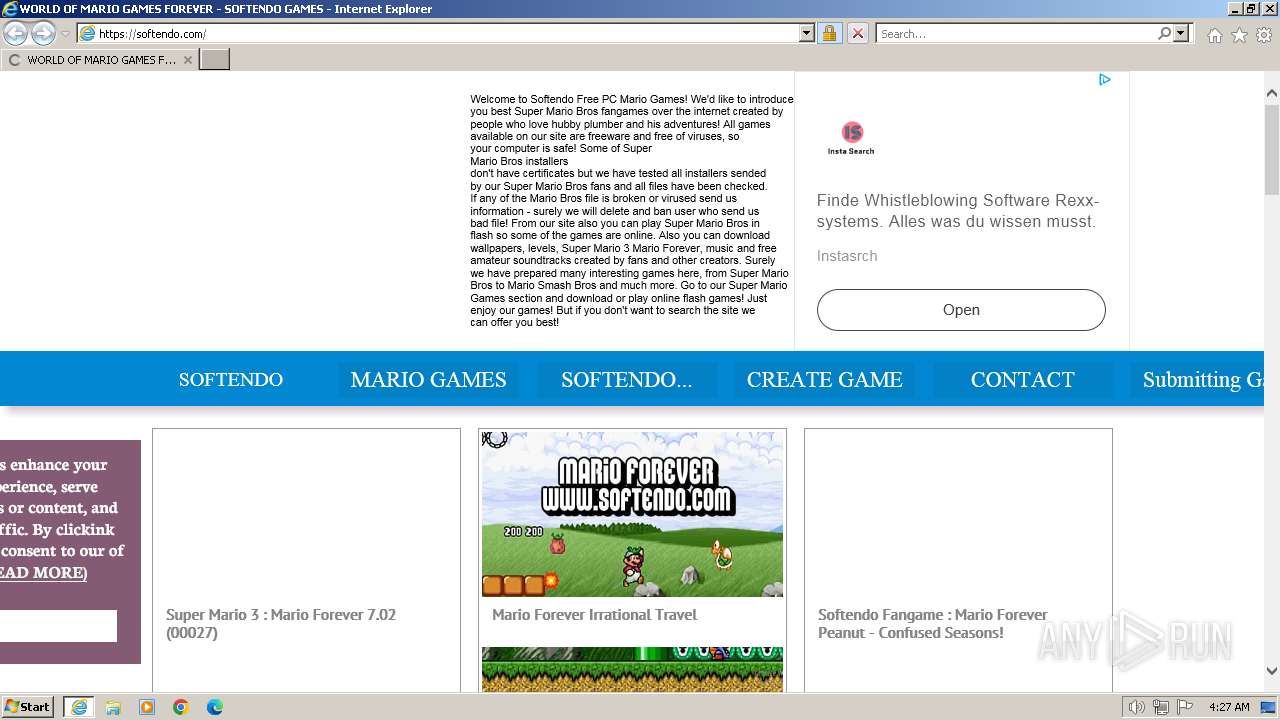
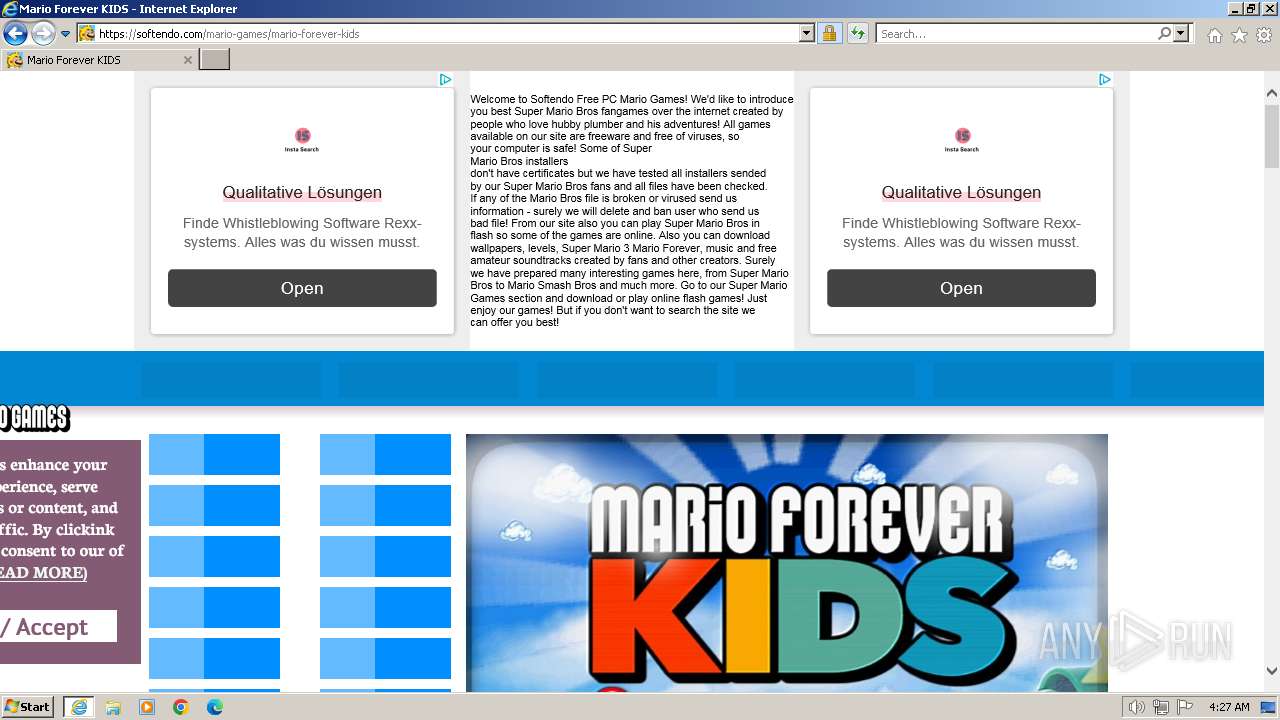
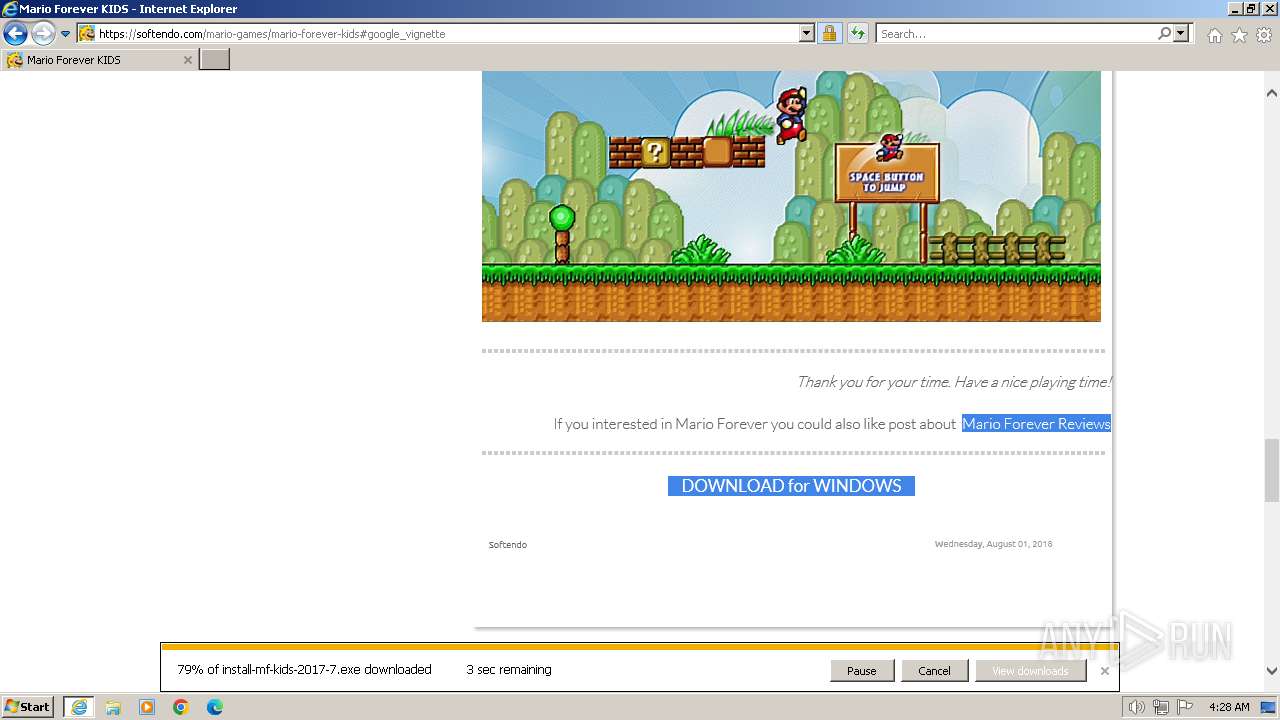
| URL: | softendo.com |
| Full analysis: | https://app.any.run/tasks/03b692c7-6763-4cd9-a5e2-73bedc48a1f6 |
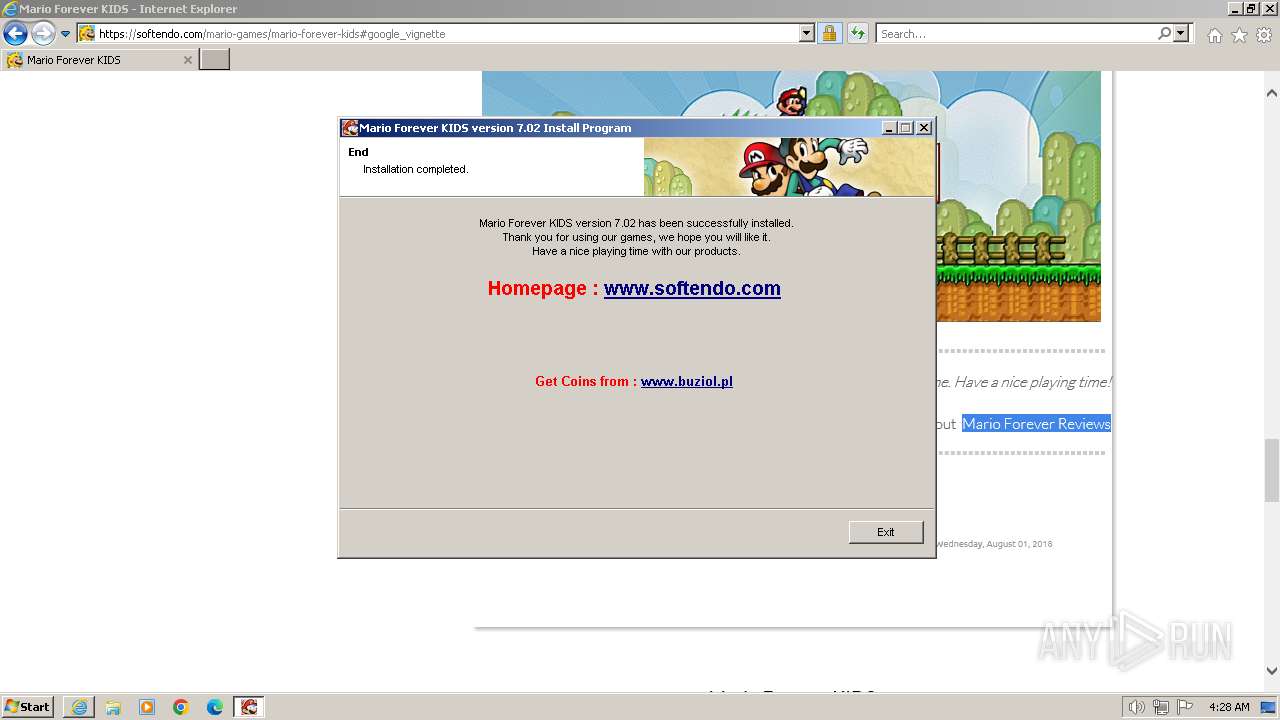
| Verdict: | Malicious activity |
| Analysis date: | December 23, 2023, 04:27:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9A5E12FE1D616EE5FC2CBF50F0EBBBBE |
| SHA1: | AAC606AEBC2A0C5D16ED02423543857656E83B27 |
| SHA256: | 6A67D8CDBCCAD12FE17AE0315B1C093FAC502BE1C250140B97F5E5AA3E123987 |
| SSDEEP: | 3:3w:3w |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
The process uses the downloaded file
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 1740)
- iexplore.exe (PID: 128)
Application launched itself
- iexplore.exe (PID: 128)
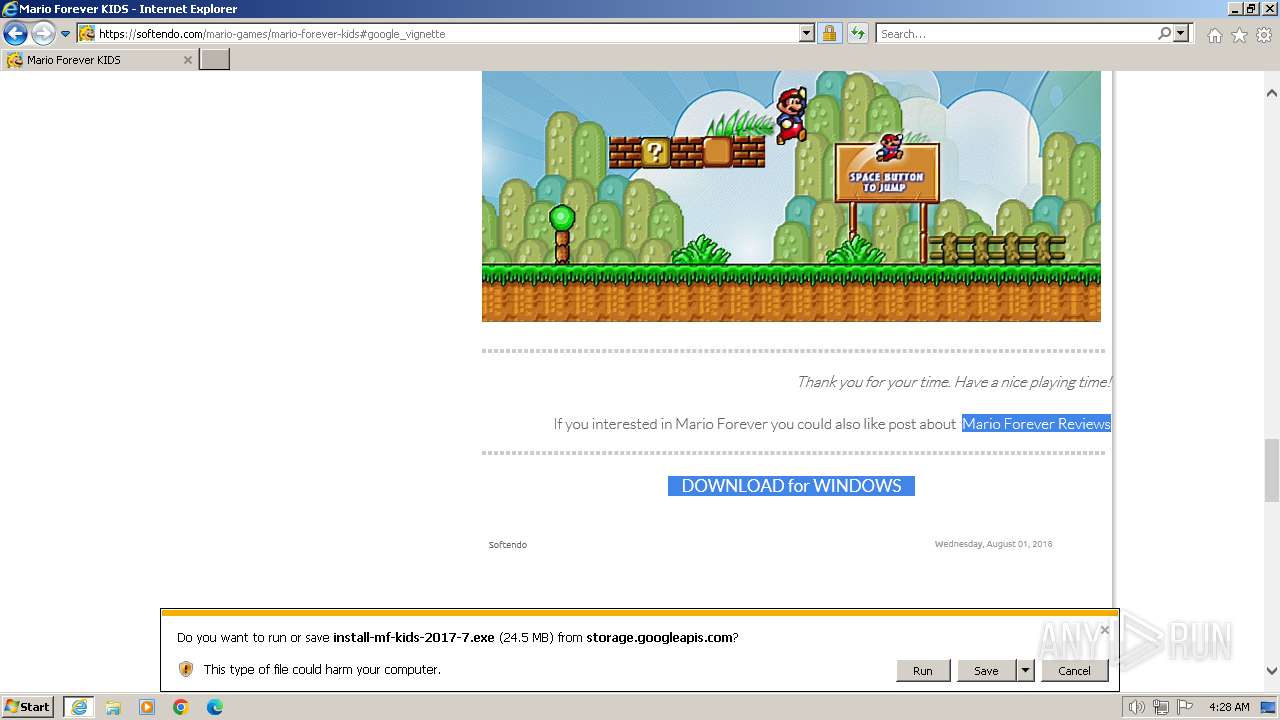
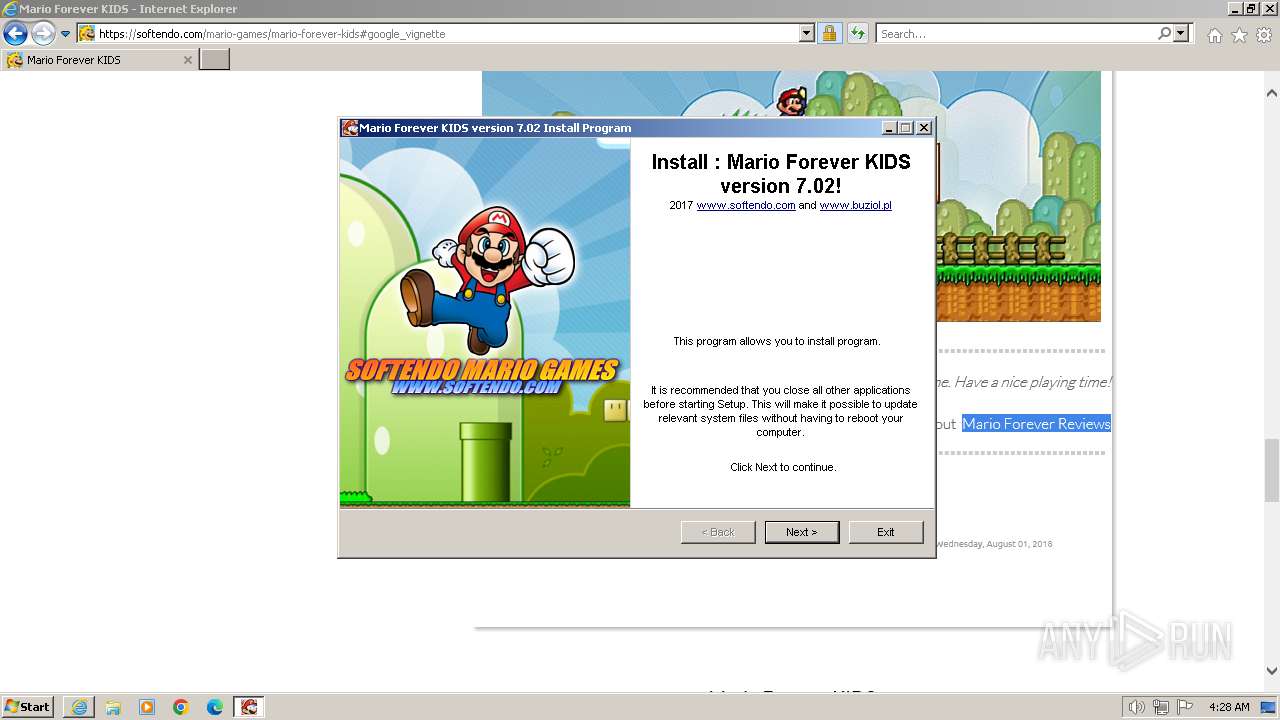
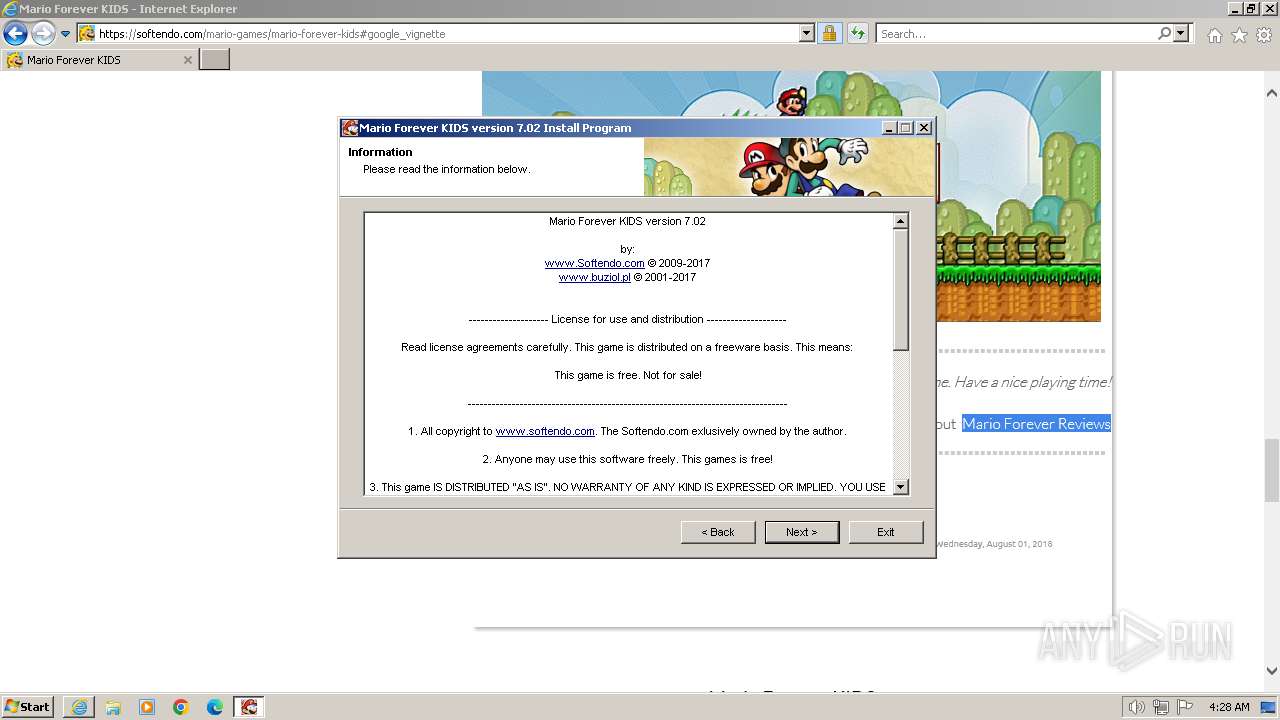
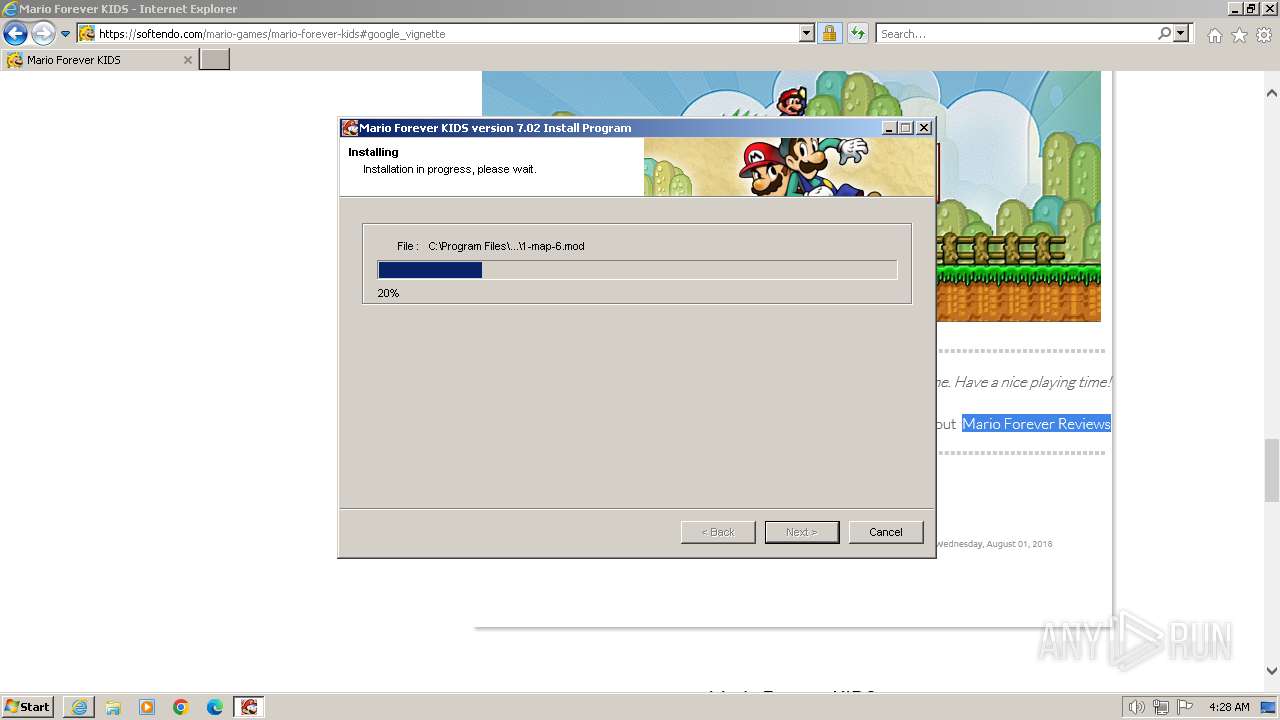
Drops the executable file immediately after the start
- iexplore.exe (PID: 324)
- iexplore.exe (PID: 128)
- install-mf-kids-2017-7.exe (PID: 2780)
Checks supported languages
- install-mf-kids-2017-7.exe (PID: 2780)
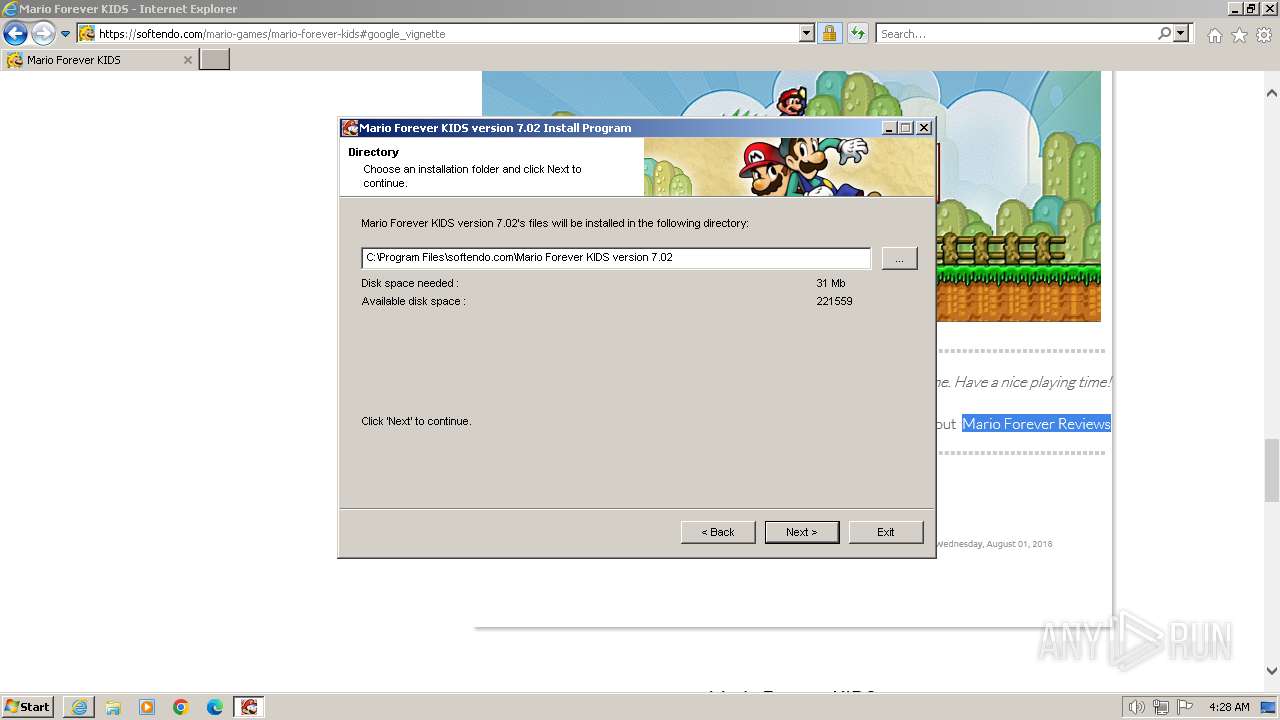
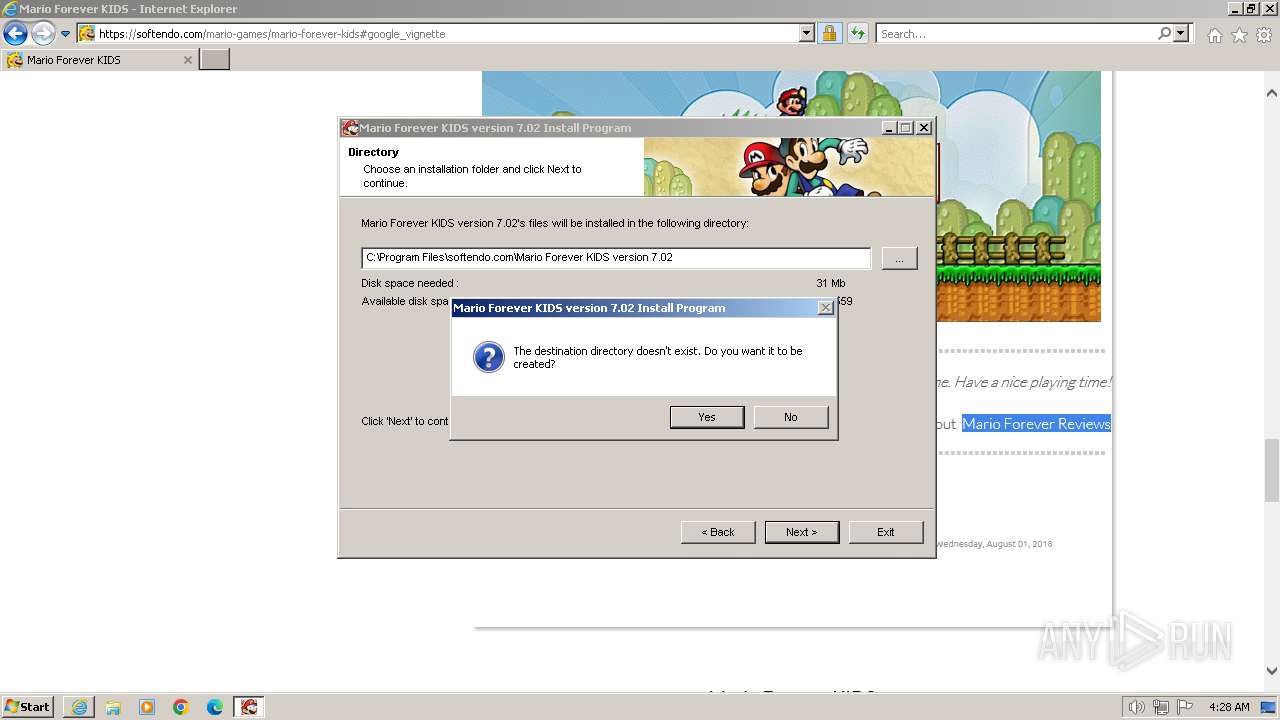
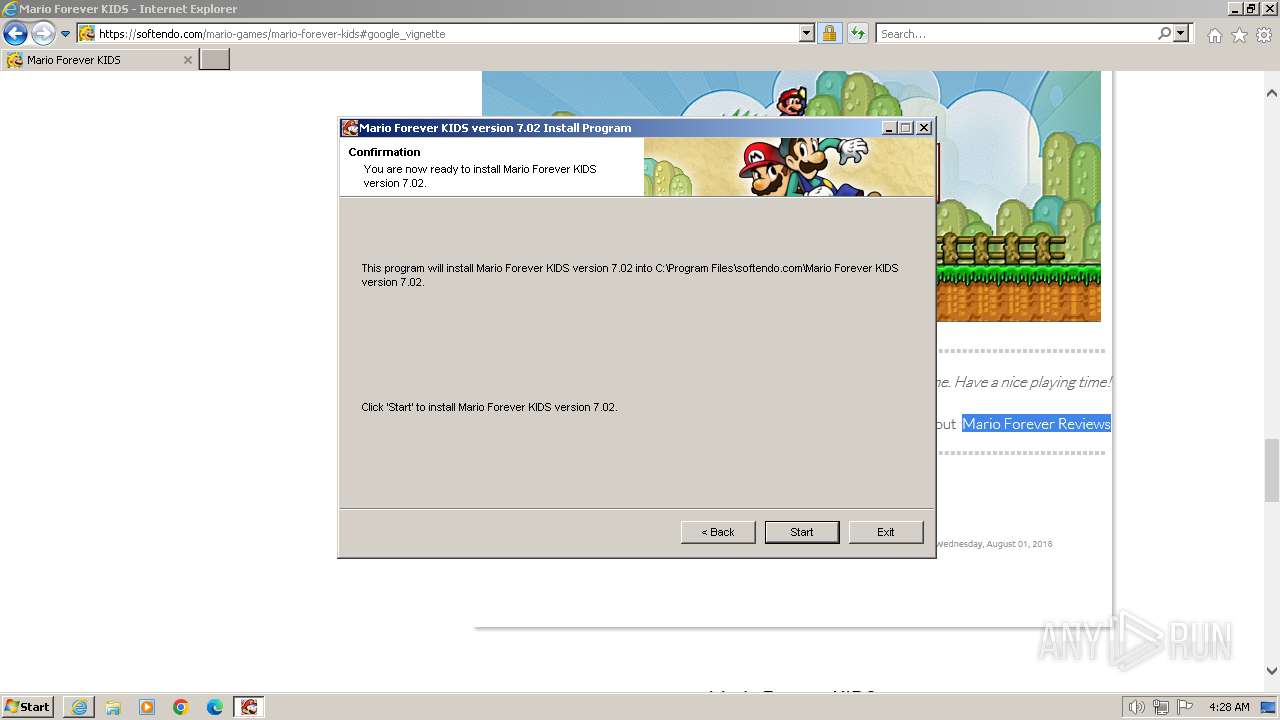
Creates files in the program directory
- install-mf-kids-2017-7.exe (PID: 2780)
Reads the computer name
- install-mf-kids-2017-7.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Internet Explorer\iexplore.exe" "softendo.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 324 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:128 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\install-mf-kids-2017-7.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\install-mf-kids-2017-7.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2, 0, 0, 32 Modules
| |||||||||||||||
| 1740 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\System32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\install-mf-kids-2017-7.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\install-mf-kids-2017-7.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2, 0, 0, 32 Modules
| |||||||||||||||
Total events
20 200
Read events
20 069
Write events
129
Delete events
2
Modification events
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
31
Suspicious files
265
Text files
212
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:845C1DB6CAEC4E662B1B68A60B168036 | SHA256:15F9F5758DEB1CD5361D560686EA66AB5DA5B2A6146C3E172E56187DED32DE86 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:966C13FB6F51E3E08245C49FF4277F56 | SHA256:7847AEBA5F0ED4C4444D4E1FFCE12565A46F910D4C4D9E0EFD3807615306AFEC | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:47D06253D92D68544F320C5174E0683F | SHA256:B8407C4C8C5A91BA79110859B485AECF9EE18ABAB8F0572EBD9E6F671FA850D5 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ATU0HOGY.htm | html | |
MD5:6E4ED61987A99B6639D30E175CFD6D83 | SHA256:19B28A9C392EF255F4624627E98FC013408A61980497F5926F39533BA5FB34EF | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:F755A40F164F79A6CF5A9E38EBCF5F56 | SHA256:8E7025E50FC3F89D1DDA4A9E81A2A38E07B208C991F6D229446EAE90944AE0BC | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:0533ED6689F8C16ACF273535AC32F800 | SHA256:807AF7324E5B3CDFF0D3448D2EABBA97497E9978697BE91830EB2812F21C9D0B | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_107454EA5A4B1BFBF1DC08B35D119AB9 | binary | |
MD5:EA4F64BFD285D35AE7908CD4A8BC6CBC | SHA256:FCCCD1246971694F317B9470144C4B0B36CA9B63434AA1F3BD98CCE4035BDAFB | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:AA471AD3D4F639FA3D56F7B99838488D | SHA256:D1E9A5E3AAB91EABB8EC2AA2C282305B71059F719213EA367C5AD2EEB658B0C2 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_107454EA5A4B1BFBF1DC08B35D119AB9 | binary | |
MD5:9C716CCBBDBD2ECE655B99135C1C38B0 | SHA256:4E479A42539145BD6274D0B129CF0C679646AA43FF8D4BA12F483DCBE24B1CF6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
150
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
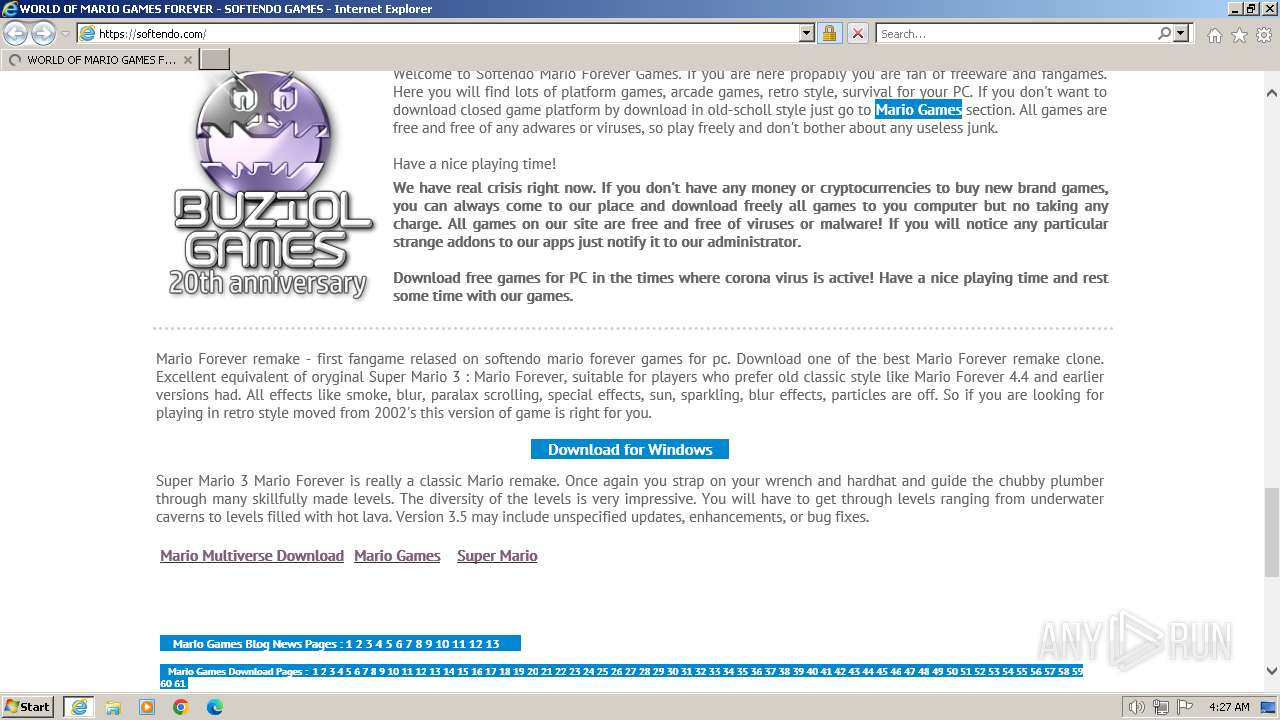
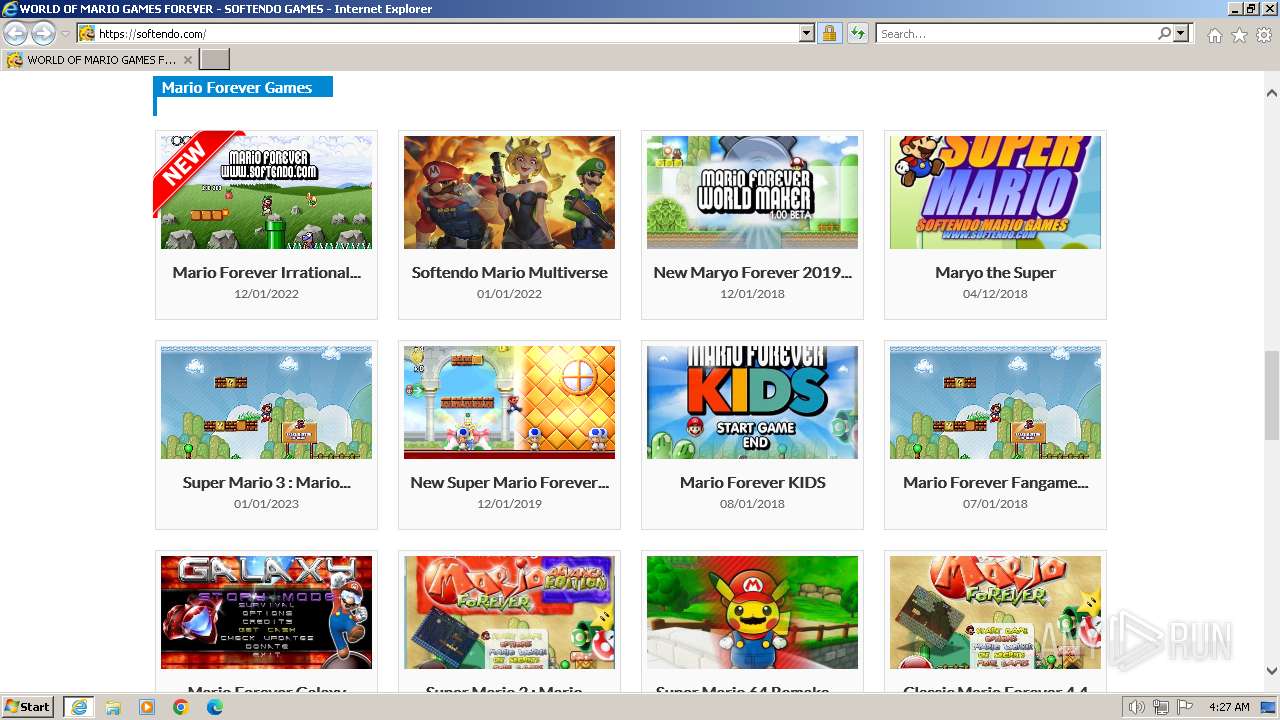
324 | iexplore.exe | GET | 301 | 66.235.200.4:80 | http://softendo.com/ | unknown | — | — | unknown |
324 | iexplore.exe | GET | 200 | 23.53.40.49:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6243fee378382ed7 | unknown | compressed | 4.66 Kb | unknown |
324 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
324 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
324 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://crt.sectigo.com/SectigoRSADomainValidationSecureServerCA.crt | unknown | binary | 1.52 Kb | unknown |
324 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://crt.sectigo.com/SectigoRSADomainValidationSecureServerCA.crt | unknown | binary | 1.52 Kb | unknown |
324 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
324 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
324 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | unknown |
324 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDy12RNyhrO3AoNxrRddGYl | unknown | binary | 472 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
324 | iexplore.exe | 66.235.200.4:80 | softendo.com | CLOUDFLARENET | US | unknown |
324 | iexplore.exe | 66.235.200.4:443 | softendo.com | CLOUDFLARENET | US | unknown |
324 | iexplore.exe | 23.53.40.49:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
324 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
324 | iexplore.exe | 142.250.186.168:443 | www.googletagmanager.com | GOOGLE | US | unknown |
324 | iexplore.exe | 68.232.34.200:443 | 149b4.wpc.azureedge.net | EDGECAST | US | whitelisted |
324 | iexplore.exe | 142.250.74.219:443 | storage.googleapis.com | GOOGLE | US | unknown |
324 | iexplore.exe | 35.190.14.35:443 | components.mywebsitebuilder.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
softendo.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
149b4.wpc.azureedge.net |
| whitelisted |
components.mywebsitebuilder.com |
| unknown |
storage.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
crt.sectigo.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |