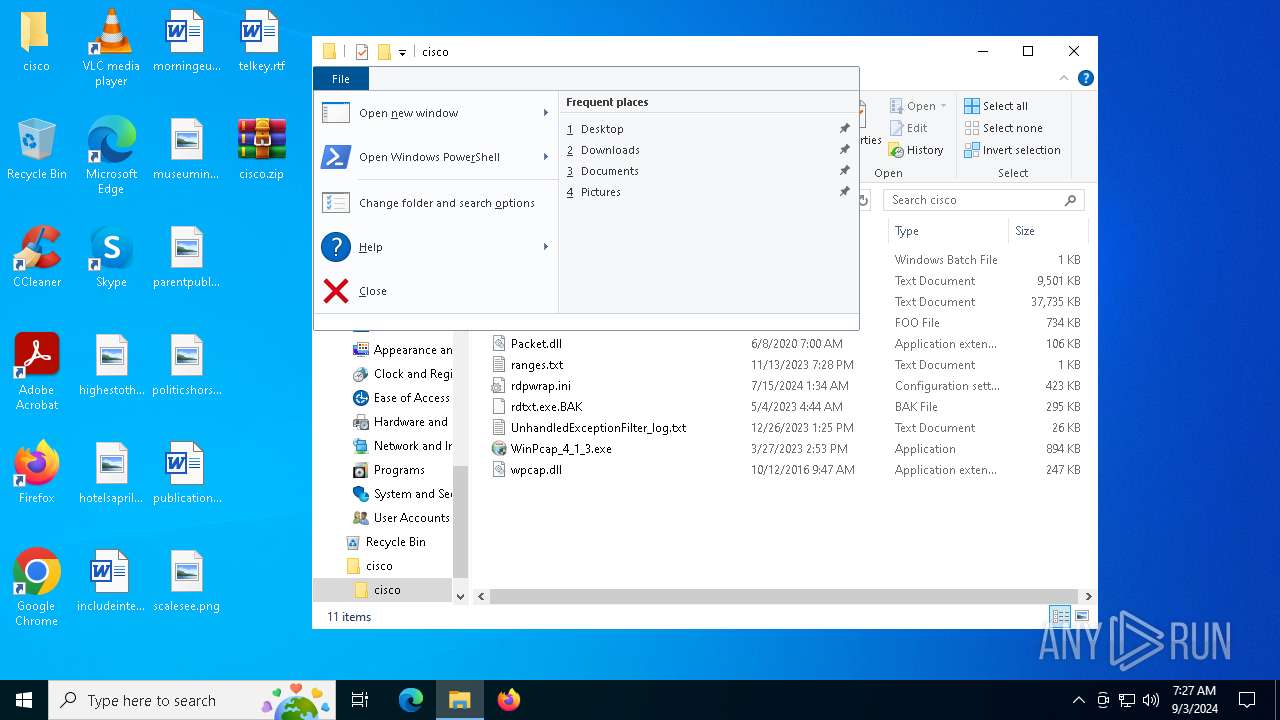
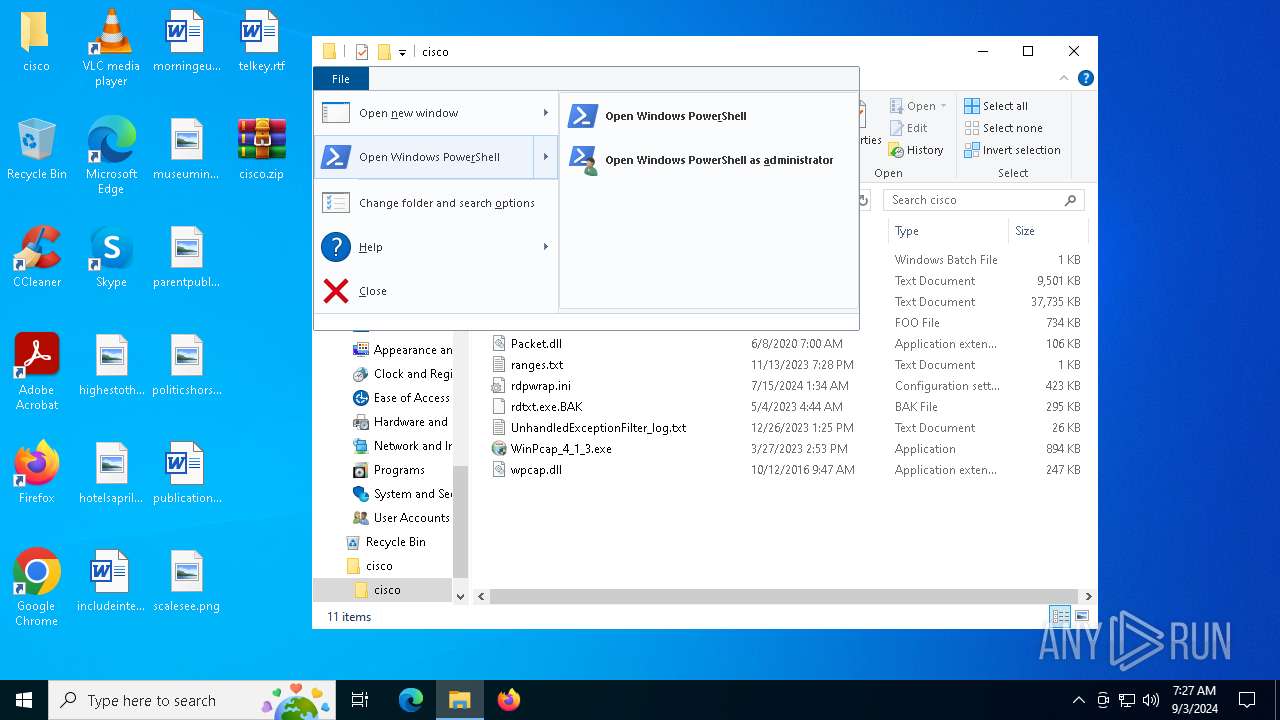
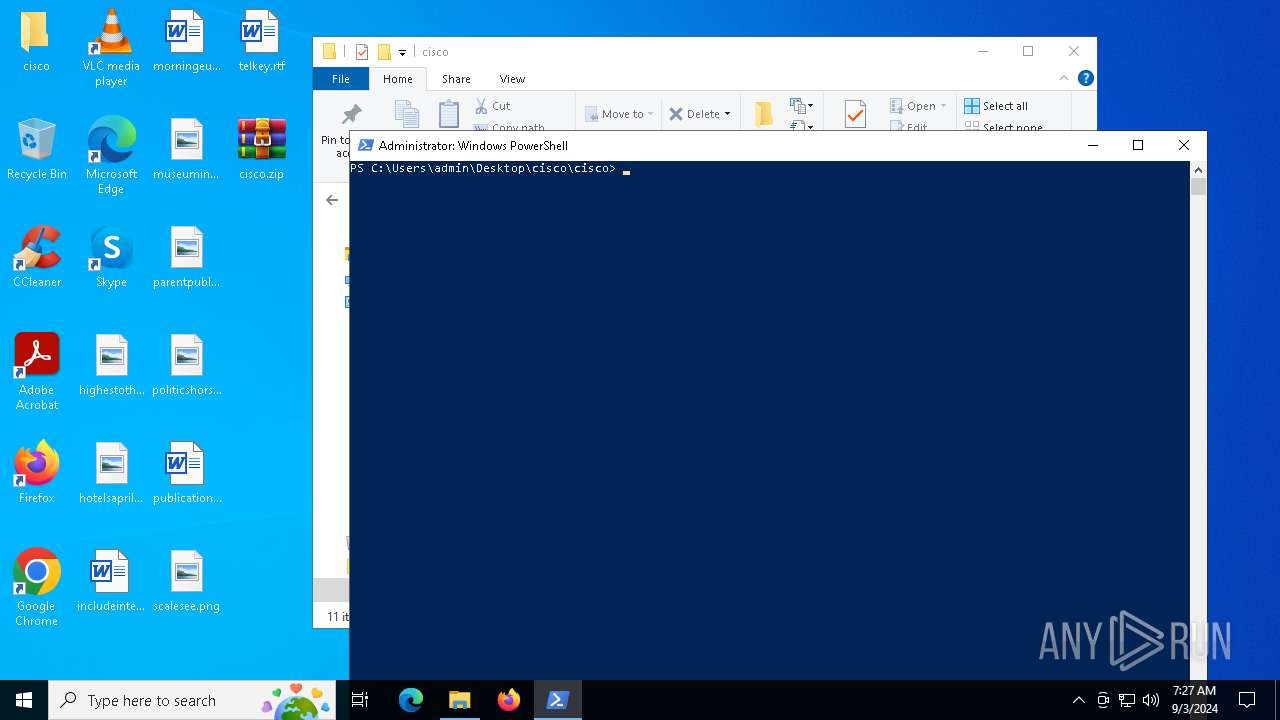
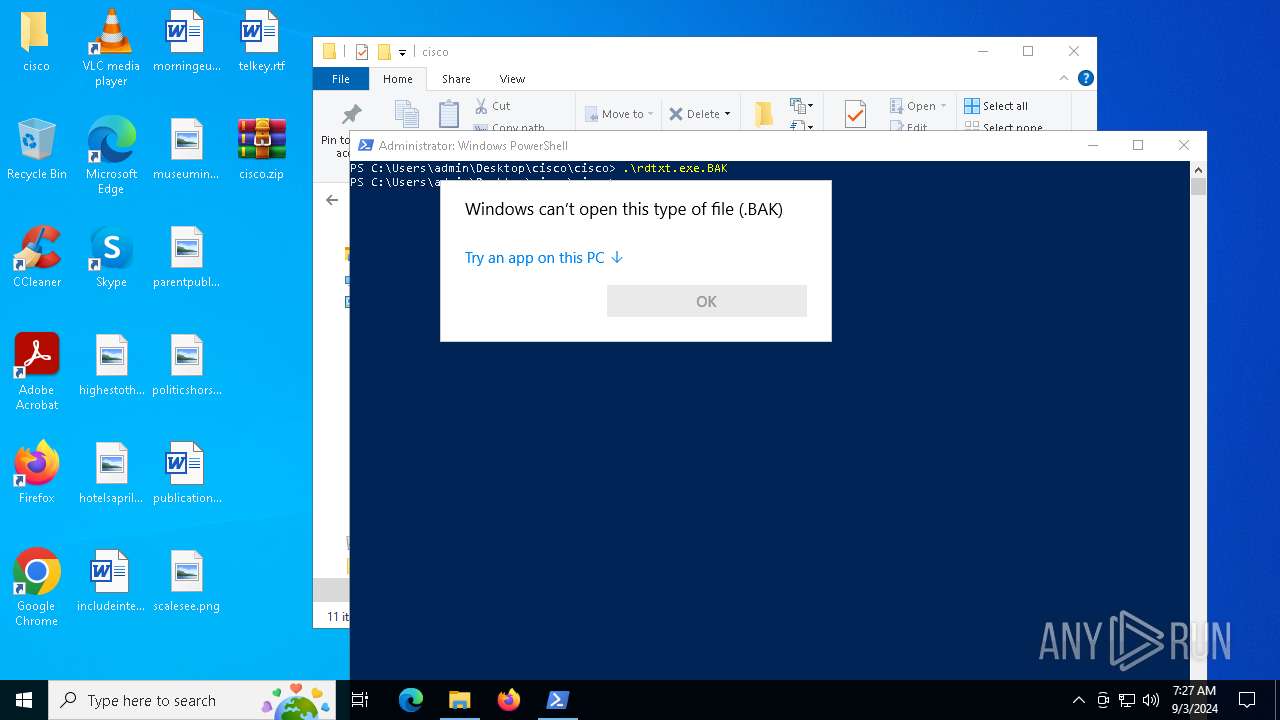
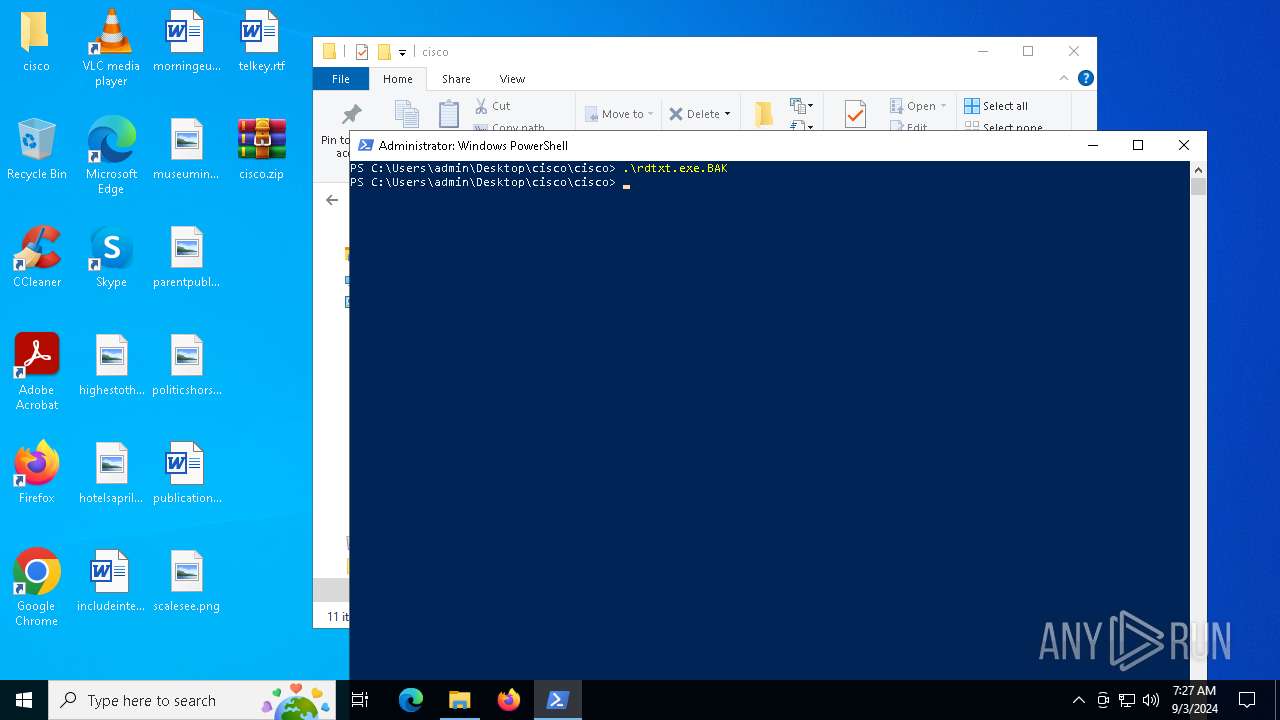
Manual execution by a user
- powershell.exe (PID: 6052)
- powershell.exe (PID: 2524)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6052)
- powershell.exe (PID: 2524)
Checks supported languages
- rdtxt.exe (PID: 5940)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 1288)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:08:28 12:57:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | cisco/ |
Total processes
127
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1288 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2520 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
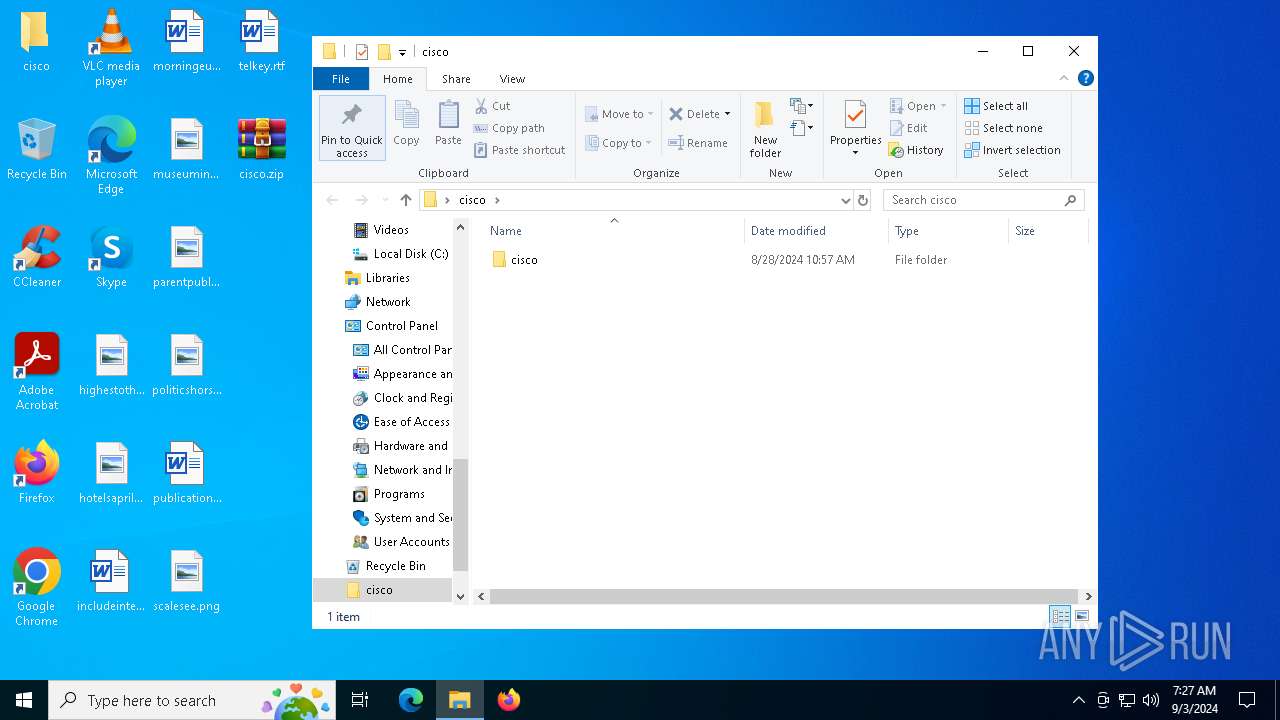
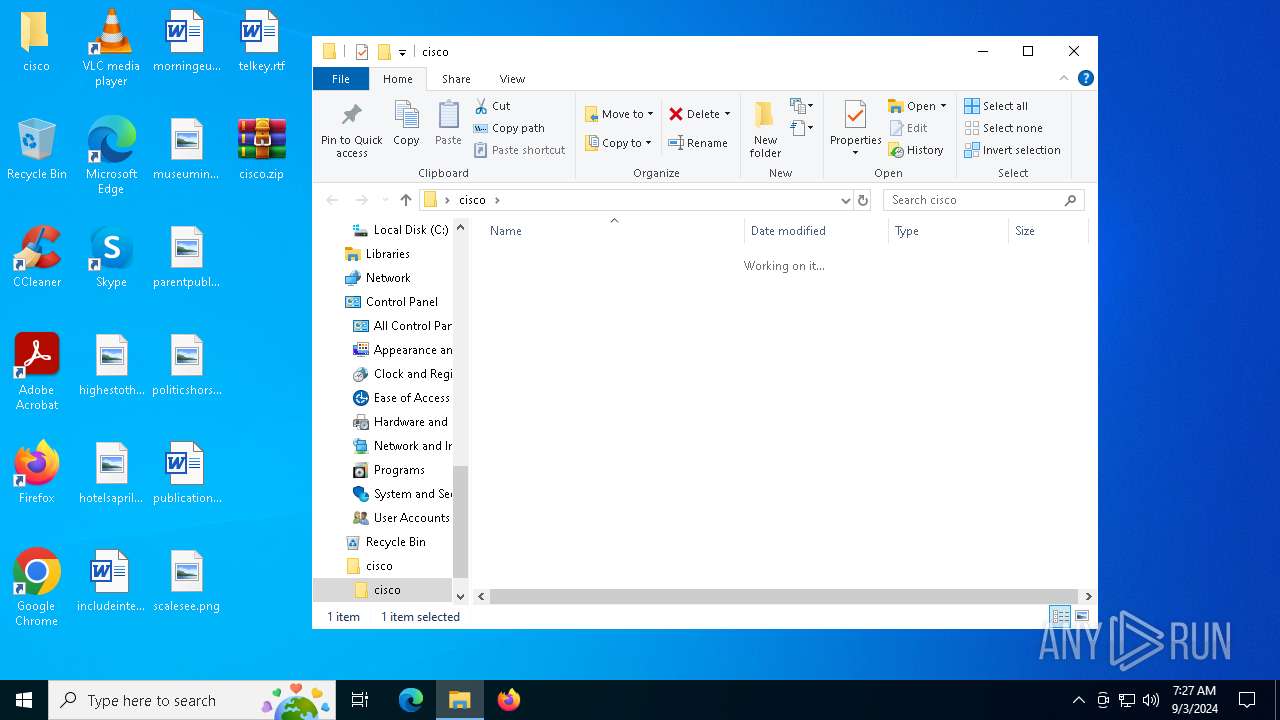
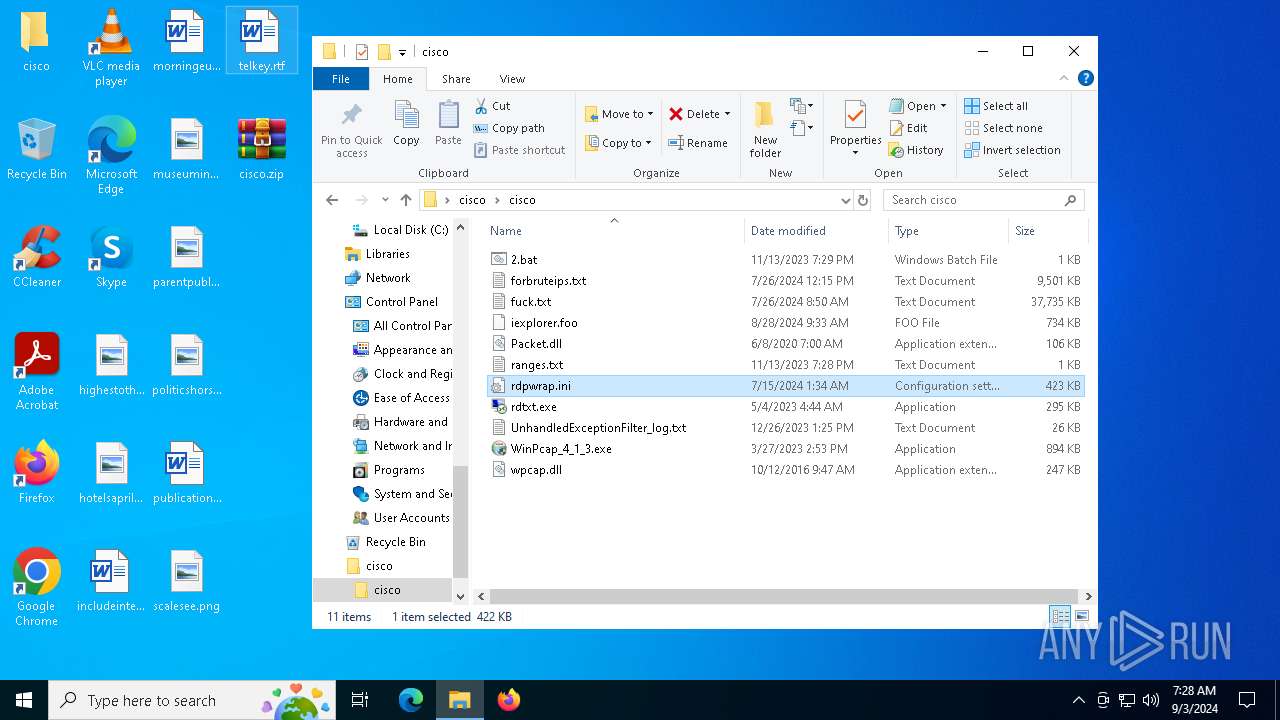
| 2524 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noexit -command Set-Location -literalPath 'C:\Users\admin\Desktop\cisco\cisco' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
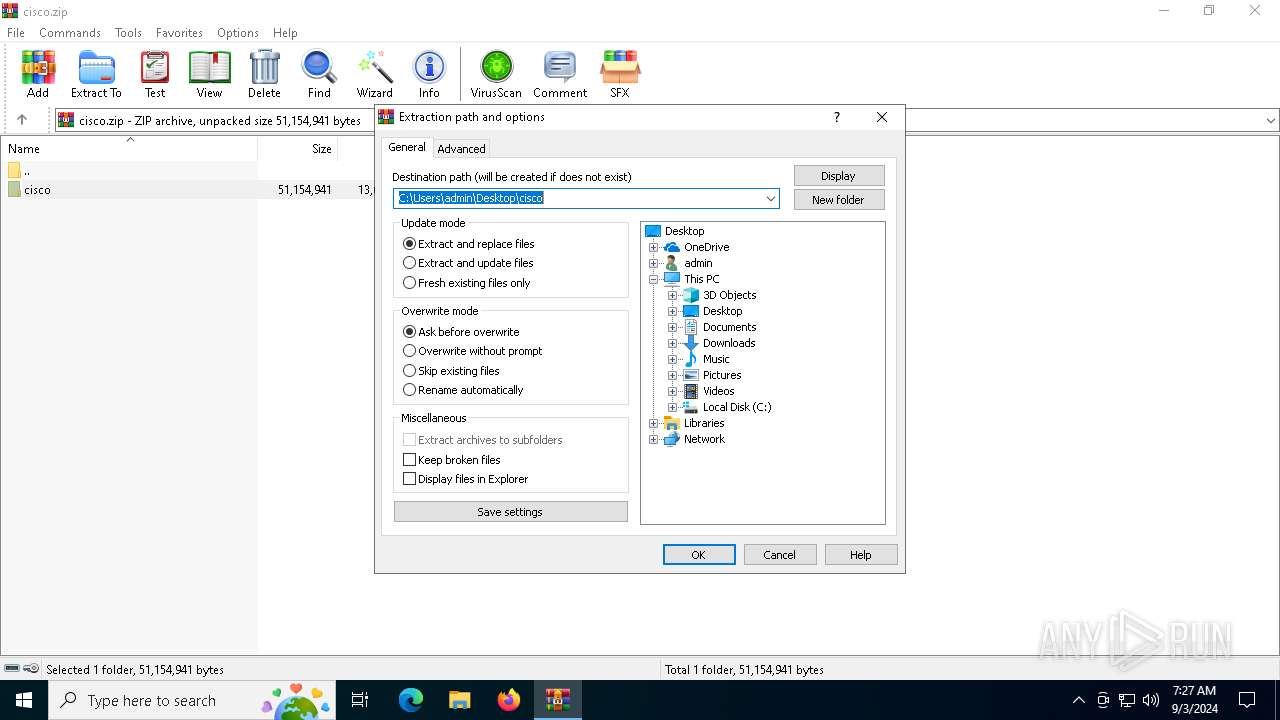
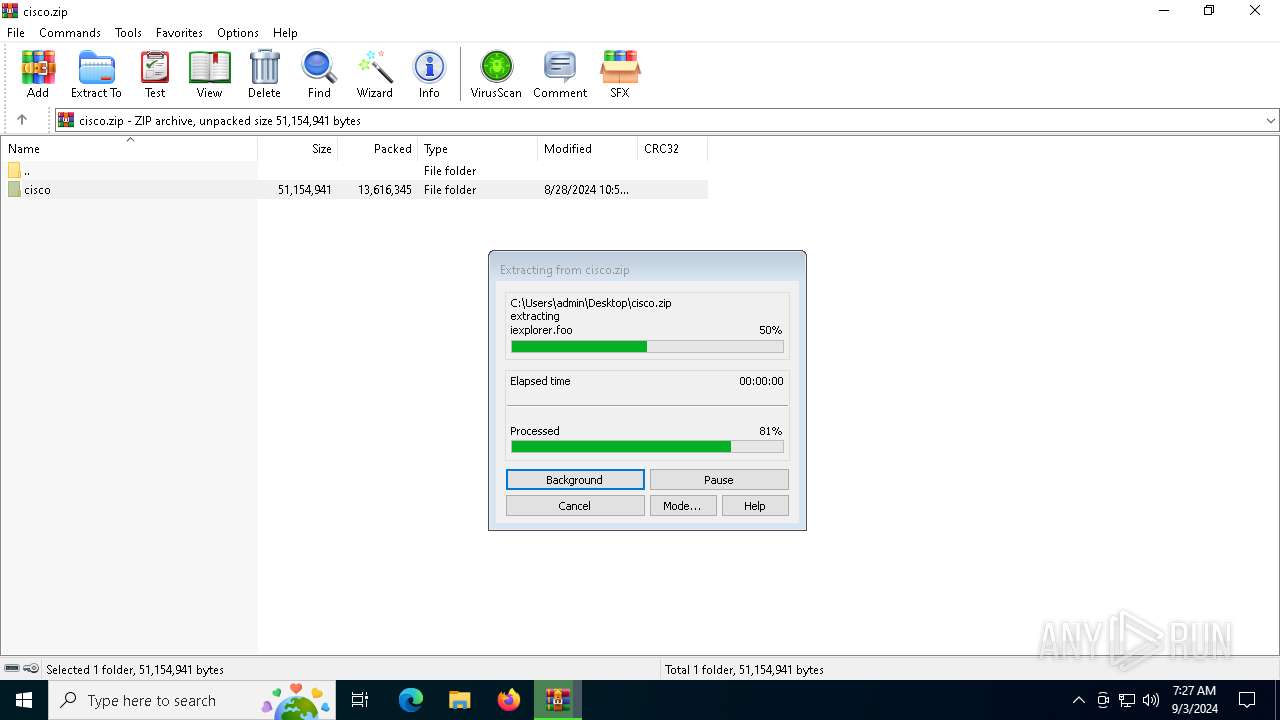
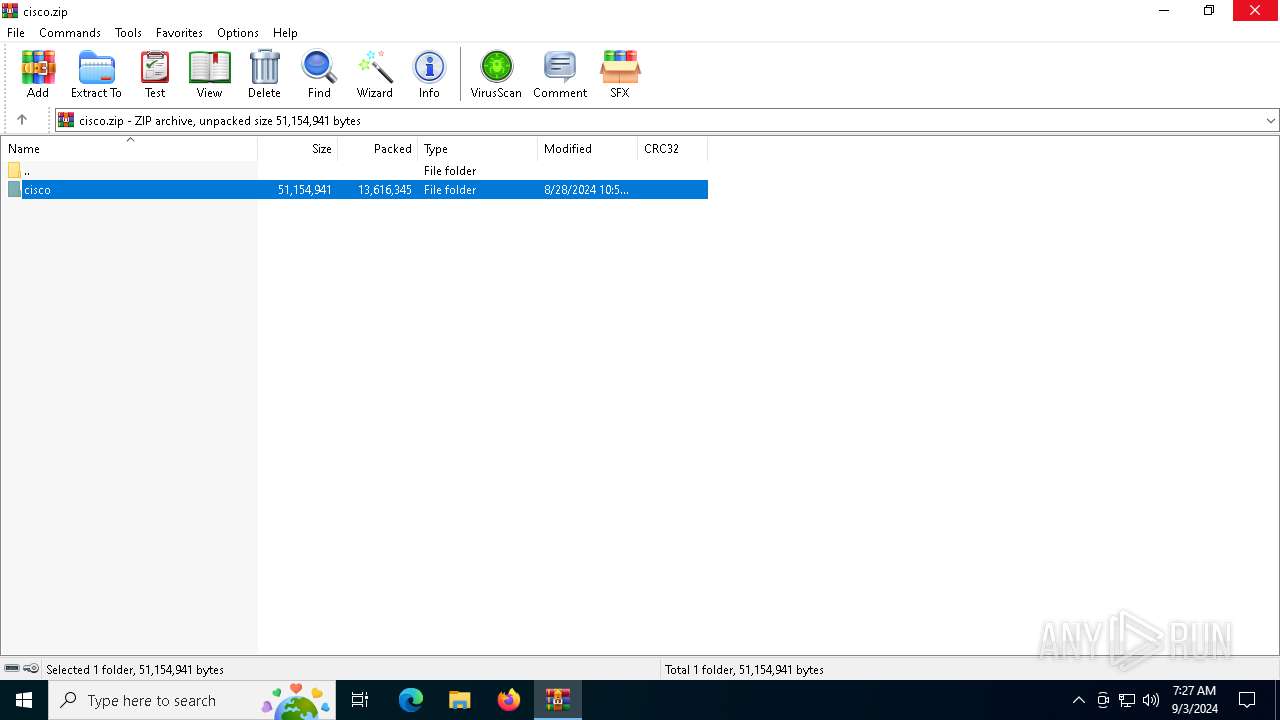
| 3376 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\cisco.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5476 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5940 | "C:\Users\admin\Desktop\cisco\cisco\rdtxt.exe" | C:\Users\admin\Desktop\cisco\cisco\rdtxt.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 0.2.0.0 Modules
| |||||||||||||||
| 6052 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noexit -command Set-Location -literalPath 'C:\Users\admin\Desktop\cisco\cisco' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6248 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
30 518
Read events
30 480
Write events
38
Delete events
0
Modification events
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\cisco.zip | |||
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\cisco | |||
| (PID) Process: | (3376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
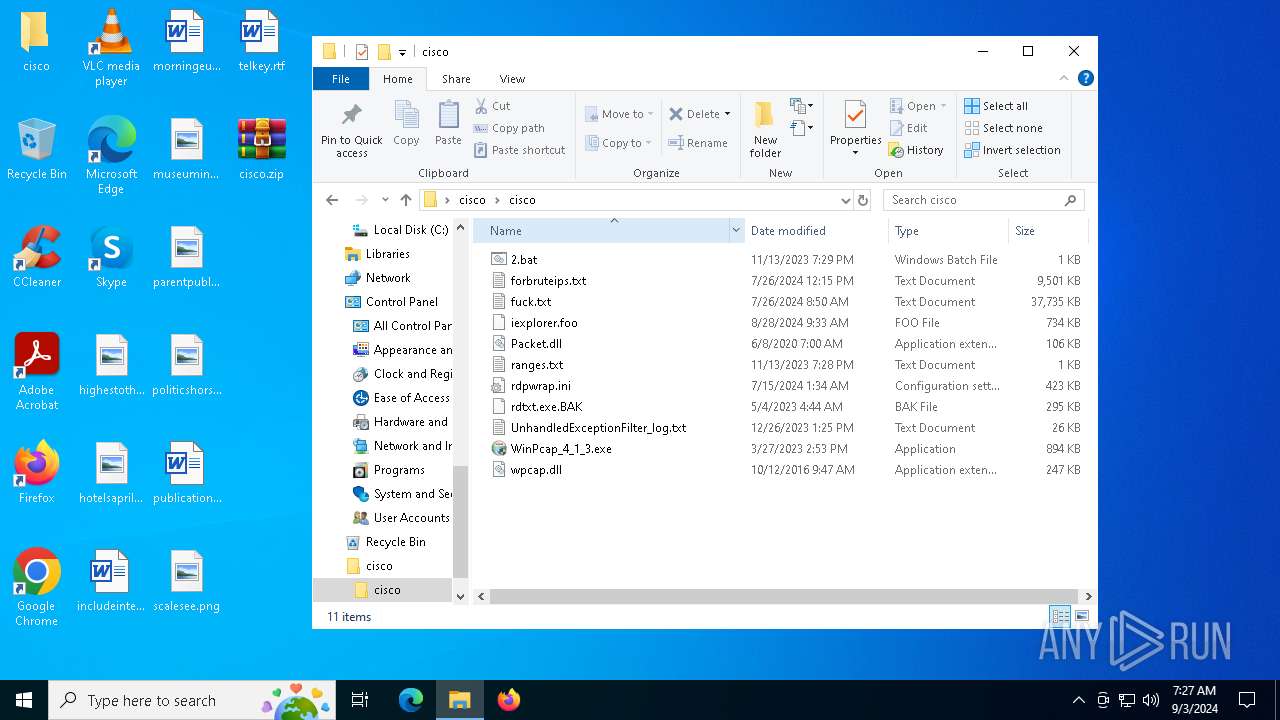
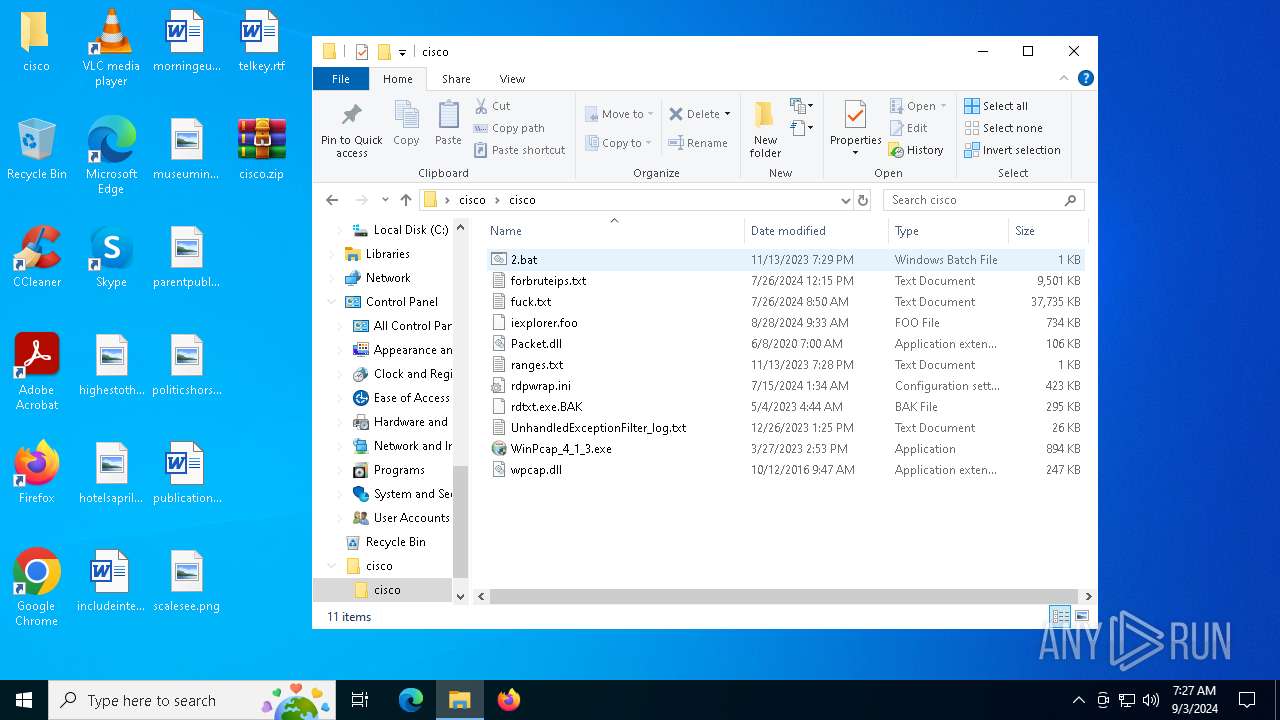
Executable files
5
Suspicious files
9
Text files
12
Unknown types
0
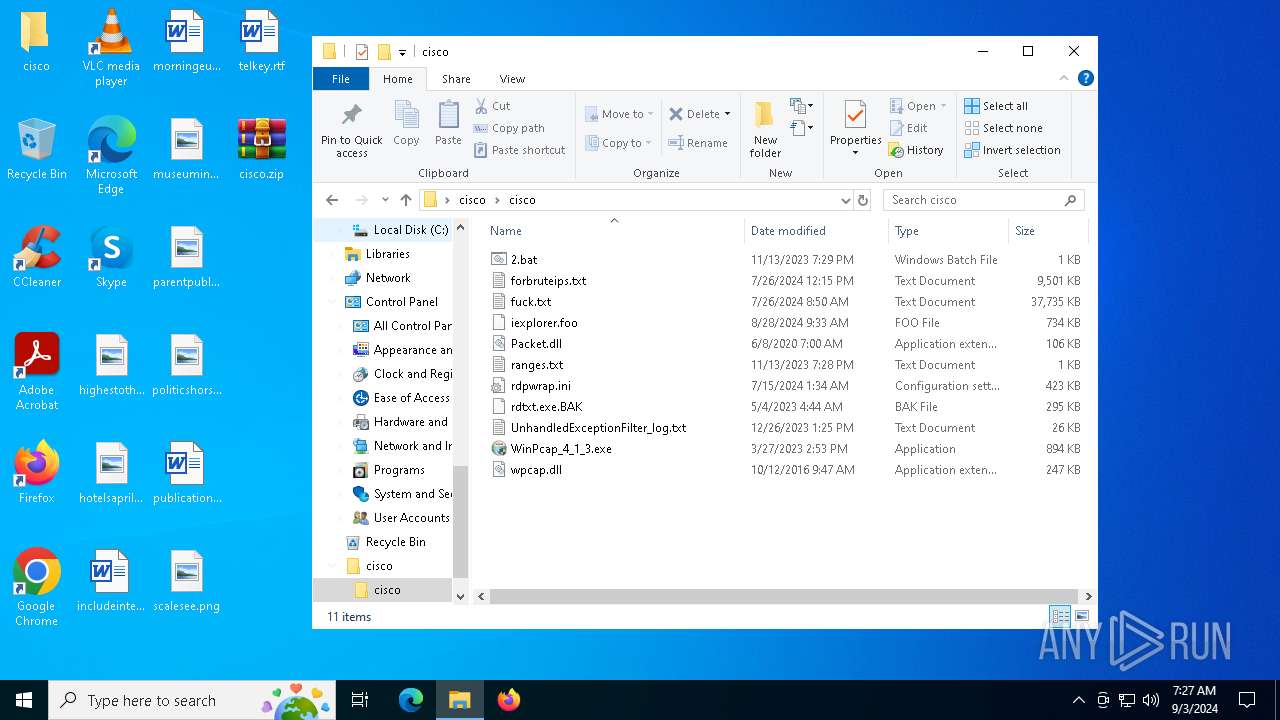
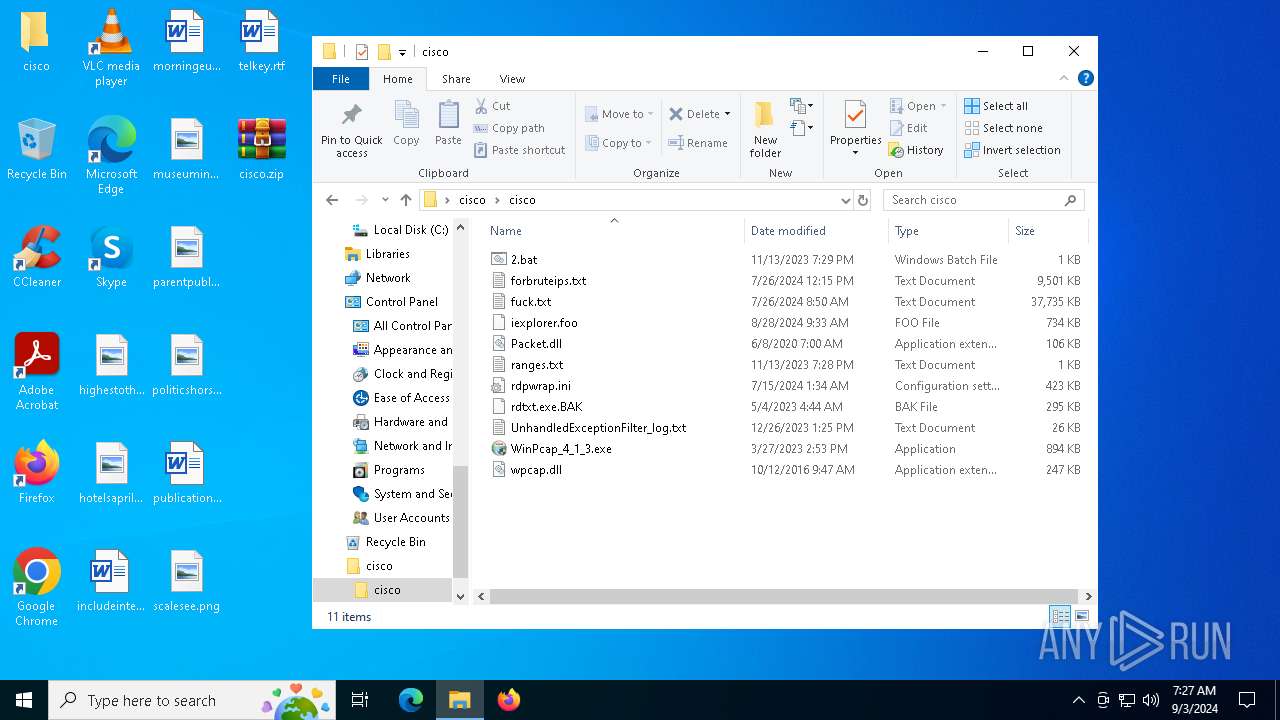
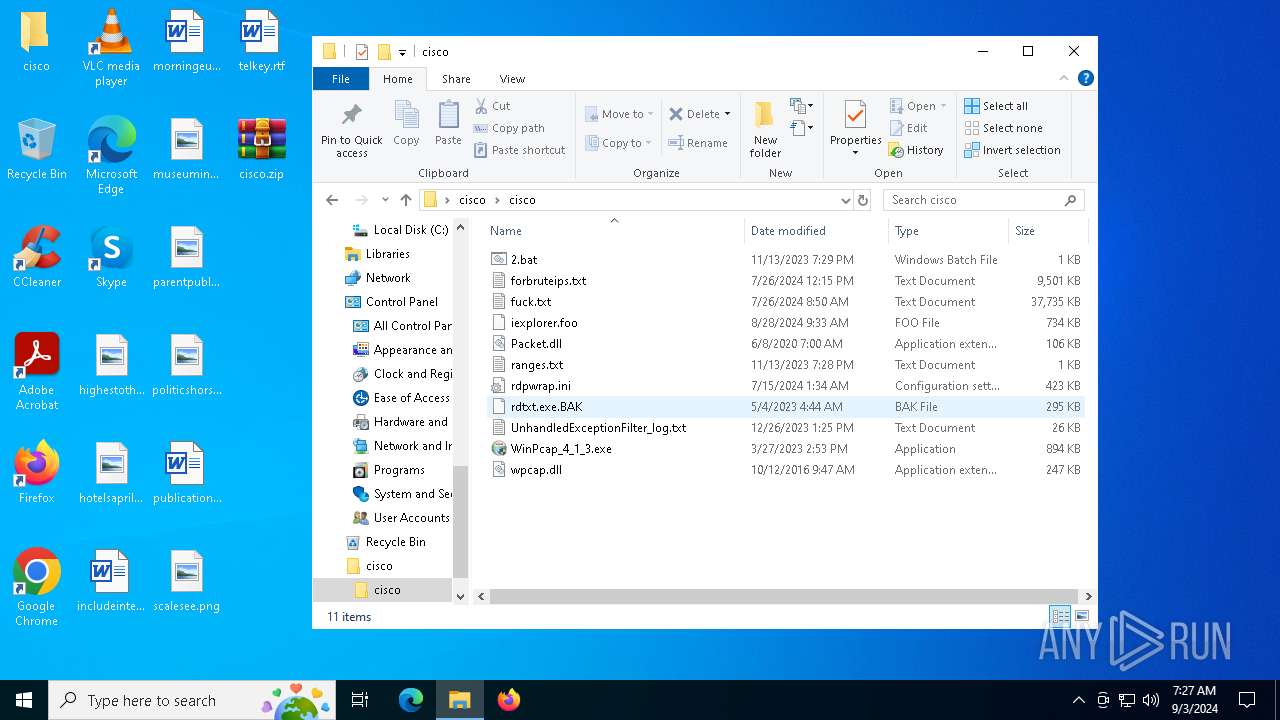
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
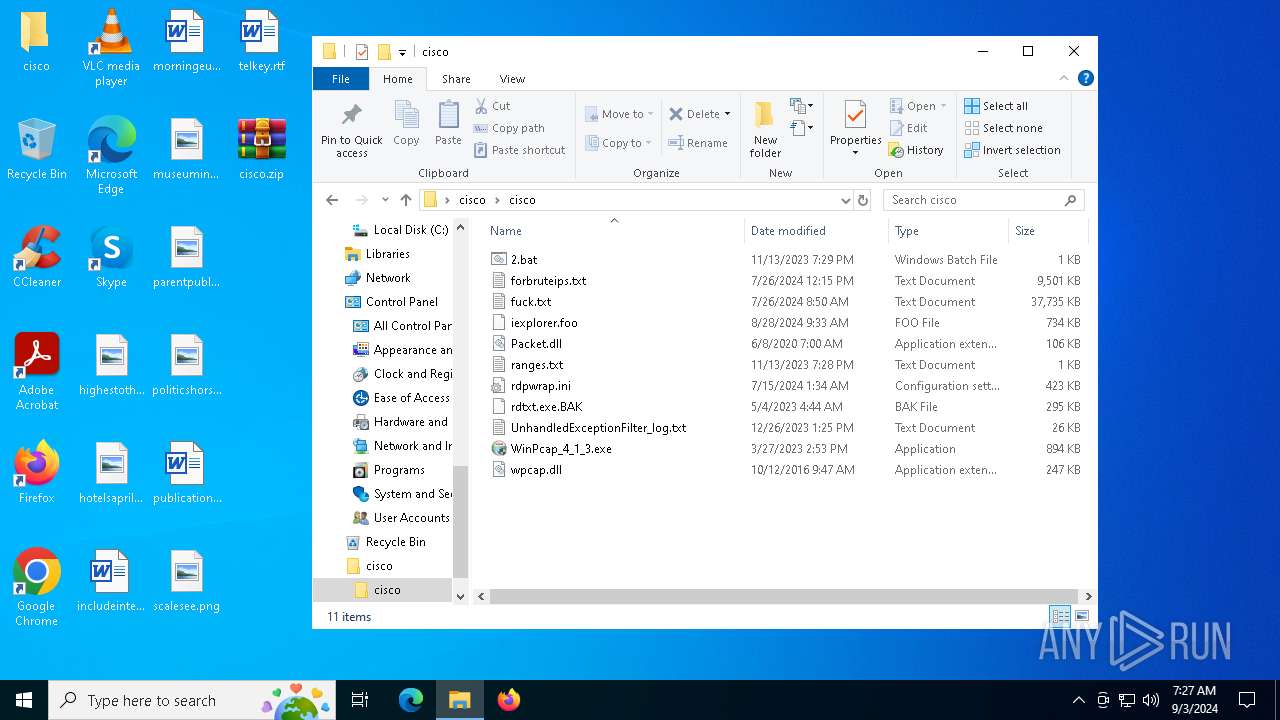
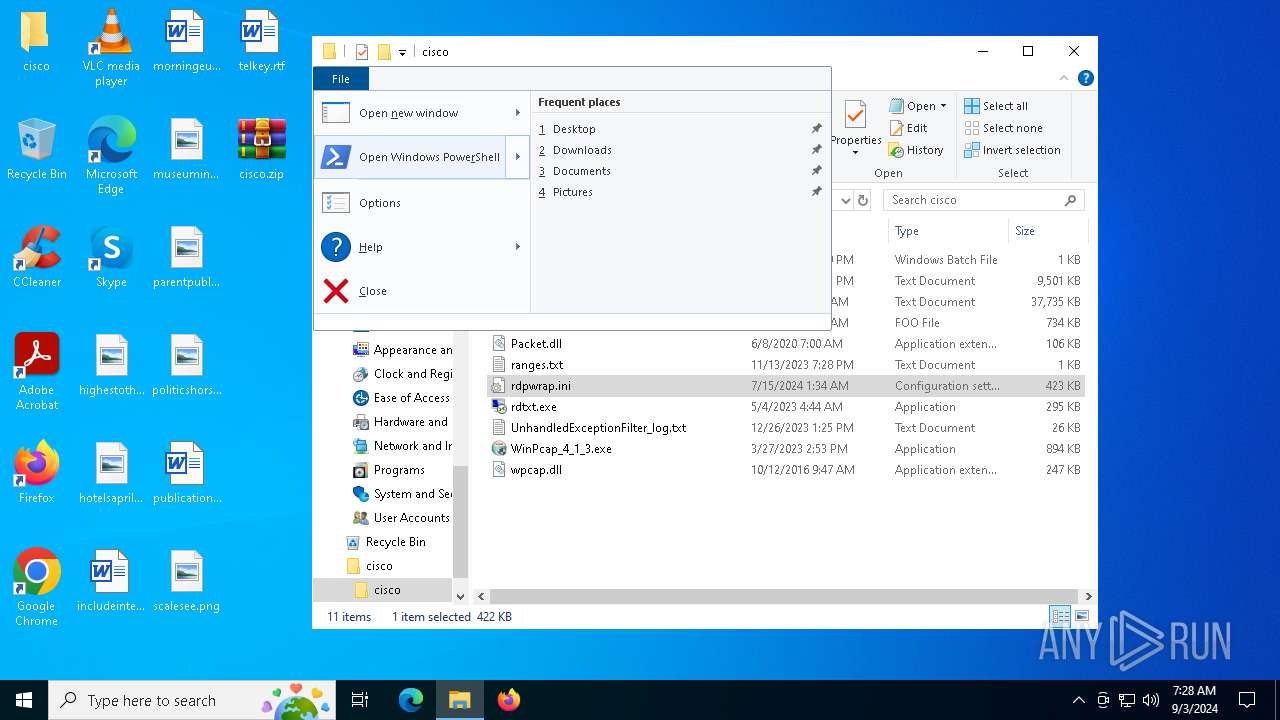
| 3376 | WinRAR.exe | C:\Users\admin\Desktop\cisco\cisco\forbruteips.txt | — | |
MD5:— | SHA256:— | |||
| 3376 | WinRAR.exe | C:\Users\admin\Desktop\cisco\cisco\fuck.txt | — | |
MD5:— | SHA256:— | |||
| 3376 | WinRAR.exe | C:\Users\admin\Desktop\cisco\cisco\2.bat | text | |
MD5:33E4AD52286B54886ED0B7E68A9AAA61 | SHA256:0899C8FA1C56B60D9426E9B8089546A6DEDB7C63FA47F7190AE93B2BE259812D | |||
| 3376 | WinRAR.exe | C:\Users\admin\Desktop\cisco\cisco\Packet.dll | executable | |
MD5:899A5BF1669610CDB78D322AC8D9358B | SHA256:AB3CCE674F5216895FD26A073771F82B05D4C8B214A89F0F288A59774A06B14B | |||
| 3376 | WinRAR.exe | C:\Users\admin\Desktop\cisco\cisco\UnhandledExceptionFilter_log.txt | text | |
MD5:BC82ACB61E1509E8980AB33C7AB5DC33 | SHA256:FA6C78A5B477C312A80AFEA861DF3565CC7B5EF729EB2D59B7541AC439072864 | |||
| 6052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zjkhznoq.0vg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\38GP05IJ35Z4NPJL3J3B.temp | binary | |
MD5:10906D612BBE44AA7944376A940DAAFA | SHA256:04DF106660D21989E099ECBBB74E8A0F9720D2BB06E98D5CC130422CC89A718C | |||
| 3376 | WinRAR.exe | C:\Users\admin\Desktop\cisco\cisco\ranges.txt | text | |
MD5:5BC1A96F08E2640770FBB65804BE7AAA | SHA256:930703938CAD4037BEEC5AAA2B4AF5E8AFC5EFF84628916835D34B0D25096CD8 | |||
| 3376 | WinRAR.exe | C:\Users\admin\Desktop\cisco\cisco\WinPcap_4_1_3.exe | executable | |
MD5:A11A2F0CFE6D0B4C50945989DB6360CD | SHA256:FC4623B113A1F603C0D9AD5F83130BD6DE1C62B973BE9892305132389C8588DE | |||
| 6052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wqm3dche.xvg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
260
DNS requests
16
Threats
218
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3716 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
508 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
508 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5644 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3716 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3716 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
508 | SIHClient.exe | 52.165.165.26:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
508 | SIHClient.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
5940 | rdtxt.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |